Raf Portnoy SVP Technology Steve Sheinberg General Counsel
Raf Portnoy SVP, Technology Steve Sheinberg General Counsel SVP, Privacy & Security BUILDING A PRIVACY AND SECURITY PROGRAM FOR YOUR NON-PROFIT
THINKING ABOUT DATA GOVERNANCE Create employee policies and build a culture that recognizes that employees are the main threat vector. Teach employees, especially about social engineering. Talk to the CIO. Get your board onboard. Get good agreements with vendors and key employees. Plan well and strive for Cyber Resiliency. Update software, install patches, remove non-approved software and hardware. Follow the principle of least privilege. Use two-factor authentication. Ensure that your physical security is sufficient. Encrypt all data, period. Segregate differing data onto separate networks. Monitor network traffic. {Most of this is policy, not tech, driven} Sheinberg and Portnoy | 2
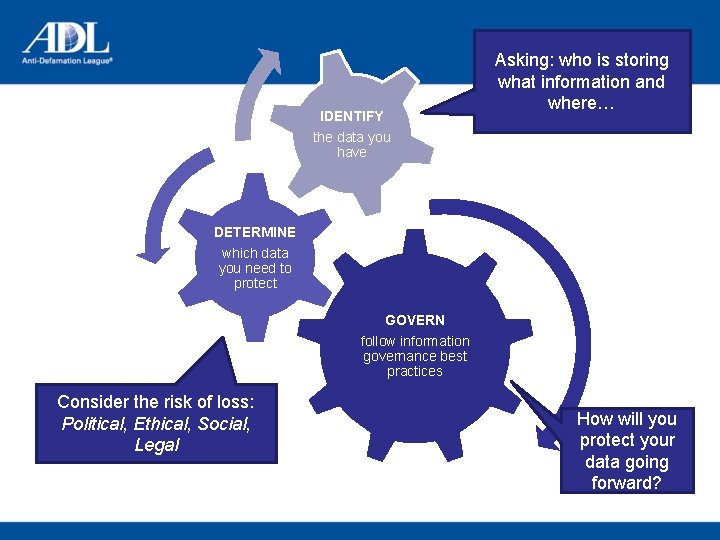
IDENTIFY Asking: who is storing what information and where… the data you have DETERMINE which data you need to protect GOVERN follow information governance best practices Consider the risk of loss: Political, Ethical, Social, Legal How will you protect your data going forward?
Mission: The mission of the Information Security and Privacy Program is to provide exceptional, secure infrastructure support and innovation in the delivery of information technology security products and services to Your Organization staff and clients. q. Improve cyber security awareness and data asset management. q. Protect information and systems to ensure that the confidentiality, integrity, and availability of all information is consistent with mission needs, internal and external threats, information value, and industry compliance.
Information Security Needs q The number and complexity of information security threats are increasing. Advanced Persistent Threats (APTs) have penetrated environments that were previously thought to have been adequately secured and can remain unnoticed for extended periods of time. q Data system growth is compounding the need for increased security attention. Additionally, mobile security, cloud security, big data security, and social media security are now “today’s problems. ”

Information Security Needs How do we know this is enough? q. We are employing cybersecurity best practices q. We are following the recommendations made by our IT auditors. q. We are following recommendations by our Security Compliance consultants.
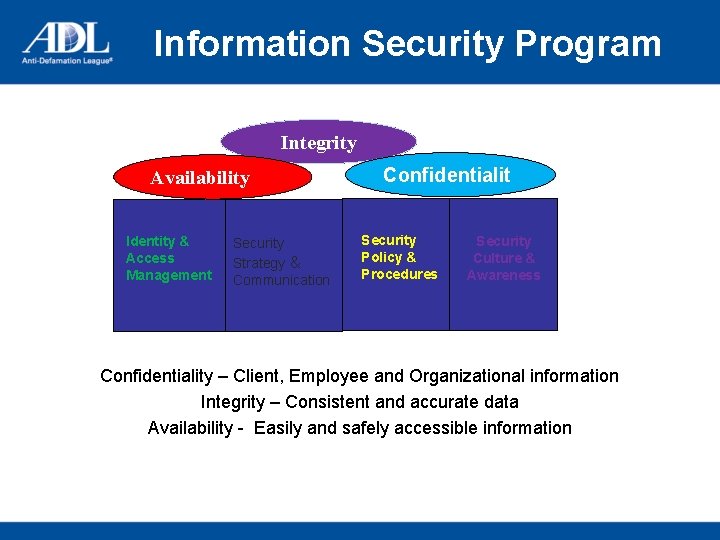
Information Security Program Integrity Availability Identity & Access Management Security Strategy & Communication Confidentialit y Security Policy & Procedures Security Culture & Awareness Confidentiality – Client, Employee and Organizational information Integrity – Consistent and accurate data Availability - Easily and safely accessible information
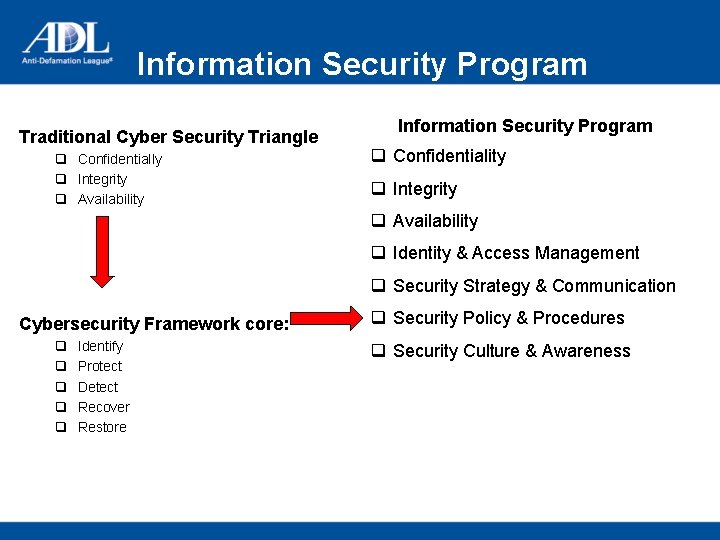
Information Security Program Traditional Cyber Security Triangle q Confidentially q Integrity q Availability Information Security Program q Confidentiality q Integrity q Availability q Identity & Access Management q Security Strategy & Communication Cybersecurity Framework core: q q q Identify Protect Detect Recover Restore q Security Policy & Procedures q Security Culture & Awareness
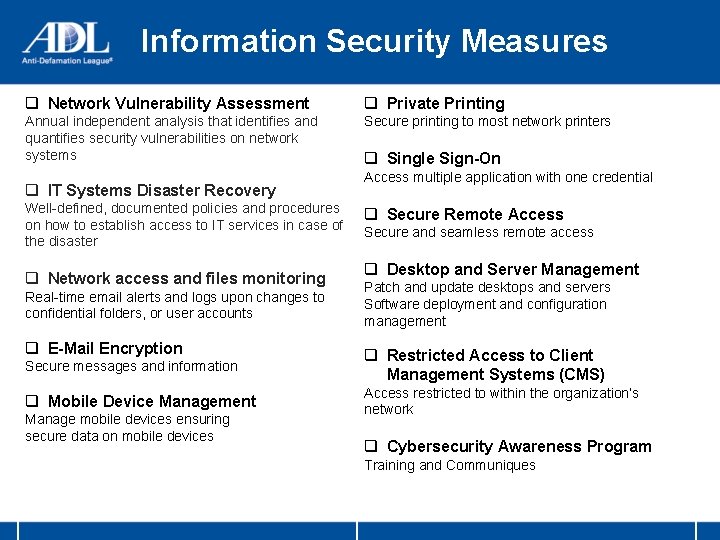
Information Security Measures q Network Vulnerability Assessment q Private Printing Annual independent analysis that identifies and quantifies security vulnerabilities on network systems Secure printing to most network printers q IT Systems Disaster Recovery Well-defined, documented policies and procedures on how to establish access to IT services in case of the disaster q Network access and files monitoring Real-time email alerts and logs upon changes to confidential folders, or user accounts q E-Mail Encryption q Single Sign-On Access multiple application with one credential q Secure Remote Access Secure and seamless remote access q Desktop and Server Management Patch and update desktops and servers Software deployment and configuration management Secure messages and information q Restricted Access to Client Management Systems (CMS) q Mobile Device Management Access restricted to within the organization’s network Manage mobile devices ensuring secure data on mobile devices q Cybersecurity Awareness Program Training and Communiques
Thank you! Questions?
- Slides: 10