R 75 20 2011 Check Point Software Technologies

![…обновление R 75. 20 Check Point © 2011 Check Point Software Technologies Ltd. [PROTECTED] …обновление R 75. 20 Check Point © 2011 Check Point Software Technologies Ltd. [PROTECTED]](https://slidetodoc.com/presentation_image_h2/e30722afbdb1aee94d5c88c70af63171/image-3.jpg)




![Спасибо! © 2011 Check Point Software Technologies Ltd. [PROTECTED] — All rights reserved Спасибо! © 2011 Check Point Software Technologies Ltd. [PROTECTED] — All rights reserved](https://slidetodoc.com/presentation_image_h2/e30722afbdb1aee94d5c88c70af63171/image-25.jpg)
- Slides: 25
Новая версия шлюза безопасности R 75. 20. Новый функционал. © 2011 Check Point Software Technologies Ltd. [PROTECTED] — All rights reserved

В начале года вышла версия R 75… Check Point © 2011 Check Point Software Technologies Ltd. [PROTECTED] — All rights reserved. | 2 2
![обновление R 75 20 Check Point 2011 Check Point Software Technologies Ltd PROTECTED …обновление R 75. 20 Check Point © 2011 Check Point Software Technologies Ltd. [PROTECTED]](https://slidetodoc.com/presentation_image_h2/e30722afbdb1aee94d5c88c70af63171/image-3.jpg)
…обновление R 75. 20 Check Point © 2011 Check Point Software Technologies Ltd. [PROTECTED] — All rights reserved. | 3 3

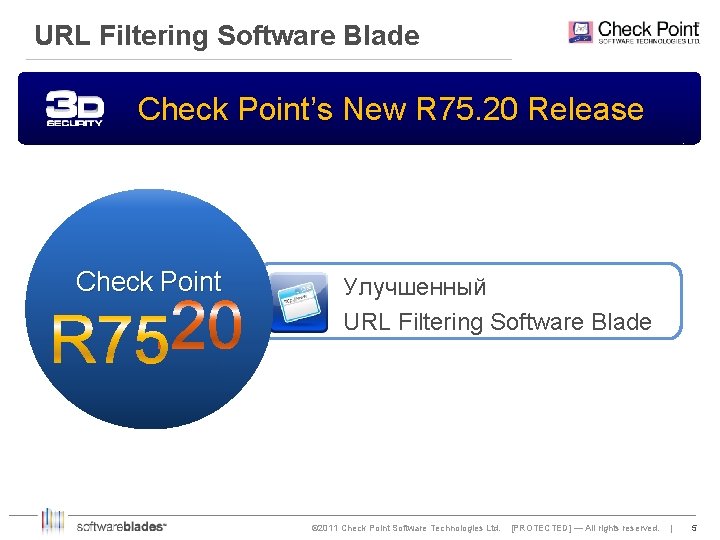
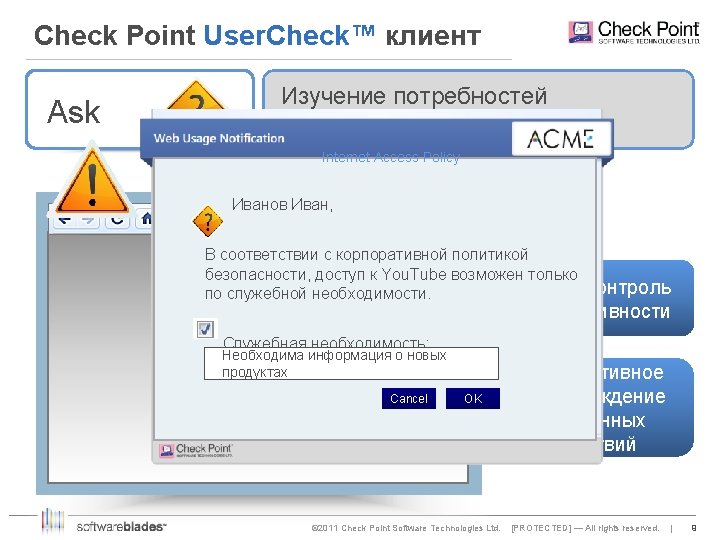
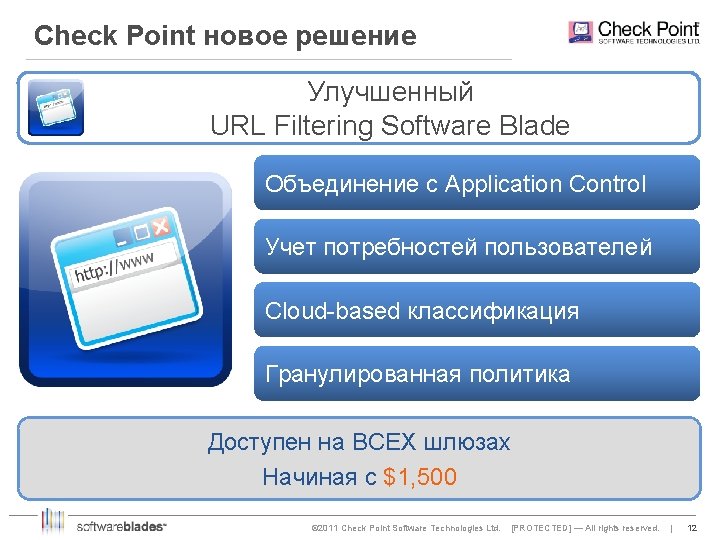
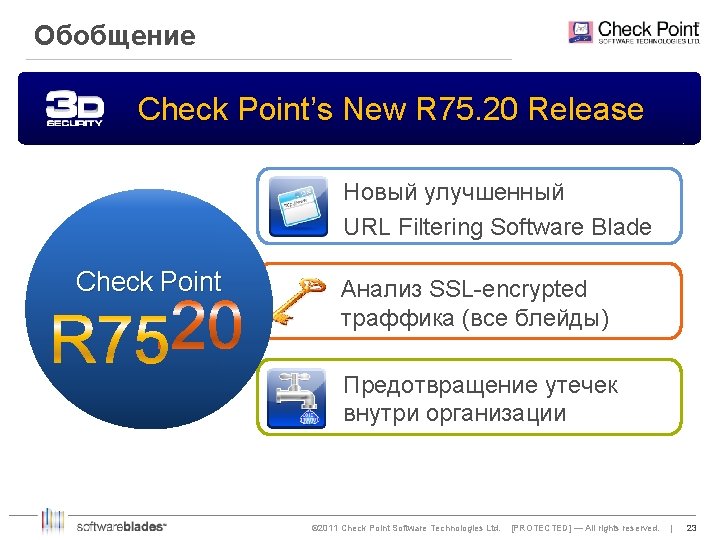
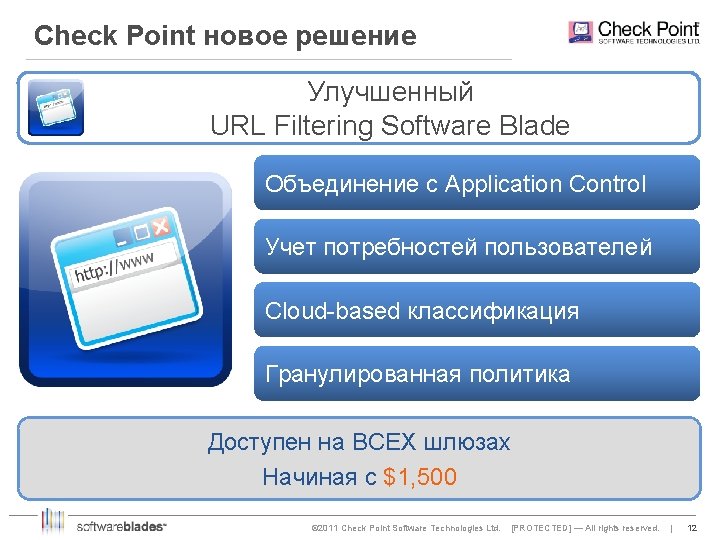
URL Filtering Software Blade Check Point’s New R 75. 20 Release Check Point Улучшенный URL Filtering Software Blade © 2011 Check Point Software Technologies Ltd. [PROTECTED] — All rights reserved. | 5 5

Необходимость контроля всего WEB трафика Websites Applications Not URL-based www. hackthissite. org www. fantasyfootball. com Facebook Chat Granularity beyond URLs Нужен унифицированный контроль! © 2011 Check Point Software Technologies Ltd. [PROTECTED] — All rights reserved. | 6 6
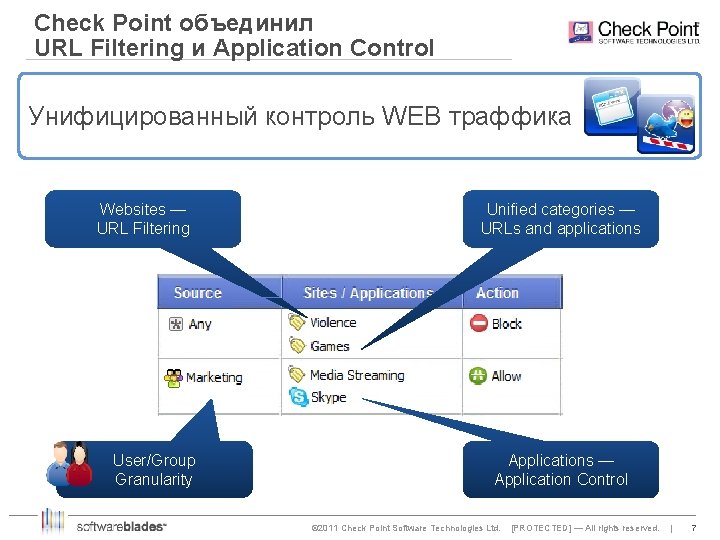
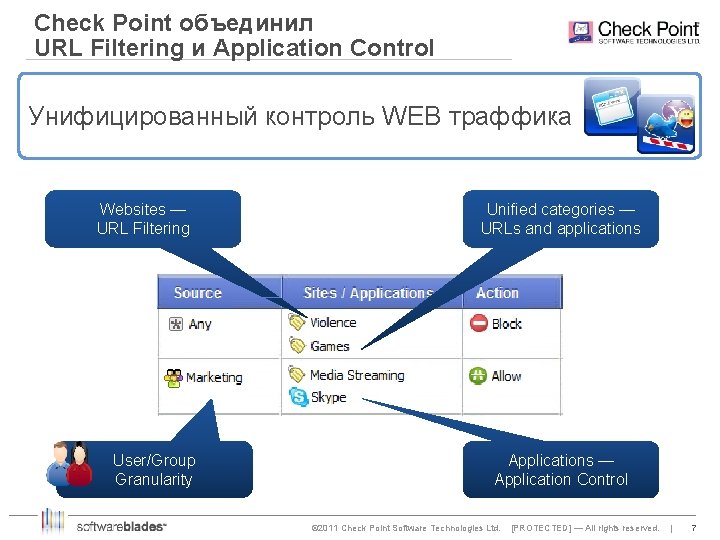
Check Point объединил URL Filtering и Application Control Унифицированный контроль WEB траффика Websites — URL Filtering User/Group Granularity Unified categories — URLs and applications Applications — Application Control © 2011 Check Point Software Technologies Ltd. [PROTECTED] — All rights reserved. | 7 7


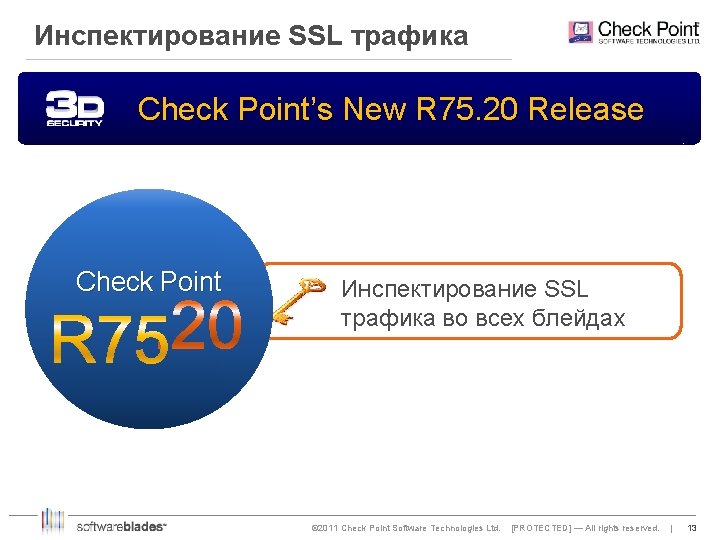
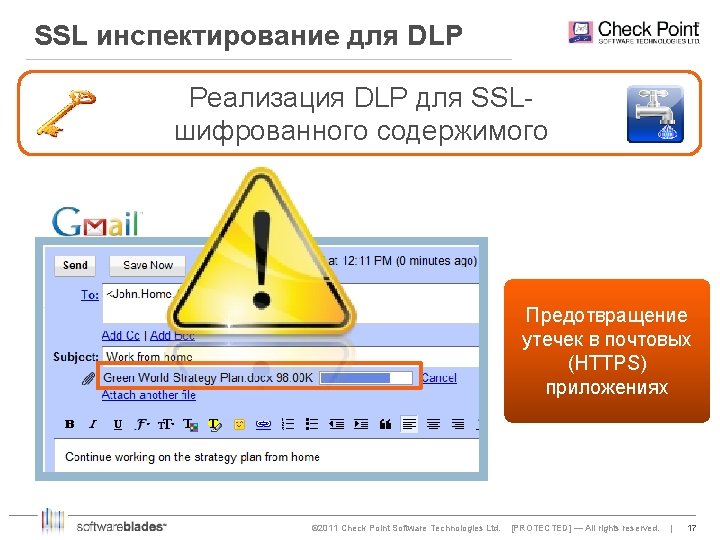
Инспектирование SSL трафика Check Point’s New R 75. 20 Release Check Point Инспектирование SSL трафика во всех блейдах © 2011 Check Point Software Technologies Ltd. [PROTECTED] — All rights reserved. | 13 13
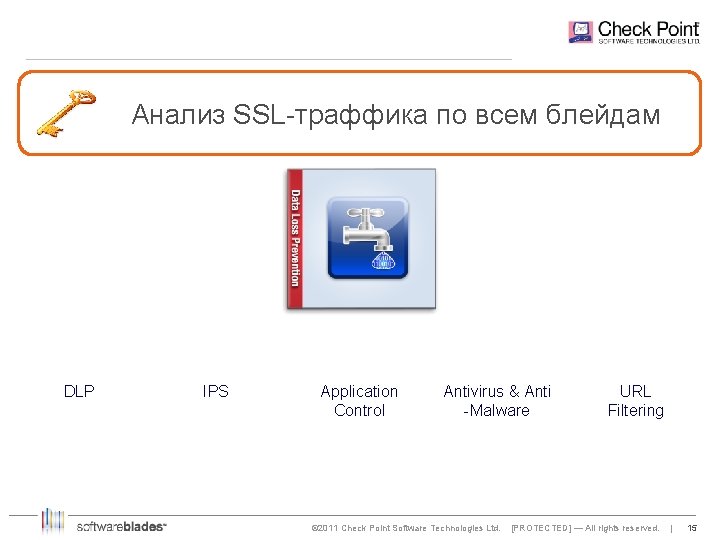
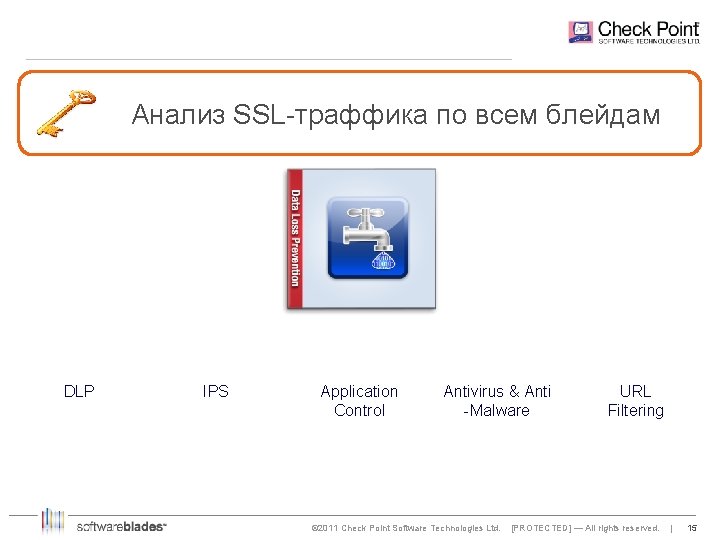
Анализ SSL-траффика по всем блейдам DLP IPS Application Control Antivirus & Anti -Malware © 2011 Check Point Software Technologies Ltd. URL Filtering [PROTECTED] — All rights reserved. | 15 15
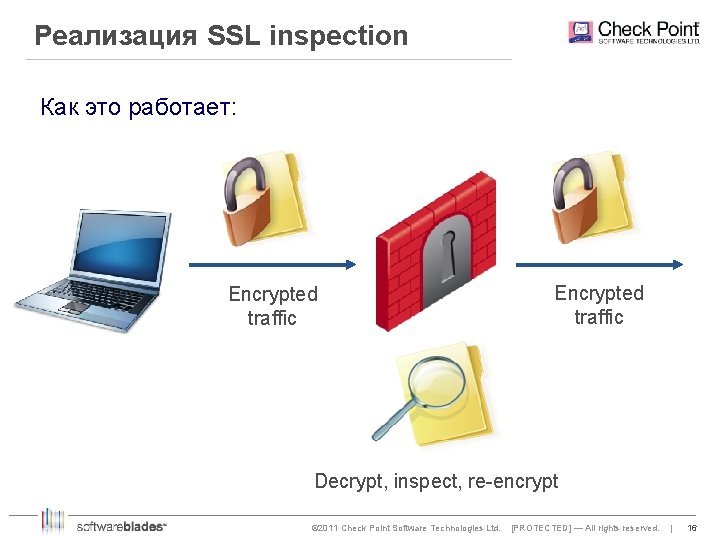
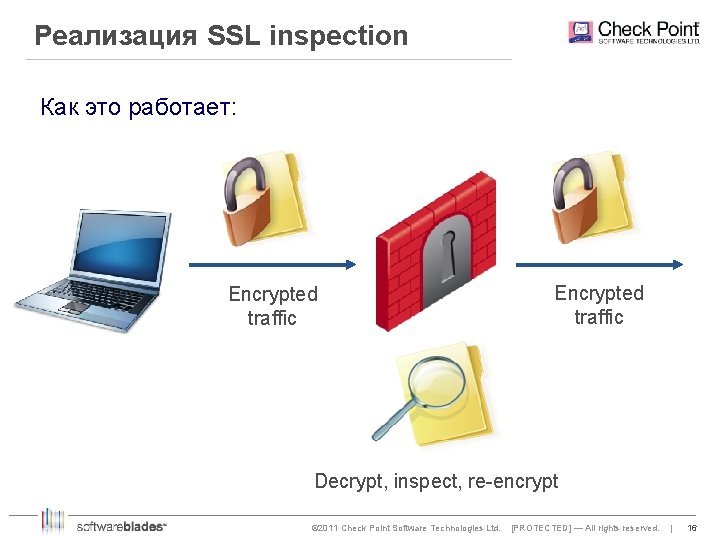
Реализация SSL inspection Как это работает: Encrypted traffic Decrypt, inspect, re-encrypt © 2011 Check Point Software Technologies Ltd. [PROTECTED] — All rights reserved. | 16 16
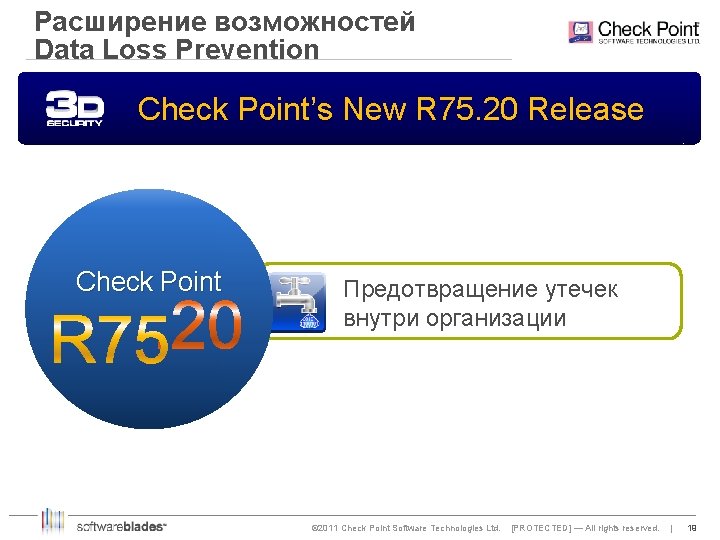
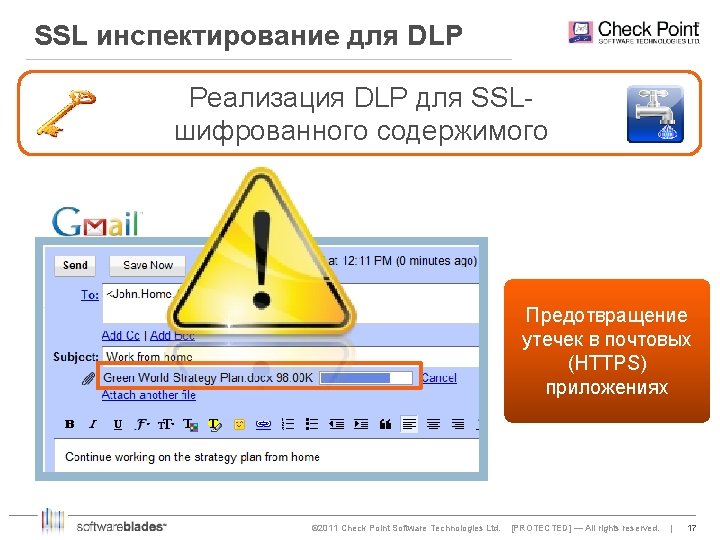
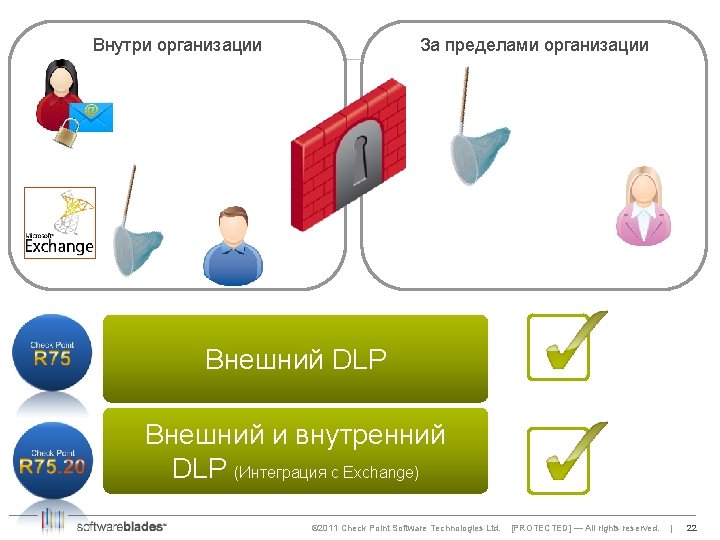
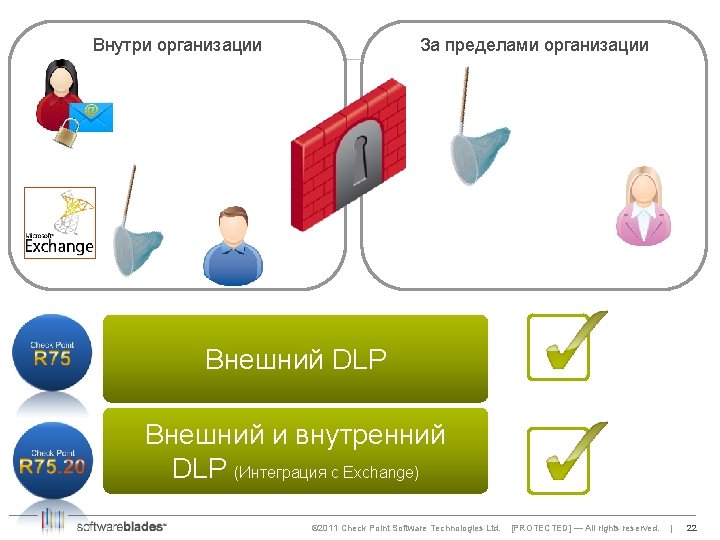
Расширение возможностей Data Loss Prevention Check Point’s New R 75. 20 Release Check Point Предотвращение утечек внутри организации © 2011 Check Point Software Technologies Ltd. [PROTECTED] — All rights reserved. | 19 19
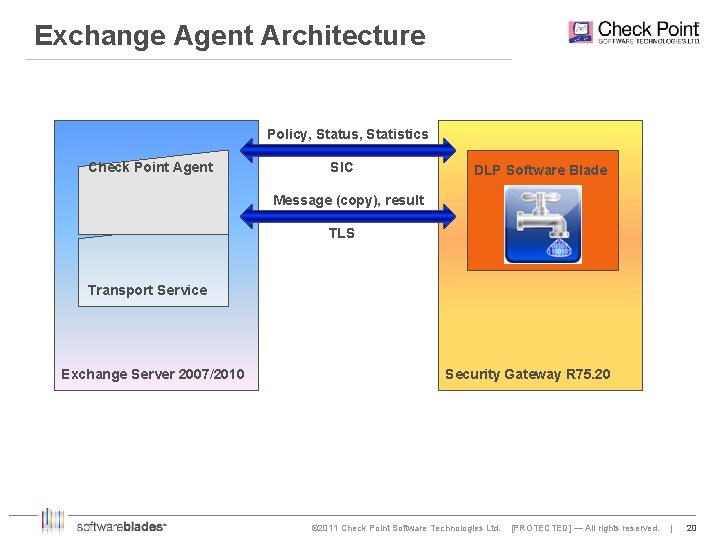
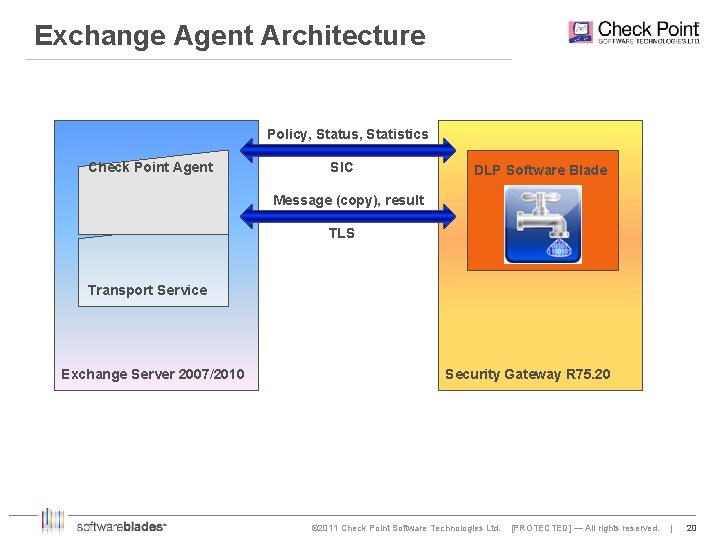
Exchange Agent Architecture Policy, Status, Statistics Check Point Agent SIC DLP Software Blade Message (copy), result TLS Transport Service Exchange Server 2007/2010 Security Gateway R 75. 20 © 2011 Check Point Software Technologies Ltd. [PROTECTED] — All rights reserved. | 20 20
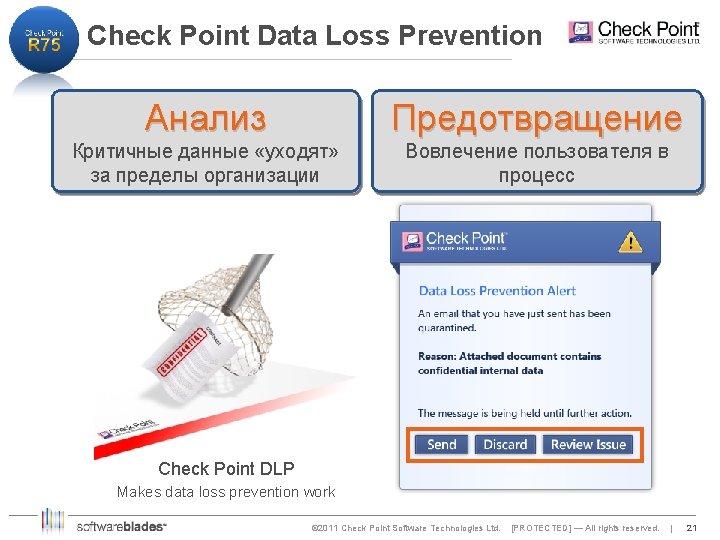
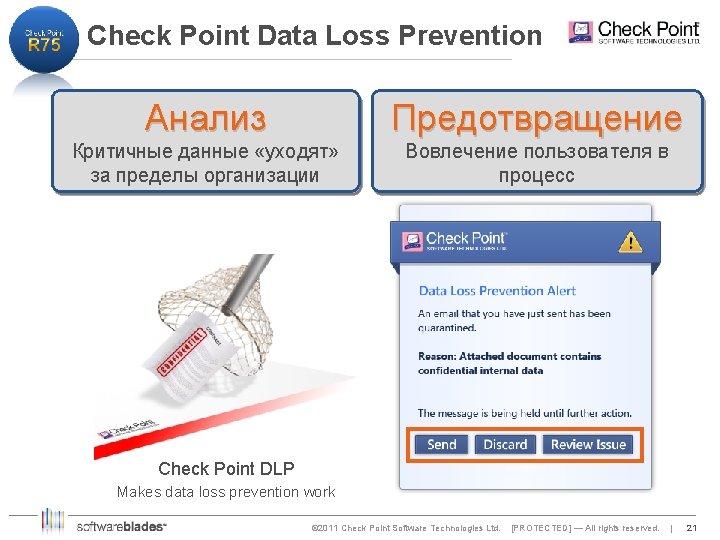
Check Point Data Loss Prevention Анализ Предотвращение Критичные данные «уходят» за пределы организации Вовлечение пользователя в процесс Check Point DLP Makes data loss prevention work © 2011 Check Point Software Technologies Ltd. [PROTECTED] — All rights reserved. | 21 21
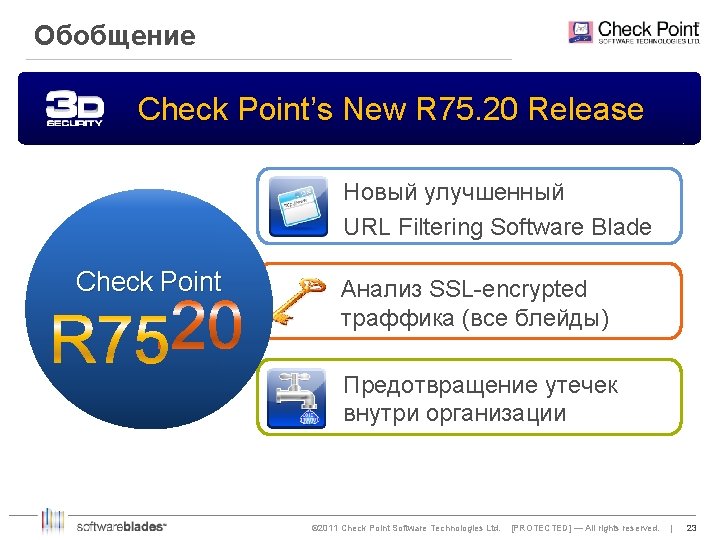
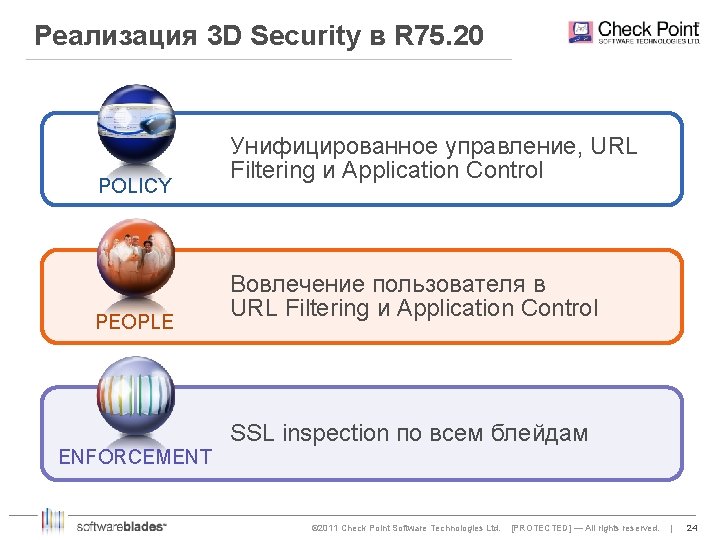
Обобщение Check Point’s New R 75. 20 Release Новый улучшенный URL Filtering Software Blade Check Point Анализ SSL-encrypted траффика (все блейды) Предотвращение утечек внутри организации © 2011 Check Point Software Technologies Ltd. [PROTECTED] — All rights reserved. | 23 23
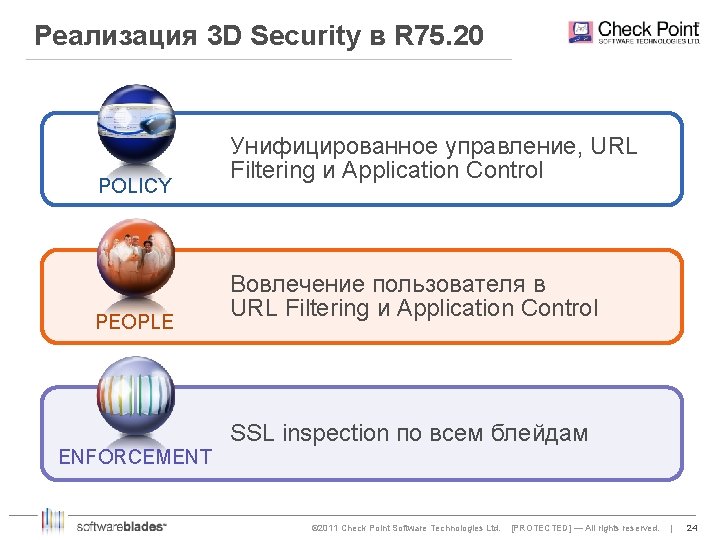
Реализация 3 D Security в R 75. 20 POLICY PEOPLE Унифицированное управление, URL Filtering и Application Control Вовлечение пользователя в URL Filtering и Application Control SSL inspection по всем блейдам ENFORCEMENT © 2011 Check Point Software Technologies Ltd. [PROTECTED] — All rights reserved. | 24 24
![Спасибо 2011 Check Point Software Technologies Ltd PROTECTED All rights reserved Спасибо! © 2011 Check Point Software Technologies Ltd. [PROTECTED] — All rights reserved](https://slidetodoc.com/presentation_image_h2/e30722afbdb1aee94d5c88c70af63171/image-25.jpg)
Спасибо! © 2011 Check Point Software Technologies Ltd. [PROTECTED] — All rights reserved