Quantum Cryptography 1 e 29 LOCK 29996224275833 x
![Result -sin(q 1 -q 2) [|00> + |11>] Coincidence + cos(q 1 -q 2) Result -sin(q 1 -q 2) [|00> + |11>] Coincidence + cos(q 1 -q 2)](https://slidetodoc.com/presentation_image/ec64489b59d45f3eb52cd35872119f2e/image-40.jpg)
![TO + OC + CT ≤ 2 P ( A & [not B] ) TO + OC + CT ≤ 2 P ( A & [not B] )](https://slidetodoc.com/presentation_image/ec64489b59d45f3eb52cd35872119f2e/image-46.jpg)

- Slides: 65
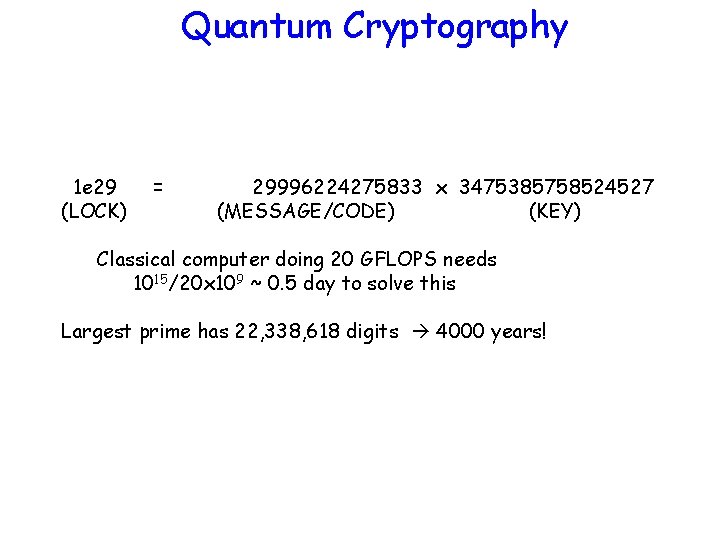
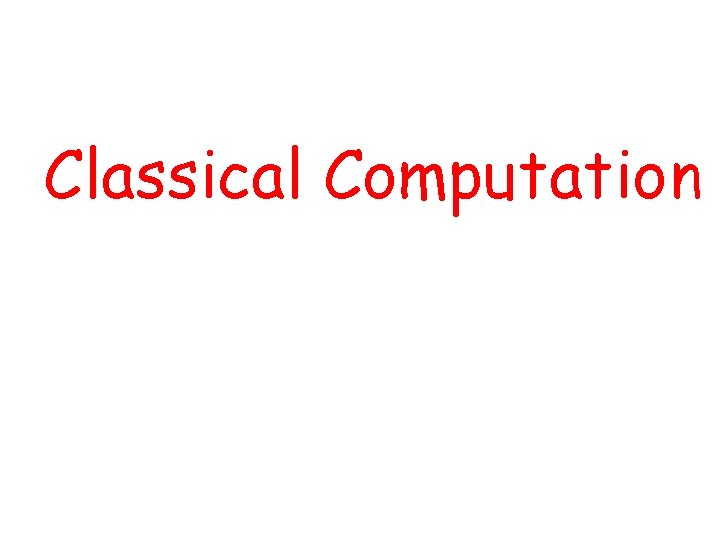
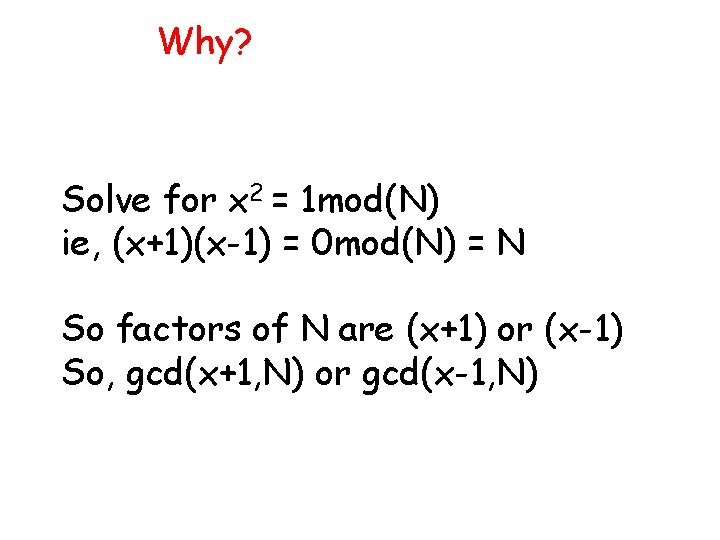
Quantum Cryptography 1 e 29 (LOCK) = 29996224275833 x 3475385758524527 (MESSAGE/CODE) (KEY) Classical computer doing 20 GFLOPS needs 1015/20 x 109 ~ 0. 5 day to solve this Largest prime has 22, 338, 618 digits 4000 years!
Classical Computation
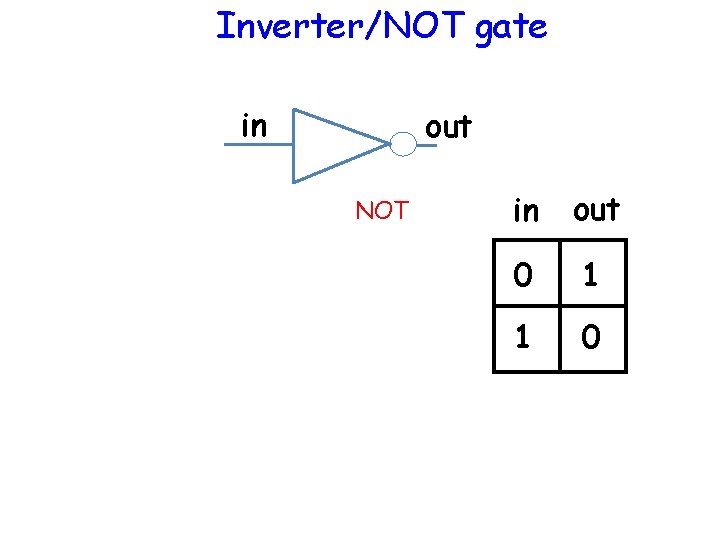
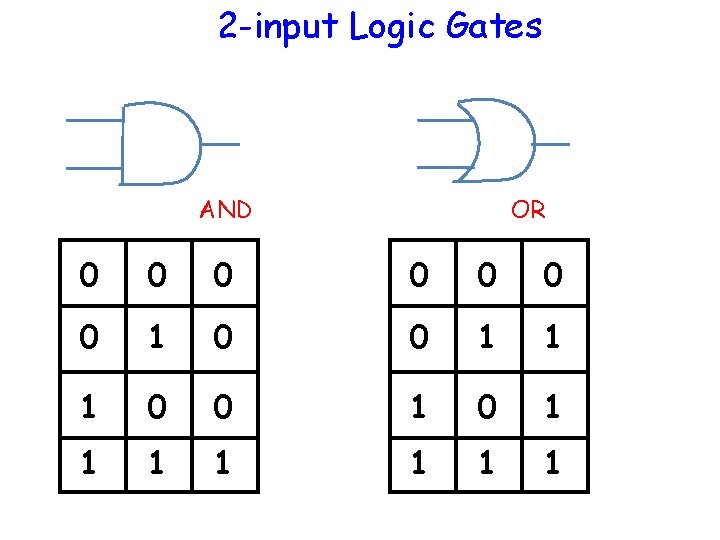
Inverter/NOT gate in out NOT in out 0 1 1 0
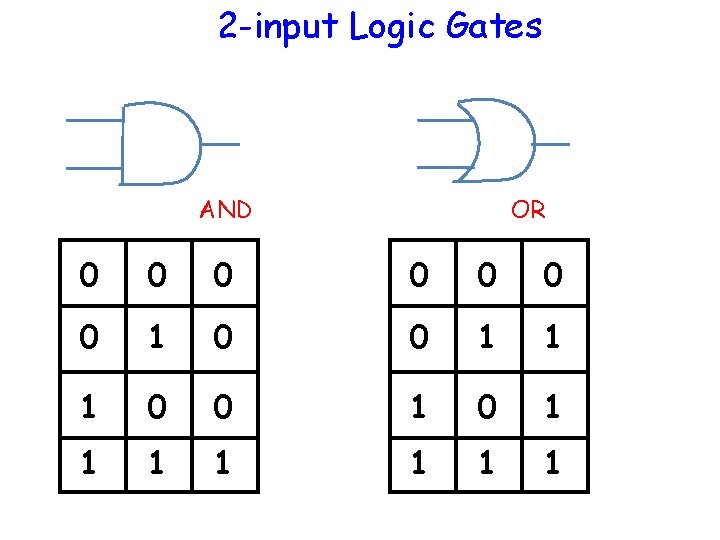
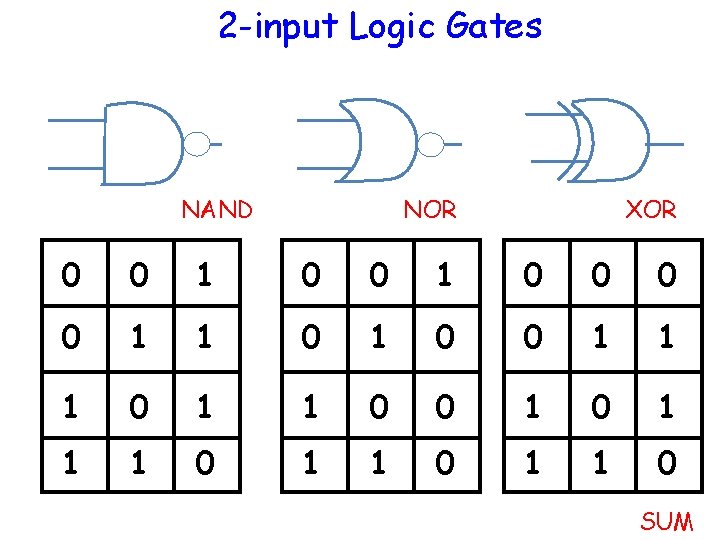
2 -input Logic Gates AND OR 0 0 0 0 1 1 1 0 0 1 1 1 1
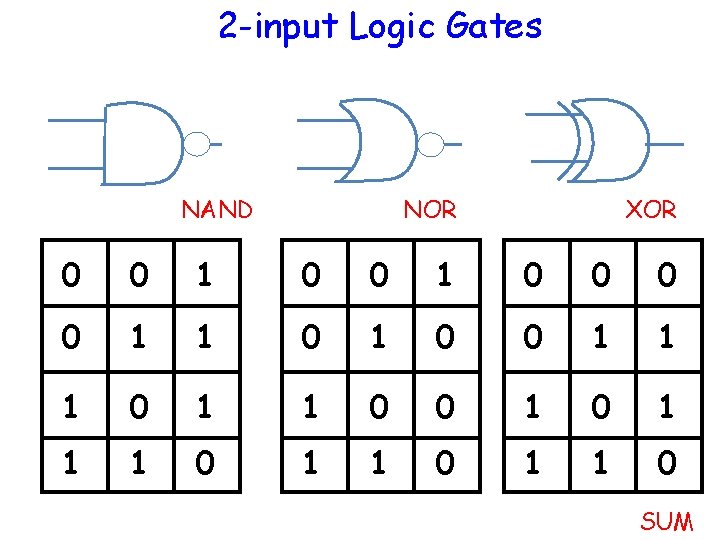
2 -input Logic Gates NAND NOR XOR 0 0 1 1 0 0 1 1 1 0 1 1 0 SUM
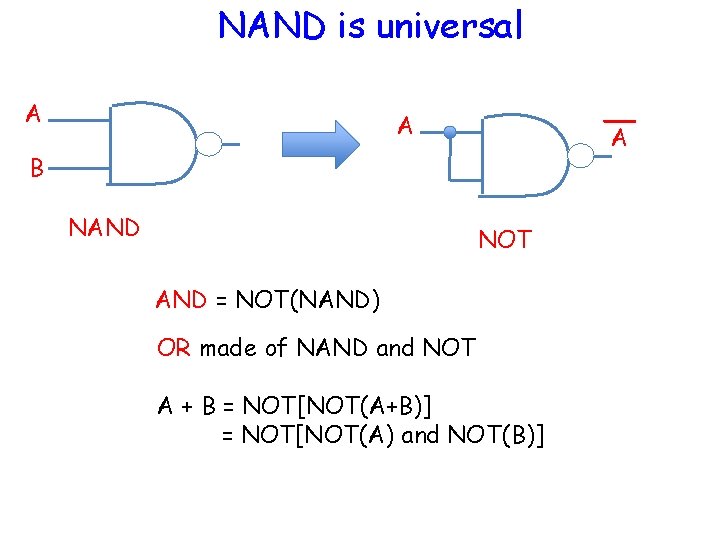
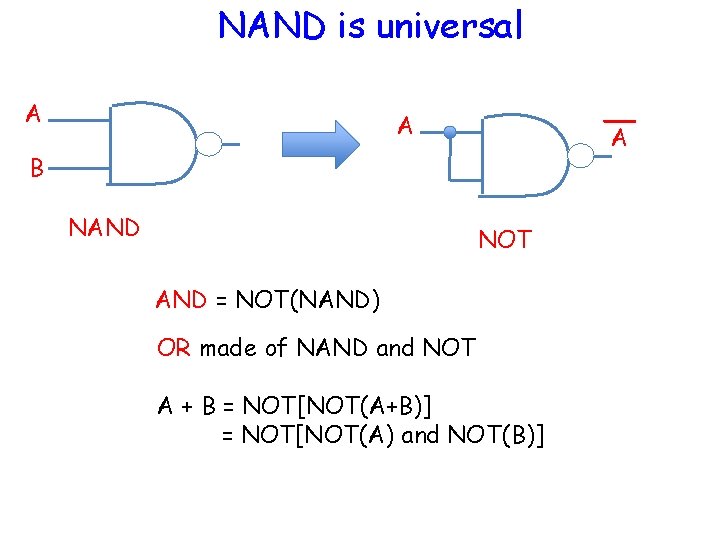
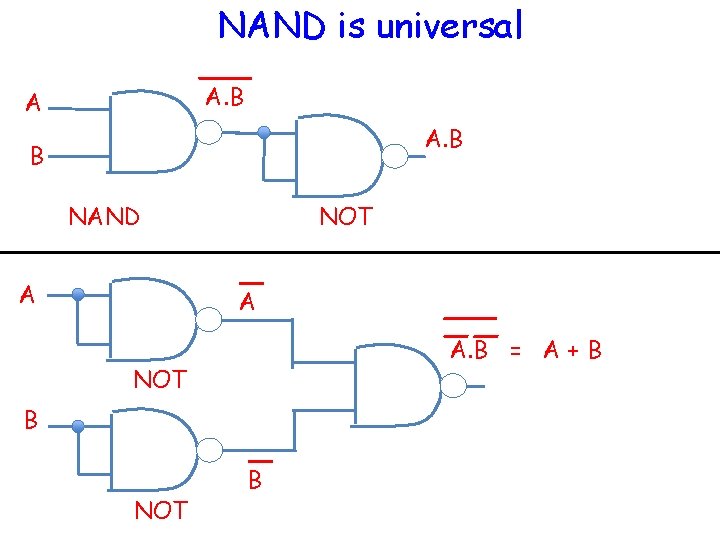
NAND is universal A A A B NAND NOT AND = NOT(NAND) OR made of NAND and NOT A + B = NOT[NOT(A+B)] = NOT[NOT(A) and NOT(B)]
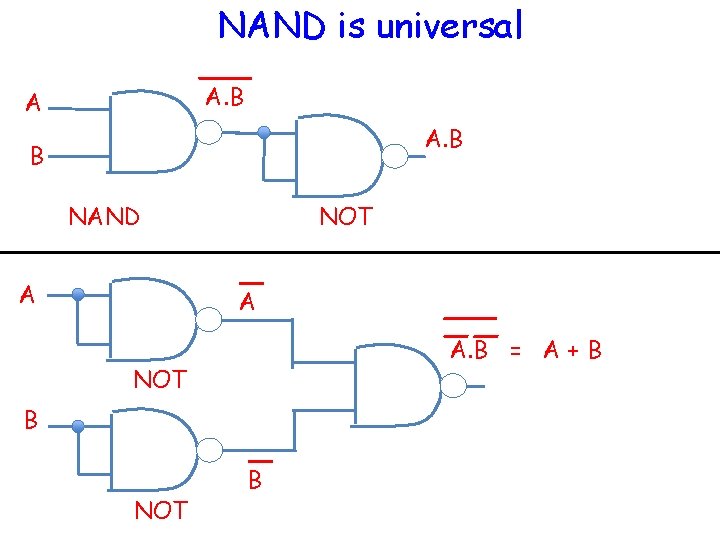
NAND is universal A. B A A. B B NAND A NOT A A. B = A + B NOT B
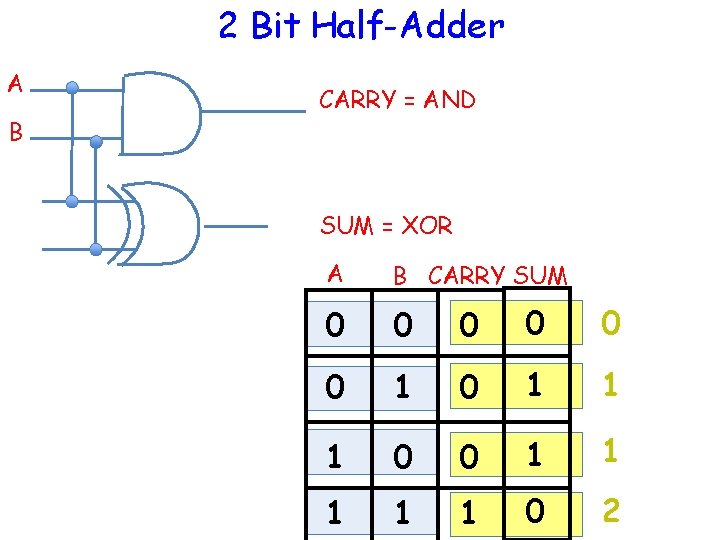
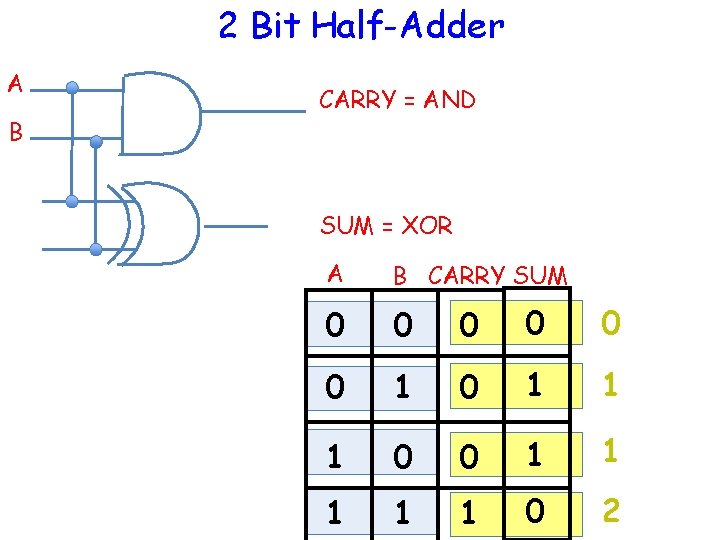
2 Bit Half-Adder A B CARRY = AND SUM = XOR A B CARRY SUM 0 0 0 1 0 1 1 1 0 2
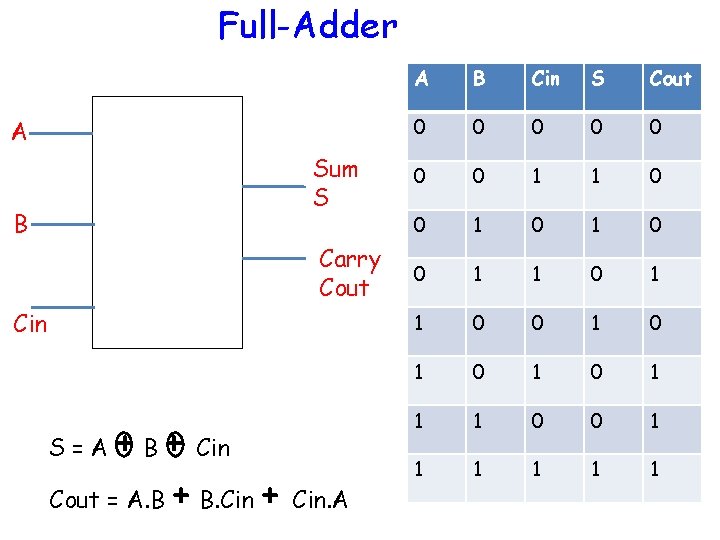
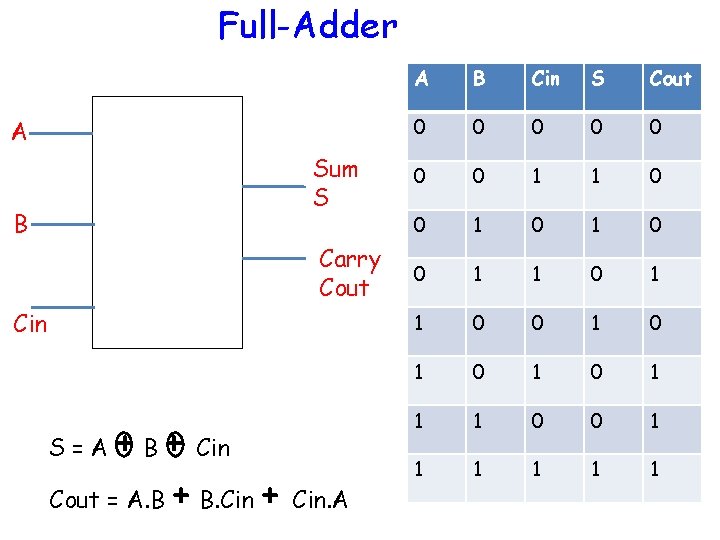
Full-Adder A Sum S B Carry Cout Cin + B + Cin Cout = A. B + B. Cin + Cin. A S=A A B Cin S Cout 0 0 0 0 1 1 0 0 1 0 1 1 1 0 0 1 1 1
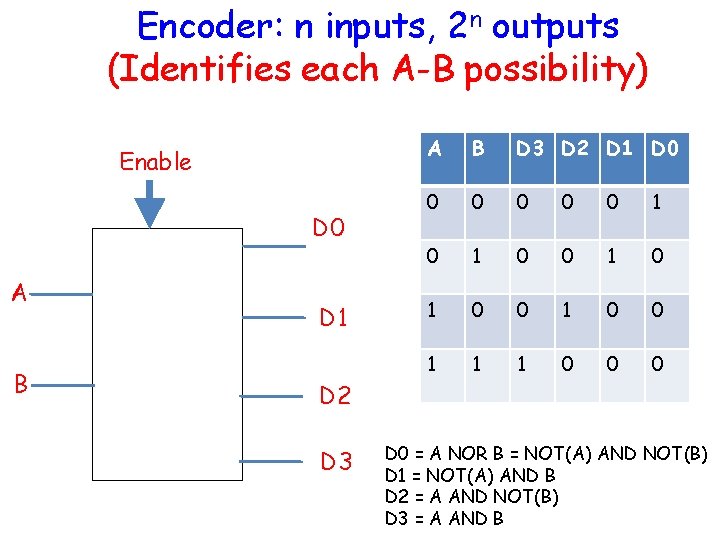
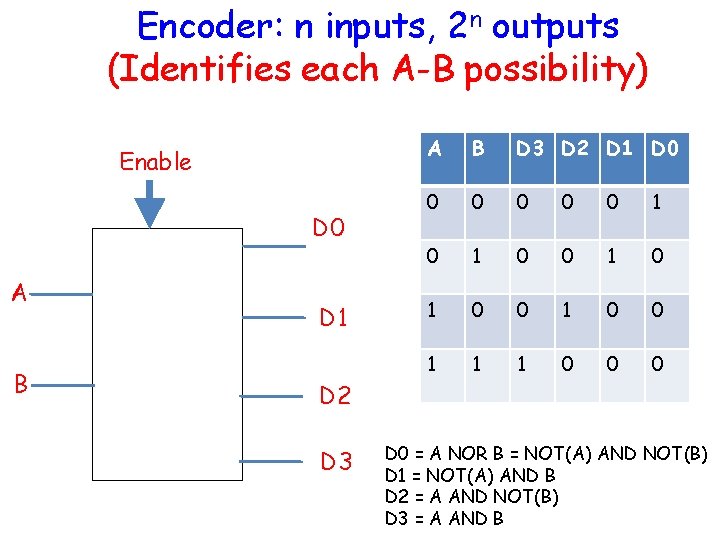
Encoder: n inputs, 2 n outputs (Identifies each A-B possibility) Enable D 0 A B D 1 A B D 3 D 2 D 1 D 0 0 0 1 0 1 0 0 1 1 1 0 0 0 D 2 D 3 D 0 = A NOR B = NOT(A) AND NOT(B) D 1 = NOT(A) AND B D 2 = A AND NOT(B) D 3 = A AND B
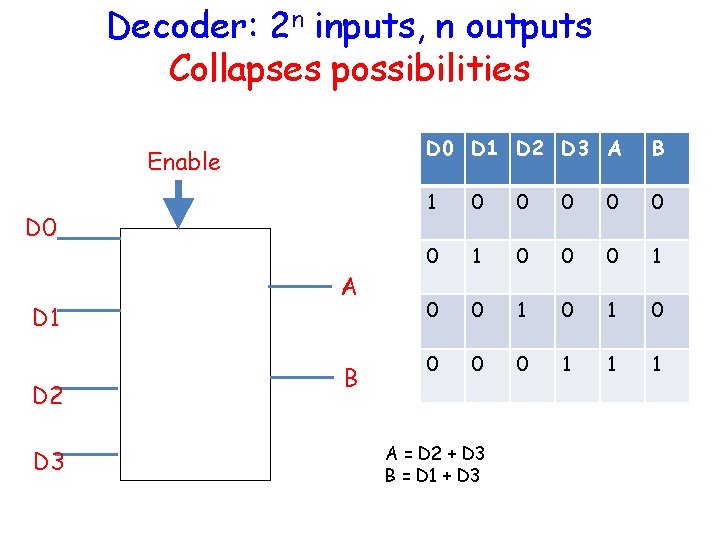
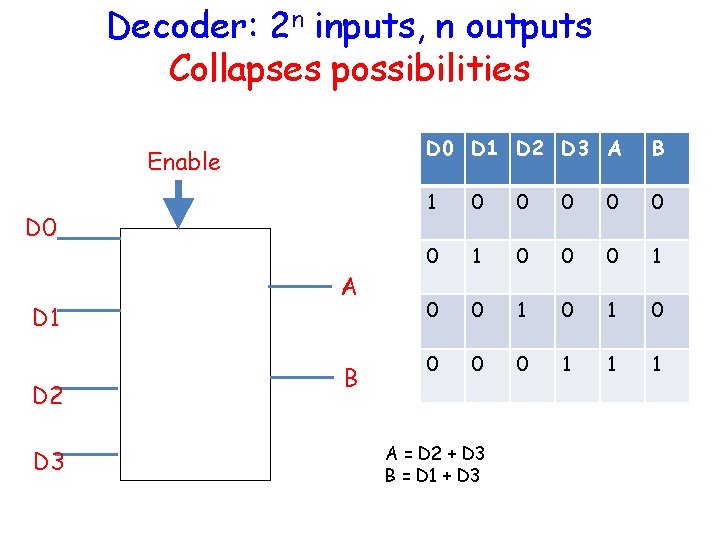
Decoder: 2 n inputs, n outputs Collapses possibilities Enable D 0 D 1 D 2 D 3 A B 1 0 0 0 1 0 1 0 0 1 1 1 A = D 2 + D 3 B = D 1 + D 3
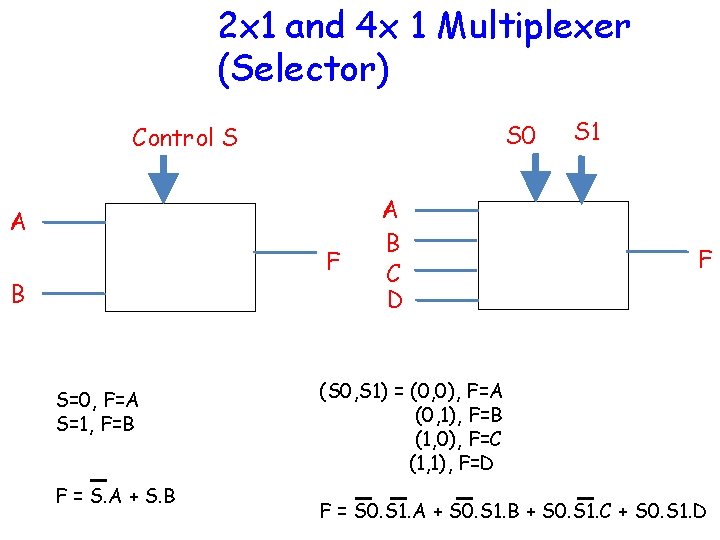
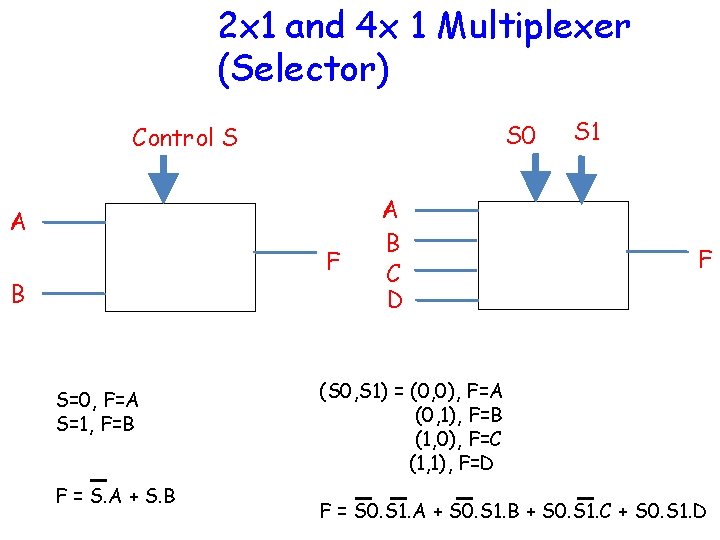
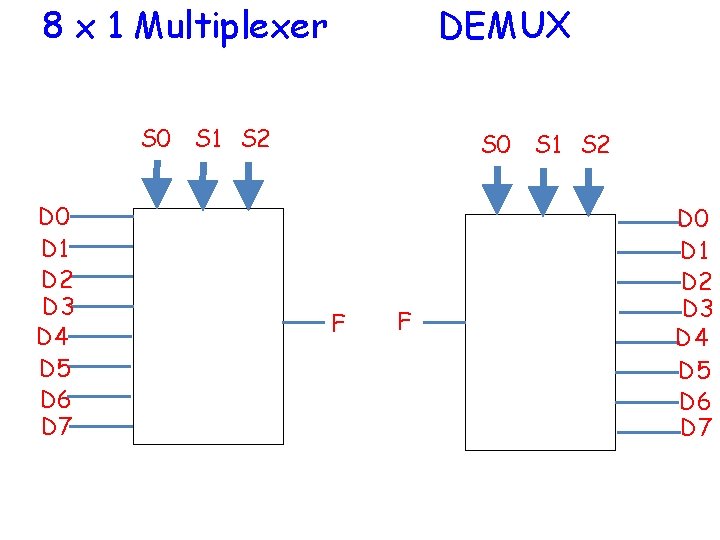
2 x 1 and 4 x 1 Multiplexer (Selector) S 0 Control S A F B S=0, F=A S=1, F=B F = S. A + S. B A B C D S 1 F (S 0, S 1) = (0, 0), F=A (0, 1), F=B (1, 0), F=C (1, 1), F=D F = S 0. S 1. A + S 0. S 1. B + S 0. S 1. C + S 0. S 1. D
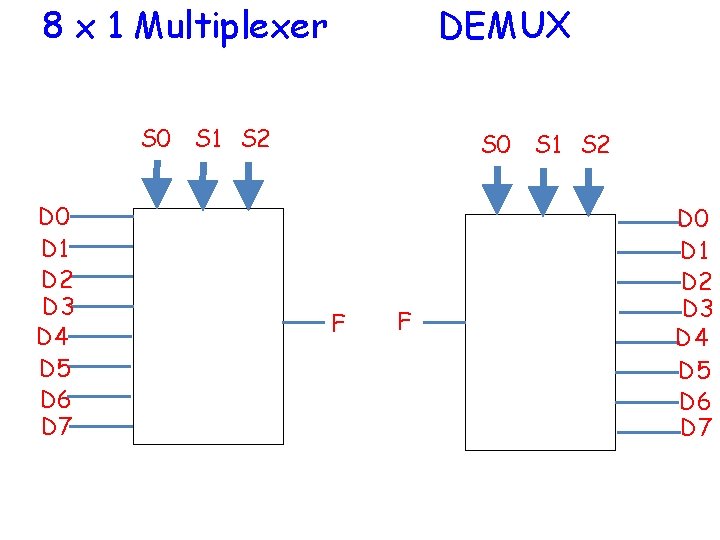
8 x 1 Multiplexer DEMUX S 0 S 1 S 2 D 0 D 1 D 2 D 3 D 4 D 5 D 6 D 7 S 0 S 1 S 2 F F D 0 D 1 D 2 D 3 D 4 D 5 D 6 D 7
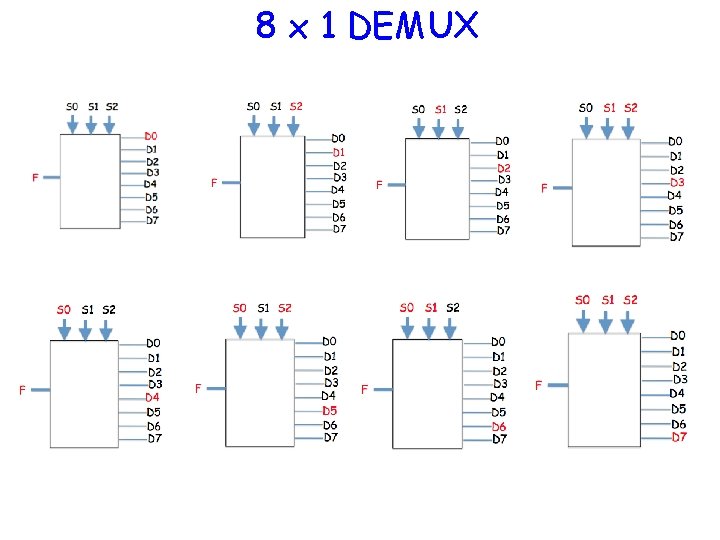
8 x 1 DEMUX
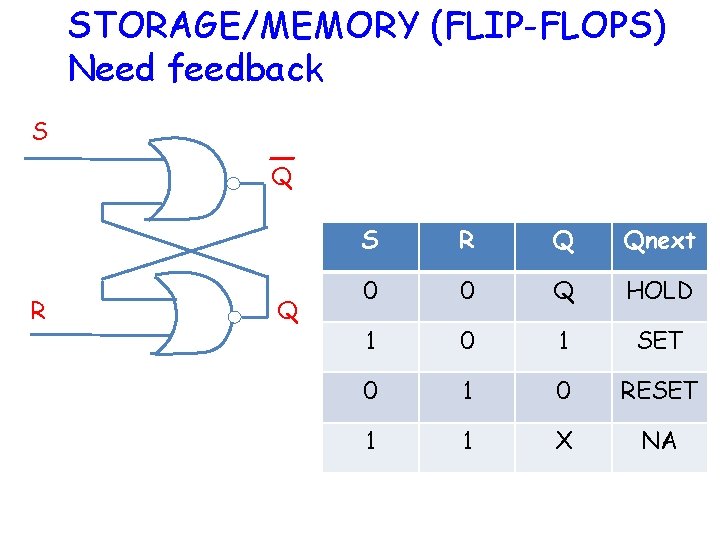
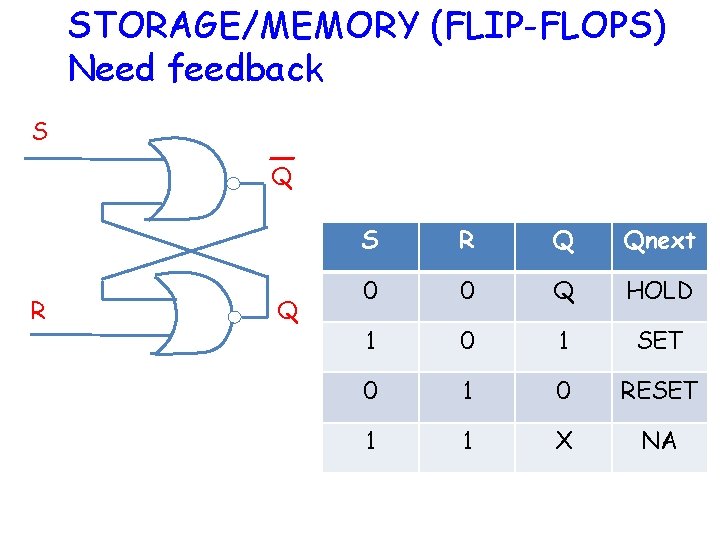
STORAGE/MEMORY (FLIP-FLOPS) Need feedback S Q R Q S R Q Qnext 0 0 Q HOLD 1 0 1 SET 0 1 0 RESET 1 1 X NA
How do we realize these gates?
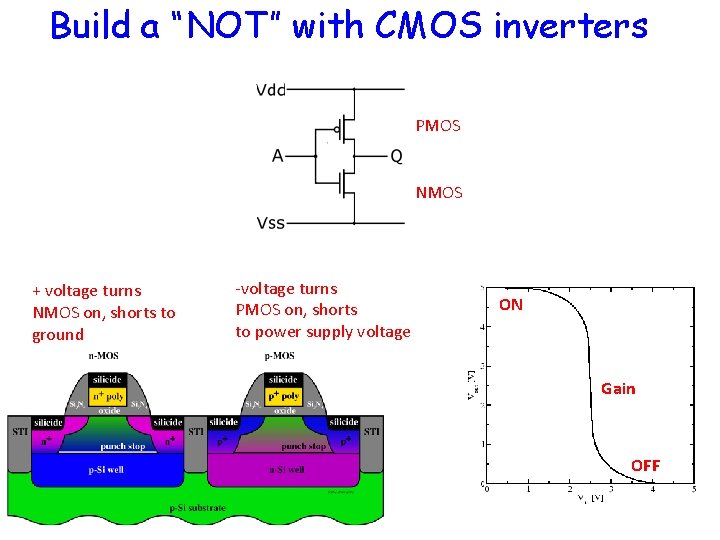
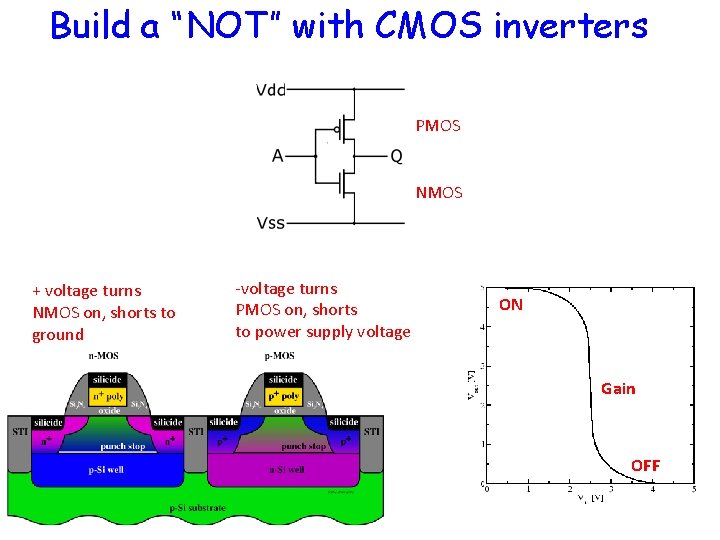
Build a “NOT” with CMOS inverters PMOS NMOS + voltage turns NMOS on, shorts to ground -voltage turns PMOS on, shorts to power supply voltage ON Gain OFF
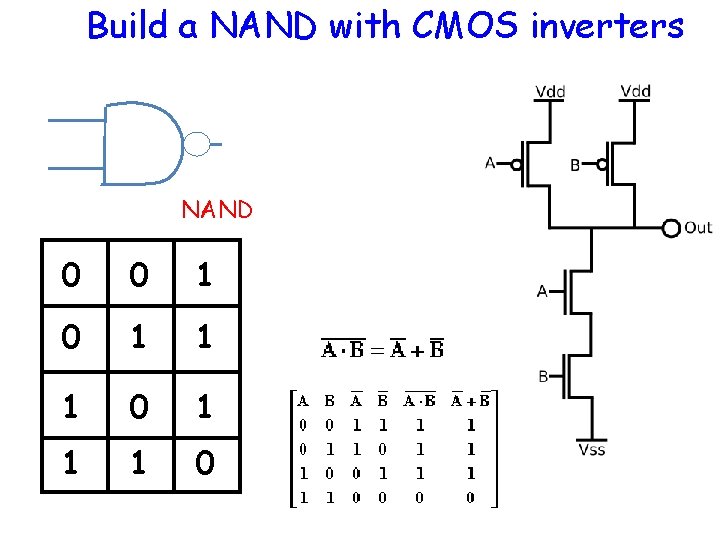
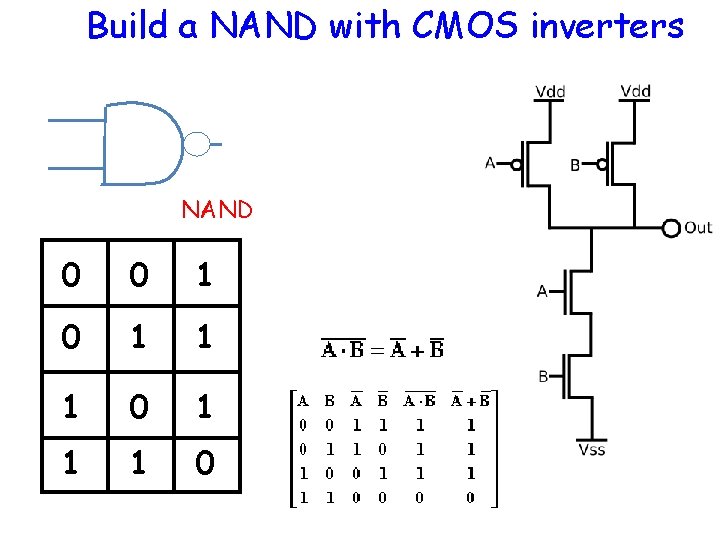
Build a NAND with CMOS inverters NAND 0 0 1 1 1 0
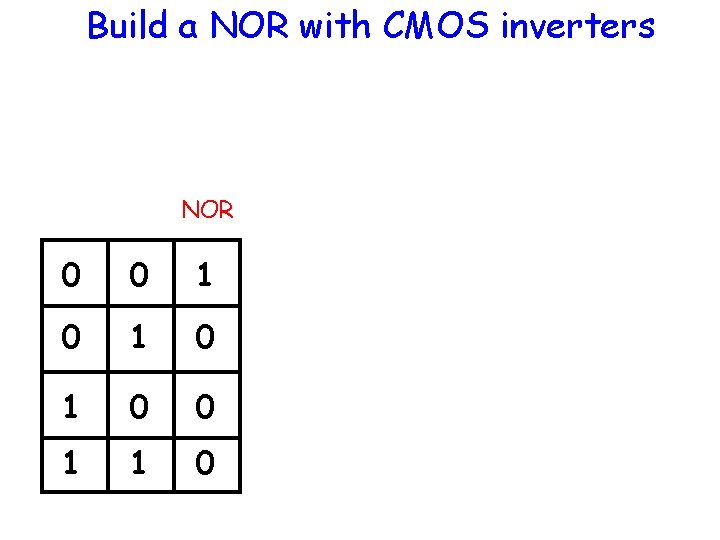
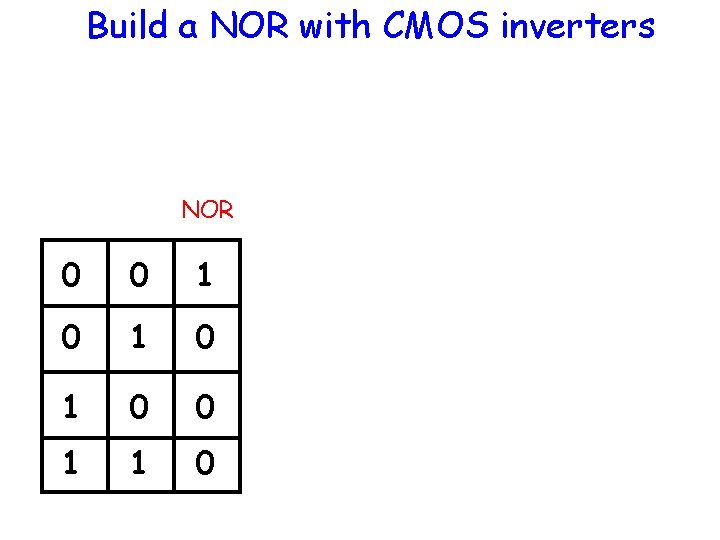
Build a NOR with CMOS inverters NOR 0 0 1 0 1 0 0 1 1 0
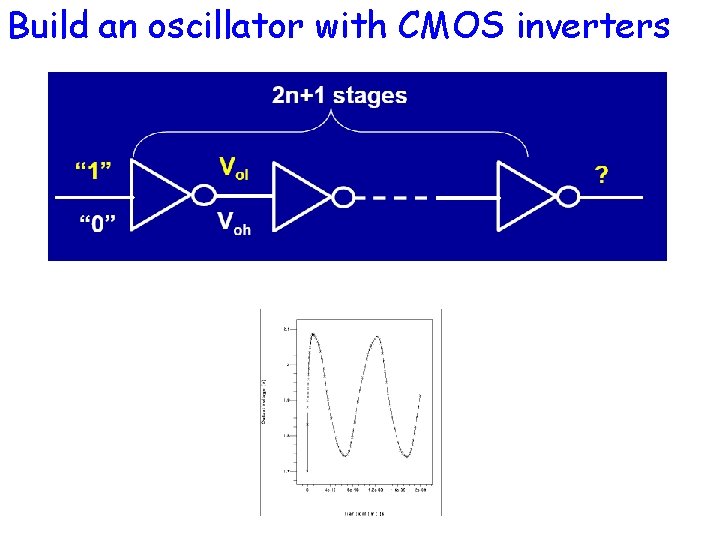
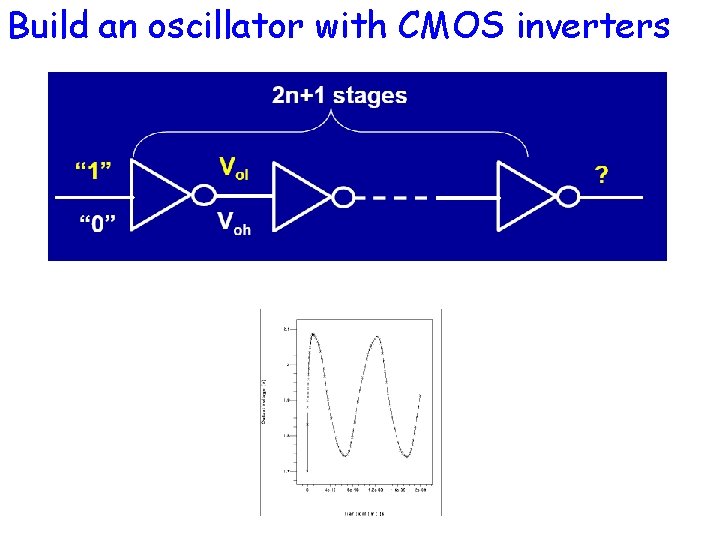
Build an oscillator with CMOS inverters
Build memory with CMOS (DRAM, SRAM, Flash)
Energetics of Computation
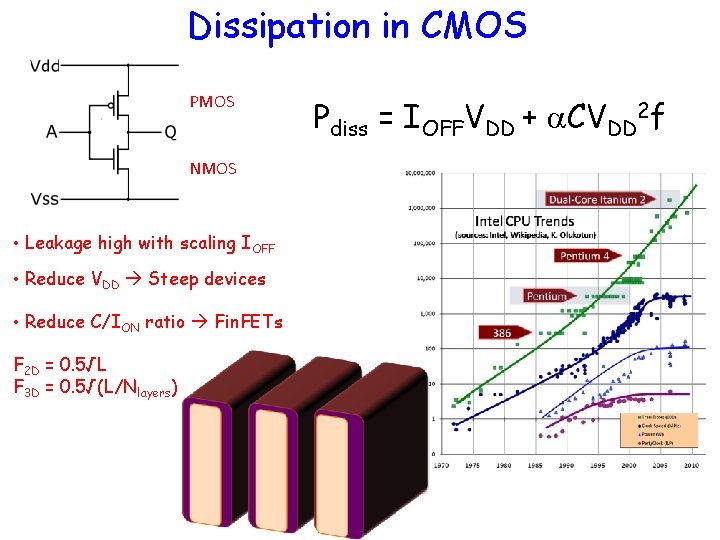
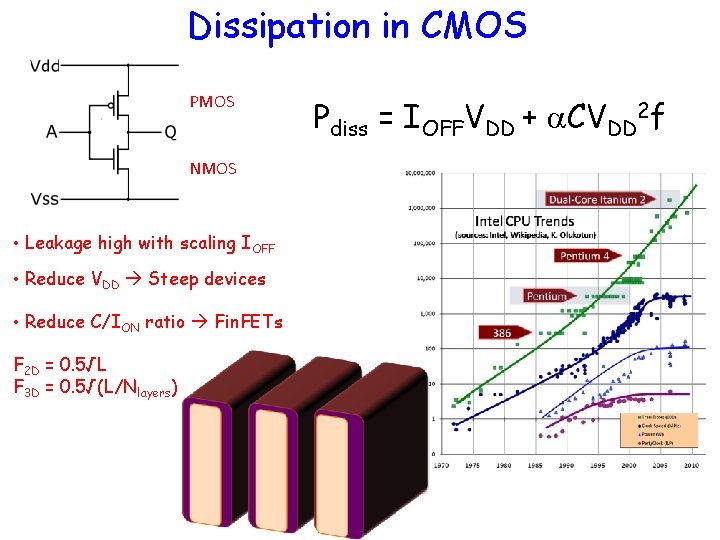
Dissipation in CMOS PMOS NMOS • Leakage high with scaling IOFF • Reduce VDD Steep devices • Reduce C/ION ratio Fin. FETs F 2 D = 0. 5√L F 3 D = 0. 5√(L/Nlayers) Pdiss = IOFFVDD + a. CVDD 2 f
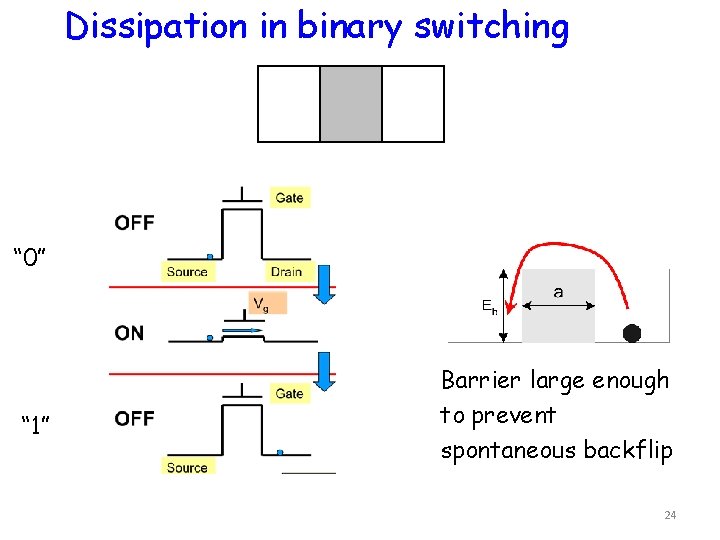
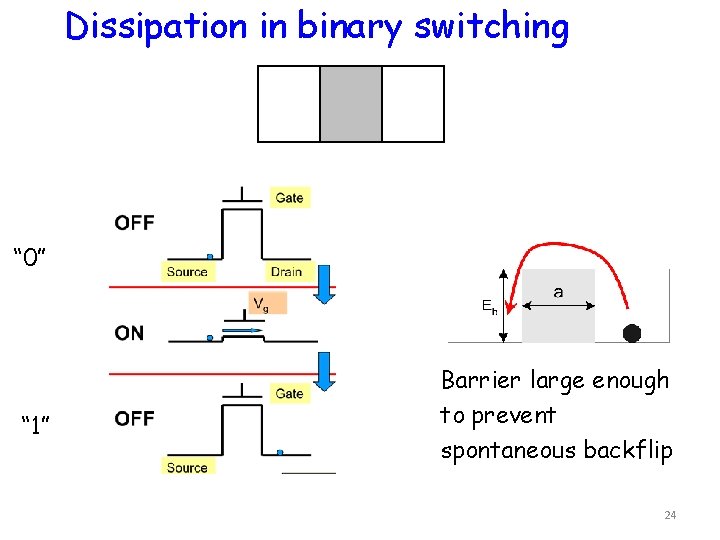
Dissipation in binary switching “ 0” “ 1” Barrier large enough to prevent spontaneous backflip 24
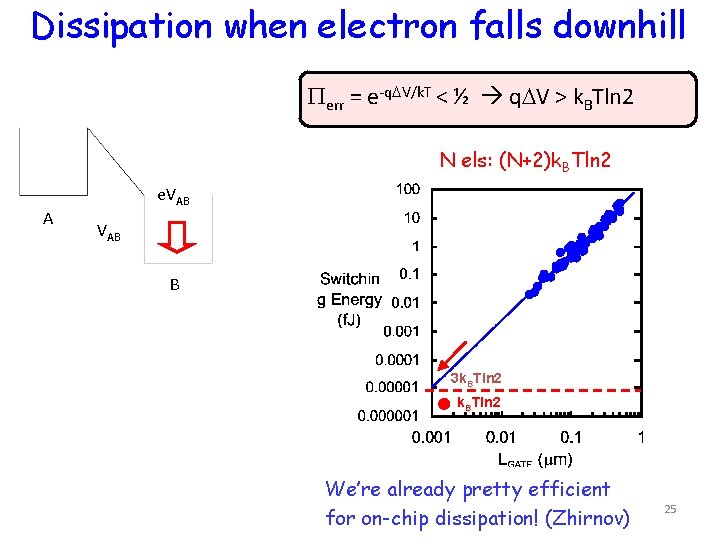
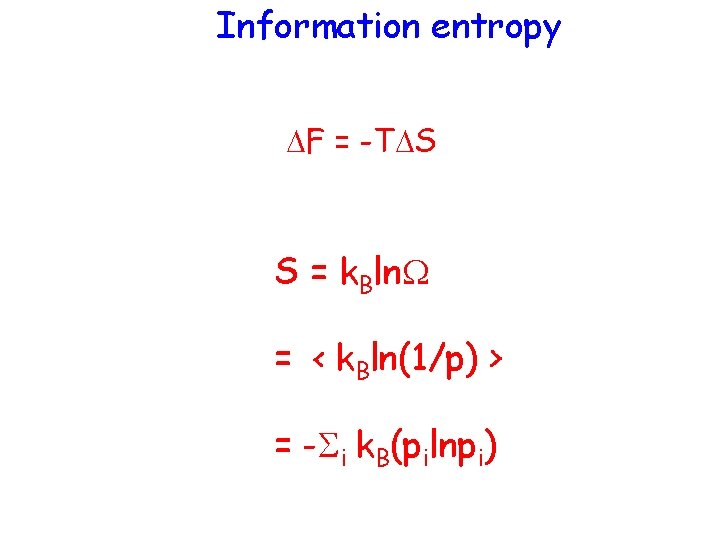
Dissipation when electron falls downhill Perr = e-q. DV/k. T < ½ q. DV > k. BTln 2 N els: (N+2)k. BTln 2 A e. VAB B 3 k. BTln 2 We’re already pretty efficient for on-chip dissipation! (Zhirnov) 25
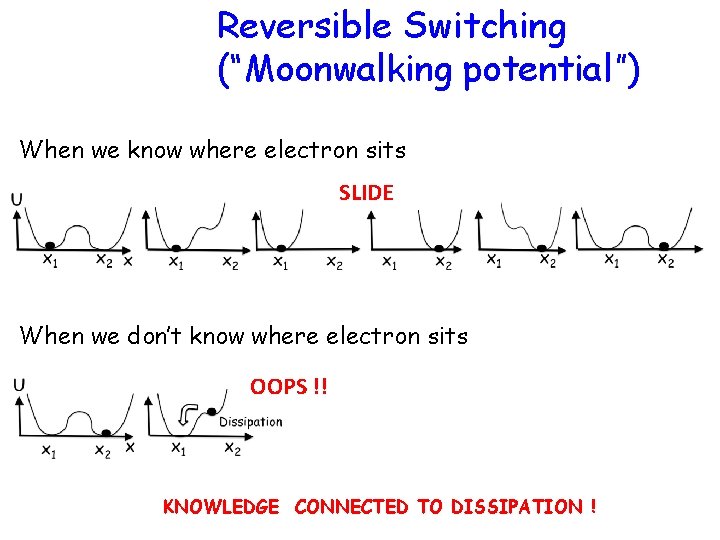
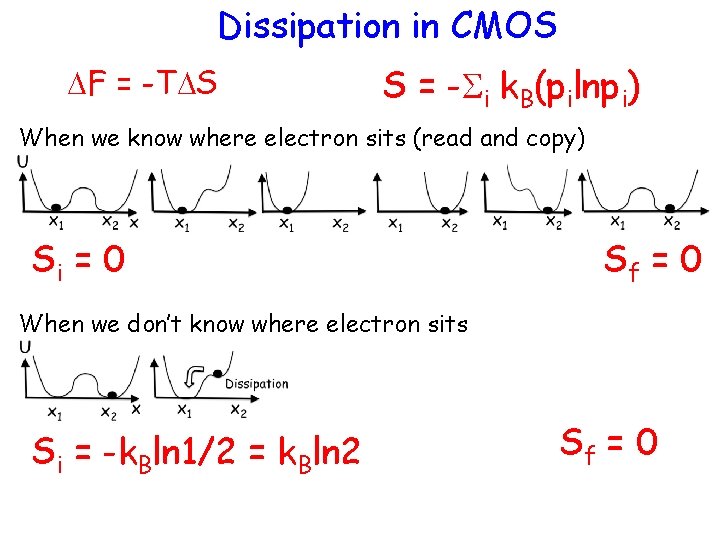
Reversible Switching (“Moonwalking potential”) When we know where electron sits SLIDE When we don’t know where electron sits OOPS !! KNOWLEDGE CONNECTED TO DISSIPATION !
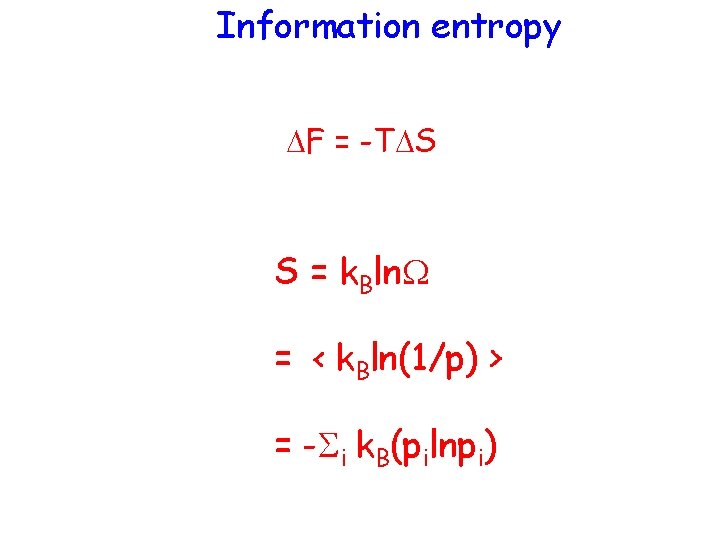
Information entropy DF = -TDS S = k. Bln. W = < k. Bln(1/p) > = -Si k. B(pilnpi)
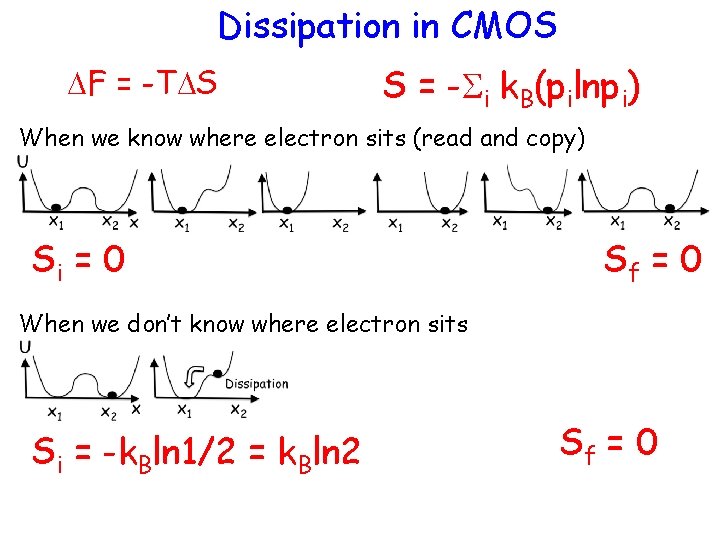
Dissipation in CMOS DF = -TDS S = -Si k. B(pilnpi) When we know where electron sits (read and copy) Si = 0 Sf = 0 When we don’t know where electron sits Si = -k. Bln 1/2 = k. Bln 2 Sf = 0
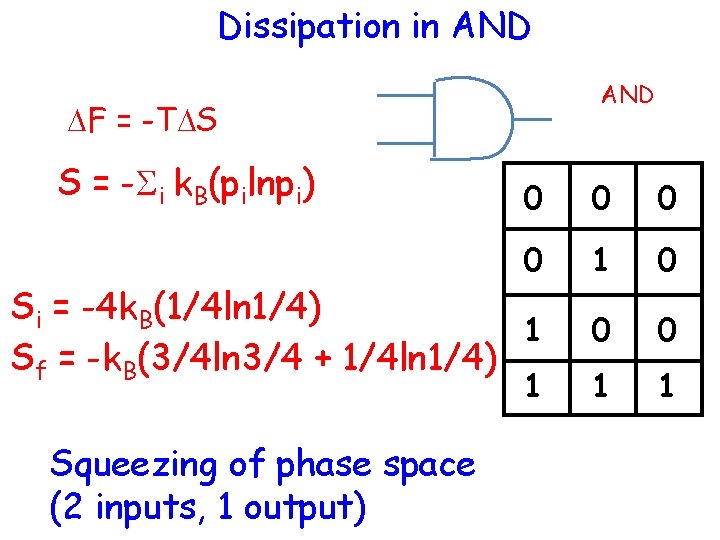
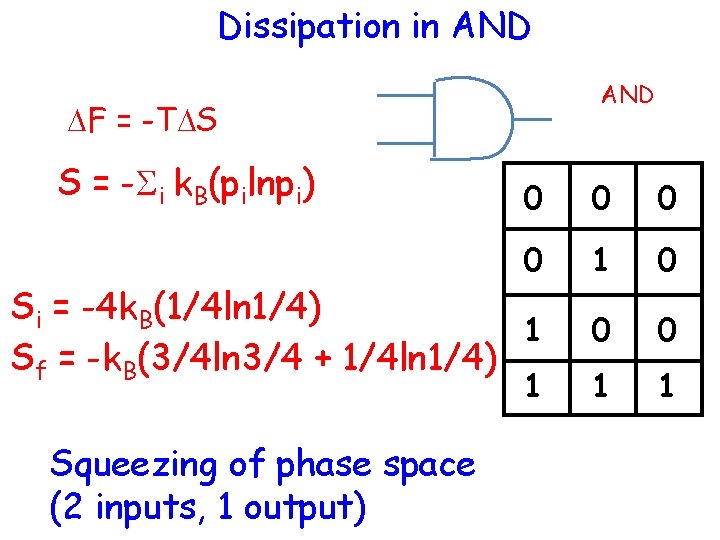
Dissipation in AND DF = -TDS S = -Si k. B(pilnpi) 0 0 1 0 0 0 1 1 Si = -4 k. B(1/4 ln 1/4) 1 Sf = -k. B(3/4 ln 3/4 + 1/4 ln 1/4) 1 Squeezing of phase space (2 inputs, 1 output)
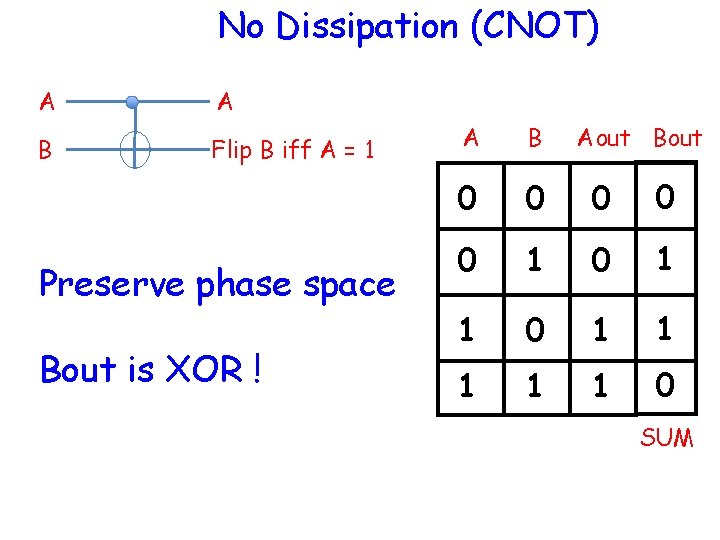
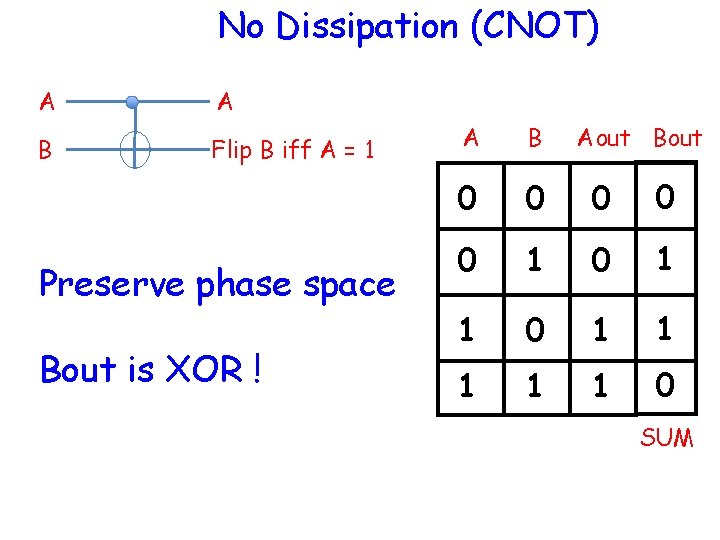
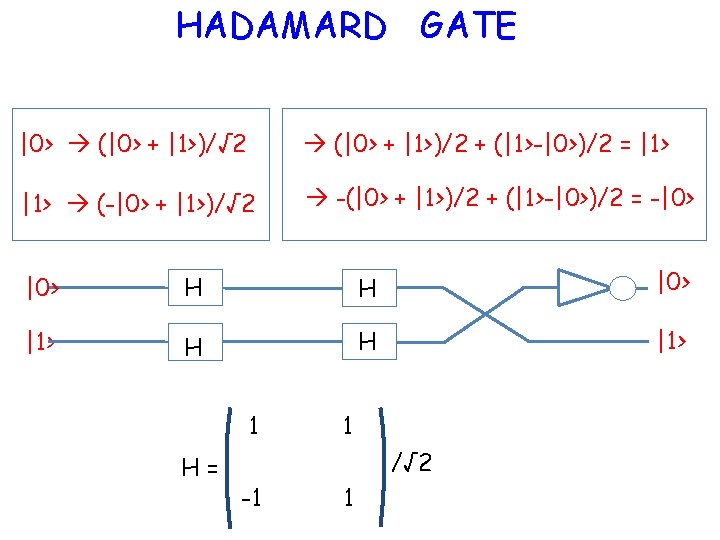
No Dissipation (CNOT) A A B Flip B iff A = 1 Preserve phase space Bout is XOR ! A B 0 0 0 1 1 1 0 Aout Bout SUM
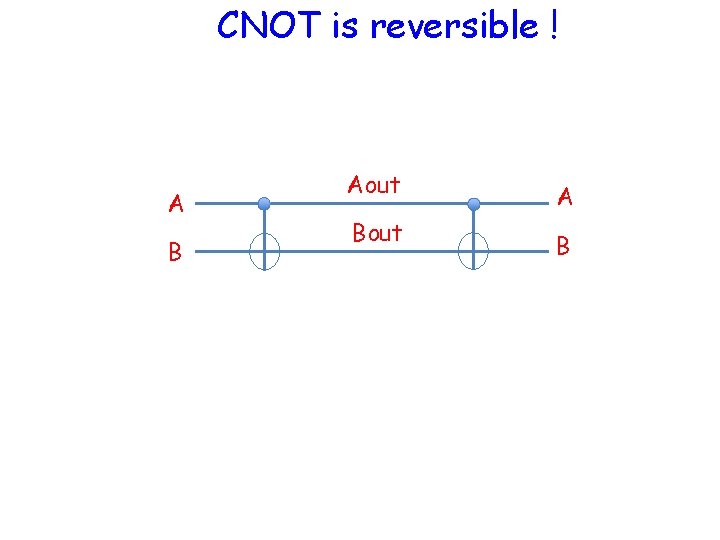
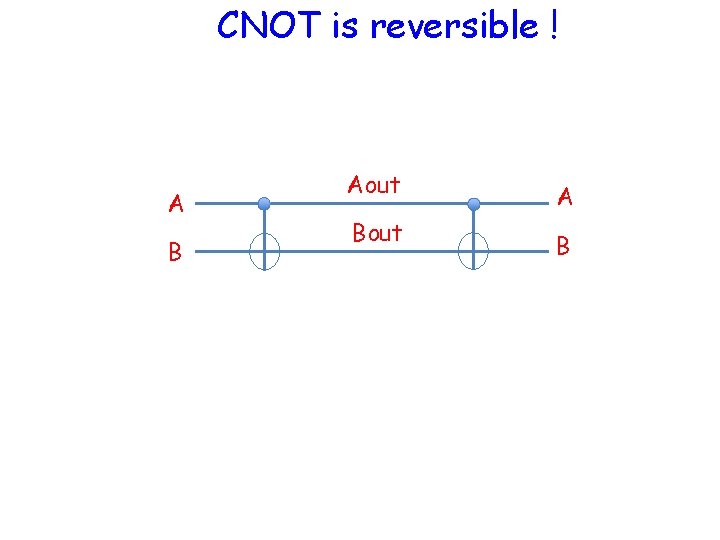
CNOT is reversible ! A B Aout Bout A B
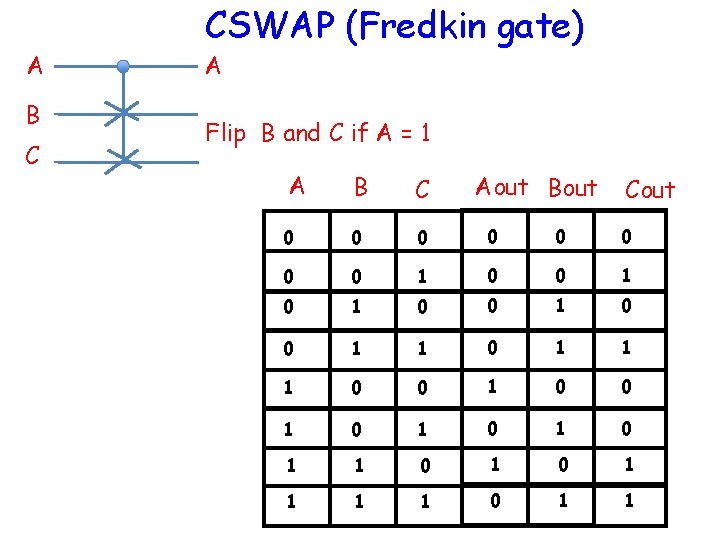
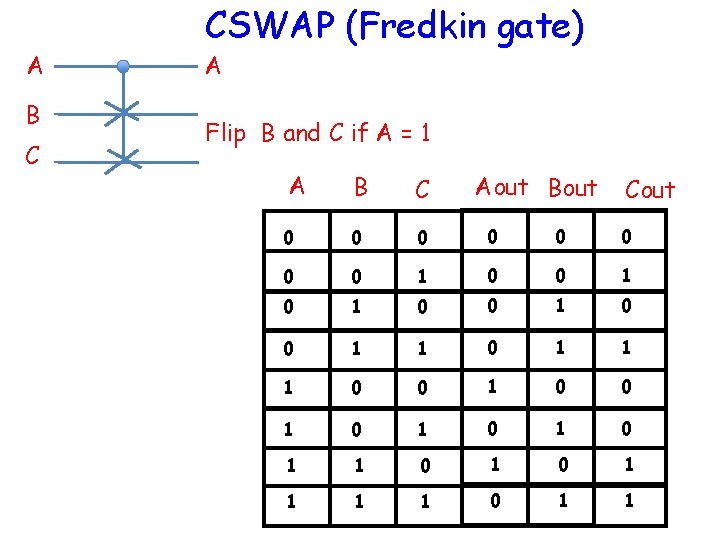
A B C CSWAP (Fredkin gate) A Flip B and C if A = 1 A B C Aout Bout 0 0 0 0 1 0 0 1 1 1 0 0 1 0 1 1 0 1 1 Cout
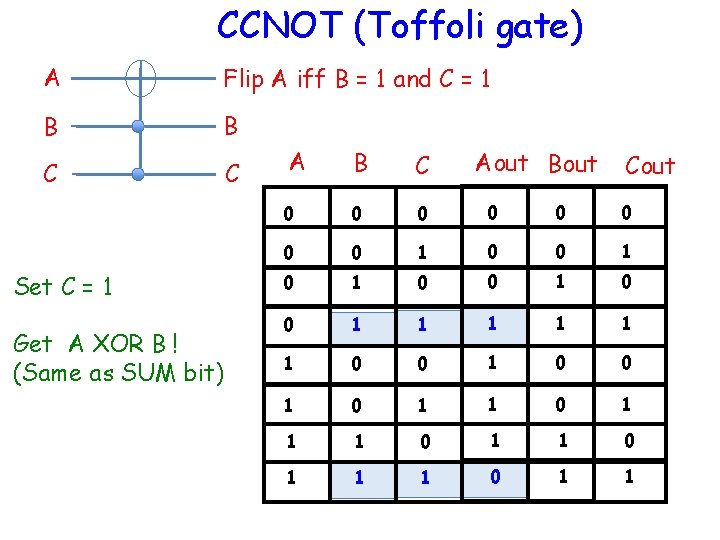
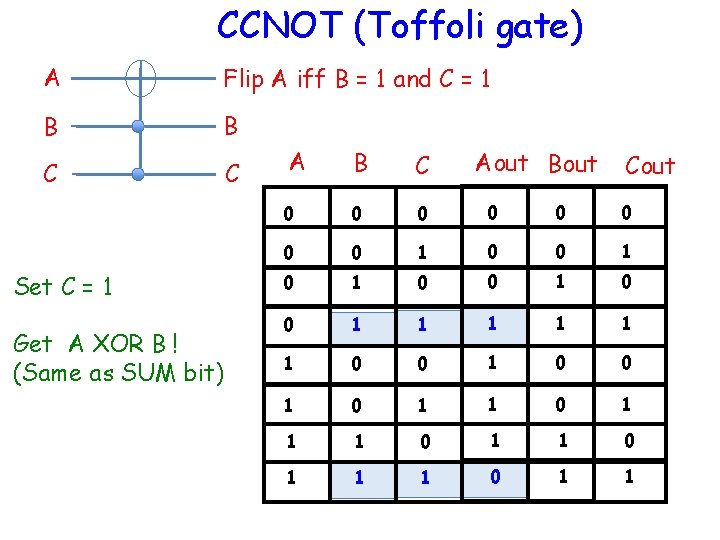
CCNOT (Toffoli gate) A Flip A iff B = 1 and C = 1 B B C C Set C = 1 Get A XOR B ! (Same as SUM bit) A B C Aout Bout 0 0 0 0 1 0 0 1 1 1 0 0 1 0 1 1 1 0 1 1 Cout
Quantum Computation
PRIME FACTORIZATION Use Superposition + Entanglement + reversible gates for one-shot computation • Shor’s Algorithm • Grover’s Algorithm • Kane’s Nuclear spin QC
What is Entanglement ?
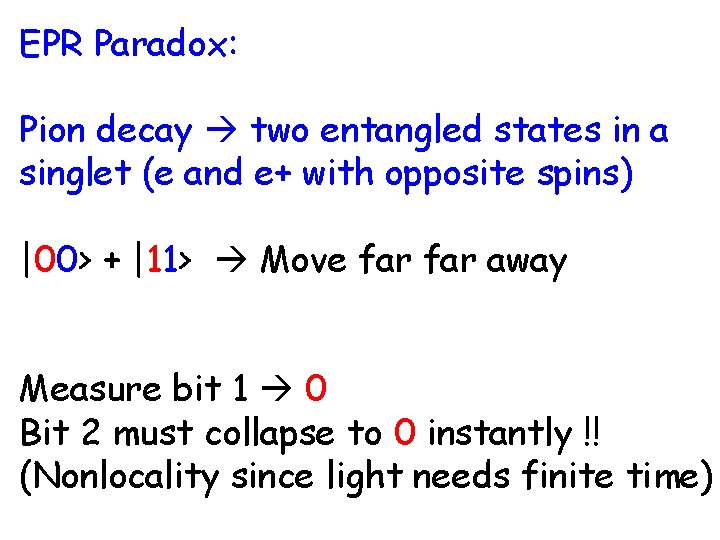
EPR Paradox: Pion decay two entangled states in a singlet (e and e+ with opposite spins) |00> + |11> Move far away Measure bit 1 0 Bit 2 must collapse to 0 instantly !! (Nonlocality since light needs finite time)
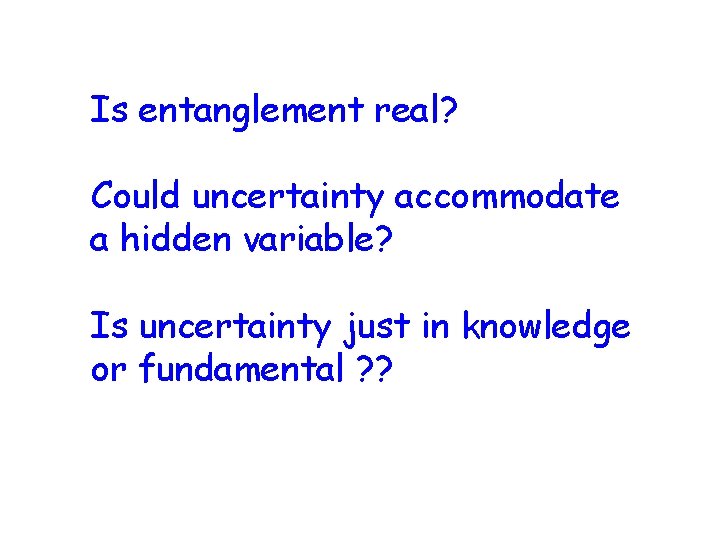
Is entanglement real? Could uncertainty accommodate a hidden variable? Is uncertainty just in knowledge or fundamental ? ?
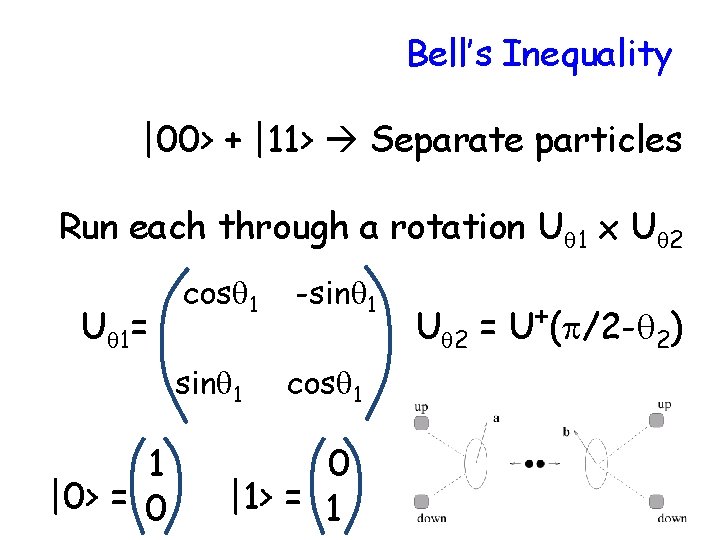
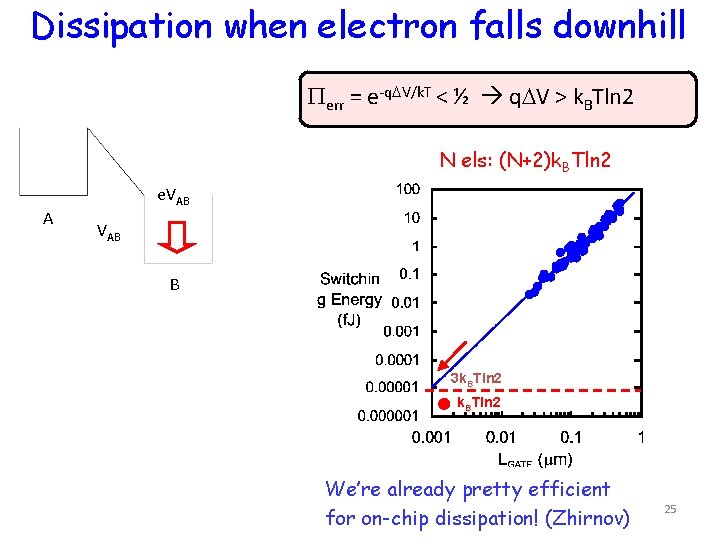
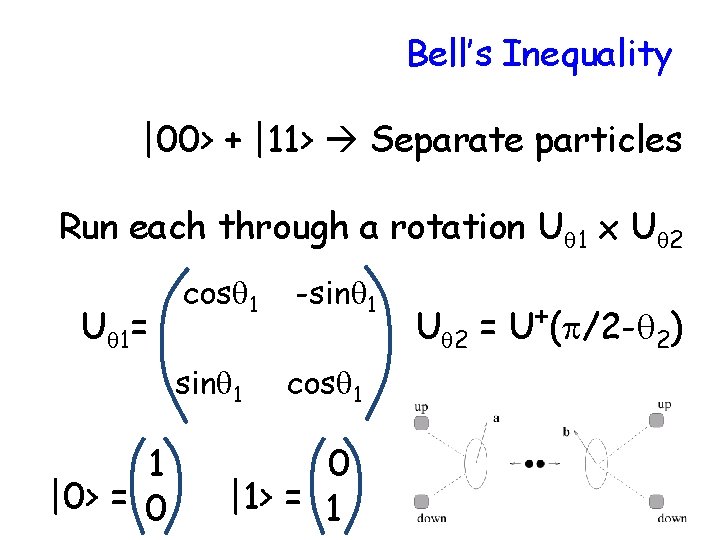
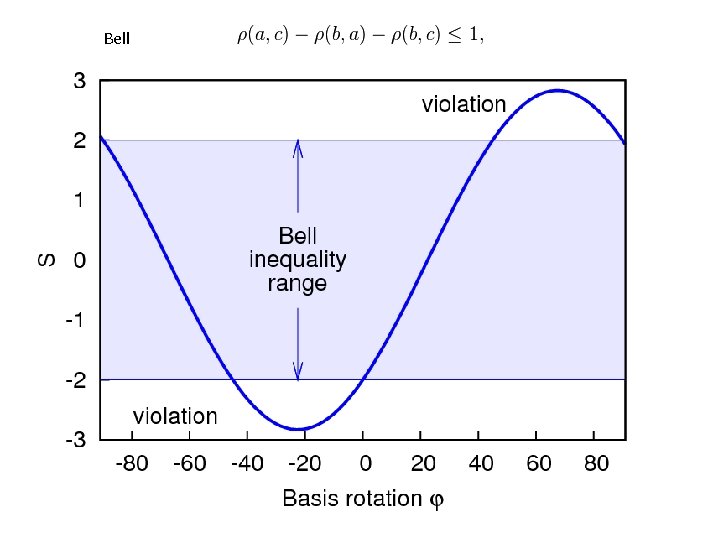
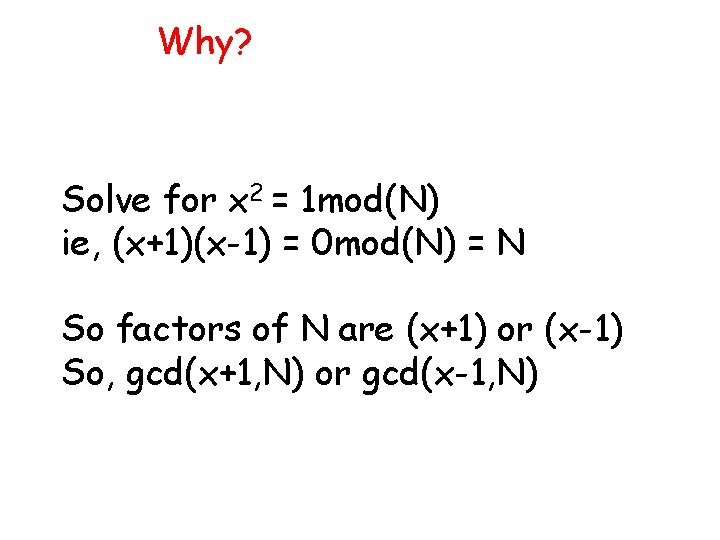
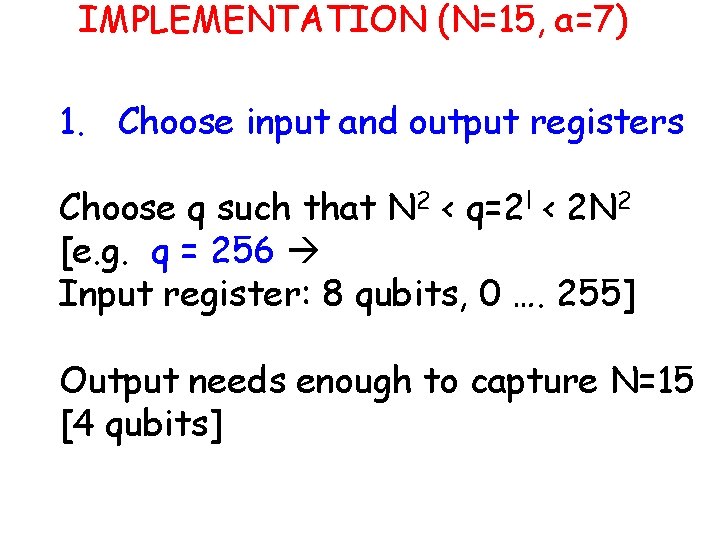
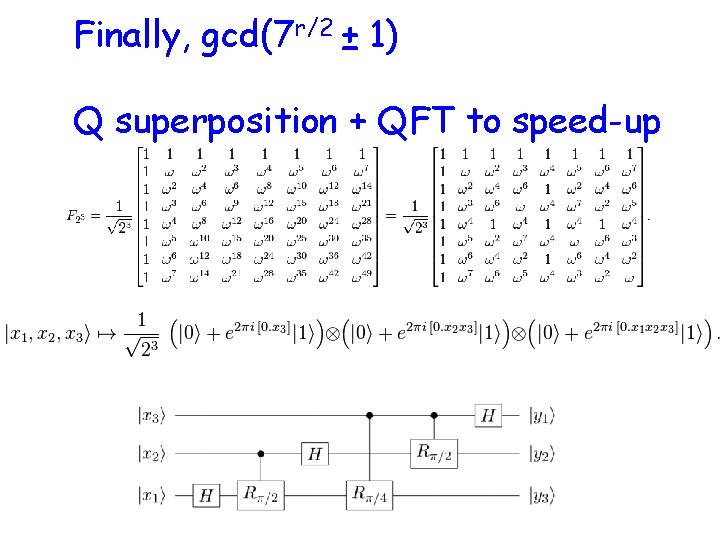
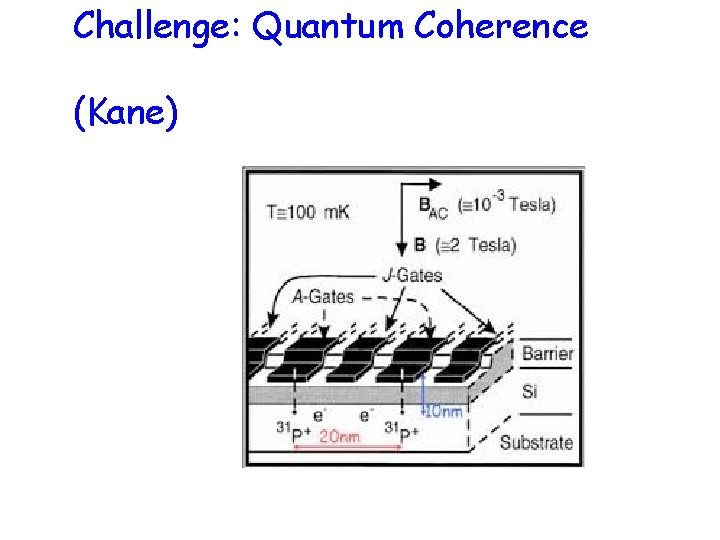
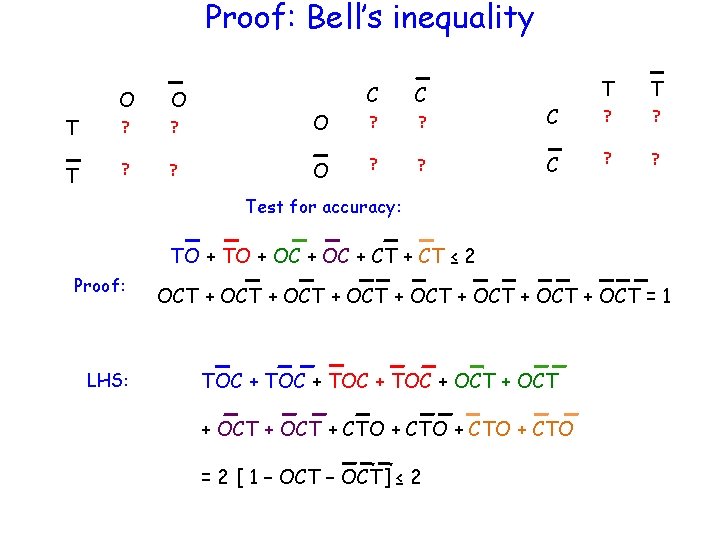
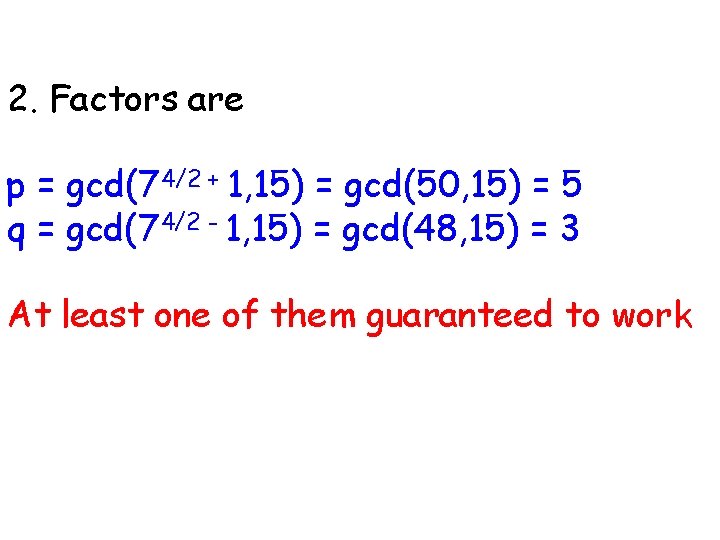
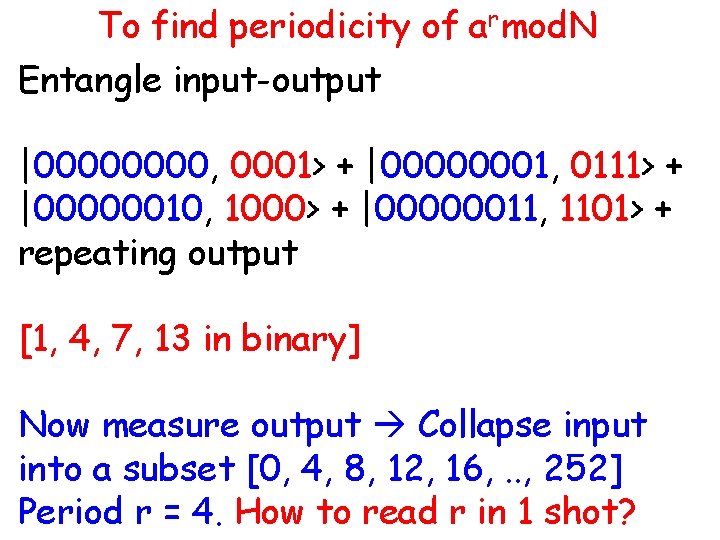
Bell’s Inequality |00> + |11> Separate particles Run each through a rotation Uq 1 x Uq 2 Uq 1= 1 |0> = 0 cosq 1 -sinq 1 cosq 1 0 |1> = 1 Uq 2 = U+(p/2 -q 2)
![Result sinq 1 q 2 00 11 Coincidence cosq 1 q 2 Result -sin(q 1 -q 2) [|00> + |11>] Coincidence + cos(q 1 -q 2)](https://slidetodoc.com/presentation_image/ec64489b59d45f3eb52cd35872119f2e/image-40.jpg)
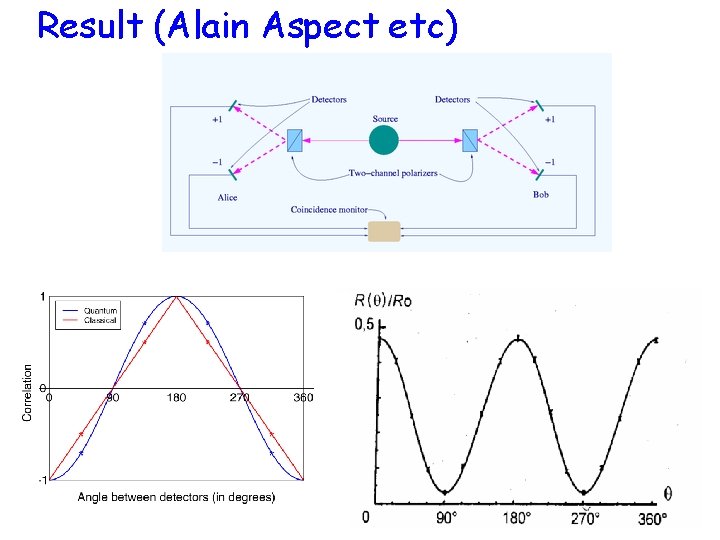
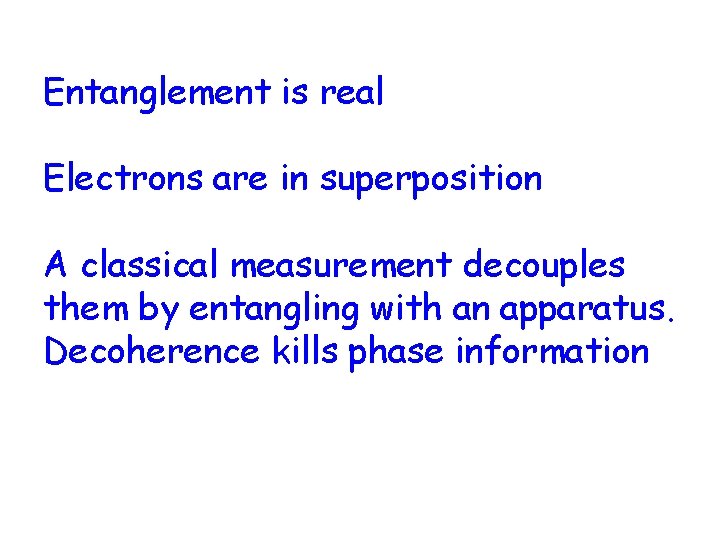
Result -sin(q 1 -q 2) [|00> + |11>] Coincidence + cos(q 1 -q 2) [ |10> - |01>] Non-coinc P(AC = 1) = sin 2(q 1 -q 2) P(AC = -1) = cos 2(q 1 -q 2) P(AC = -1) – P(AC = 1) = P(01) + P(10) – P(00) – P(11) = correlation = cos[2(q 1 -q 2)]
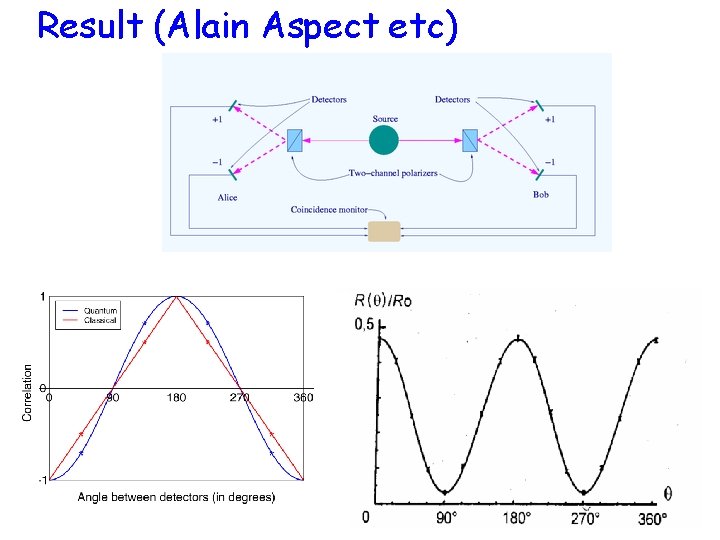
Result (Alain Aspect etc)
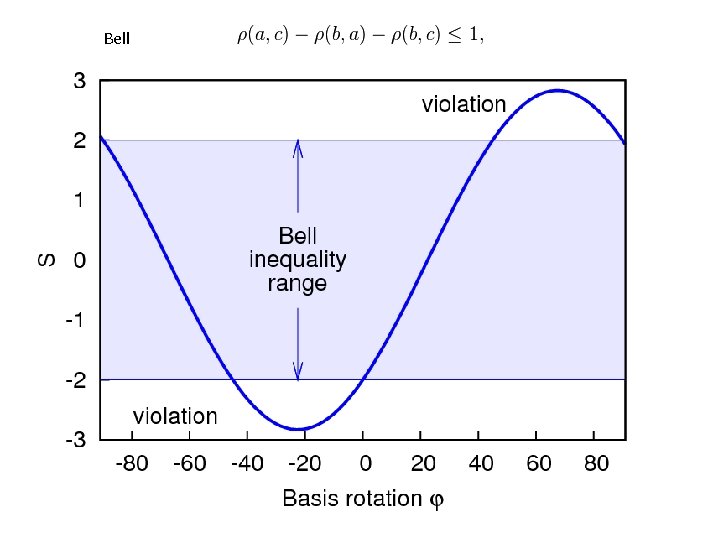
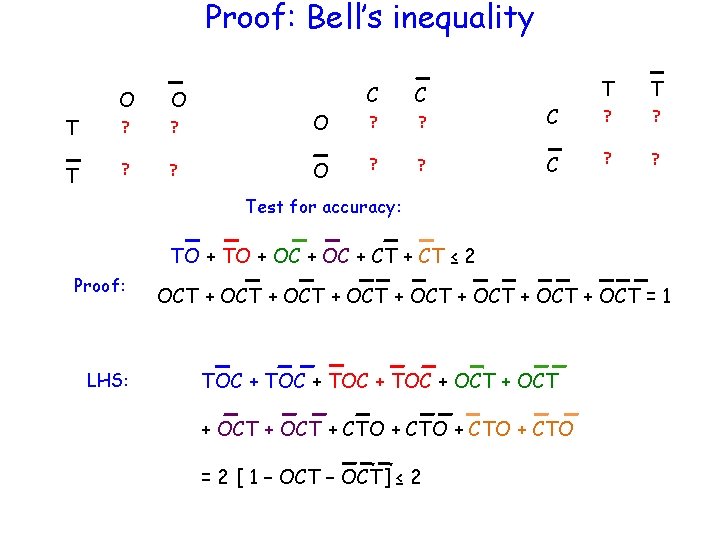
Bell
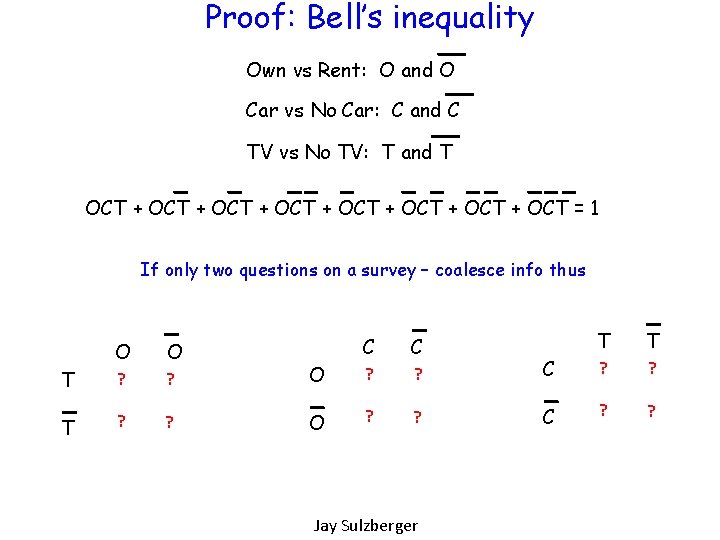
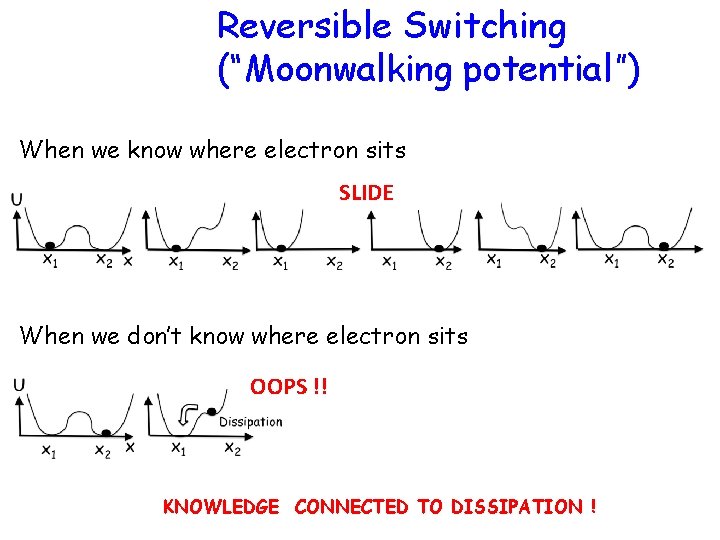
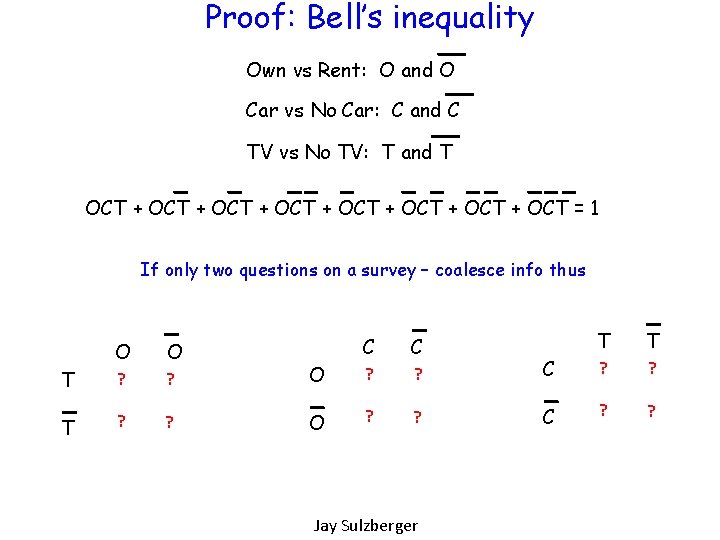
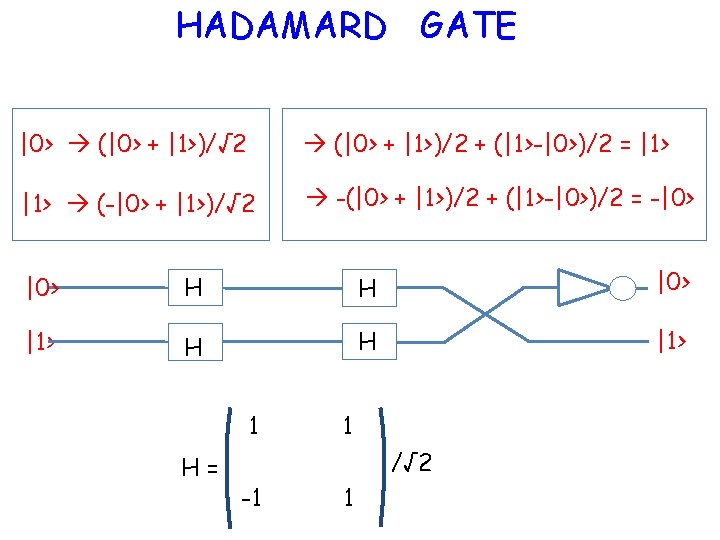
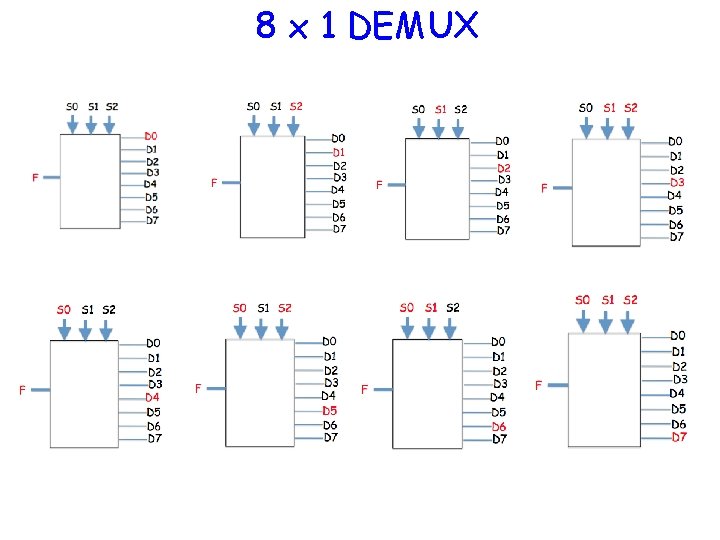
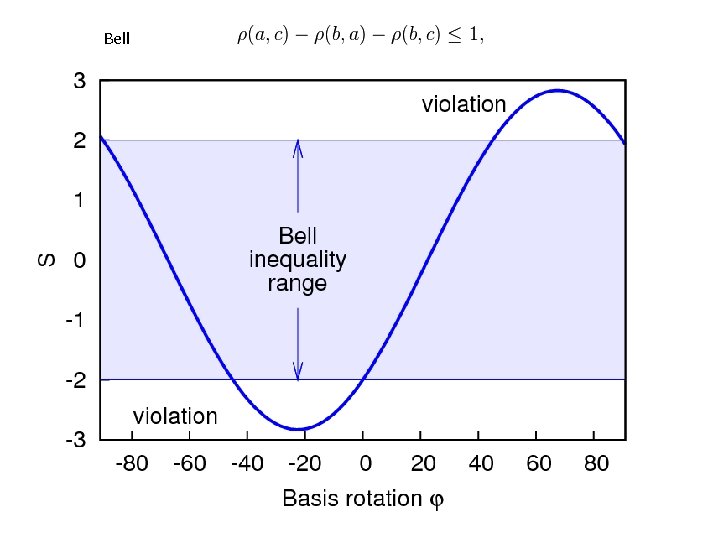
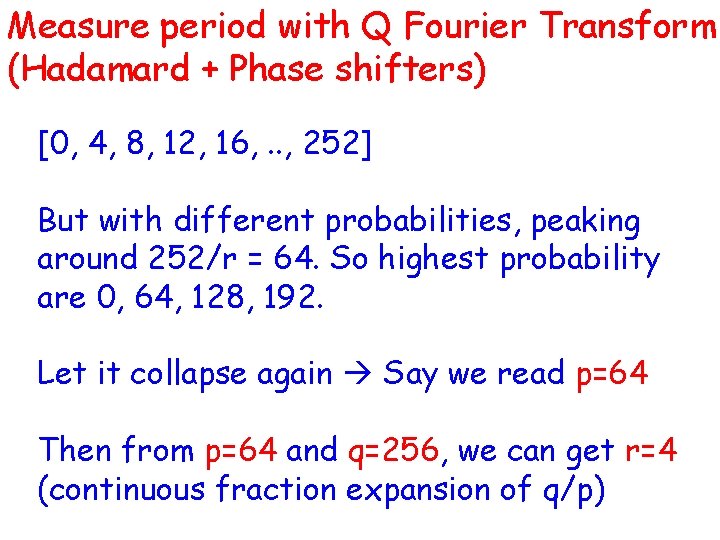
Proof: Bell’s inequality Own vs Rent: O and O Car vs No Car: C and C TV vs No TV: T and T OCT + OCT + OCT = 1 If only two questions on a survey – coalesce info thus T T O O ? ? O C C ? ? C Jay Sulzberger T T ? ?
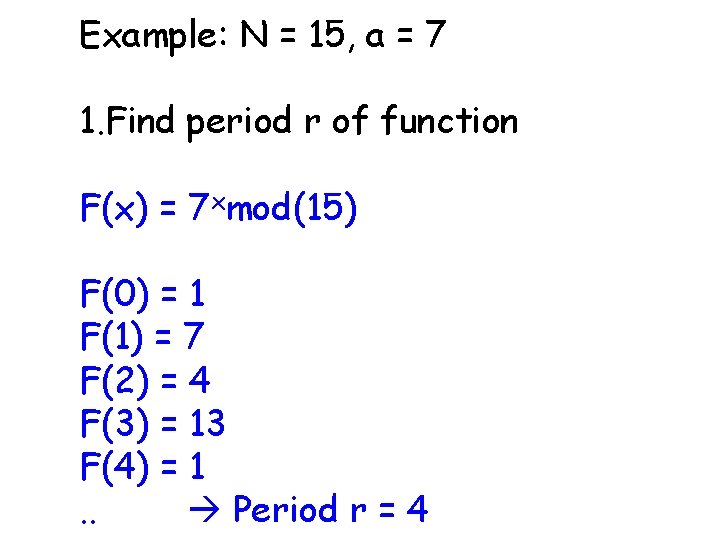
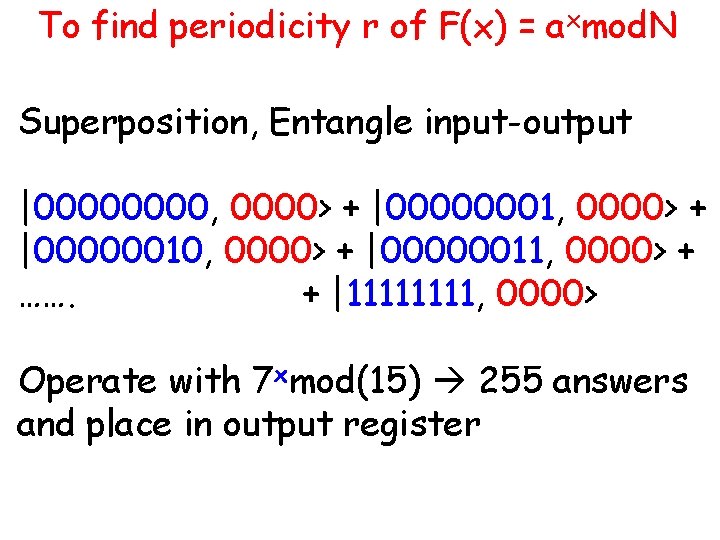
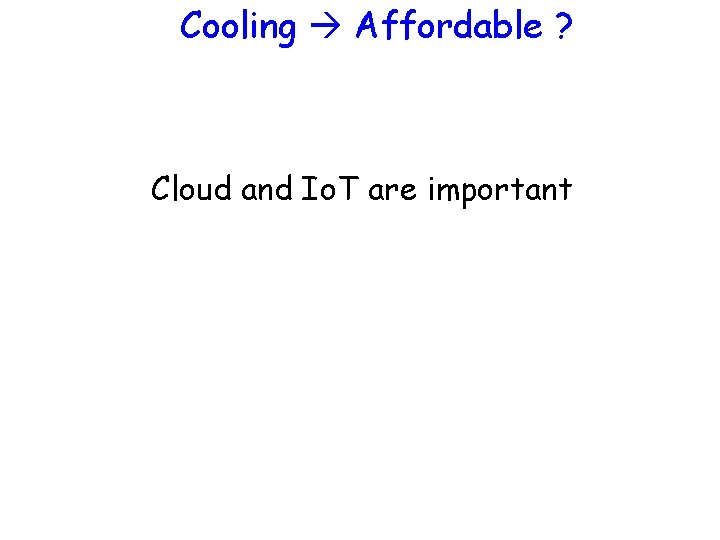
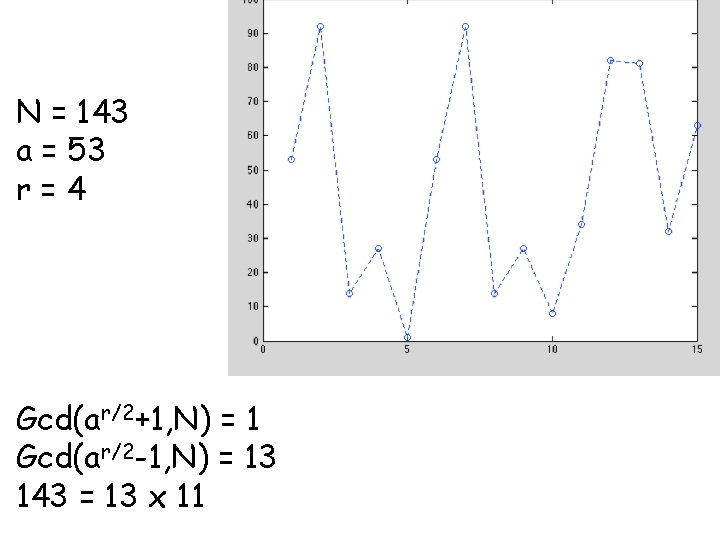
Proof: Bell’s inequality T T O O ? ? O C C ? ? C T T ? ? Test for accuracy: TO + OC + CT ≤ 2 Proof: LHS: OCT + OCT + OCT = 1 TOC + OCT + CTO + CTO = 2 [ 1 – OCT] ≤ 2
Bell
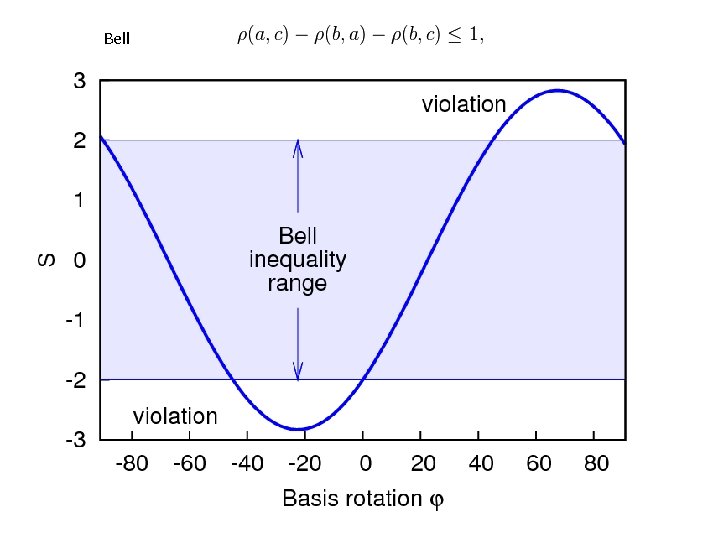
![TO OC CT 2 P A not B TO + OC + CT ≤ 2 P ( A & [not B] )](https://slidetodoc.com/presentation_image/ec64489b59d45f3eb52cd35872119f2e/image-46.jpg)
TO + OC + CT ≤ 2 P ( A & [not B] ) + P ( B & [not C] ) http: //arxiv. org/pdf/0704. 2529 v 2. pdf ≥ P(A
Entanglement is real Electrons are in superposition A classical measurement decouples them by entangling with an apparatus. Decoherence kills phase information
Entanglement is real How can we use this for QC ?

Prime Factorization
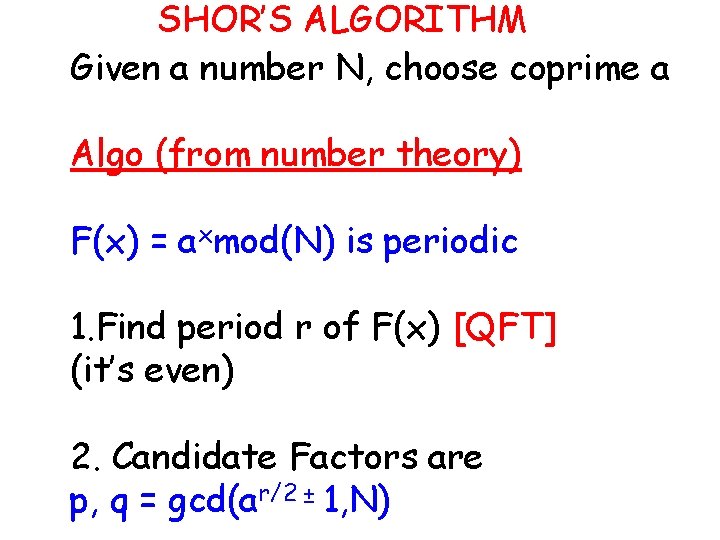
Useful for Quantum Cryptography 1 e 29 (LOCK) = 29996224275833 x 3475385758524527 (MESSAGE/CODE) (KEY) Classical computer doing 20 GFLOPS needs 1015/20 x 109 ~ 0. 5 day to solve this Largest prime has 22, 338, 618 digits 4000 years! Create superposition of all states related to key as input Entangle with gateable output Measure output input collapses (don’t peek yet !) Use gates to do Fourier Transform on input further collapses Now Read input From input + output reads, we can get factor !!!
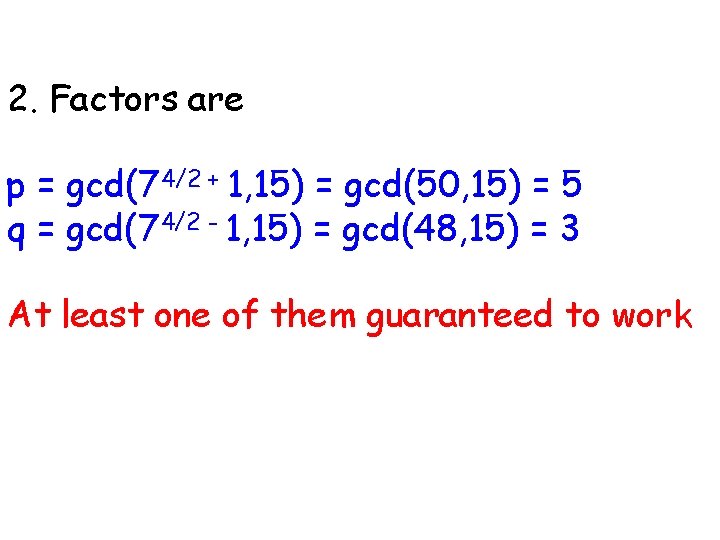
SHOR’S ALGORITHM Given a number N, choose coprime a Algo (from number theory) F(x) = axmod(N) is periodic 1. Find period r of F(x) [QFT] (it’s even) 2. Candidate Factors are p, q = gcd(ar/2 ± 1, N)
Why? Solve for x 2 = 1 mod(N) ie, (x+1)(x-1) = 0 mod(N) = N So factors of N are (x+1) or (x-1) So, gcd(x+1, N) or gcd(x-1, N)
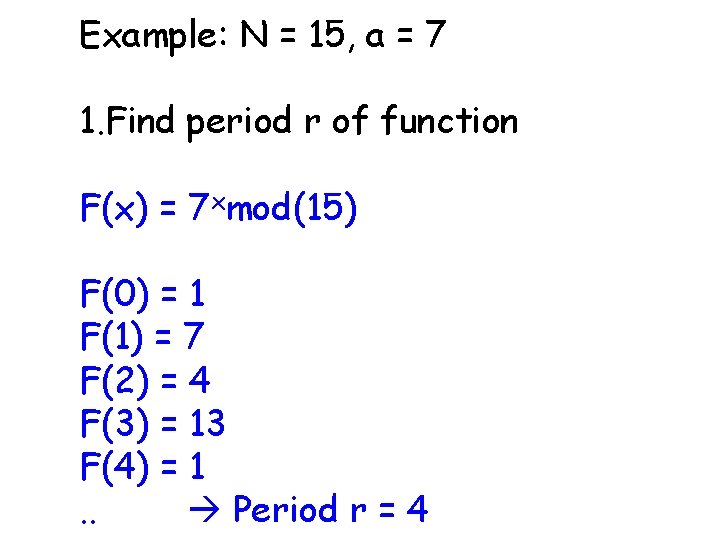
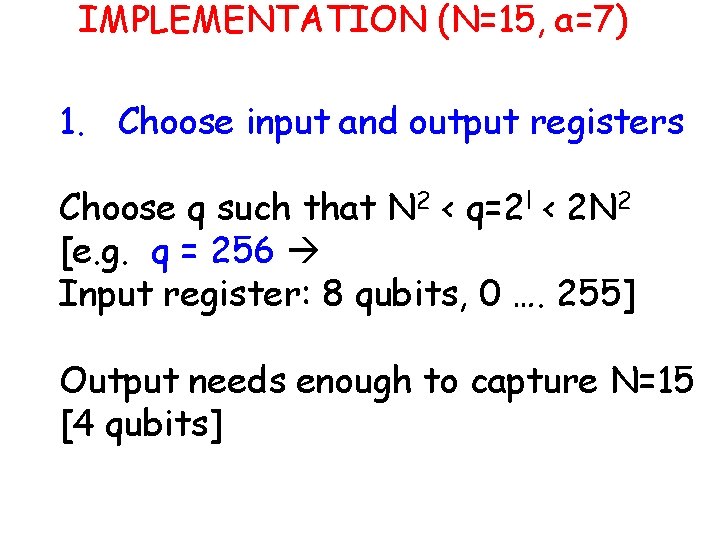
Example: N = 15, a = 7 1. Find period r of function F(x) = 7 xmod(15) F(0) = 1 F(1) = 7 F(2) = 4 F(3) = 13 F(4) = 1. . Period r = 4
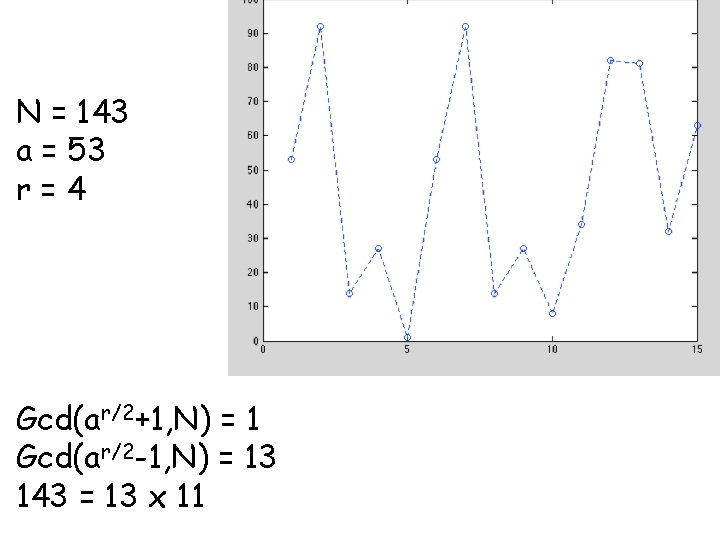
2. Factors are p = gcd(74/2 + 1, 15) = gcd(50, 15) = 5 q = gcd(74/2 - 1, 15) = gcd(48, 15) = 3 At least one of them guaranteed to work
N = 143 a = 53 r=4 Gcd(ar/2+1, N) = 1 Gcd(ar/2 -1, N) = 13 143 = 13 x 11
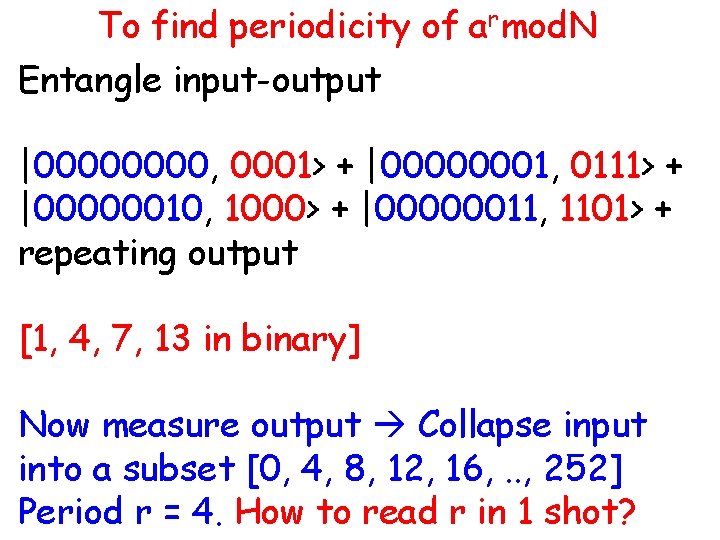
IMPLEMENTATION (N=15, a=7) 1. Choose input and output registers Choose q such that N 2 < q=2 l < 2 N 2 [e. g. q = 256 Input register: 8 qubits, 0 …. 255] Output needs enough to capture N=15 [4 qubits]
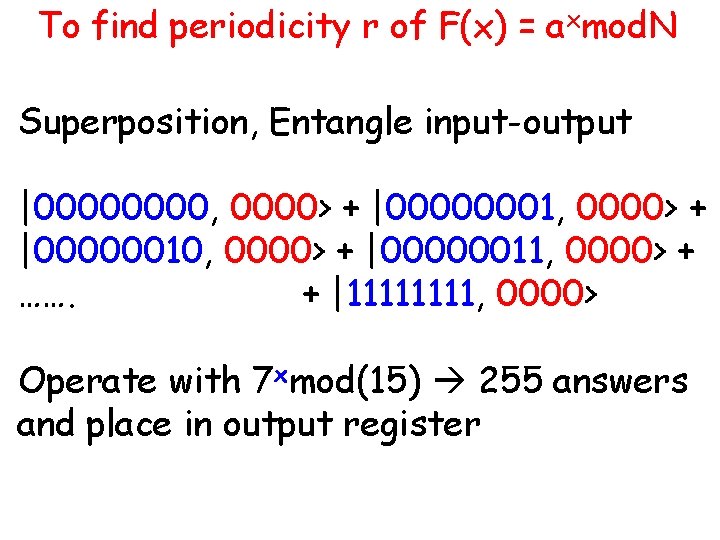
To find periodicity r of F(x) = axmod. N Superposition, Entangle input-output |0000, 0000> + |00000001, 0000> + |00000010, 0000> + |00000011, 0000> + ……. + |1111, 0000> Operate with 7 xmod(15) 255 answers and place in output register
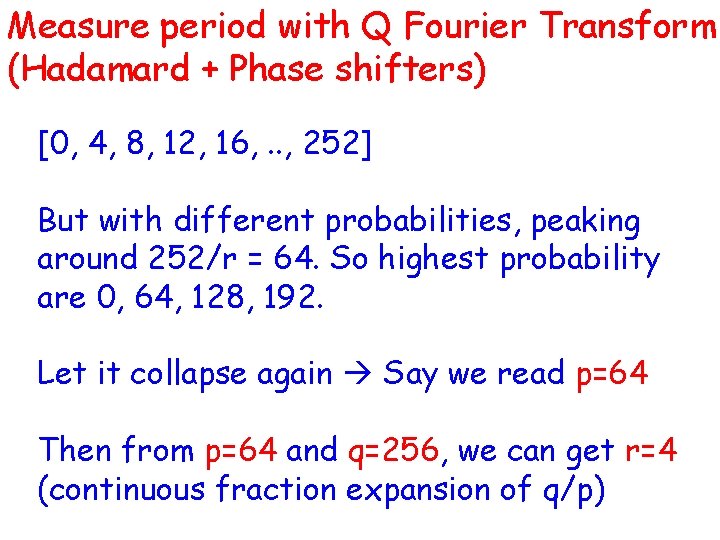
To find periodicity of armod. N Entangle input-output |0000, 0001> + |00000001, 0111> + |00000010, 1000> + |00000011, 1101> + repeating output [1, 4, 7, 13 in binary] Now measure output Collapse input into a subset [0, 4, 8, 12, 16, . . , 252] Period r = 4. How to read r in 1 shot?
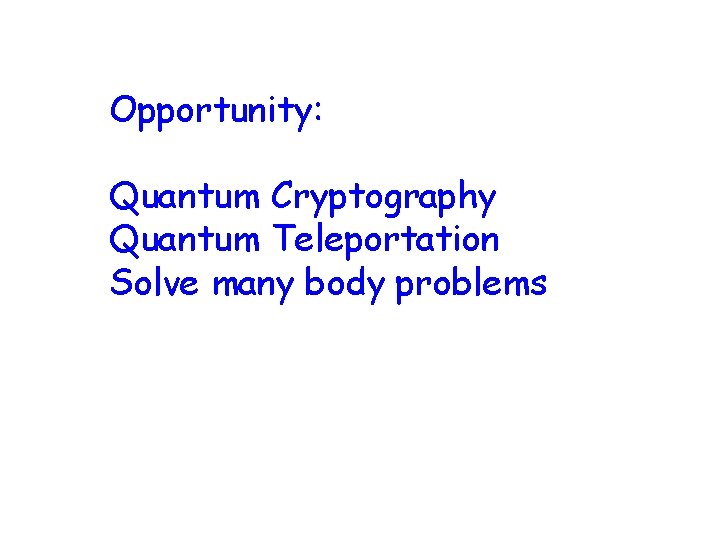
Measure period with Q Fourier Transform (Hadamard + Phase shifters) [0, 4, 8, 12, 16, . . , 252] But with different probabilities, peaking around 252/r = 64. So highest probability are 0, 64, 128, 192. Let it collapse again Say we read p=64 Then from p=64 and q=256, we can get r=4 (continuous fraction expansion of q/p)
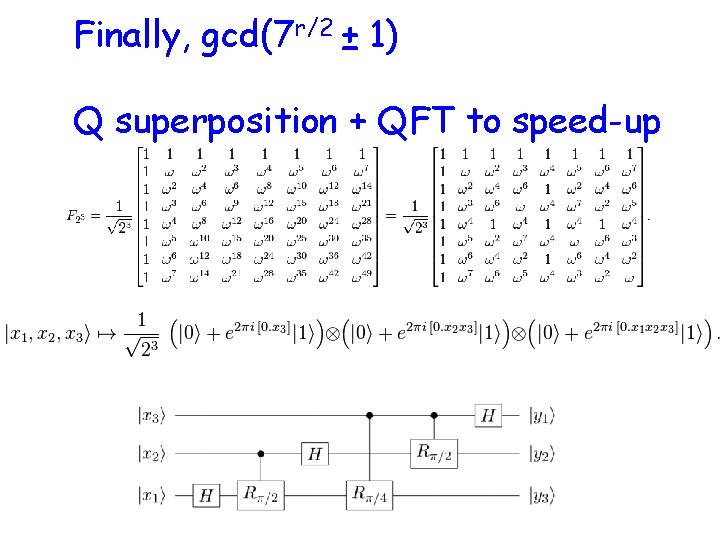
Finally, gcd(7 r/2 ± 1) Q superposition + QFT to speed-up
Opportunity: Quantum Cryptography Quantum Teleportation Solve many body problems
Di. Vincenzo’s 5 criteria • Scalable physical system with well Characterized qubits • Initialize • Universal set of Q-Gates H = - B. S 1 – JS 1. S 2 • Maintain Quantum Coherence • Efficient Read out
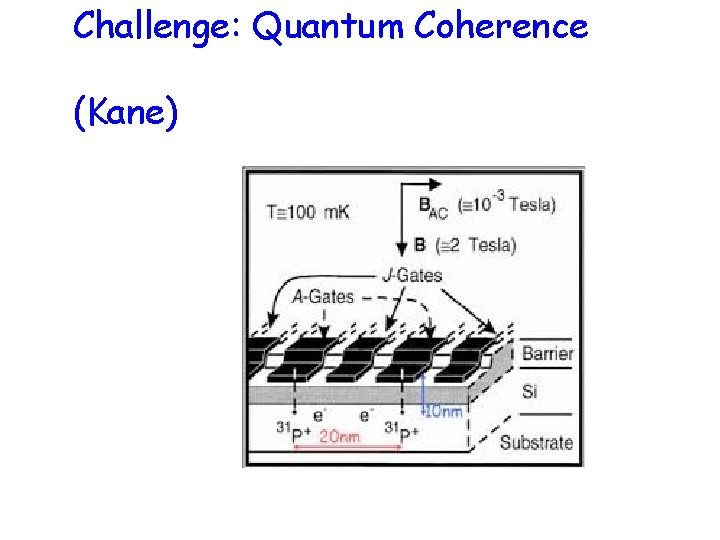
Challenge: Quantum Coherence (Kane)
Cooling Affordable ? Cloud and Io. T are important