QR Code Authentication with Embedded Message Authentication Code
QR Code Authentication with Embedded Message Authentication Code Source: Mobile Networks and Applications, pp. 112, 2016. (published online: 17 Nov. 2016) Authors: Changsheng Chen Speaker: Huang Peng-Cheng Date:
Outline • Related Works • The Proposed Scheme • Experimental results • Conclusions • Comments 2
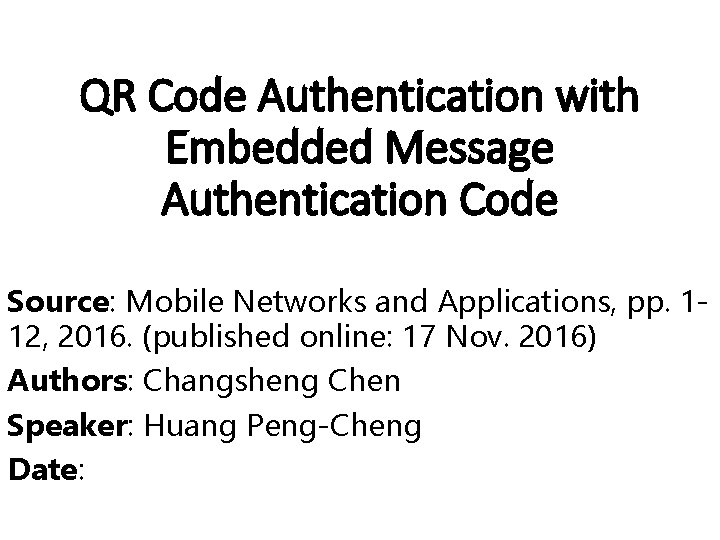
Related works(1/2) --QR code The structure for QR code of version 6 with error correction level medium 3
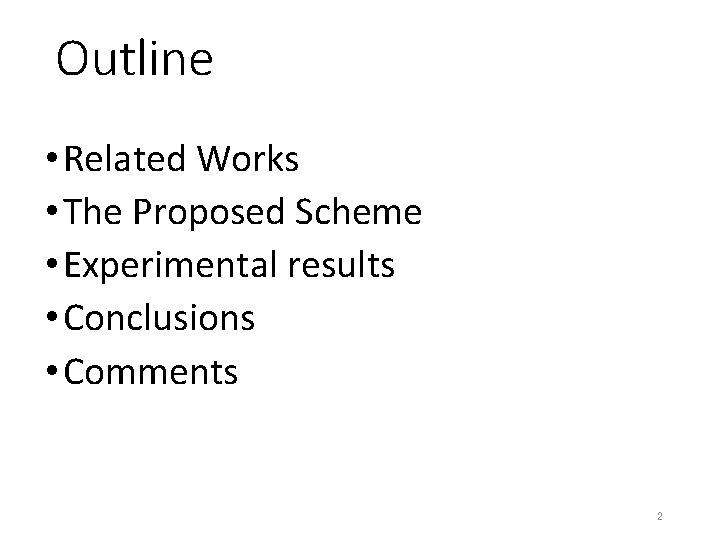
Related Works(2/2) The mask operation in the QR code generation process. 4
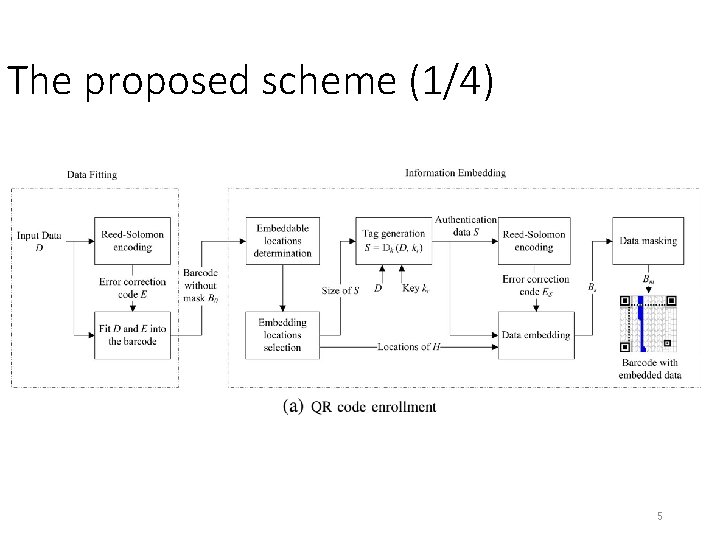
The proposed scheme (1/4) 5
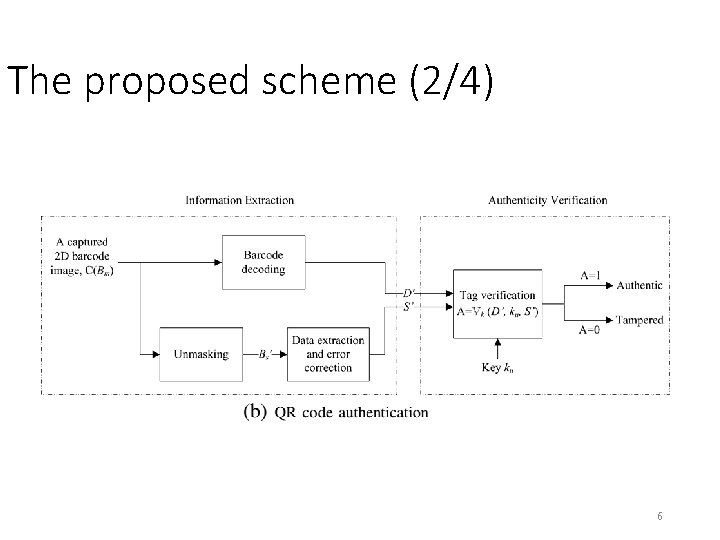
The proposed scheme (2/4) 6
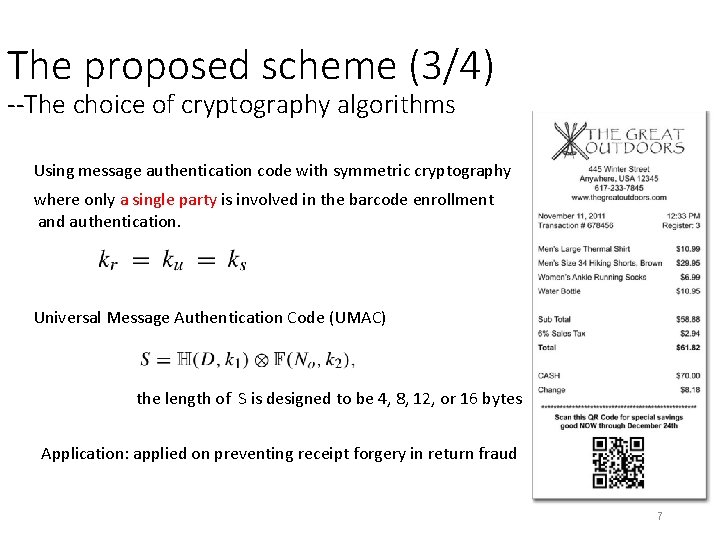
The proposed scheme (3/4) --The choice of cryptography algorithms Using message authentication code with symmetric cryptography where only a single party is involved in the barcode enrollment and authentication. Universal Message Authentication Code (UMAC) the length of S is designed to be 4, 8, 12, or 16 bytes Application: applied on preventing receipt forgery in return fraud 7
The proposed scheme (4/4) --The choice of cryptography algorithms Using digital signature with asymmetric cryptography where multiple parties is involved in the barcode enrollment and authentication. The Elliptic Curve Digital Signature Algorithm (ECDSA) Application: payment information authentication 8
Experimental results (1/5) --Decoding performances 9
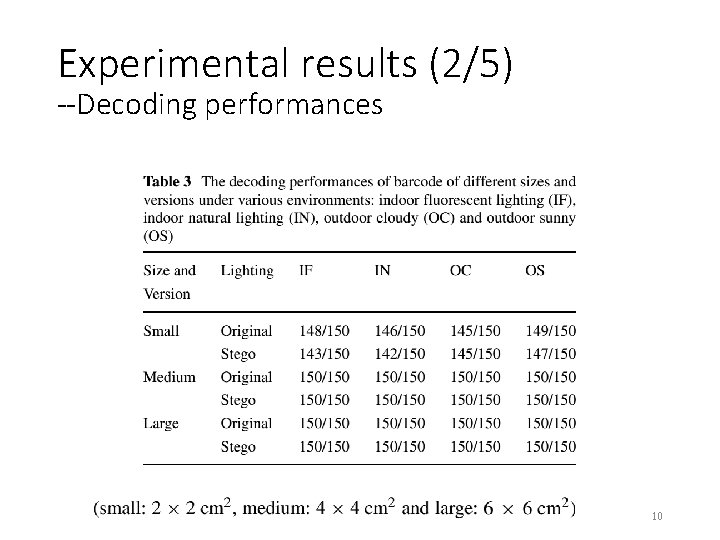
Experimental results (2/5) --Decoding performances 10
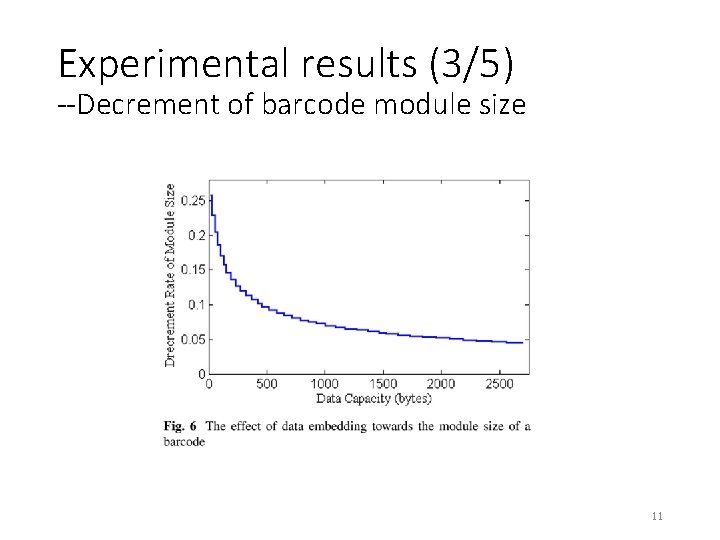
Experimental results (3/5) --Decrement of barcode module size 11
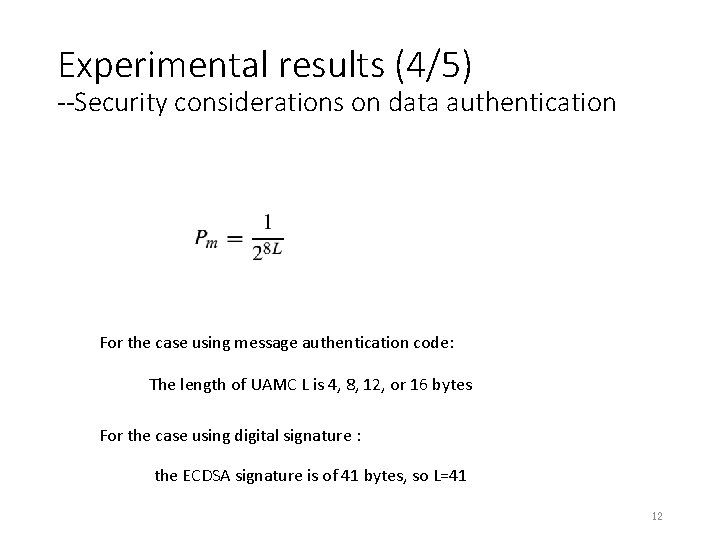
Experimental results (4/5) --Security considerations on data authentication For the case using message authentication code: The length of UAMC L is 4, 8, 12, or 16 bytes For the case using digital signature : the ECDSA signature is of 41 bytes, so L=41 12
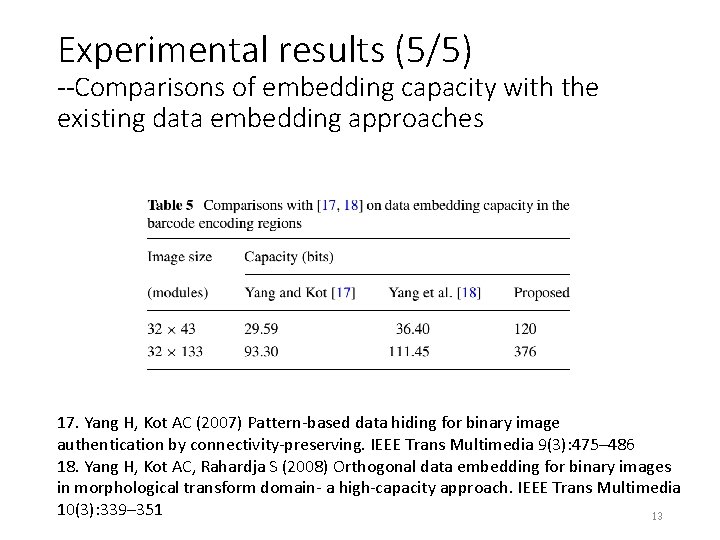
Experimental results (5/5) --Comparisons of embedding capacity with the existing data embedding approaches 17. Yang H, Kot AC (2007) Pattern-based data hiding for binary image authentication by connectivity-preserving. IEEE Trans Multimedia 9(3): 475– 486 18. Yang H, Kot AC, Rahardja S (2008) Orthogonal data embedding for binary images in morphological transform domain- a high-capacity approach. IEEE Trans Multimedia 10(3): 339– 351 13
Conclusions üOff-line certification üHigh security üHigh capacity 14
comments 1. The approach is implemented with the error correction mechanism of QR code. 2. Embed the authentication code by using data hiding approach. 3. The secret payload can be improved by exploiting the characteristic of RS code. 15
- Slides: 15