Qo S in the Control Internet Raouf Boutaba
Qo. S in the Control Internet Raouf Boutaba School of Computer Science University of Waterloo E-mail: rboutaba@bbcr. uwaterloo. ca APNOMS’ 02 , Jeju, Korea 1
Outline m m m Multimedia Networking Applications Challenges and Solutions in IP Networks Audio/Video Compression in the Internet Streaming Stored Audio/Video, RTSP Real time (phone) over IP best effort RTP, RTCP, H. 323 Improving Qo. S in IP: Basic Principles Scheduling and Policing Mechanisms Integrated & Differentiated IP Services MPLS and traffic engineering Policy Based Networking for Qo. S control COPS extensions for distributed control APNOMS’ 02 , Jeju, Korea 2
Multimedia Networking Appl’s r Typically sensitive to delay, but can tolerate packet loss (would cause minor glitches that can be concealed) r Data contains audio and video content (“continuous media”), r Three classes: m Streaming stored audio and video m One to many streaming of real-time audio and video m Real-time interactive audio and video APNOMS’ 02 , Jeju, Korea 3
Streaming Stored Audio/Video r Clients m Request audio/video files (compressed) from servers Examples: Music, Movies m Clients pipeline reception over the network and display r Delay m From client request until display start can be 1 to 10 seconds m Playback starts while client continues receiving file from server -> Streaming r User interactivity m User can control operation (similar to VCR): pause, resume, fast forward, rewind, etc. APNOMS’ 02 , Jeju, Korea 4
Unidirectionnel Real Time r Similar to existing TV and radio stations, but delivery on the network m Microsoft provides an Internet radio station guide r One to many streaming m Many users who are simultaneously receiving the same realtime audio/video program m Efficient distribution through multicasting (however, today’s most one-to-many audio/video transmission in the Internet use separate unicast streams) r Non-interactive, just listen/view r Delay m From client click until playback start is up to 10’s seconds APNOMS’ 02 , Jeju, Korea 5
Real-time Interactive Appl’s r Internet Phone or video conference r Delay m More stringent delay requirement than Streaming and Unidirectional because of real-time nature m Video: < 150 msec acceptable m Audio: < 150 msec good, < 400 msec acceptable r Interactivity m One-to-many real-time is not interactive as users cannot pause or rewind transmission (hundreds others listening) m Interactive in the sense that participants can orally and visually respond to each other in real time APNOMS’ 02 , Jeju, Korea 6
Challenges r TCP/UDP/IP suite provides best-effort, no guarantees on expectation or variance of packet delay r Streaming applications delay of 5 to 10 seconds is typical and has been acceptable, but performance deteriorate if links are congested (transoceanic) r Real-Time Interactive requirements on delay and its jitter have been satisfied by over-provisioning (providing plenty of bandwidth), what will happen when the load increases? . . . r Most router implementations use only FCFS packet processing and transmission scheduling APNOMS’ 02 , Jeju, Korea 7
Challenges (Cont) r To mitigate impact of “best-effort” protocols, we can: m. Use UDP to avoid TCP and its slow-start phase… m. Delay playback (~100 ms) to diminish networkinduced jitter m. Buffer content at client and control playback to remedy jitter m. Adapt compression level to available bandwidth metc… APNOMS’ 02 , Jeju, Korea 8
Solution Approaches in IP Networks r Just add more bandwidth and enhance caching capabilities (over-provisioning) r Need major change of the protocols: m Incorporate resource reservation (bandwidth, processing, buffering), and new scheduling policies m Set up service level agreements with applications, monitor and enforce the agreements, charge accordingly r Need moderate changes: m Use small number of (possibly two) traffic classes for all packets and differentiate service accordingly m Charge based on class of packets (platinum, low-budget) m Network capacity is provided to ensure first class packets incur no significant delay at routers APNOMS’ 02 , Jeju, Korea 9
Audio and Video Compression r Audio and video are digitized and compressed m Need for digitization: Internet transmits bits m Need for compression: uncompressed audio/video consumes tremendous amount of storage and bandwidth m Compression removes inherent redundancies in digitized audio/video r Reduces amount of data by order of magnitude m Example: A single image of 1024 pixels * 1024 pixels; each pixel encoded into 24 bits m Without compression: è Requires 3 MB of storage è Takes 7 min over a 64 Kbps link m With a modest compression (10: 1 compression rate) è Requires 300 KB of storage è Takes less than 6 seconds APNOMS’ 02 , Jeju, Korea 10
Audio Compression in the Internet r Pulse Code Modulation (PCM) m Analog audio signal is sampled at some fixed rate; Value of each sample is an arbitrary real number m Each sample is rounded to one of a finite number of values (“quantization”). Number of quantization values is power of 2 m Each quantization value is represented by a fixed number of bits. Bit representations of all samples are concatenated together form the digital signal r Examples of PCM encoding m Speech: 8000 samples/sec; 8 bits per sample -> 64 Kbps rate m Compact Disk: 44, 100 samples/sec; 16 bits per sample -> rate of 705. 6 Kbps for mono and 1. 411 Mbps for stereo r Compression techniques used to reduce bit rate m GSM (13 Kbps); G. 729 (8 Kbps); G. 723(6. 4 and 5. 3 Kbps) m MPEG layer 3 (MP 3): 128 or 112 Kbps (near CD-quality music) APNOMS’ 02 , Jeju, Korea 11
Video Compression in the Internet r Principles m A video is a sequence of images; each image is displayed at constant rate, e. g. at 24 or 30 images per second m An uncompressed, digitally encoded image consists of an array of pixels; each pixel is encoded into a number of bits to represent luminance and color m Two types of redundancy in video (exploited in compression) è Spatial redundancy (within a given image; e. g. white space) è Temporal redundancy (repetition from image to subsequent image; e. g. two exactly same images) r MPEG m MPEG 1, for CD-ROM quality video (1. 5 Mbps) m MPEG 2, for high quality DVD video (3 -6 Mbps) m MPEG 4, for object oriented video compression r H. 261 (also popular in the Internet) APNOMS’ 02 , Jeju, Korea 12
Streaming Stored Audio/Video r Important and growing application due to reduction of storage costs, increase in high speed network access from homes, enhancements to caching and introduction of Qo. S in IP networks r Audio/Video file is segmented and sent over either TCP or UDP, public segmentation protocol: Real-Time Protocol (RTP) r User interactive control is provided, eg the public protocol Real Time Streaming Protocol (RTSP) r Helper Application: displays content, which is typically requested via a Web browser; eg Real. Player; typical functions: m Decompression m Jitter removal m Error correction: use redundant packets to be used for reconstruction of original stream m GUI for user control APNOMS’ 02 , Jeju, Korea 13
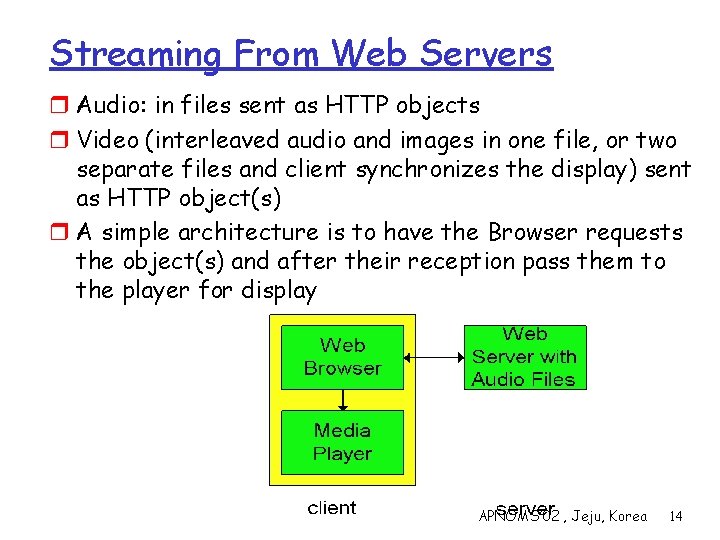
Streaming From Web Servers r Audio: in files sent as HTTP objects r Video (interleaved audio and images in one file, or two separate files and client synchronizes the display) sent as HTTP object(s) r A simple architecture is to have the Browser requests the object(s) and after their reception pass them to the player for display APNOMS’ 02 , Jeju, Korea 14
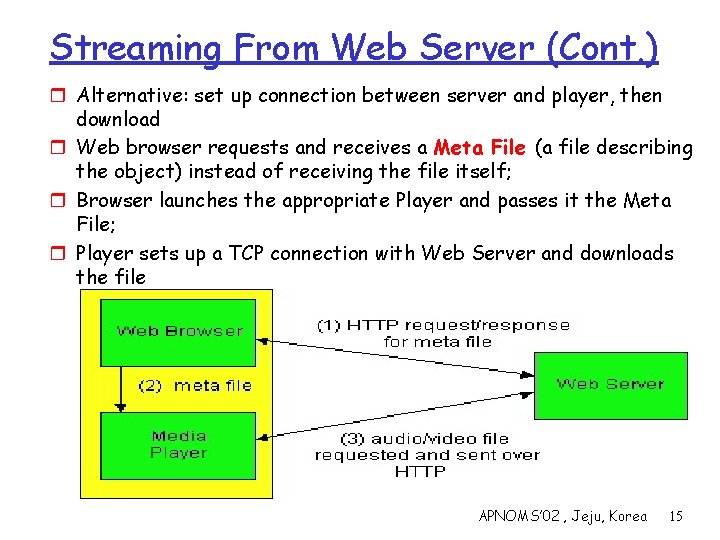
Streaming From Web Server (Cont. ) r Alternative: set up connection between server and player, then download r Web browser requests and receives a Meta File (a file describing the object) instead of receiving the file itself; r Browser launches the appropriate Player and passes it the Meta File; r Player sets up a TCP connection with Web Server and downloads the file APNOMS’ 02 , Jeju, Korea 15
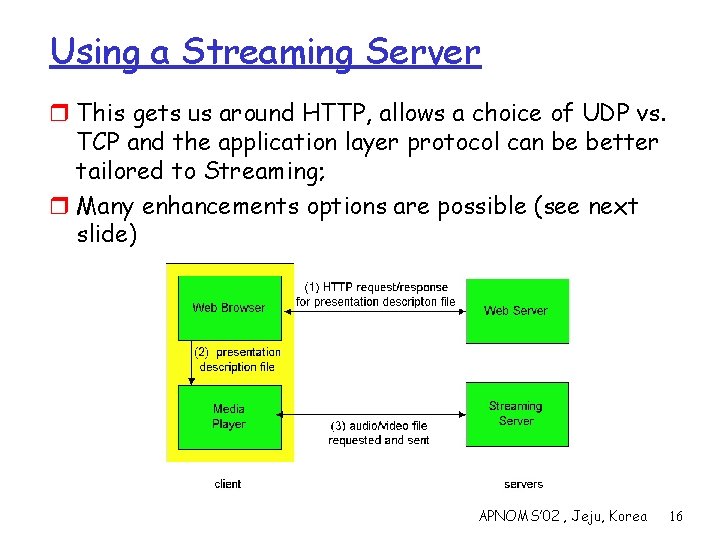
Using a Streaming Server r This gets us around HTTP, allows a choice of UDP vs. TCP and the application layer protocol can be better tailored to Streaming; r Many enhancements options are possible (see next slide) APNOMS’ 02 , Jeju, Korea 16
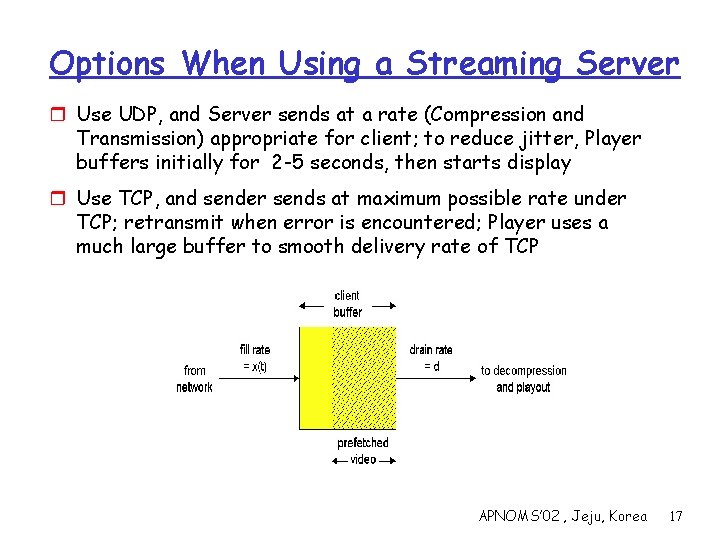
Options When Using a Streaming Server r Use UDP, and Server sends at a rate (Compression and Transmission) appropriate for client; to reduce jitter, Player buffers initially for 2 -5 seconds, then starts display r Use TCP, and sender sends at maximum possible rate under TCP; retransmit when error is encountered; Player uses a much large buffer to smooth delivery rate of TCP APNOMS’ 02 , Jeju, Korea 17
Real Time Streaming Protocol r For user to control display: rewind, fast forward, pause, resume, etc… r Out-of-band protocol (uses two connections, one for control messages (Port 554) and one for media stream r RFC 2326 permits use of either TCP or UDP for the control messages connection, sometimes called the RTSP Channel r As before, meta file is communicated to web browser which then launches the Player; Player sets up an RTSP connection for control messages in addition to the connection for the streaming media APNOMS’ 02 , Jeju, Korea 18
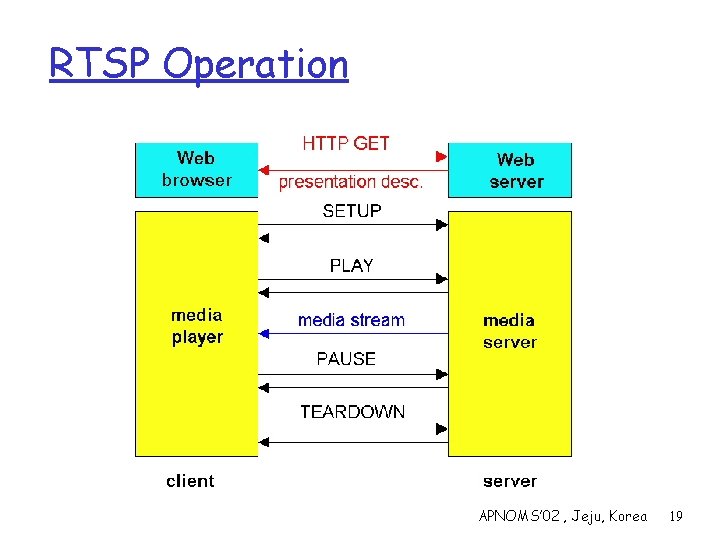
RTSP Operation APNOMS’ 02 , Jeju, Korea 19
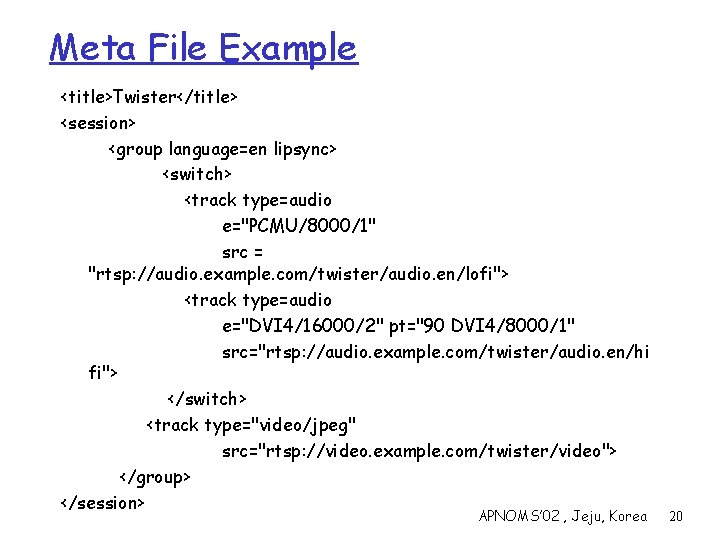
Meta File Example <title>Twister</title> <session> <group language=en lipsync> <switch> <track type=audio e="PCMU/8000/1" src = "rtsp: //audio. example. com/twister/audio. en/lofi"> <track type=audio e="DVI 4/16000/2" pt="90 DVI 4/8000/1" src="rtsp: //audio. example. com/twister/audio. en/hi fi"> </switch> <track type="video/jpeg" src="rtsp: //video. example. com/twister/video"> </group> </session> APNOMS’ 02 , Jeju, Korea 20
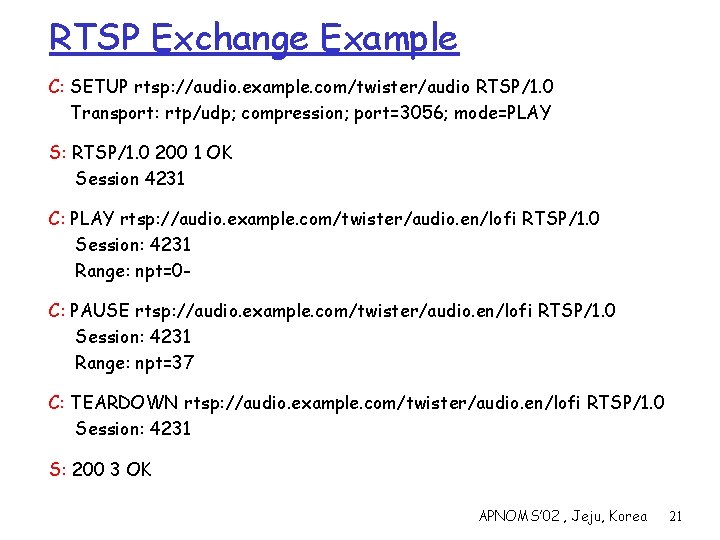
RTSP Exchange Example C: SETUP rtsp: //audio. example. com/twister/audio RTSP/1. 0 Transport: rtp/udp; compression; port=3056; mode=PLAY S: RTSP/1. 0 200 1 OK Session 4231 C: PLAY rtsp: //audio. example. com/twister/audio. en/lofi RTSP/1. 0 Session: 4231 Range: npt=0 C: PAUSE rtsp: //audio. example. com/twister/audio. en/lofi RTSP/1. 0 Session: 4231 Range: npt=37 C: TEARDOWN rtsp: //audio. example. com/twister/audio. en/lofi RTSP/1. 0 Session: 4231 S: 200 3 OK APNOMS’ 02 , Jeju, Korea 21
Real Time (Phone) Over IP’s Best Effort r Internet phone applications generate packets during talk spurts r Bit rate is 8 KBytes, and every 20 msec, the sender forms a packet of 160 Bytes + a header to be discussed below r The coded voice information is encapsulated into a UDP packet and sent out; some packets may be lost; up to 20 % loss is tolerable; using TCP eliminates loss but at a considerable cost: variance in delay; FEC is sometimes used to fix errors and make up losses r End-to-end delays above 400 msec cannot be tolerated; packets that are that delayed are ignored at the receiver r Delay jitter is handled by using timestamps, sequence numbers, and delaying playout at receivers either a fixed or a variable amount r With fixed playout delay, the delay should be as small as possible without missing too many packets; delay cannot exceed 400 msec APNOMS’ 02 , Jeju, Korea 22
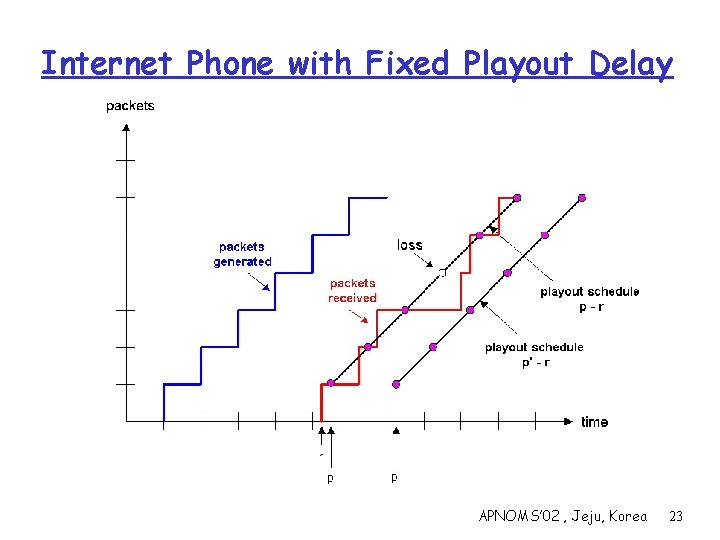
Internet Phone with Fixed Playout Delay APNOMS’ 02 , Jeju, Korea 23
Adaptive Playout Delay r Objective is to use a value for p-r that tracks the network delay performance as it varies during a phone call r The playout delay is computed for each talk spurt based on observed average delay and observed deviation from this average delay r Estimated average delay and deviation of average delay are computed in a manner similar to estimates of RTT and deviation in TCP r The beginning of a talk spurt is identified from examining the timestamps in successive and/or sequence numbers of chunks APNOMS’ 02 , Jeju, Korea 24
Recovery From Packet Loss r Loss is in a broader sense: packet never arrives or arrives later than its scheduled playout time r Since retransmission is inappropriate for Real Time applications, FEC or Interleaving are used to reduce loss impact r Simplest FEC scheme adds a redundant chunk made up of exclusive OR of a group of n chunks; redundancy is 1/n; can reconstruct if at most one lost chunk; playout time schedule assumes a loss per group r Mixed quality streams are used to include redundant duplicates of chunks; upon loss playout available redundant chunk, albeit a lower quality one r With one redundant chunk per chunk can recover from single losses APNOMS’ 02 , Jeju, Korea 25
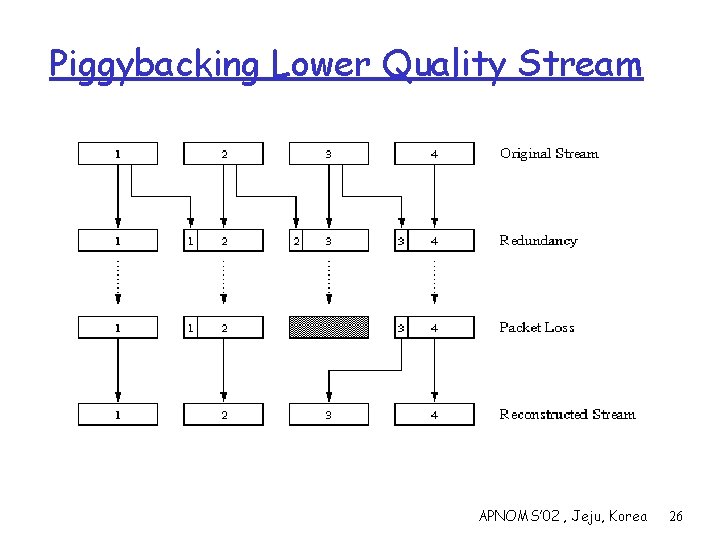
Piggybacking Lower Quality Stream APNOMS’ 02 , Jeju, Korea 26
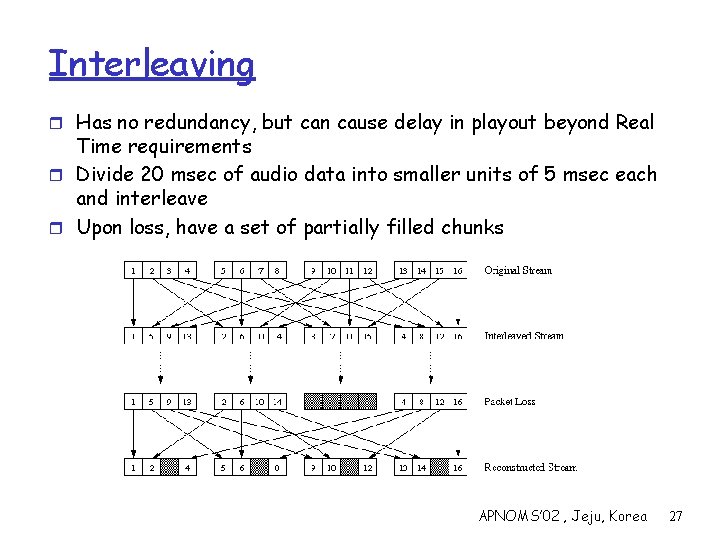
Interleaving r Has no redundancy, but can cause delay in playout beyond Real Time requirements r Divide 20 msec of audio data into smaller units of 5 msec each and interleave r Upon loss, have a set of partially filled chunks APNOMS’ 02 , Jeju, Korea 27
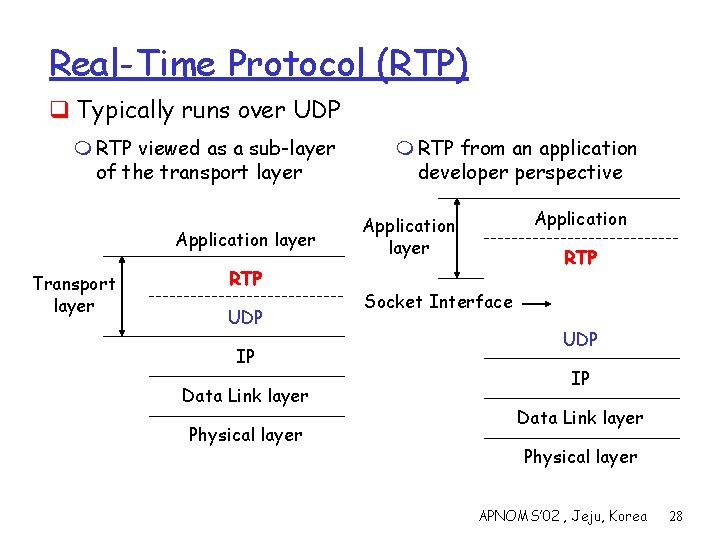
Real-Time Protocol (RTP) q Typically runs over UDP m RTP viewed as a sub-layer of the transport layer Application layer Transport layer RTP UDP IP Data Link layer Physical layer m RTP from an application developer perspective Application layer RTP Socket Interface UDP IP Data Link layer Physical layer APNOMS’ 02 , Jeju, Korea 28
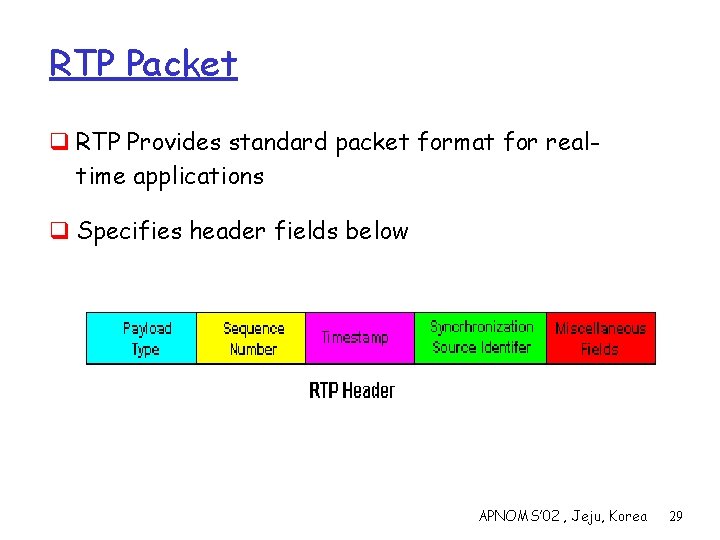
RTP Packet q RTP Provides standard packet format for realtime applications q Specifies header fields below APNOMS’ 02 , Jeju, Korea 29
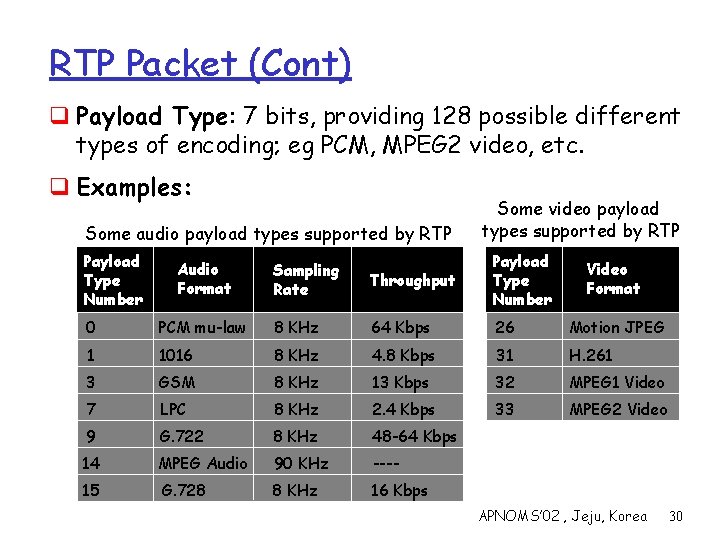
RTP Packet (Cont) q Payload Type: 7 bits, providing 128 possible different types of encoding; eg PCM, MPEG 2 video, etc. q Examples: Some audio payload types supported by RTP Payload Type Number Audio Format Some video payload types supported by RTP Sampling Rate Throughput Payload Type Number Video Format 0 PCM mu-law 8 KHz 64 Kbps 26 Motion JPEG 1 1016 8 KHz 4. 8 Kbps 31 H. 261 3 GSM 8 KHz 13 Kbps 32 MPEG 1 Video 7 LPC 8 KHz 2. 4 Kbps 33 MPEG 2 Video 9 G. 722 8 KHz 48 -64 Kbps 14 MPEG Audio 90 KHz ---- 15 G. 728 8 KHz 16 Kbps APNOMS’ 02 , Jeju, Korea 30
RTP Packet (Cont) q Sequence Number: 16 bits; used to detect packet loss. q Timestamp: 32 bits; gives the sampling instant of the first audio/video byte in the packet; used to remove jitter introduced by the network; the timestamp is derived from a sampling clock at the sender. q Synchronization Source identifier (SSRC): 32 bits; identifies the source of a stream; each stream in an RTP session has a distinct SSRC; assigned randomly by the source when the new stream is started. APNOMS’ 02 , Jeju, Korea 31
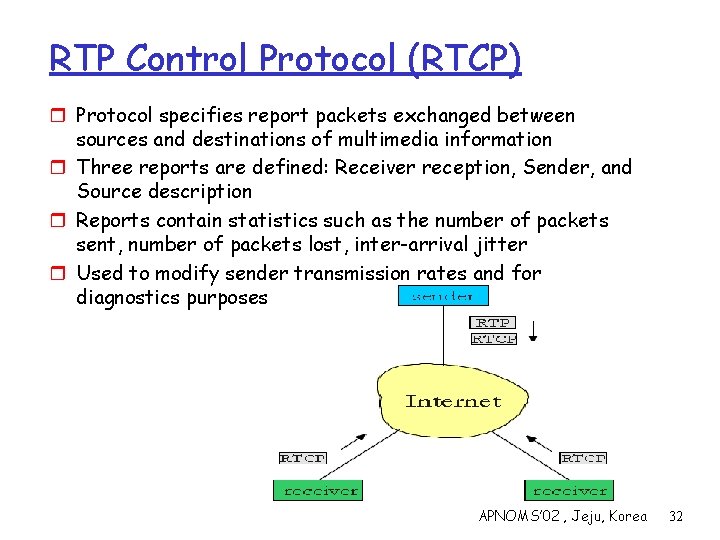
RTP Control Protocol (RTCP) r Protocol specifies report packets exchanged between sources and destinations of multimedia information r Three reports are defined: Receiver reception, Sender, and Source description r Reports contain statistics such as the number of packets sent, number of packets lost, inter-arrival jitter r Used to modify sender transmission rates and for diagnostics purposes APNOMS’ 02 , Jeju, Korea 32
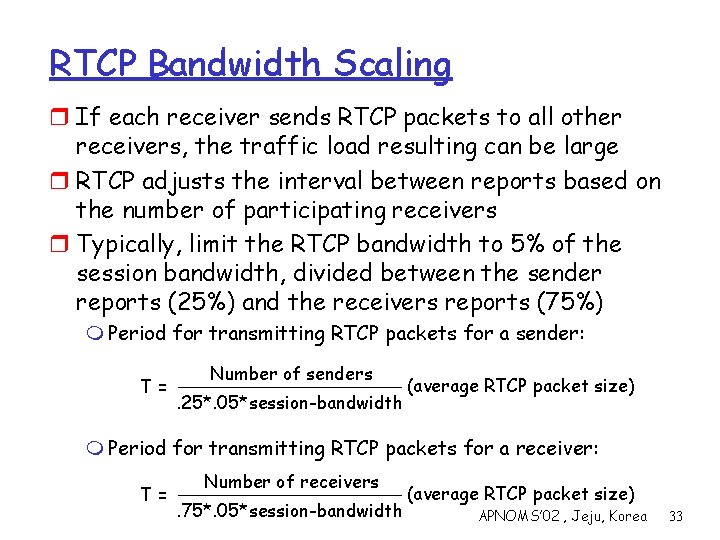
RTCP Bandwidth Scaling r If each receiver sends RTCP packets to all other receivers, the traffic load resulting can be large r RTCP adjusts the interval between reports based on the number of participating receivers r Typically, limit the RTCP bandwidth to 5% of the session bandwidth, divided between the sender reports (25%) and the receivers reports (75%) m Period for transmitting RTCP packets for a sender: T= Number of senders. 25*. 05*session-bandwidth (average RTCP packet size) m Period for transmitting RTCP packets for a receiver: T= Number of receivers. 75*. 05*session-bandwidth (average RTCP packet size) APNOMS’ 02 , Jeju, Korea 33
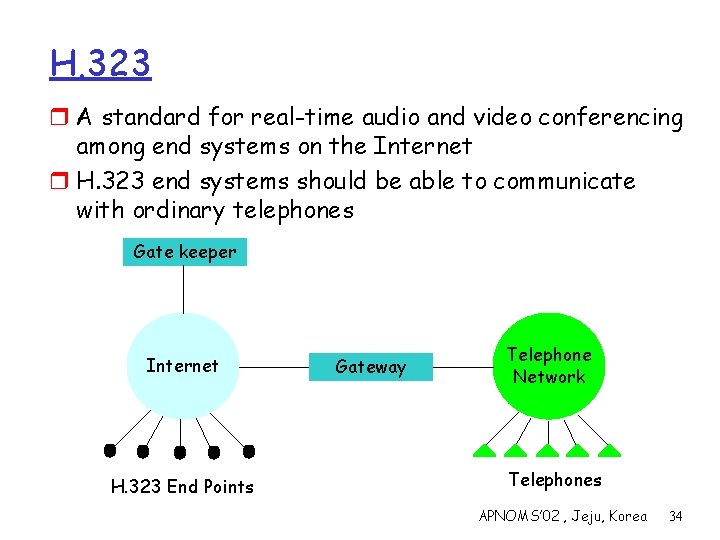
H. 323 r A standard for real-time audio and video conferencing among end systems on the Internet r H. 323 end systems should be able to communicate with ordinary telephones Gate keeper Internet H. 323 End Points Gateway Telephone Network Telephones APNOMS’ 02 , Jeju, Korea 34
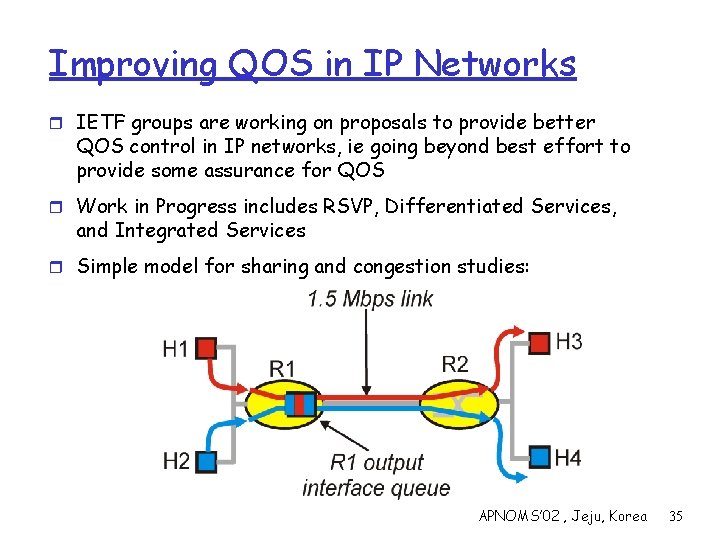
Improving QOS in IP Networks r IETF groups are working on proposals to provide better QOS control in IP networks, ie going beyond best effort to provide some assurance for QOS r Work in Progress includes RSVP, Differentiated Services, and Integrated Services r Simple model for sharing and congestion studies: APNOMS’ 02 , Jeju, Korea 35
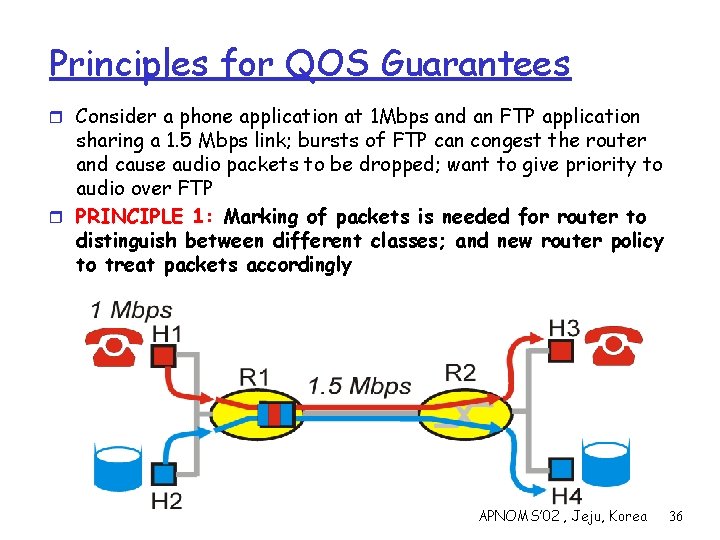
Principles for QOS Guarantees r Consider a phone application at 1 Mbps and an FTP application sharing a 1. 5 Mbps link; bursts of FTP can congest the router and cause audio packets to be dropped; want to give priority to audio over FTP r PRINCIPLE 1: Marking of packets is needed for router to distinguish between different classes; and new router policy to treat packets accordingly APNOMS’ 02 , Jeju, Korea 36
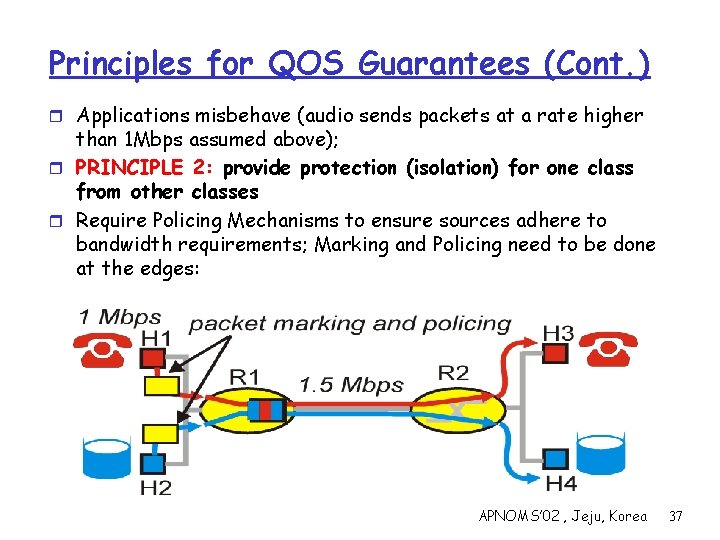
Principles for QOS Guarantees (Cont. ) r Applications misbehave (audio sends packets at a rate higher than 1 Mbps assumed above); r PRINCIPLE 2: provide protection (isolation) for one class from other classes r Require Policing Mechanisms to ensure sources adhere to bandwidth requirements; Marking and Policing need to be done at the edges: APNOMS’ 02 , Jeju, Korea 37
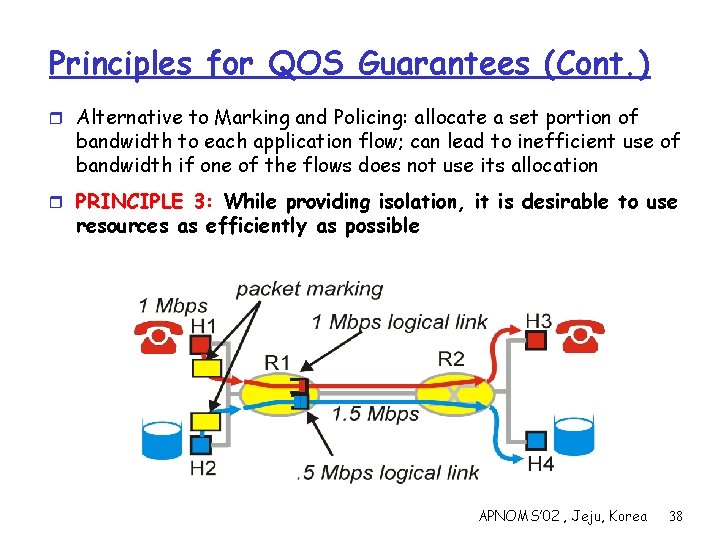
Principles for QOS Guarantees (Cont. ) r Alternative to Marking and Policing: allocate a set portion of bandwidth to each application flow; can lead to inefficient use of bandwidth if one of the flows does not use its allocation r PRINCIPLE 3: While providing isolation, it is desirable to use resources as efficiently as possible APNOMS’ 02 , Jeju, Korea 38
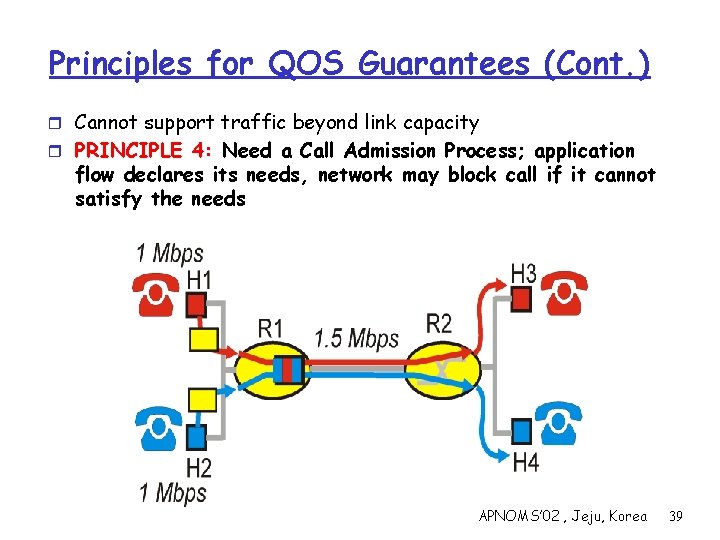
Principles for QOS Guarantees (Cont. ) r Cannot support traffic beyond link capacity r PRINCIPLE 4: Need a Call Admission Process; application flow declares its needs, network may block call if it cannot satisfy the needs APNOMS’ 02 , Jeju, Korea 39
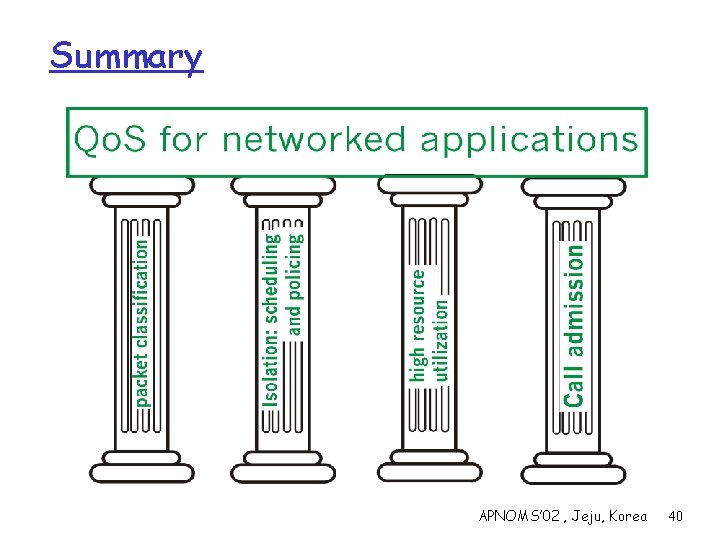
Summary APNOMS’ 02 , Jeju, Korea 40
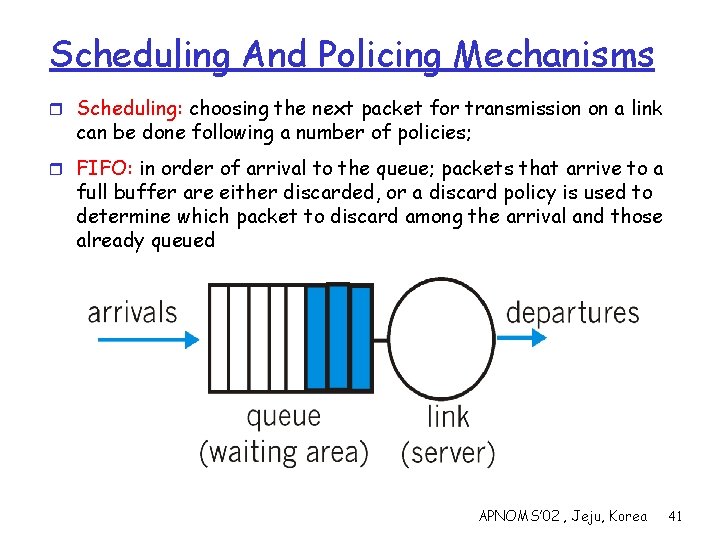
Scheduling And Policing Mechanisms r Scheduling: choosing the next packet for transmission on a link can be done following a number of policies; r FIFO: in order of arrival to the queue; packets that arrive to a full buffer are either discarded, or a discard policy is used to determine which packet to discard among the arrival and those already queued APNOMS’ 02 , Jeju, Korea 41
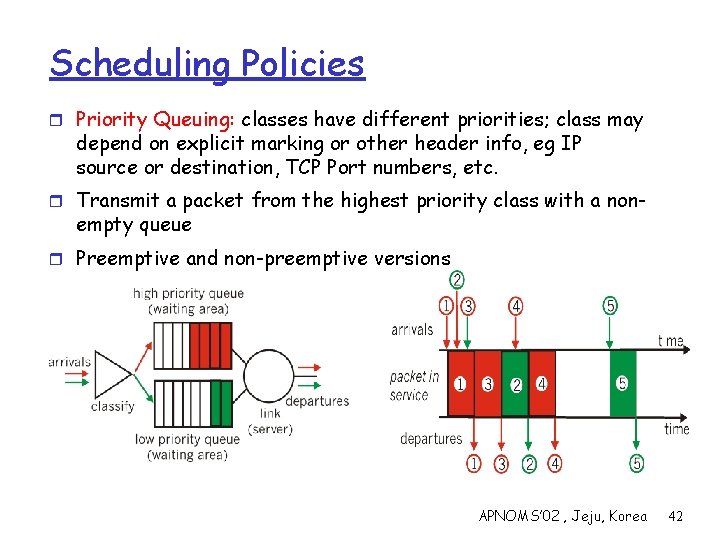
Scheduling Policies r Priority Queuing: classes have different priorities; class may depend on explicit marking or other header info, eg IP source or destination, TCP Port numbers, etc. r Transmit a packet from the highest priority class with a non- empty queue r Preemptive and non-preemptive versions APNOMS’ 02 , Jeju, Korea 42
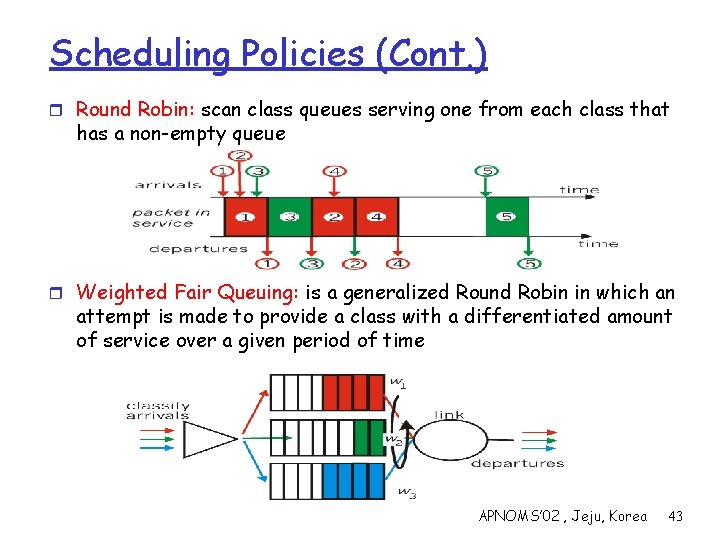
Scheduling Policies (Cont. ) r Round Robin: scan class queues serving one from each class that has a non-empty queue r Weighted Fair Queuing: is a generalized Round Robin in which an attempt is made to provide a class with a differentiated amount of service over a given period of time APNOMS’ 02 , Jeju, Korea 43
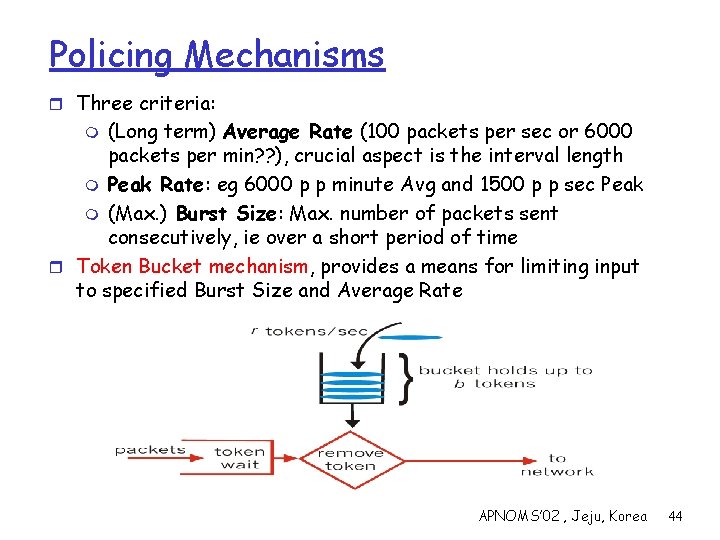
Policing Mechanisms r Three criteria: (Long term) Average Rate (100 packets per sec or 6000 packets per min? ? ), crucial aspect is the interval length m Peak Rate: eg 6000 p p minute Avg and 1500 p p sec Peak m (Max. ) Burst Size: Max. number of packets sent consecutively, ie over a short period of time r Token Bucket mechanism, provides a means for limiting input to specified Burst Size and Average Rate m APNOMS’ 02 , Jeju, Korea 44
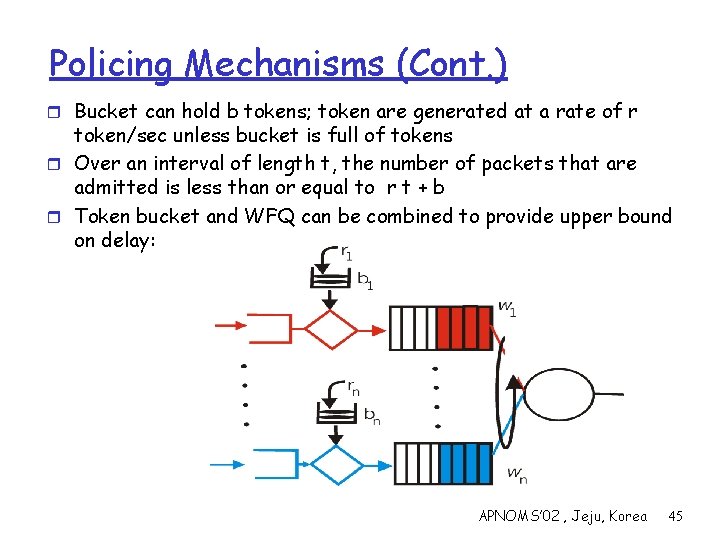
Policing Mechanisms (Cont. ) r Bucket can hold b tokens; token are generated at a rate of r token/sec unless bucket is full of tokens r Over an interval of length t, the number of packets that are admitted is less than or equal to r t + b r Token bucket and WFQ can be combined to provide upper bound on delay: APNOMS’ 02 , Jeju, Korea 45
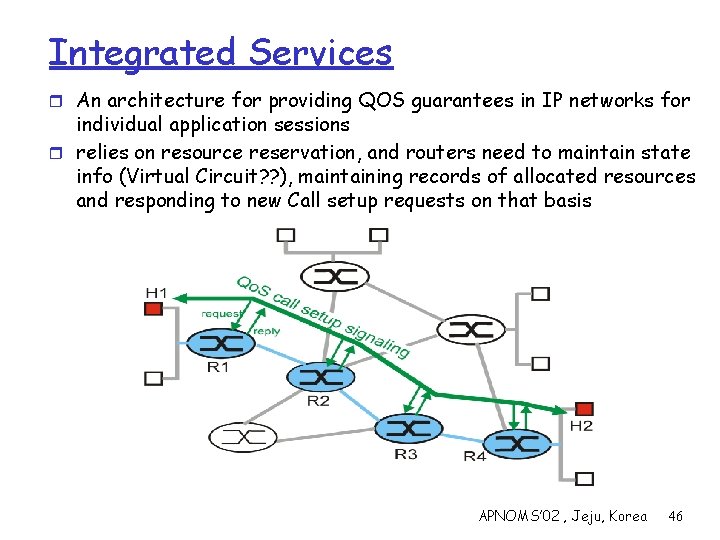
Integrated Services r An architecture for providing QOS guarantees in IP networks for individual application sessions r relies on resource reservation, and routers need to maintain state info (Virtual Circuit? ? ), maintaining records of allocated resources and responding to new Call setup requests on that basis APNOMS’ 02 , Jeju, Korea 46
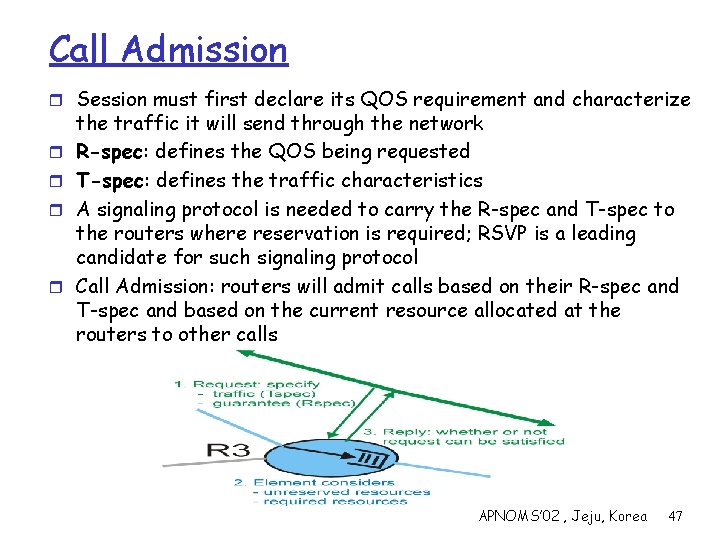
Call Admission r Session must first declare its QOS requirement and characterize r r the traffic it will send through the network R-spec: defines the QOS being requested T-spec: defines the traffic characteristics A signaling protocol is needed to carry the R-spec and T-spec to the routers where reservation is required; RSVP is a leading candidate for such signaling protocol Call Admission: routers will admit calls based on their R-spec and T-spec and based on the current resource allocated at the routers to other calls APNOMS’ 02 , Jeju, Korea 47
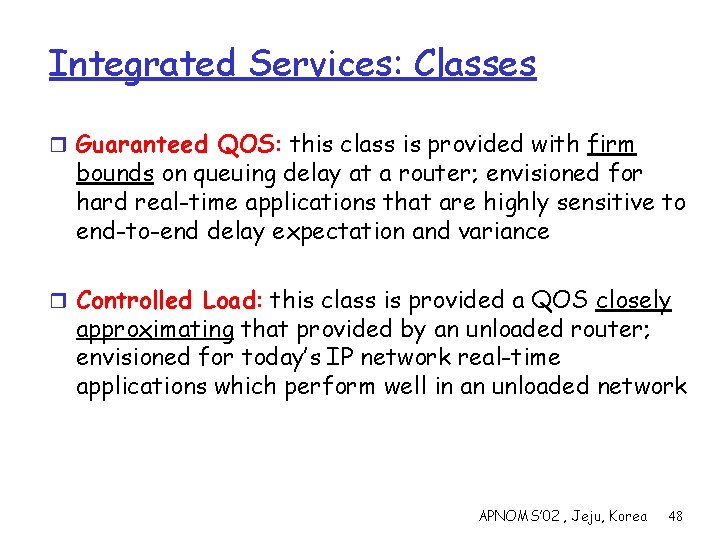
Integrated Services: Classes r Guaranteed QOS: this class is provided with firm bounds on queuing delay at a router; envisioned for hard real-time applications that are highly sensitive to end-to-end delay expectation and variance r Controlled Load: this class is provided a QOS closely approximating that provided by an unloaded router; envisioned for today’s IP network real-time applications which perform well in an unloaded network APNOMS’ 02 , Jeju, Korea 48
Differentiated Services r Intended to address the following difficulties with Intserv r r and RSVP; Scalability: maintaining states by routers in high speed networks is difficult due to the very large number of flows Flexible Service Models: Intserv has only two classes, want to provide more qualitative service classes; want to provide ‘relative’ service distinction (Platinum, Gold, Silver, …) Simpler signaling: (than RSVP) many applications and users may only want to specify a more qualitative notion of service Approach: m Only simple functions in the core, and relatively complex functions at edge routers (or hosts) m Do not define service classes, instead provides functional components with which service classes can be built APNOMS’ 02 , Jeju, Korea 49
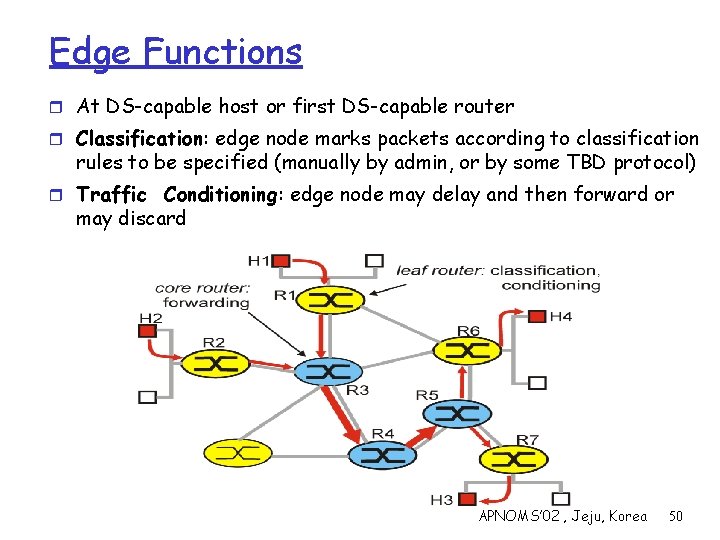
Edge Functions r At DS-capable host or first DS-capable router r Classification: edge node marks packets according to classification rules to be specified (manually by admin, or by some TBD protocol) r Traffic Conditioning: edge node may delay and then forward or may discard APNOMS’ 02 , Jeju, Korea 50
Core Functions r Forwarding: according to “Per-Hop-Behavior” or PHB specified for the particular packet class; such PHB is strictly based on class marking (no other header fields can be used to influence PHB) r No state info to be maintained by routers! APNOMS’ 02 , Jeju, Korea 51
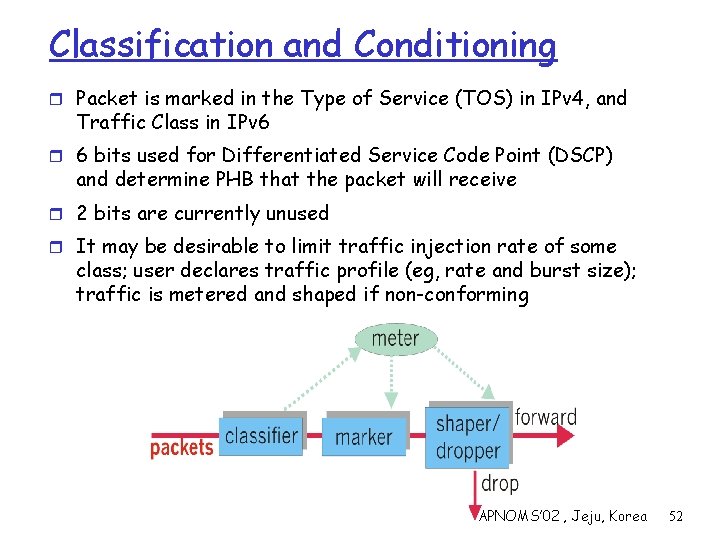
Classification and Conditioning r Packet is marked in the Type of Service (TOS) in IPv 4, and Traffic Class in IPv 6 r 6 bits used for Differentiated Service Code Point (DSCP) and determine PHB that the packet will receive r 2 bits are currently unused r It may be desirable to limit traffic injection rate of some class; user declares traffic profile (eg, rate and burst size); traffic is metered and shaped if non-conforming APNOMS’ 02 , Jeju, Korea 52
Forwarding (PHB) r PHB result in a different observable (measurable) forwarding performance behavior r PHB does not specify what mechanisms to use to ensure required PHB performance behavior r Examples: m Class A gets x% of outgoing link bandwidth over time intervals of a specified length m Class A packets leave first before packets from class B r PHBs under consideration: m Expedited Forwarding: departure rate of packets from a class equals or exceeds a specified rate (logical link with a minimum guaranteed rate) m Assured Forwarding: 4 classes, each guaranteed a minimum amount of bandwidth and buffering; each with three drop preference partitions APNOMS’ 02 , Jeju, Korea 53
Differentiated Services Issues r AF and EF are not even in a standard track yet… research ongoing r “Virtual Leased lines” and “Olympic” services are being discussed r Impact of crossing multiple ASs and routers that are not DS-capable r. . . APNOMS’ 02 , Jeju, Korea 54
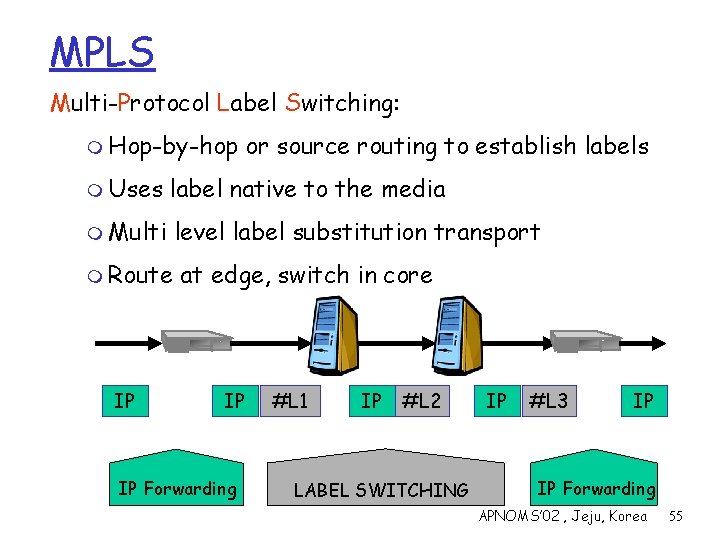
MPLS Multi-Protocol Label Switching: m Hop-by-hop or source routing to establish labels m Uses label native to the media m Multi level label substitution transport m Route IP at edge, switch in core IP IP Forwarding #L 1 IP #L 2 LABEL SWITCHING IP #L 3 IP IP Forwarding APNOMS’ 02 , Jeju, Korea 55
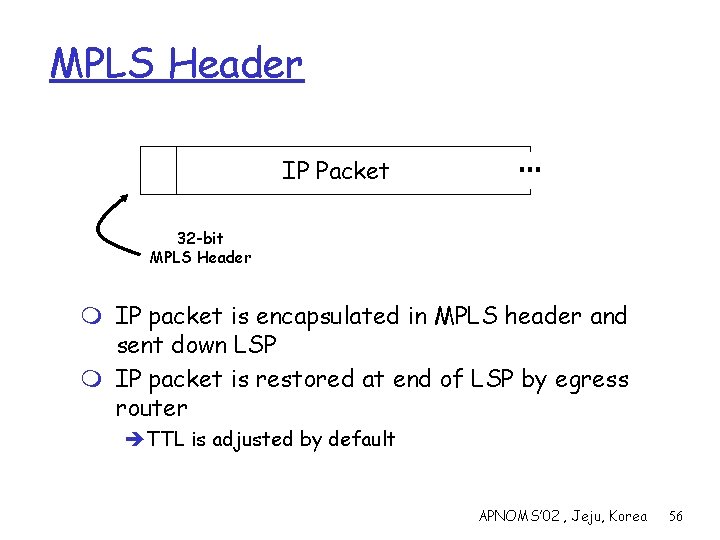
MPLS Header IP Packet … 32 -bit MPLS Header m IP packet is encapsulated in MPLS header and sent down LSP m IP packet is restored at end of LSP by egress router èTTL is adjusted by default APNOMS’ 02 , Jeju, Korea 56
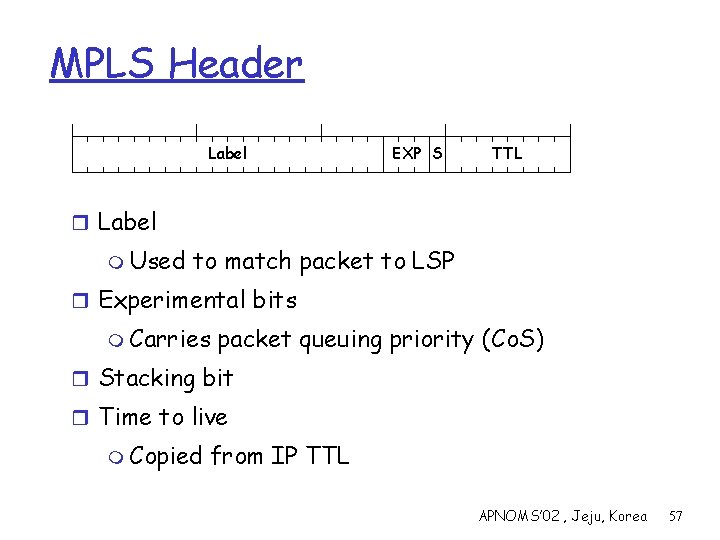
MPLS Header Label EXP S TTL r Label m Used to match packet to LSP r Experimental bits m Carries packet queuing priority (Co. S) r Stacking bit r Time to live m Copied from IP TTL APNOMS’ 02 , Jeju, Korea 57
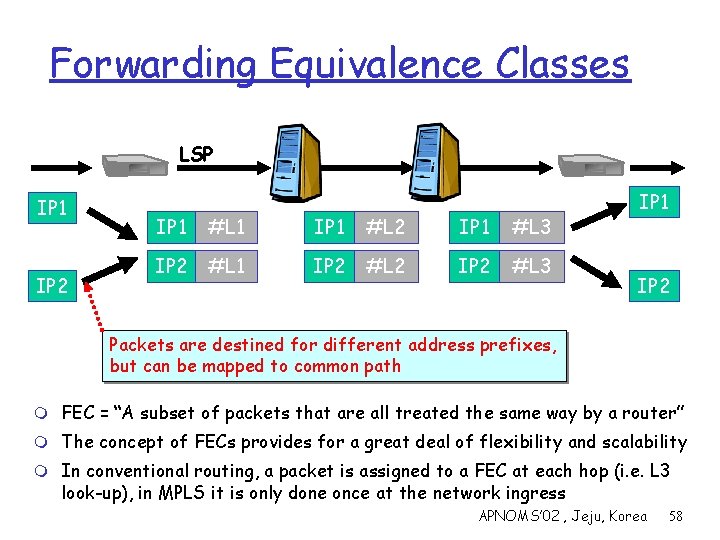
Forwarding Equivalence Classes LSP IP 1 IP 2 IP 1 #L 1 IP 1 #L 2 IP 1 #L 3 IP 2 #L 1 IP 2 #L 2 IP 2 #L 3 IP 1 IP 2 Packets are destined for different address prefixes, but can be mapped to common path m FEC = “A subset of packets that are all treated the same way by a router” m The concept of FECs provides for a great deal of flexibility and scalability m In conventional routing, a packet is assigned to a FEC at each hop (i. e. L 3 look-up), in MPLS it is only done once at the network ingress APNOMS’ 02 , Jeju, Korea 58
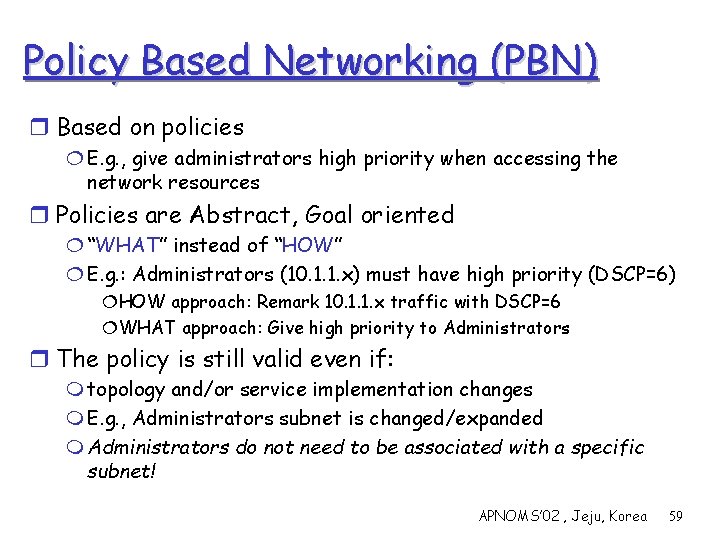
Policy Based Networking (PBN) r Based on policies ¦ E. g. , give administrators high priority when accessing the network resources r Policies are Abstract, Goal oriented ¦ “WHAT” instead of “HOW” ¦ E. g. : Administrators (10. 1. 1. x) must have high priority (DSCP=6) ¦HOW approach: Remark 10. 1. 1. x traffic with DSCP=6 ¦WHAT approach: Give high priority to Administrators r The policy is still valid even if: m topology and/or service implementation changes m E. g. , Administrators subnet is changed/expanded m Administrators do not need to be associated with a specific subnet! APNOMS’ 02 , Jeju, Korea 59
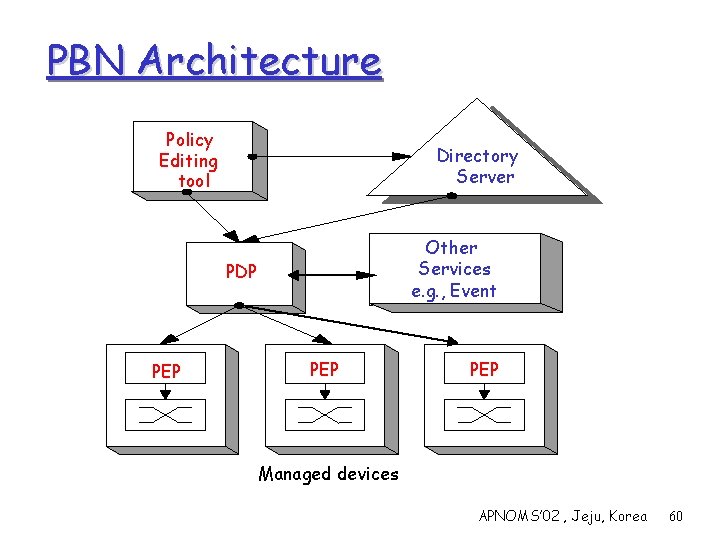
PBN Architecture Policy Editing tool Directory Server Other Services e. g. , Event PDP PEP PEP Managed devices APNOMS’ 02 , Jeju, Korea 60
![Common Open Policy Service r The COPS BASE protocol [RFC 2784] m Policy-related information Common Open Policy Service r The COPS BASE protocol [RFC 2784] m Policy-related information](http://slidetodoc.com/presentation_image/67cee8c850eabf329d29716a60283d80/image-61.jpg)
Common Open Policy Service r The COPS BASE protocol [RFC 2784] m Policy-related information exchange b/w the PDP to the PEP m Determines the behavior of the entities, as far as the communication is concerned m Does not define the semantics of the exchanged data m Does not describe HOW this data is produced by the PDP or HOW this data will be interpreted by the PEP r COPS client-types m Control different management areas (Diff. Serv, RSVP, accounting, Security, etc. ) m Each PEP implements one or more clients of various clienttypes m Client-types are defined in separate documents (standard or vendor-specific) m COPS-RSVP and COPS-PR are such clients APNOMS’ 02 , Jeju, Korea 61
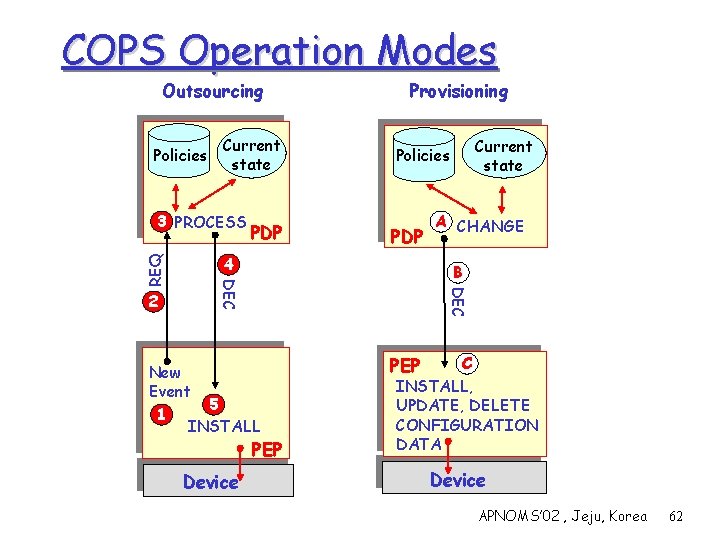
COPS Operation Modes Outsourcing Policies Current state PDP 4 B New Event 5 1 INSTALL PEP Device A CHANGE DEC 2 PDP Current state Policies DEC REQ 3 PROCESS Provisioning C INSTALL, UPDATE, DELETE CONFIGURATION DATA PEP Device APNOMS’ 02 , Jeju, Korea 62
![COPS-PR [RFC 3084] Policy Server 1. The PEP connects to the PDP, reports its COPS-PR [RFC 3084] Policy Server 1. The PEP connects to the PDP, reports its](http://slidetodoc.com/presentation_image/67cee8c850eabf329d29716a60283d80/image-63.jpg)
COPS-PR [RFC 3084] Policy Server 1. The PEP connects to the PDP, reports its capabilities/limitations and requests configuration data PDP 2. The PDP generates the initial policies according to the global policies and current network state 2 PROCESS The PDP sends initial policies 4. The PEP stores these policies in its PIB. The data in the PIB determines the behavior of the device Provisioning A. The PDP detects changes B. The PDP sends commands that add, update or delete policies in the PIB C. The PEP updates its PIB A CHANGE 3 B 1 DEC 3. Current state Policies DEC r Initialization REQ r BOOT 4 INSTALL PEP C INSTALL UPDATE, DELETE PIB Device APNOMS’ 02 , Jeju, Korea 63
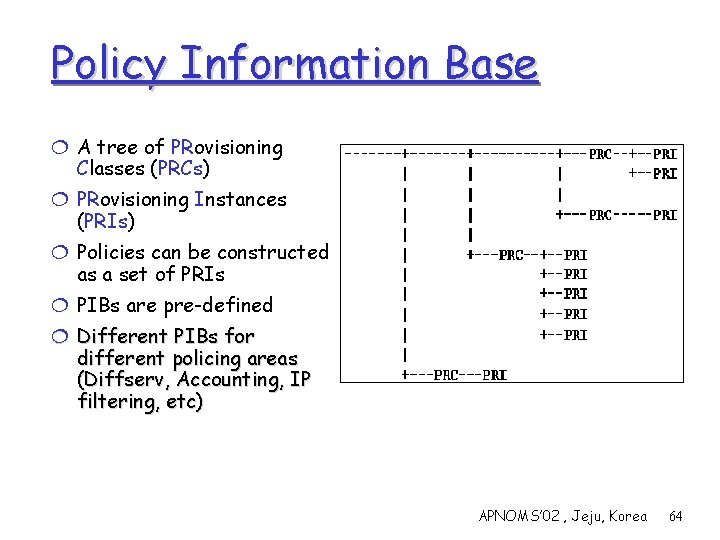
Policy Information Base ¦ A tree of PRovisioning Classes (PRCs) ¦ PRovisioning Instances (PRIs) ¦ Policies can be constructed as a set of PRIs ¦ PIBs are pre-defined ¦ Different PIBs for different policing areas (Diffserv, Accounting, IP filtering, etc) APNOMS’ 02 , Jeju, Korea 64
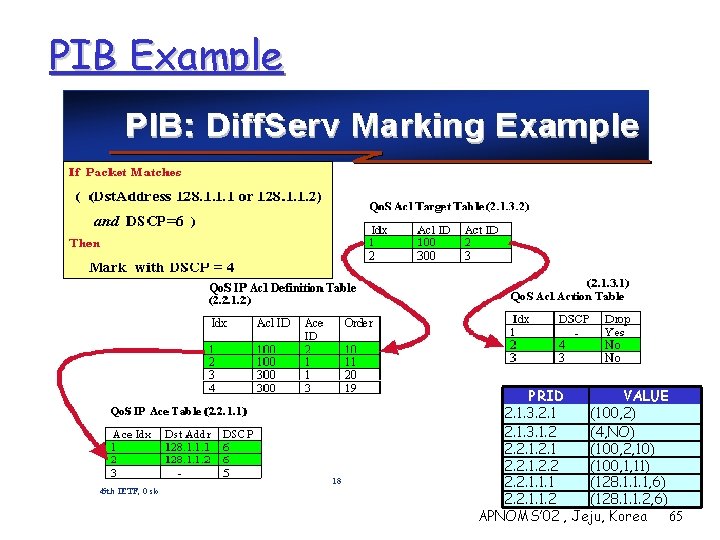
PIB Example PRID VALUE 2. 1. 3. 2. 1 (100, 2) 2. 1. 3. 1. 2 (4, NO) 2. 2. 1 (100, 2, 10) 2. 2. 1. 2. 2 (100, 1, 11) 2. 2. 1. 1. 1 (128. 1. 1. 1, 6) 2. 2. 1. 1. 2 (128. 1. 1. 2, 6) APNOMS’ 02 , Jeju, Korea 65
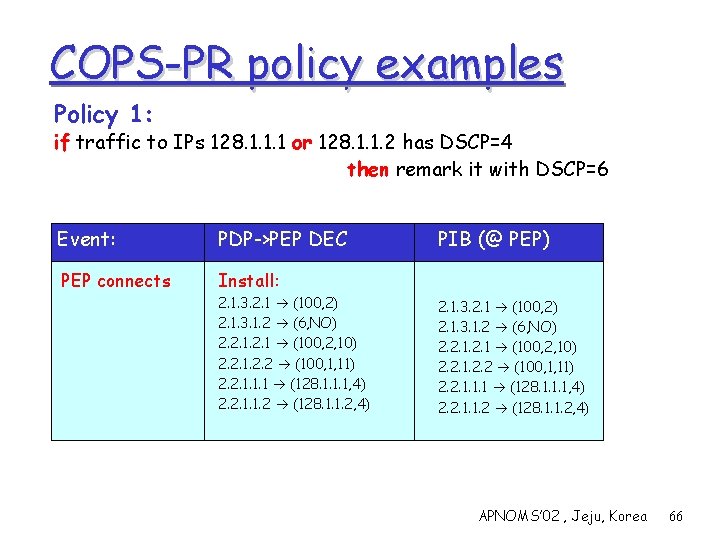
COPS-PR policy examples Policy 1: if traffic to IPs 128. 1. 1. 1 or 128. 1. 1. 2 has DSCP=4 then remark it with DSCP=6 Event: PDP->PEP DEC PEP connects Install: 2. 1. 3. 2. 1 (100, 2) 2. 1. 3. 1. 2 (6, NO) 2. 2. 1 (100, 2, 10) 2. 2. 1. 2. 2 (100, 1, 11) 2. 2. 1. 1. 1 (128. 1. 1. 1, 4) 2. 2. 1. 1. 2 (128. 1. 1. 2, 4) PIB (@ PEP) 2. 1. 3. 2. 1 (100, 2) 2. 1. 3. 1. 2 (6, NO) 2. 2. 1 (100, 2, 10) 2. 2. 1. 2. 2 (100, 1, 11) 2. 2. 1. 1. 1 (128. 1. 1. 1, 4) 2. 2. 1. 1. 2 (128. 1. 1. 2, 4) APNOMS’ 02 , Jeju, Korea 66
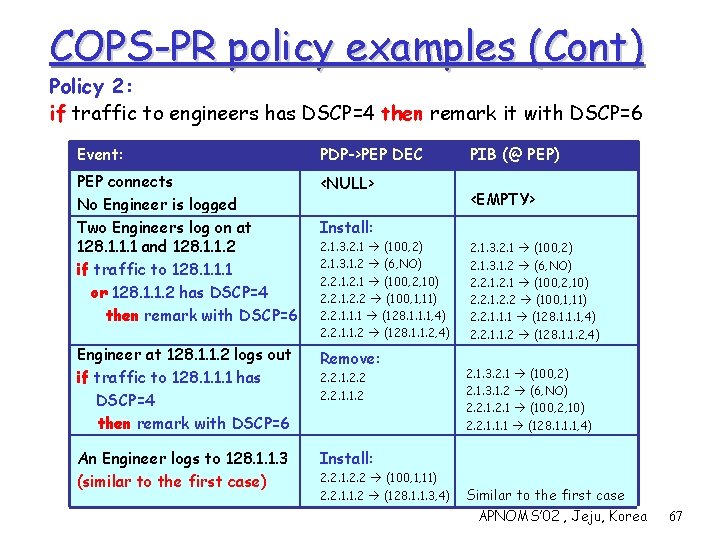
COPS-PR policy examples (Cont) Policy 2: if traffic to engineers has DSCP=4 then remark it with DSCP=6 Event: PDP->PEP DEC PEP connects No Engineer is logged Two Engineers log on at 128. 1. 1. 1 and 128. 1. 1. 2 if traffic to 128. 1. 1. 1 or 128. 1. 1. 2 has DSCP=4 then remark with DSCP=6 <NULL> Engineer at 128. 1. 1. 2 logs out if traffic to 128. 1. 1. 1 has DSCP=4 then remark with DSCP=6 Remove: An Engineer logs to 128. 1. 1. 3 (similar to the first case) Install: PIB (@ PEP) <EMPTY> Install: 2. 1. 3. 2. 1 (100, 2) 2. 1. 3. 1. 2 (6, NO) 2. 2. 1 (100, 2, 10) 2. 2. 1. 2. 2 (100, 1, 11) 2. 2. 1. 1. 1 (128. 1. 1. 1, 4) 2. 2. 1. 1. 2 (128. 1. 1. 2, 4) 2. 2. 1. 1. 2 2. 2. 1. 2. 2 (100, 1, 11) 2. 2. 1. 1. 2 (128. 1. 1. 3, 4) 2. 1. 3. 2. 1 (100, 2) 2. 1. 3. 1. 2 (6, NO) 2. 2. 1 (100, 2, 10) 2. 2. 1. 2. 2 (100, 1, 11) 2. 2. 1. 1. 1 (128. 1. 1. 1, 4) 2. 2. 1. 1. 2 (128. 1. 1. 2, 4) 2. 1. 3. 2. 1 (100, 2) 2. 1. 3. 1. 2 (6, NO) 2. 2. 1 (100, 2, 10) 2. 2. 1. 1. 1 (128. 1. 1. 1, 4) Similar to the first case APNOMS’ 02 , Jeju, Korea 67
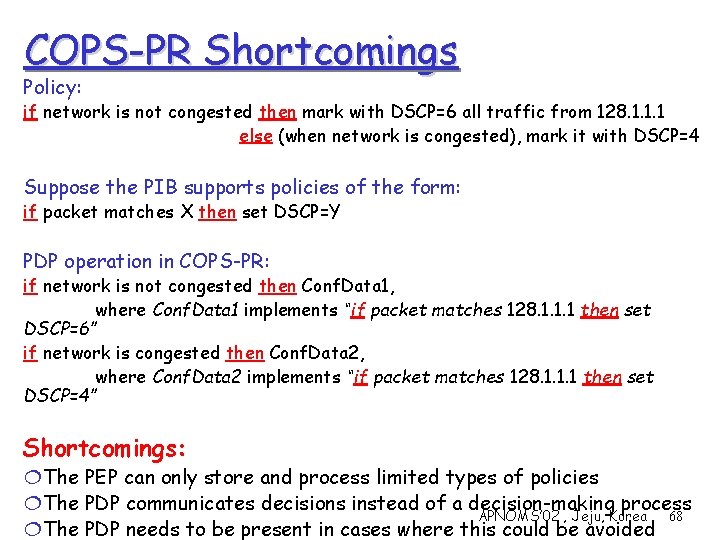
COPS-PR Shortcomings Policy: if network is not congested then mark with DSCP=6 all traffic from 128. 1. 1. 1 else (when network is congested), mark it with DSCP=4 Suppose the PIB supports policies of the form: if packet matches X then set DSCP=Y PDP operation in COPS-PR: if network is not congested then Conf. Data 1, where Conf. Data 1 implements “if packet matches 128. 1. 1. 1 then set DSCP=6” if network is congested then Conf. Data 2, where Conf. Data 2 implements “if packet matches 128. 1. 1. 1 then set DSCP=4” Shortcomings: ¦The PEP can only store and process limited types of policies ¦The PDP communicates decisions instead of a decision-making process APNOMS’ 02 , Jeju, Korea 68 ¦The PDP needs to be present in cases where this could be avoided
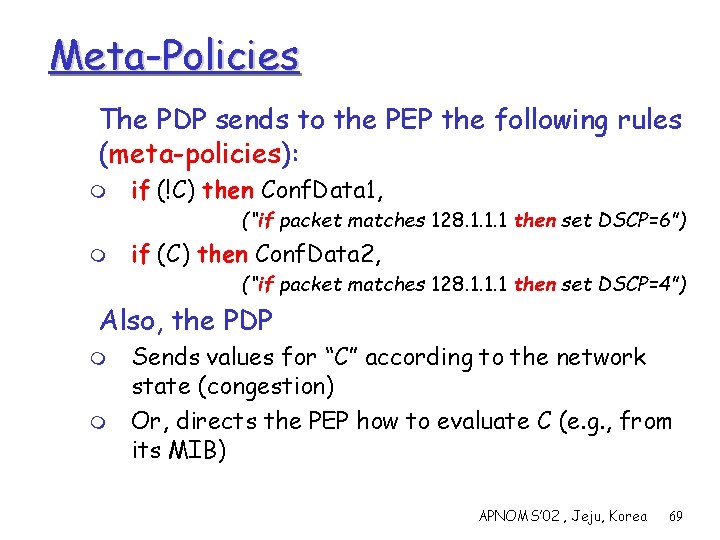
Meta-Policies The PDP sends to the PEP the following rules (meta-policies): m if (!C) then Conf. Data 1, (“if packet matches 128. 1. 1. 1 then set DSCP=6”) m if (C) then Conf. Data 2, (“if packet matches 128. 1. 1. 1 then set DSCP=4”) Also, the PDP m m Sends values for “C” according to the network state (congestion) Or, directs the PEP how to evaluate C (e. g. , from its MIB) APNOMS’ 02 , Jeju, Korea 69
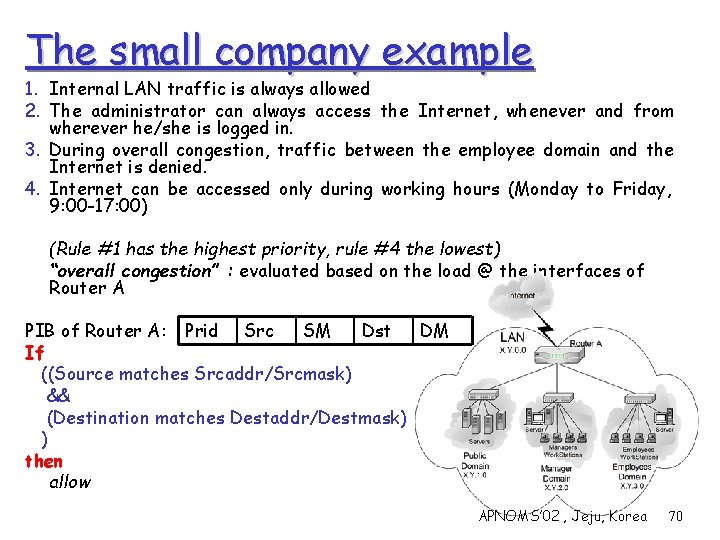
The small company example 1. Internal LAN traffic is always allowed 2. The administrator can always access the Internet, whenever and from wherever he/she is logged in. 3. During overall congestion, traffic between the employee domain and the Internet is denied. 4. Internet can be accessed only during working hours (Monday to Friday, 9: 00 -17: 00) (Rule #1 has the highest priority, rule #4 the lowest) “overall congestion” : evaluated based on the load @ the interfaces of Router A SM Dst DM PIB of Router A: Prid Src If ((Source matches Srcaddr/Srcmask) && (Destination matches Destaddr/Destmask) ) then allow APNOMS’ 02 , Jeju, Korea 70
Without Meta-policies Events 08: 59: No Admin. logged on 09: 00: Start of working day 11: 00: Congestion detected 11: 05: No congestion 15: 08: Congestion detected 15: 11: Administrator logs on at X. Y. 3. 7 15: 20: No congestion 17: 00: End of working day 17: 15: Administrator logs out APNOMS’ 02 , Jeju, Korea 71
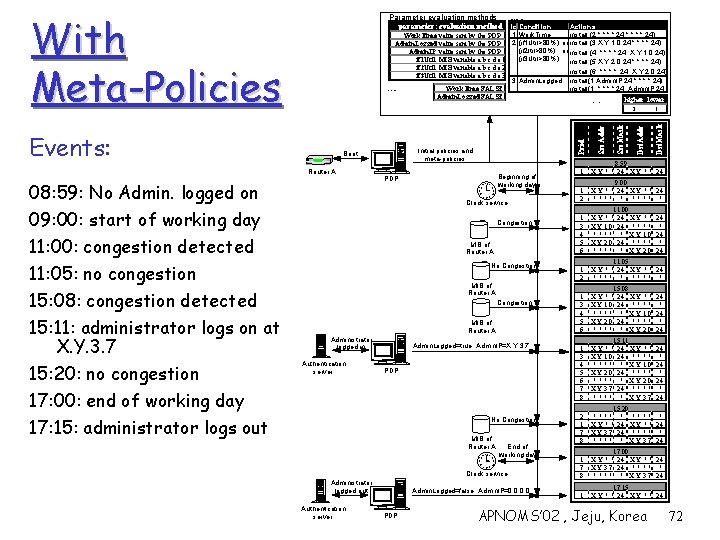
With Meta-Policies Parameter evaluation methods parameter: evaluation method id Condition Actions 1 Work. Time install (2, *. *, 24, *. *. *, *, 24) Work. Time: value sent by the PDP 2 (if 1 Util>80%) or install (3, X. Y. 1. 0, 24, *. *, 24) Admin. Logged: value sent by the PDP (if 2 Itil>80%) or install (4, *. *, 24, X. Y. 1. 0, 24) Admin. IP: value sent by the PDP (if 3 Util>80%) if 1 Util: MIB variable a. b. c. d. e 1 install (5, X. Y. 2. 0, 24, *. *, 24) if 2 Util: MIB variable a. b. c. d. e 2 install (6, *. * , 24, X. Y. 2. 0, 24) if 3 Util: MIB variable a. b. c. d. e 3 3 Admin. Logged install(1, Admin. IP, 24, *. *, 24) Work. Time: FALSE install(1, *. *, 24, Admin. IP, 24, ) Admin. Logged: FALSE higher lower Initial values conflicts PDP 1112 1 2 10 9 3 8 4 7 6 5 Beginning of working day Clock service, Congestion MIB of Router A No Congestion MIB of Router A Administrator logged in Authentication server Admin. Logged=true, Admin. IP=X. Y. 3. 7 PDP No Congestion MIB of Router A 1112 1 10 2 9 3 8 4 7 6 5 End of working day Clock service, Administrator logged out Authentication server Admin. Logged=false, Admin. IP=0. 0 PDP 1 Dst. Mask Dst. Addr Src. Mask Src. Addr Initial policies and meta-policies Boot Router A Prid 2 Events: 08: 59: No Admin. logged on 09: 00: start of working day 11: 00: congestion detected 11: 05: no congestion 15: 08: congestion detected 15: 11: administrator logs on at X. Y. 3. 7 15: 20: no congestion 17: 00: end of working day 17: 15: administrator logs out Meta-Policies 1 8: 59 X. Y. *. * 24 1 2 9: 00 X. Y. *. * 24 *. * * 1 3 4 5 6 11: 00 X. Y. *. * 24 X. Y. *. * X. Y. 1. 0 24 *. * * X. Y. 1. 0 X. Y. 2. 0 24 *. * * X. Y. 2. 0 1 2 11: 05 X. Y. *. * 24 *. * * 1 3 4 5 6 15: 08 X. Y. *. * 24 X. Y. *. * X. Y. 1. 0 24 *. * * X. Y. 1. 0 X. Y. 2. 0 24 *. * * X. Y. 2. 0 24 * 24 1 3 4 5 6 7 8 15: 11 X. Y. *. * 24 X. Y. *. * X. Y. 1. 0 24 *. * * X. Y. 1. 0 X. Y. 2. 0 24 *. * * X. Y. 2. 0 X. Y. 3. 7 24 *. * * X. Y. 3. 7 24 * 24 2 1 7 8 15: 20 *. * * *. * X. Y. *. * 24 X. Y. *. * X. Y. 3. 7 24 *. * * X. Y. 3. 7 * 24 1 7 8 17: 00 X. Y. *. * 24 X. Y. 3. 7 24 *. * * X. Y. 3. 7 24 1 17: 15 X. Y. *. * 24 APNOMS’ 02 , Jeju, Korea 24 * 24 72
Meta-Policies: Formal Definition if (Condition) then {Actions} r Actions: m pre-generated COPS-PR commands m may contain parameters r Condition: m a logical expression (encoded in a predefined way, e. g. , according to an XML DTD) m contains parameters r The PDP directs the PEP how to evaluate the parameters m m m MIB Value sent by the PDP Other (download script or code, LDAP, …) APNOMS’ 02 , Jeju, Korea 73
The Meta-Policy PIB PRCs APNOMS’ 02 , Jeju, Korea 74
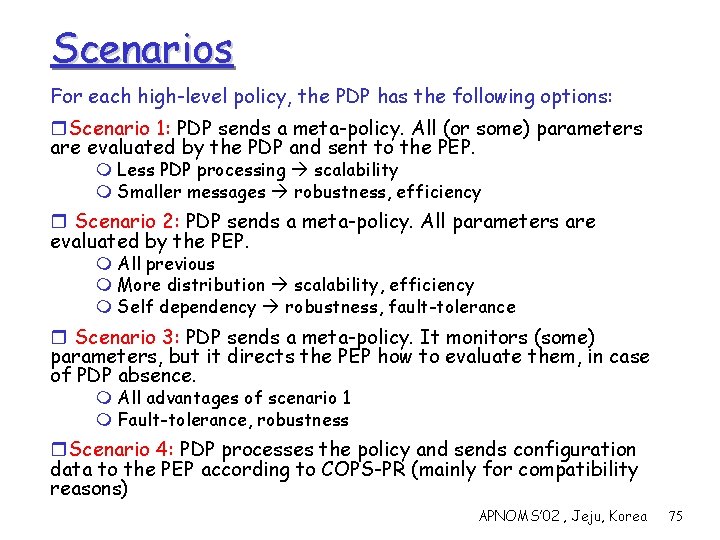
Scenarios For each high-level policy, the PDP has the following options: r. Scenario 1: PDP sends a meta-policy. All (or some) parameters are evaluated by the PDP and sent to the PEP. m Less PDP processing scalability m Smaller messages robustness, efficiency r Scenario 2: PDP sends a meta-policy. All parameters are evaluated by the PEP. m All previous m More distribution scalability, efficiency m Self dependency robustness, fault-tolerance r Scenario 3: PDP sends a meta-policy. It monitors (some) parameters, but it directs the PEP how to evaluate them, in case of PDP absence. m All advantages of scenario 1 m Fault-tolerance, robustness r. Scenario 4: PDP processes the policy and sends configuration data to the PEP according to COPS-PR (mainly for compatibility reasons) APNOMS’ 02 , Jeju, Korea 75
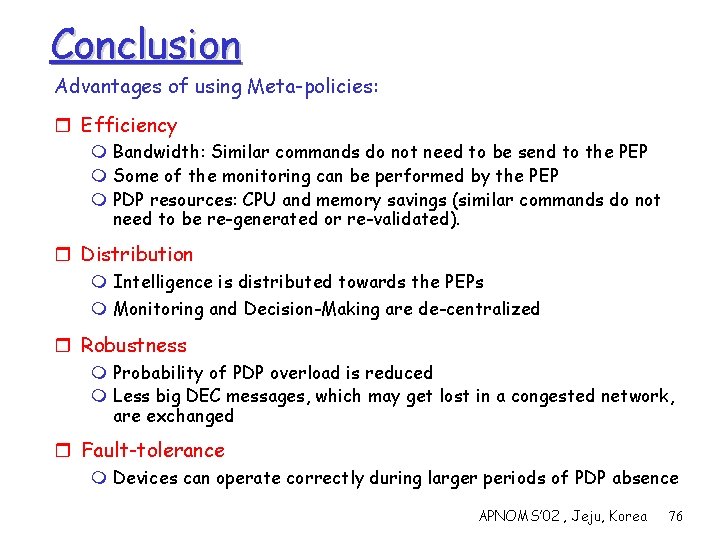
Conclusion Advantages of using Meta-policies: r Efficiency m Bandwidth: Similar commands do not need to be send to the PEP m Some of the monitoring can be performed by the PEP m PDP resources: CPU and memory savings (similar commands do not need to be re-generated or re-validated). r Distribution m Intelligence is distributed towards the PEPs m Monitoring and Decision-Making are de-centralized r Robustness m Probability of PDP overload is reduced m Less big DEC messages, which may get lost in a congested network, are exchanged r Fault-tolerance m Devices can operate correctly during larger periods of PDP absence APNOMS’ 02 , Jeju, Korea 76
Conclusion (Cont) Tradeoff: Additional functionality increased complexity r PDP: More complex algorithms m However, the PDP is already complex r PEP: Increased CPU & memory requirements m The PDP may decide to send only a small number of selected meta-policies that will not overload the devices but they will increase the overall efficiency significantly m The backwards compatibility allows PEPs not to implement the extra functionality (no meta-policies) APNOMS’ 02 , Jeju, Korea 77
References q Open Source ¦ The Meta-Policy Information Base, http: //sourceforge. net/projects/metapib/ q Internet Drafts ¦ A. Polyrakis and R. Boutaba, The Meta-Policy PIB, Internet Draft, IETF, http: //www. ietf. org/internet-drafts/draft-polirakis-mpib 00. txt. ¦ R. Boutaba and A. Polyrakis, COPS-PR-MP, Internet Draft, IETF, http: //www. ietf. org/internet-drafts/draft-boutaba-copsprmp-00. txt q Publications ¦ A. Polyrakis and R. Boutaba, The Meta-Policy Information Base, IEEE Network Magazine, special issue on Policy-based Networking, Vol. 16, No. 2, pp. 40 -48 2002. ¦ R. Boutaba and A. Polyrakis, Extending COPS-PR with Meta-policies for Scalable management of IP Networks, Journal of Network and Systems Management, special issue on Management of Converged Networks, Vol. 10, No. 1, March 2002 ¦ R. Boutaba, A. Polirakis, Towards Extensible Policy Enforcement Points, IEEE Policy Workshop (Policy’ 01), pp. 247 -261, 2001. APNOMS’ 02 , Jeju, Korea 78
- Slides: 78