Publickey encryption Symmetrickey encryption Invertible function Security depends
Public-key encryption
Symmetric-key encryption • Invertible function • Security depends on the shared secret – a particular key. • Fast, highly secure • Fine for repeated communication • Poor fit for one-shot communication, signatures
Asymmetric-key (public key) encryption • The basic idea: • A user has two keys: a public key and a private key. • A message can be encrypted with the public key and decrypted with the private key to provide security. • A message can be encrypted with the private key and decrypted with the public key to provide signatures.
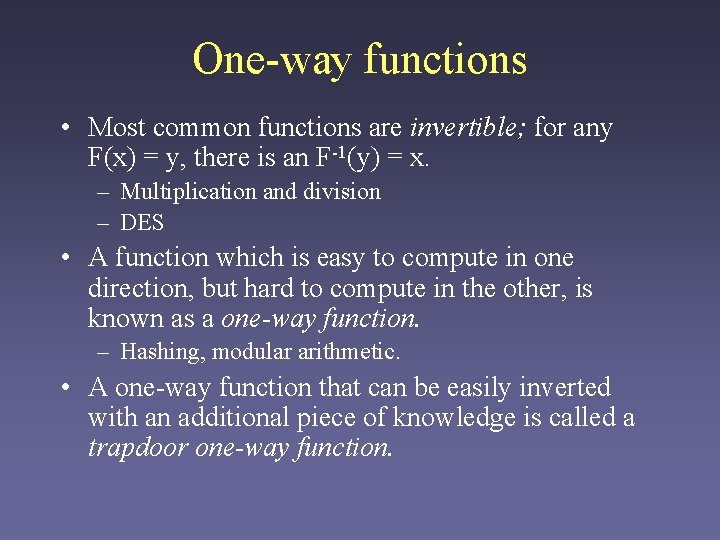
One-way functions • Most common functions are invertible; for any F(x) = y, there is an F-1(y) = x. – Multiplication and division – DES • A function which is easy to compute in one direction, but hard to compute in the other, is known as a one-way function. – Hashing, modular arithmetic. • A one-way function that can be easily inverted with an additional piece of knowledge is called a trapdoor one-way function.
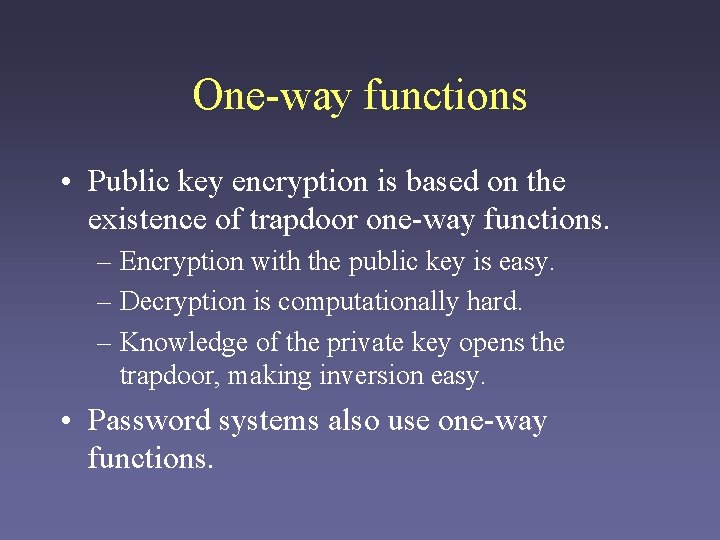
One-way functions • Public key encryption is based on the existence of trapdoor one-way functions. – Encryption with the public key is easy. – Decryption is computationally hard. – Knowledge of the private key opens the trapdoor, making inversion easy. • Password systems also use one-way functions.
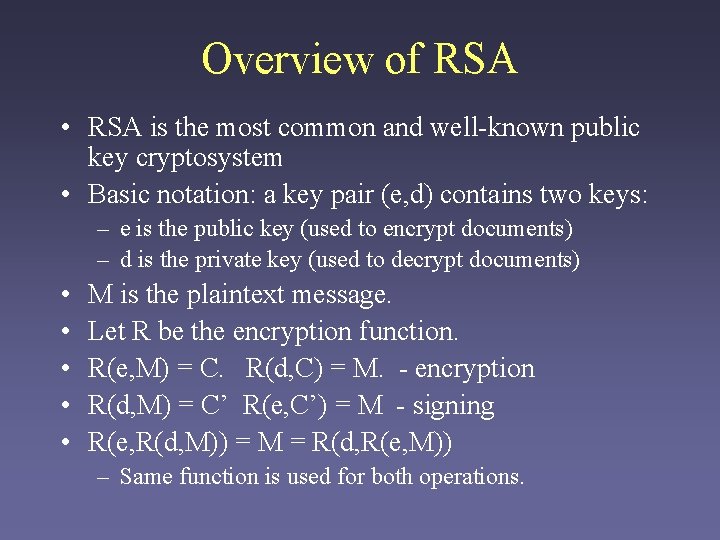
Overview of RSA • RSA is the most common and well-known public key cryptosystem • Basic notation: a key pair (e, d) contains two keys: – e is the public key (used to encrypt documents) – d is the private key (used to decrypt documents) • • • M is the plaintext message. Let R be the encryption function. R(e, M) = C. R(d, C) = M. - encryption R(d, M) = C’ R(e, C’) = M - signing R(e, R(d, M)) = M = R(d, R(e, M)) – Same function is used for both operations.
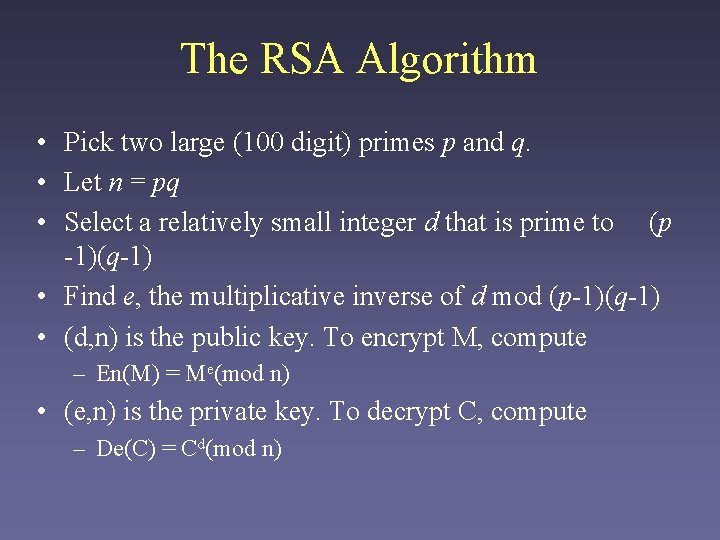
The RSA Algorithm • Pick two large (100 digit) primes p and q. • Let n = pq • Select a relatively small integer d that is prime to (p -1)(q-1) • Find e, the multiplicative inverse of d mod (p-1)(q-1) • (d, n) is the public key. To encrypt M, compute – En(M) = Me(mod n) • (e, n) is the private key. To decrypt C, compute – De(C) = Cd(mod n)
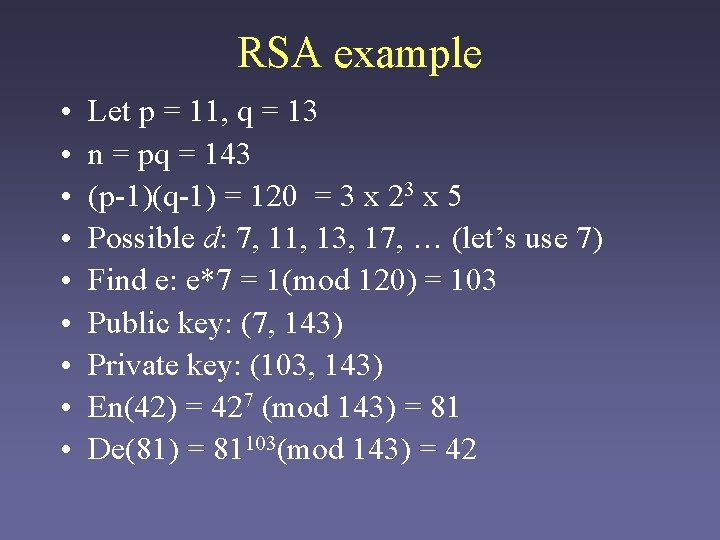
RSA example • • • Let p = 11, q = 13 n = pq = 143 (p-1)(q-1) = 120 = 3 x 23 x 5 Possible d: 7, 11, 13, 17, … (let’s use 7) Find e: e*7 = 1(mod 120) = 103 Public key: (7, 143) Private key: (103, 143) En(42) = 427 (mod 143) = 81 De(81) = 81103(mod 143) = 42
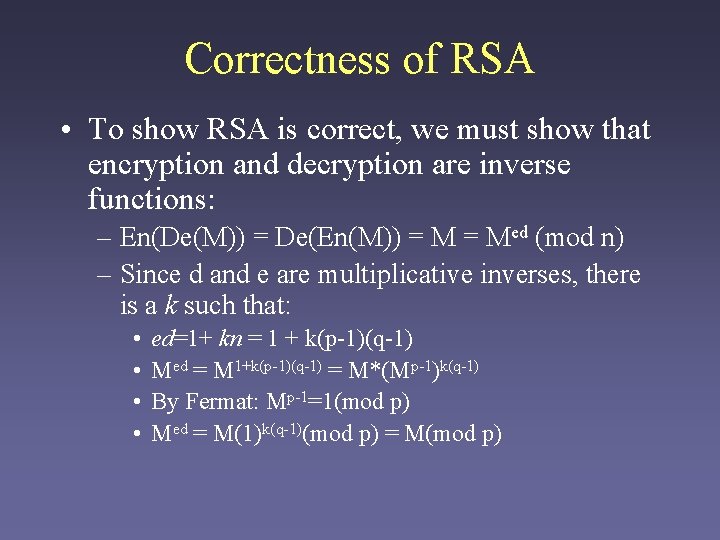
Correctness of RSA • To show RSA is correct, we must show that encryption and decryption are inverse functions: – En(De(M)) = De(En(M)) = Med (mod n) – Since d and e are multiplicative inverses, there is a k such that: • • ed=1+ kn = 1 + k(p-1)(q-1) Med = M 1+k(p-1)(q-1) = M*(Mp-1)k(q-1) By Fermat: Mp-1=1(mod p) Med = M(1)k(q-1)(mod p) = M(mod p)
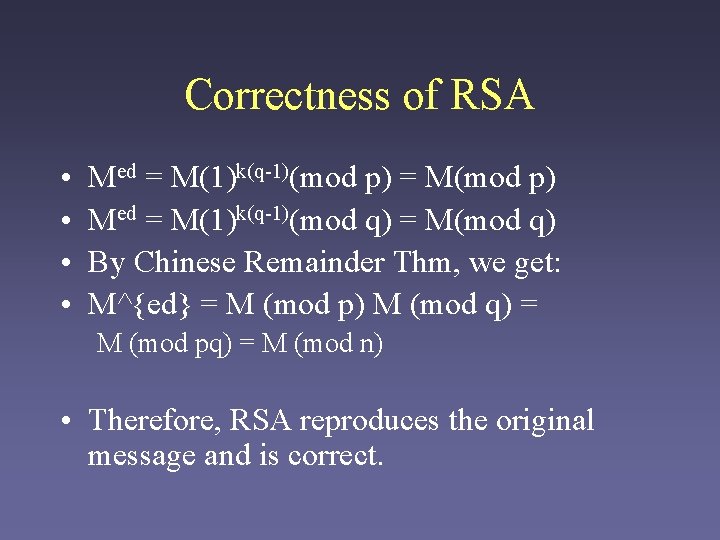
Correctness of RSA • • Med = M(1)k(q-1)(mod p) = M(mod p) Med = M(1)k(q-1)(mod q) = M(mod q) By Chinese Remainder Thm, we get: M^{ed} = M (mod p) M (mod q) = M (mod pq) = M (mod n) • Therefore, RSA reproduces the original message and is correct.
Strengths of RSA • • No prior communication needed Highly secure (for large enough keys) Well-understood Allows both encryption and signing
Weaknesses of RSA • Large keys needed (1024 bits is current standard) • Relatively slow – Not suitable for very large messages • Public keys must still be distributed safely.
Security of RSA • The security of RSA is dependent on the assumption that it’s difficult to generate the private key d from the public key e and the modulus n. • Equivalent to integer factorization problem. – This is how we got e and d in the first place. • Factoring is thought to be computationally hard. – No proof, though!
- Slides: 13