Public Policy From Legal Issues to Privacy Legal
Public Policy: From Legal Issues to Privacy
Legal and Ethical Issues: an Overview • • • Privacy Intellectual Property Free Speech Taxation Consumer Protection
Ethical Issues • What is considered to be right and wrong? • Unethical is not necessarily illegal. • Being unethical depends on the organization, country, and the specific circumstances surrounding the scenarios.
Code of Ethics • A collection of principles intended as a guide for its members • A guide for members of a company or an association
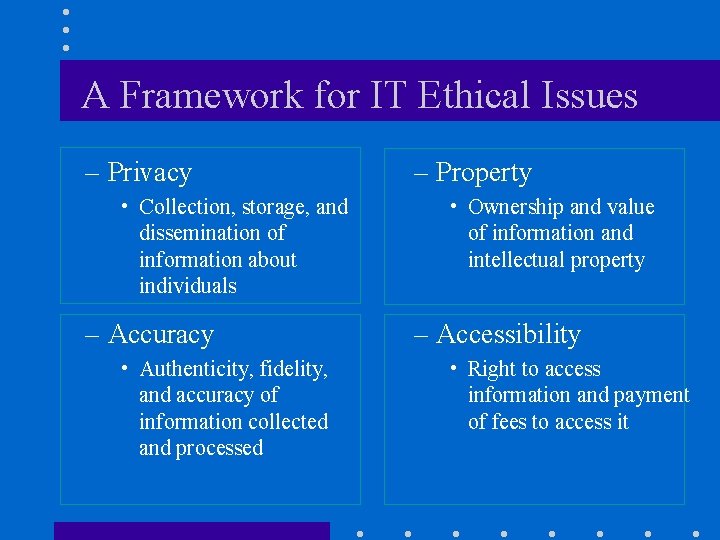
A Framework for IT Ethical Issues – Privacy • Collection, storage, and dissemination of information about individuals – Accuracy • Authenticity, fidelity, and accuracy of information collected and processed – Property • Ownership and value of information and intellectual property – Accessibility • Right to access information and payment of fees to access it
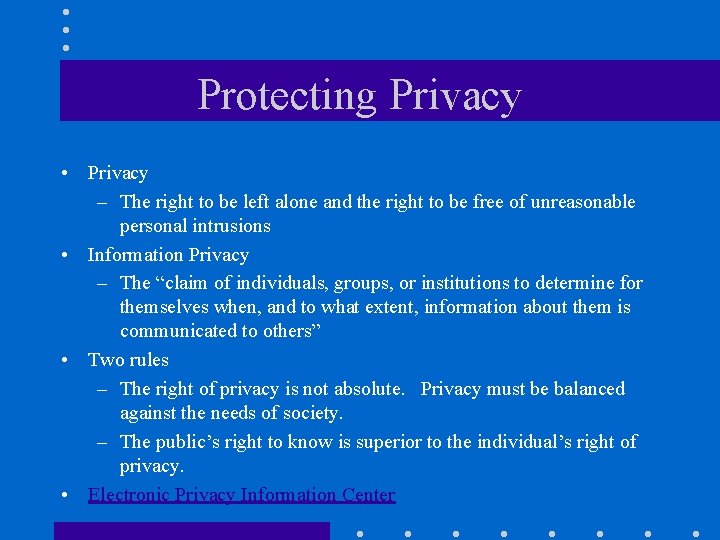
Protecting Privacy • Privacy – The right to be left alone and the right to be free of unreasonable personal intrusions • Information Privacy – The “claim of individuals, groups, or institutions to determine for themselves when, and to what extent, information about them is communicated to others” • Two rules – The right of privacy is not absolute. Privacy must be balanced against the needs of society. – The public’s right to know is superior to the individual’s right of privacy. • Electronic Privacy Information Center
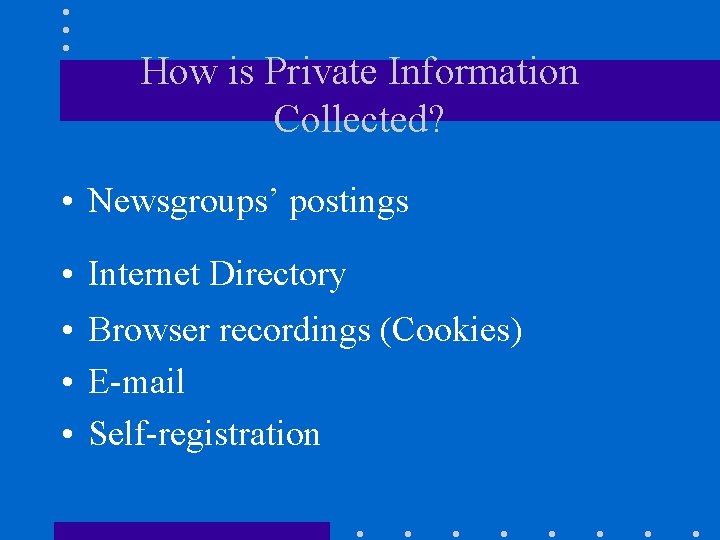
How is Private Information Collected? • Newsgroups’ postings • Internet Directory • Browser recordings (Cookies) • E-mail • Self-registration

Cookies • Reasons for using cookies – – – to personalize information to improve online sales/services to simplify tracking of popular links or demographics to keep sites fresh and relevant to the user’s interests to enable subscribers to log in without having to enter a password every visit – to keep track of a customer’s search preferences – personal profiles created are more accurate than self-registration • Solutions to cookies – users can delete cookie files stored in their computer – use of anti-cookie software
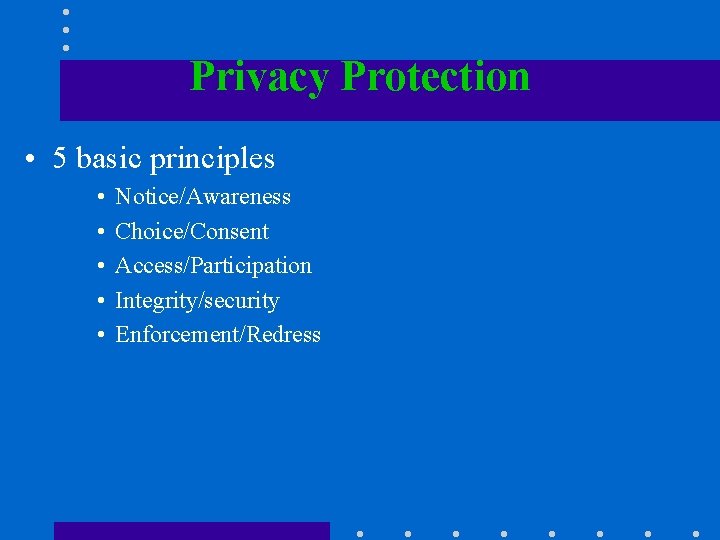
Privacy Protection • 5 basic principles • • • Notice/Awareness Choice/Consent Access/Participation Integrity/security Enforcement/Redress
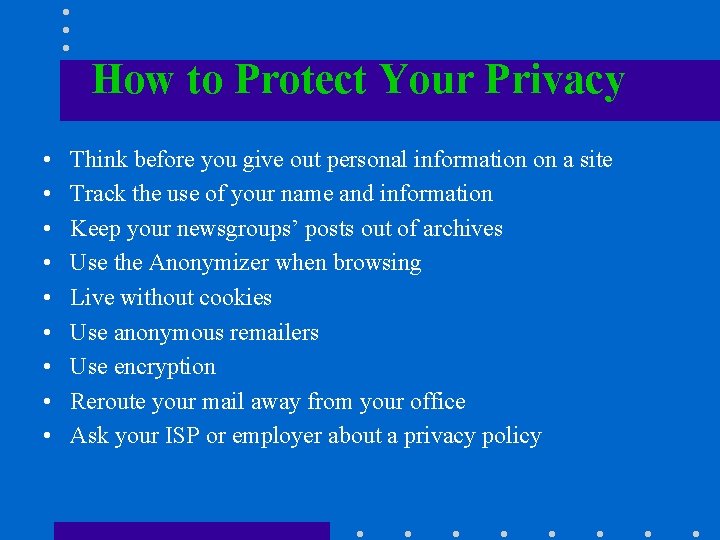
How to Protect Your Privacy • • • Think before you give out personal information on a site Track the use of your name and information Keep your newsgroups’ posts out of archives Use the Anonymizer when browsing Live without cookies Use anonymous remailers Use encryption Reroute your mail away from your office Ask your ISP or employer about a privacy policy
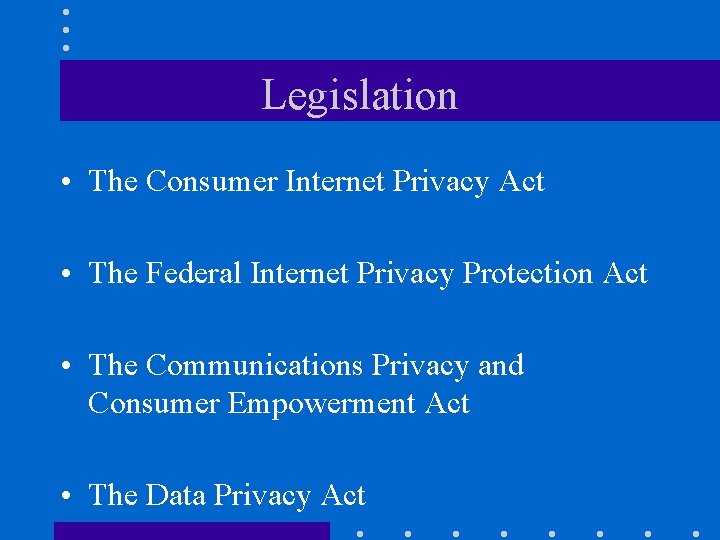
Legislation • The Consumer Internet Privacy Act • The Federal Internet Privacy Protection Act • The Communications Privacy and Consumer Empowerment Act • The Data Privacy Act
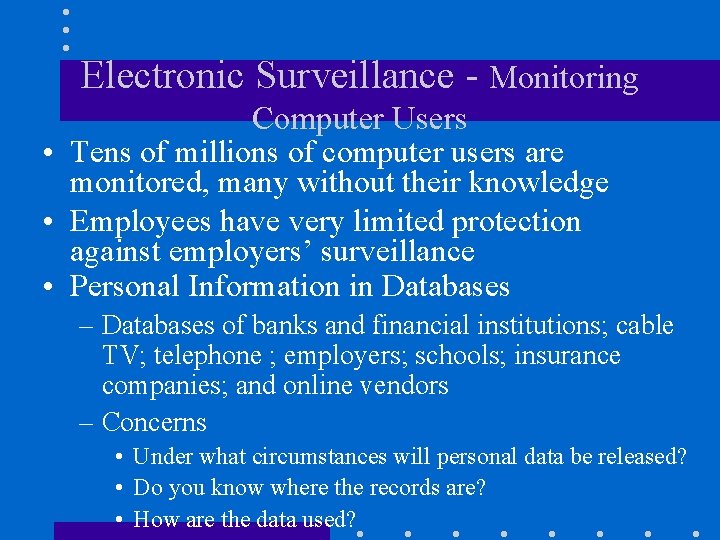
Electronic Surveillance - Monitoring Computer Users • Tens of millions of computer users are monitored, many without their knowledge • Employees have very limited protection against employers’ surveillance • Personal Information in Databases – Databases of banks and financial institutions; cable TV; telephone ; employers; schools; insurance companies; and online vendors – Concerns • Under what circumstances will personal data be released? • Do you know where the records are? • How are the data used?
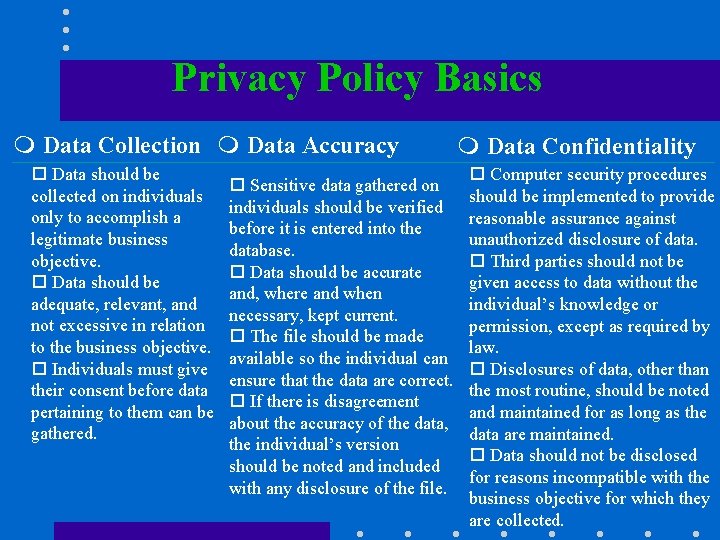
Privacy Policy Basics m Data Collection m Data Accuracy o Data should be collected on individuals only to accomplish a legitimate business objective. o Data should be adequate, relevant, and not excessive in relation to the business objective. o Individuals must give their consent before data pertaining to them can be gathered. o Sensitive data gathered on individuals should be verified before it is entered into the database. o Data should be accurate and, where and when necessary, kept current. o The file should be made available so the individual can ensure that the data are correct. o If there is disagreement about the accuracy of the data, the individual’s version should be noted and included with any disclosure of the file. m Data Confidentiality o Computer security procedures should be implemented to provide reasonable assurance against unauthorized disclosure of data. o Third parties should not be given access to data without the individual’s knowledge or permission, except as required by law. o Disclosures of data, other than the most routine, should be noted and maintained for as long as the data are maintained. o Data should not be disclosed for reasons incompatible with the business objective for which they are collected.
Intellectual Property • Copyright – A statutory grant that provides the creators of intellectual property with ownership of it for 28 years • Trade Secret – Intellectual work such as a business plan, which is a company secret and is not based on public information • Patent – A document that grants the holder exclusive rights on an invention for 17 years
Copyright Protection Techniques • Digital watermarks • embedding of invisible marks • can be represented by bits in digital content • hidden in the source data, becoming inseparable from such data
Intellectual Property Protection Acts • Electronic Theft (NET) Act – imposes criminal liability for individuals who reproduce or distribute copies of copyrighted works even if no commercial advantage or financial gain exists • Digital Copyright Clarification and Technology Education Act – limits the scope of digital copyright infringement by allowing distance learning exemptions • Online Copyright Liability Limitation Act – seeks to protect Internet access providers from liability for direct and vicarious liability under specific circumstances where they have no control or knowledge of infringement
Intellectual Property Protection Acts (continued) • Digital Millennium Copyright Act – reasserts copyright in cyberspace – makes illegal most attempts to defeat anti-copying technology – requires the National Telecommunications and Information Administration to review the effect the bill would have on the free flow of information and makes recommendations for any changes two years after it is signed into law – lets companies and common citizens circumvent anti-copying technology when necessary to make software or hardware compatible with other products, to conduct encryption research or to keep personal information from being spread via Internet “cookies” or other copy-protection tools – forbids excessive copying of databases, even when those databases contain information already in the public domain
International Aspects of Intellectual Property • The World Intellectual Property Organization – more than 60 member countries to come up with an international treaty – part of the agreement is called the ‘database treaty’ – its aim is to protect the investment of firms that collect and arrange information
Domain Names • Two controversies · Whether top-level domain names (similar to com, org and gov) should be added · The use of trademark names by companies for domain names that belong to other companies • Network Solutions Inc. • Contracted by the government to assign domain addresses
The Debate about Free Speech on the Internet • Free speech debate “Most citizens are implacably opposed to censorship in any form — except censorship of whatever they personally happen to find offensive. ” • What the boundaries are, and how they should be enforced Governments protective of their role in society, parents concerned about exposing their children to inappropriate Web pages and chat rooms, and federal agencies attempting to deal with illegal actions Citizen action groups desiring to protect every ounce of their freedom to speak, individuals concerned about their right to information on the Internet, and organizations seeking to empower the citizens of the earth
The Debate about Free Speech on the Internet (cont. ) – Provisions in law for 2 cases that limit free speech • obscene material • compelling government interest – “Indecency” – “any comment, request, suggestion, proposal, image, or other communication that, in context, depicts or describes, in terms patently offensive as measured by contemporary community standards, sexual or excretory activities or organs”
Protecting Children • 3 approaches – No information should be held back and parents should be responsible for monitoring their own children – The government is the only one who can truly protect children from this material – To hold the Internet providers responsible for all the material and information they provide
Legal Perspectives in the USA • • • Child Online Protection Act Internet Tax Freedom Act Family Friendly Internet Access Act Internet Protection Act Internet School Filtering Act
Spamming • What is spamming, why is it bad? – Spamming – “the practice of indiscriminate distribution of messages (for example junk mail) without permission of the receiver and without consideration for the messages’ appropriateness” – Spamming’s negative impacts • slowing the Internet in general • shutting ISPs down completely
Controlling Spamming • Legislation, Legal – – The Electronic Mailbox Protection Act The Unsolicited Commercial Electronic Mail Act The Netizens Protection Act The Telephone Consumer Protection Act • How to cut spamming – Tell users not to validate their addresses by answering spam requests for replies if they want to be taken off mailing lists – Disable the relay feature on SMTP (mail) servers so mail cannot be bounced off the server – Delete spam and forget it – Use software packages, e. g. www. getlost. com and www. junkbusters. com
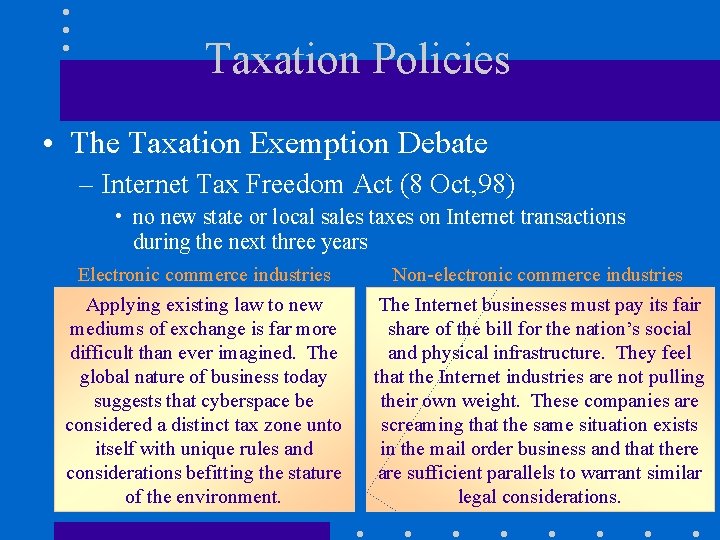
Taxation Policies • The Taxation Exemption Debate – Internet Tax Freedom Act (8 Oct, 98) • no new state or local sales taxes on Internet transactions during the next three years Electronic commerce industries Applying existing law to new mediums of exchange is far more difficult than ever imagined. The global nature of business today suggests that cyberspace be considered a distinct tax zone unto itself with unique rules and considerations befitting the stature of the environment. Non-electronic commerce industries The Internet businesses must pay its fair share of the bill for the nation’s social and physical infrastructure. They feel that the Internet industries are not pulling their own weight. These companies are screaming that the same situation exists in the mail order business and that there are sufficient parallels to warrant similar legal considerations.
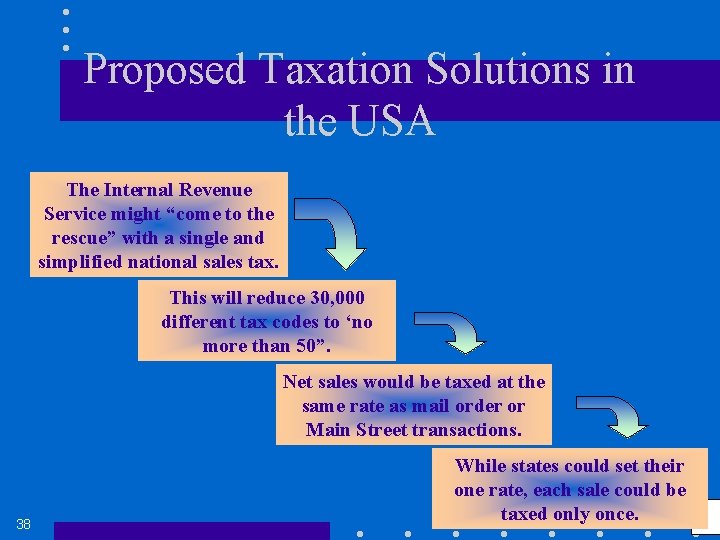
Proposed Taxation Solutions in the USA The Internal Revenue Service might “come to the rescue” with a single and simplified national sales tax. This will reduce 30, 000 different tax codes to ‘no more than 50”. Net sales would be taxed at the same rate as mail order or Main Street transactions. 38 While states could set their one rate, each sale could be taxed only once.
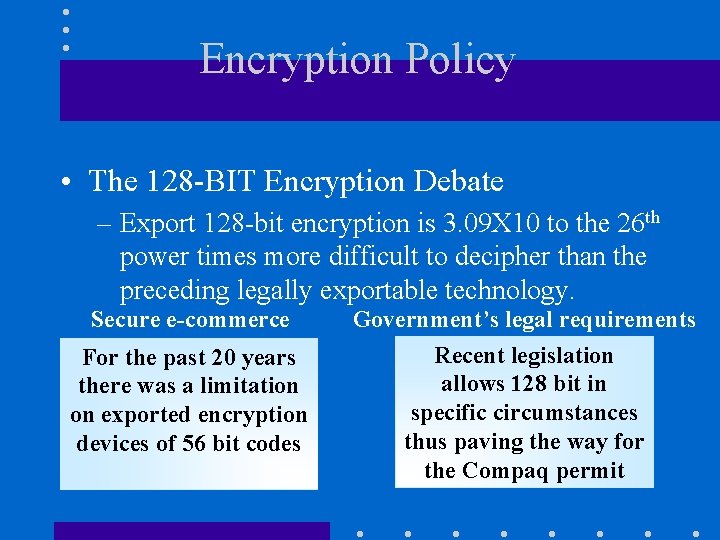
Encryption Policy • The 128 -BIT Encryption Debate – Export 128 -bit encryption is 3. 09 X 10 to the 26 th power times more difficult to decipher than the preceding legally exportable technology. Secure e-commerce For the past 20 years there was a limitation on exported encryption devices of 56 bit codes Government’s legal requirements Recent legislation allows 128 bit in specific circumstances thus paving the way for the Compaq permit
Encryption Policy (cont. ) • Data Encryption Standard (DES) – A published federal encryption standard created to protect unclassified computer data and communications – Law Enforcement’s Plea • Cryptographers would follow an audit trail to ensure that keys haven’t been released improperly, however, law enforcement does not trust that process – First Amendment Right • Technology can encrypt so thoroughly, that every computer on earth, working in tandem, would take trillions of years to decode the encryption – Business View • EFF (Electronic Frontier Foundation) believes that software, networked communications and cryptography
Other Legal Issues • What are the rules of electronic contracting, and whose jurisdiction prevails when buyers, brokers, and sellers are in different states and/or countries? • How can gambling be controlled on the Internet? Gambling is legal in Nevada and other states. How can the winner’s tax be collected? • When are electronic documents admissible evidence in the courts of law? What do you do if they are not? • Time and place can carry different dates for the buyers and sellers when they are across the ocean. • Is a digital signature legal? • The use of multiple networks and trading partners makes the documentation of responsibility difficult. How is such a problem overcome?
Electronic Contracts • Uniform Electronic Transactions Act – Provides the means to effectuate transactions accomplished through an electronic medium • Uniform Commercial Code (UCC) – Provides a government code that supports existing and future electronic technologies in the exchange of goods or of services related to exchange of goods
Electronic Contracts (cont. ) • Shrink-wrap agreements (or box top licenses) – The user is bound to the license by opening the package å This has been a point of contention for some time å The court felt that more information would provide more benefit to the consumer given the limited space available on the exterior of the package • Click-wrap contracts – The software vendor offers to sell or license the use of the software according to the terms accompanying the software – The buyer agrees to be bound by the terms based on certain conduct
Fraud on the Internet • Online Auction Fraud • Internet Stocks Fraud • Other Financial Fraud – Selling bogus investments, phantom business opportunities, and other fraud schemes • Other Fraud in EC – Customers may • receive poor quality products and services • not get products in time

Federal Trade Commission (FTC) Consumer Alerts The “Dirty Dozen” • • Business opportunities Bulk mail solicitors Investment opportunities Work-at-home schemes Health and diet schemes Effortless income Guaranteed loans or credit, on easy terms • • • Free goods Chain letters Cable descrambler kits Credit repair Vacation prize promotion
Buyer Protection • Tips for safe electronic shopping – Look for reliable brand names at sites. – Search any unfamiliar site for address and phone and fax number. Call up and quiz a person about the sellers. – Check the seller with the local Chamber of Commerce, Better Business Bureau, or TRUSTe as described later. – Investigate how secure the seller’s site is and how well it is organized.
Buyer Protection – Examine the money-back guarantees, warranties, and service agreements. – Compare prices to those in regular stores; toolow prices may be too good to be true. – Ask friends what they know. Find testimonials and endorsements. – Find out what you can do in case of a dispute. – Consult the National Fraud Information Center. – Check www. consumerworld. org – Do not forget the you have shopper’s rights.
Third Party Service • Public organizations and private companies attempt to protect consumers – TRUSTe’s “Trustmark” • non-profit group • to build user’s trust and confidence in the Internet by promoting the polices of disclosure and informed consent – BBB (Better Business Bureau) • private non-profit organizations supported largely by membership • to provide reports on business firms that are helpful to consumers before making a purchase
Authentication • If authentication can be solved …. . – students will be able to take exams online – fraud of recipients of government entitlements and other payments will be reduced to a bare minimum – buyers will be assured who the sellers are and sellers will know who the buyers are with a very high degree of confidence – arrangements will be made so that only authorized people in companies can place purchasing orders – interviews for employment, possible marriage, and other matching applications will be accurate – trust in your partners and in EC in general will
Biometrics Controls • • Photo of face Fingerprints Hand geometry Blood vessel pattern in the retina of a person’s eye • Voice • Signature. y h Cat • Keystroke dynamics
Seller Protection • Sellers must be protected against: – Use of their names by others – Use of their unique words and phrases, names, and slogans and their web addresses – Dealing with customers that deny that they placed an order – Several other potential legal issues are related to sellers’ protection – Customers downloading copyrighted software and/or knowledge and selling it to others
Managerial Issues • Multinational corporations face different cultures in the different countries in which they are doing business • Issues of privacy, ethics, and so on may seem to be tangential to running a business, but ignoring them may hinder the operation of many organizations • The impact of electronic commerce and the Internet can be so strong that the entire manner in which companies do business will be changed, with significant impacts on procedures, people, organizational structure, management, and business processes
- Slides: 41