Public Key Infrastructure X 509 PKI Marco Casassa
Public Key Infrastructure (X 509 PKI) Marco Casassa Mont Trusted E-Services Laboratory - HP Labs - Bristol Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK
Outline • Basic Problem of Confidence and Trust • Background: Cryptography, Digital Signature, Digital Certificates • (X 509) Public Key Infrastructure (PKI) • (X 509) PKI: Trust and Legal Issues Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK
Confidence and Trust Issues in the Digital World Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK
Basic Problem Bob Intranet Extranet Internet Alice Bob and Alice want to exchange data in a digital world. There are Confidence and Trust Issues … Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK
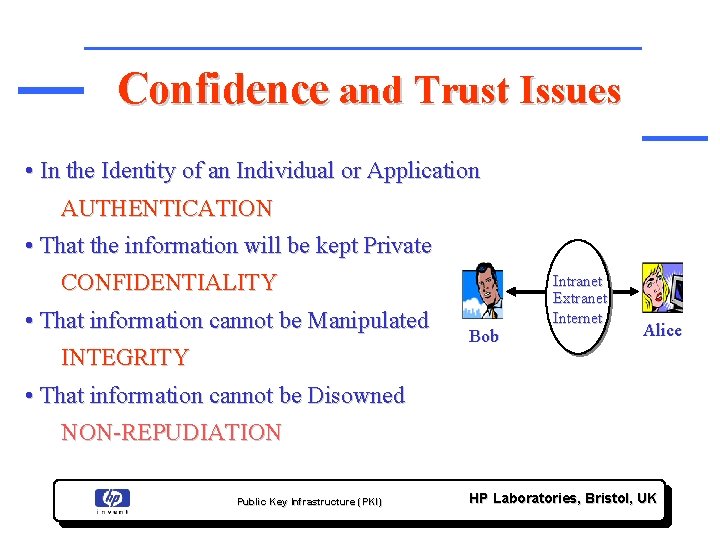
Confidence and Trust Issues • In the Identity of an Individual or Application AUTHENTICATION • That the information will be kept Private CONFIDENTIALITY • That information cannot be Manipulated INTEGRITY Bob Intranet Extranet Internet Alice • That information cannot be Disowned NON-REPUDIATION Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK
Starting Point: Cryptography Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK
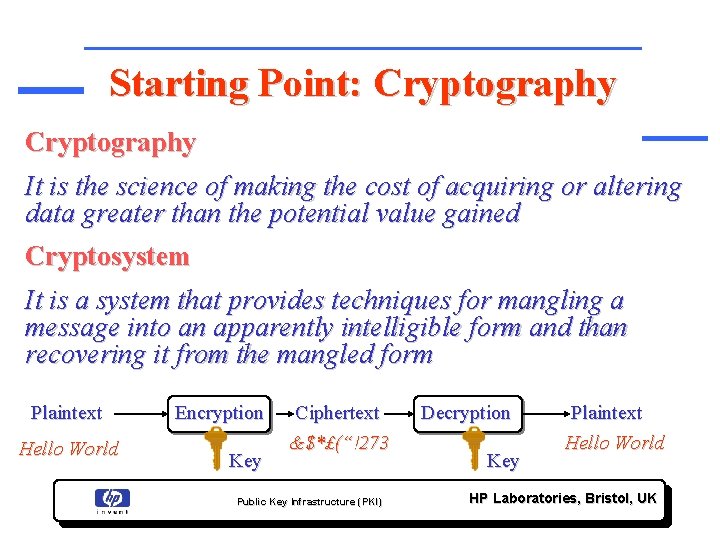
Starting Point: Cryptography It is the science of making the cost of acquiring or altering data greater than the potential value gained Cryptosystem It is a system that provides techniques for mangling a message into an apparently intelligible form and than recovering it from the mangled form Plaintext Hello World Encryption Key Ciphertext &$*£(“!273 Public Key Infrastructure (PKI) Decryption Key Plaintext Hello World HP Laboratories, Bristol, UK
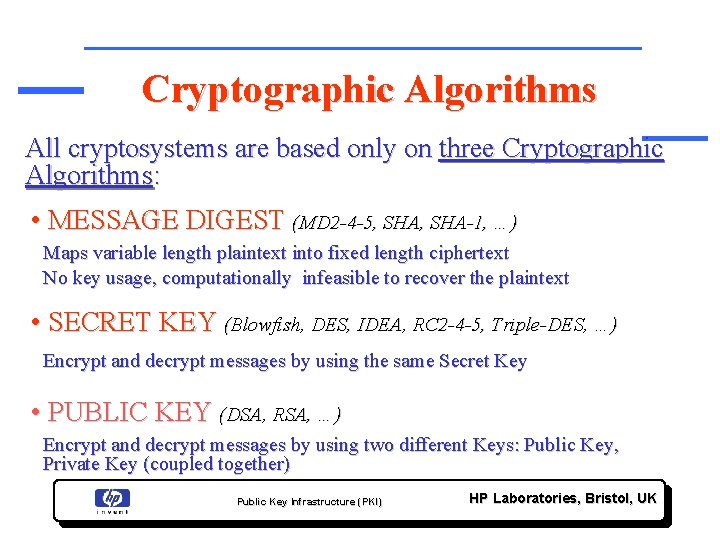
Cryptographic Algorithms All cryptosystems are based only on three Cryptographic Algorithms: • MESSAGE DIGEST (MD 2 -4 -5, SHA-1, …) Maps variable length plaintext into fixed length ciphertext No key usage, computationally infeasible to recover the plaintext • SECRET KEY (Blowfish, DES, IDEA, RC 2 -4 -5, Triple-DES, …) Encrypt and decrypt messages by using the same Secret Key • PUBLIC KEY (DSA, RSA, …) Encrypt and decrypt messages by using two different Keys: Public Key, Private Key (coupled together) Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK
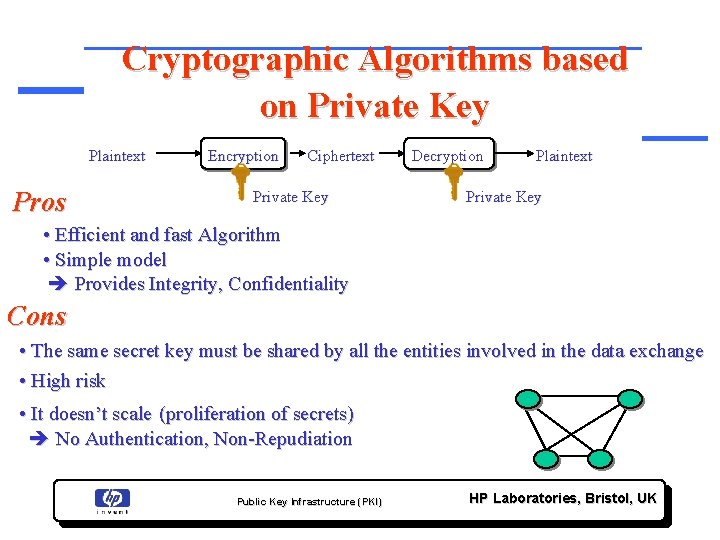
Cryptographic Algorithms based on Private Key Plaintext Pros Encryption Ciphertext Private Key Decryption Plaintext Private Key • Efficient and fast Algorithm • Simple model Provides Integrity, Confidentiality Cons • The same secret key must be shared by all the entities involved in the data exchange • High risk • It doesn’t scale (proliferation of secrets) No Authentication, Non-Repudiation Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK
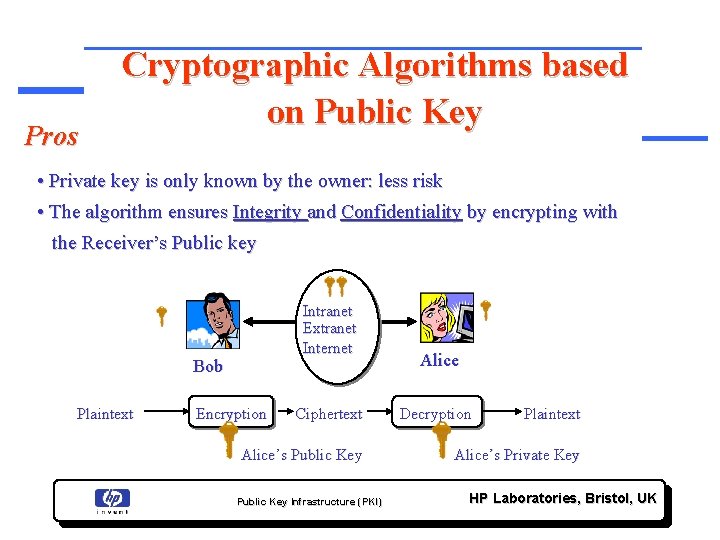
Pros Cryptographic Algorithms based on Public Key • Private key is only known by the owner: less risk • The algorithm ensures Integrity and Confidentiality by encrypting with the Receiver’s Public key Intranet Extranet Internet Bob Plaintext Encryption Ciphertext Alice’s Public Key Infrastructure (PKI) Alice Decryption Plaintext Alice’s Private Key HP Laboratories, Bristol, UK
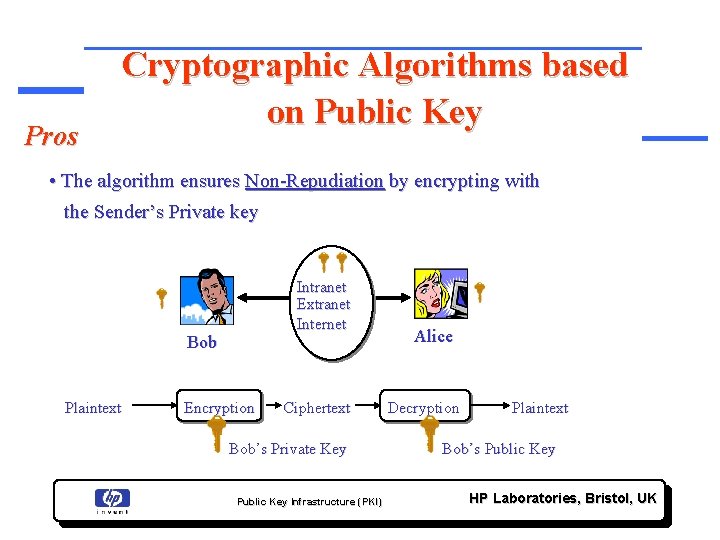
Pros Cryptographic Algorithms based on Public Key • The algorithm ensures Non-Repudiation by encrypting with the Sender’s Private key Intranet Extranet Internet Bob Plaintext Encryption Ciphertext Bob’s Private Key Public Key Infrastructure (PKI) Alice Decryption Plaintext Bob’s Public Key HP Laboratories, Bristol, UK
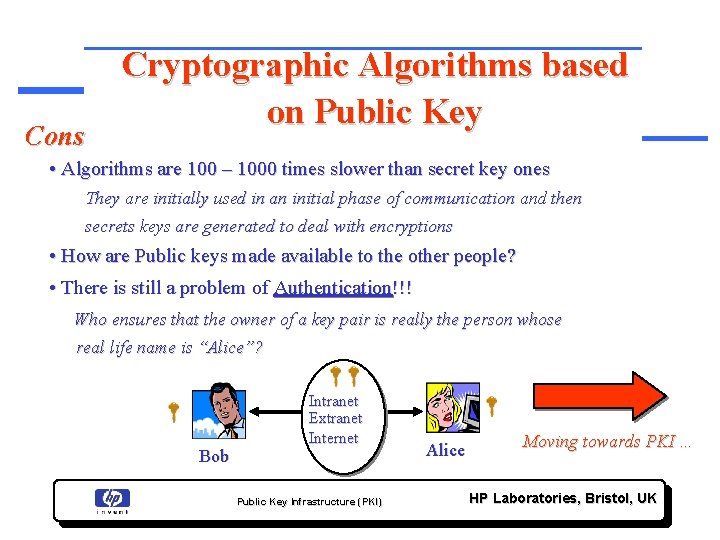
Cons Cryptographic Algorithms based on Public Key • Algorithms are 100 – 1000 times slower than secret key ones They are initially used in an initial phase of communication and then secrets keys are generated to deal with encryptions • How are Public keys made available to the other people? • There is still a problem of Authentication!!! Who ensures that the owner of a key pair is really the person whose real life name is “Alice”? Bob Intranet Extranet Internet Public Key Infrastructure (PKI) Alice Moving towards PKI … HP Laboratories, Bristol, UK
Digital Signature Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK
Digital Signature A Digital Signature is a data item that vouches the origin and the integrity of a Message • The originator of a message uses a signing key (Private Key) to sign the message and send the message and its digital signature to a recipient • The recipient uses a verification key (Public Key) to verify the origin of the message and that it has not been tampered with while in transit Bob Intranet Extranet Internet Public Key Infrastructure (PKI) Alice HP Laboratories, Bristol, UK
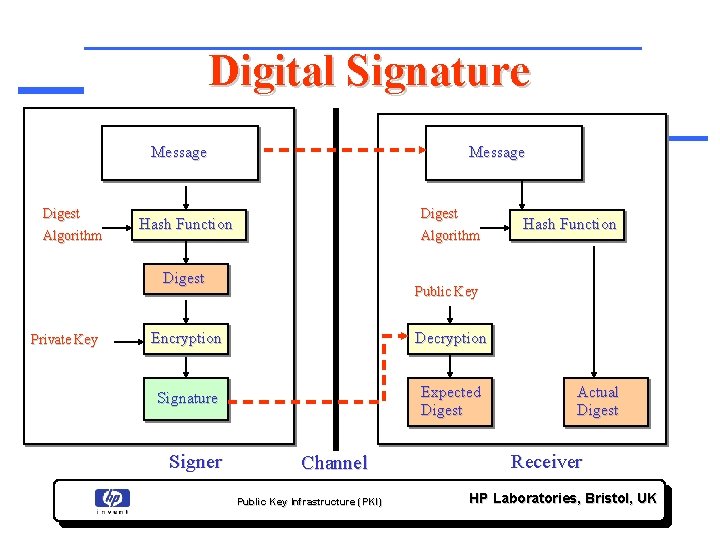
Digital Signature Message Digest Algorithm Message Digest Hash Function Algorithm Digest Private Key Public Key Encryption Decryption Signature Expected Digest Signer Hash Function Channel Public Key Infrastructure (PKI) Actual Digest Receiver HP Laboratories, Bristol, UK
Digital Signature There is still a problem linked to the “Real Identity” of the Signer. Why should I trust what the Sender claims to be? Moving towards PKI … Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK

Digital Certificate Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK

Digital Certificate A Digital Certificate is a binding between an entity’s Public Key and one or more Attributes relating its Identity. • The entity can be a Person, an Hardware Component, a Service, etc. • A Digital Certificate is issued (and signed) by someone - Usually the issuer is a Trusted Third Party • A self-signed certificate usually is not very trustworthy Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK
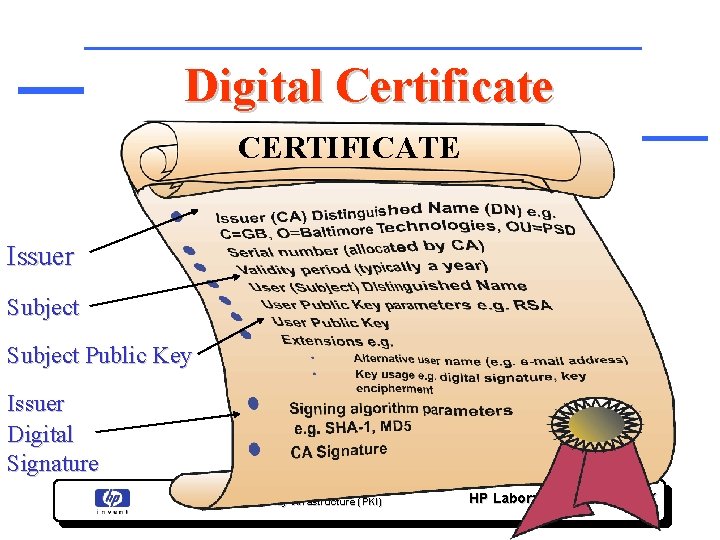
Digital Certificate CERTIFICATE Issuer Subject Public Key Issuer Digital Signature Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK
Digital Certificate Problems • How are Digital Certificates Issued? • Who is issuing them? • Why should I Trust the Certificate Issuer? • How can I check if a Certificate is valid? • How can I revoke a Certificate? • Who is revoking Certificates? Moving towards PKI … Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK
Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK
Public Key Infrastructure (PKI) A Public Key Infrastructure is an Infrastructure to support and manage Public Key-based Digital Certificates Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK
Public Key Infrastructure (PKI) “A PKI is a set of agreed-upon standards, Certification Authorities (CA), structure between multiple CAs, methods to discover and validate Certification Paths, Operational Protocols, Management Protocols, Interoperable Tools and supporting Legislation” “Digital Certificates” book – Jalal Feghhi, Jalil Feghhi, Peter Williams Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK
Public Key Infrastructure (PKI) Focus on: • X 509 PKI • X 509 Digital Certificates Standards defined by IETF, PKIX WG: http: //www. ietf. org/ … even if X 509 is not the only approach (e. g. SPKI) Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK
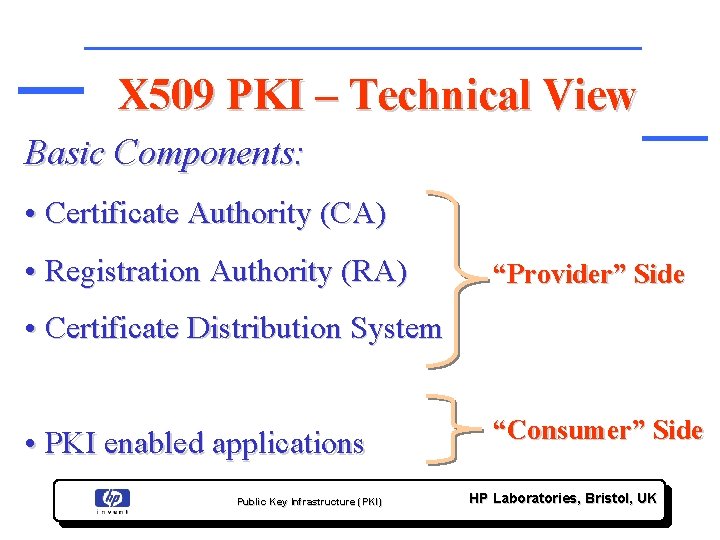
X 509 PKI – Technical View Basic Components: • Certificate Authority (CA) • Registration Authority (RA) “Provider” Side • Certificate Distribution System • PKI enabled applications Public Key Infrastructure (PKI) “Consumer” Side HP Laboratories, Bristol, UK
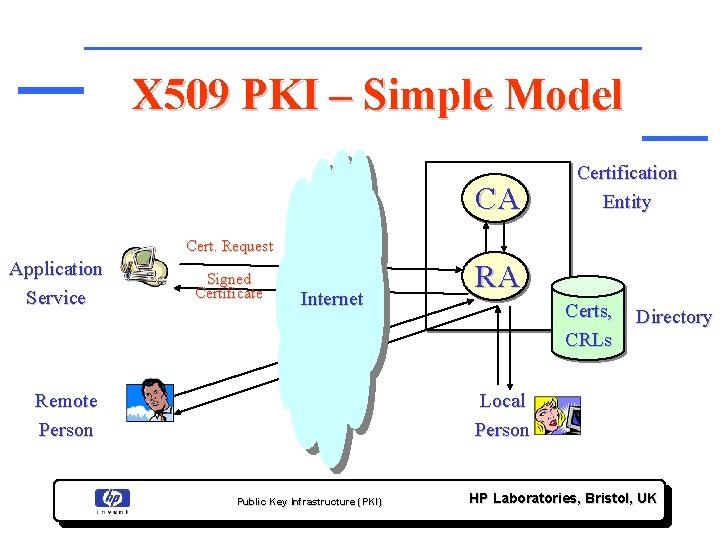
X 509 PKI – Simple Model CA Certification Entity Cert. Request Application Service Signed Certificate Internet Remote Person RA Certs, CRLs Directory Local Person Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK
X 509 PKI Certificate Authority (CA) Basic Tasks: • Key Generation • Digital Certificate Generation • Certificate Issuance and Distribution • Revocation • Key Backup and Recovery System • Cross-Certification Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK
X 509 PKI Registration Authority (RA) Basic Tasks: • Registration of Certificate Information • Face-to-Face Registration • Remote Registration • Automatic Registration • Revocation Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK
X 509 PKI Certificate Distribution System Provide Repository for: • Digital Certificates • Certificate Revocation Lists (CRLs) Typically: • Special Purposes Databases • LDAP directories Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK

Certificate Revocation List Revoked Certificates remain in CRL until they expire Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK
Certificate Revocation List (CRL) • CRLs are published by CAs at well defined interval of time • It is a responsibility of “Users” of certificates to “download” a CRL and verify if a certificate has been revoked • User application must deal with the revocation processes Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK
Online Certificate Status Protocol (OCSP) • An alternative to CRLs • IETF/PKIX standard for a real-time check if a certificate has been revoked/suspended • Requires a high availability OCSP Server Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK
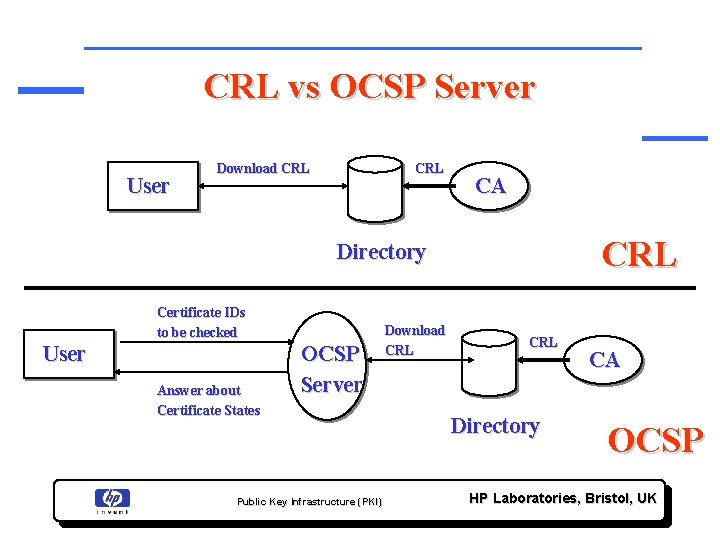
CRL vs OCSP Server User Download CRL CA CRL Directory Certificate IDs to be checked User Answer about Certificate States OCSP Server Public Key Infrastructure (PKI) Download CRL Directory CA OCSP HP Laboratories, Bristol, UK
X 509 PKI-enabled Applications Functionality Required: • Cryptographic functionality • Secure storage of Personal Information • Digital Certificate Handling • Directory Access • Communication Facilities Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK
X 509 PKI Trust and Legal Issues Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK
X 509 PKI Trust and Legal Issues • Why should I Trust a CA? • How can I determine the liability of a CA? Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK
X 509 PKI Approaches to Trust and Legal Aspects • Why should I Trust a CA? Certificate Hierarchies, Cross-Certification • How can I determine the liability of a CA? Certificate Policies (CP) and Certificate Policy Statement (CPS) Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK
X 509 PKI Approach to Trust Certificate Hierarchies and Cross-Certification Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK
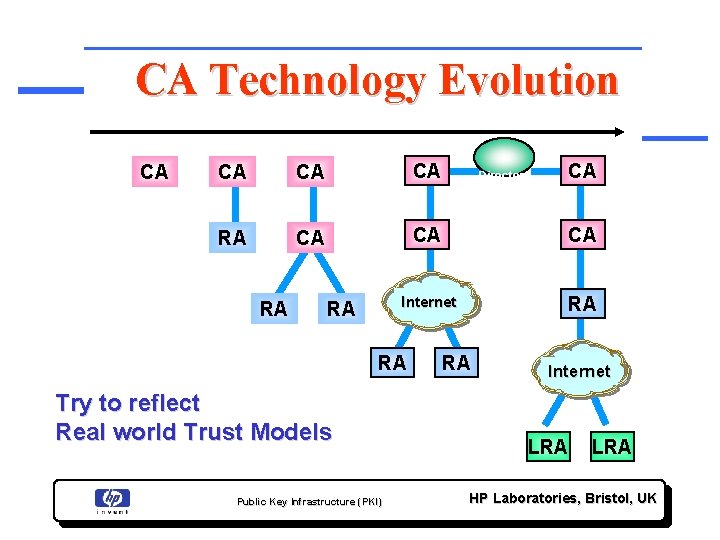
CA Technology Evolution CA CA RA CA CA CA Internet RA RA Try to reflect Real world Trust Models Public Key Infrastructure (PKI) Directory Services RA CA Internet LRA HP Laboratories, Bristol, UK
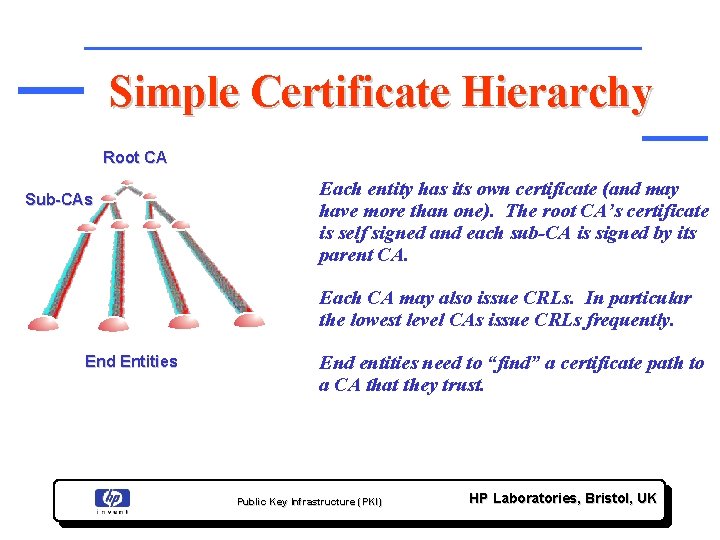
Simple Certificate Hierarchy Root CA Sub-CAs Each entity has its own certificate (and may have more than one). The root CA’s certificate is self signed and each sub-CA is signed by its parent CA. Each CA may also issue CRLs. In particular the lowest level CAs issue CRLs frequently. End Entities End entities need to “find” a certificate path to a CA that they trust. Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK
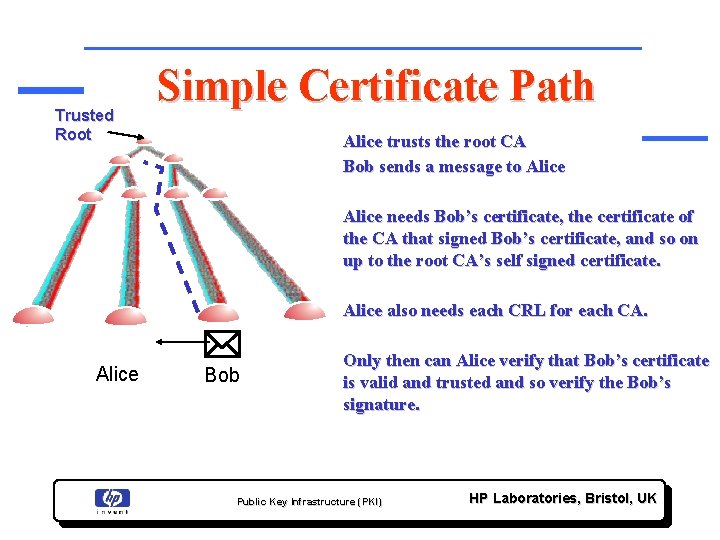
Trusted Root Simple Certificate Path Alice trusts the root CA Bob sends a message to Alice needs Bob’s certificate, the certificate of the CA that signed Bob’s certificate, and so on up to the root CA’s self signed certificate. Alice also needs each CRL for each CA. Alice * Bob Only then can Alice verify that Bob’s certificate is valid and trusted and so verify the Bob’s signature. Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK
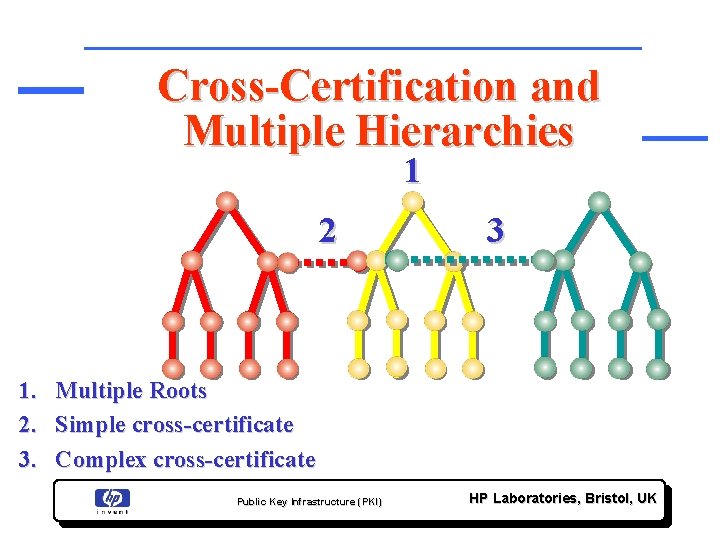
Cross-Certification and Multiple Hierarchies 1 2 3 1. Multiple Roots 2. Simple cross-certificate 3. Complex cross-certificate Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK
X 509 PKI Approach to Trust : Problems Things are getting more and more complex if Hierarchies and Cross-Certifications are used Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK
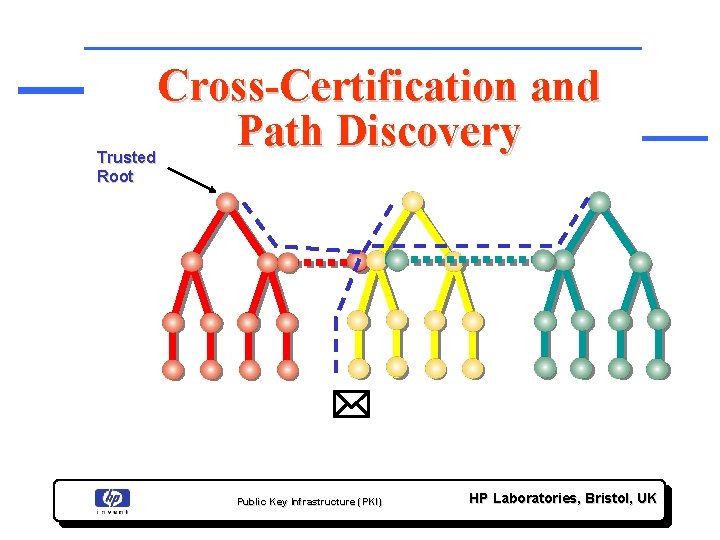
Trusted Root Cross-Certification and Trusted Path Discovery Root 3 * Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK
X 509 PKI Approach to Legal Aspects Certificate Policy And Certificate Practice Statement Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK
Certificate Policy (CP) • A document that sets out the rights, duties and obligations of each party in a Public Key Infrastructure • The Certificate Policy (CP) is a document which usually has legal effect • A CP is usually publicly exposed by CAs, for example on a Web Site (Veri. Sign, etc. ) Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK
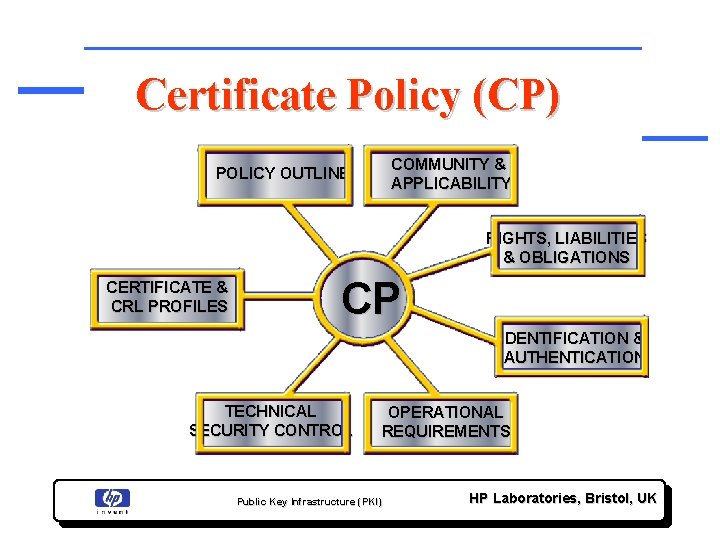
Certificate Policy (CP) COMMUNITY & APPLICABILITY POLICY OUTLINE RIGHTS, LIABILITIES & OBLIGATIONS CERTIFICATE & CRL PROFILES CP IDENTIFICATION & AUTHENTICATION TECHNICAL SECURITY CONTROL OPERATIONAL REQUIREMENTS Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK
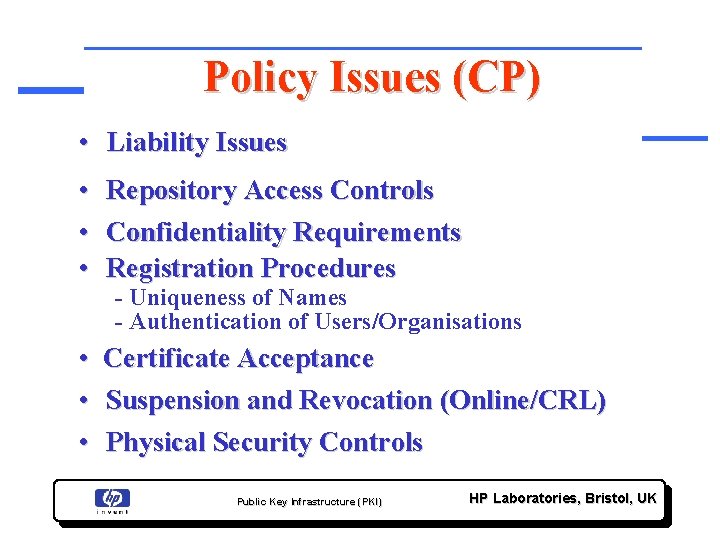
Policy Issues (CP) • Liability Issues • Repository Access Controls • Confidentiality Requirements • Registration Procedures - Uniqueness of Names - Authentication of Users/Organisations • Certificate Acceptance • Suspension and Revocation (Online/CRL) • Physical Security Controls Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK
Certificate Policy Statement (CPS) • A document that sets out what happens in practice to support the policy statements made in the CP in a PKI • The Certificate Practice Statement (CPS) is a document which may have legal effect in limited circumstances Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK
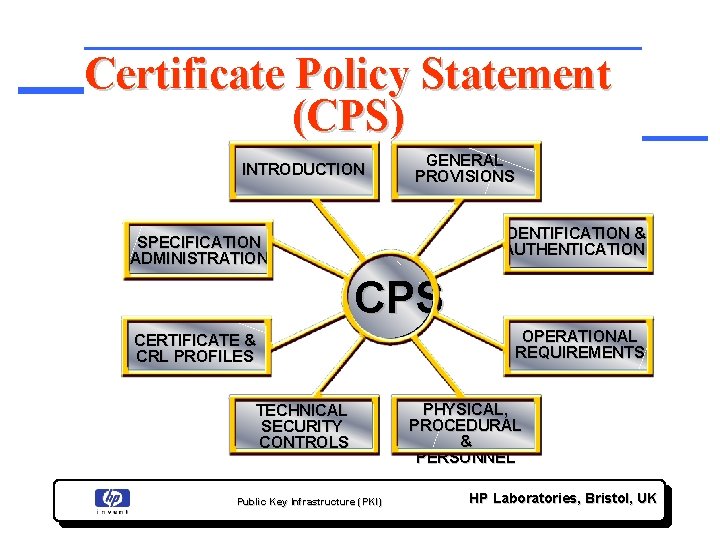
Certificate Policy Statement (CPS) INTRODUCTION GENERAL PROVISIONS IDENTIFICATION & AUTHENTICATION SPECIFICATION ADMINISTRATION CPS CERTIFICATE & CRL PROFILES TECHNICAL SECURITY CONTROLS Public Key Infrastructure (PKI) OPERATIONAL REQUIREMENTS PHYSICAL, PROCEDURAL & PERSONNEL HP Laboratories, Bristol, UK
IETF (PKIX) Standards • X. 509 Certificate and CRL Profiles • PKI Management Protocols • Certificate Request Formats • CP/CPS Framework • LDAP, OCSP, etc. http: //www. ietf. org/ Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK
Identity is Not Enough: Attribute Certificates IETF (PKIX WG) is also defining standards for Attribute Certificates (ACs): • Visa Card (Attribute) vs. Passport (Identity) • Attribute Certificates specify Attributes associated to an Identity • Attribute Certificates don’t contain a Public key but a link to an Identity Certificate Public Key Infrastructure (PKI) HP Laboratories, Bristol, UK
- Slides: 52