Public Key Encryption with Keyword Search Authors D
Public Key Encryption with Keyword Search Authors: D. Boneh, G. Di Crescenzo, R. Ostrovsky, and G. Persiano -Presented by Brijesh 1
Mobile People Architecture (Stanford) n n MPA – focuses on people (and not devices) as endpoints of communication. A personal proxy maintains a list of devices, a person is currently reachable on and routes based on urgency/ keywords etc. . 2
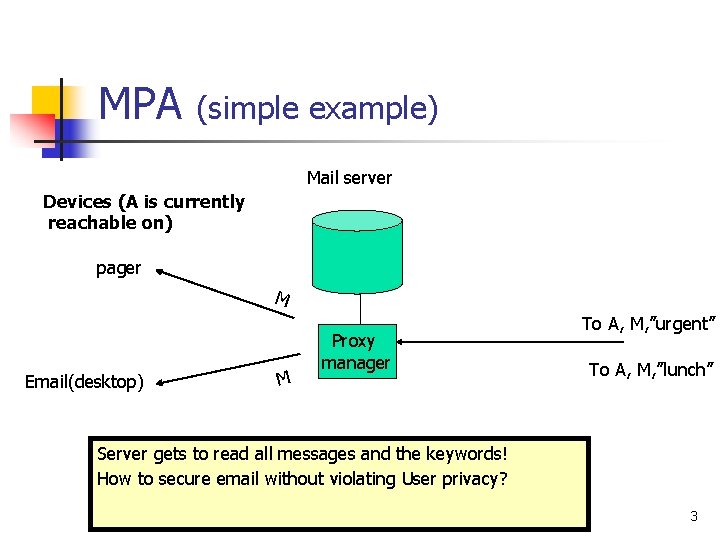
MPA (simple example) Mail server Devices (A is currently reachable on) pager M Email(desktop) M Proxy manager To A, M, ”urgent” To A, M, ”lunch” Server gets to read all messages and the keywords! How to secure email without violating User privacy? 3
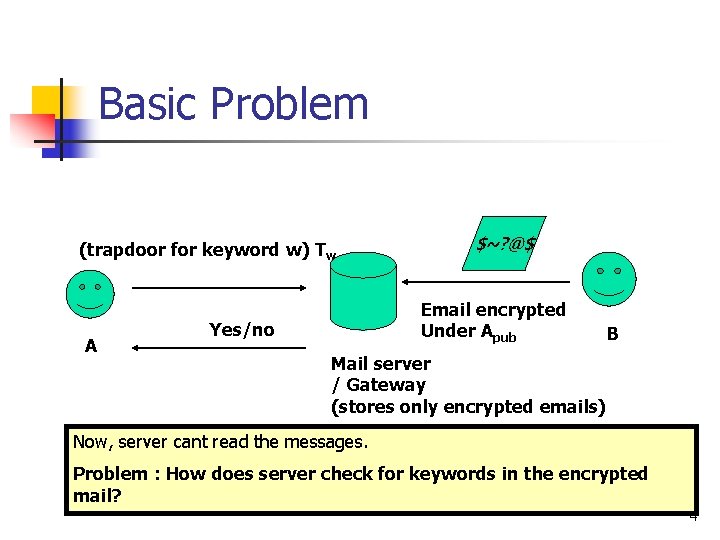
Basic Problem (trapdoor for keyword w) Tw A $~? @$ Email encrypted Under Apub Yes/no B Mail server / Gateway (stores only encrypted emails) Now, server cant read the messages. Problem : How does server check for keywords in the encrypted mail? 4
![Basics Mail server B [EApub[msg], PEKS(Apub, W 1), PEKS(Apub, W 2), …. PEKS(Apub, Wk)] Basics Mail server B [EApub[msg], PEKS(Apub, W 1), PEKS(Apub, W 2), …. PEKS(Apub, Wk)]](http://slidetodoc.com/presentation_image/89147ee7e66bc62a0afa6a92dda75bde/image-5.jpg)
Basics Mail server B [EApub[msg], PEKS(Apub, W 1), PEKS(Apub, W 2), …. PEKS(Apub, Wk)] Encrypted mail for A PEKS for each keyword 5
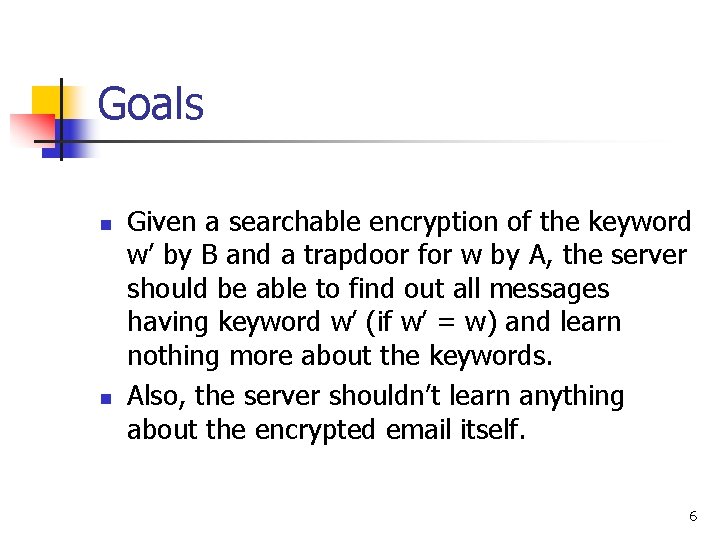
Goals n n Given a searchable encryption of the keyword w’ by B and a trapdoor for w by A, the server should be able to find out all messages having keyword w’ (if w’ = w) and learn nothing more about the keywords. Also, the server shouldn’t learn anything about the encrypted email itself. 6
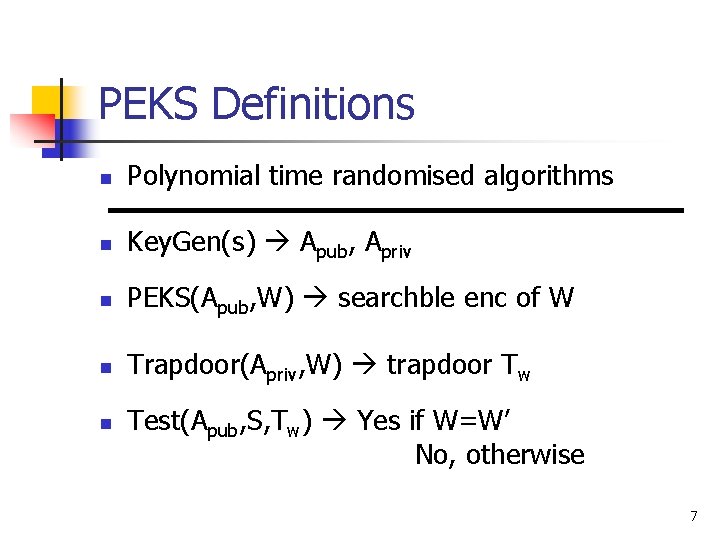
PEKS Definitions n Polynomial time randomised algorithms n Key. Gen(s) Apub, Apriv n PEKS(Apub, W) searchble enc of W n Trapdoor(Apriv, W) trapdoor Tw n Test(Apub, S, Tw) Yes if W=W’ No, otherwise 7
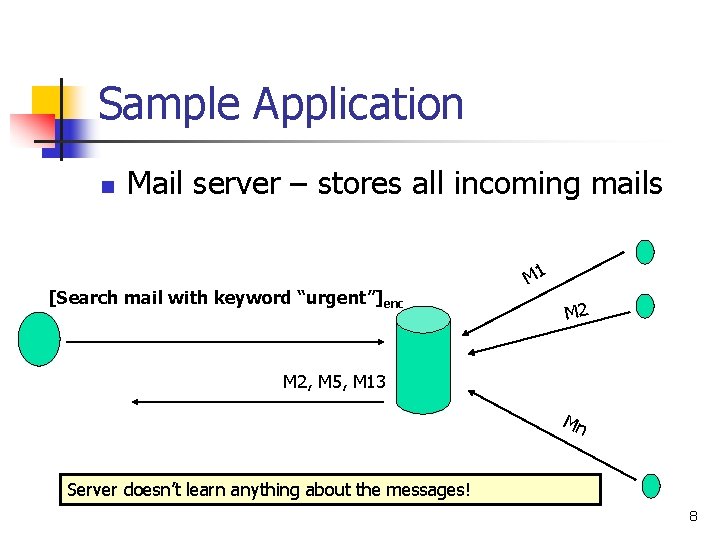
Sample Application n Mail server – stores all incoming mails [Search mail with keyword “urgent”]enc M 1 M 2, M 5, M 13 Mn Server doesn’t learn anything about the messages! 8
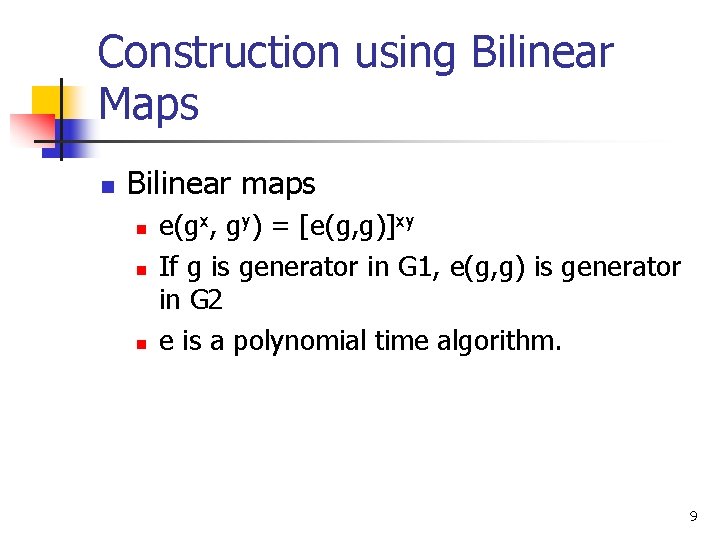
Construction using Bilinear Maps n Bilinear maps n n n e(gx, gy) = [e(g, g)]xy If g is generator in G 1, e(g, g) is generator in G 2 e is a polynomial time algorithm. 9
![Construction using Bilinear Maps n Key. Gen: random α Apub = [g, gα] Apriv Construction using Bilinear Maps n Key. Gen: random α Apub = [g, gα] Apriv](http://slidetodoc.com/presentation_image/89147ee7e66bc62a0afa6a92dda75bde/image-10.jpg)
Construction using Bilinear Maps n Key. Gen: random α Apub = [g, gα] Apriv = α n PEKS(Apub, w): n n n Sender picks a random r t = e(H 1(w), hr) H 1: {0, 1}* G 1 Output S=[A, B] = [gr, H 2(t)] 10
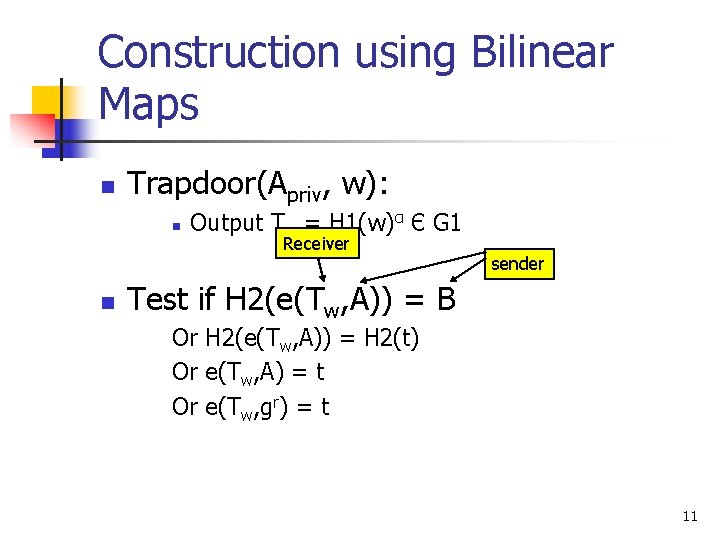
Construction using Bilinear Maps n Trapdoor(Apriv, w): n n Output Tw = H 1(w)α Є G 1 Receiver sender Test if H 2(e(Tw, A)) = B Or H 2(e(Tw, A)) = H 2(t) Or e(Tw, A) = t Or e(Tw, gr) = t 11
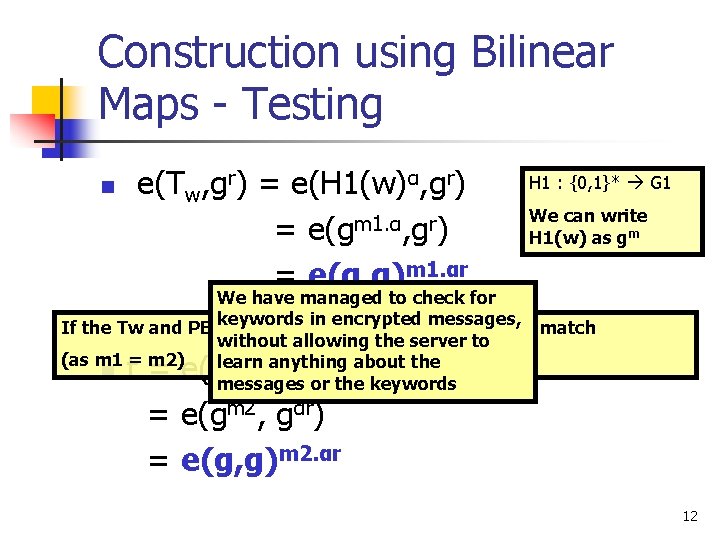
Construction using Bilinear Maps - Testing n e(Tw, gr) = e(H 1(w)α, gr) = e(gm 1. α, gr) = e(g, g)m 1. αr H 1 : {0, 1}* G 1 We can write H 1(w) as gm We have managed to check for keywords in encrypted messages, If the Tw and PEKS correspond to same w, there is a match without allowing the server to (as m 1 = m 2) learn anything r about the n messages or the keywords t = e(H 1(w), h ) = e(gm 2, gαr) = e(g, g)m 2. αr 12
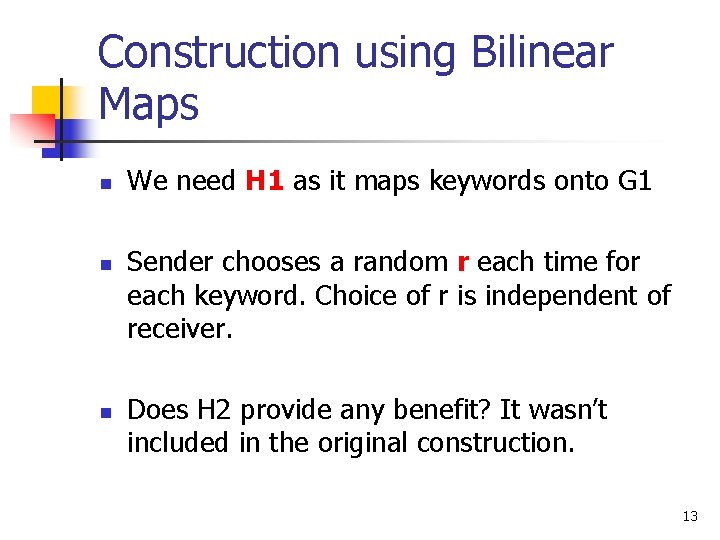
Construction using Bilinear Maps n n n We need H 1 as it maps keywords onto G 1 Sender chooses a random r each time for each keyword. Choice of r is independent of receiver. Does H 2 provide any benefit? It wasn’t included in the original construction. 13
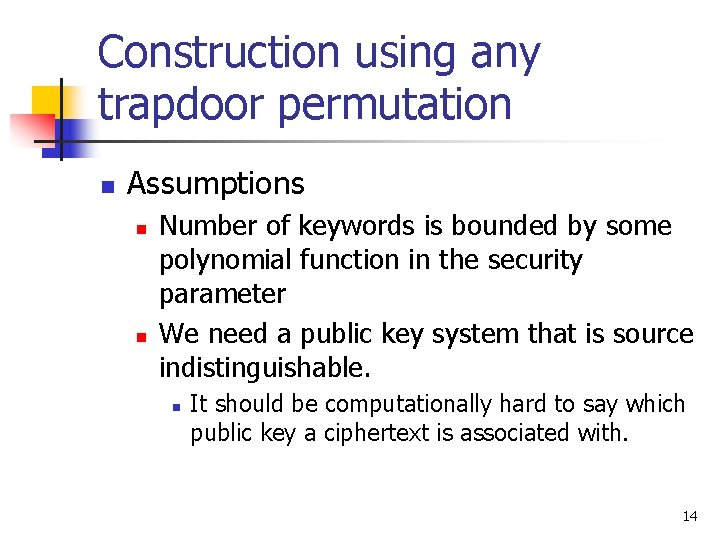
Construction using any trapdoor permutation n Assumptions n n Number of keywords is bounded by some polynomial function in the security parameter We need a public key system that is source indistinguishable. n It should be computationally hard to say which public key a ciphertext is associated with. 14
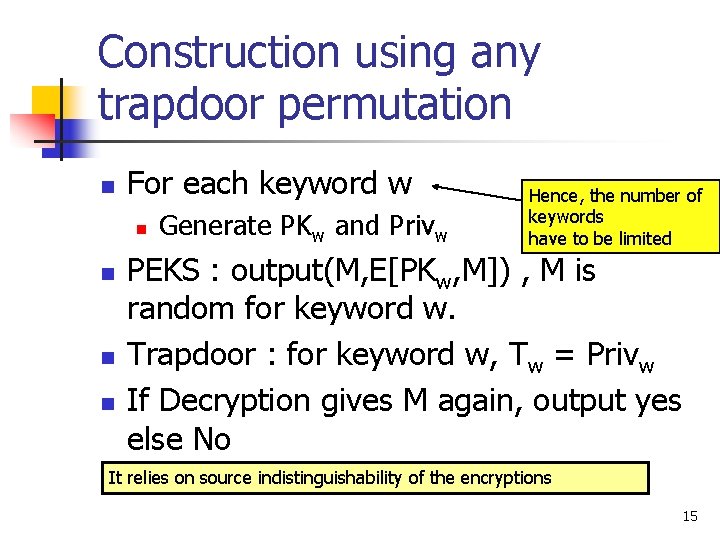
Construction using any trapdoor permutation n For each keyword w n n Generate PKw and Privw Hence, the number of keywords have to be limited PEKS : output(M, E[PKw, M]) , M is random for keyword w. Trapdoor : for keyword w, Tw = Privw If Decryption gives M again, output yes else No It relies on source indistinguishability of the encryptions 15
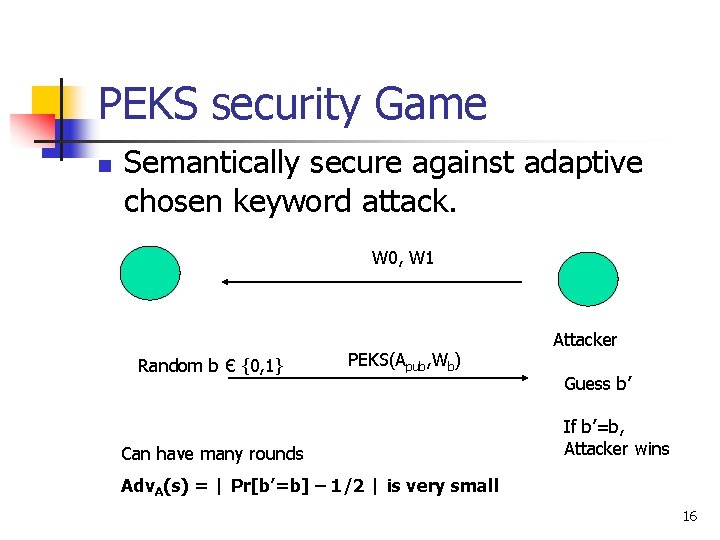
PEKS security Game n Semantically secure against adaptive chosen keyword attack. W 0, W 1 Random b Є {0, 1} PEKS(Apub, Wb) Can have many rounds Attacker Guess b’ If b’=b, Attacker wins Adv. A(s) = | Pr[b’=b] – 1/2 | is very small 16
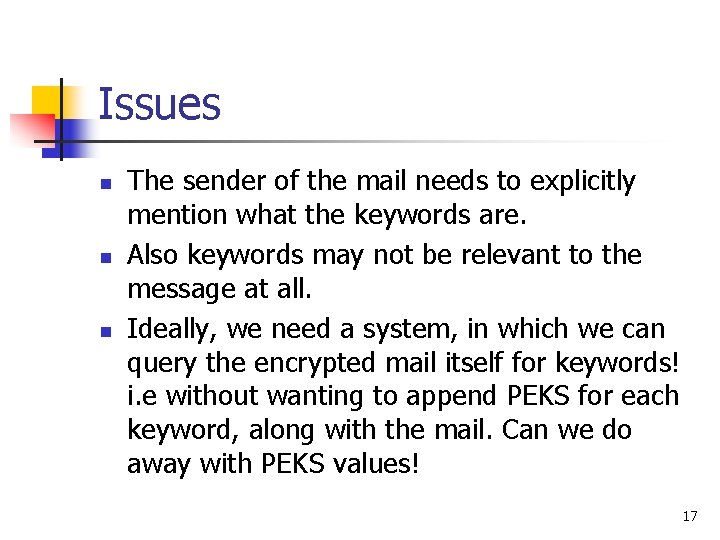
Issues n n n The sender of the mail needs to explicitly mention what the keywords are. Also keywords may not be relevant to the message at all. Ideally, we need a system, in which we can query the encrypted mail itself for keywords! i. e without wanting to append PEKS for each keyword, along with the mail. Can we do away with PEKS values! 17
Issues n n The same trapdoor can be used many times in the future as well by the mail server ? Can an attacker reuse the trapdoor to get some information about the message or the keyword? 18
Open problem n n I m not sure if this has been done before or if it is possible. We want to be able to search the encrypted message itself for any word, given some trapdoor information. 19
Questions 20
- Slides: 20