Public Health Information Network PHIN 2008 Collaborating for
Public Health Information Network (PHIN) 2008 Collaborating for Public Health While Preserving Personal Privacy: Challenges and Potential Solutions Dixie B. Baker, Ph. D. Senior Vice President Chief Technology Officer, Health Solutions Copyright 2008, Science Applications International Corporation 1
Agenda 4 Individually Identifiable Health Information (IIHI) in the Public Health Timeline 4 Legal Framework for Privacy Protection in Public Health 4 Privacy and Health Risk Model* 4 Recommendations 4 Summary * Update to a model first presented in Baker, D. B. Privacy and security in public health: maintaining the delicate balance between personal privacy and population safety. Proceedings of the 2006 Annual Computer Security Applications Conference. IEEE. Dec 2006. Copyright 2008, Science Applications International Corporation 2
Definitions (As Used in This Presentation) 4 Privacy – the state of being free from intrusion or disturbance in one’s private life or affairs; * in the US, the right to such a state 4 Security – something that frees from danger or harm, or that makes safe; * defensive measures that protect the confidentiality, integrity, and availability of sensitive and safety-critical health information *Dictionary. com Unabridged (V 1. 1) Copyright 2008, Science Applications International Corporation 3
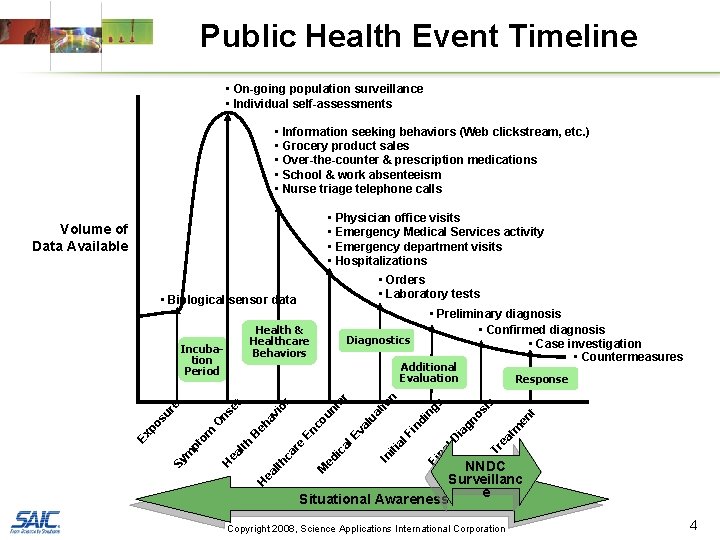
Public Health Event Timeline • On-going population surveillance • Individual self-assessments • Information seeking behaviors (Web clickstream, etc. ) • Grocery product sales • Over-the-counter & prescription medications • School & work absenteeism • Nurse triage telephone calls • Physician office visits • Emergency Medical Services activity • Emergency department visits • Hospitalizations Volume of Data Available • Orders • Laboratory tests • Biological sensor data Health & Healthcare Behaviors Incubation Period Tr ea os gn ia l. D Fi na tm en t is s di ng in l. F iti a In ic ed Response n al al Ev En re NNDC Surveillanc e Situational Awareness M ca lth ea H ua un co av eh B lth ea H tio te r r io et om m pt Sy Diagnostics Additional Evaluation O ns re su po Ex • Preliminary diagnosis • Confirmed diagnosis • Case investigation • Countermeasures Copyright 2008, Science Applications International Corporation 4
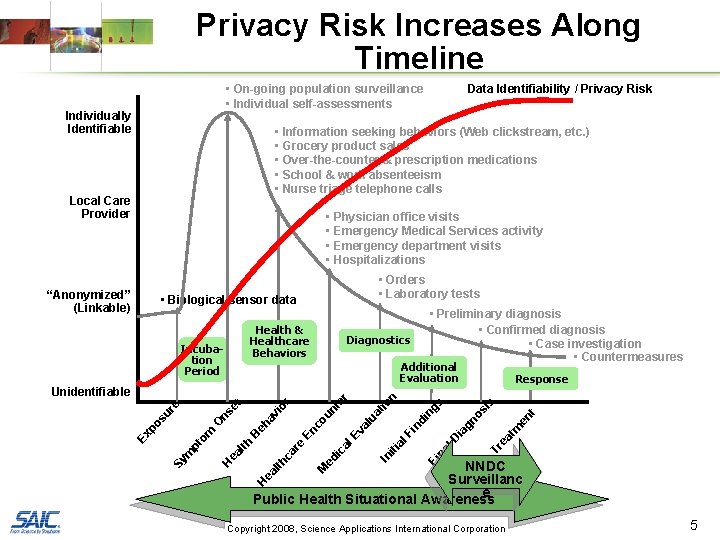
Privacy Risk Increases Along Timeline • On-going population surveillance • Individual self-assessments Individually Identifiable Data Identifiability / Privacy Risk • Information seeking behaviors (Web clickstream, etc. ) • Grocery product sales • Over-the-counter & prescription medications • School & work absenteeism • Nurse triage telephone calls Local Care Provider • Physician office visits • Emergency Medical Services activity • Emergency department visits • Hospitalizations • Biological sensor data Health & Healthcare Behaviors Incubation Period Additional Evaluation Tr ea os gn ia l. D na Fi l. F iti a tm en t s di ng in al Ev al ed ic is n ua un co En re ca tio r av eh Response H M lth NNDC Surveillanc e Public Health Situational Awareness ea H ea lth B om m pt Sy io et O ns re su po te r Unidentifiable Ex • Preliminary diagnosis • Confirmed diagnosis • Case investigation • Countermeasures Diagnostics In “Anonymized” (Linkable) • Orders • Laboratory tests Copyright 2008, Science Applications International Corporation 5
Legal Foundation for Privacy Protection in Public Health 4 US Constitution establishes foundation for both privacy protection and state responsibility for public health 4 Privacy Act of 1974 defines privacy requirements for federal agencies • Prohibits disclosure without written consent • Requires accountability • Includes exception for “protection of the health and safety of individuals and the public” 4 Public Health and Welfare Act (Title 42, Section 242 m) defines privacy requirements for public health • Prohibits disclosure of identities of individuals and establishments • Restricts use of information to purpose intended • Specifically addresses National Center for Health Statistics (CDC) and international public health cooperation • Imposes additional privacy and confidentiality protections for certain classes of information (e. g. , developmental disabilities, DNA, HIV/AIDS, mental health) Copyright 2008, Science Applications International Corporation 6
HIPAA on Public Health 4 Health Insurance Portability and Accountability Act (HIPAA) Privacy Rule specifically enables covered entities to release Protected Health Information (PHI) to public health authorities without individual authorization • Restricted to “minimum necessary” for the purpose intended • Must be audited 4 Not straight-forward – interpretations vary from state to state • Some public health agencies and laboratories perform “covered functions” (e. g. , diagnostic testing, providing patient care) making them “covered entities” • State law that imposes stronger protections than Privacy Rule take precedence over HIPAA Privacy Rule Copyright 2008, Science Applications International Corporation 7
Inconsistencies in Privacy Law 4 Inconsistent and fragmented laws exist at both state and federal levels 4 A number of federal and state laws afford heightened privacy protections for certain classes of sensitive information • Variation between HIPAA Privacy Rule & federal law governing the confidentiality of alcohol and drug abuse patients • Majority of states impose higher protections to drug & alcohol abuse information, as well as HIV/AIDS, mental health, and genetic information – often require patient permission & vary from state to state • Public Health and Welfare Act names its own set of “special classes” 4 Differences in definition of terms (e. g. , medical record, record locator service) 4 No standard requirement (or interpretation) for patient consent; no uniform wording on consent forms 4 Laws designed for paper-based exchanges may fail to address, or may not be applicable to, electronic transmission, storage, and authentication 4 Inconsistent laws addressing the disclosure and re-disclosure of information for treatment purposes 4 Inconsistent laws addressing the disclosure of public health information (e. g. , immunization records, communicable diseases) 4 Inconsistencies in state laws – and in understanding & interpretation of state and federal laws – impede the exchange of information across state lines Copyright 2008, Science Applications International Corporation 8
Public Health Challenge How can public health achieve and maintain an optimal balance between assuring the health and safety of the U. S. population and protecting the privacy of individuals within that population? Copyright 2008, Science Applications International Corporation 9
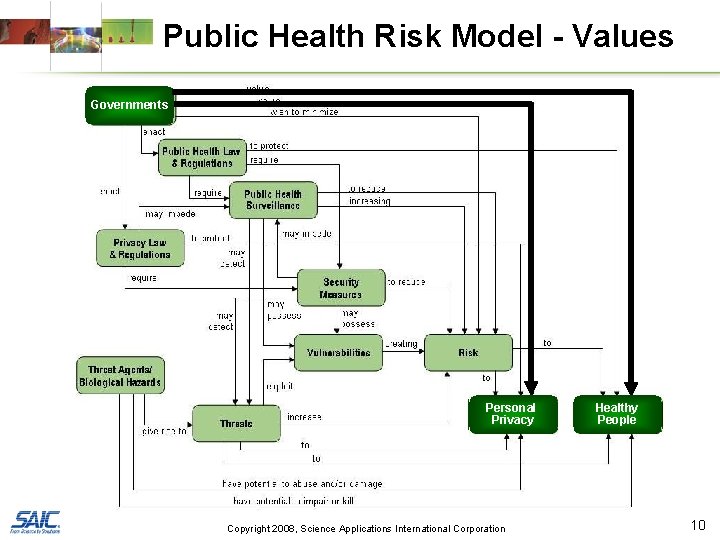
Public Health Risk Model - Values Governments Personal Privacy Copyright 2008, Science Applications International Corporation Healthy People 10
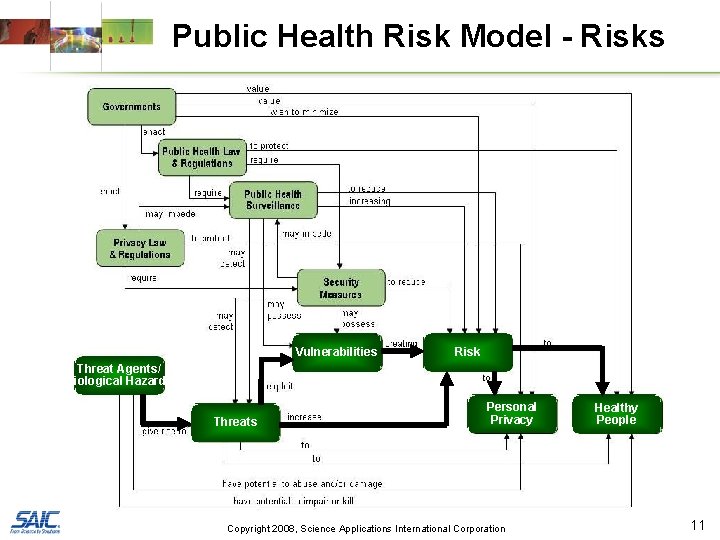
Public Health Risk Model - Risks Vulnerabilities Risk Threat Agents/ Biological Hazards Threats Personal Privacy Copyright 2008, Science Applications International Corporation Healthy People 11
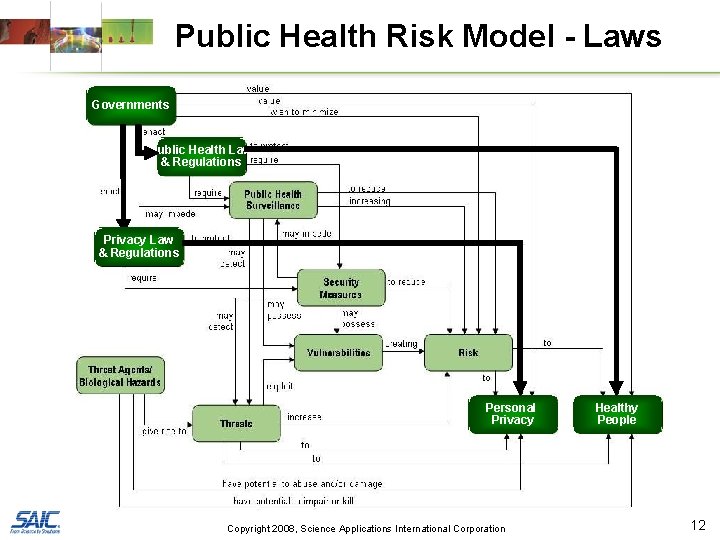
Public Health Risk Model - Laws Governments Public Health Law & Regulations Privacy Law & Regulations Personal Privacy Copyright 2008, Science Applications International Corporation Healthy People 12
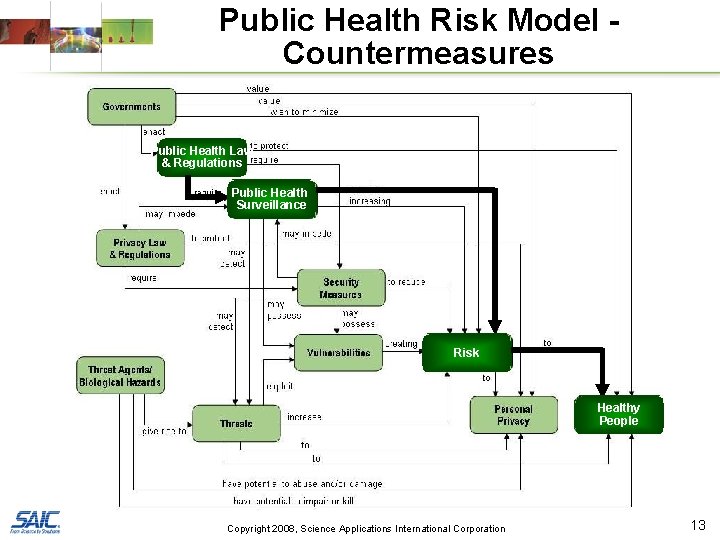
Public Health Risk Model Countermeasures Public Health Law & Regulations Public Health Surveillance Risk Healthy People Copyright 2008, Science Applications International Corporation 13
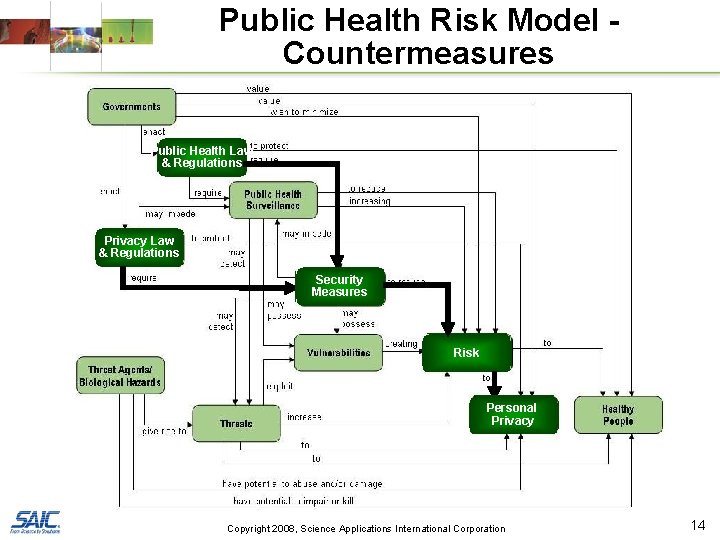
Public Health Risk Model Countermeasures Public Health Law & Regulations Privacy Law & Regulations Security Measures Risk Personal Privacy Copyright 2008, Science Applications International Corporation 14
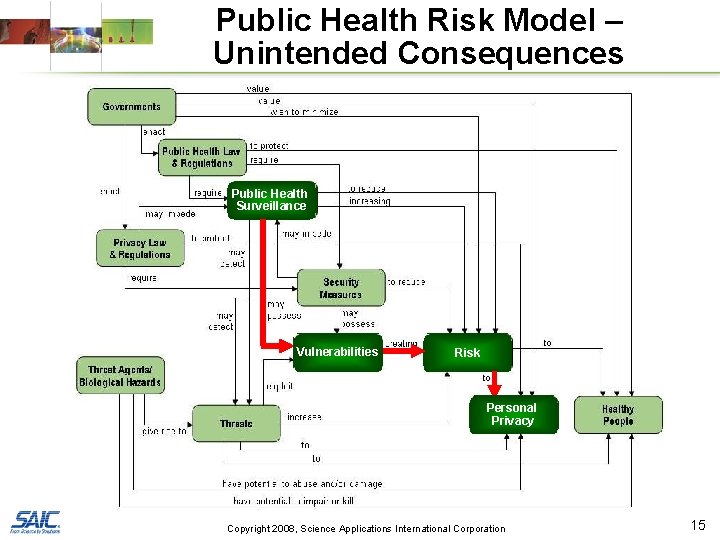
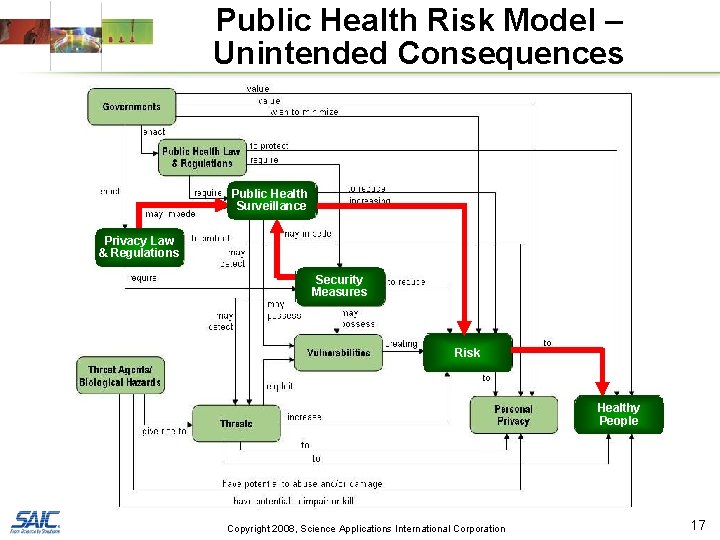
Public Health Risk Model – Unintended Consequences Public Health Surveillance Vulnerabilities Risk Personal Privacy Copyright 2008, Science Applications International Corporation 15
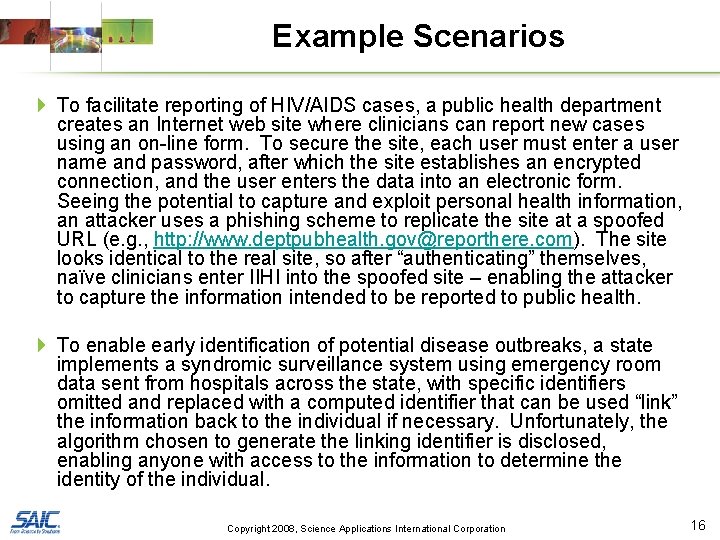
Example Scenarios 4 To facilitate reporting of HIV/AIDS cases, a public health department creates an Internet web site where clinicians can report new cases using an on-line form. To secure the site, each user must enter a user name and password, after which the site establishes an encrypted connection, and the user enters the data into an electronic form. Seeing the potential to capture and exploit personal health information, an attacker uses a phishing scheme to replicate the site at a spoofed URL (e. g. , http: //www. deptpubhealth. gov@reporthere. com). The site looks identical to the real site, so after “authenticating” themselves, naïve clinicians enter IIHI into the spoofed site – enabling the attacker to capture the information intended to be reported to public health. 4 To enable early identification of potential disease outbreaks, a state implements a syndromic surveillance system using emergency room data sent from hospitals across the state, with specific identifiers omitted and replaced with a computed identifier that can be used “link” the information back to the individual if necessary. Unfortunately, the algorithm chosen to generate the linking identifier is disclosed, enabling anyone with access to the information to determine the identity of the individual. Copyright 2008, Science Applications International Corporation 16
Public Health Risk Model – Unintended Consequences Public Health Surveillance Privacy Law & Regulations Security Measures Risk Healthy People Copyright 2008, Science Applications International Corporation 17
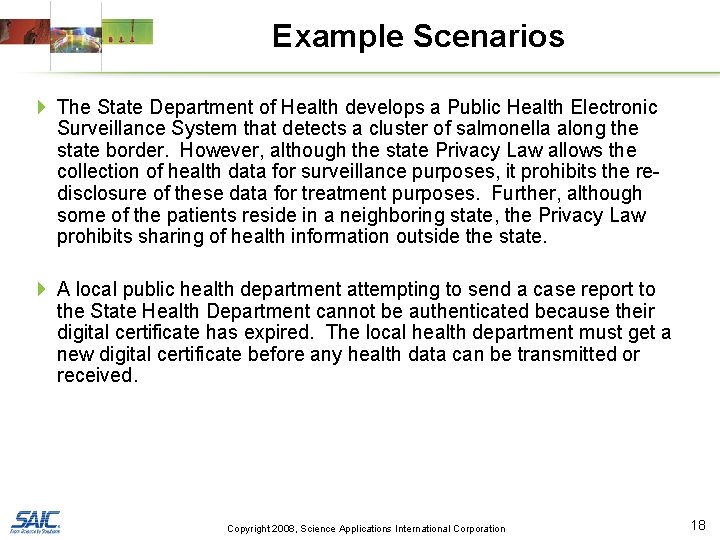
Example Scenarios 4 The State Department of Health develops a Public Health Electronic Surveillance System that detects a cluster of salmonella along the state border. However, although the state Privacy Law allows the collection of health data for surveillance purposes, it prohibits the redisclosure of these data for treatment purposes. Further, although some of the patients reside in a neighboring state, the Privacy Law prohibits sharing of health information outside the state. 4 A local public health department attempting to send a case report to the State Health Department cannot be authenticated because their digital certificate has expired. The local health department must get a new digital certificate before any health data can be transmitted or received. Copyright 2008, Science Applications International Corporation 18
Privacy Policy Recommendations 4 Adhere to “least privilege principle” • Include only those identifiable data elements necessary for the intended application • Assign to each role and each individual only those access privileges necessary to perform the assigned functions 4 Restrict use of individually identifiable health information (IIHI) to only those purposes for which it was collected 4 Allow and enable “breaking the glass” when necessary to protect public health and safety 4 Audit accesses to IIHI information 4 Remove IIHI from systems when it no longer is needed 4 Support legislation and initiatives to unify health privacy policy throughout the US Copyright 2008, Science Applications International Corporation 19
Example Minimum Data Sets 4 HIPAA Privacy Rule identifies 18 elements that if removed from Protected Health Information (PHI) renders it “de-identified” • Privacy Rule specifically enables the collection of PHI for public health purposes without the individual’s consent – i. e. , deidentification is not required for public health – but must be “minimum necessary” 4 Public health community identifies “minimum necessary” for each context • Electronic Laboratory Reporting (ELR) – lab to state • National Electronic Disease Surveillance System (NEDSS) – state to CDC • Bio. Sense – hospitals to CDC Copyright 2008, Science Applications International Corporation 20
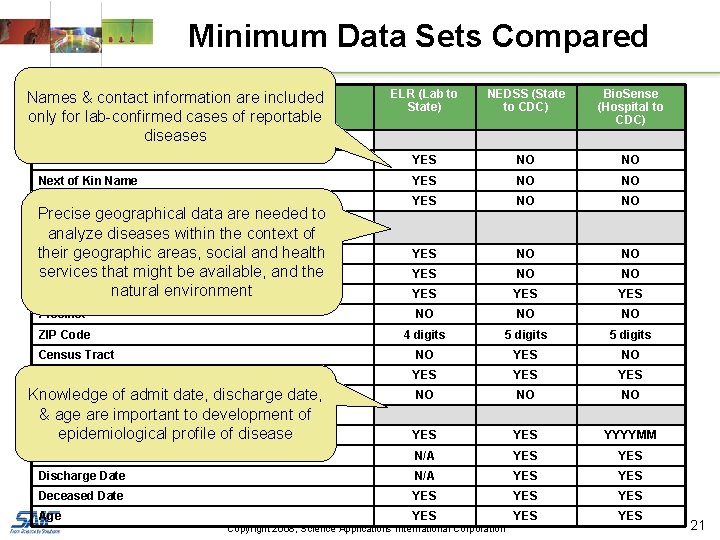
Minimum Data Sets Compared HIPAA&De-Identification Data Elements Names contact information are included only for lab-confirmed cases of reportable diseases (A) NAMES ELR (Lab to State) NEDSS (State to CDC) Bio. Sense (Hospital to CDC) Patient Name YES NO NO Next of Kin Name YES NO NO Provider Names YES NO NO YES YES Precinct NO NO NO ZIP Code 4 digits 5 digits Census Tract NO YES NO State YES YES NO NO NO YES YYYYMM Admit Date N/A YES Discharge Date N/A YES Deceased Date YES YES YES Precise geographical data are needed to (B) GEOGRAPHIC SUBDIVISIONS SMALLER THAN STATE analyze diseases within the context of their areas, social and health Street geographic Address services that might be available, and the City natural environment County Equivalent Geocode Knowledge of admit date, discharge date, (C) DATES & age are(YYYYMMDD) important to development of epidemiological profile of disease Date of Birth Age Copyright 2008, Science Applications International Corporation 21
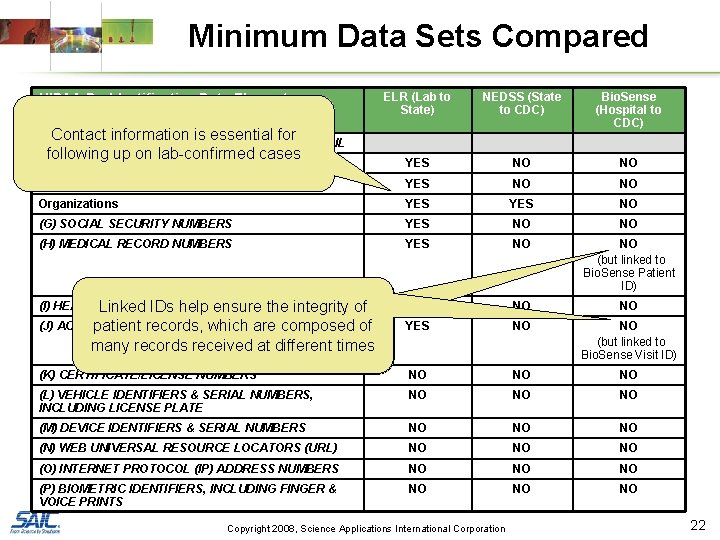
Minimum Data Sets Compared HIPAA De-Identification Data Elements ELR (Lab to State) NEDSS (State to CDC) Bio. Sense (Hospital to CDC) Patient/Next of Kin YES NO NO Providers YES NO NO Organizations YES NO (G) SOCIAL SECURITY NUMBERS YES NO NO (H) MEDICAL RECORD NUMBERS YES NO NO (but linked to Bio. Sense Patient ID) (I) HEALTHLinked PLAN BENEFICIARY NUMBERS IDs help ensure the Contact information is essential for following up on lab-confirmed cases (D-F) TELEPHONE NUMBERS, FAX NUMBERS, EMAIL integrity of (J) ACCOUNT NUMBERS patient records, which are composed of many records received at different times NO NO NO YES NO NO (but linked to Bio. Sense Visit ID) (K) CERTIFICATE/LICENSE NUMBERS NO NO NO (L) VEHICLE IDENTIFIERS & SERIAL NUMBERS, INCLUDING LICENSE PLATE NO NO NO (M) DEVICE IDENTIFIERS & SERIAL NUMBERS NO NO NO (N) WEB UNIVERSAL RESOURCE LOCATORS (URL) NO NO NO (O) INTERNET PROTOCOL (IP) ADDRESS NUMBERS NO NO NO (P) BIOMETRIC IDENTIFIERS, INCLUDING FINGER & VOICE PRINTS NO NO NO Copyright 2008, Science Applications International Corporation 22
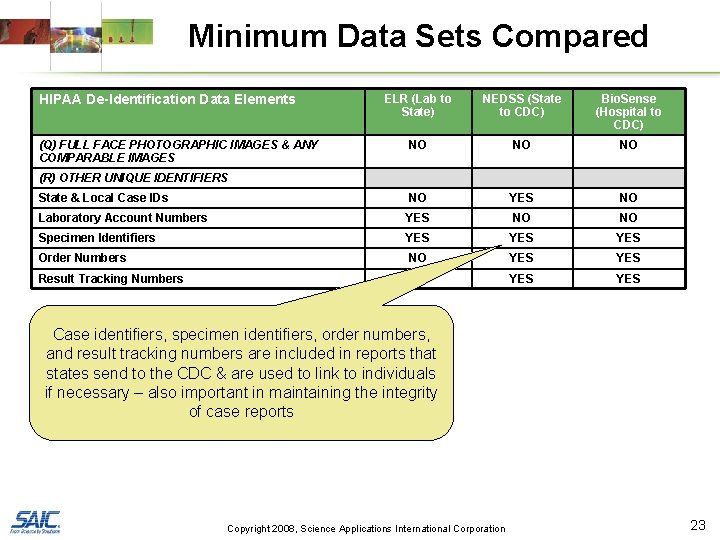
Minimum Data Sets Compared HIPAA De-Identification Data Elements ELR (Lab to State) NEDSS (State to CDC) Bio. Sense (Hospital to CDC) NO NO NO State & Local Case IDs NO YES NO Laboratory Account Numbers YES NO NO Specimen Identifiers YES YES Order Numbers NO YES Result Tracking Numbers YES YES (Q) FULL FACE PHOTOGRAPHIC IMAGES & ANY COMPARABLE IMAGES (R) OTHER UNIQUE IDENTIFIERS Case identifiers, specimen identifiers, order numbers, and result tracking numbers are included in reports that states send to the CDC & are used to link to individuals if necessary – also important in maintaining the integrity of case reports Copyright 2008, Science Applications International Corporation 23
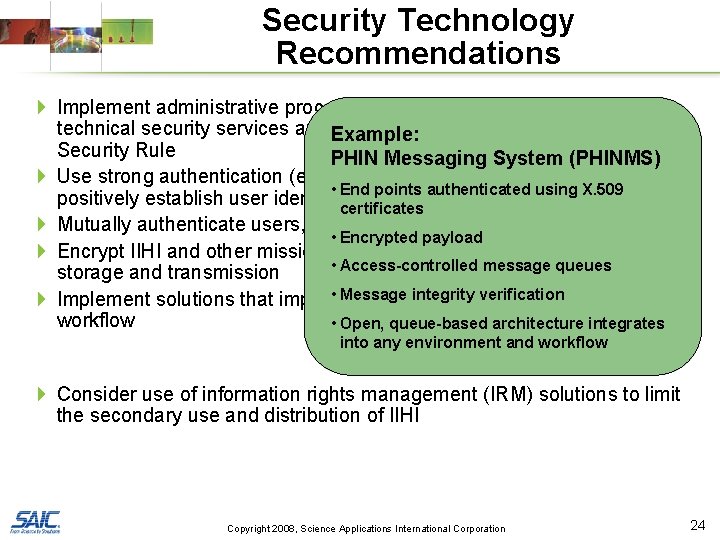
Security Technology Recommendations 4 Implement administrative procedures, physical safeguards, and technical security services and Example: mechanisms specified in HIPAA Security Rule PHIN Messaging System (PHINMS) 4 Use strong authentication (e. g. , password plus X. 509 certificate) to • End points authenticated using X. 509 positively establish user identity certificates 4 Mutually authenticate users, end points, and web applications • Encrypted payload 4 Encrypt IIHI and other mission-critical public health data for both • Access-controlled message queues storage and transmission • Message verification 4 Implement solutions that impose minimalintegrity disruption and delay in the workflow • Open, queue-based architecture integrates into any environment and workflow 4 Consider use of information rights management (IRM) solutions to limit the secondary use and distribution of IIHI Copyright 2008, Science Applications International Corporation 24
Summary 4 Detecting biological events as near to the time of initial exposure as possible can significantly reduce the health risk to the public – but at the same time introduces risks to personal privacy 4 HIPAA explicitly enables public health to use protected health information without individual authorization – must assure that “minimum necessary” is collected 4 Achieving and maintaining an optimal balance between individual privacy and population safety is a continuous challenge for public health at all jurisdictional levels and in all functional areas Copyright 2008, Science Applications International Corporation 25
- Slides: 25