PUBLIC Dynamic Cyber Threats and Cyber Resilience Robert
PUBLIC Dynamic Cyber Threats and Cyber Resilience Robert Duncan, CISO 16 June 2016 "What's past is prologue. "-- The Tempest

About Direct. Line Group Direct Line Group plc is a FTSE 100 constituent. 11, 000 Employees UK home insurance market share: 17% 2 UK personal motor market share: 14% PUBLIC We provide insurance products via brand partners such as Nationwide, The Royal Bank of Scotland, Sainsbury’s, Nat. West and Prudential plc. A number of sites in the UK Commercial: 0. 7 million in-force policies Rescue and other personal lines: 8. 3 million in-force policies
Two hypothetical firms, which would you insure? PUBLIC Firm 1: ISO 27001 certified Only buys ‘top vendors’ NIST Framework aligned – hundreds of pages of evidence Audited 4 times in a year, with thousands of hours spent between the internal audit team and CISO team to ‘prove’ security Strong 3 lines of defence model, ‘Risk acceptances’ to decide on investments in additional controls vs ‘acceptances’ Firm 2: Guided by NIST or other framework Deploys ‘top’ vendors and startups(creative yet unproven) On site Red Team and/or Internal Penetration testers constantly adapting controls – empowered to push fixes External firms invited in regularly to test controls and issue reports to Audit and 2 nd line Risk 3
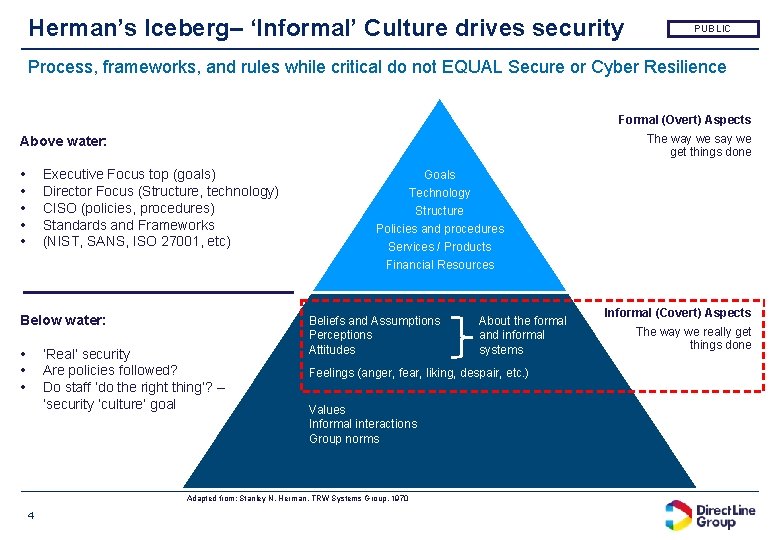
Herman’s Iceberg– ‘Informal’ Culture drives security PUBLIC Process, frameworks, and rules while critical do not EQUAL Secure or Cyber Resilience Formal (Overt) Aspects The way we say we get things done Above water: • • • Executive Focus top (goals) Director Focus (Structure, technology) CISO (policies, procedures) Standards and Frameworks (NIST, SANS, ISO 27001, etc) Below water: • • • ‘Real’ security Are policies followed? Do staff ‘do the right thing’? – ‘security ‘culture’ goal Goals Technology Structure Policies and procedures Services / Products Financial Resources Beliefs and Assumptions Perceptions Attitudes Feelings (anger, fear, liking, despair, etc. ) Values Informal interactions Group norms Adapted from: Stanley N. Herman. TRW Systems Group, 1970 4 About the formal and informal systems Informal (Covert) Aspects The way we really get things done
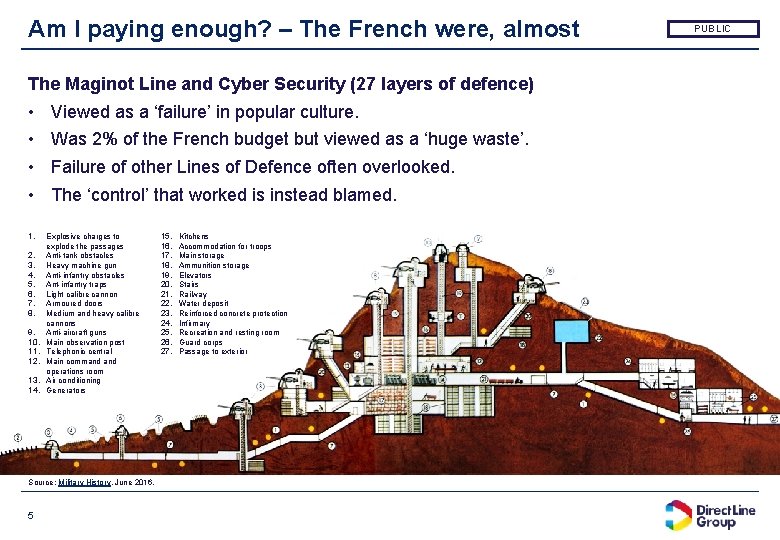
Am I paying enough? – The French were, almost The Maginot Line and Cyber Security (27 layers of defence) • • 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. 11. 12. 13. 14. Viewed as a ‘failure’ in popular culture. Was 2% of the French budget but viewed as a ‘huge waste’. Failure of other Lines of Defence often overlooked. The ‘control’ that worked is instead blamed. Explosive charges to explode the passages Anti-tank obstacles Heavy machine gun Anti-infantry obstacles Ant-infantry traps Light calibre cannon Armoured doors Medium and heavy calibre cannons Anti-aircraft guns Main observation post Telephonic central Main command operations room Air conditioning Generators Source: Military History, June 2016, 5 15. 16. 17. 18. 19. 20. 21. 22. 23. 24. 25. 26. 27. Kitchens Accommodation for troops Main storage Ammunition storage Elevators Stairs Railway Water deposit Reinforced concrete protection Infirmary Recreation and resting room Guard corps Passage to exterior PUBLIC

Am I paying enough … for the right controls? PUBLIC “We could hardly dream of building a kind of great wall of France, which would in any case be far too costly. Instead we have foreseen powerful but flexible means of organizing defence, based on the dual principle of taking full advantage of the terrain and establishing a continuous line of fire everywhere. ” ANDRE MAGINOT, 10 DECEMBER 1929 Other investments were ‘blocked’ due to ‘enough spend’ on the line, and new attack styles (zero days) not considered nor rapid incident response The Maginot line, however, was not to blame for: • The British expeditionary force, Belgium, and French troops in the area suffering German Blitzkrieg attacks. • The Luftwaffe destroying many Allied aircraft on the ground. • The Luftwaffe obtaining air supremacy. 6
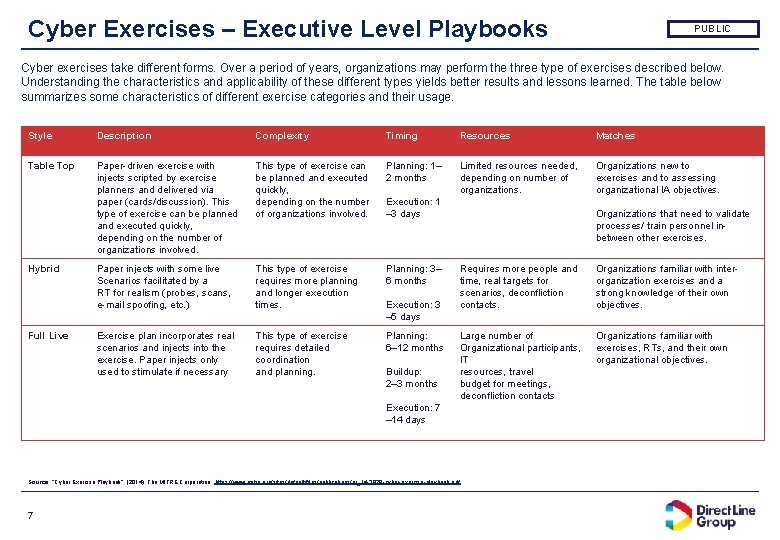
Cyber Exercises – Executive Level Playbooks PUBLIC Cyber exercises take different forms. Over a period of years, organizations may perform the three type of exercises described below. Understanding the characteristics and applicability of these different types yields better results and lessons learned. The table below summarizes some characteristics of different exercise categories and their usage. Style Description Complexity Timing Resources Matches Table Top Paper-driven exercise with injects scripted by exercise planners and delivered via paper (cards/discussion). This type of exercise can be planned and executed quickly, depending on the number of organizations involved. Planning: 1– 2 months Limited resources needed, depending on number of organizations. Organizations new to exercises and to assessing organizational IA objectives. Paper injects with some live Scenarios facilitated by a RT for realism (probes, scans, e-mail spoofing, etc. ) This type of exercise requires more planning and longer execution times. Planning: 3– 6 months Exercise plan incorporates real scenarios and injects into the exercise. Paper injects only used to stimulate if necessary This type of exercise requires detailed coordination and planning. Planning: 6– 12 months Hybrid Full Live Execution: 1 – 3 days Execution: 3 – 5 days Buildup: 2– 3 months Organizations that need to validate processes/ train personnel inbetween other exercises. Requires more people and time, real targets for scenarios, deconfliction contacts. Organizations familiar with inter- organization exercises and a strong knowledge of their own objectives. Large number of Organizational participants, IT resources, travel budget for meetings, deconfliction contacts Organizations familiar with exercises, RTs, and their own organizational objectives. Execution: 7 – 14 days Source: “Cyber Exercise Playbook”, (2014), The MITRE Corporation, https: //www. mitre. org/sites/default/files/publications/pr_14 -3929 -cyber-exercise-playbook. pdf 7
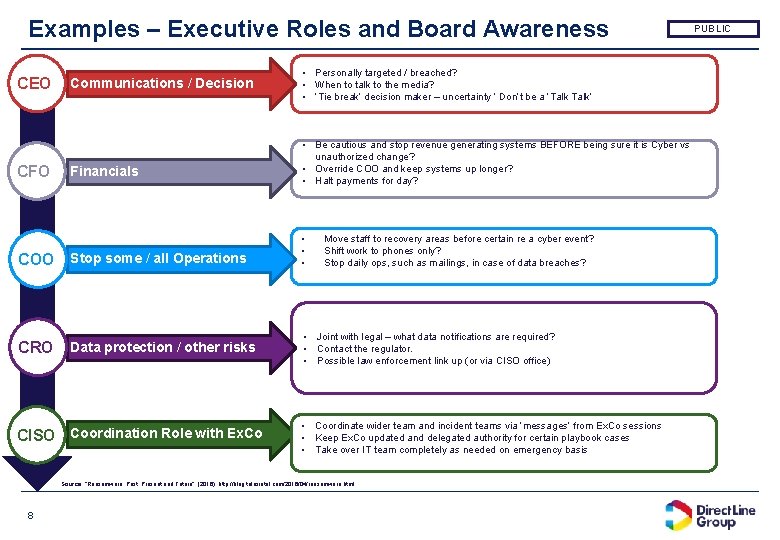
Examples – Executive Roles and Board Awareness CEO CFO Communications / Decision • Personally targeted / breached? • When to talk to the media? • ‘Tie break’ decision maker – uncertainty ‘ Don’t be a ‘Talk’ Financials • Be cautious and stop revenue generating systems BEFORE being sure it is Cyber vs unauthorized change? • Override COO and keep systems up longer? • Halt payments for day? COO Stop some / all Operations CRO Data protection / other risks CISO Coordination Role with Ex. Co • • • Move staff to recovery areas before certain re a cyber event? Shift work to phones only? Stop daily ops, such as mailings, in case of data breaches? • Joint with legal – what data notifications are required? • Contact the regulator. • Possible law enforcement link up (or via CISO office) • Coordinate wider team and incident teams via ‘messages’ from Ex. Co sessions • Keep Ex. Co updated and delegated authority for certain playbook cases • Take over IT team completely as needed on emergency basis Source: “Ransomware: Past, Present and Future”, (2016), http: //blog. talosintel. com/2016/04/ransomware. html 8 PUBLIC
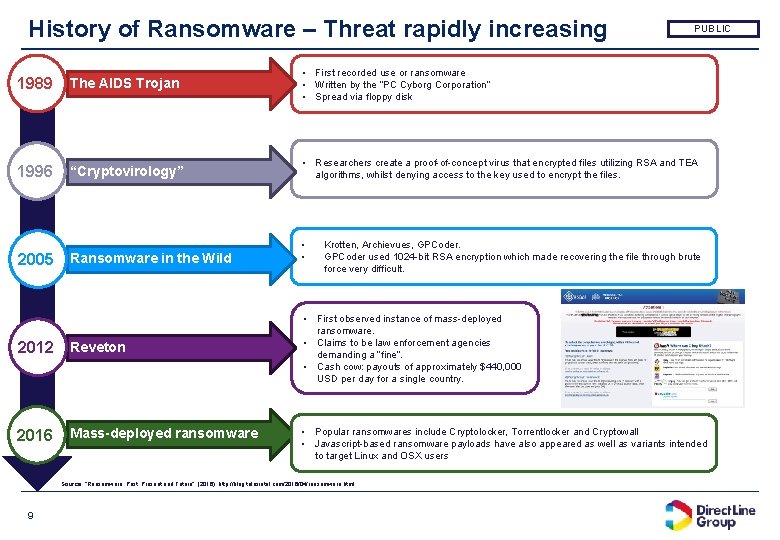
History of Ransomware – Threat rapidly increasing PUBLIC 1989 The AIDS Trojan • First recorded use or ransomware • Written by the “PC Cyborg Corporation” • Spread via floppy disk 1996 “Cryptovirology” • Researchers create a proof-of-concept virus that encrypted files utilizing RSA and TEA algorithms, whilst denying access to the key used to encrypt the files. 2005 Ransomware in the Wild • • 2012 Reveton 2016 Mass-deployed ransomware Krotten, Archievues, GPCoder used 1024 -bit RSA encryption which made recovering the file through brute force very difficult. • First observed instance of mass-deployed ransomware. • Claims to be law enforcement agencies demanding a “fine”. • Cash cow: payouts of approximately $440, 000 USD per day for a single country. • Popular ransomwares include Cryptolocker, Torrentlocker and Cryptowall • Javascript-based ransomware payloads have also appeared as well as variants intended to target Linux and OSX users Source: “Ransomware: Past, Present and Future”, (2016), http: //blog. talosintel. com/2016/04/ransomware. html 9
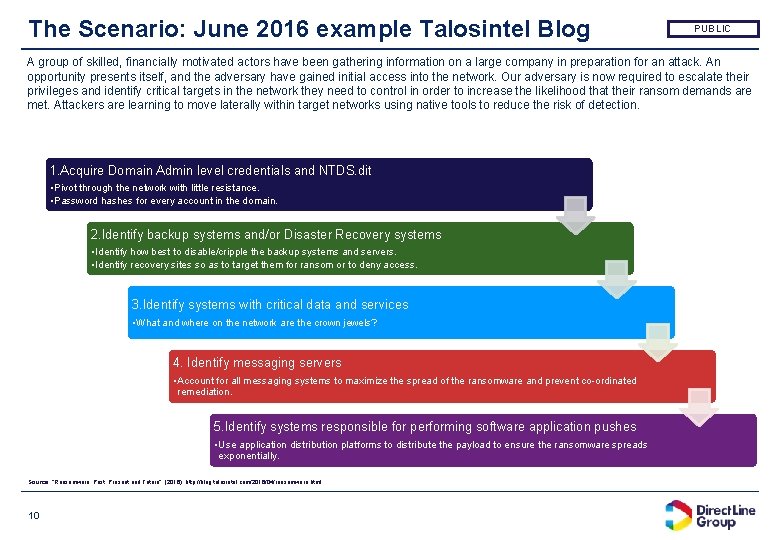
The Scenario: June 2016 example Talosintel Blog PUBLIC A group of skilled, financially motivated actors have been gathering information on a large company in preparation for an attack. An opportunity presents itself, and the adversary have gained initial access into the network. Our adversary is now required to escalate their privileges and identify critical targets in the network they need to control in order to increase the likelihood that their ransom demands are met. Attackers are learning to move laterally within target networks using native tools to reduce the risk of detection. 1. Acquire Domain Admin level credentials and NTDS. dit • Pivot through the network with little resistance. • Password hashes for every account in the domain. 2. Identify backup systems and/or Disaster Recovery systems • Identify how best to disable/cripple the backup systems and servers. • Identify recovery sites so as to target them for ransom or to deny access. 3. Identify systems with critical data and services • What and where on the network are the crown jewels? 4. Identify messaging servers • Account for all messaging systems to maximize the spread of the ransomware and prevent co-ordinated remediation. 5. Identify systems responsible for performing software application pushes • Use application distribution platforms to distribute the payload to ensure the ransomware spreads exponentially. Source: “Ransomware: Past, Present and Future”, (2016), http: //blog. talosintel. com/2016/04/ransomware. html 10
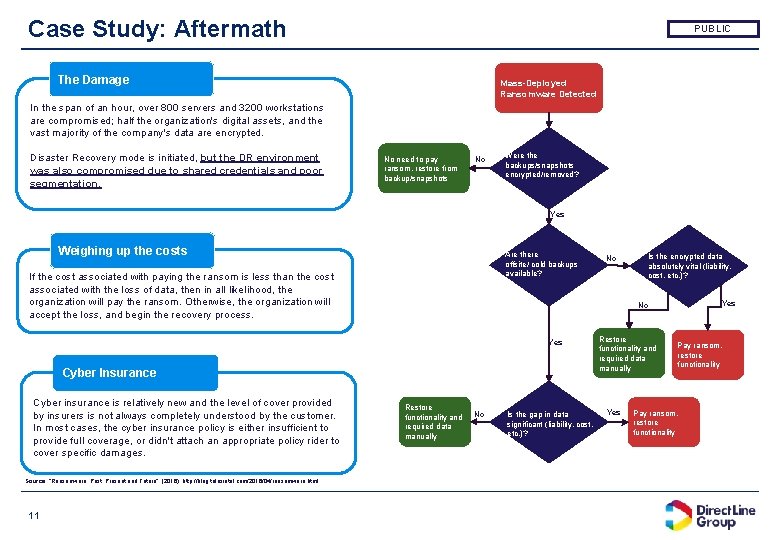
Case Study: Aftermath PUBLIC The Damage Mass-Deployed Ransomware Detected In the span of an hour, over 800 servers and 3200 workstations are compromised; half the organization's digital assets, and the vast majority of the company's data are encrypted. Disaster Recovery mode is initiated, but the DR environment was also compromised due to shared credentials and poor segmentation. No need to pay ransom, restore from backup/snapshots No Were the backups/snapshots encrypted/removed? Yes Weighing up the costs Are there offsite/ cold backups available? If the cost associated with paying the ransom is less than the cost associated with the loss of data, then in all likelihood, the organization will pay the ransom. Otherwise, the organization will accept the loss, and begin the recovery process. Cyber Insurance Source: “Ransomware: Past, Present and Future”, (2016), http: //blog. talosintel. com/2016/04/ransomware. html 11 Is the encrypted data absolutely vital (liability, cost, etc. )? Yes No Yes Cyber insurance is relatively new and the level of cover provided by insurers is not always completely understood by the customer. In most cases, the cyber insurance policy is either insufficient to provide full coverage, or didn't attach an appropriate policy rider to cover specific damages. No Restore functionality and required data manually No Is the gap in data significant (liability, cost, etc. )? Restore functionality and required data manually Yes Pay ransom, restore functionality
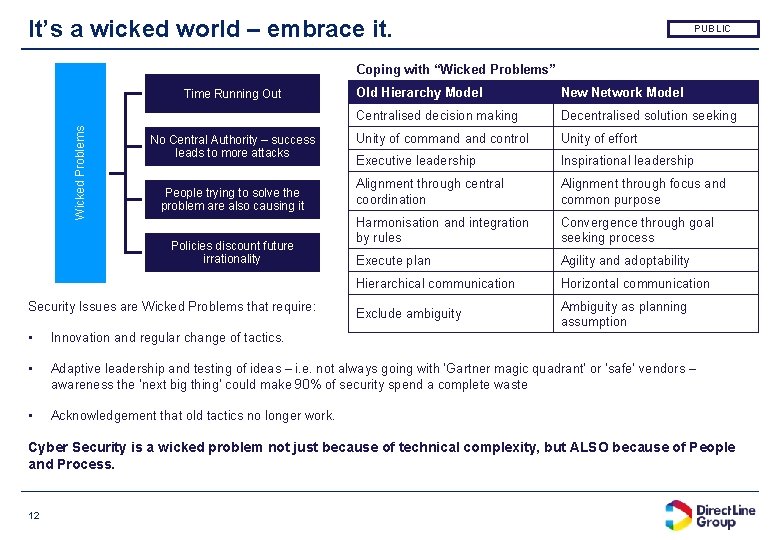
It’s a wicked world – embrace it. PUBLIC Coping with “Wicked Problems” Wicked Problems Time Running Out No Central Authority – success leads to more attacks People trying to solve the problem are also causing it Policies discount future irrationality Security Issues are Wicked Problems that require: Old Hierarchy Model New Network Model Centralised decision making Decentralised solution seeking Unity of command control Unity of effort Executive leadership Inspirational leadership Alignment through central coordination Alignment through focus and common purpose Harmonisation and integration by rules Convergence through goal seeking process Execute plan Agility and adoptability Hierarchical communication Horizontal communication Exclude ambiguity Ambiguity as planning assumption • Innovation and regular change of tactics. • Adaptive leadership and testing of ideas – i. e. not always going with ‘Gartner magic quadrant’ or ‘safe’ vendors – awareness the ‘next big thing’ could make 90% of security spend a complete waste • Acknowledgement that old tactics no longer work. Cyber Security is a wicked problem not just because of technical complexity, but ALSO because of People and Process. 12

PUBLIC 13
- Slides: 13