PseudoRandom Number Generation How it Works What the
Pseudo-Random Number Generation How it Works, What the CIA Knows, and What Options Exist in Perl? February 13 th, 2014 – Houston Perl Mongers Robert Stone Host. Gator. com
Overview • What are Random Number Generators? • Pseudo vs Truly Random • Terms • Sample Types • Perl’s Built In Random Number Generator • Configuration • drand 48 • What the CIA Knows • Elliptic Curve Cryptography • Dual_EC_DRBG Implementation • Snowden, RSA Security and Open. SSL • What Options Exist in Perl? • Best Practices • Modules xkcd
Background – Pseudo vs Truly Random • Truly Random vs Pseudorandom • Sources of True Randomness • Deterministic Random Bit Generator • Why bother with Pseudo Randomness at all? • • Speed Nonblocking Cost Reproducibility Breaking Bad
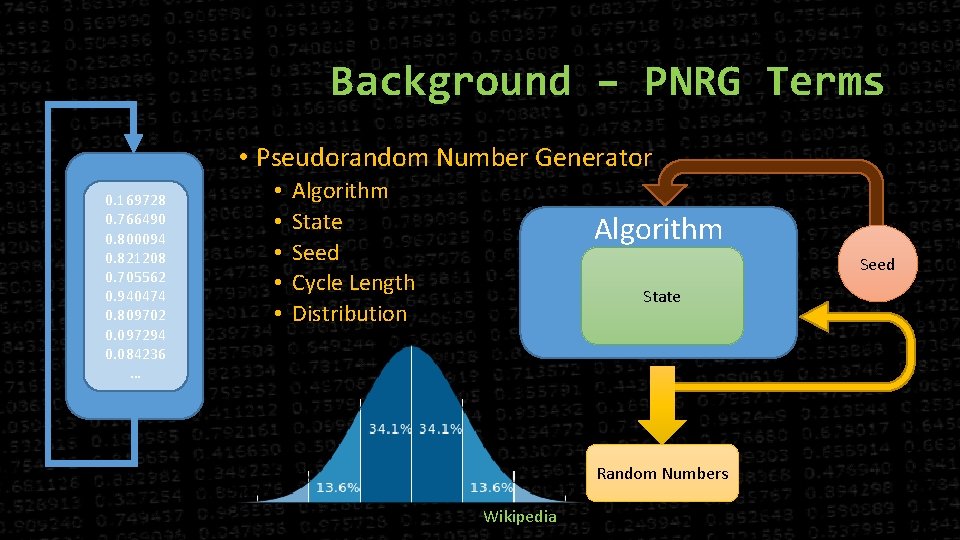
Background – PNRG Terms • Pseudorandom Number Generator 0. 169728 0. 766490 0. 800094 0. 821208 0. 705562 0. 940474 0. 809702 0. 097294 0. 084236 … • • • Algorithm State Seed Cycle Length Distribution Algorithm Seed State Random Numbers Wikipedia
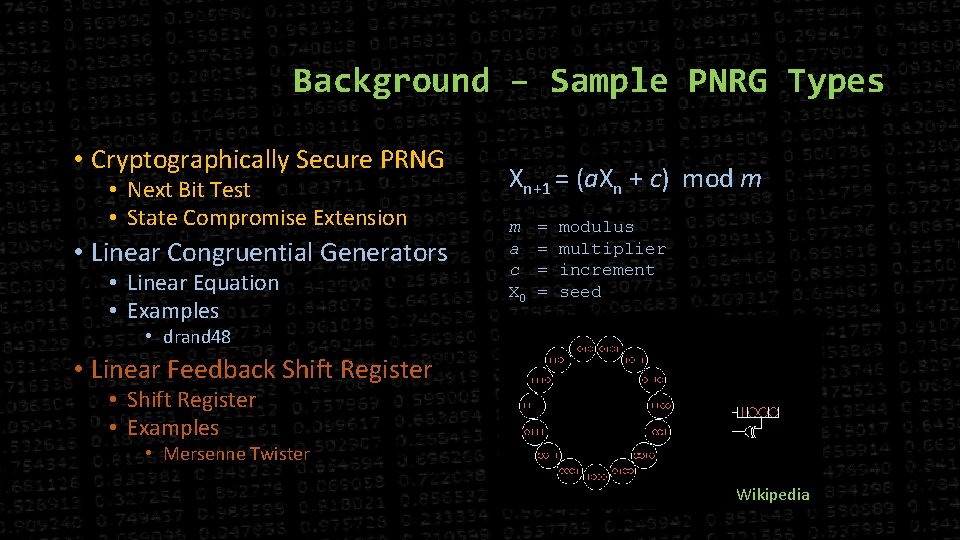
Background – Sample PNRG Types • Cryptographically Secure PRNG • Next Bit Test • State Compromise Extension • Linear Congruential Generators • Linear Equation • Examples Xn+1 = (a. Xn + c) mod m m a c X 0 = = modulus multiplier increment seed • drand 48 • Linear Feedback Shift Register • Examples • Mersenne Twister Wikipedia
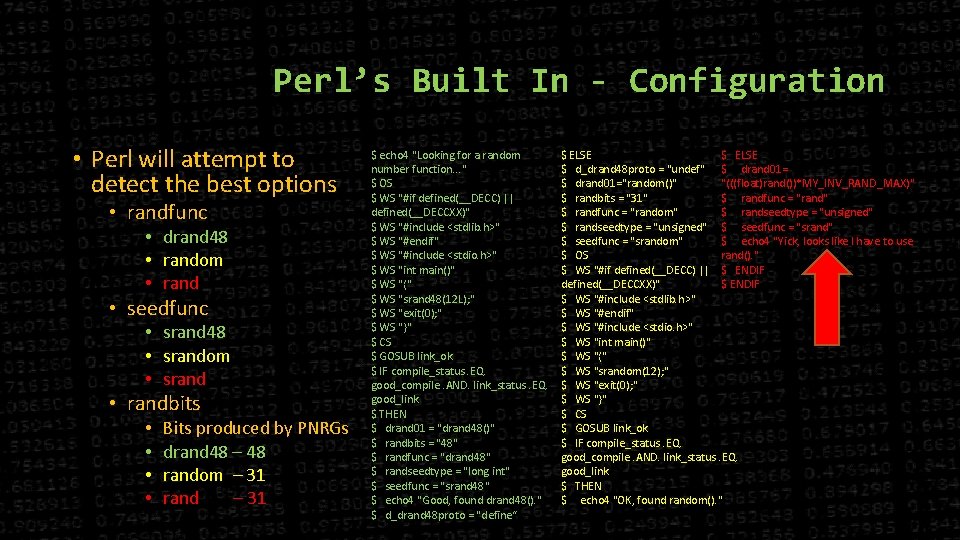
Perl’s Built In - Configuration • Perl will attempt to detect the best options • randfunc • drand 48 • random • rand • seedfunc • srand 48 • srandom • srand • randbits • • Bits produced by PNRGs drand 48 – 48 random – 31 rand – 31 $ echo 4 "Looking for a random number function. . . " $ OS $ WS "#if defined(__DECC) || defined(__DECCXX)" $ WS "#include <stdlib. h>" $ WS "#endif" $ WS "#include <stdio. h>" $ WS "int main()" $ WS "{" $ WS "srand 48(12 L); " $ WS "exit(0); " $ WS "}" $ CS $ GOSUB link_ok $ IF compile_status. EQ. good_compile. AND. link_status. EQ. good_link $ THEN $ drand 01 = "drand 48()" $ randbits = "48" $ randfunc = "drand 48" $ randseedtype = "long int" $ seedfunc = "srand 48" $ echo 4 "Good, found drand 48(). " $ d_drand 48 proto = "define“ $ ELSE $ d_drand 48 proto = "undef" $ drand 01="random()" "(((float)rand())*MY_INV_RAND_MAX)" $ randbits = "31" $ randfunc = "random" $ randseedtype = "unsigned" $ seedfunc = "srandom" $ echo 4 "Yick, looks like I have to use $ OS rand(). " $ WS "#if defined(__DECC) || $ ENDIF defined(__DECCXX)" $ ENDIF $ WS "#include <stdlib. h>" $ WS "#endif" $ WS "#include <stdio. h>" $ WS "int main()" $ WS "{" $ WS "srandom(12); " $ WS "exit(0); " $ WS "}" $ CS $ GOSUB link_ok $ IF compile_status. EQ. good_compile. AND. link_status. EQ. good_link $ THEN $ echo 4 "OK, found random(). "
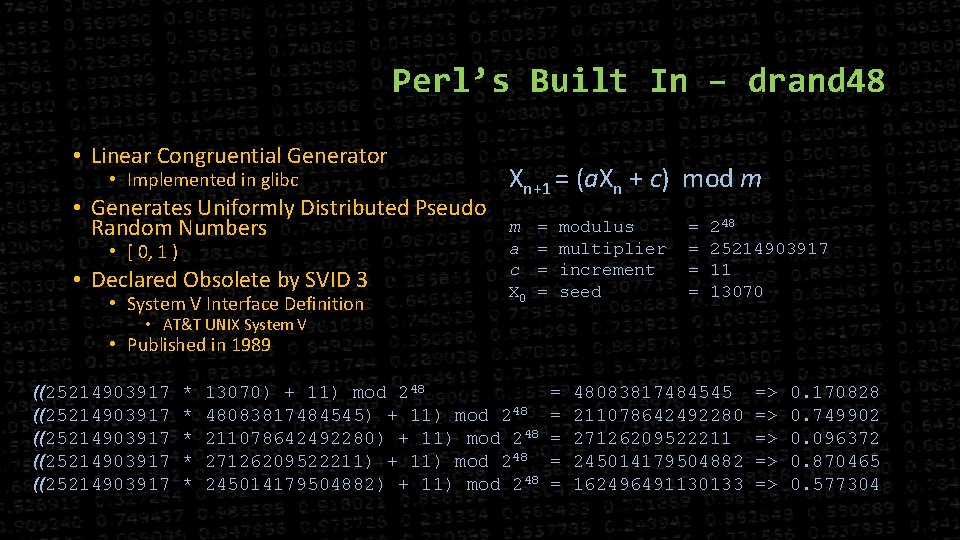
Perl’s Built In – drand 48 • Linear Congruential Generator • Implemented in glibc • Generates Uniformly Distributed Pseudo Random Numbers • [ 0, 1 ) • Declared Obsolete by SVID 3 • System V Interface Definition Xn+1 = (a. Xn + c) mod m m a c X 0 = = modulus multiplier increment seed = = 248 25214903917 11 13070 • AT&T UNIX System V • Published in 1989 ((25214903917 ((25214903917 * * * 13070) + 11) mod 248 48083817484545) + 11) mod 248 211078642492280) + 11) mod 248 27126209522211) + 11) mod 248 245014179504882) + 11) mod 248 = = = 48083817484545 211078642492280 27126209522211 245014179504882 162496491130133 => => => 0. 170828 0. 749902 0. 096372 0. 870465 0. 577304
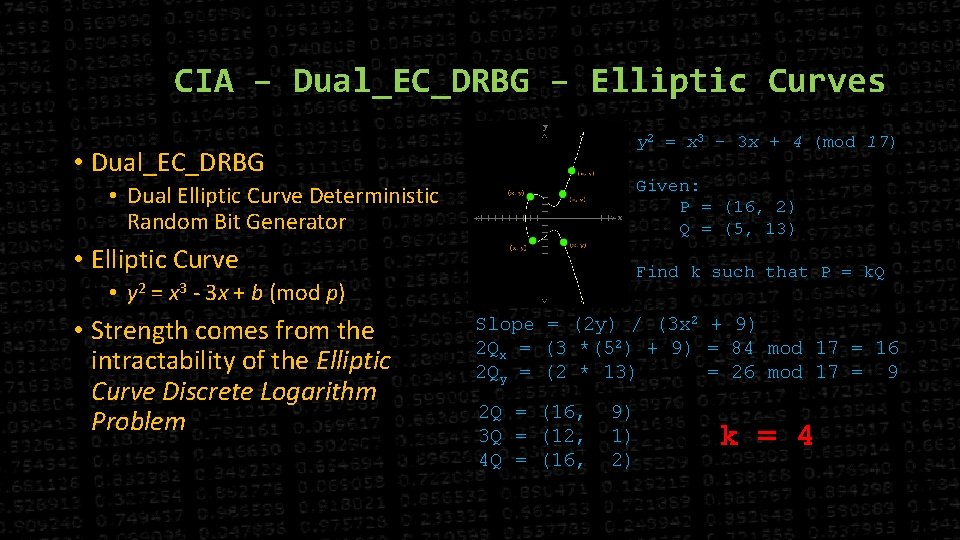
CIA – Dual_EC_DRBG – Elliptic Curves y 2 = x 3 - 3 x + 4 (mod 17) • Dual_EC_DRBG Given: P = (16, 2) Q = (5, 13) • Dual Elliptic Curve Deterministic Random Bit Generator • Elliptic Curve Find k such that P = k. Q • y 2 = x 3 - 3 x + b (mod p) • Strength comes from the intractability of the Elliptic Curve Discrete Logarithm Problem Slope = (2 y) / (3 x 2 + 9) 2 Qx = (3 *(52) + 9) = 84 mod 17 = 16 2 Qy = (2 * 13) = 26 mod 17 = 9 2 Q = (16, 3 Q = (12, 4 Q = (16, 9) 1) 2) k = 4
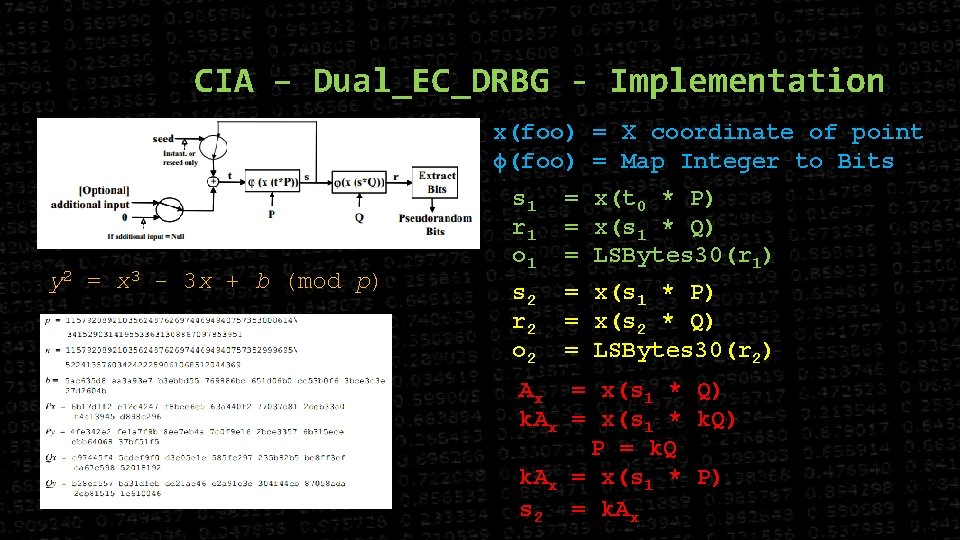
CIA – Dual_EC_DRBG - Implementation x(foo) = X coordinate of point ϕ(foo) = Map Integer to Bits y 2 = x 3 - 3 x + b (mod p) s 1 r 1 o 1 = x(t 0 * P) = x(s 1 * Q) = LSBytes 30(r 1) s 2 r 2 o 2 = x(s 1 * P) = x(s 2 * Q) = LSBytes 30(r 2) Ax = x(s 1 * Q) k. Ax = x(s 1 * k. Q) P = k. Q k. Ax = x(s 1 * P) s 2 = k. Ax
CIA – Dual_EC_DRBG - Backdoor • Does anyone know what k is? • Dan Schumow and Niels Ferguson • “On the Possibility of a Back Door in the NIST SP 800 -90 Dual EC Prng” in August 2007 • Edward Snowden • September 5 th, 2013 project Bullrun Leaked • Leaked Documents and NY Times Saying YES! • The N. S. A. wrote the standard and aggressively pushed it on the international group, privately calling the effort “a challenge in finesse. ” • “Eventually, N. S. A. became the sole editor, ” the memo says. • SSL • RSA BSAFE • $10 Million to Make Default • Open. SSL • Never actually worked due to a one line bug in fips_drbg_ec. c Wikipedia
Perl – Best Practices • Know Your Purpose and Your Goals • Do I really need a CSPRNG? • What is at risk? • Know Your Configuration • DON’T SEED SRAND WITH TIME!
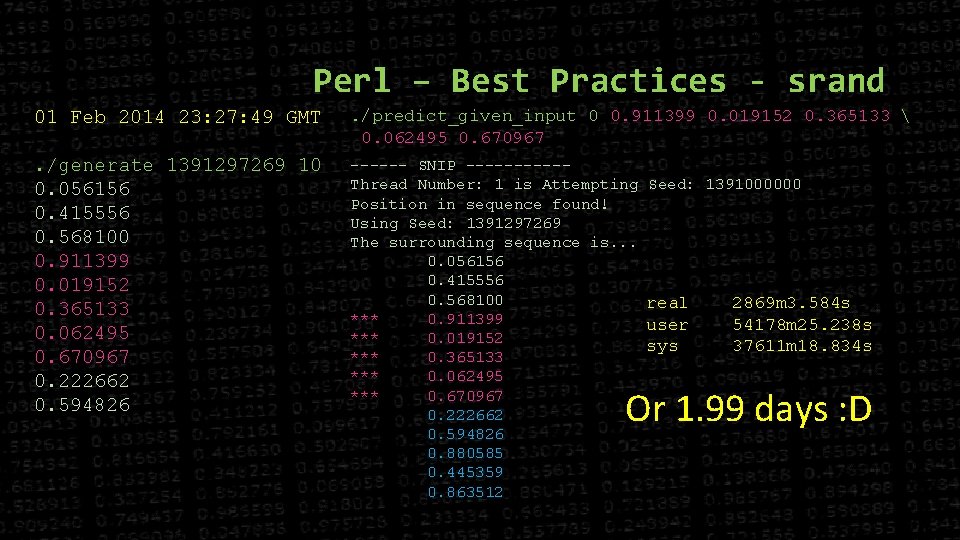
Perl – Best Practices - srand 01 Feb 2014 23: 27: 49 GMT . /predict_given_input 0 0. 911399 0. 019152 0. 365133 0. 062495 0. 670967 . /generate 1391297269 10 0. 056156 0. 415556 0. 568100 0. 911399 0. 019152 0. 365133 0. 062495 0. 670967 0. 222662 0. 594826 ------ SNIP -----Thread Number: 1 is Attempting Position in sequence found! Using Seed: 1391297269 The surrounding sequence is. . . 0. 056156 0. 415556 0. 568100 *** 0. 911399 *** 0. 019152 *** 0. 365133 *** 0. 062495 *** 0. 670967 0. 222662 0. 594826 0. 880585 0. 445359 0. 863512 Seed: 1391000000 real user sys 2869 m 3. 584 s 54178 m 25. 238 s 37611 m 18. 834 s Or 1. 99 days : D
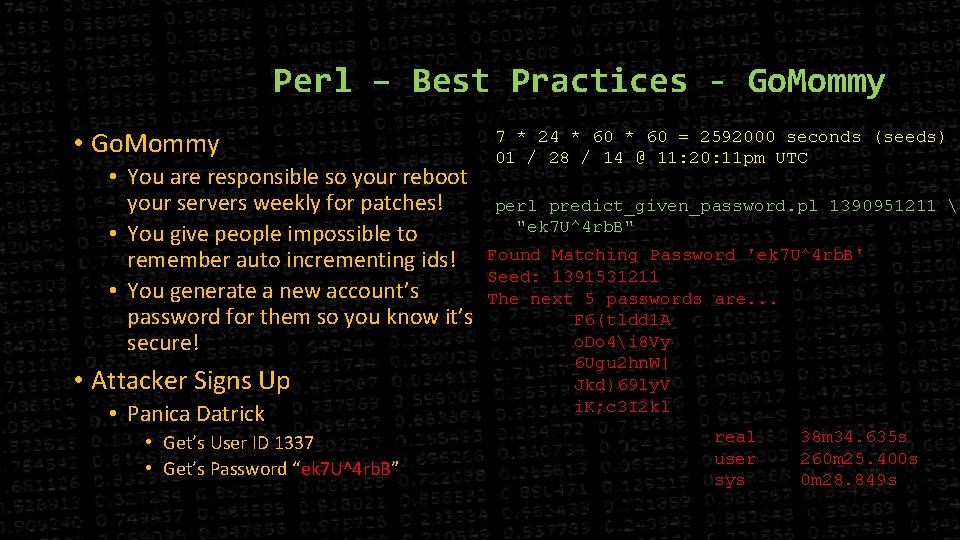
Perl – Best Practices - Go. Mommy • You are responsible so your reboot your servers weekly for patches! • You give people impossible to remember auto incrementing ids! • You generate a new account’s password for them so you know it’s secure! • Attacker Signs Up • Panica Datrick • Get’s User ID 1337 • Get’s Password “ek 7 U^4 rb. B” 7 * 24 * 60 = 2592000 seconds (seeds) 01 / 28 / 14 @ 11: 20: 11 pm UTC perl predict_given_password. pl 1390951211 "ek 7 U^4 rb. B" Found Matching Password 'ek 7 U^4 rb. B' Seed: 1391531211 The next 5 passwords are. . . F 6(tldd 1 A o. Do 4i 8 Vy 6 Ugu 2 hn. W| Jkd)69 ly. V i. K; c 3 I 2 kl real user sys 38 m 34. 635 s 260 m 25. 400 s 0 m 28. 849 s
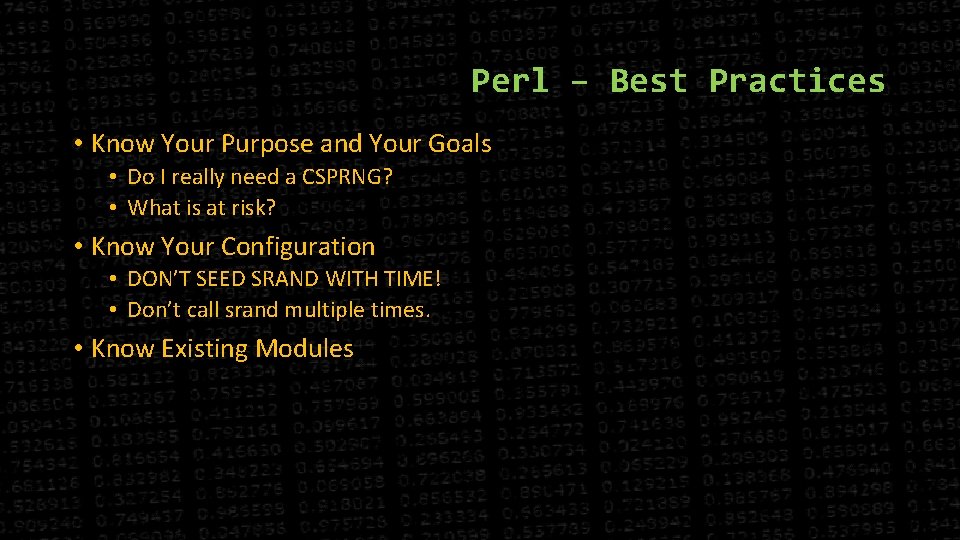
Perl – Best Practices • Know Your Purpose and Your Goals • Do I really need a CSPRNG? • What is at risk? • Know Your Configuration • DON’T SEED SRAND WITH TIME! • Don’t call srand multiple times. • Know Existing Modules
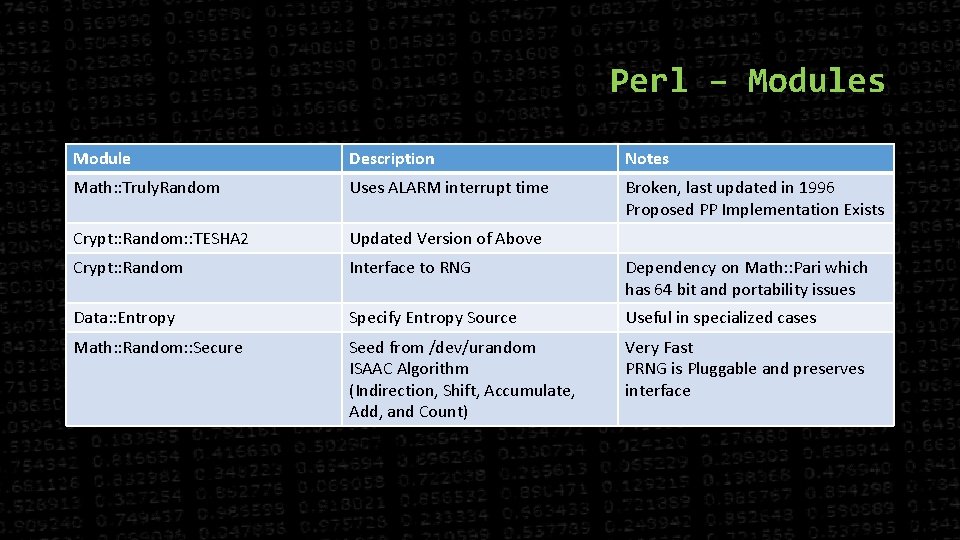
Perl – Modules Module Description Notes Math: : Truly. Random Uses ALARM interrupt time Broken, last updated in 1996 Proposed PP Implementation Exists Crypt: : Random: : TESHA 2 Updated Version of Above Crypt: : Random Interface to RNG Dependency on Math: : Pari which has 64 bit and portability issues Data: : Entropy Specify Entropy Source Useful in specialized cases Math: : Random: : Secure Seed from /dev/urandom ISAAC Algorithm (Indirection, Shift, Accumulate, Add, and Count) Very Fast PRNG is Pluggable and preserves interface
Questions ? • Learn More! • Numberphile (these guys rock!) • http: //youtu. be/ulg_AHBOIQU • Bruce Schneier • https: //www. schneier. com/blog/archives/2007/11/the_strange_sto. html • NIST 800 -90 A • http: //csrc. nist. gov/publications/nistpubs/800 -90 A/SP 800 -90 A. pdf
- Slides: 16