Protocol Verification for Cellular Networks Chunyi Peng The
- Slides: 12
Protocol Verification for Cellular Networks Chunyi Peng The Ohio State University
2 Protocol Verification is Gaining Momentum 2 Protocol verification for the Internet Since 1990 s Single protocol with implementation Emerging techniques for network verification E. g. , Anteater [SIGCOMM’ 11], Head Space Analysis[NSDI’ 12], NICE [NSDI’ 12], Alloy[SIGCOMM’ 13], Net. Check[NSDI’ 14], Software Dataplane [NSDI’ 14] … Largely unexplored territory in cellular networks 2 E. g. , [Cohrs’ 89, SIGCOMM], [Holzmann’ 91], [Smith’ 96], TCP [NSDI’ 04], Routing[SIGCOMM’ 05], … Few efforts, e. g. , 2 G handoff [Orava’ 92], Authentication [Tang’ 13]
Case for PV in Cellular Networks 3 Historically, cellular network protocols did not go through rigorous screening by the research community Cellular Protocol Characteristics Technical Challenges Key Research Aspects
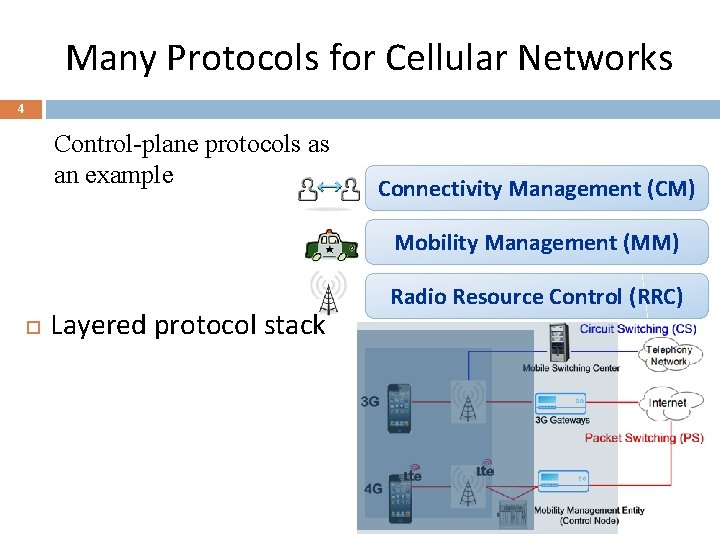
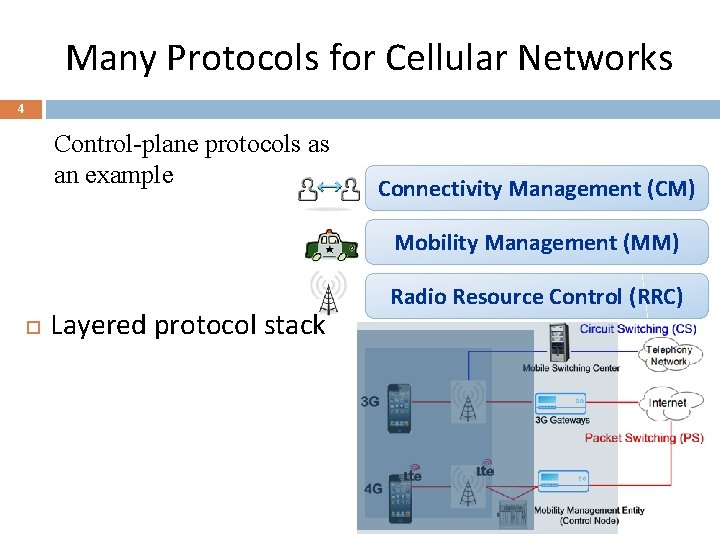
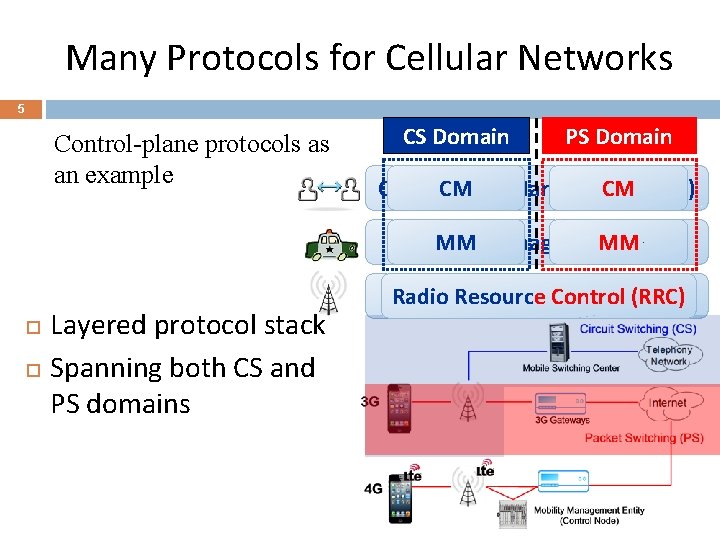
Many Protocols for Cellular Networks 4 Control-plane protocols as an example Connectivity Management (CM) Mobility Management (MM) Layered protocol stack Radio Resource Control (RRC)
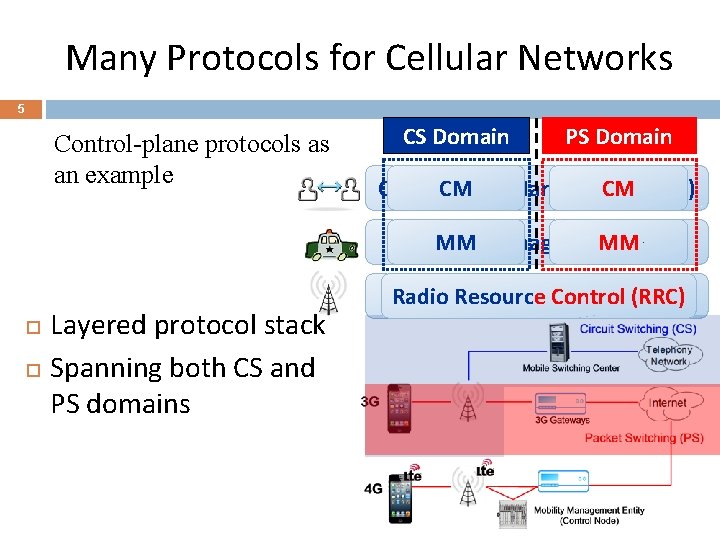
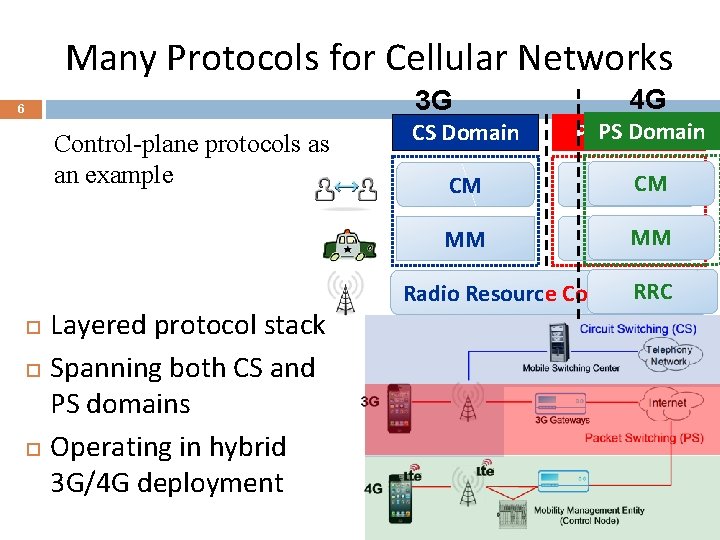
Many Protocols for Cellular Networks 5 Control-plane protocols as an example CS Domain PS Domain Connectivity CM Management CM (CM) Mobility MM Management MM (MM) Layered protocol stack Spanning both CS and PS domains Radio Resource Control (RRC)
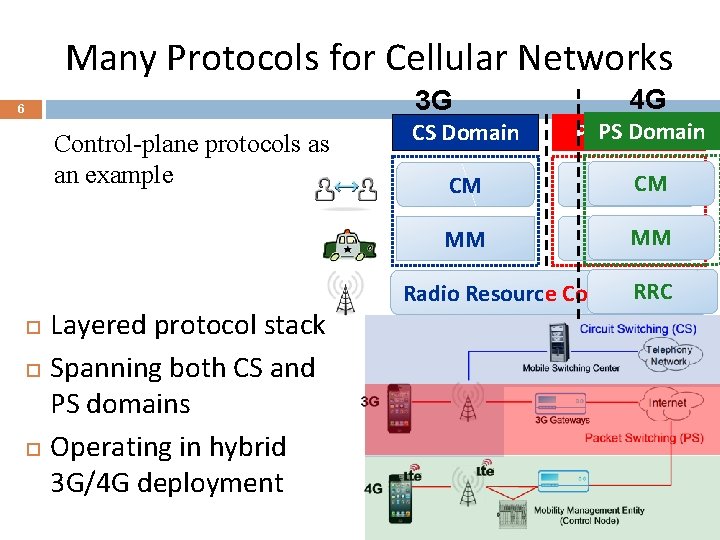
Many Protocols for Cellular Networks 3 G 6 Control-plane protocols as an example Layered protocol stack Spanning both CS and PS domains Operating in hybrid 3 G/4 G deployment 4 G CS Domain PSPS Domain CM CMCM MM MM MM Radio Resource Control. RRC (RRC)
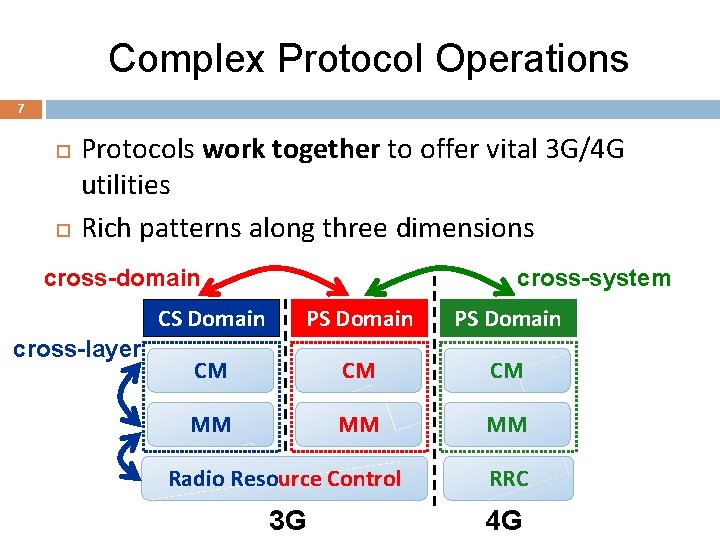
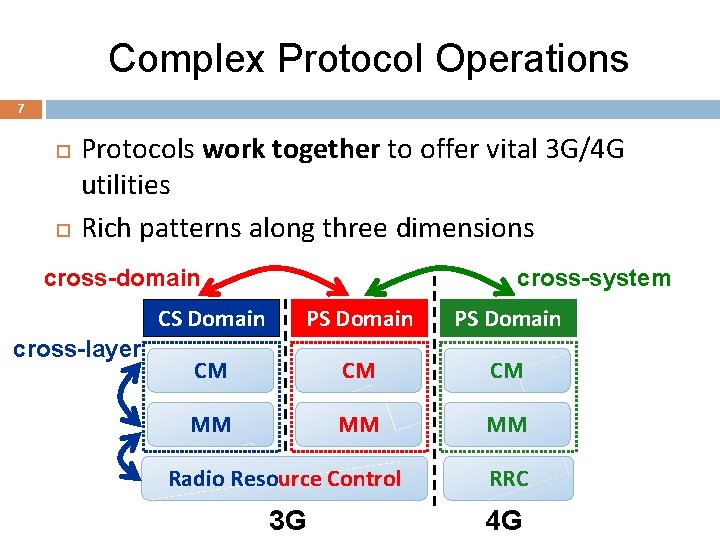
Complex Protocol Operations 7 Protocols work together to offer vital 3 G/4 G utilities Rich patterns along three dimensions cross-domain cross-layer cross-system CS Domain PS Domain CM CM CM MM MM MM Radio Resource Control RRC 3 G 4 G
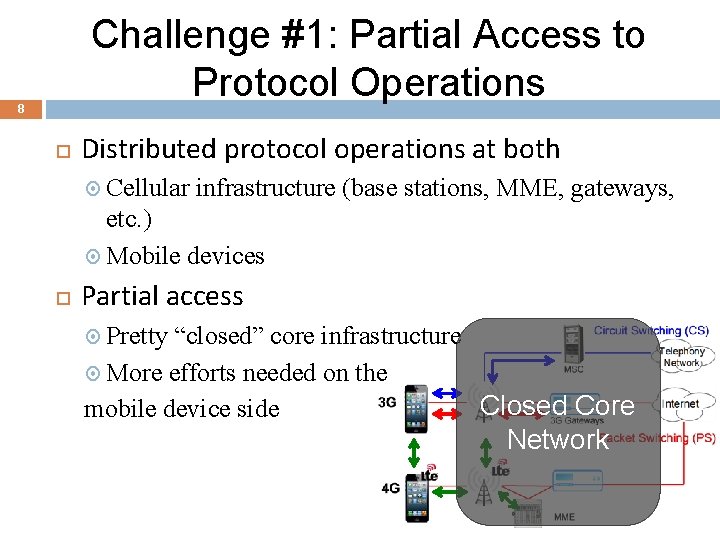
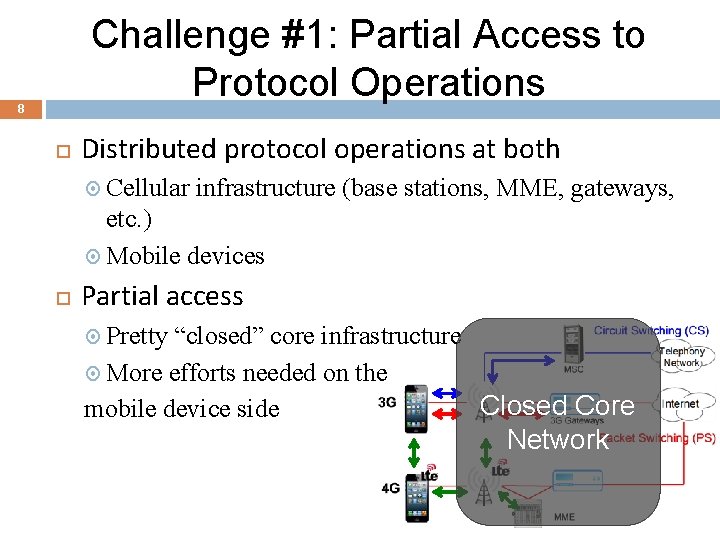
Challenge #1: Partial Access to Protocol Operations 8 Distributed protocol operations at both Cellular infrastructure (base stations, MME, gateways, etc. ) Mobile devices Partial access Pretty “closed” core infrastructure More efforts needed on the Closed Core mobile device side Network 8
Challenge #2: Design & Operation 9 Verification problems stem from both Design specifications Operations Implementations Common-case vs Worst-case No well-defined common cases Lack of wireless net benchmarks Norm rather than exceptions Temporal-Spatial dynamics: Mobility, dynamic radio links
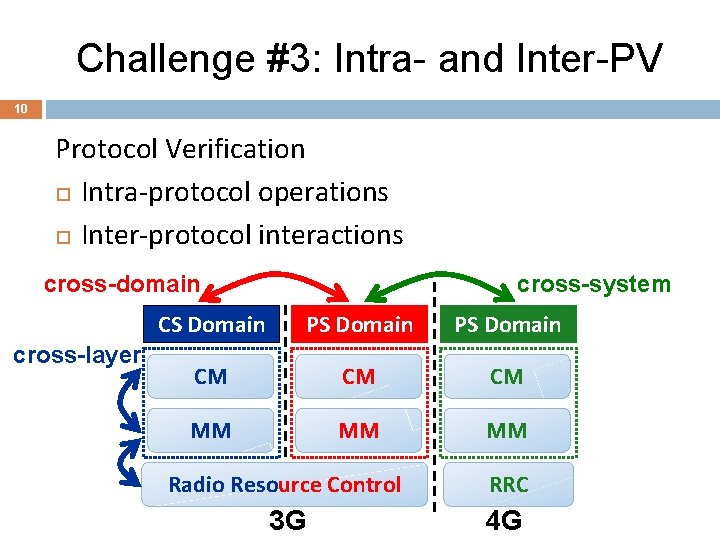
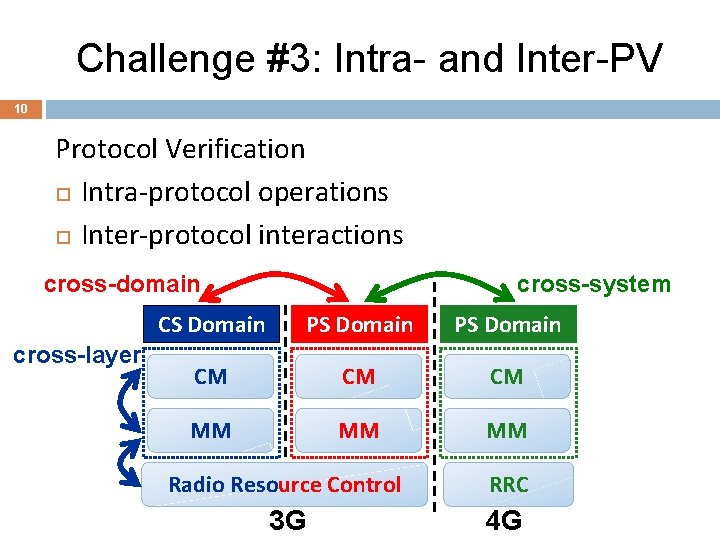
Challenge #3: Intra- and Inter-PV 10 Protocol Verification Intra-protocol operations Inter-protocol interactions cross-domain cross-layer 10 cross-system CS Domain PS Domain CM CM CM MM MM MM Radio Resource Control RRC 3 G 4 G
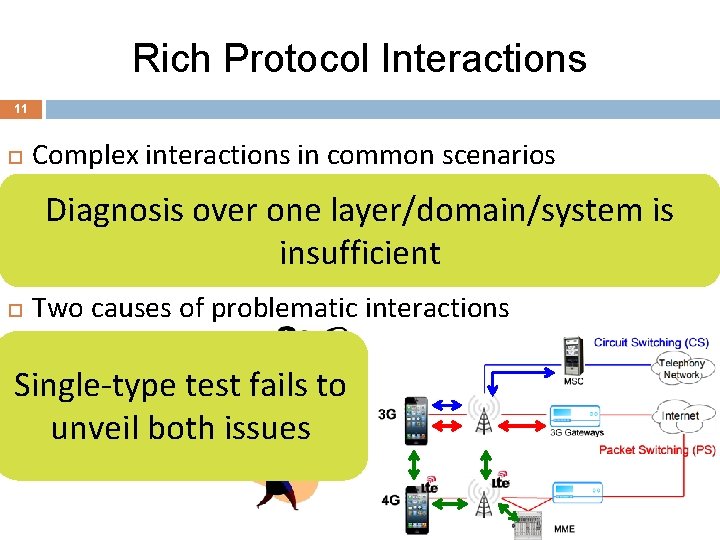
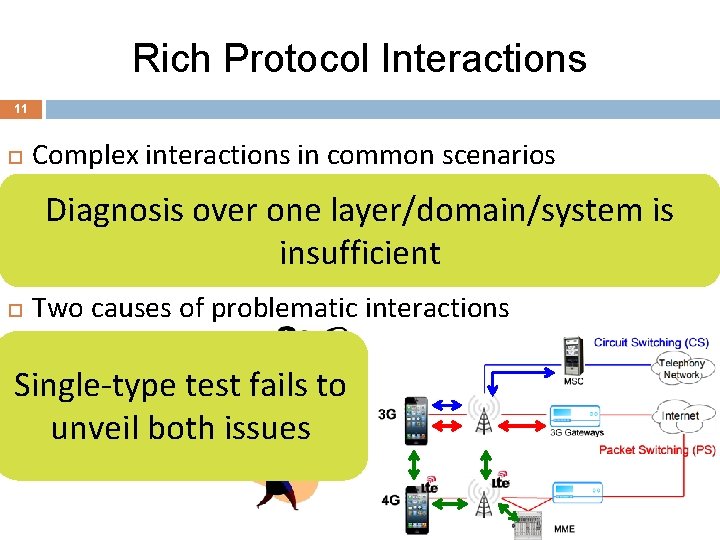
Rich Protocol Interactions 11 Complex interactions in common scenarios Inevitable interplay between radio, mobility, data/voice Diagnosis over one layer/domain/system is Concurrent voice and data use insufficient 3 G/4 G switch due to hybrid deployment, mobility, voice Two causes of problematic interactions Design defects Operation/Implementation Single-type test fails to slips unveil both issues
Research Topics 12 Many Topics remain: New PV Methodology for Cellular Networks (in)Validation of Results Software Tools for Automated Verification for “Results from Protocol Verification Research” Needs community testbed and data archive We are still at starting stage of PV research