PROTOCOL ARCHITECTURE TCPIP AND INTERNETBASED APPLICATIONS A A
PROTOCOL ARCHITECTURE, TCP/IP, AND INTERNET-BASED APPLICATIONS A. A. Waseem & Waleej Haider 1
OSI MODEL n n The OSI (Open Systems Interconnection) model was introduced by ISO (International Standards Organization) It is a multinational body dedicated to worldwide agreement on international standards that covers all aspects of network communications The purpose of the OSI model is to show to facilitate communication between different systems without requiring changes to the logic of the underlying hardware and software. The OSI model is not a protocol; it is a model for understanding and designing a network architecture A. A. Waseem & Waleej Haider 2 that is flexible, robust, and interoperable.
OSI MODEL n n n The OSI model divides the functions of a protocol into a series of layers. Each layer has the property that it only uses the functions of the layer below, and only exports functionality to the layer above. A system that implements protocol behavior consisting of a series of these layers is known as a 'protocol stack' or 'stack'. Protocol stacks can be implemented either in hardware or software, or a mixture of both. Typically, only the lower layers are implemented in hardware, with the higher layers being implemented in software. A. A. Waseem & Waleej Haider 3
Cont’d n n OSI model is roughly stick on in the computing and networking industry. Its main feature is in the interface between layers which dictates the conditions (specifications) on how one layer interacts with another. This means that a layer written by one manufacturer can operate with a layer from another (assuming that the specification is interpreted correctly. ) They are ISO standards in the OSI community. A. A. Waseem & Waleej Haider 4
Cont’d: OSI n n n The logical separation of layers makes reasoning about the behavior of protocol stacks much easier, allowing the design of complex but highly reliable protocol stacks. Within a single machine, each layer performs services for the next higher layer, and makes requests of the next lower layer. An implementation of several OSI layers is often referred to as a stack (as in TCP/IP stack). The OSI reference model is a hierarchical structure of seven layers that defines the requirements for communications between two computers. It was conceived allow interoperability A. A. to Waseem & Waleej Haider 5
Cont’d n n n The model allows all network elements to operate together, regardless of who built them. By the late 1970's, ISO was recommending the implementation of the OSI model as a networking standard. Of course, by that time, TCP/IP had been in use for years. TCP/IP was fundamental to ARPANET and the other networks that evolved into the Internet. Only a subset of the whole OSI model is used today. It is widely believed that much of the specification is too complicated and its full functionality has taken too long to implement 6 A. A. Waseem & Waleej Haider
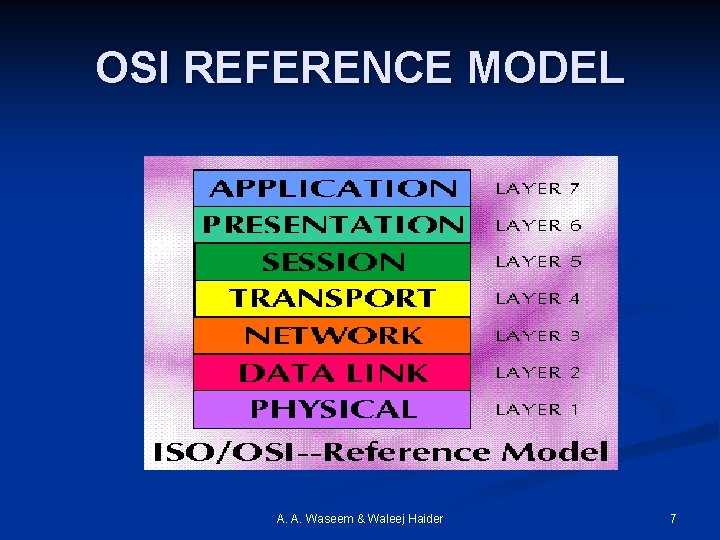
OSI REFERENCE MODEL A. A. Waseem & Waleej Haider 7
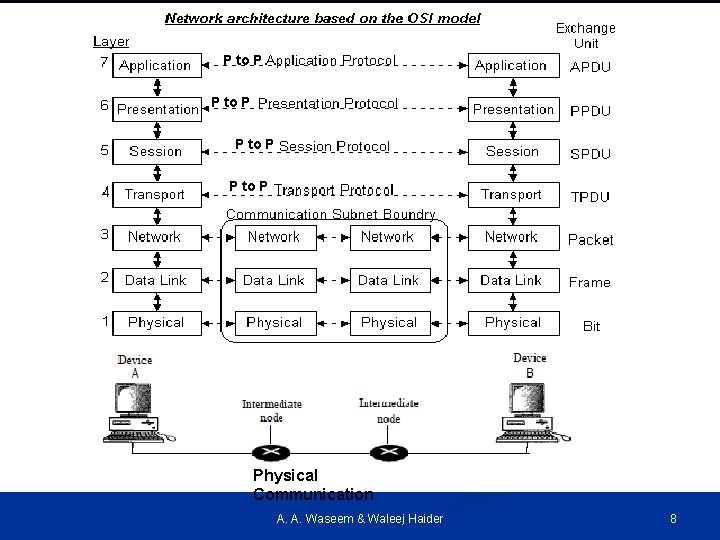
P to P Physical Communication A. A. Waseem & Waleej Haider 8
Layered Architecture Above figure shows the layers involved when a message is sent from device A to device B. n As the message travels from A to B, it may pass through many intermediate nodes. n These intermediate nodes usually involve only the first three layers of the OSI model. n A. A. Waseem & Waleej Haider 9
Layered Architecture (cont. . ) n n Between devices, layer x on one device communicates with layer x on another device. This communication is governed by an agreedupon series of rules and conventions called protocols. The processes on each device that communicate at a given layer are called peer-to-peer processes. Communication between devices is therefore a peer-to-peer process using the protocols appropriate to a given layer. A. A. Waseem & Waleej Haider 10
Interfaces between the Layers n n n As in the Figure below, device A sends a stream of bits to device B (through intermediate nodes). At the higher layers communication must move down through the layers on device A, over to device B, and then back up through the layers Each layer in the sending device adds its own information to the message it receives from the layer just above it and passes the whole package to the layer just below it. At layer I the entire package is converted to a form that can be transmitted to the receiving device. At the receiving machine, the message is unwrapped layer by layer, with each process receiving and removing the data meant for it. A. A. Waseem & Waleej Haider 11
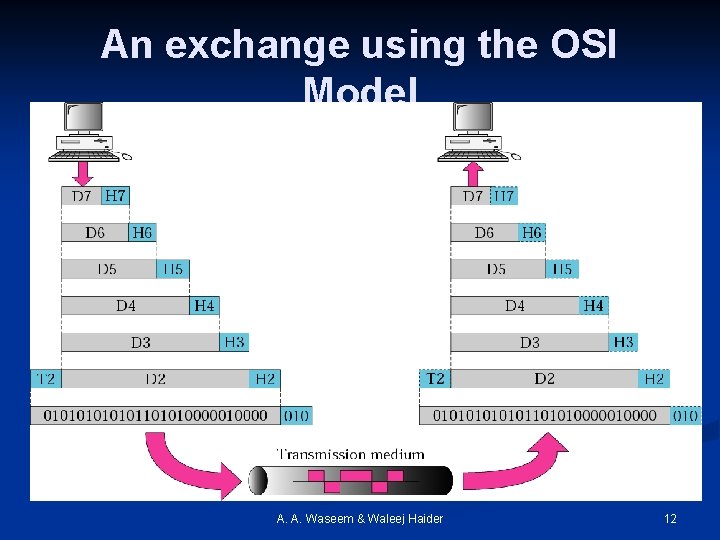
An exchange using the OSI Model A. A. Waseem & Waleej Haider 12
Organization of the Layers n n The seven layers belonging to three subgroups: Layers I, 2, and 3 (physical, data link, and network) are the network support layers They deal with the physical aspects of moving data from one device to another Such as electrical specifications, physical connections, physical addressing, transport timing and reliability A. A. Waseem & Waleej Haider 13
Organization of the Layers(…) n n n Layers 5, 6, and 7(session, presentation, and application) called user support layers They allow interoperability among unrelated software systems. Layer 4, the transport layer, links the two subgroups and ensures that what the lower layers have transmitted is in a form that the upper layers can use. A. A. Waseem & Waleej Haider 14
The 7 Layers of the OSI Model 7) Application : Responsible for providing services to the user, whether human or software, to access the network - This layer provides user interfaces and support for services such as e-mail (SMTP/POP), remote file access and transfer (FTP), shared database management, and other types of network software services (HTTP) - Communication partners are identified, - Quality of service is identified, - User authentication and privacy are considered, and any constraints on data syntax are identified. - Everything at this layer is application-specific. n A. A. Waseem & Waleej Haider 15
Cont. . n Specific services provided by the application layer include the following: • Network virtual terminal– allows a user to log on to a remote host • File transfer, access, and management-- allows a user to access files in a remote host (to make changes or read data) • Mail services-- provides the basis for e-mail forwarding and storage • Directory services--provides distributed database sources and access about various objects and services. A. A. Waseem & Waleej Haider 16
6) Presentation : The presentation layer is responsible for translation, compression, and encryption. It is concerned with the syntax and semantics of the information exchanged between two systems n This layer provides independence from differences in data representation (e. g. , encryption) by translating from application to network format, and vice versa. This layer works to transform data into the form that the application layer can accept. This layer formats and encrypts data to be sent across a network, providing freedom from compatibility problems. It allows devices to be referenced as name rather than address. It is sometimes called syntax layer. Specific responsibilities of the presentation layer includes: • Translation- the message changed into a common format before being transmitted • Encryption- code the sensitive information to another form to ensure privacy and decrypt to original form at the receiver • Compression- reduces the number of bits contained in the 17 A. A. Waseem & Waleej Haider n
n n n 5) Session : Responsible for dialog control and synchronization. This layer is the network dialog controller. It establishes, maintains, and synchronizes the interaction among communicating applications. The session layer sets up, coordinates, and terminates conversations, exchanges, and dialogues between the applications at each end. Specific responsibilities of the session layer includes: n n Dialog control- allows two processes to enter into a dialog, takes place in either half-duplex or full-duplex mode. Synchronization- allows a process to add checkpoints, or synchronization points, to a stream of data. n For example, if a system is sending a file of 2000 pages, it is advisable to insert checkpoints after every 100 pages to ensure that each 100 -page A. unit is received and acknowledged A. Waseem & Waleej Haider independently in order to avoid re-transmission of the whole file 18 if
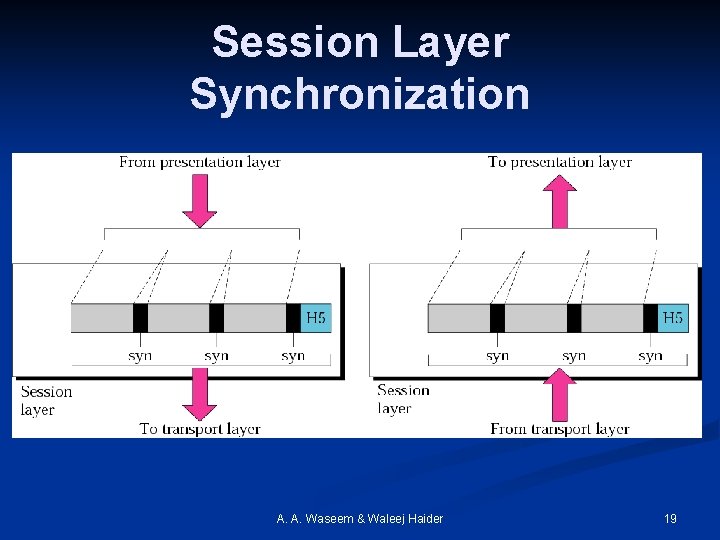
Session Layer Synchronization A. A. Waseem & Waleej Haider 19
n n n 4) Transport : Transport layer is responsible for the delivery of a message from one process to another It is responsible for process-to-process delivery of the entire message. The transport layer ensures that the whole message arrives intact and in order, managing both error control and flow control at the source-to-destination level Other responsibilities of the transport layer includes: Service-point addressing - transport layer header includes a type of address called a service-point address (or port address-16 bit) that gets the entire message to the correct process on that computer. Segmentation and reassembly- A message is divided into transmittable segments, with each segment containing a sequence number. These numbers enable the transport layer to reassemble the message correctly upon arriving at the destination and to identify and replace packets that were lost in transmission. A. A. Waseem & Waleej Haider 20
- Slides: 20