Protecting Your Local Host From Remote Security Attacks




- Slides: 45

Protecting Your Local Host From Remote Security Attacks Jonathon Giffin, Somesh Jha, Bart Miller University of Wisconsin Wi. SA - Jonathon Giffin
Overview • How to Easily do Dangerous and Malicious Things to a Running Job • How to Detect Manipulations of Your Jobs with Pre-Execution Static Analysis and Runtime Monitoring 12/21/2021 Wi. SA - Jonathon Giffin 2
A New View • Running programs are objects to be easily manipulated • The vehicle: the Dyn. Inst API 12/21/2021 Wi. SA - Jonathon Giffin 3
Dyn. Inst: Dynamic Instrumentation • Machine independent library for instrumentation of running processes • Modify control flow of the process: – Load new code into the process – Remove, replace, or redirect function calls – Asynchronously call any function in the process 12/21/2021 Wi. SA - Jonathon Giffin 4
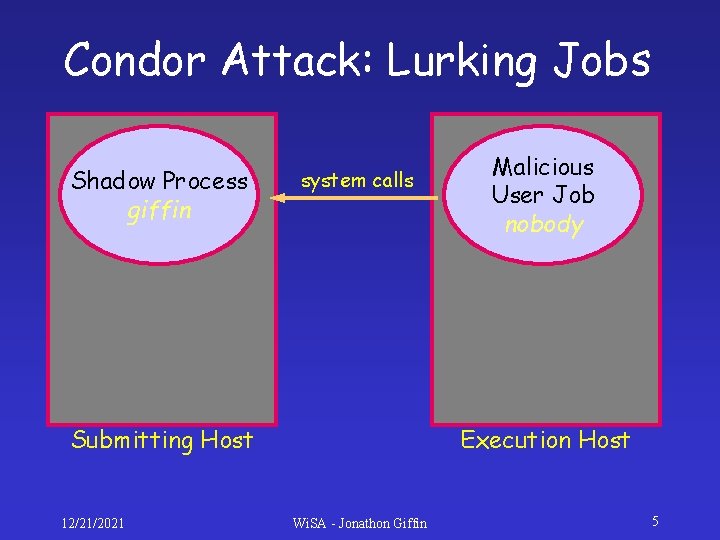
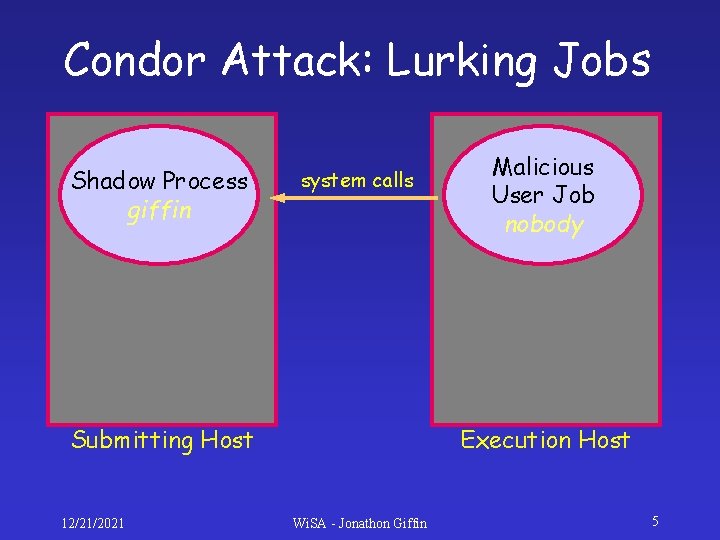
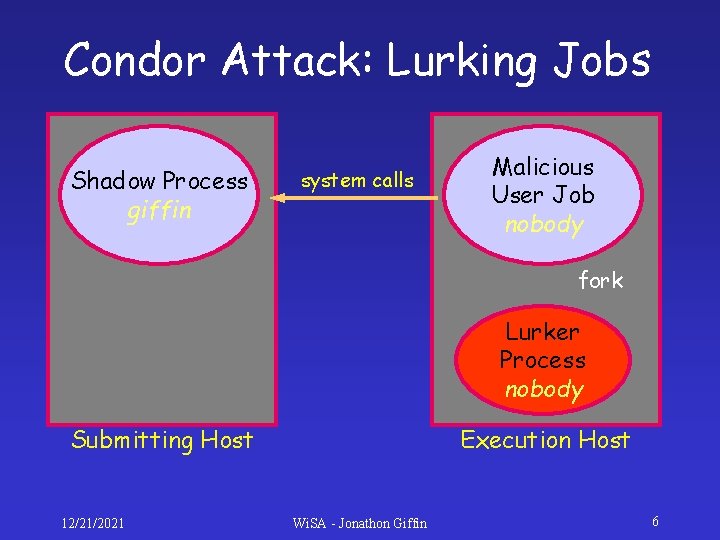
Condor Attack: Lurking Jobs Shadow Process giffin system calls Submitting Host 12/21/2021 Malicious User Job nobody Execution Host Wi. SA - Jonathon Giffin 5
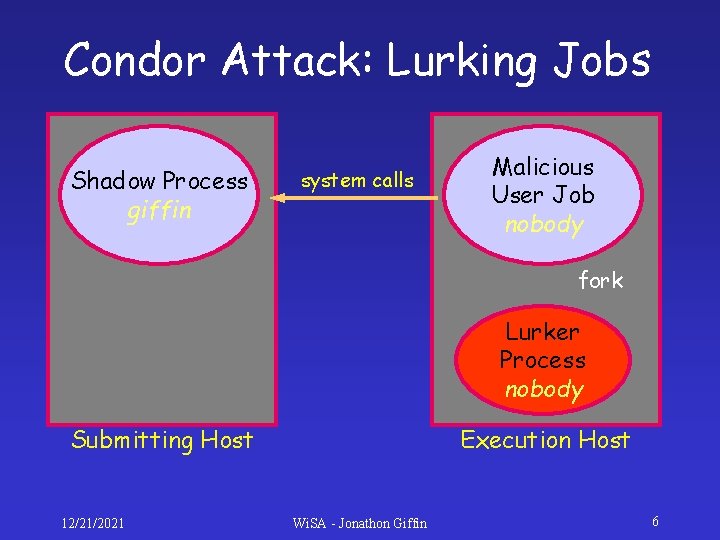
Condor Attack: Lurking Jobs Shadow Process giffin system calls Malicious User Job nobody fork Lurker Process nobody Submitting Host 12/21/2021 Execution Host Wi. SA - Jonathon Giffin 6
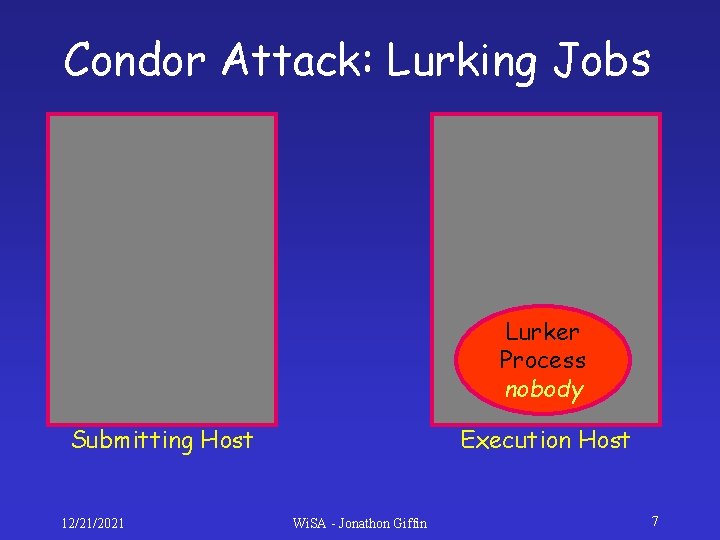
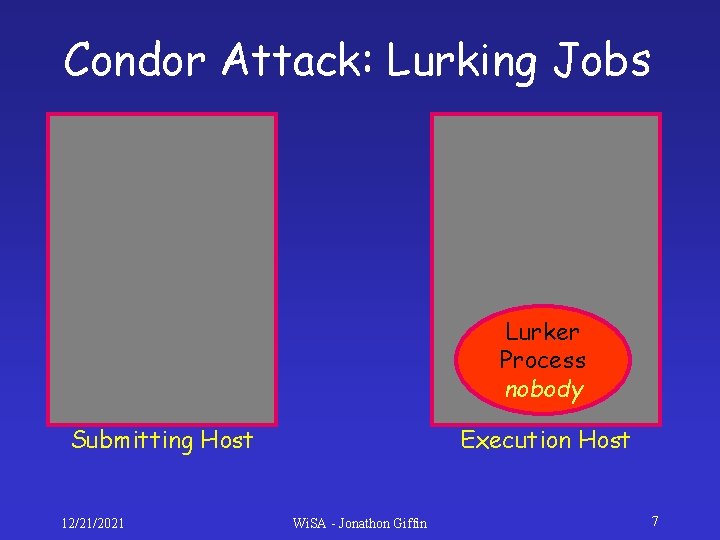
Condor Attack: Lurking Jobs Lurker Process nobody Submitting Host 12/21/2021 Execution Host Wi. SA - Jonathon Giffin 7
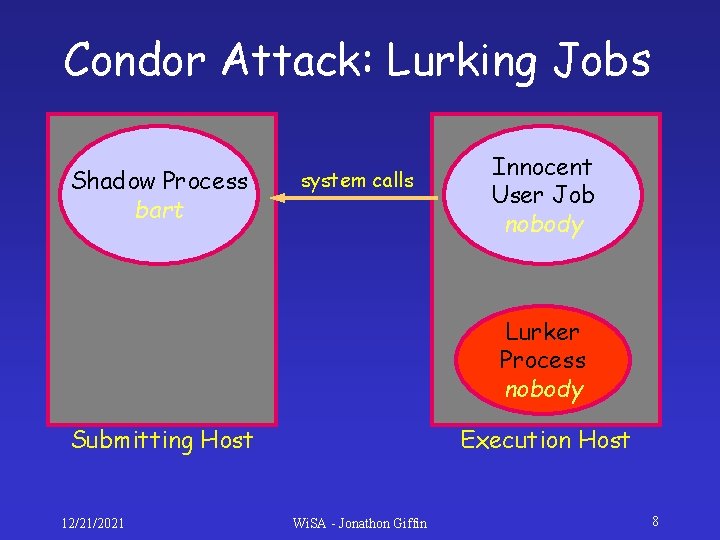
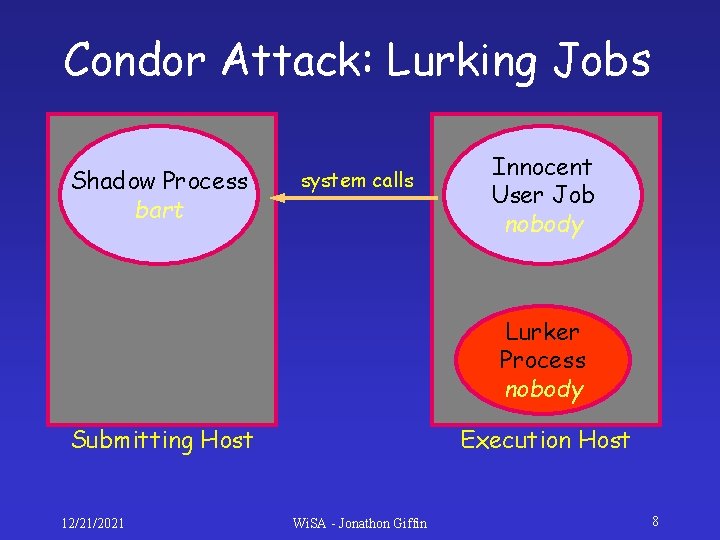
Condor Attack: Lurking Jobs Shadow Process bart system calls Innocent User Job nobody Lurker Process nobody Submitting Host 12/21/2021 Execution Host Wi. SA - Jonathon Giffin 8
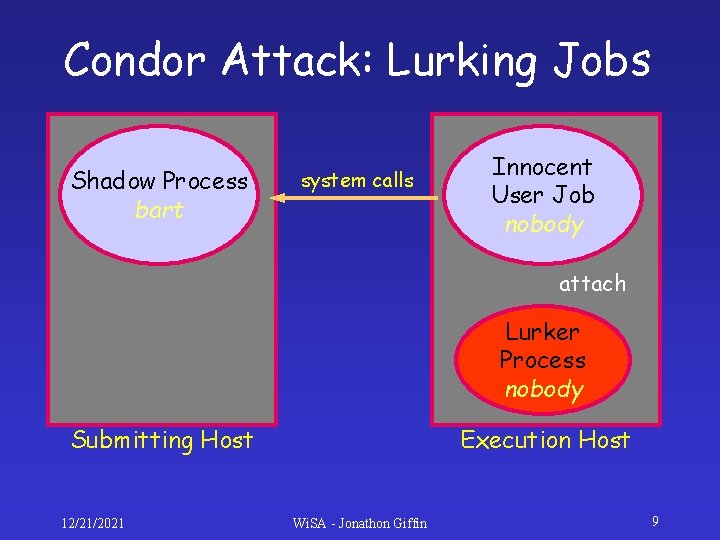
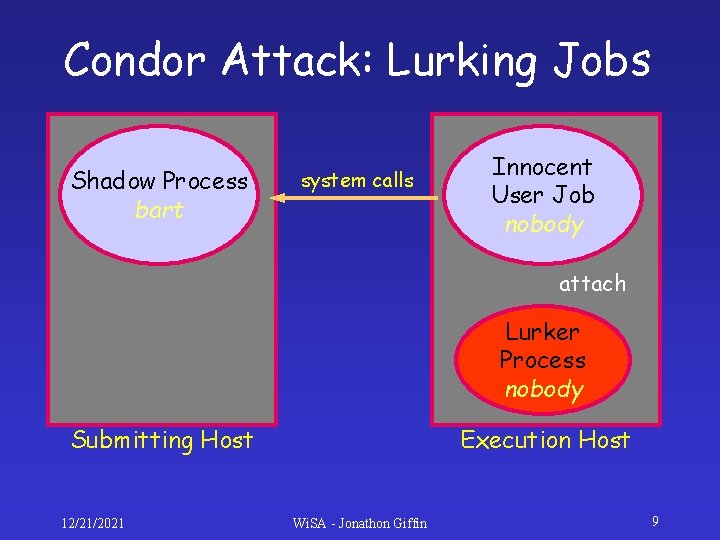
Condor Attack: Lurking Jobs Shadow Process bart system calls Innocent User Job nobody attach Lurker Process nobody Submitting Host 12/21/2021 Execution Host Wi. SA - Jonathon Giffin 9
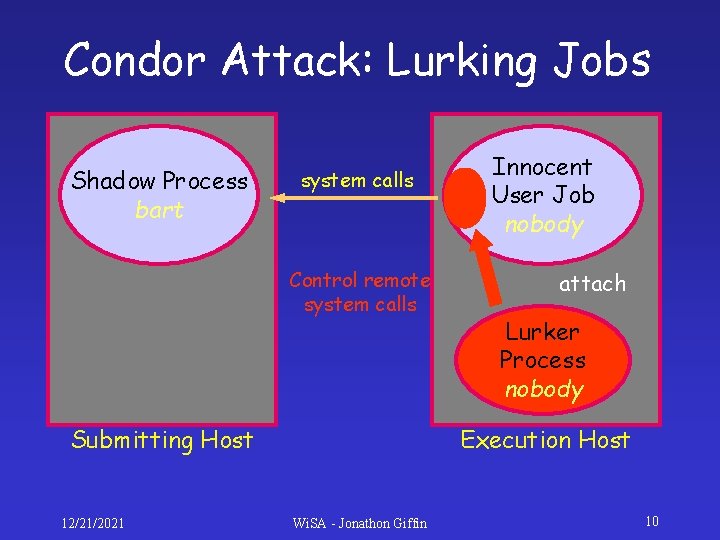
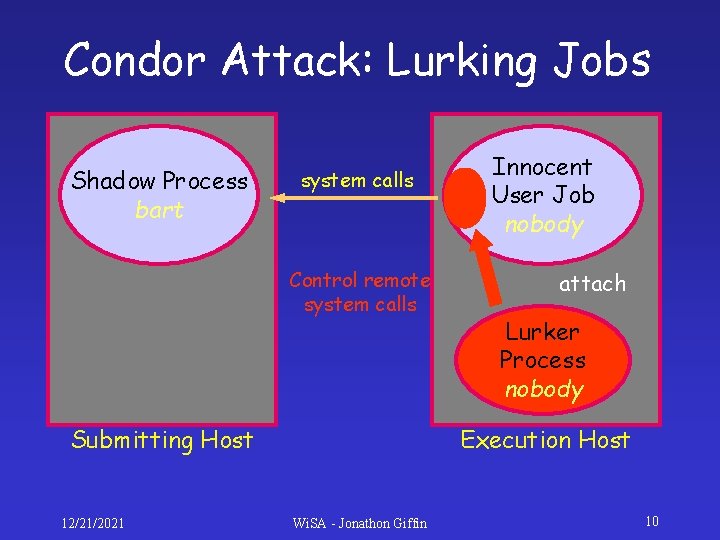
Condor Attack: Lurking Jobs Shadow Process bart system calls Control remote system calls Submitting Host 12/21/2021 Innocent User Job nobody attach Lurker Process nobody Execution Host Wi. SA - Jonathon Giffin 10
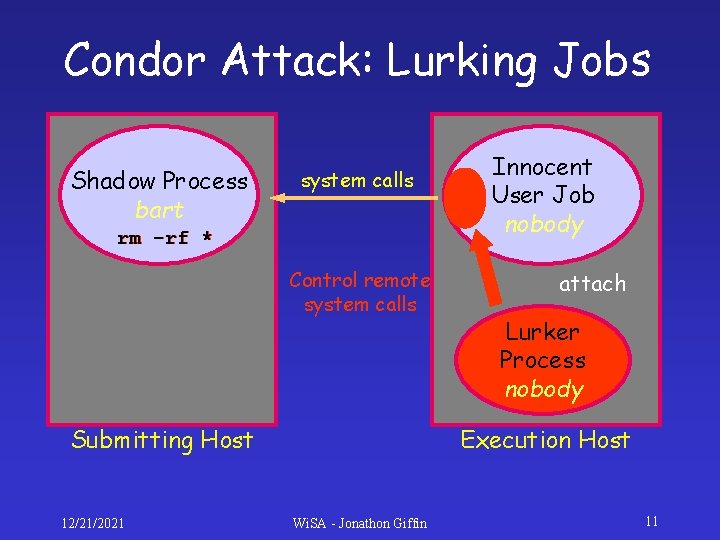
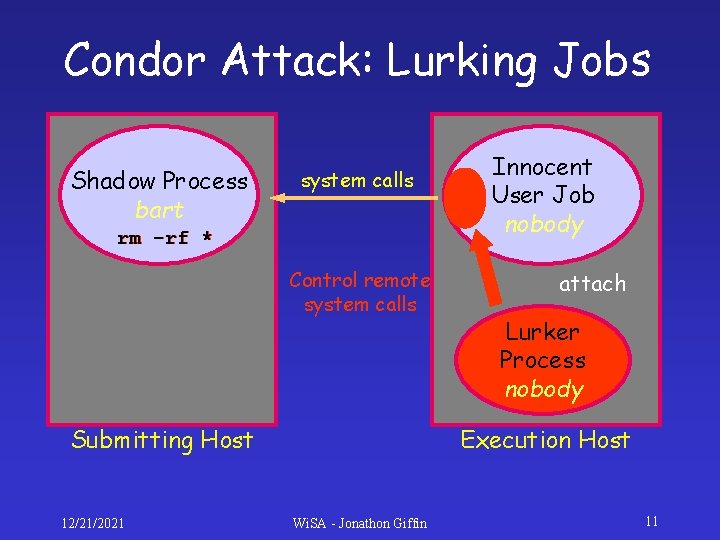
Condor Attack: Lurking Jobs Shadow Process bart system calls rm -rf * Control remote system calls Submitting Host 12/21/2021 Innocent User Job nobody attach Lurker Process nobody Execution Host Wi. SA - Jonathon Giffin 11
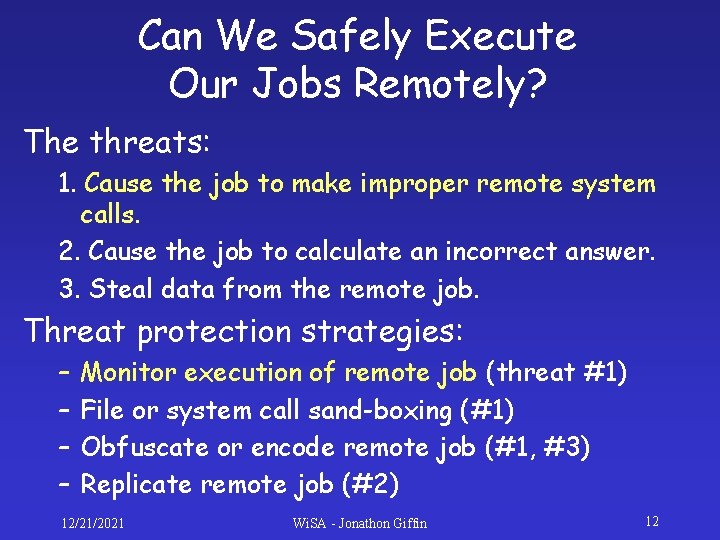
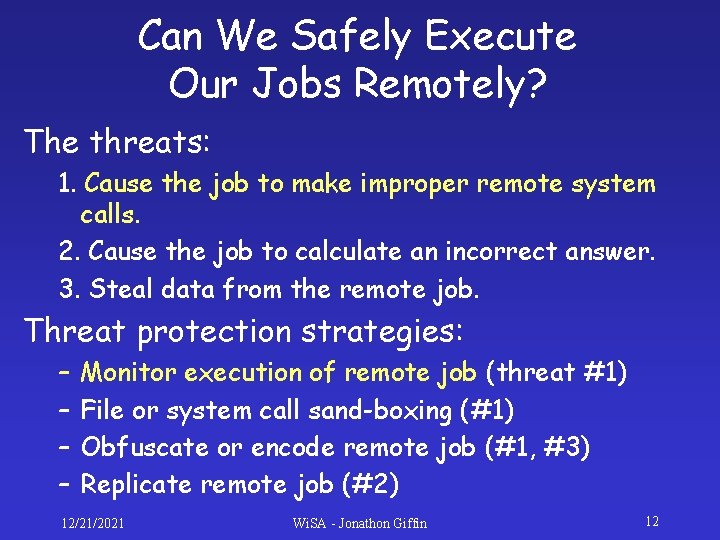
Can We Safely Execute Our Jobs Remotely? The threats: 1. Cause the job to make improper remote system calls. 2. Cause the job to calculate an incorrect answer. 3. Steal data from the remote job. Threat protection strategies: – – Monitor execution of remote job (threat #1) File or system call sand-boxing (#1) Obfuscate or encode remote job (#1, #3) Replicate remote job (#2) 12/21/2021 Wi. SA - Jonathon Giffin 12
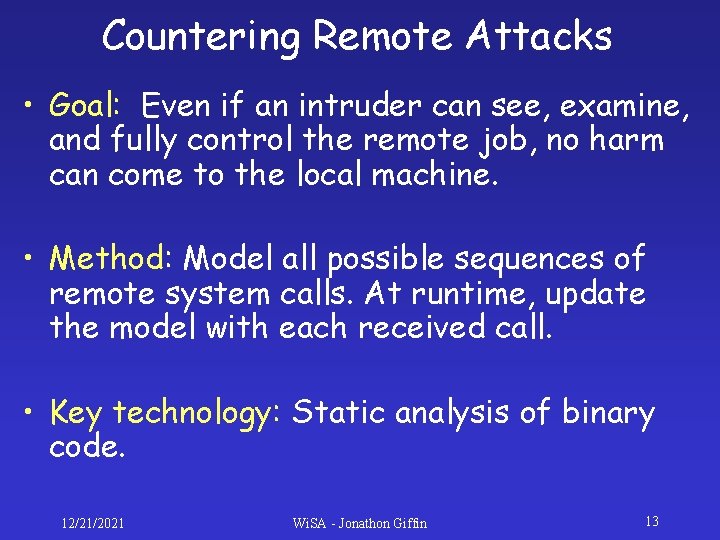
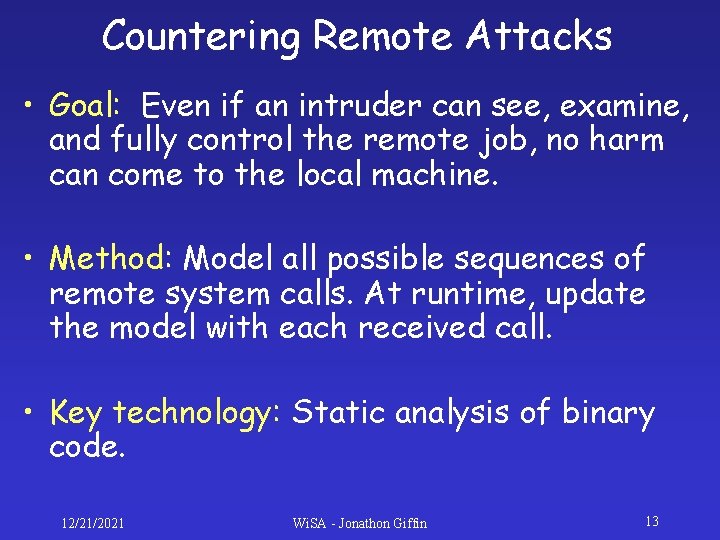
Countering Remote Attacks • Goal: Even if an intruder can see, examine, and fully control the remote job, no harm can come to the local machine. • Method: Model all possible sequences of remote system calls. At runtime, update the model with each received call. • Key technology: Static analysis of binary code. 12/21/2021 Wi. SA - Jonathon Giffin 13
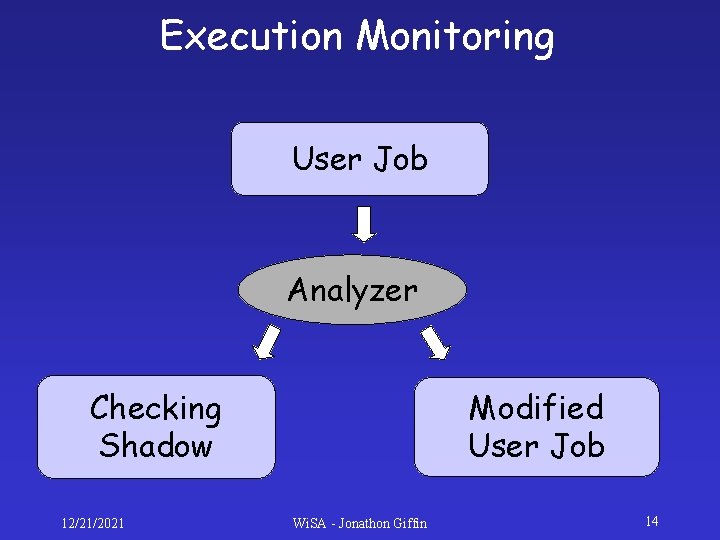
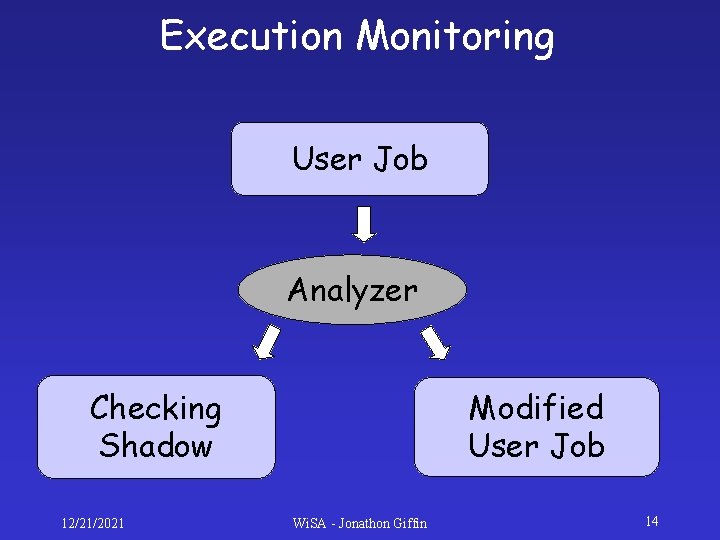
Execution Monitoring User Job Analyzer Checking Shadow 12/21/2021 Modified User Job Wi. SA - Jonathon Giffin 14
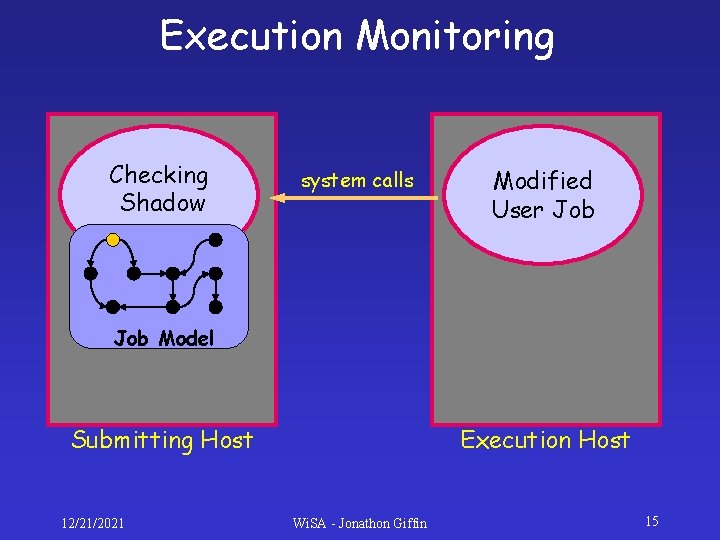
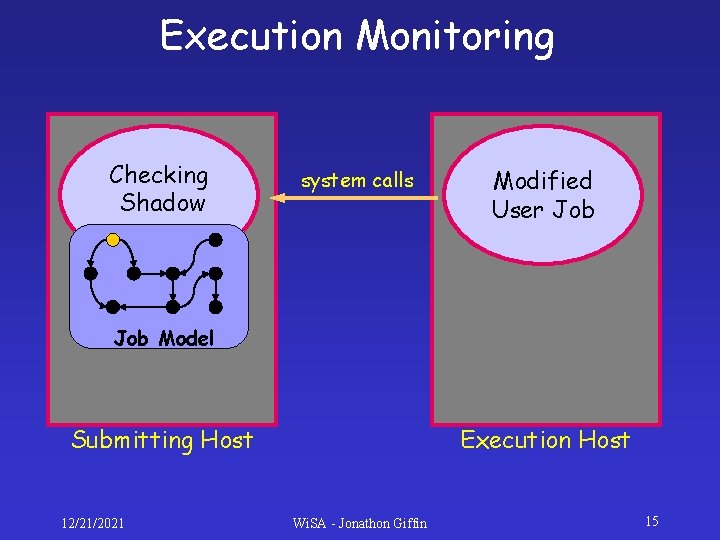
Execution Monitoring Checking Shadow system calls Modified User Job Model Submitting Host 12/21/2021 Execution Host Wi. SA - Jonathon Giffin 15
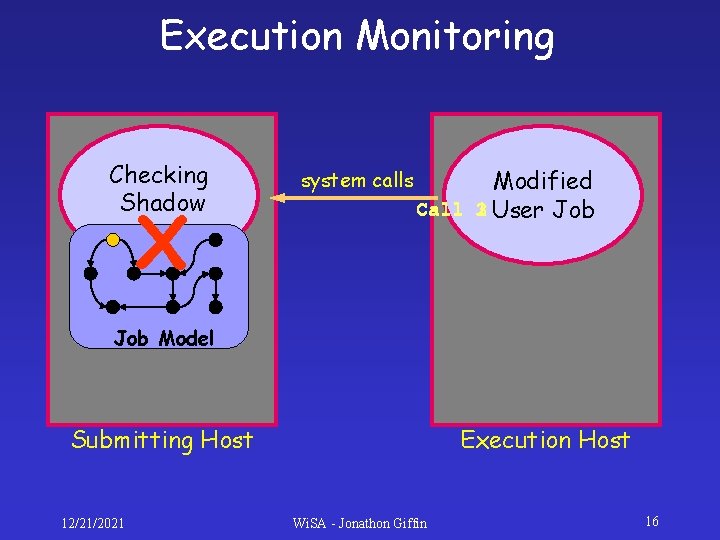
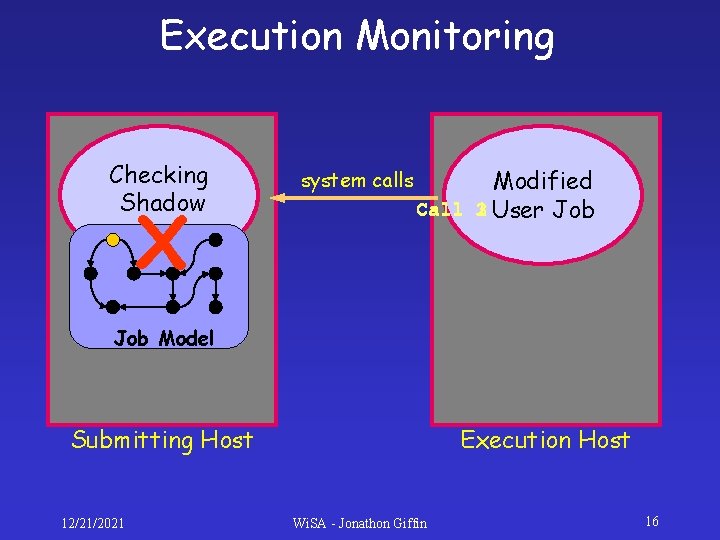
Execution Monitoring Checking Shadow X system calls Modified 1 User Job Call 3 2 Job Model Submitting Host 12/21/2021 Execution Host Wi. SA - Jonathon Giffin 16
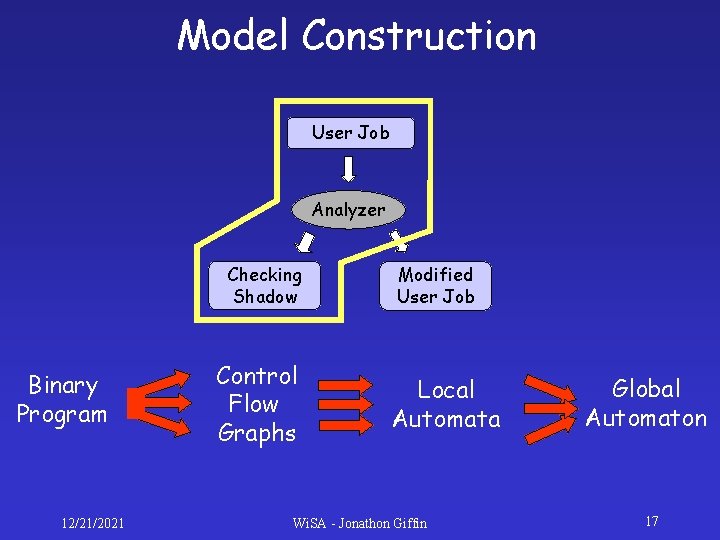
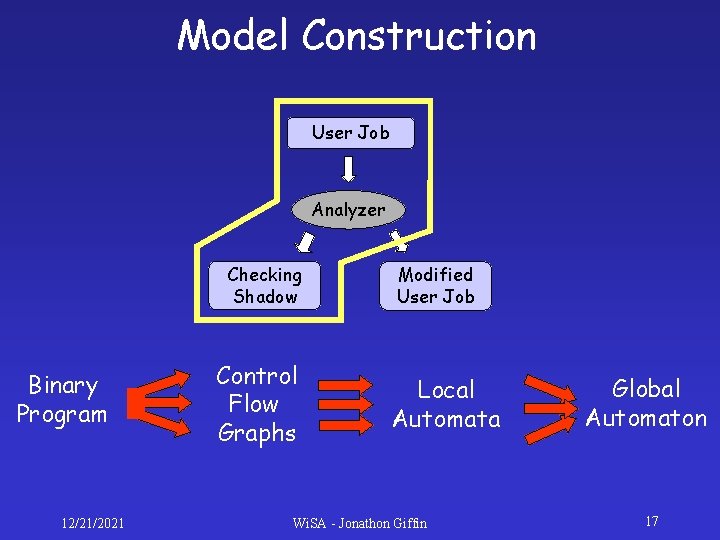
Model Construction User Job Analyzer Checking Shadow Binary Program 12/21/2021 Control Flow Graphs Modified User Job Local Automata Wi. SA - Jonathon Giffin Global Automaton 17
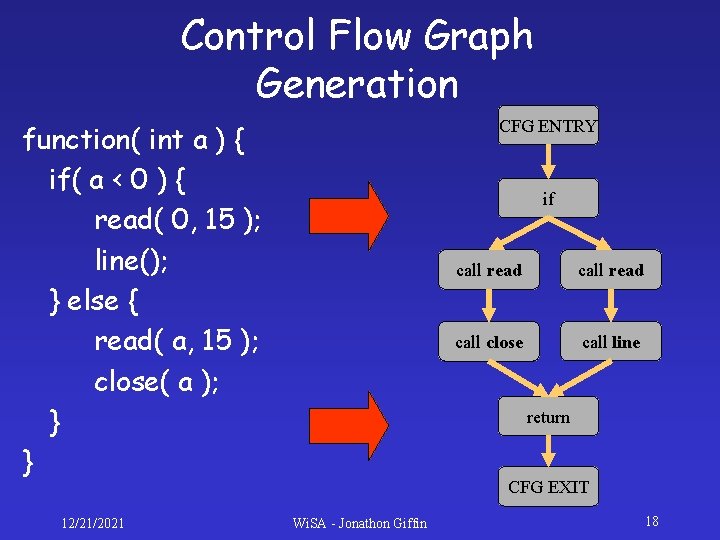
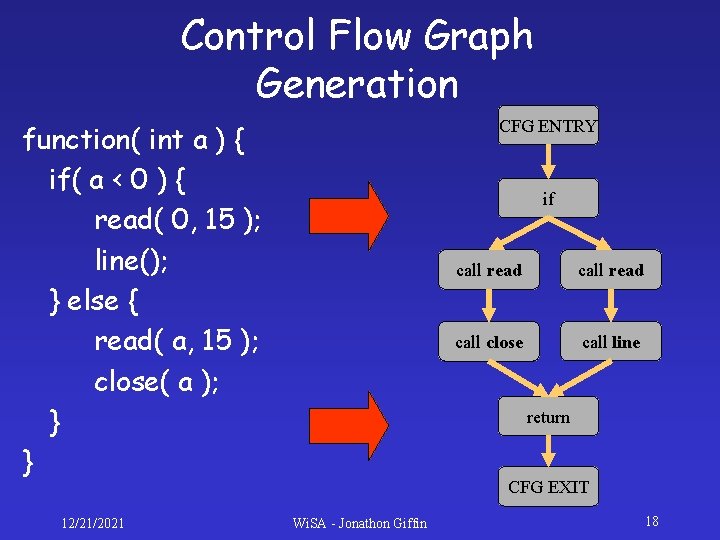
Control Flow Graph Generation CFG ENTRY function( int a ) { if( a < 0 ) { read( 0, 15 ); line(); } else { read( a, 15 ); close( a ); } } 12/21/2021 if call read call close call line return CFG EXIT Wi. SA - Jonathon Giffin 18
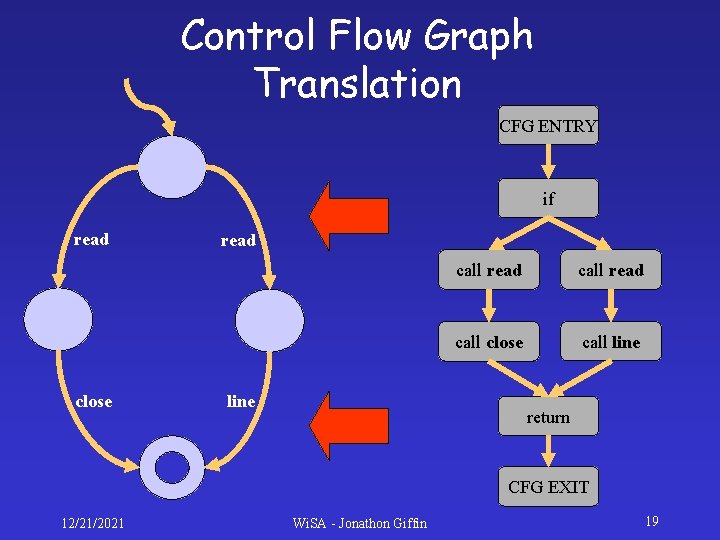
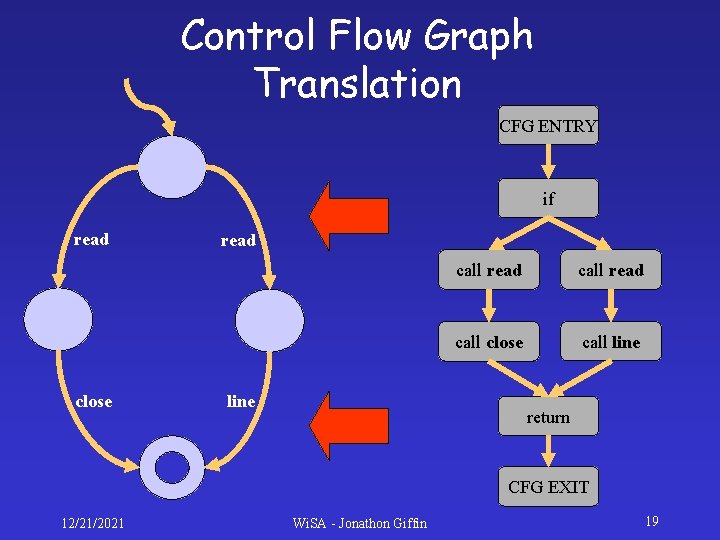
Control Flow Graph Translation CFG ENTRY if read close read line call read call close call line return CFG EXIT 12/21/2021 Wi. SA - Jonathon Giffin 19
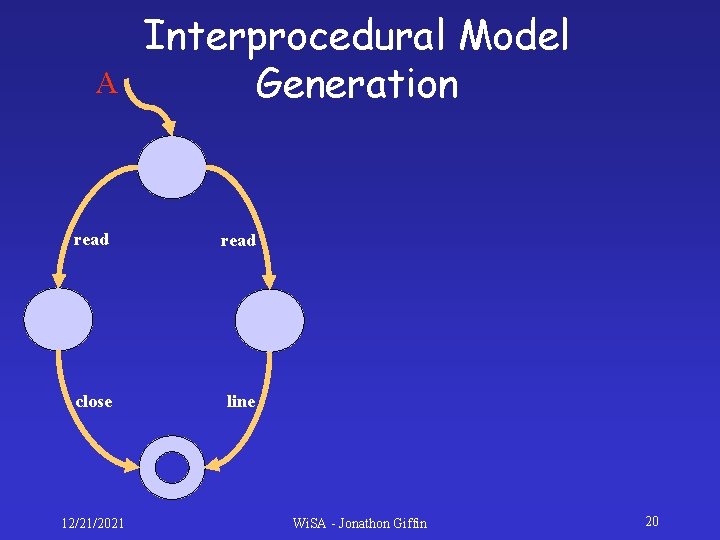
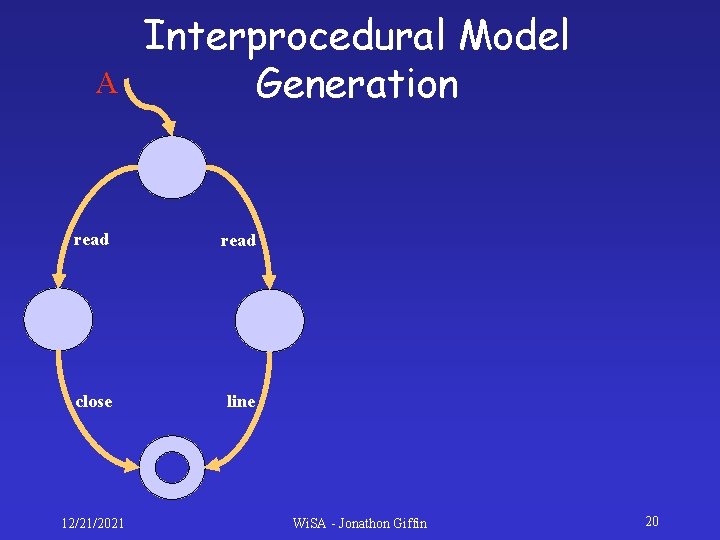
A Interprocedural Model Generation read close line 12/21/2021 Wi. SA - Jonathon Giffin 20
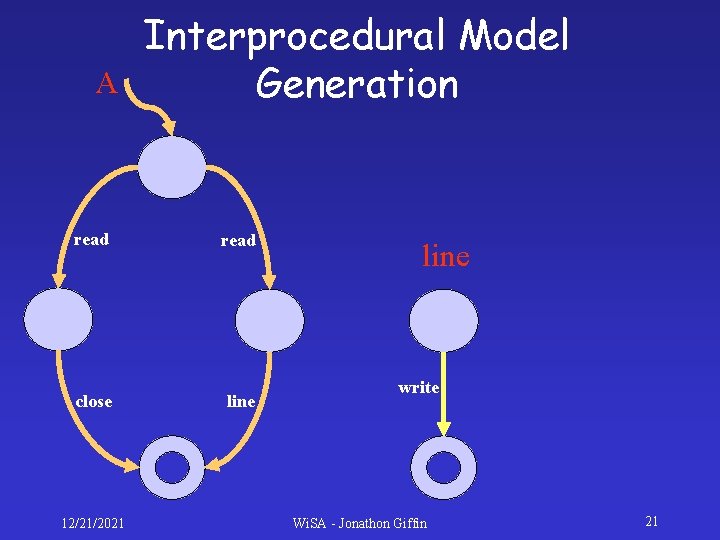
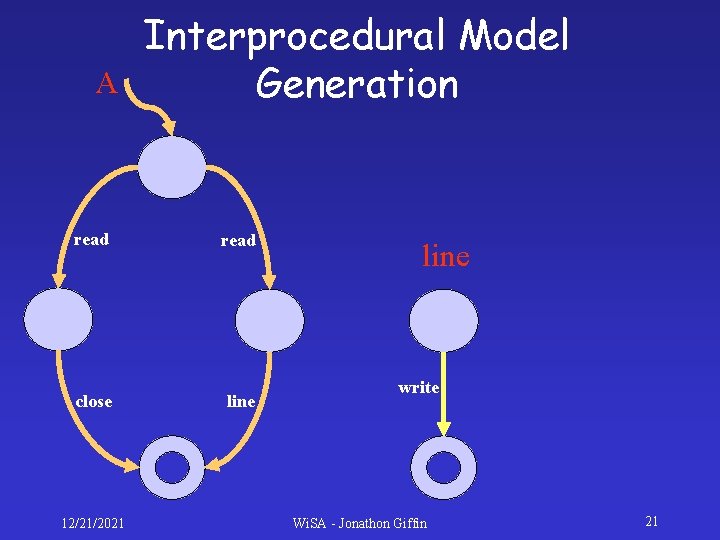
A Interprocedural Model Generation read close line 12/21/2021 line write Wi. SA - Jonathon Giffin 21
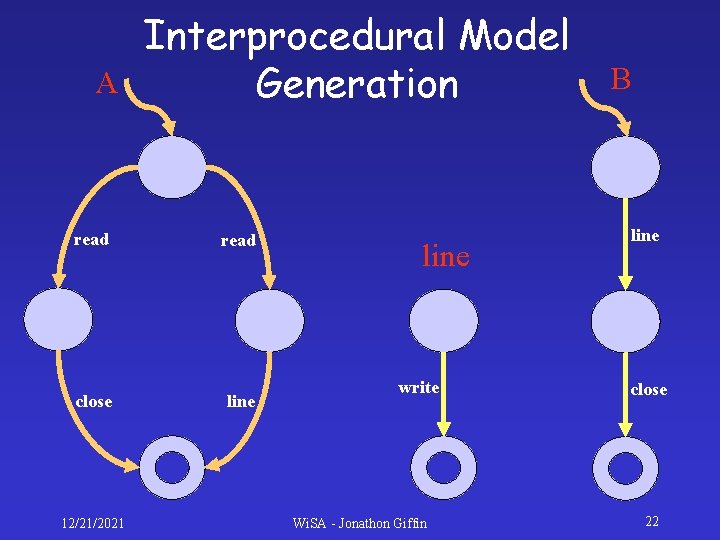
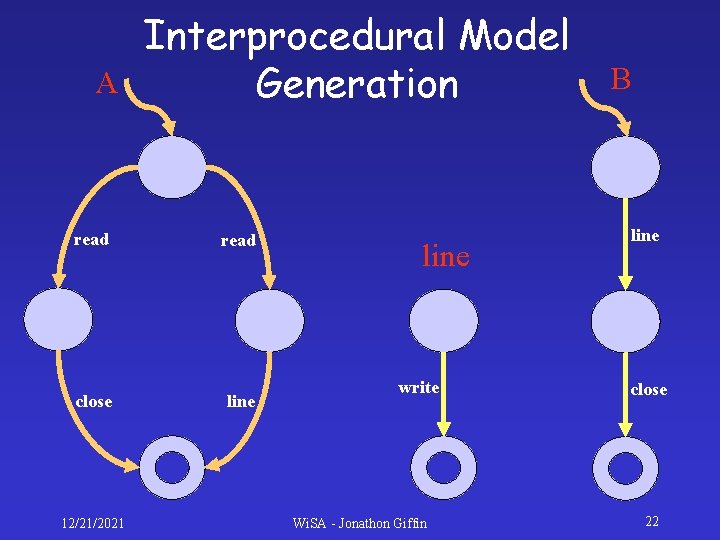
A Interprocedural Model Generation read close line 12/21/2021 line write Wi. SA - Jonathon Giffin B line close 22
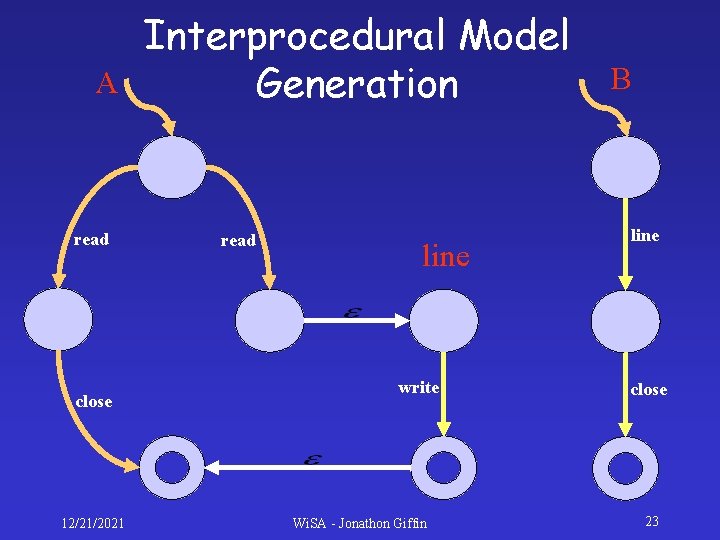
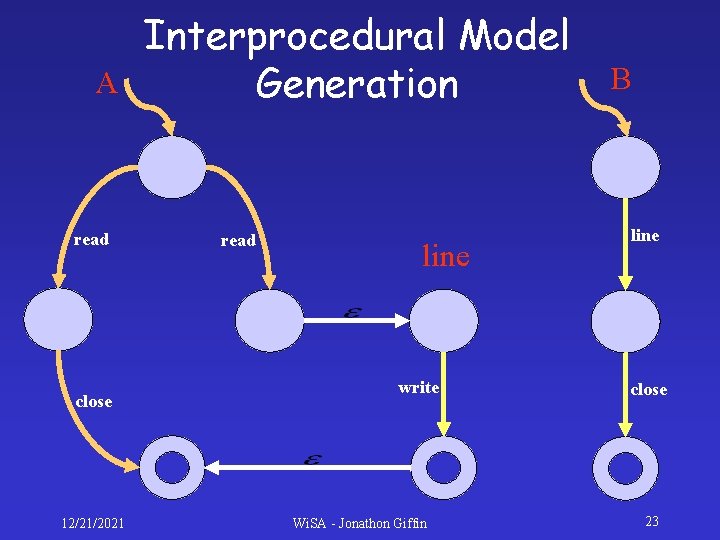
A read close 12/21/2021 Interprocedural Model Generation read line write Wi. SA - Jonathon Giffin B line close 23
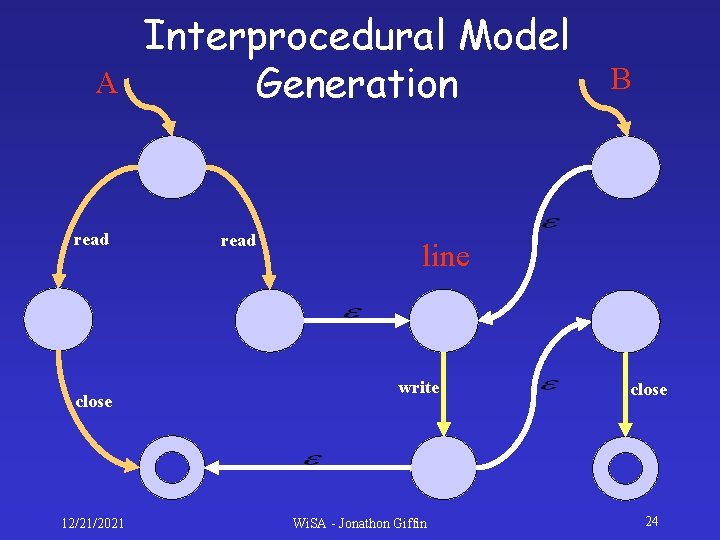
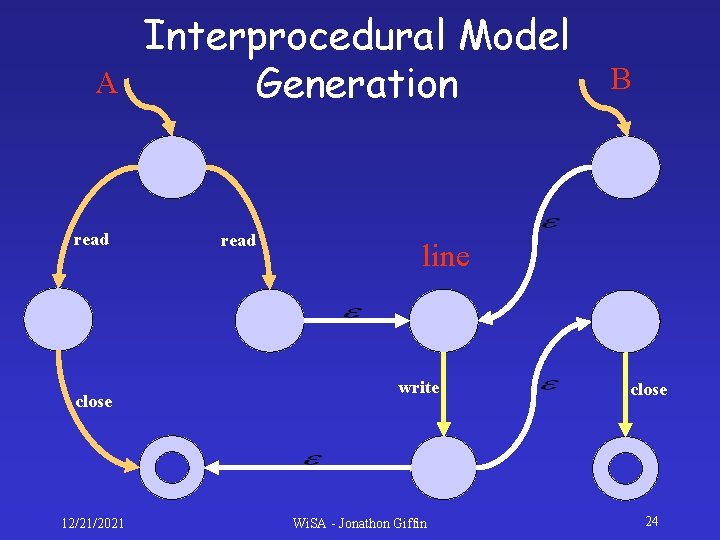
A read close 12/21/2021 Interprocedural Model Generation read B line write Wi. SA - Jonathon Giffin close 24
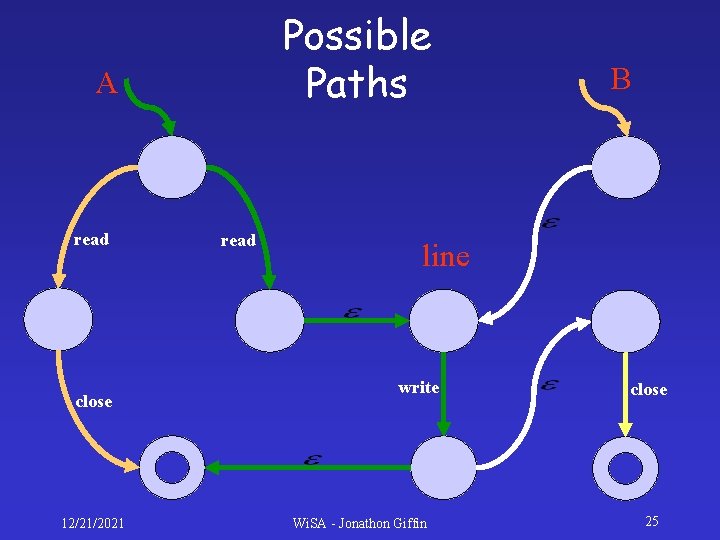
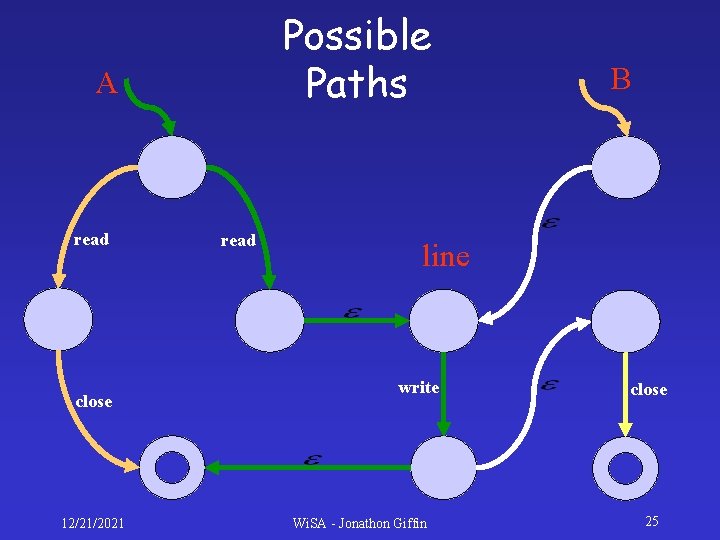
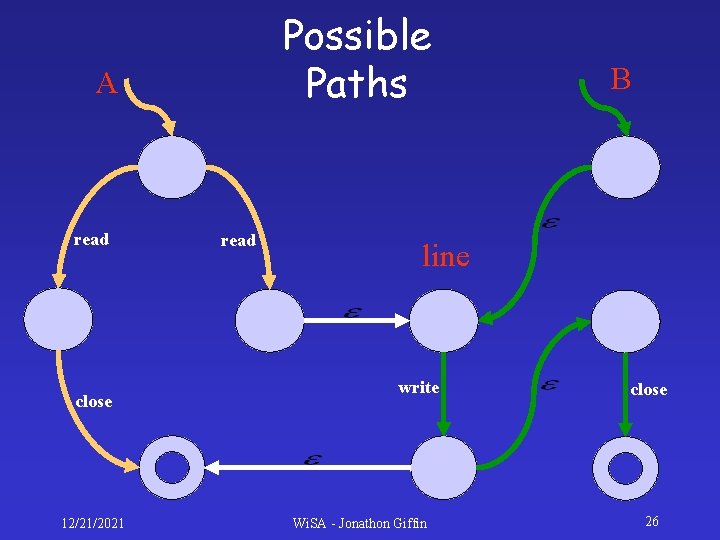
Possible Paths A read close 12/21/2021 read B line write Wi. SA - Jonathon Giffin close 25
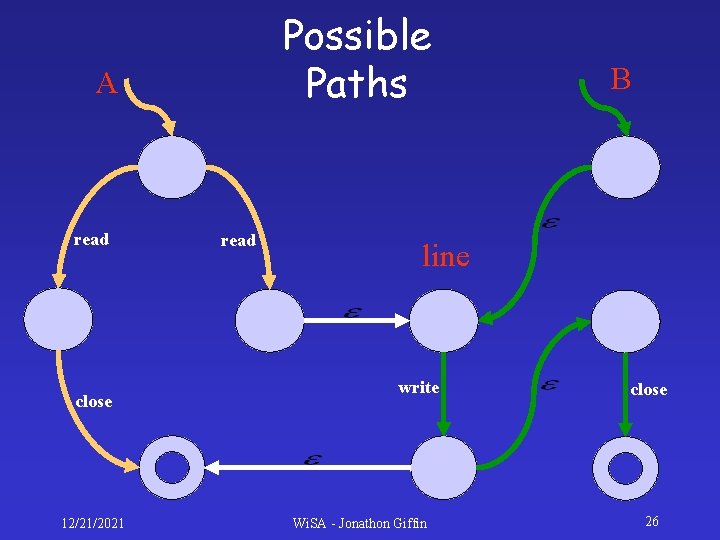
Possible Paths A read close 12/21/2021 read B line write Wi. SA - Jonathon Giffin close 26
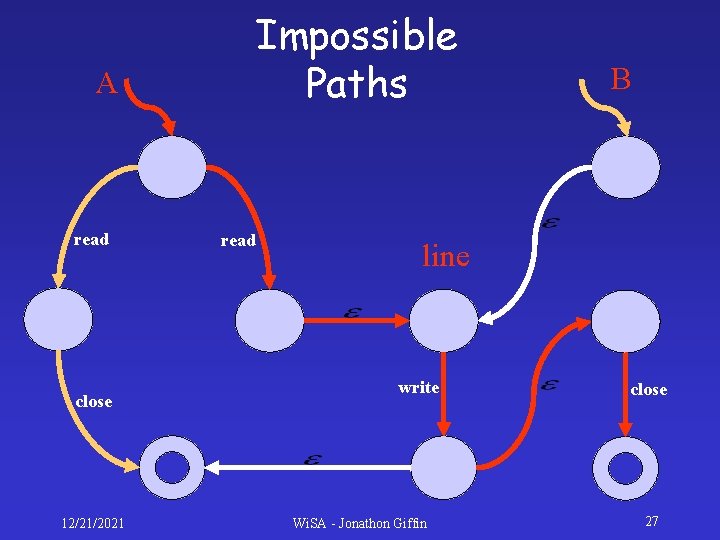
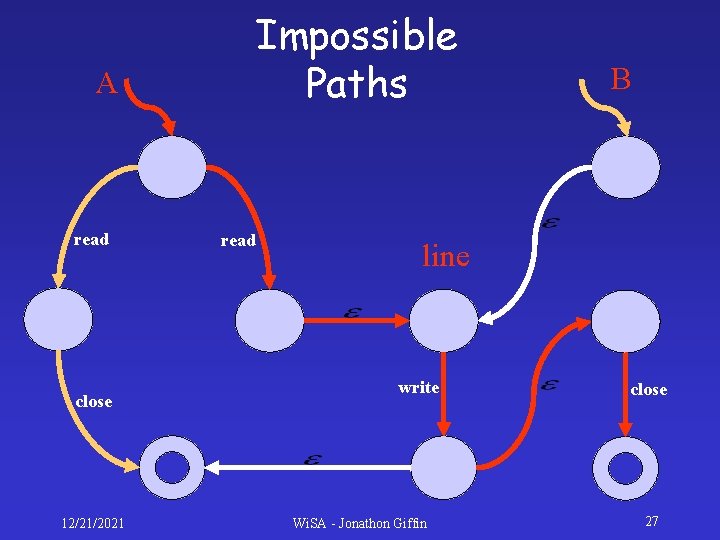
Impossible Paths A read close 12/21/2021 read B line write Wi. SA - Jonathon Giffin close 27
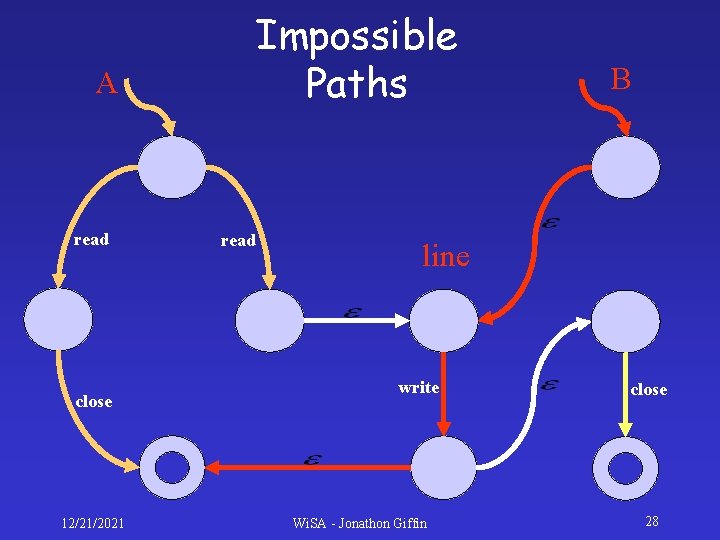
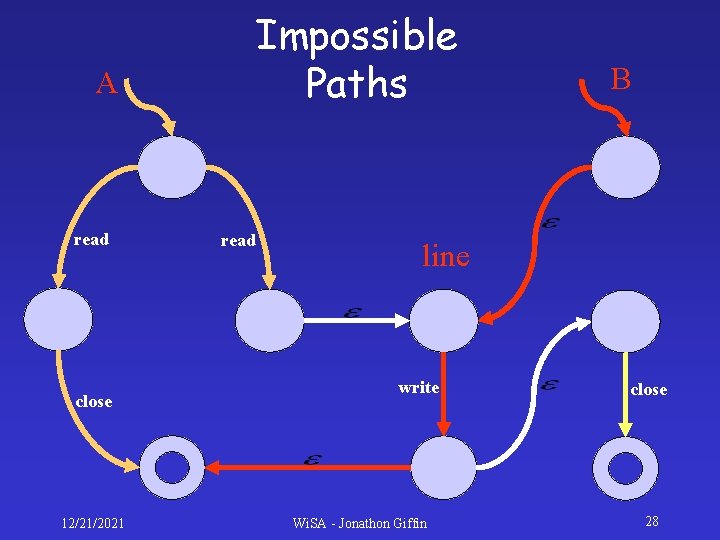
Impossible Paths A read close 12/21/2021 read B line write Wi. SA - Jonathon Giffin close 28
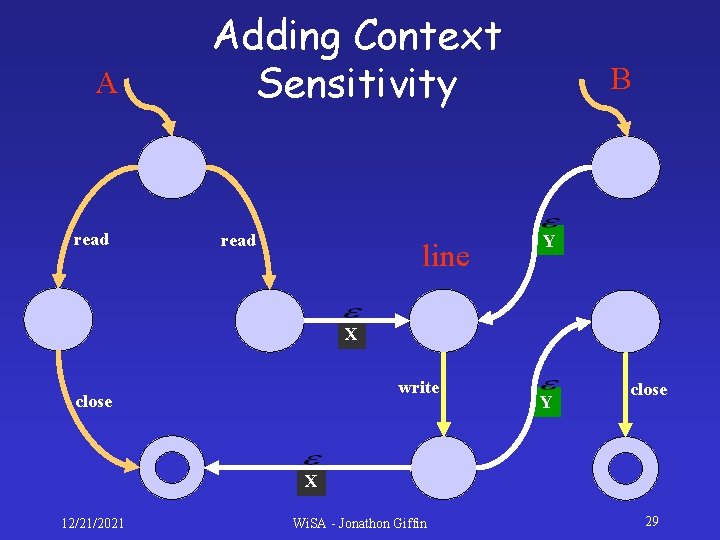
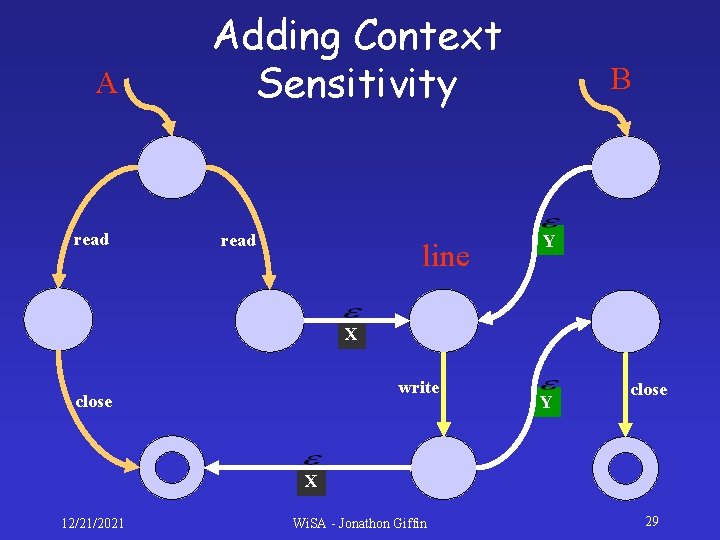
A read Adding Context Sensitivity read line B Y X write close Y close X 12/21/2021 Wi. SA - Jonathon Giffin 29
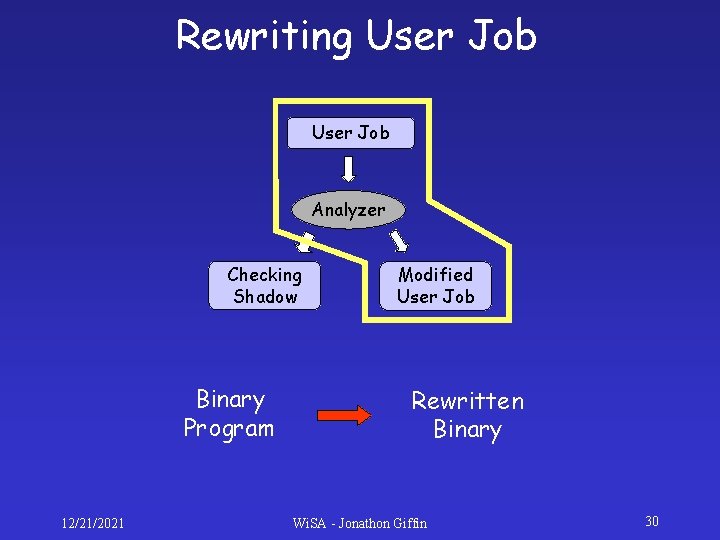
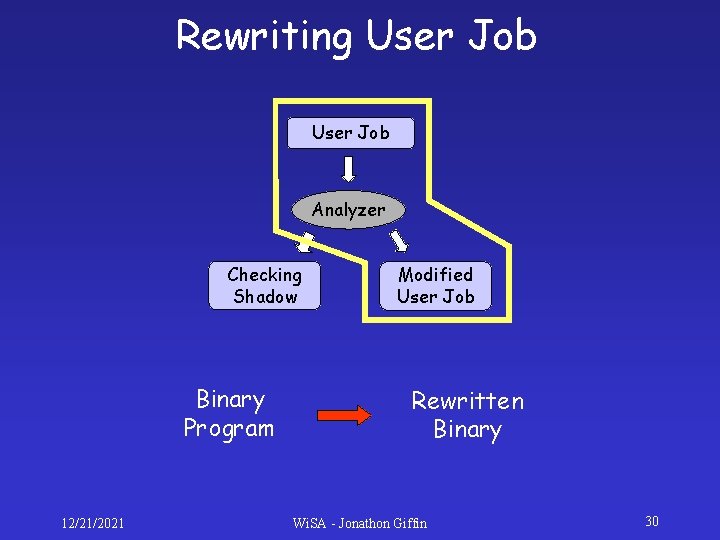
Rewriting User Job Analyzer Checking Shadow Binary Program 12/21/2021 Modified User Job Rewritten Binary Wi. SA - Jonathon Giffin 30
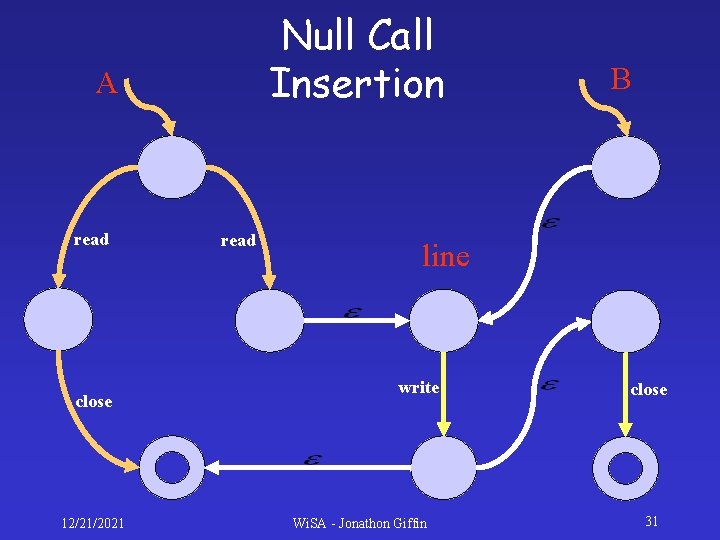
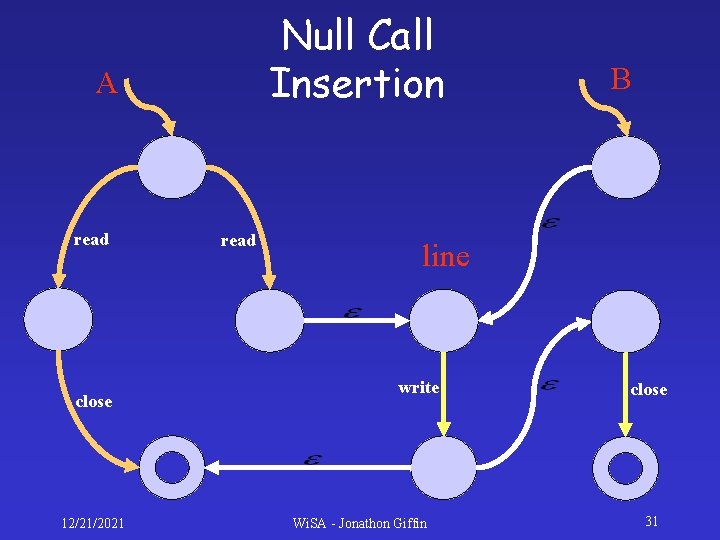
Null Call Insertion A read close 12/21/2021 read B line write Wi. SA - Jonathon Giffin close 31
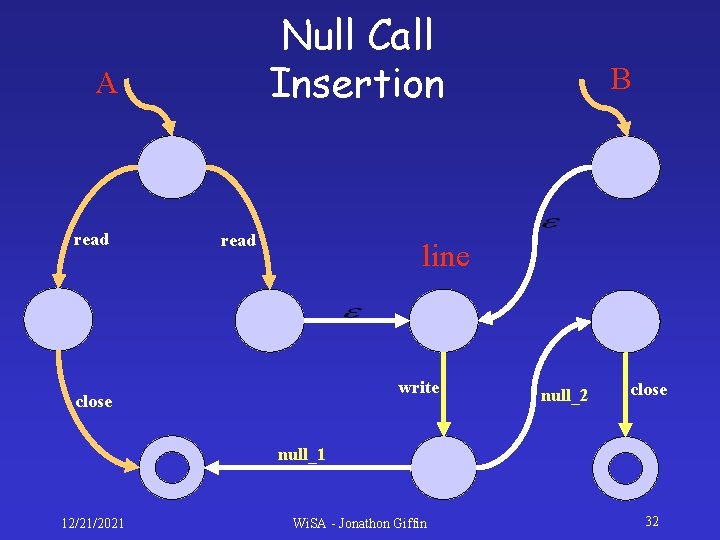
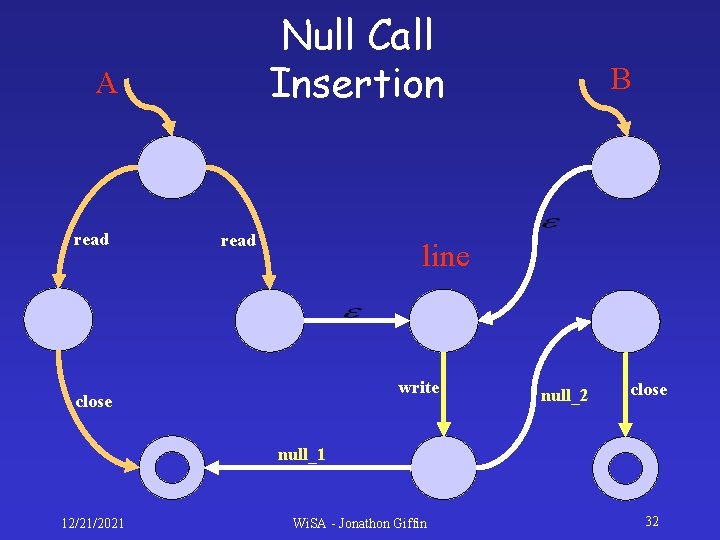
Null Call Insertion A read B line write close null_2 close null_1 12/21/2021 Wi. SA - Jonathon Giffin 32
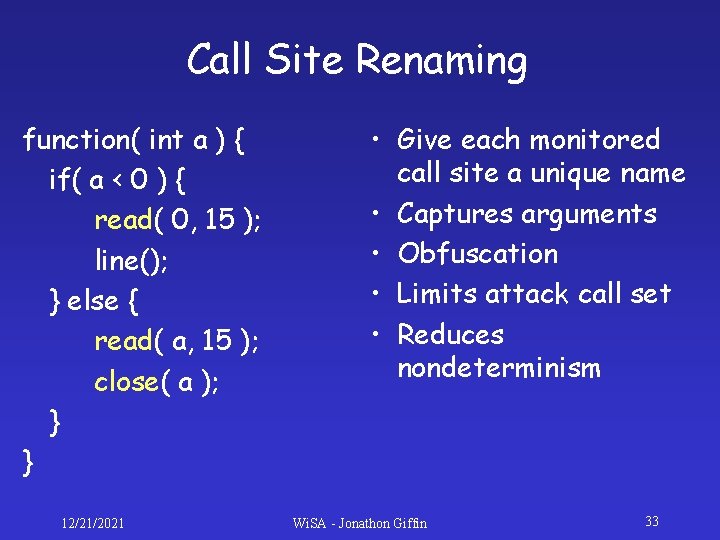
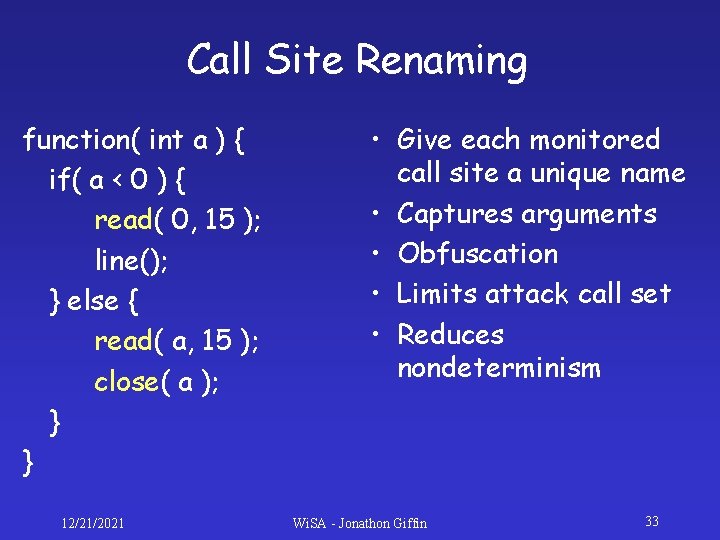
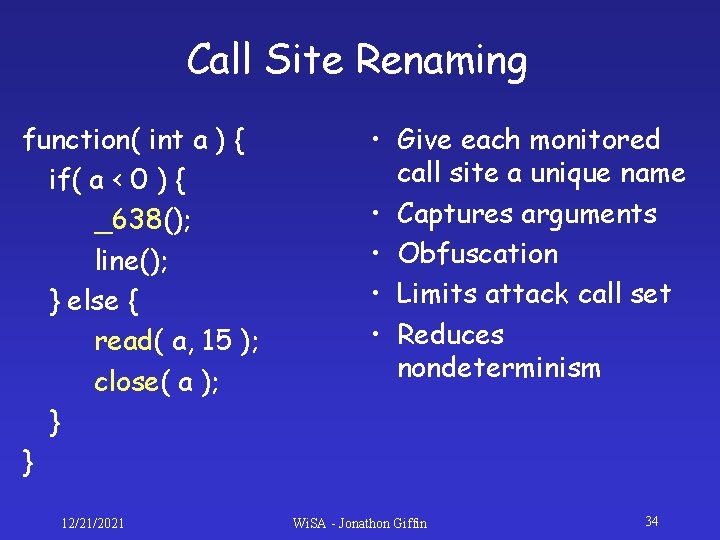
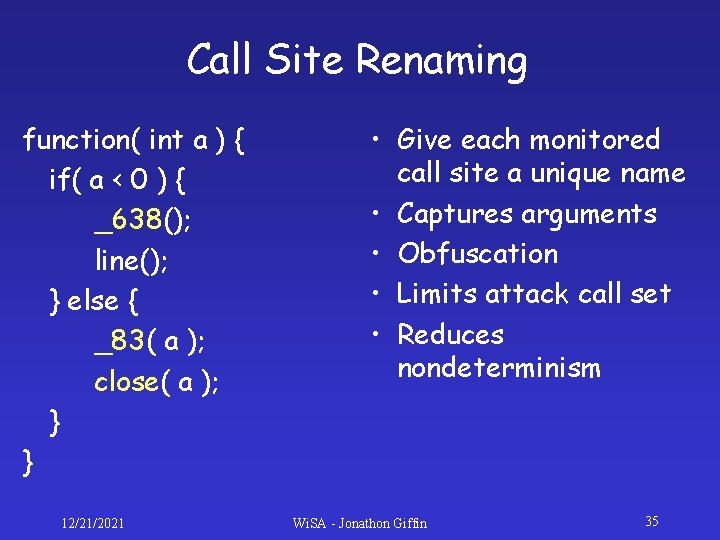
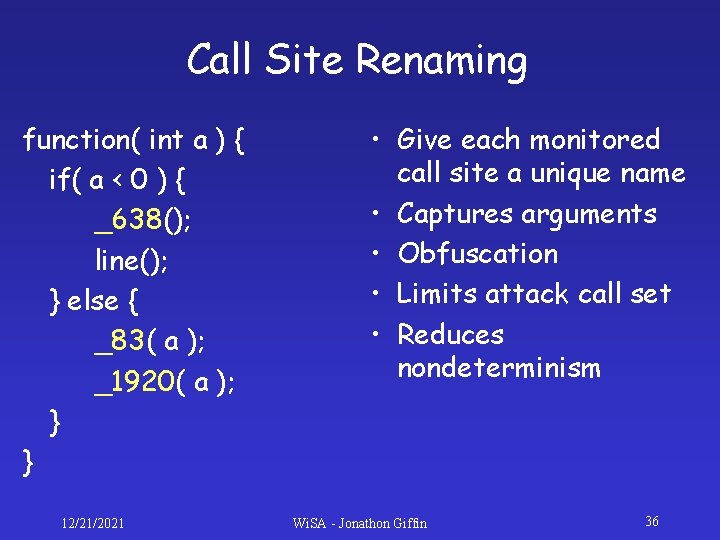
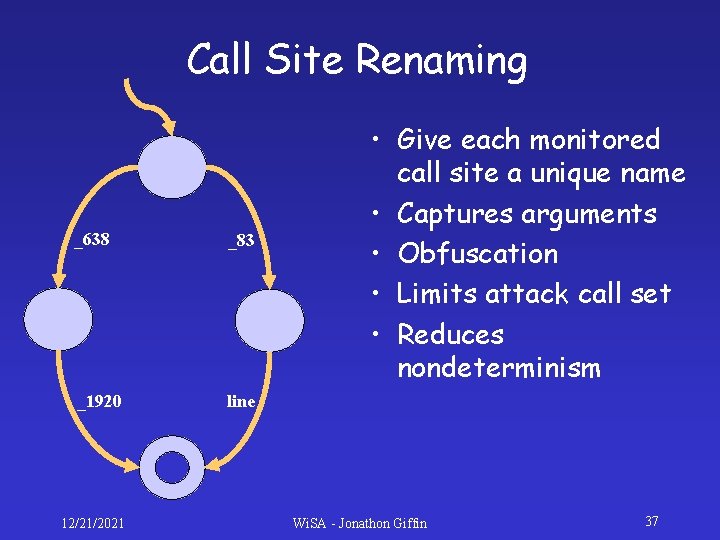
Call Site Renaming function( int a ) { if( a < 0 ) { read( 0, 15 ); line(); } else { read( a, 15 ); close( a ); } } 12/21/2021 • Give each monitored call site a unique name • Captures arguments • Obfuscation • Limits attack call set • Reduces nondeterminism Wi. SA - Jonathon Giffin 33
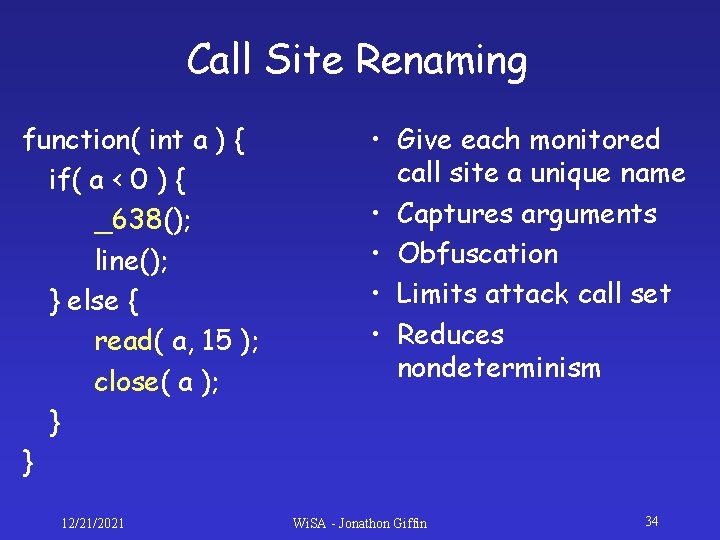
Call Site Renaming function( int a ) { if( a < 0 ) { _638(); line(); } else { read( a, 15 ); close( a ); } } 12/21/2021 • Give each monitored call site a unique name • Captures arguments • Obfuscation • Limits attack call set • Reduces nondeterminism Wi. SA - Jonathon Giffin 34
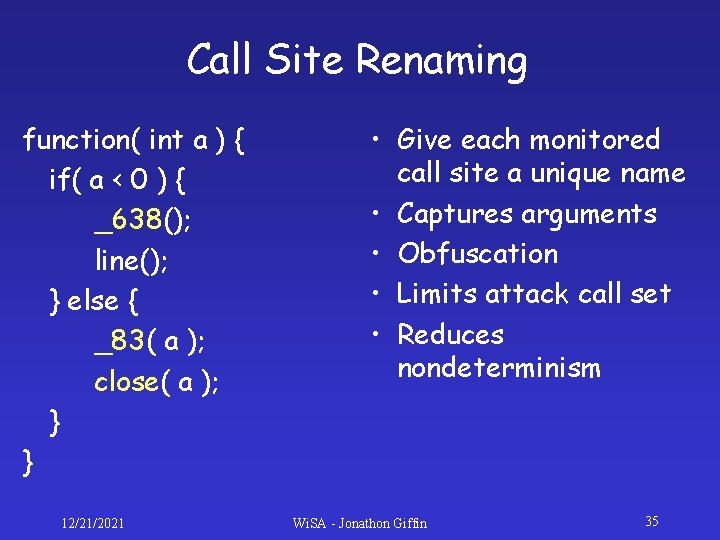
Call Site Renaming function( int a ) { if( a < 0 ) { _638(); line(); } else { _83( a ); close( a ); } } 12/21/2021 • Give each monitored call site a unique name • Captures arguments • Obfuscation • Limits attack call set • Reduces nondeterminism Wi. SA - Jonathon Giffin 35
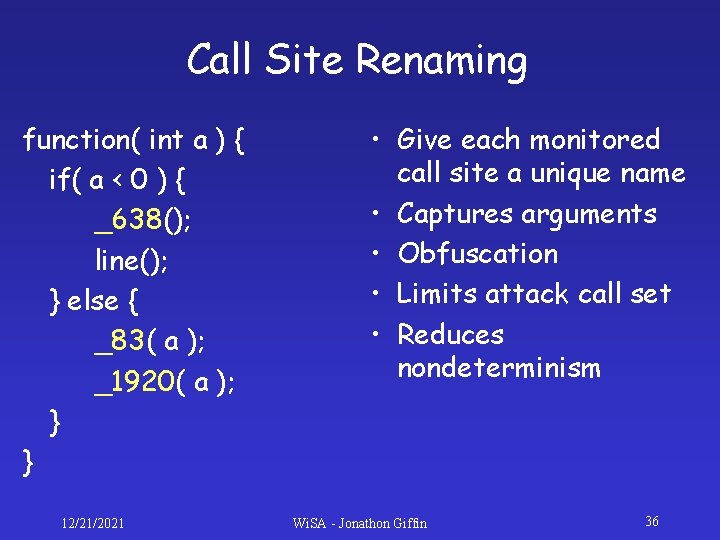
Call Site Renaming function( int a ) { if( a < 0 ) { _638(); line(); } else { _83( a ); _1920( a ); } } 12/21/2021 • Give each monitored call site a unique name • Captures arguments • Obfuscation • Limits attack call set • Reduces nondeterminism Wi. SA - Jonathon Giffin 36
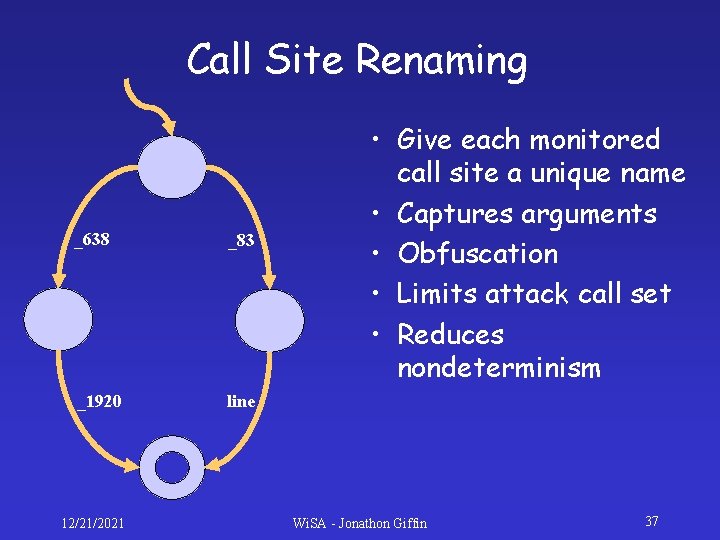
Call Site Renaming _638 _83 _1920 line 12/21/2021 • Give each monitored call site a unique name • Captures arguments • Obfuscation • Limits attack call set • Reduces nondeterminism Wi. SA - Jonathon Giffin 37
Prototype Implementation • • • Simulates remote execution environment Null calls inserted at function entries Measure null call overheads Measure null call bandwidth use Measure model precision 12/21/2021 Wi. SA - Jonathon Giffin 38
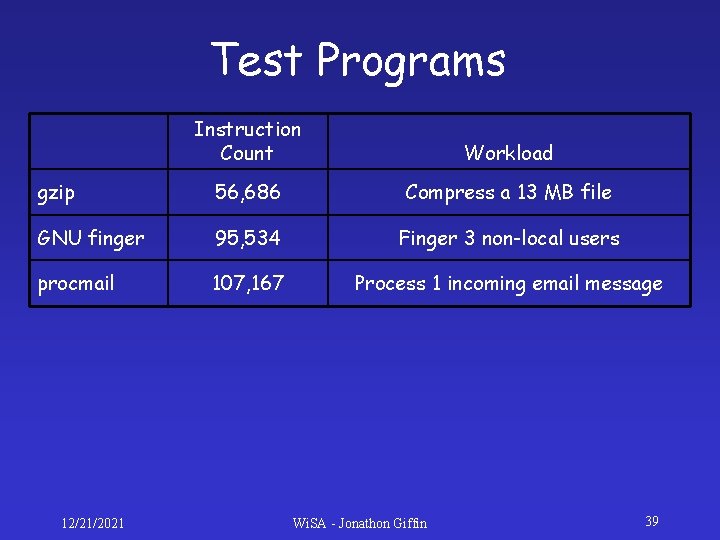
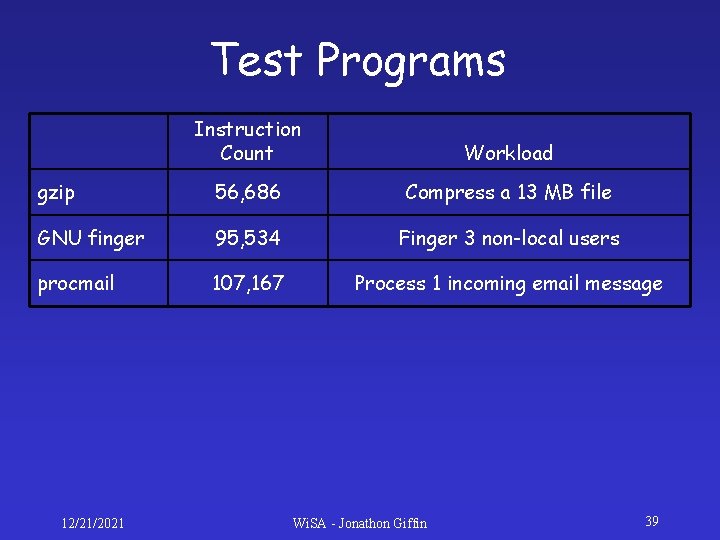
Test Programs Instruction Count Workload gzip 56, 686 Compress a 13 MB file GNU finger 95, 534 Finger 3 non-local users procmail 107, 167 Process 1 incoming email message 12/21/2021 Wi. SA - Jonathon Giffin 39
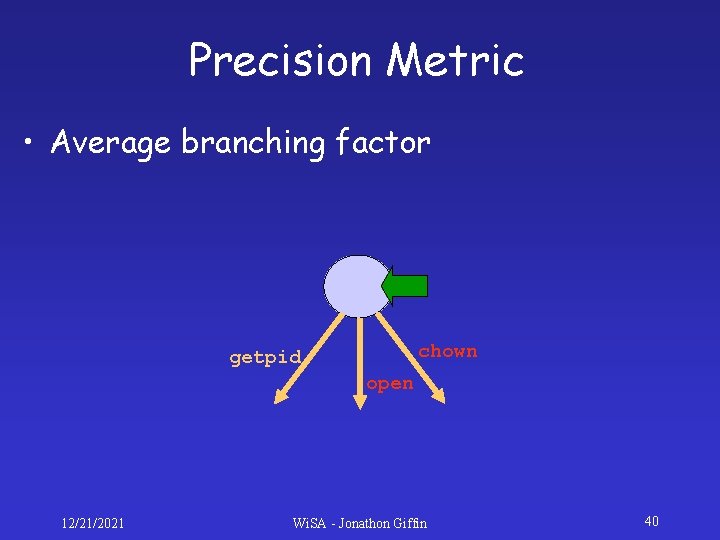
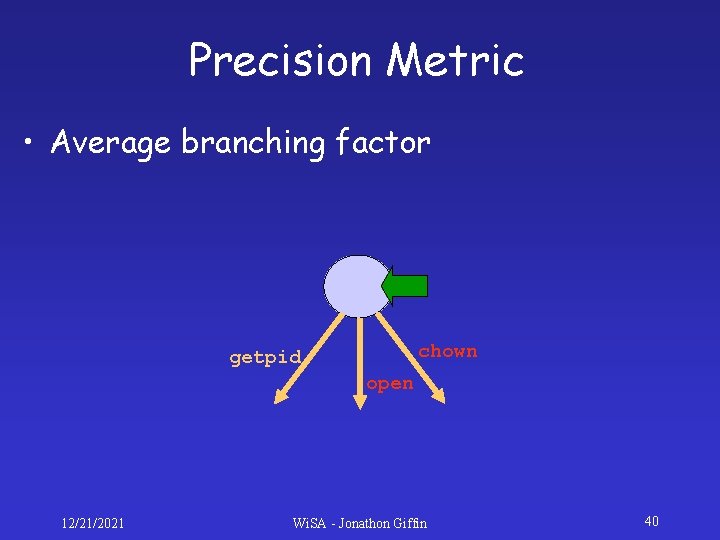
Precision Metric • Average branching factor chown getpid open 12/21/2021 Wi. SA - Jonathon Giffin 40

12/21/2021 Wi. SA - Jonathon Giffin 41
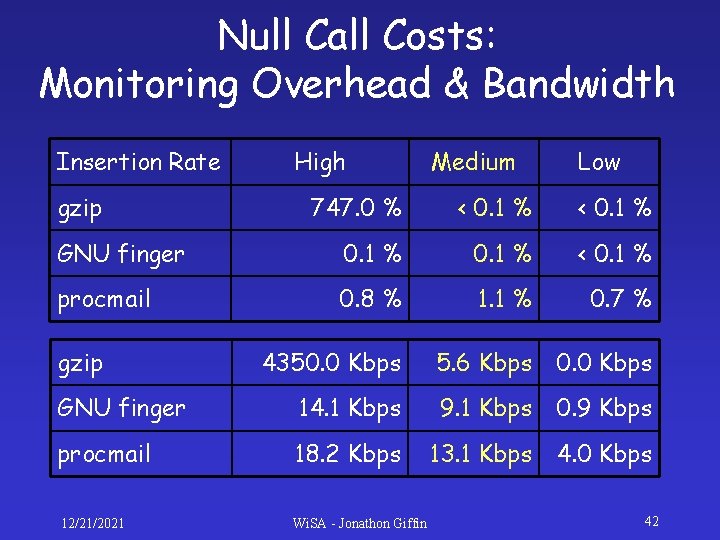
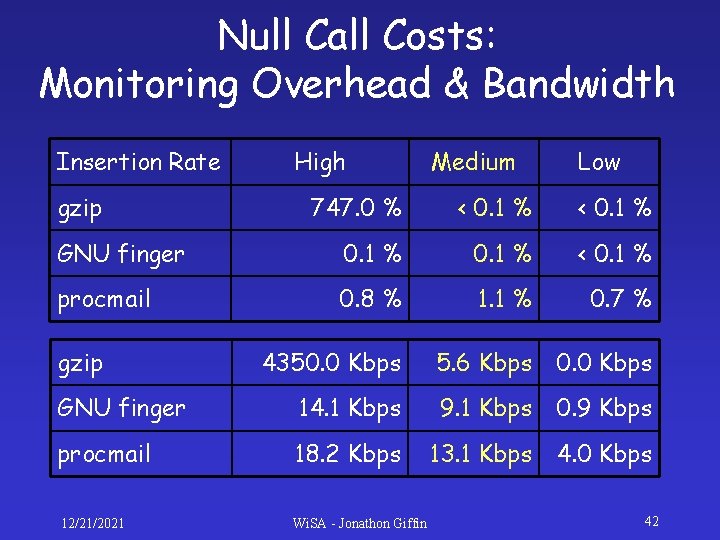
Null Call Costs: Monitoring Overhead & Bandwidth Insertion Rate gzip High Medium Low 747. 0 % < 0. 1 % GNU finger 0. 1 % < 0. 1 % procmail 0. 8 % 1. 1 % 0. 7 % 4350. 0 Kbps 5. 6 Kbps 0. 0 Kbps GNU finger 14. 1 Kbps 9. 1 Kbps 0. 9 Kbps procmail 18. 2 Kbps 13. 1 Kbps 4. 0 Kbps 12/21/2021 Wi. SA - Jonathon Giffin gzip 42

12/21/2021 Wi. SA - Jonathon Giffin 43
Important Ideas • Running jobs remotely enables malicious attacks against the shadow process. • Pre-execution static analysis to construct a model of the remote call sequences addresses this threat. • Improving model precision is a hard problem. Null calls are an effective and reasonable optimization. 12/21/2021 Wi. SA - Jonathon Giffin 44

Protecting Your Local Host From Remote Security Attacks Jonathon Giffin, Somesh Jha, Bart Miller University of Wisconsin Wi. SA - Jonathon Giffin