Protecting your data with Azure AD Arjan Cornelisssen




- Slides: 23

Protecting your data with Azure AD
Arjan Cornelisssen Share. Point & Office 365 Architect Work. Together. tech @arjancornelis
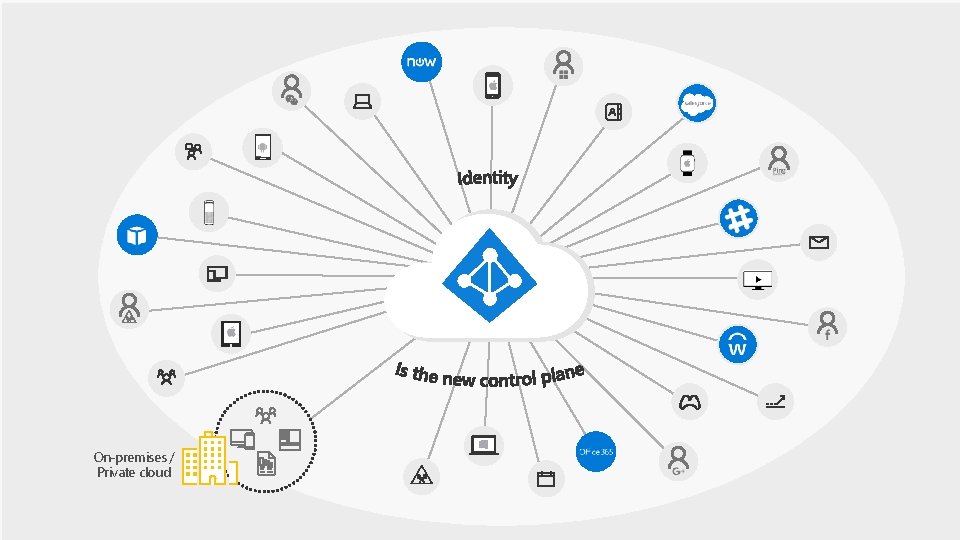
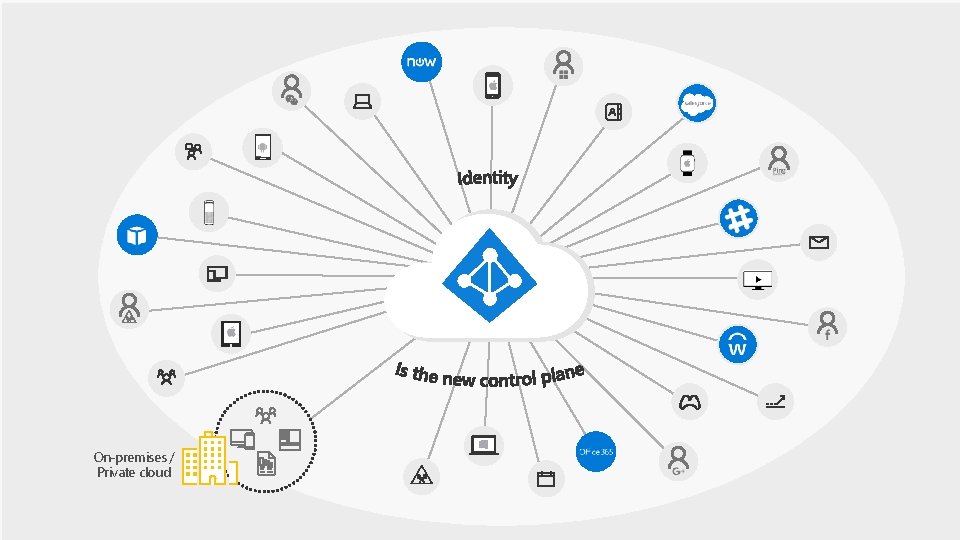
On-premises / Private cloud
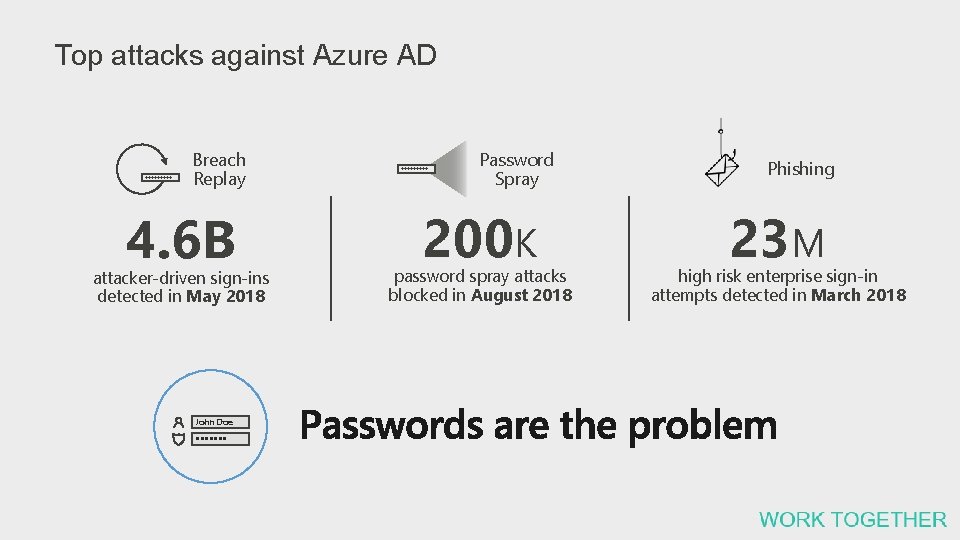
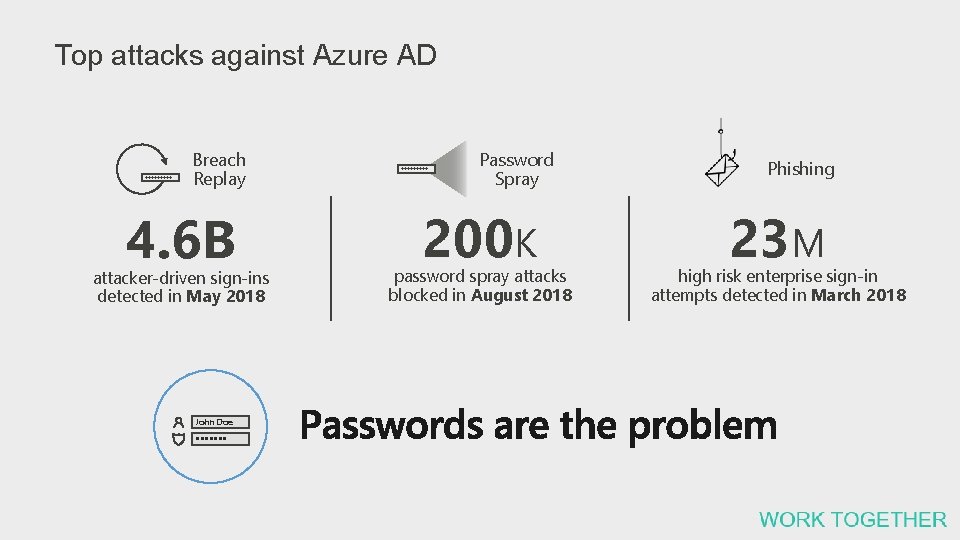
Top attacks against Azure AD lllll Breach Replay 4. 6 B attacker-driven sign-ins detected in May 2018 John Doe lllllllll Password Spray 200 K password spray attacks blocked in August 2018 Phishing 23 M high risk enterprise sign-in attempts detected in March 2018
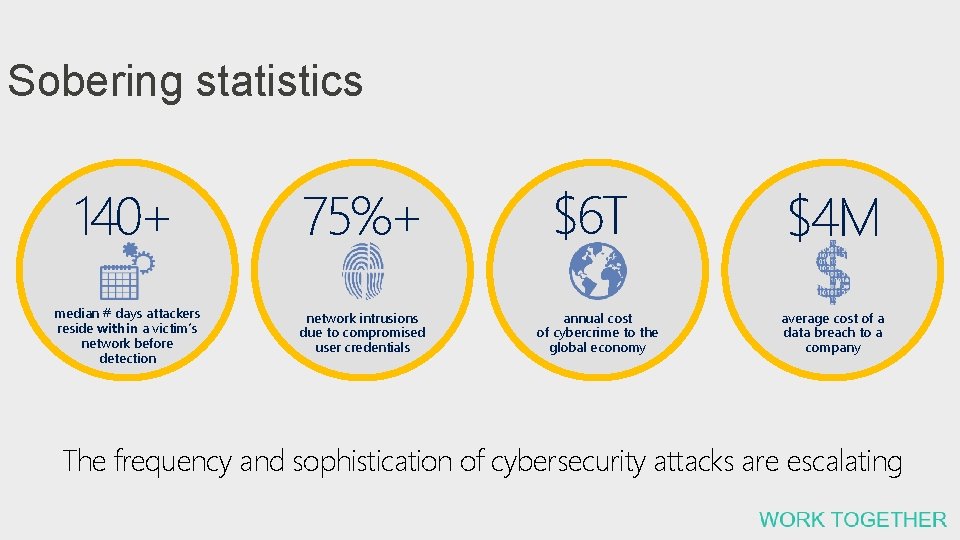
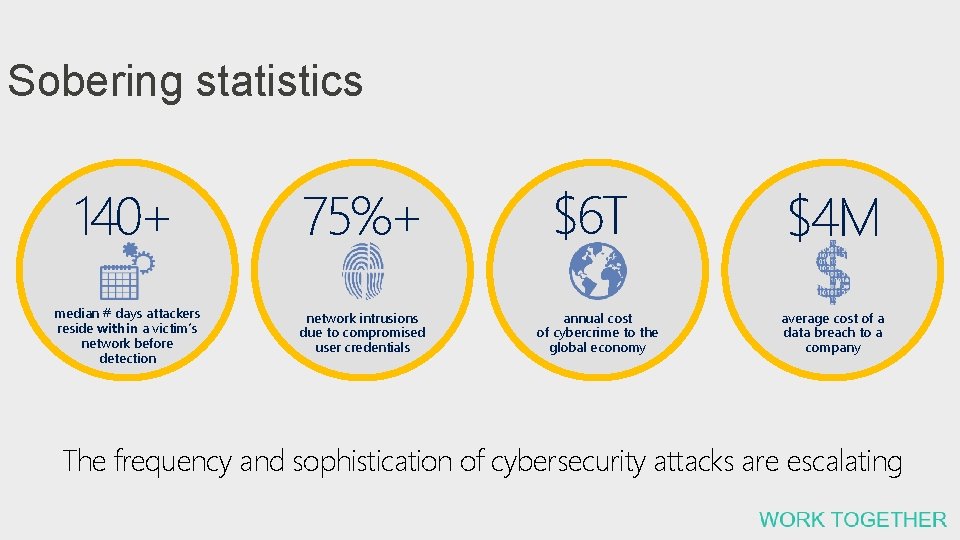
Sobering statistics 140+ 75%+ median # days attackers reside within a victim’s network before detection network intrusions due to compromised user credentials $6 T annual cost of cybercrime to the global economy $4 M average cost of a data breach to a company The frequency and sophistication of cybersecurity attacks are escalating
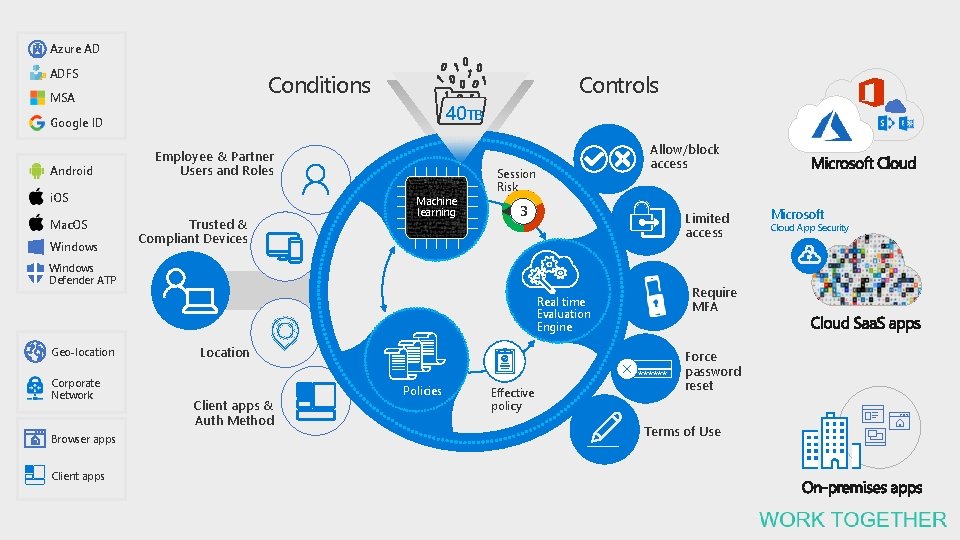
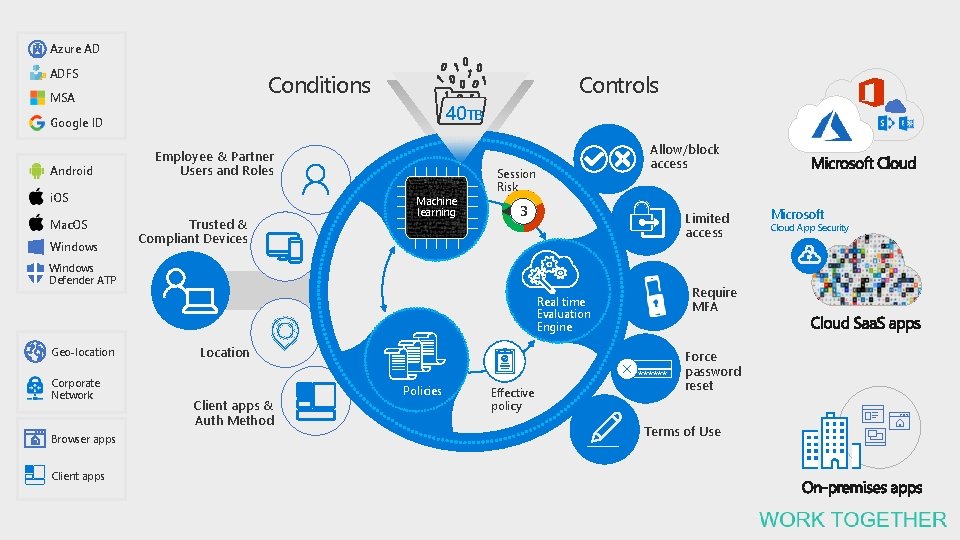
Azure AD ADFS Controls Conditions MSA 40 TB Google ID Android Employee & Partner Users and Roles i. OS Mac. OS Windows Trusted & Compliant Devices Machine learning Allow/block access Session Risk 3 Limited access Windows Defender ATP Require MFA Real time Evaluation Engine Geo-location Corporate Network Browser apps Client apps Location Client apps & Auth Method Policies ****** Effective policy Force password reset Terms of Use Microsoft Cloud App Security

Multi Factor Authentication
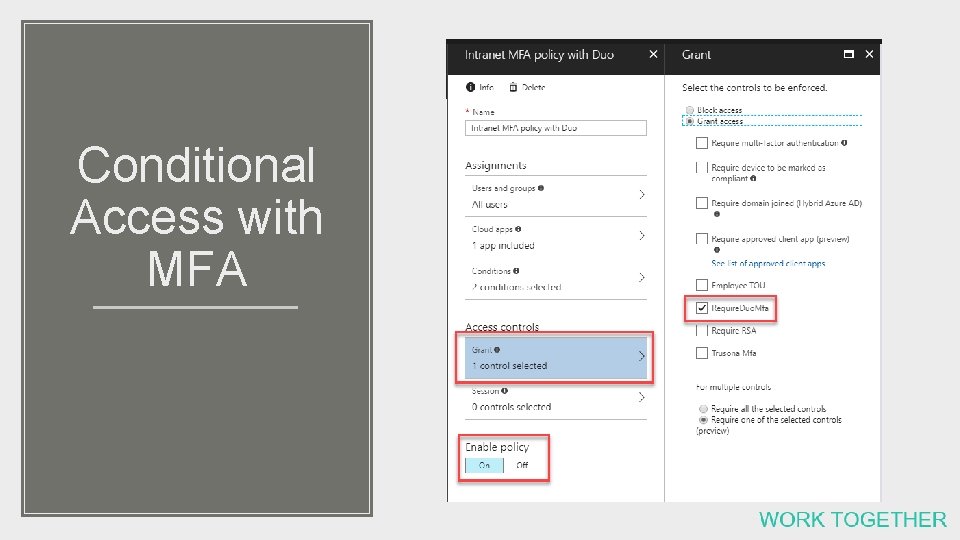
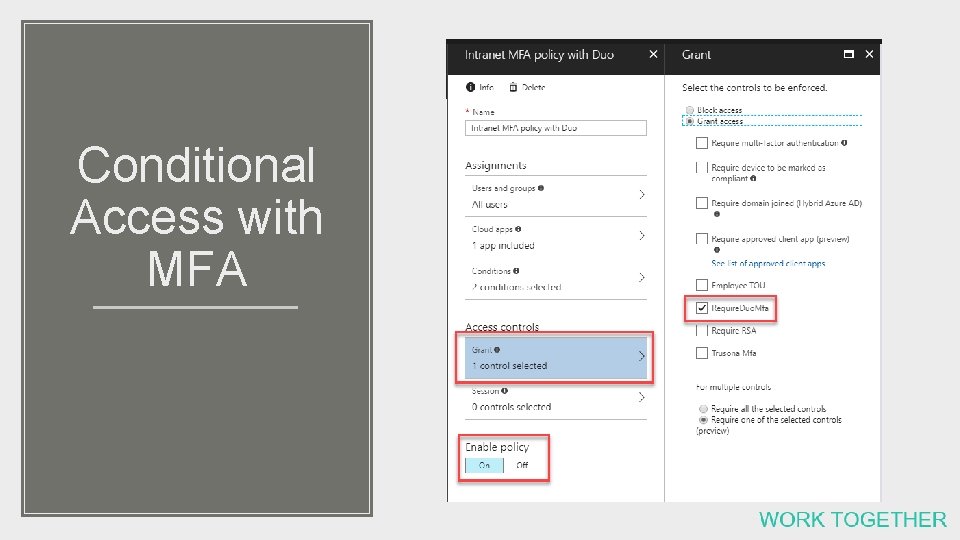
Conditional Access with MFA
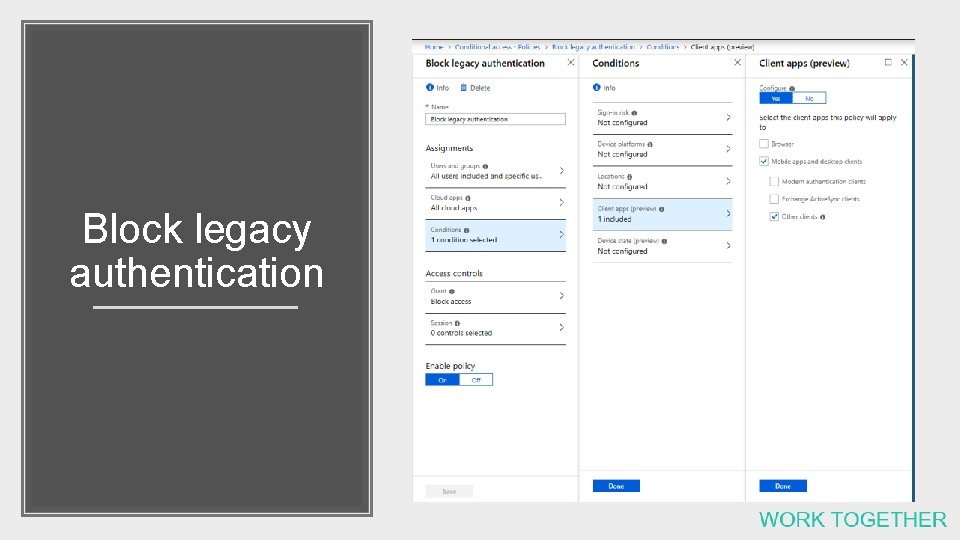
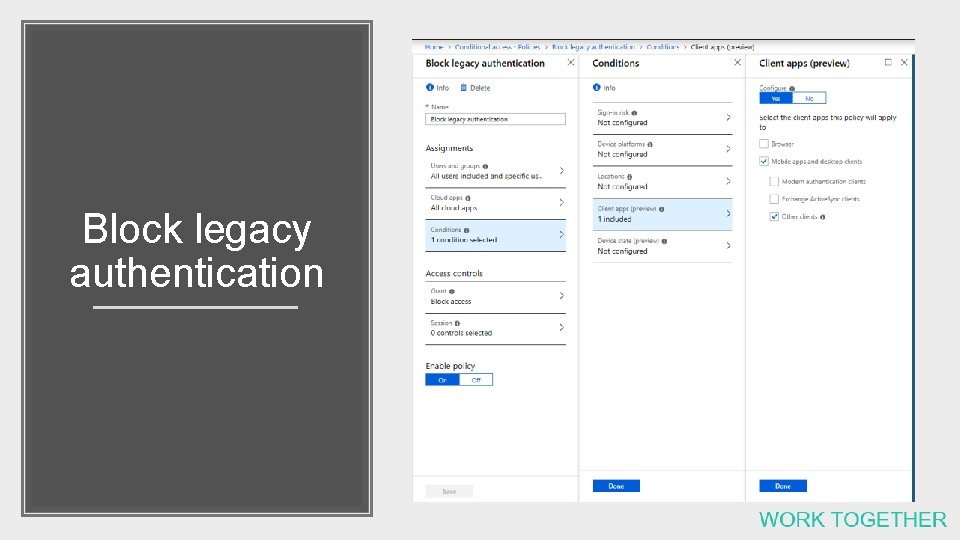
Block legacy authentication
Demo
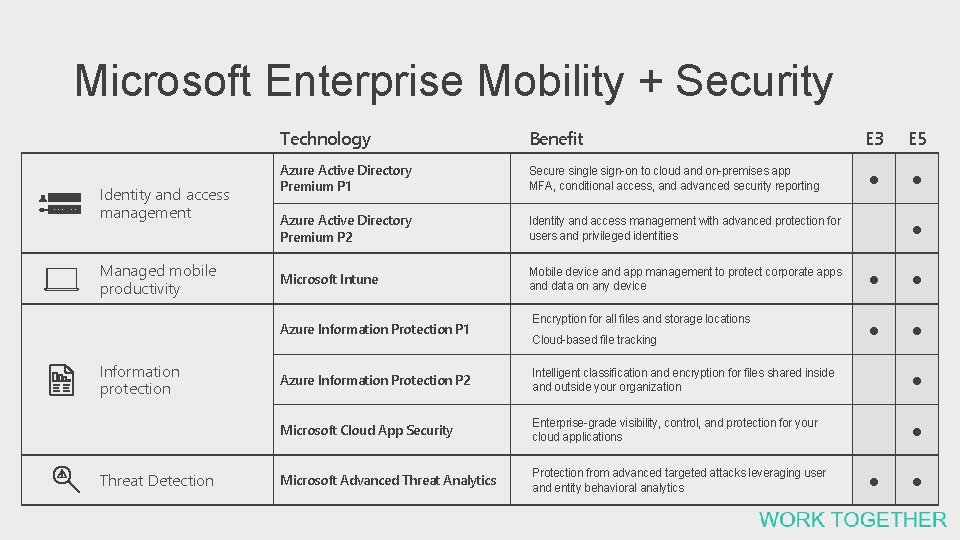
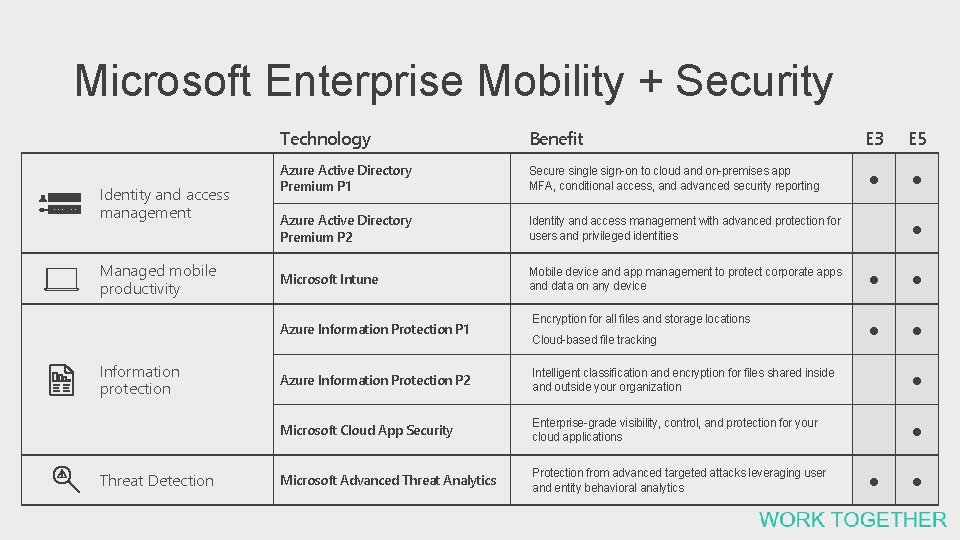
Microsoft Enterprise Mobility + Security Identity and access management Managed mobile productivity Technology Benefit Azure Active Directory Premium P 1 Secure single sign-on to cloud and on-premises app MFA, conditional access, and advanced security reporting Azure Active Directory Premium P 2 Identity and access management with advanced protection for users and privileged identities Microsoft Intune Mobile device and app management to protect corporate apps and data on any device ● ● Encryption for all files and storage locations ● ● Azure Information Protection P 1 Information protection Threat Detection Cloud-based file tracking E 3 E 5 ● ● ● Azure Information Protection P 2 Intelligent classification and encryption for files shared inside and outside your organization ● Microsoft Cloud App Security Enterprise-grade visibility, control, and protection for your cloud applications ● Microsoft Advanced Threat Analytics Protection from advanced targeted attacks leveraging user and entity behavioral analytics ● ●

Admin side
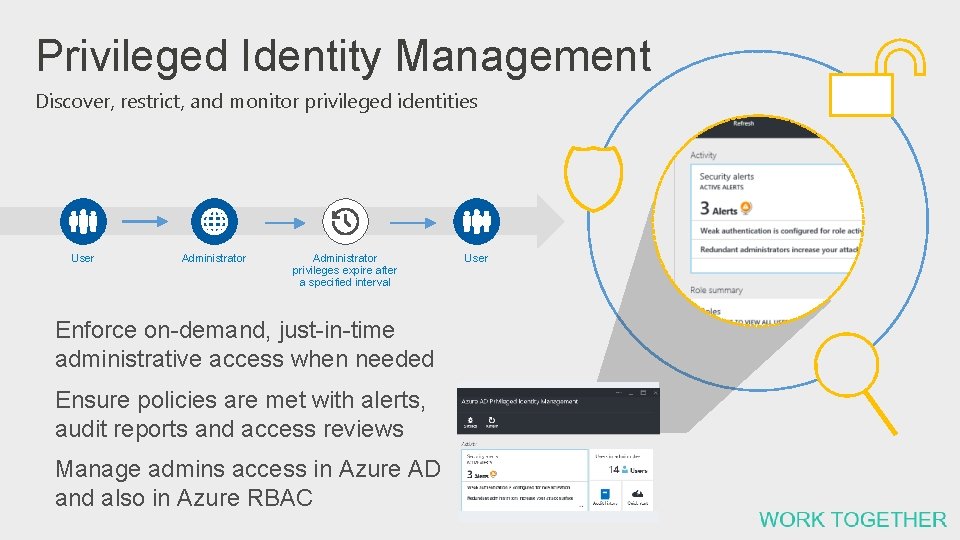
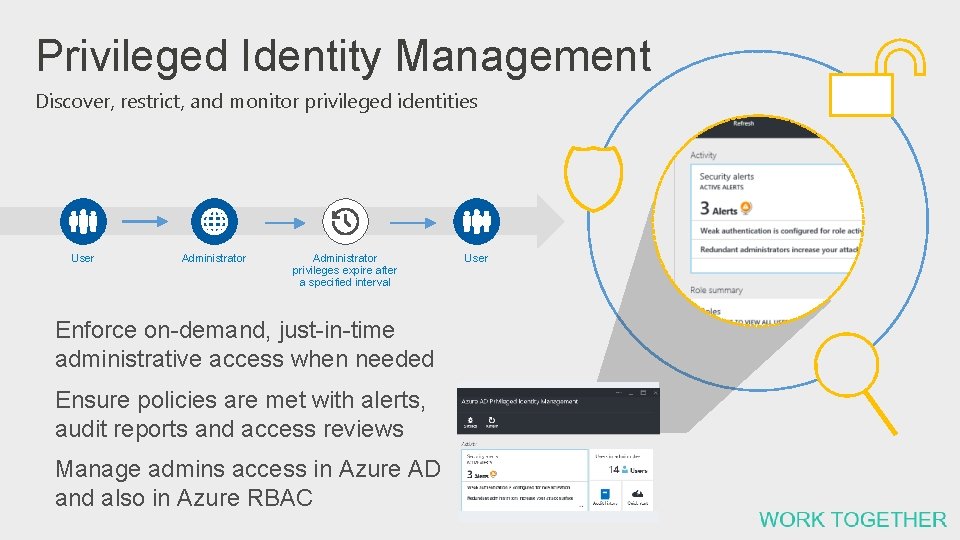
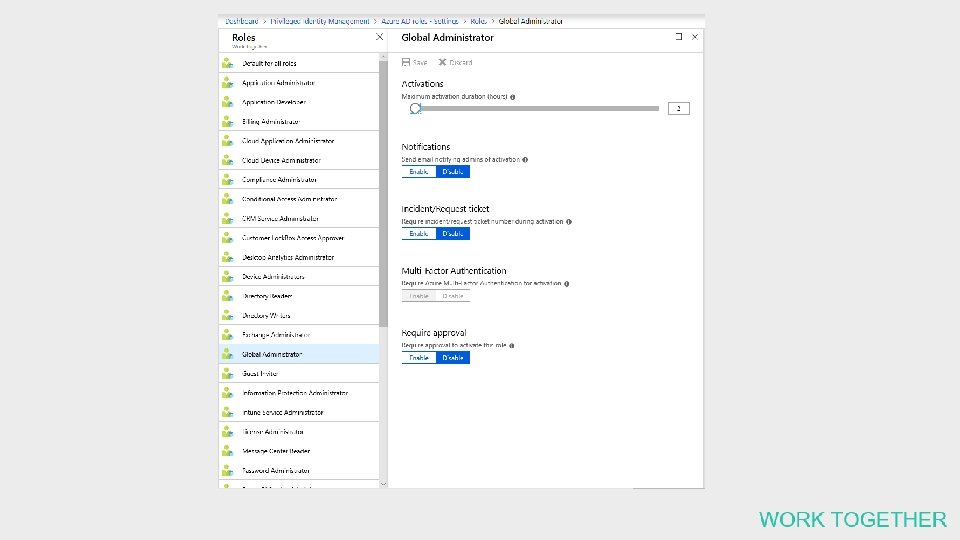
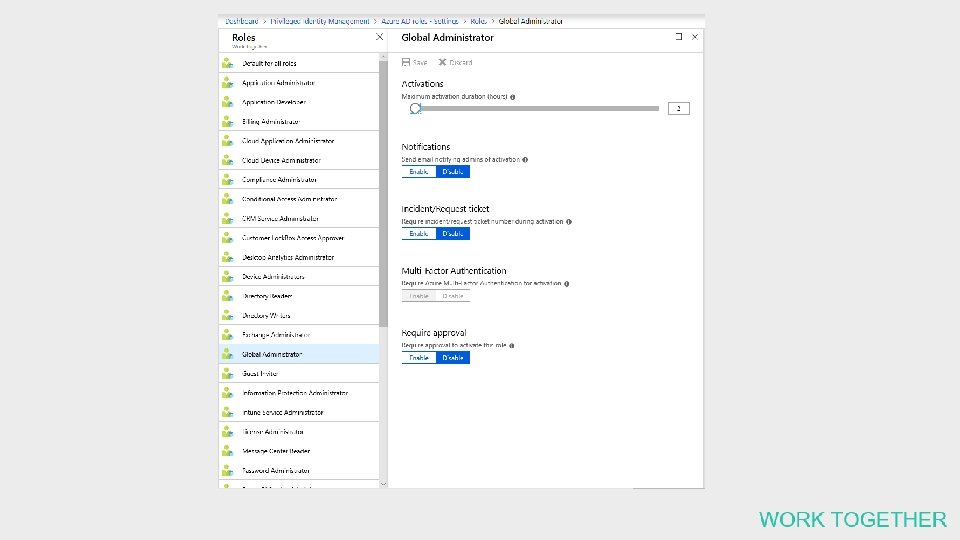
Privileged Identity Management Discover, restrict, and monitor privileged identities User Administrator privileges expire after a specified interval Enforce on-demand, just-in-time administrative access when needed Ensure policies are met with alerts, audit reports and access reviews Manage admins access in Azure AD and also in Azure RBAC User
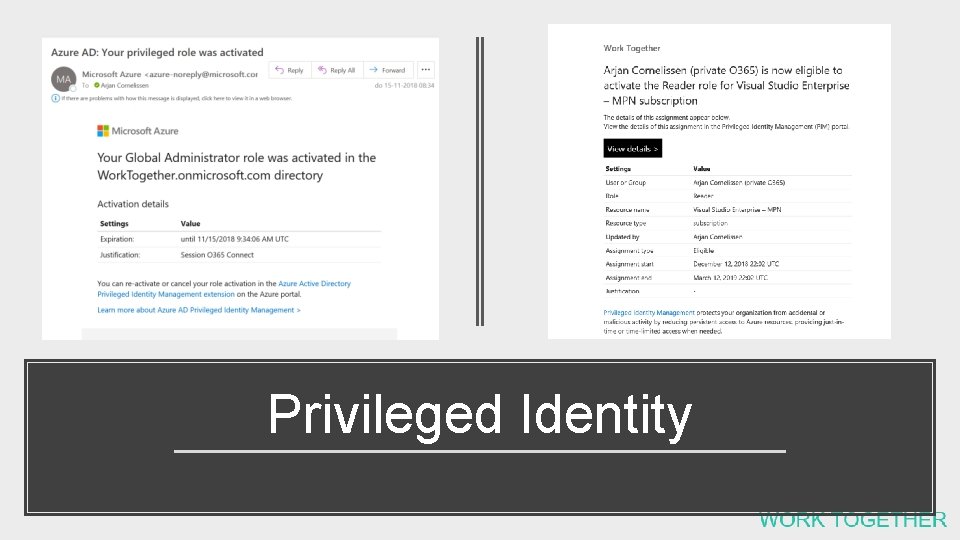
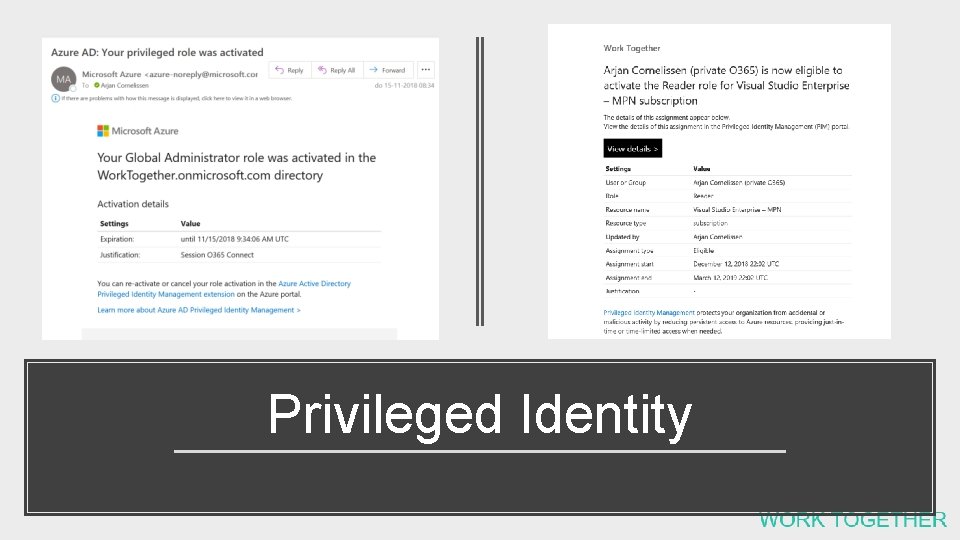
Privileged Identity
Demo
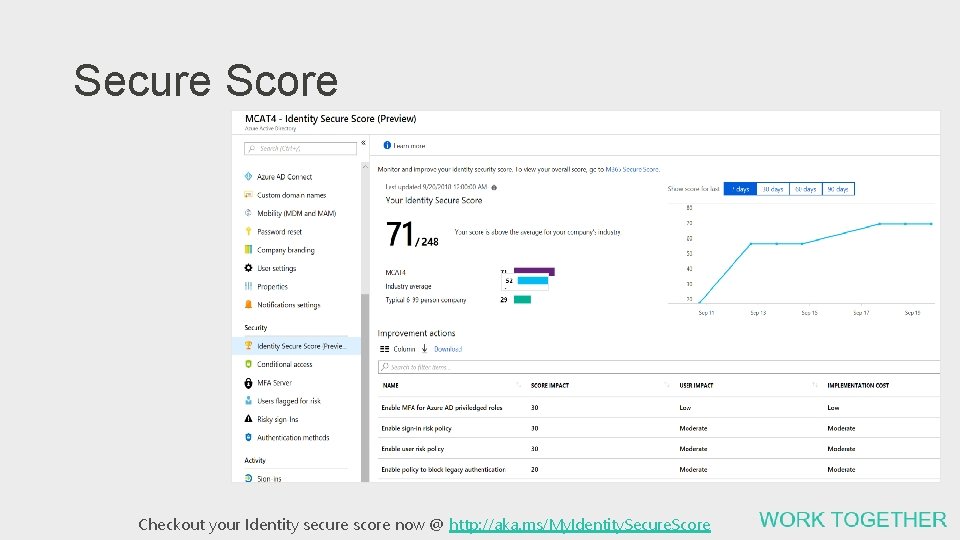
Identity Secure Score Visibility into your Identity security position and how to improve it Insights into your Identity security position Guidance to increase your security level Set an ideal score. Easily compare score against other organizations Choose controls to achieve ideal score based on impact. View trends Ignore controls that are not valid for you. 3 rd party product support. Checkout your Identity secure score now @ http: //aka. ms/My. Identity. Secure. Score
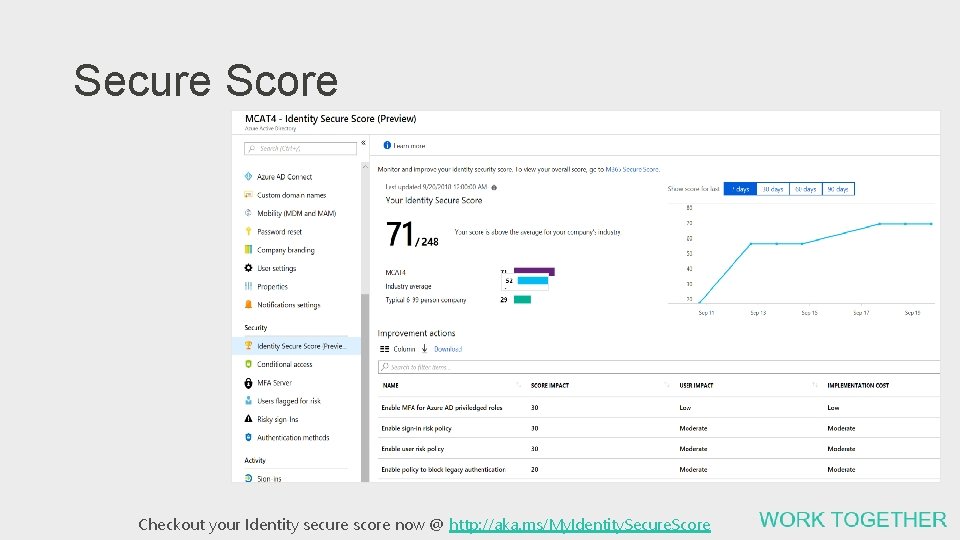
Secure Score Checkout your Identity secure score now @ http: //aka. ms/My. Identity. Secure. Score
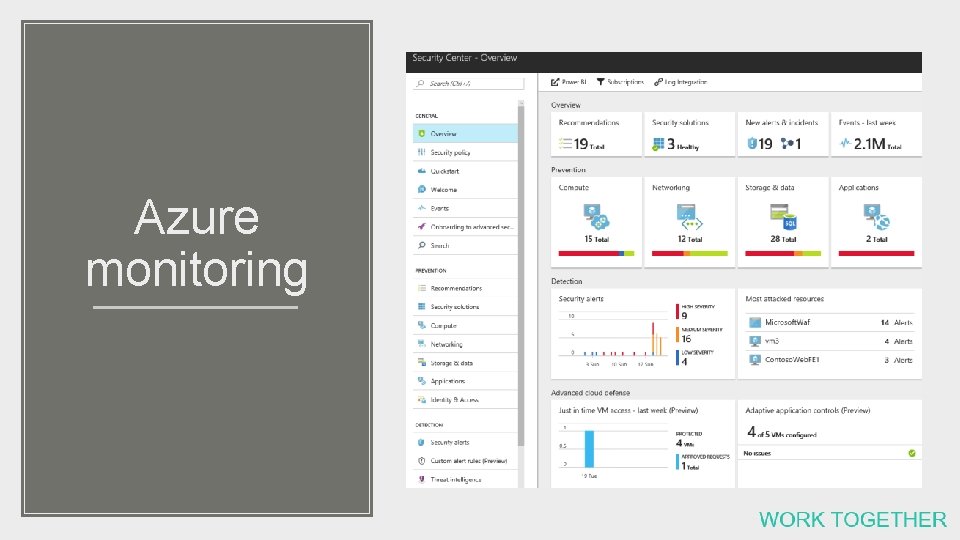
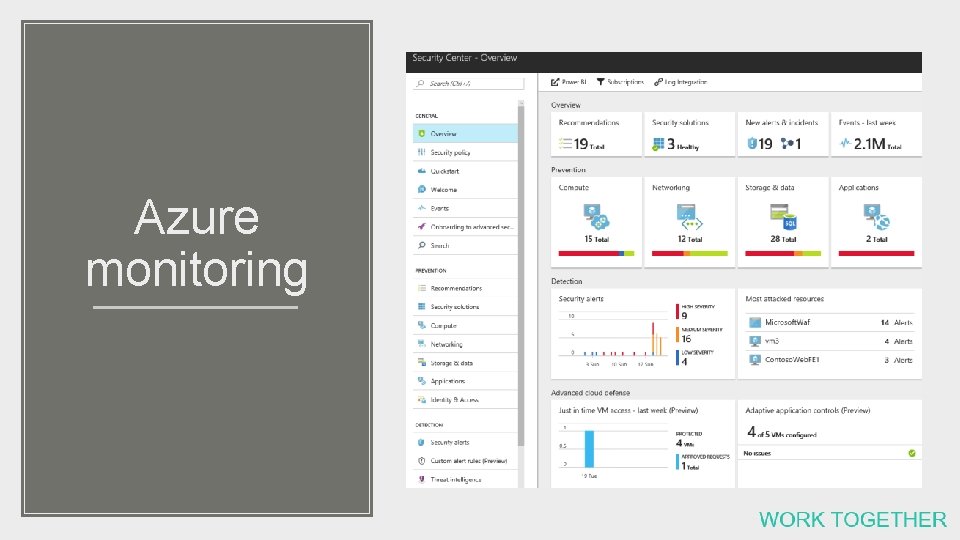
Azure monitoring

Preview features
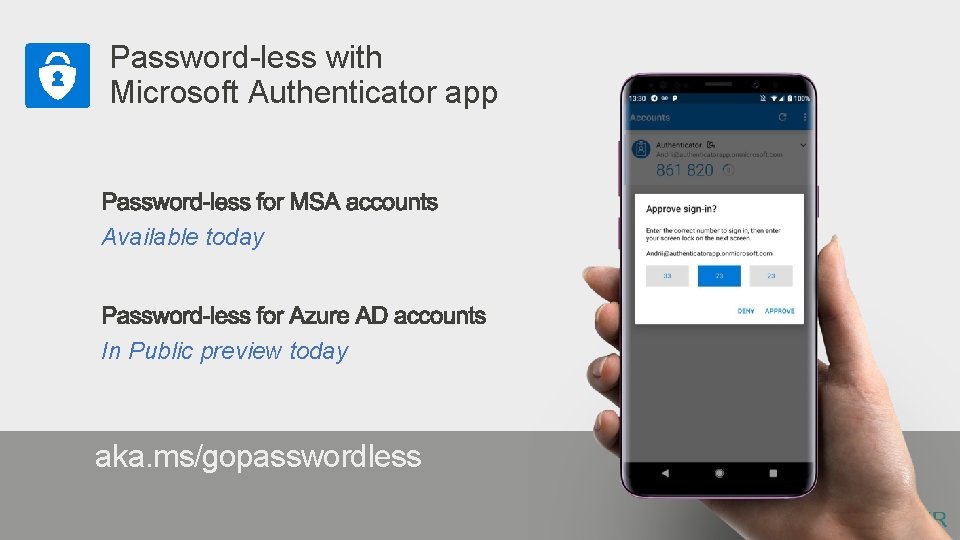
Password-less with Microsoft Authenticator app Available today In Public preview today aka. ms/gopasswordless
Demo
Our Security mindset needs to be updated