PROTECTING PEOPLE FROM ADVANCED THREATS Peter Boll 1

PROTECTING PEOPLE FROM ADVANCED THREATS Peter Boll 1 © 2016 Proofpoint, Inc.
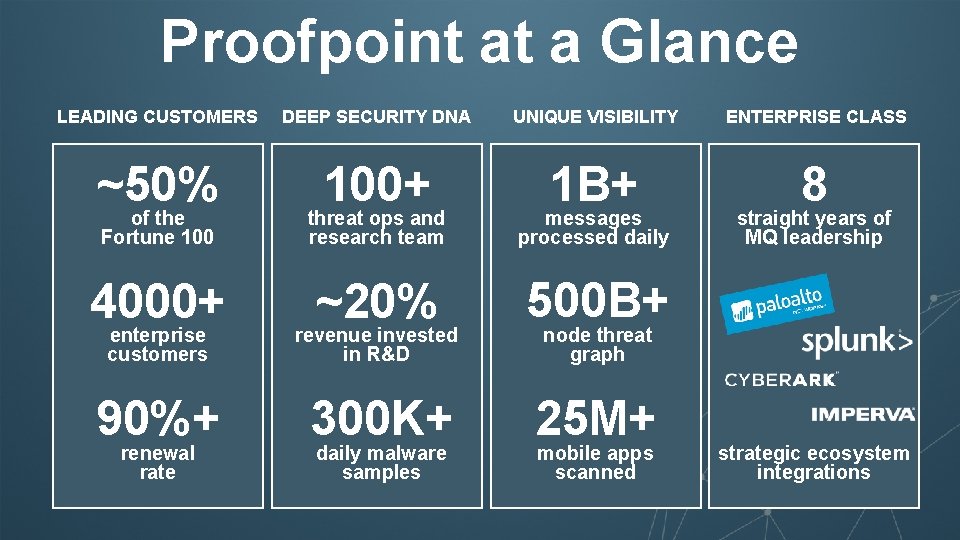
Proofpoint at a Glance LEADING CUSTOMERS DEEP SECURITY DNA UNIQUE VISIBILITY ENTERPRISE CLASS ~50% 100+ 1 B+ 8 of the Fortune 100 threat ops and research team messages processed daily 4000+ enterprise customers ~20% revenue invested in R&D 500 B+ 90%+ 300 K+ 25 M+ renewal rate daily malware samples straight years of MQ leadership node threat graph mobile apps scanned strategic ecosystem integrations 2 © 2016 Proofpoint, Inc.
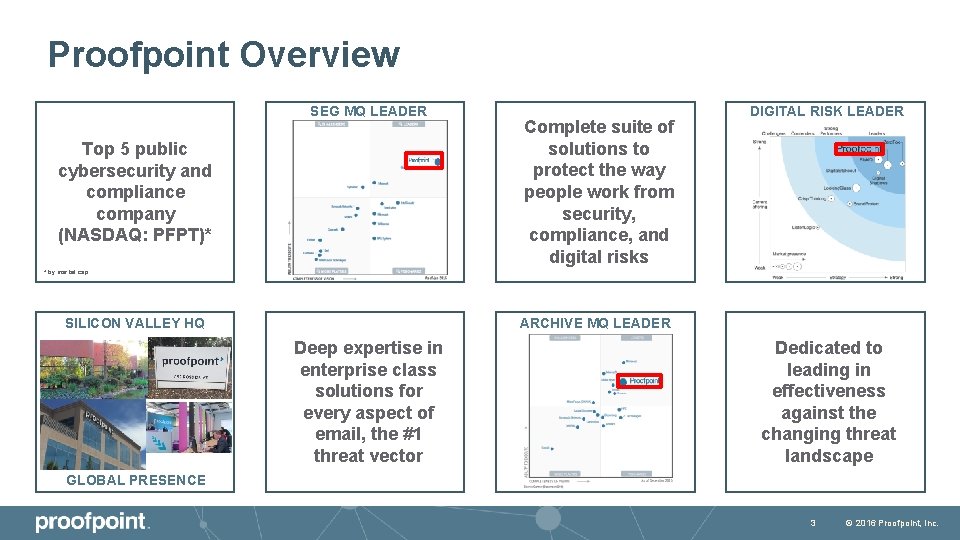
Proofpoint Overview SEG MQ LEADER Top 5 public cybersecurity and compliance company (NASDAQ: PFPT)* Complete suite of solutions to protect the way people work from security, compliance, and digital risks DIGITAL RISK LEADER * by market cap SILICON VALLEY HQ ARCHIVE MQ LEADER Deep expertise in enterprise class solutions for every aspect of email, the #1 threat vector Dedicated to leading in effectiveness against the changing threat landscape GLOBAL PRESENCE 3 © 2016 Proofpoint, Inc.
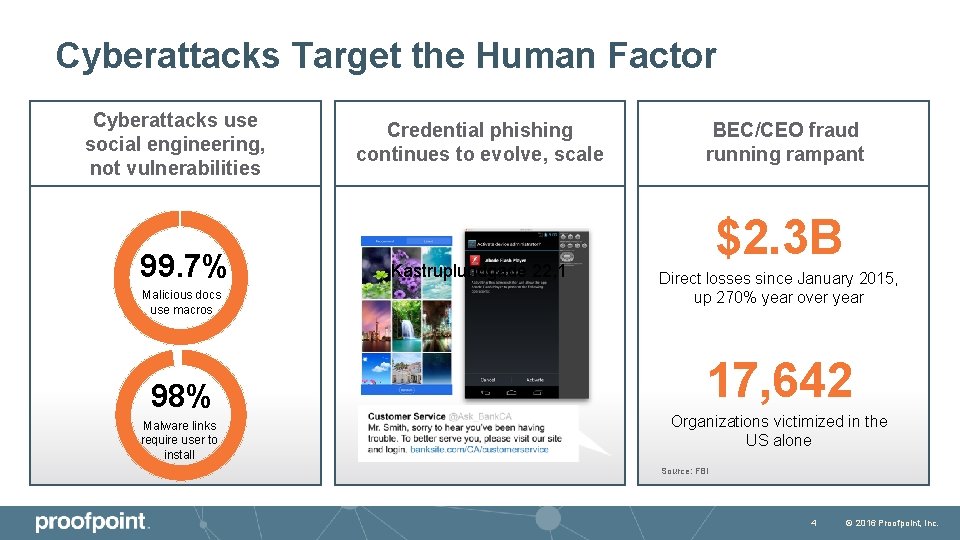
Cyberattacks Target the Human Factor Cyberattacks use social engineering, not vulnerabilities 99. 7% Malicious docs use macros 98% Malware links require user to install Credential phishing continues to evolve, scale Kastruplundgade 22, 1 BEC/CEO fraud running rampant $2. 3 B Direct losses since January 2015, up 270% year over year 17, 642 Organizations victimized in the US alone Source: FBI 4 © 2016 Proofpoint, Inc.
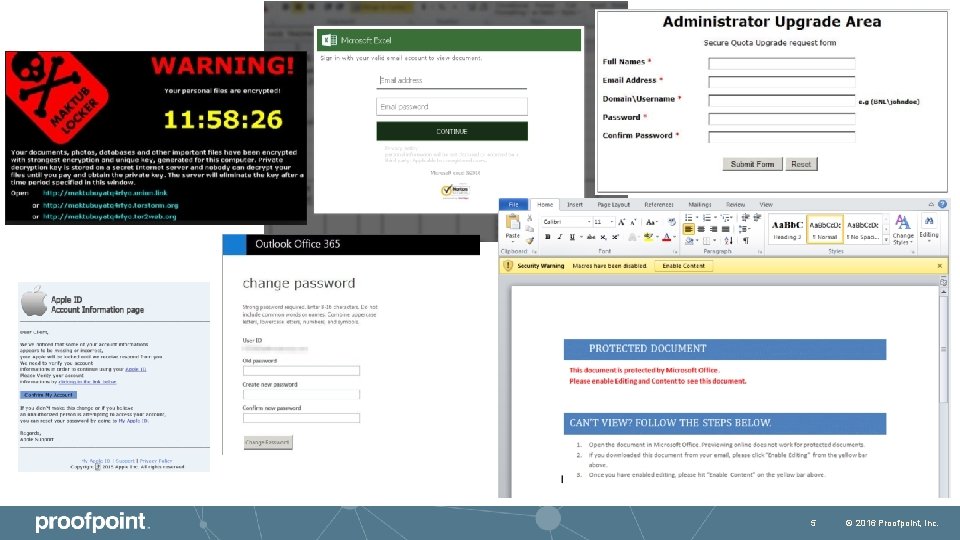
5 © 2016 Proofpoint, Inc.
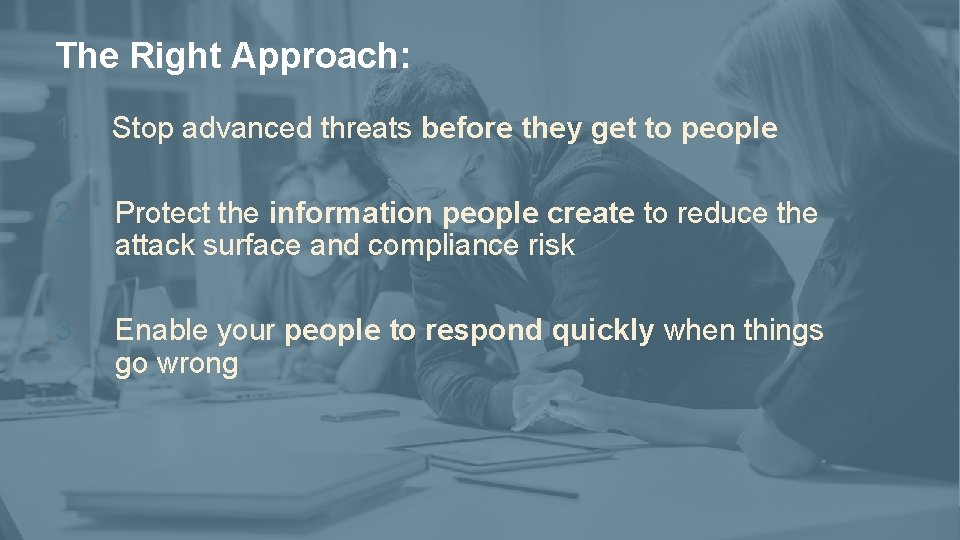
The Right Approach: 1. Stop advanced threats before they get to people 2. Protect the information people create to reduce the attack surface and compliance risk 3. Enable your people to respond quickly when things go wrong 6 © 2016 Proofpoint, Inc.
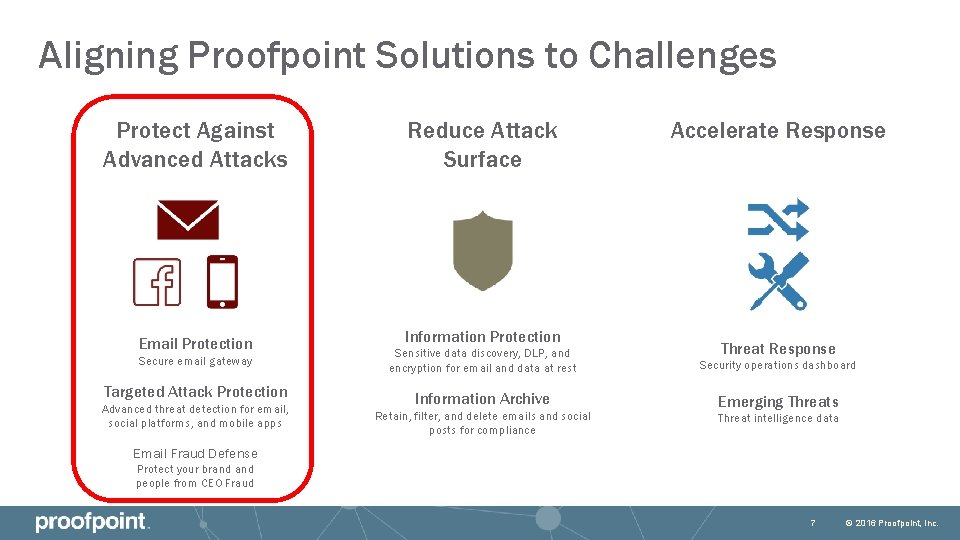
Aligning Proofpoint Solutions to Challenges Protect Against Advanced Attacks Reduce Attack Surface Email Protection Information Protection Secure email gateway Targeted Attack Protection Advanced threat detection for email, social platforms, and mobile apps Accelerate Response Threat Response Sensitive data discovery, DLP, and encryption for email and data at rest Security operations dashboard Information Archive Emerging Threats Retain, filter, and delete emails and social posts for compliance Threat intelligence data Email Fraud Defense Protect your brand people from CEO Fraud 7 © 2016 Proofpoint, Inc.
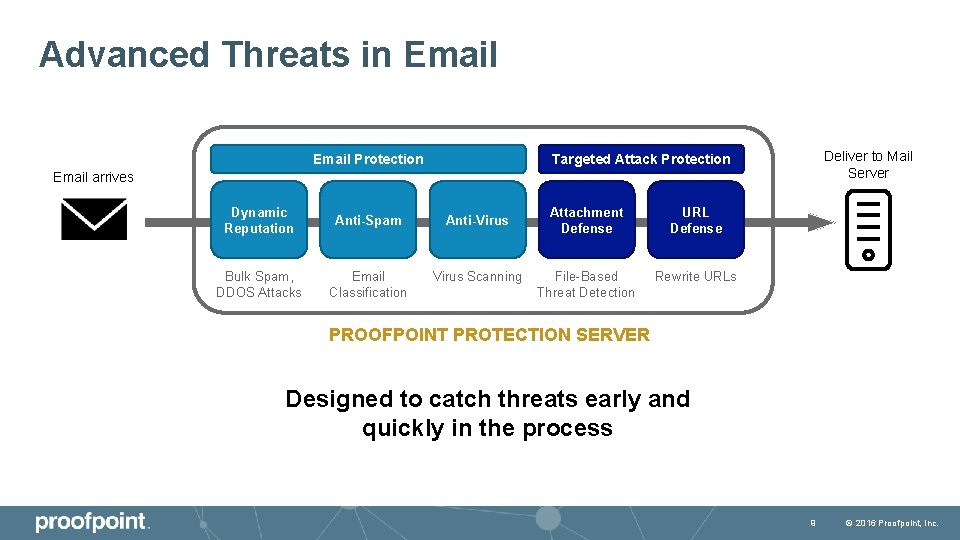
Advanced Threats in Email Protection Deliver to Mail Server Targeted Attack Protection Email arrives Dynamic Reputation Anti-Spam Anti-Virus Bulk Spam, DDOS Attacks Email Classification Virus Scanning Attachment Defense URL Defense File-Based Threat Detection Rewrite URLs PROOFPOINT PROTECTION SERVER Designed to catch threats early and quickly in the process 9 © 2016 Proofpoint, Inc.

Proofpoint Advanced Threat Differentiation Architecture Analysis Intelligence Cloud Architecture Multi-Stage Analysis Techniques Global Visibility Protect in the Flow of Attack Channels Learn Across the Entire Attack Chain Actionable Forensic Insight 11 © 2016 Proofpoint, Inc.

Introducing Targeted Attack Protection 13 © 2016 Proofpoint, Inc.
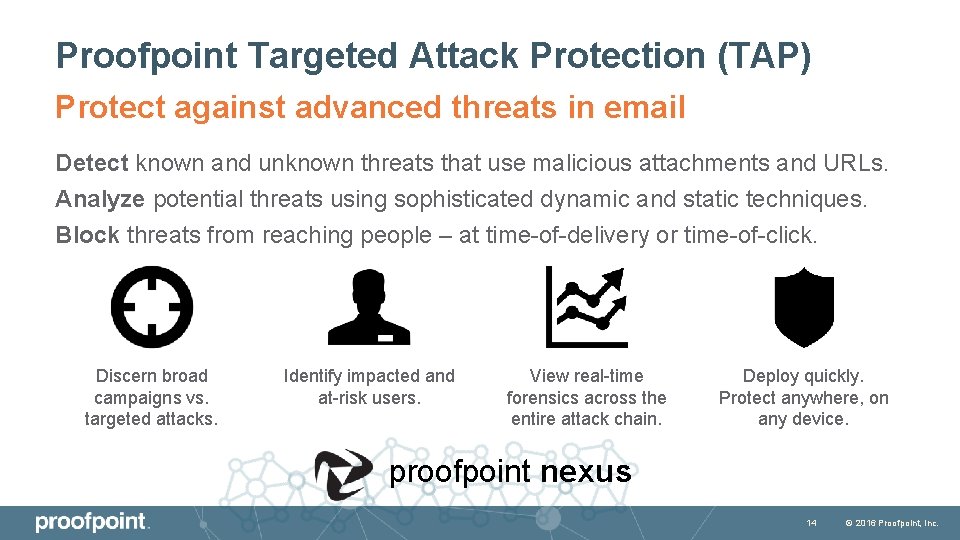
Proofpoint Targeted Attack Protection (TAP) Protect against advanced threats in email Detect known and unknown threats that use malicious attachments and URLs. Analyze potential threats using sophisticated dynamic and static techniques. Block threats from reaching people – at time-of-delivery or time-of-click. Discern broad campaigns vs. targeted attacks. Identify impacted and at-risk users. View real-time forensics across the entire attack chain. Deploy quickly. Protect anywhere, on any device. proofpoint nexus 14 © 2016 Proofpoint, Inc.
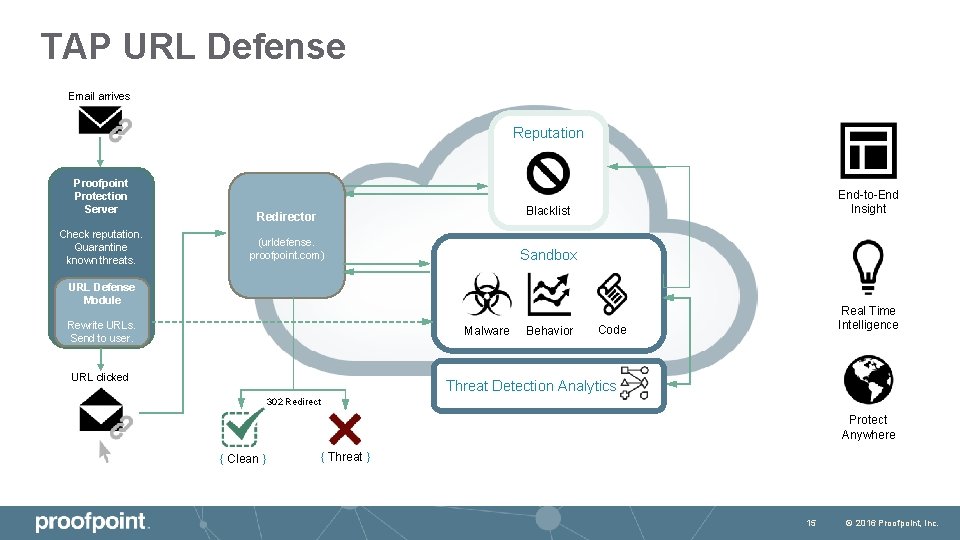
TAP URL Defense Email arrives Reputation Proofpoint Protection Server Check reputation. Quarantine known threats. End-to-End Insight Blacklist Redirector (urldefense. proofpoint. com) Sandbox URL Defense Module Rewrite URLs. Send to user. Malware URL clicked Behavior Real Time Intelligence Code Threat Detection Analytics 302 Redirect Protect Anywhere { Clean } { Threat } 15 © 2016 Proofpoint, Inc.
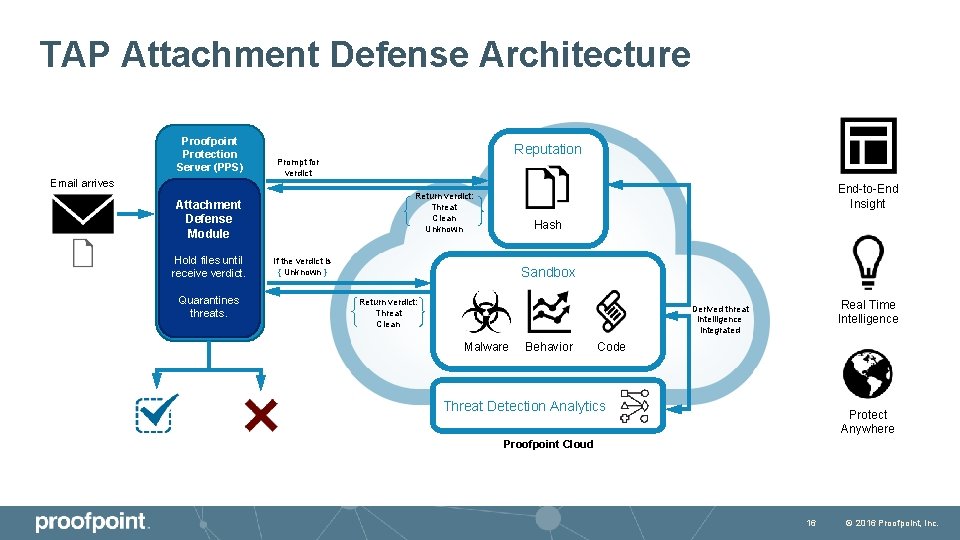
TAP Attachment Defense Architecture Proofpoint Protection Server (PPS) Email arrives Quarantines threats. End-to-End Insight Return verdict: Threat Clean Unknown Attachment Defense Module Hold files until receive verdict. Reputation Prompt for verdict Hash If the verdict is { Unknown } Sandbox Return verdict: Threat Clean Real Time Intelligence Derived threat intelligence integrated Malware Behavior Code Threat Detection Analytics Protect Anywhere Proofpoint Cloud 16 © 2016 Proofpoint, Inc.
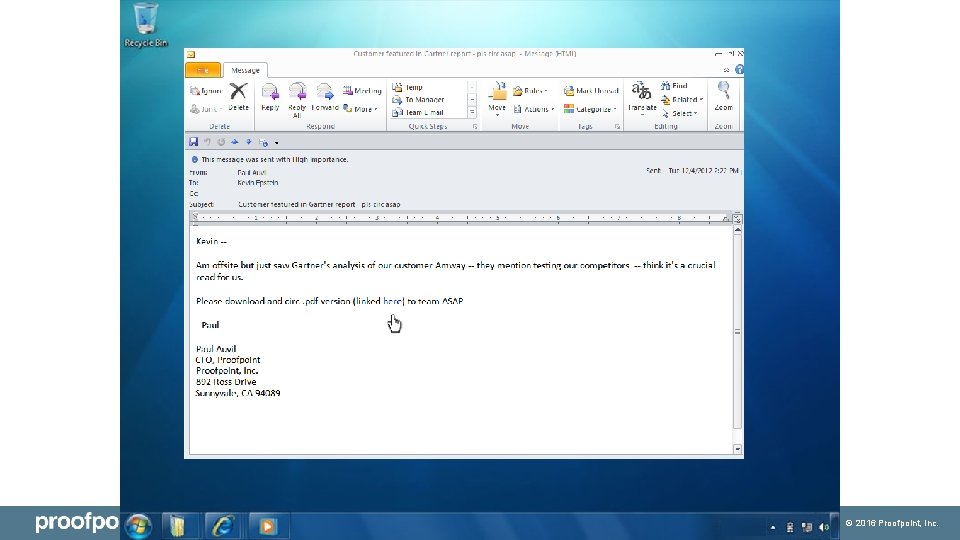
17 © 2016 Proofpoint, Inc.
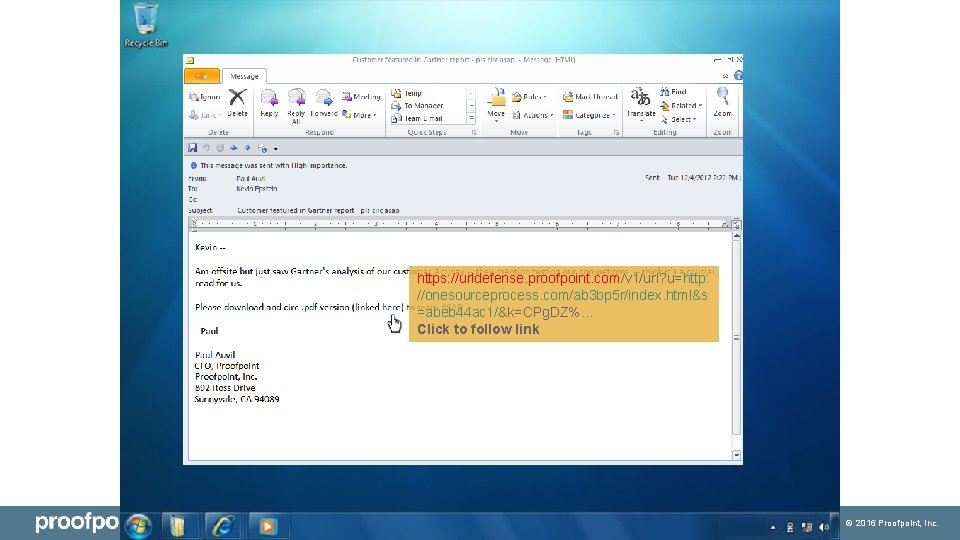
https: //urldefense. proofpoint. com/v 1/url? u=http: //onesourceprocess. com/ab 3 bp 5 r/index. html&s =abeb 44 ac 1/&k=CPg. DZ%. . . Click to follow link 18 © 2016 Proofpoint, Inc.
PROOFPOINT NEXUS AT WORK 23 © 2016 Proofpoint, Inc.
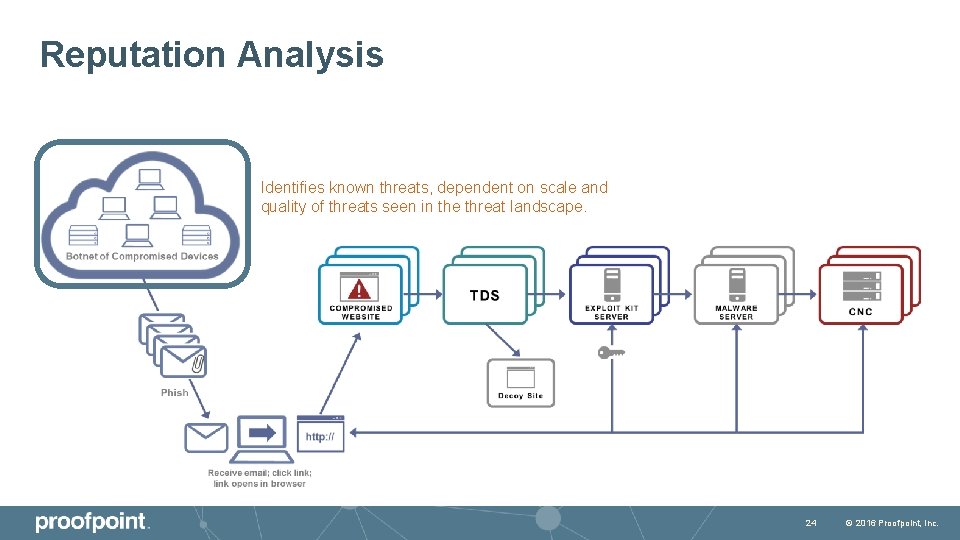
Reputation Analysis Identifies known threats, dependent on scale and quality of threats seen in the threat landscape. 24 © 2016 Proofpoint, Inc.
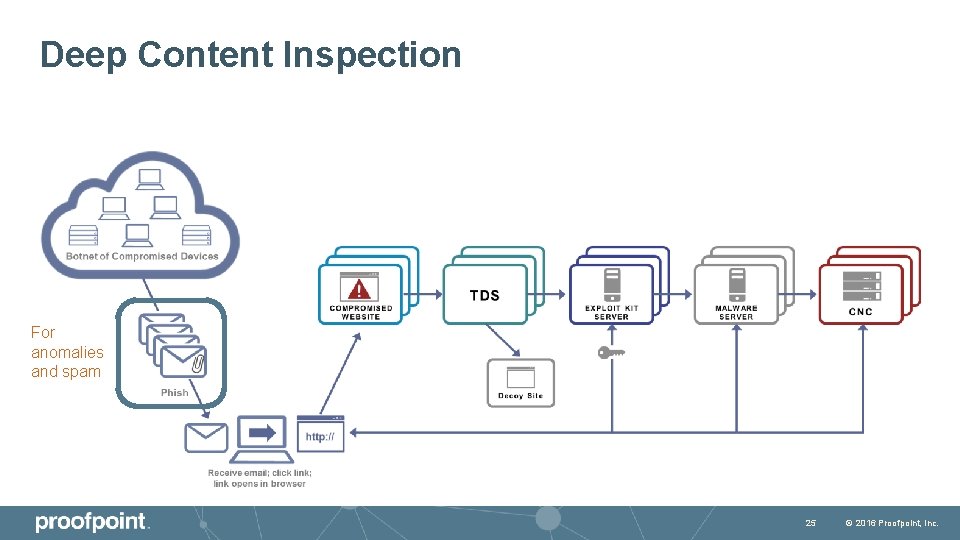
Deep Content Inspection For anomalies and spam 25 © 2016 Proofpoint, Inc.
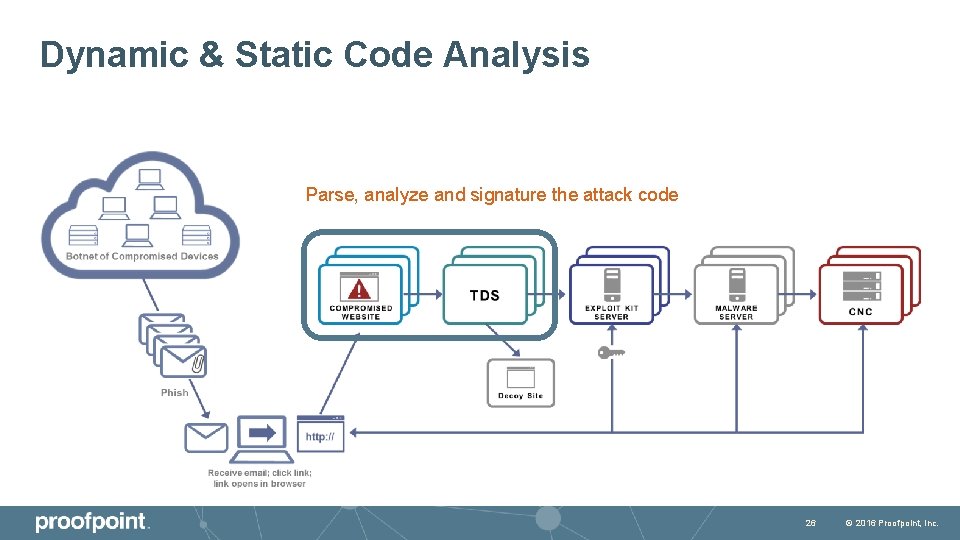
Dynamic & Static Code Analysis Parse, analyze and signature the attack code 26 © 2016 Proofpoint, Inc.
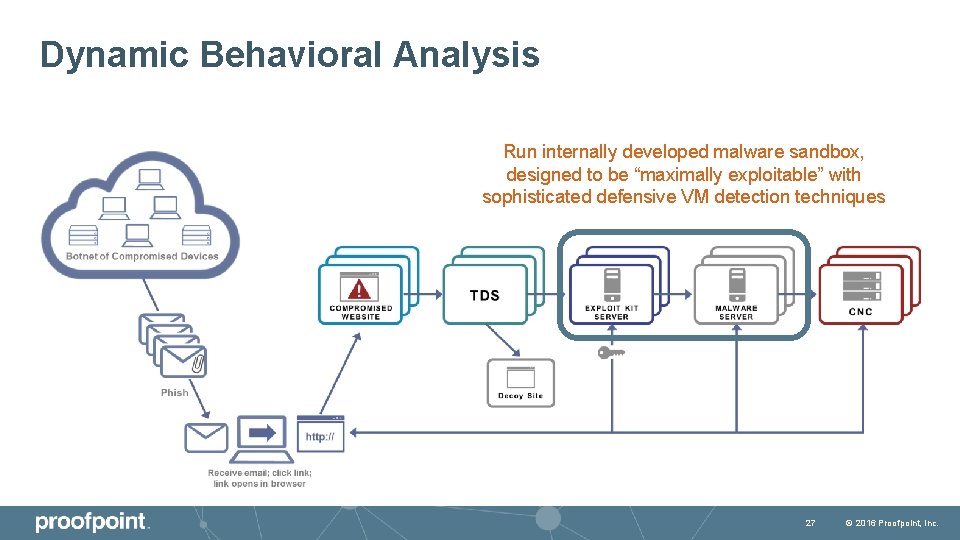
Dynamic Behavioral Analysis Run internally developed malware sandbox, designed to be “maximally exploitable” with sophisticated defensive VM detection techniques 27 © 2016 Proofpoint, Inc.
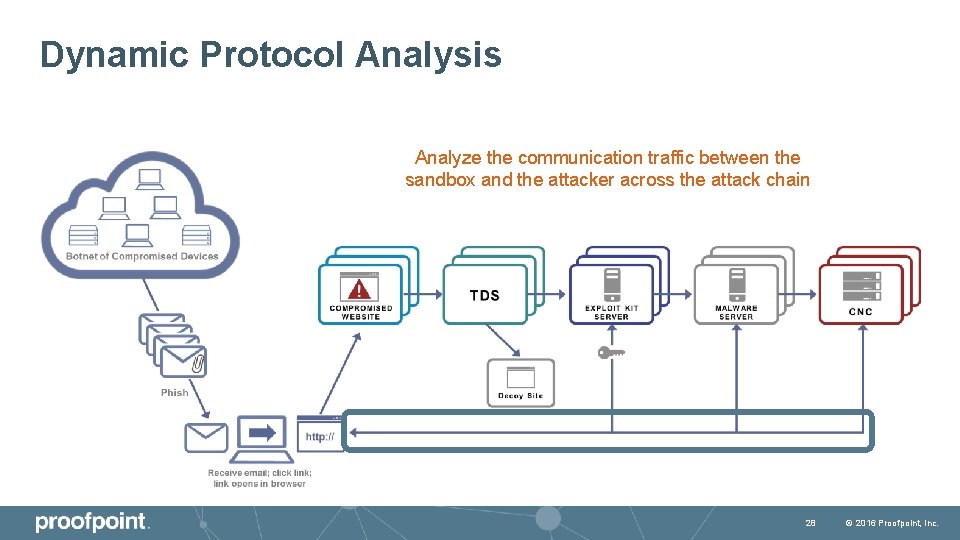
Dynamic Protocol Analysis Analyze the communication traffic between the sandbox and the attacker across the attack chain 28 © 2016 Proofpoint, Inc.
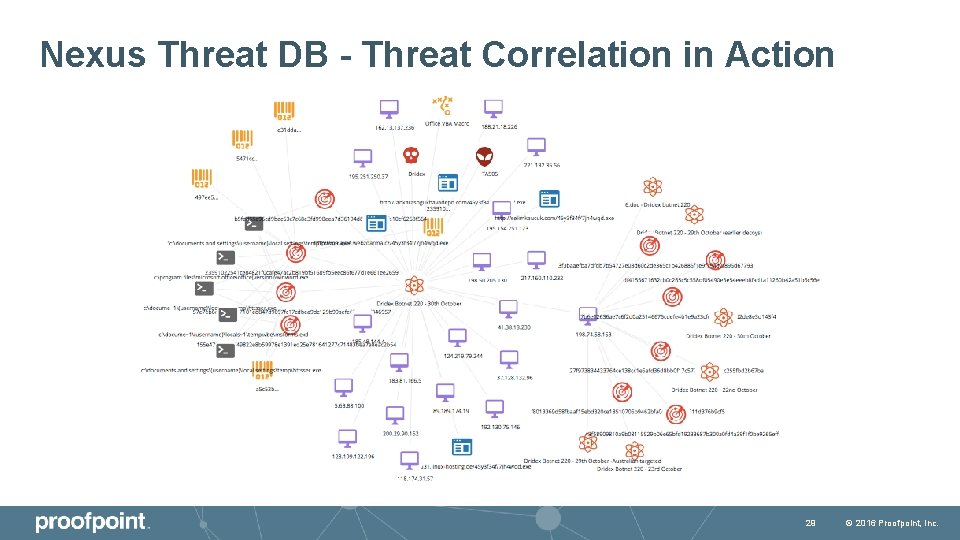
Nexus Threat DB - Threat Correlation in Action 29 © 2016 Proofpoint, Inc.

TAP THREAT DASHBOARD 30 © 2016 Proofpoint, Inc.
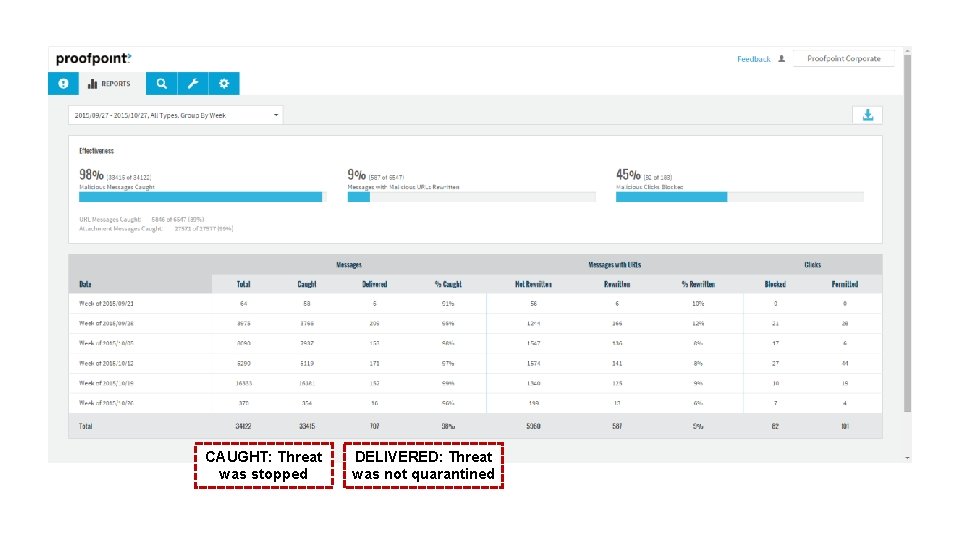
CAUGHT: Threat was stopped DELIVERED: Threat was not quarantined
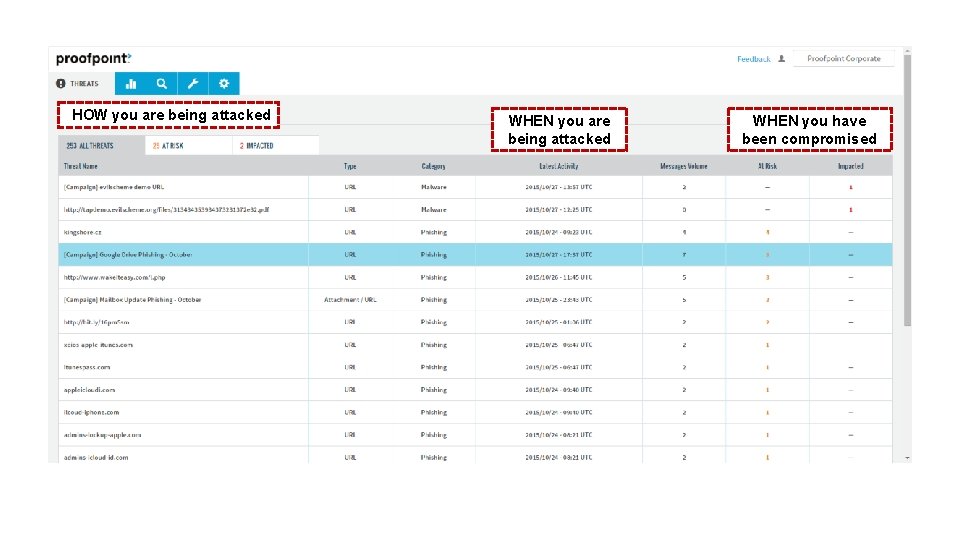
HOW you are being attacked WHEN you have been compromised
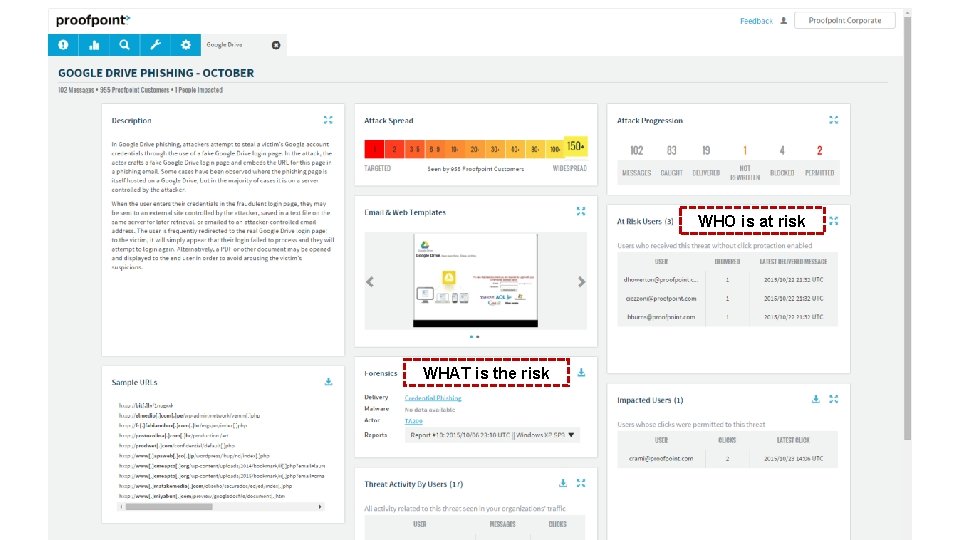
WHO is at risk WHAT is the risk
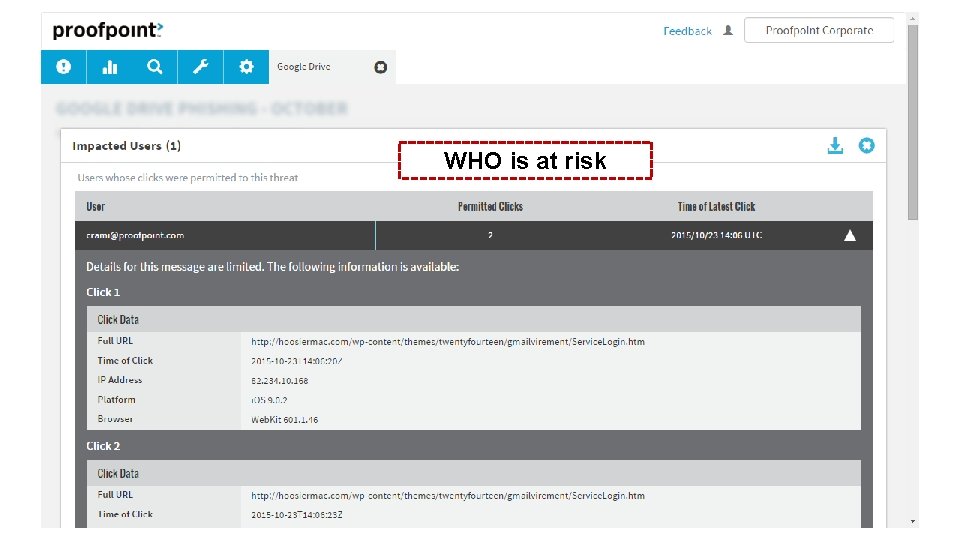
WHO is at risk
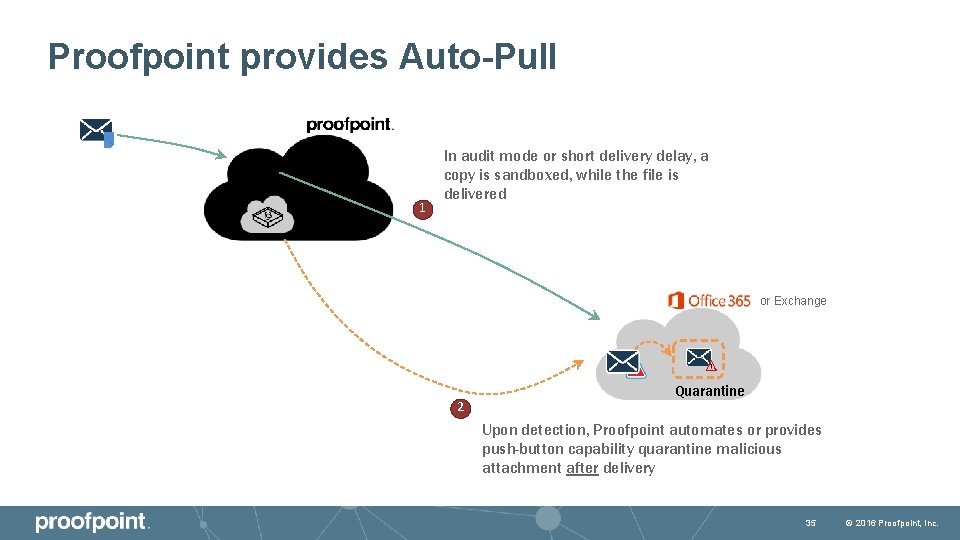
Proofpoint provides Auto-Pull 1 In audit mode or short delivery delay, a copy is sandboxed, while the file is delivered or Exchange 2 Quarantine Upon detection, Proofpoint automates or provides push-button capability quarantine malicious attachment after delivery 35 © 2016 Proofpoint, Inc.

Business Email Compromise Protection 37 © 2016 Proofpoint, Inc.
How Proofpoint helps address Impostor Email Authentication Support – Sender AND Recipient Granular Policy & Filtering Dynamic Classification & Analysis 38 © 2016 Proofpoint, Inc.
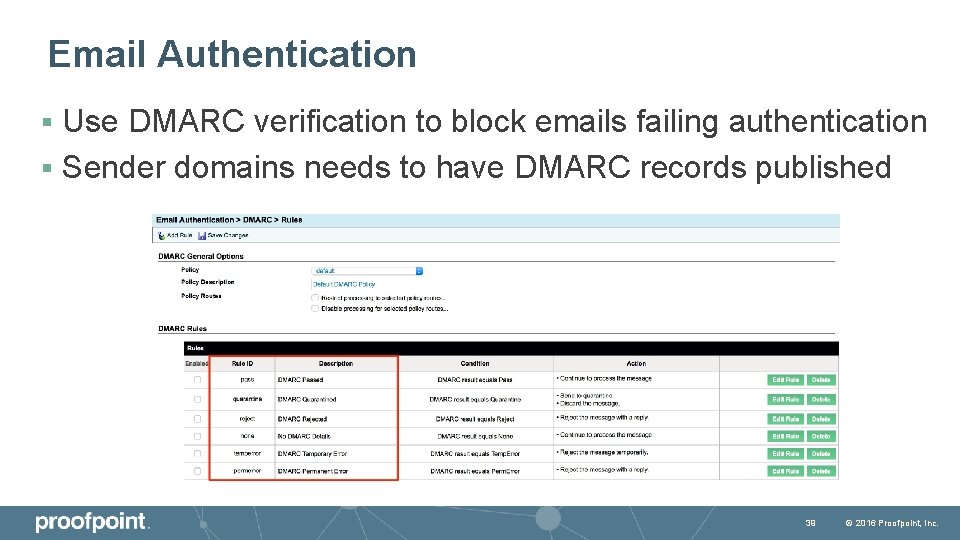
Email Authentication Use DMARC verification to block emails failing authentication § Sender domains needs to have DMARC records published § 39 © 2016 Proofpoint, Inc.
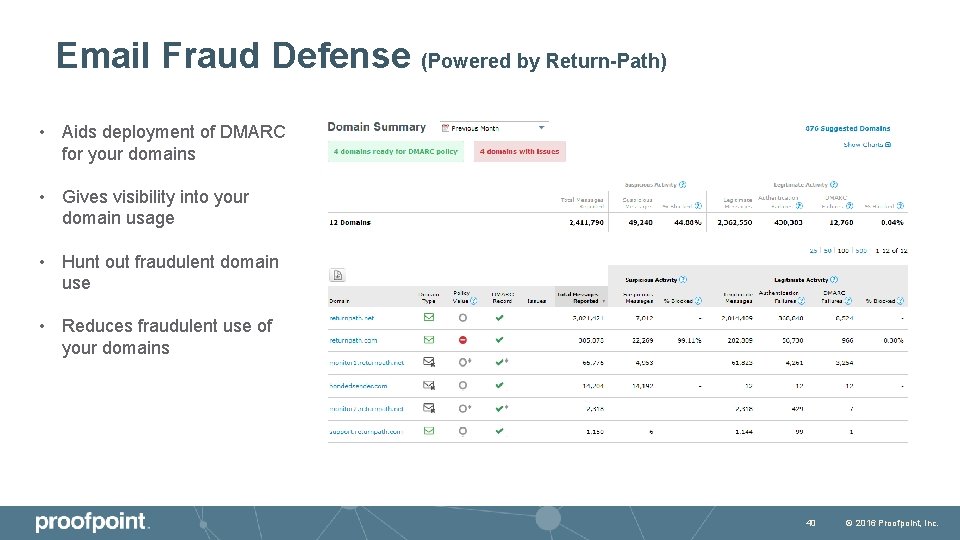
Email Fraud Defense (Powered by Return-Path) • Aids deployment of DMARC for your domains • Gives visibility into your domain usage • Hunt out fraudulent domain use • Reduces fraudulent use of your domains 40 © 2016 Proofpoint, Inc.
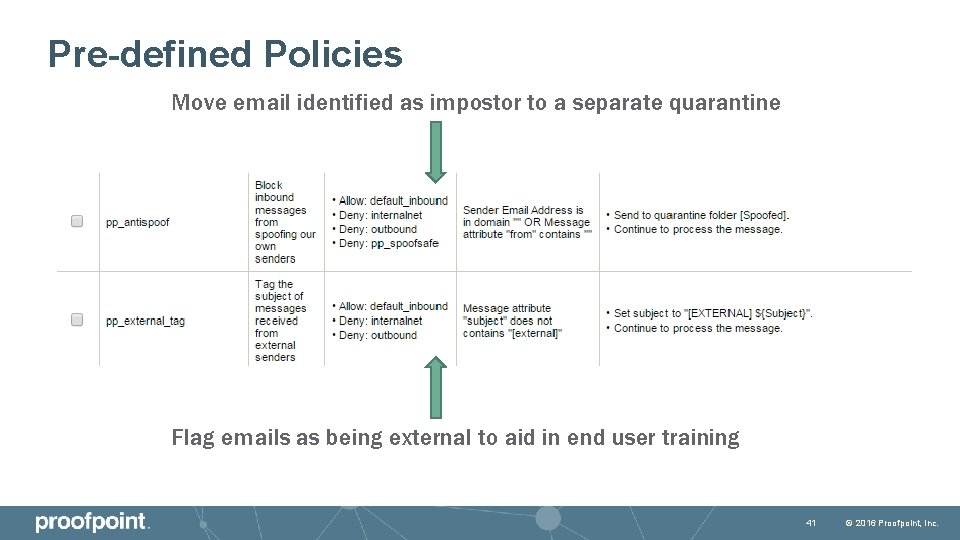
Pre-defined Policies Move email identified as impostor to a separate quarantine Flag emails as being external to aid in end user training 41 © 2016 Proofpoint, Inc.
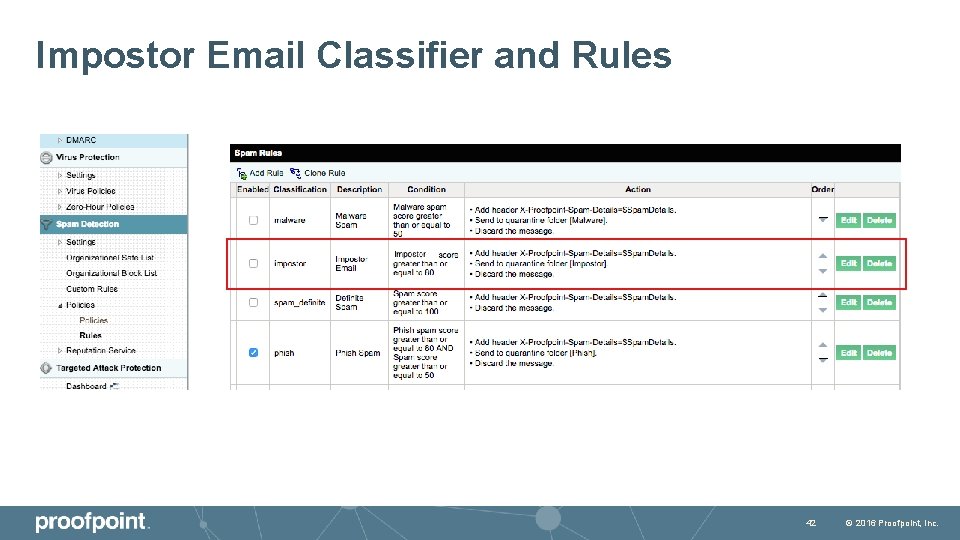
Impostor Email Classifier and Rules 42 © 2016 Proofpoint, Inc.
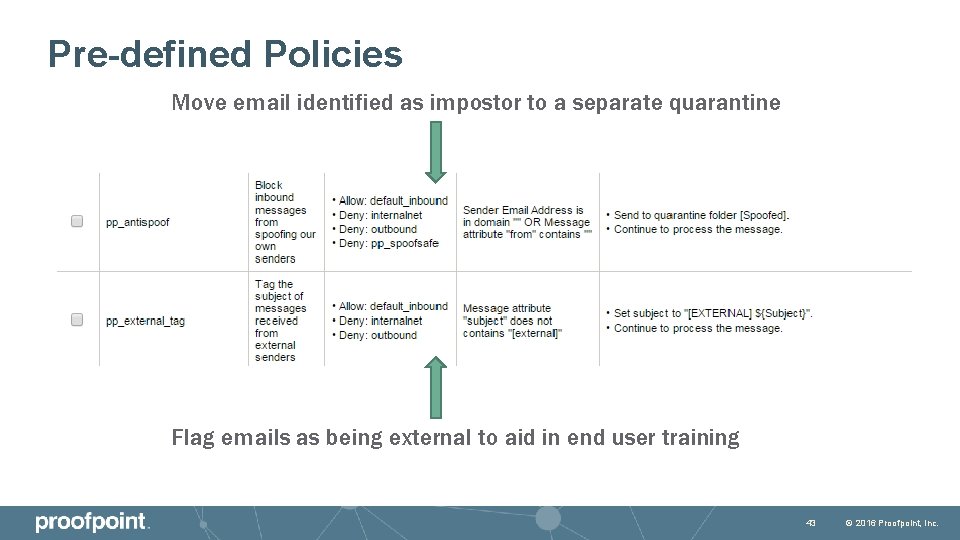
Pre-defined Policies Move email identified as impostor to a separate quarantine Flag emails as being external to aid in end user training 43 © 2016 Proofpoint, Inc.
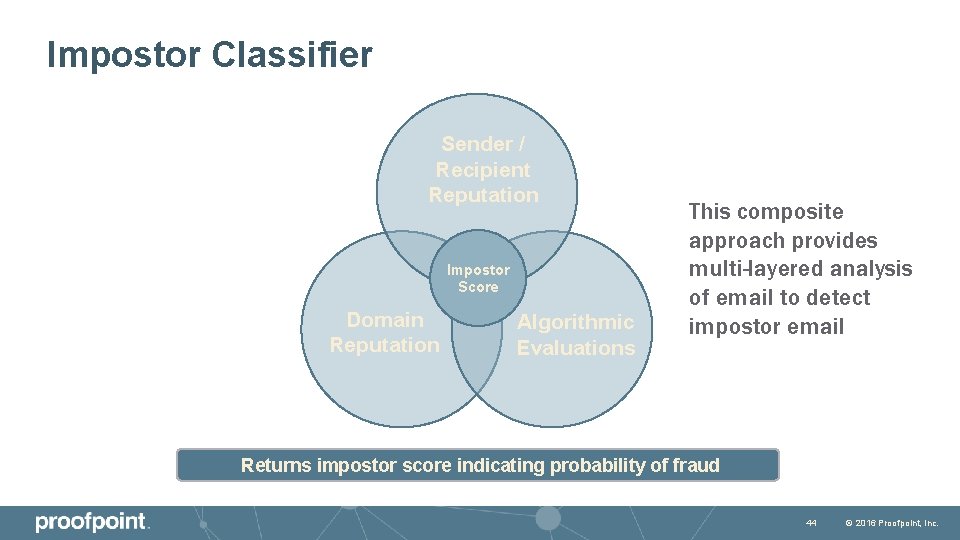
Impostor Classifier Sender / Recipient Reputation Impostor Score Domain Reputation Algorithmic Evaluations This composite approach provides multi-layered analysis of email to detect impostor email Returns impostor score indicating probability of fraud 44 © 2016 Proofpoint, Inc.
Summary Not all threats use malware Accurate detection to identify low volume email threats Augment policy with effective technology to remove burden on staff 45 © 2016 Proofpoint, Inc.

Product Portfolio 51 © 2016 Proofpoint, Inc.
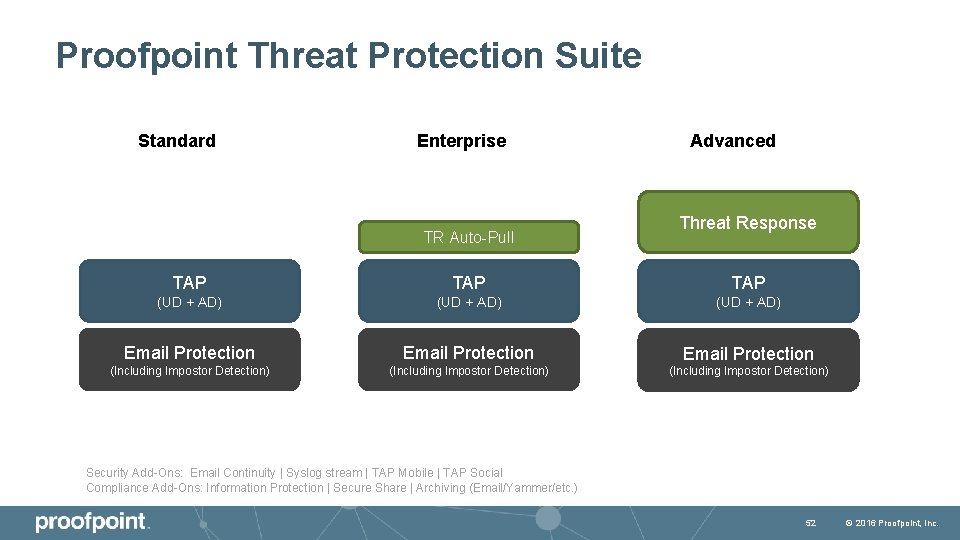
Proofpoint Threat Protection Suite Standard Enterprise TR Auto-Pull Advanced Threat Response TAP TAP (UD + AD) Email Protection (Including Impostor Detection) Security Add-Ons: Email Continuity | Syslog stream | TAP Mobile | TAP Social Compliance Add-Ons: Information Protection | Secure Share | Archiving (Email/Yammer/etc. ) 52 © 2016 Proofpoint, Inc.

Discovering Threats Pre-POC 53 © 2016 Proofpoint, Inc.
POC Challenges § I’m Sure I’m Already Protected! § I’m Generally Happy With my Solution! § Incumbent Solution Embedded in Network Infrastructure! § Lengthy Change Control / Need a Compelling Reason to Move! 54 © 2016 Proofpoint, Inc.
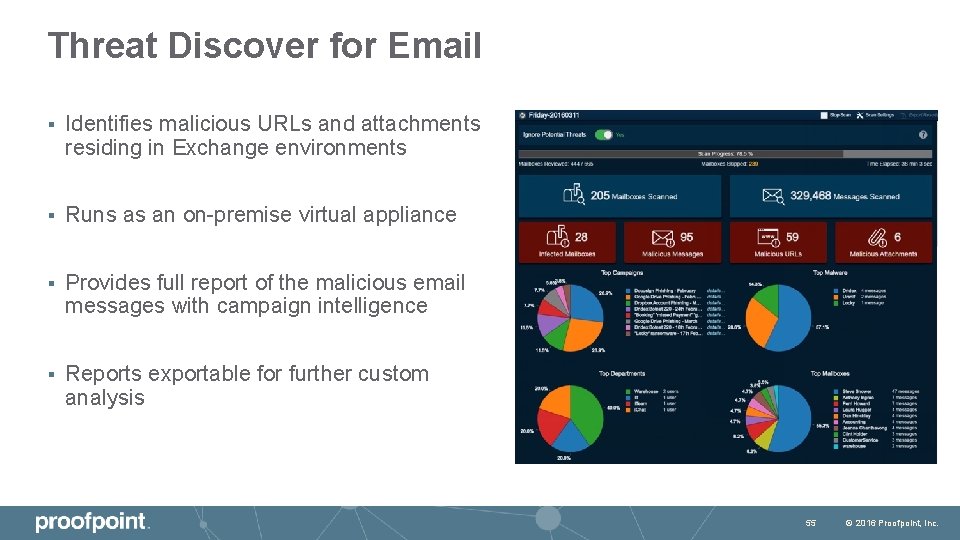
Threat Discover for Email § Identifies malicious URLs and attachments residing in Exchange environments § Runs as an on-premise virtual appliance § Provides full report of the malicious email messages with campaign intelligence § Reports exportable for further custom analysis 55 © 2016 Proofpoint, Inc.
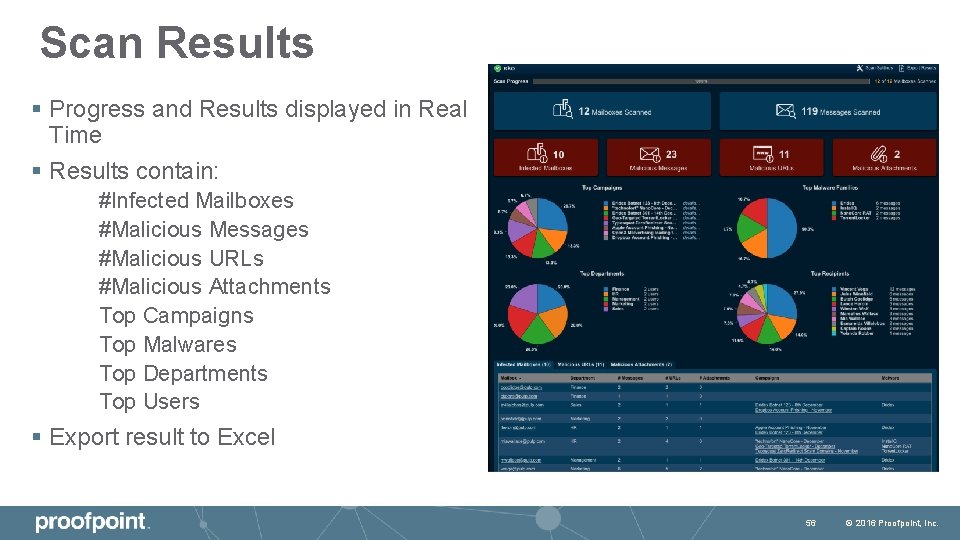
Scan Results § Progress and Results displayed in Real Time § Results contain: #Infected Mailboxes #Malicious Messages #Malicious URLs #Malicious Attachments Top Campaigns Top Malwares Top Departments Top Users § Export result to Excel 56 © 2016 Proofpoint, Inc.

57 © 2016 Proofpoint, Inc.
- Slides: 44