Protecting Critical Energy Infrastructure Information CEII FERC CEII


- Slides: 45
Protecting Critical Energy Infrastructure Information (CEII): FERC CEII Rules and Related Federal Regulations and Partnerships PRESENTATION FOR PLI BY SUSAN J. COURT PRINCIPAL, SJC ENERGY CONSULTANTS, LLC JUNE 16, 2015
Overview of Presentation • Legal Context • FERC’s CEII Rules and Procedures • DOE/IG Inspection Report (January 2015) • Other Federal Agencies and Federal-Private Partnerships
Legal Context Overview • FERC • The FOIA • Classification of Documents
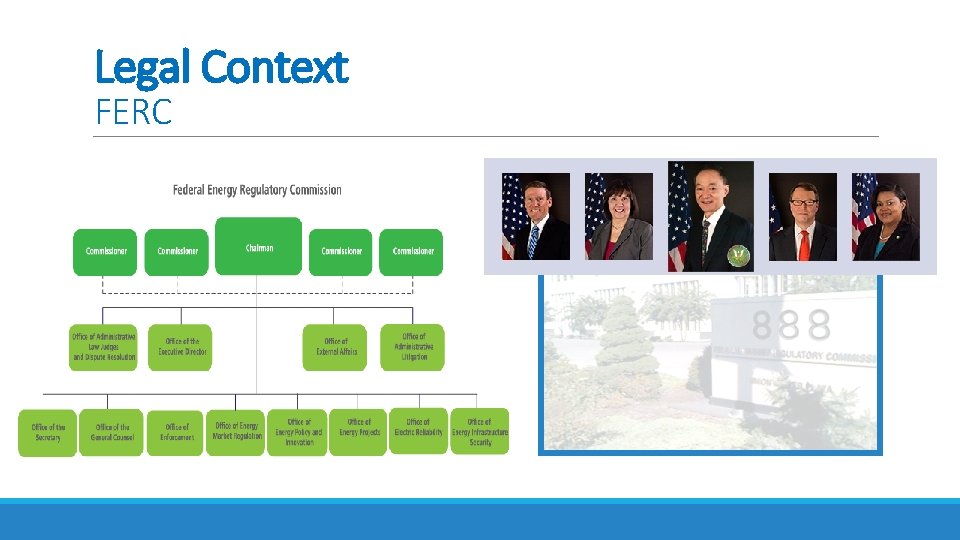
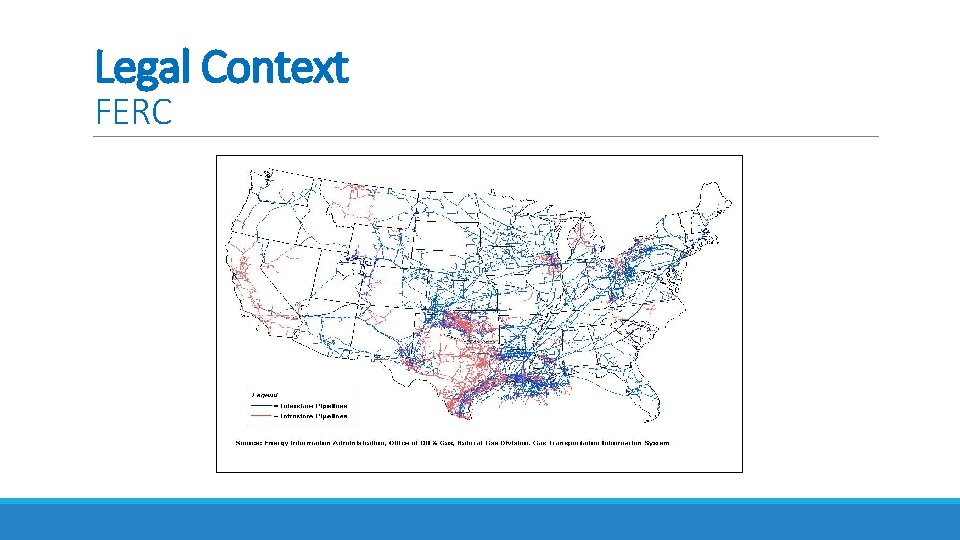
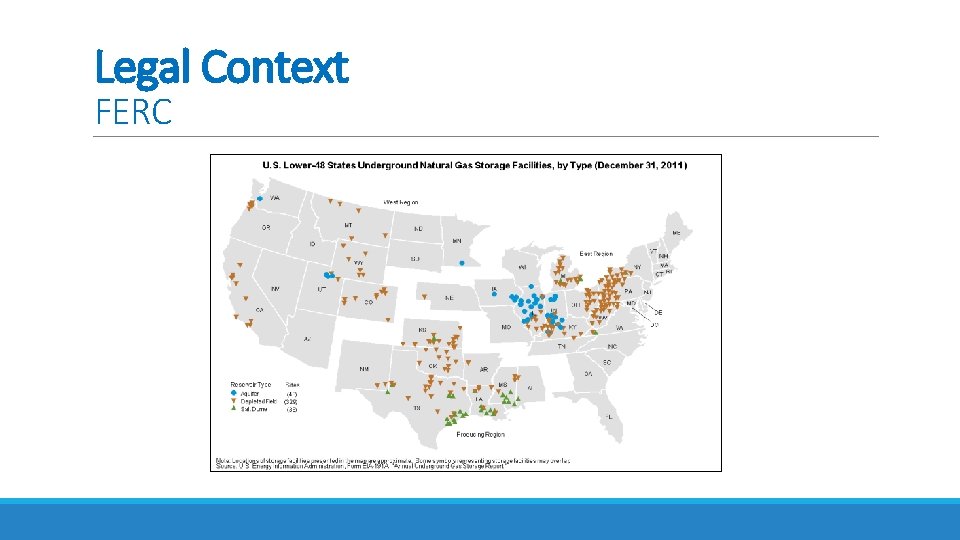
Legal Context FERC
Legal Context FERC Pictures courtesy of FERC
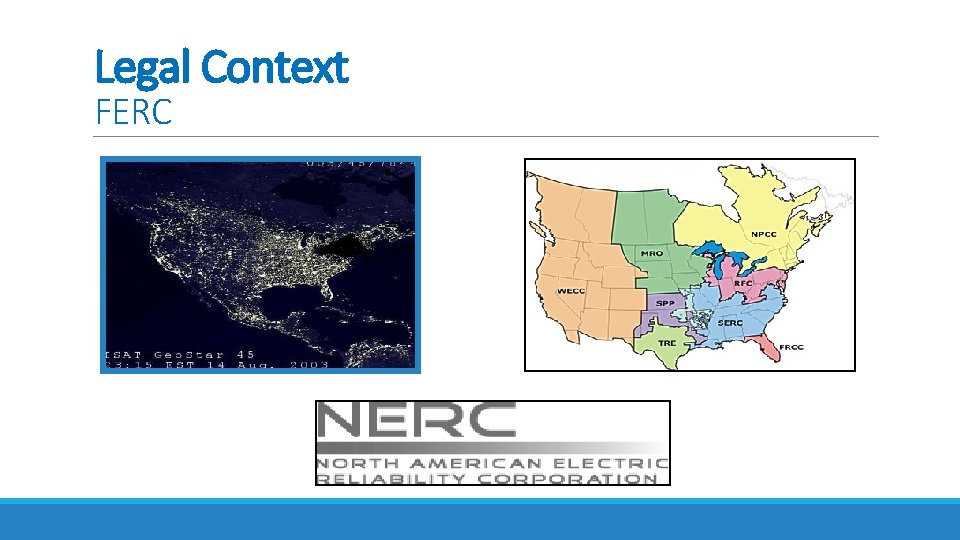
Legal Context FERC
Legal Context FERC
Legal Context FERC Pictures courtesy of FERC
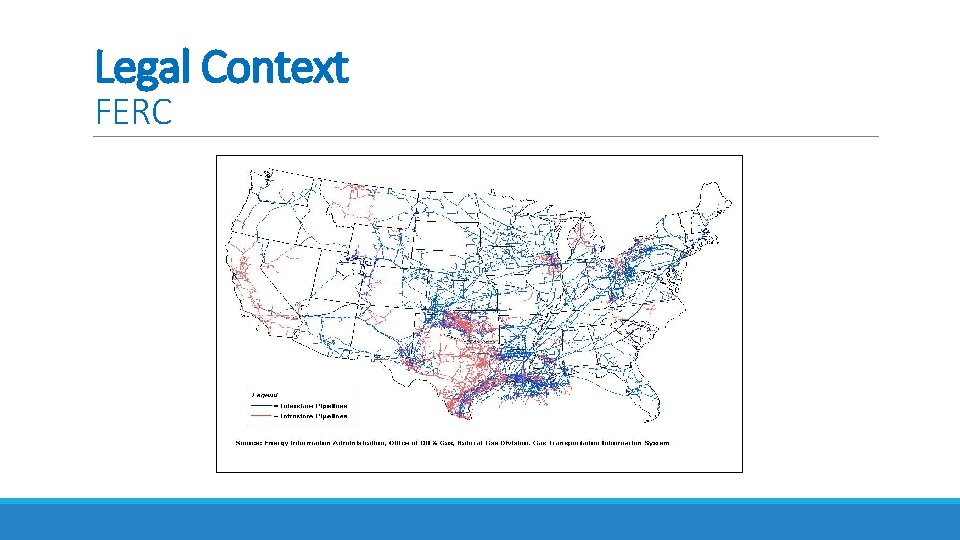
Legal Context FERC
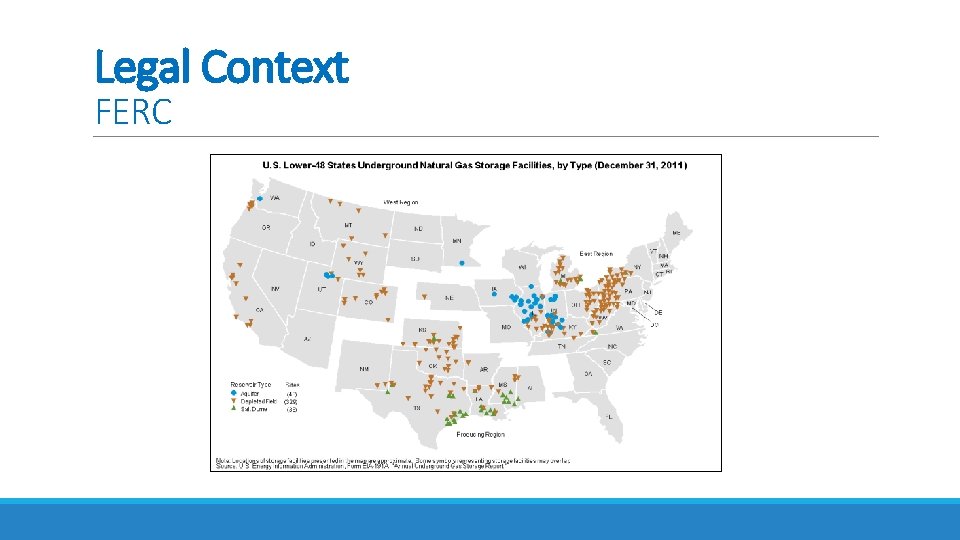
Legal Context FERC

Legal Context FERC Pictures courtesy of FERC
Legal Context The FOIA • 5 U. S. C. § 552 • 18 C. F. R. § 388. 112 (FERC)
Legal Context The FOIA FERC’s Administration of the FOIA • The Initial Request • Statutory Time Limits • Offices’ Responsibilities Regarding Searches • Review of Documents • Submitter’s Rights • The Response
Legal Context The FOIA Exemptions The FOIA allows an agency to withhold documents that are: classified documents; documents related solely to the internal personnel rules and practices of an agency; documents specifically exempted from disclosure by another statute; trade secrets and privileged commercial or financial information; inter-agency or intra-agency memos or letters that would be considered "privileged" for litigation purposes; personnel and medical files (the "personal privacy" exemption); records compiled for law enforcement purposes (but these are only exempt where they could reasonably be expected to interfere with enforcement proceedings, or would deprive a person of the right to a fair trial, or could reasonably be expected to endanger someone's life or physical safety, etc. ); • reports made for regulatory purposes by financial institutions to the government; and • Geological and geophysical information (including maps) related to oil and gas wells. • • See also 18 CFR § 388. 107 Commission Records Exempt from Public Disclosure (FERC’s codification of the FOIA’s nine exemptions).
Legal Context Classification of Documents Executive Orders • Executive Order 11652 (Classification and Declassification of National Security Information and Material) (Mar. 8, 1972), as amended. • Executive Order 13526 ( Classified National Security Information) (Dec. 9, 2009). Regulations: General Provisions: 32 C. F. R. Part 2001, Subpart B – Classification FERC Provisions: 18 C. F. R. Part 3 a – National Security Information Classifications: Top Secret – unauthorized disclosure could reasonably be expected to cause exceptionally grave damage to the national security Secret – unauthorized disclosure could reasonably be expected to cause serious damage to the national security. Confidential – unauthorized disclosure could reasonably be expected to cause damage to the national security.
Legal Context Classification of Documents (SCIF) Sensitive Compartmented Information Facility
FERC’S CEII Rules and Procedures Overview • FERC’s Initial Response to 9/11 • FERC’s CEII Rulemakings • Definition of CEII • Examples of CEII • Code of Federal Regulations • Process for Protecting CEII • Process for Accessing CEII
FERC’S CEII Rules and Procedures FERC’s Initial Response to 9/11 • Removal of documents from the Internet • Statement of Policy on Extraordinary Expenditures Necessary to Safeguard National Energy Supplies, 96 FERC ¶ 61, 299 (Sept. 14, 2001). • Statement of Policy on Previously Public Documents, 97 FERC ¶ 61, 030 (Oct. 18, 2001). • Notice of Inquiry and Guidance for Filings in the Interim, 98 FERC ¶ 61, 017 (Jan. 16, 2002).
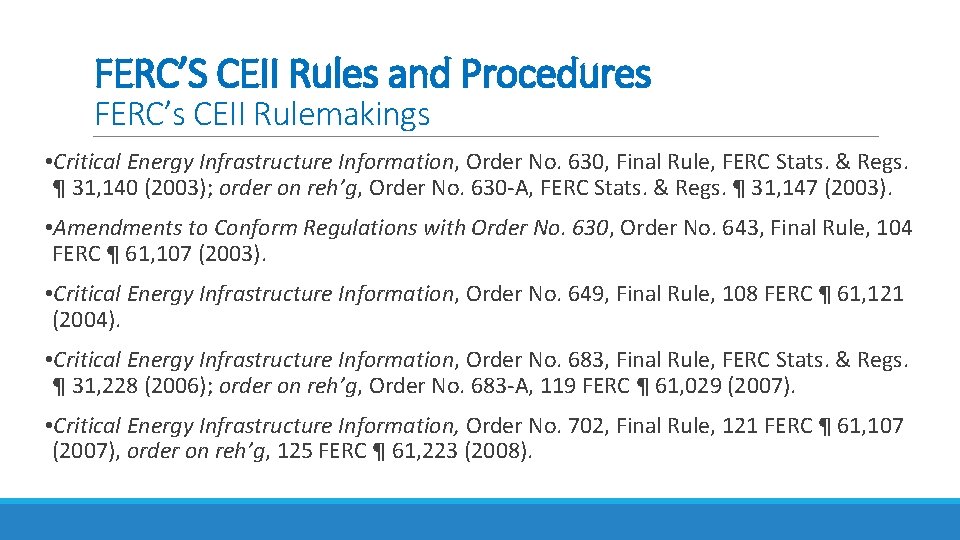
FERC’S CEII Rules and Procedures FERC’s CEII Rulemakings • Critical Energy Infrastructure Information, Order No. 630, Final Rule, FERC Stats. & Regs. ¶ 31, 140 (2003); order on reh’g, Order No. 630 -A, FERC Stats. & Regs. ¶ 31, 147 (2003). • Amendments to Conform Regulations with Order No. 630, Order No. 643, Final Rule, 104 FERC ¶ 61, 107 (2003). • Critical Energy Infrastructure Information, Order No. 649, Final Rule, 108 FERC ¶ 61, 121 (2004). • Critical Energy Infrastructure Information, Order No. 683, Final Rule, FERC Stats. & Regs. ¶ 31, 228 (2006); order on reh’g, Order No. 683 -A, 119 FERC ¶ 61, 029 (2007). • Critical Energy Infrastructure Information, Order No. 702, Final Rule, 121 FERC ¶ 61, 107 (2007), order on reh’g, 125 FERC ¶ 61, 223 (2008).
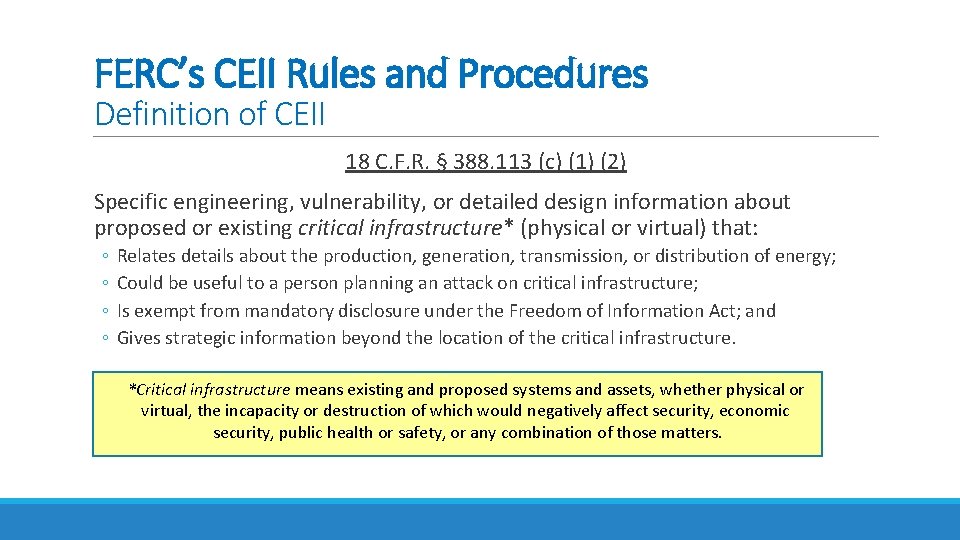
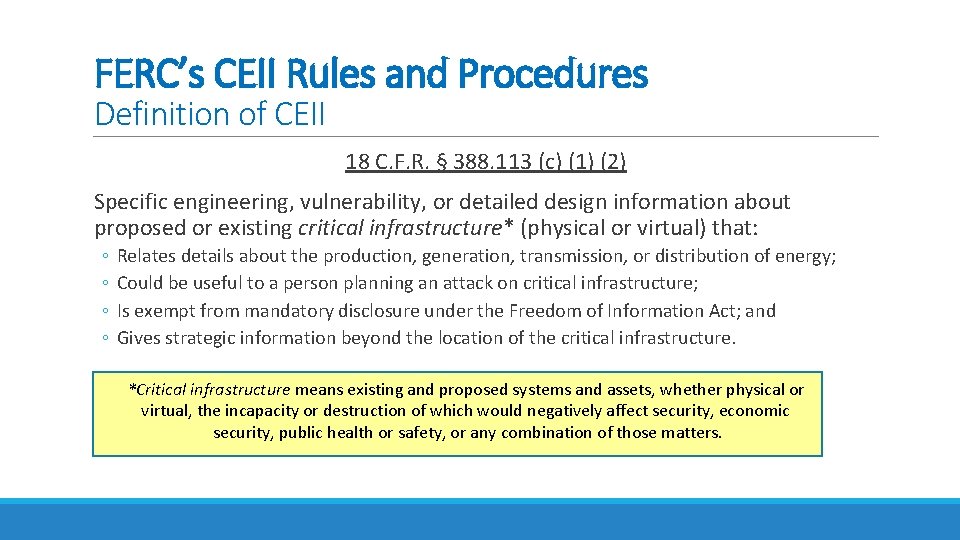
FERC’s CEII Rules and Procedures Definition of CEII 18 C. F. R. § 388. 113 (c) (1) (2) Specific engineering, vulnerability, or detailed design information about proposed or existing critical infrastructure* (physical or virtual) that: ◦ ◦ Relates details about the production, generation, transmission, or distribution of energy; Could be useful to a person planning an attack on critical infrastructure; Is exempt from mandatory disclosure under the Freedom of Information Act; and Gives strategic information beyond the location of the critical infrastructure. *Critical infrastructure means existing and proposed systems and assets, whether physical or virtual, the incapacity or destruction of which would negatively affect security, economic security, public health or safety, or any combination of those matters.
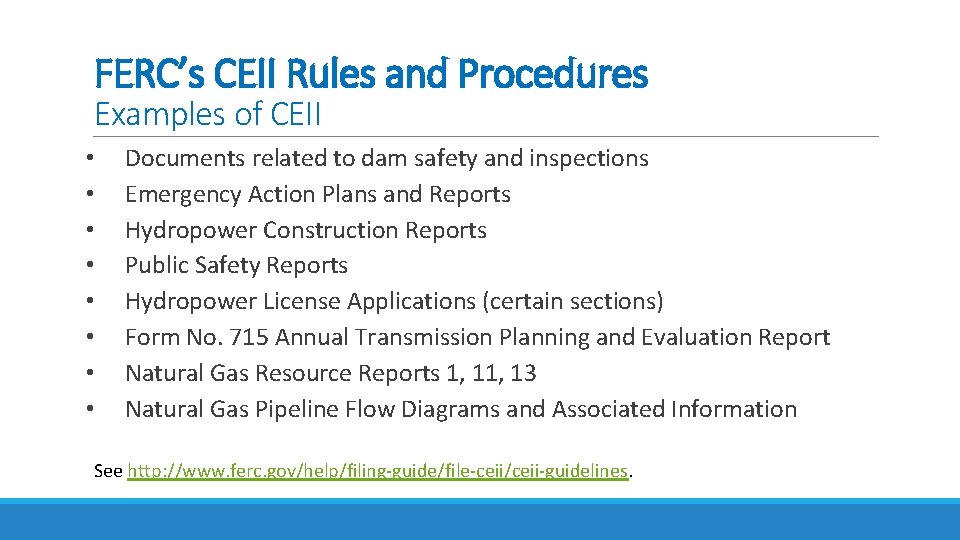
FERC’s CEII Rules and Procedures Examples of CEII • Documents related to dam safety and inspections • Emergency Action Plans and Reports • Hydropower Construction Reports • Public Safety Reports • Hydropower License Applications (certain sections) • Form No. 715 Annual Transmission Planning and Evaluation Report • Natural Gas Resource Reports 1, 13 • Natural Gas Pipeline Flow Diagrams and Associated Information See http: //www. ferc. gov/help/filing-guide/file-ceii/ceii-guidelines.
FERC’s CEII Rules and Procedures Code of Federal Regulations • 18 CFR § 388. 112: Request for CEII Treatment of Documents Submitted to the Commission • 18 CFR § 388. 113: Accessing CEII
FERC’s CEII Rules and Procedures Process for Protecting CEII Request for CEII Treatment of Documents Submitted to the Commission 18 CFR § 388. 112 (2)(b) Initial Steps • A person requesting that a document filed with the Commission be treated as CEII (the requesting filer) must designate the document as CEII in making an electronic filing or clearly indicate a request for such treatment on a paper filing. • The requesting filer must clearly label the cover page and pages or portions of the document containing material for which CEII treatment is claimed in bold, capital lettering, indicating that it contains Critical Energy Infrastructure Information, and marked “DO NOT RELEASE. ” • The requesting filer also must submit to the Commission a public version with the information that is claimed to be CEII redacted, to the extent practicable. • The requesting filer must also include in its filing a justification for CEII treatment. See also http: //ferc. gov/help/submission-guide/user-guide. pdf
FERC’s CEII Rules and Procedures Process for Protecting CEII Request for CEII Treatment of Documents Submitted to the Commission 18 CFR § 388. 112 (c) Effect Of CEII Claim • The documents for which CEII treatment is claimed are maintained in the Commission's document repositories as non-public until such time as the Commission determines that the document is not entitled to the treatment sought and is subject to disclosure. • The request for CEII treatment and the public version of the document are made available while the request is pending.
FERC’s CEII Rules and Procedures Process for Protecting CEII Request for CEII Treatment of Documents Submitted to the Commission 18 CFR § 388. 112 (d) and (e) Notifications • Notification of request and opportunity to comment. When someone seeks a document for which CEII status has been claimed (CEII requester), or when the Commission itself is considering release of such information, FERC staff notifies the person who submitted the document and gives the person an opportunity (at least five calendar days) in which to comment in writing on the request. A copy of this notice is sent to the CEII requester. • Notification before release. Notice of a decision by the Commission or a Commission official to release information for which CEII status has been sought is given to any person claiming that the information is CEII no less than 5 calendar days before disclosure. The notice must briefly explain why the person's objections to disclosure are not sufficient.
FERC’s CEII Rules and Procedures Process for Accessing CEII Accessing Critical Energy Infrastructure Information 18 CFR 388. 113 (d)(1)-(3) Demonstrated Need for the Information • Entities which by definition have a demonstrated need ◦ Company Access to its Own Information ◦ Federal government employee ◦ Certain landowners • Entities which must make an affirmative demonstration and follow certain procedures
FERC CEII’s Rules and Procedures Process for Accessing CEII Accessing Critical Energy Infrastructure Information 18 CFR 388. 113 (d)(4)(i)-(vi) Procedures • Individual Requests • Submit a signed, written request with FERC CEII Coordinator. • File an executed non-disclosure agreement (NDA). • Organizational Requests • Submit a signed, written request with FERC CEII Coordinator. • Be authorized to represent that all the employees who intend to access information agree to be bound by an NDA. • Term of Access and Validity of NDA • Denial of Access
FERC CEII’s Rules and Procedures Process for Protecting and Accessing CEII In Order No. 649, the Commission committed to provide CEII contact people with whom filers could consult prior to making filings that might contain CEII. http: //ferc. gov/legal/ceii-foia/ceii/contacts. asp
DOE/IG Inspection Report (January 2015) Overview • Background • Findings and Conclusion • FERC’s Response to Management Alert (Oct. 2014) • Recommendations • FERC’s Chairman’s Response • Classification Issues
Inspection Report Review of Controls for Protecting Nonpublic Information at the Federal Energy Regulatory Commission U. S. Department of Energy Office of Inspector General Office of Audits and Inspections DOE/IG-0933 Report January 2015

DOE/IG Inspection Report (January 2015) Background
DOE/IG Inspection Report (January 2015) Findings and Conclusions Findings • February 2013: Chairman Wellinghoff directed staff to identify critical electric substations and create substation failure scenarios. • March 2013: Despite sensitivity of the analysis and simulations, he and other FERC officials began sharing some or all of the information with industry and Federal officials, even though no effort was made to determine whether the admittedly sensitive information was classified. • FERC Staff designated the study and related briefing materials as CEII, and required recipients to sign nondisclosure agreements (NDAs). • Staff nevertheless failed to obtain NDAs uniformly and to keep track of them, and generally demonstrated inadequate understanding of the CEII rules and the process of classification. Conclusion FERC’s controls, processes, and procedures for protecting nonpublic information are severely lacking.
DOE/IG Inspection Report (January 2015) FERC’s Response to Management Alert (Oct. 2014) • Identified the holders of the relevant sensitive nonpublic information and segregated and secured the information. • Sought assistance to determine classification of information. • Took steps to revise its security classification and ethics-training to ensure that Commission employees are aware of their responsibility to protect sensitive nonpublic information.
DOE/IG Inspection Report (January 2015) Recommendations • Ensure Commission employees are aware of and properly trained on their responsibilities related to CEII. • Ensure Commission employees possess the necessary security clearances and receive adequate initial and refresher training concerning the identification and protection of classified information. • Ensure that established CEII processes to protect and control nonpublic information are current and that such policies are disseminated and properly implemented. • Work with appropriate officials to address the apparent confusion between the Commission and the Department regarding respective roles, responsibilities and authorities to classify Commission-created information. • Determine whether to seek specific authority to protect or classify as necessary Commission developed documents and develop necessary guides and training associated with any authorities obtained.
DOE/IG Inspection Report (January 2015) FERC’s Chairman’s Response • Directed the 2014 annual mandatory ethics training for FERC staff to emphasize the CEII process, as will future training. • Initiated a review of employee security clearances and refresher training. • Modified its mandatory Annual Classified Security Training to emphasize the protection and control of classified matters. • Directed staff to include enhanced guidance on appropriate procedures surrounding the creation of classified matters in 2015 training, to be concluded by August 2015. • Plan to re-engage DOE personnel to training affected FERC employees. • Directed staff to review the CEII regulations, and report back by May 1, 2015, on whether and how those regulations should be revised to ensure that they are appropriate to protect relevant nonpublic information. • Directed staff to coordinate with DOE regarding their respective roles in the classification process, and further directed staff to draft guidance by July 1, 2015, for review by Department officials. • Directed staff to explore whether FERC needs additional statutory authority to protect FERC-developed documents.
This just in…. • June 4, 2015: DOE IG issued another management alert to FERC —Review of Allegations of Improper Disclosure of Confidential, Nonpublic FERC Information. • Background: • On March 9, 2015, former Chairman Jon Wellinghoff used a nonpublic video from a FERC Office of Enforcement (OE) deposition at a public conference. • Subsequently, an OE employee and the attorney for the deposed trader expressed concern to the Commission about unauthorized use of nonpublic information. • March 24, 2015, FERC referred the matter to the DOE/IG. • Recommendations • Determine if former Chairman violated the Confidentiality of Investigations requirement and determine what, if any, sanctions are available to address the former chairman’s actions. • Determine if the Commission currently has the necessary authorities it needs to prevent the disclosure or misuse of sensitive or nonpublic information. • Expedite the current effort to update and strengthen the Commission’s postemployment guidance and exit processes. • Management Response: agreement to take corrective actions in response to the report’s recommendations.
DOE/IG Inspection Report (January 2015) Classification Issues • July 2014: FERC officials sought classification reviews of the study from both DOE and the Department of Homeland Security (DHS). • DHS acknowledged that it did not have the authority to classify FERC-generated information, and opined that it considered Study to contain sensitive but not necessarily classified information. • DOE eventually agreed with DHS that the Study did not contain classified information, although it appeared to disagree with FERC’s General Counsel that FERC did not have the original authority to classify the document in the first place. • Both DHS and DOE seemed influenced by fact that the study was based on an absolutely worst case scenario, i. e. , the Study was bunk.
Other Federal Agencies and Federal-Private Partnerships – Overview • U. S. Departments of Homeland Security and Agriculture • National Infrastructure Protection Plan (NIPP) • North American Electric Reliability Corporation (NERC)
Other Federal Agencies and Federal-Private Partnerships – DHS and USDA (Forest Service) Critical Infrastructure Information (as defined by U. S. Department of Homeland Security Regulations at 6 C. F. R. § 29. 2 (2014)). Sensitive Security Information (as defined by the U. S. Department of Agriculture (U. S. Forest Service) in USDA Departmental Regulation No. 3440 -2 (Control and Protection of “Sensitive Security Information”) (Jan. 30, 2003)).
Other Federal Agencies and Federal-Private Partnerships – NIPP National Infrastructure Protection Plan Key Concepts • Provides an updated approach to critical infrastructure security and resilience • Greater focus on integration of cyber and physical security efforts • Closer alignment to national preparedness efforts • Increased focus on cross sector and cross jurisdictional coordination to achieve results • Integration of information-sharing as an essential component of the risk management framework • Recognizes the key role and knowledge of critical infrastructure owners and operators • Integrates efforts by all levels of government, private, and nonprofit sectors by providing an inclusive partnership framework and recognizing unique expertise and capabilities each participant brings to the national effort • Reflects today’s integrated all-hazards environment • Grounded in business principles and existing policy • Drives action toward long-term improvement
Other Federal Agencies and Federal Private Partnerships – NIPP - Energy Sector-Specific Plan General http: //www. dhs. gov/xlibrary/assets/nipp-ssp-energy-2010. pdf
Other Federal Agencies and Federal Private Partnerships – NIPP - Energy Sector-Specific Plan Electricity Sector Information Sharing and Analysis Center (ES-ISAC) • Operator • Purpose • Membership • Information Sharing • Activities
Other Federal Agencies and Federal. Private Partnerships – NERC North American Electric Reliability Corporation • NERC’s Modified Use of FERC’s Definition of CEII http: //www. nerc. com/Filings. Orders/us/Rule. Of. Procedure. DL/NERC_ROP_E ffective_20150319. pdf (page 91). • NERC’s Security Guidelines for the Electricity Sector: Protecting Potentially Sensitive Information http: //www. nerc. com/docs/cip/sgwg/Protecting%20 Sensitive%20 Informa tion%20 Guideline%20 Draft%20 Revision%20 clean%20 -%2020120309 V 2%205. pdf
Thank You. Questions? Susan J. Court SJC Energy Consultants, LLC susan. court@courtenergy. com http: //www. courtenergy. com