Proposal of MISTY 1 as a Block Cipher

Proposal of MISTY 1 as a Block Cipher of Cipher Suites in TLS Hirosato Tsuji Toshio Tokita Mitsubishi Electric Corporation 2000/08/01 48 th IETF, Pittsburgh, PA, USA
Presentation Agenda ¨Block Cipher “MISTY 1” --- by Toshio Tokita ¨ Current Status and Next Steps of MISTY 1 to support TLS --- by Hirosato Tsuji 2000/08/01 48 th IETF, Pittsburgh, PA, USA 2
Block Cipher MISTY 1 Toshio Tokita Mitsubishi Electric Corporation MISTY@isl. melco. jp 2000/08/01 48 th IETF, Pittsburgh, PA, USA
Overview ¨ Secret-key block cipher 64 -bit block, 128 -bit key, a variable number of rounds (8 -round recommended) proposed by M. Matsui (Mitsubishi) in 1996 at Fast Software Encryption Workshop “FSE 4” ¨ Widely used in many applications: Governmental applications: Public transportation systems, Secure network systems, etc Commercial products: S/MIME E-mail software, VPN(Routers/Hubs), Encryption LSI, PKI Software & services, etc 2000/08/01 48 th IETF, Pittsburgh, PA, USA 4
Recent News ¨ “KASUMI” has been adopted as a mandatory algorithm for data confidentiality and data integrity in W-CDMA by 3 GPP. (March, 2000) ¨ KASUMI will be also used in current GSM systems as an alternative for A 5. ¨ KASUMI is a variant of MISTY 1 designed for W-CDMA systems. “KASUMI”=“MIST” 3 GPP: 3 rd Generation Partnership Project 2000/08/01 48 th IETF, Pittsburgh, PA, USA 5
Pointers ¨ ISO 9979 No. 13 (algorithm registration) ¨ URL for Internet-Draft : http: //www. ietf. org/internet-drafts/draft-ohtamisty 1 desc-02. txt ¨ Specifications http: //www. mitsubishi. com/ghp_japan/misty_e_b. pdf ¨ Royalty Free License http: //www. mitsubishi. com/ghp_japan/misty/licensee. htm MISTY 1 essential patent is licensed under royalty free conditions. 2000/08/01 48 th IETF, Pittsburgh, PA, USA 6
Design Criteria ¨High security: – Provable security against differential and linear cryptanalysis ¨Multi platform: – High speed in both software and hardware implementations ¨Compact: – Low gate count and low power consumption in hardware 2000/08/01 48 th IETF, Pittsburgh, PA, USA 7
High security ¨ MISTY 1 is designed to be highly secure as a 64 -bit block cipher; particularly to be provably secure against differential and linear cryptanalysis. Powerful Cryptographic Attacks u Differential Cryptanalysis (Biham, Shamir 1990) – First DES attack faster than an exhaustive key search u Linear Cryptanalysis (Matsui 1993) – First successful computer experiment for breaking DES 2000/08/01 48 th IETF, Pittsburgh, PA, USA 8
Multi Platform ¨ MISTY 1 is designed to be sufficiently fast in both software and hardware implementations. Ex 1) Pentium III (800 MHz) Encryption speed (Assembly Language Program) 230 Mbps Ex 2) ASIC H/W (Mitsubishi 0. 35 micron CMOS Design Library) Encryption speed Gate size 2000/08/01 800 Mbps 50 Kgates 48 th IETF, Pittsburgh, PA, USA 9
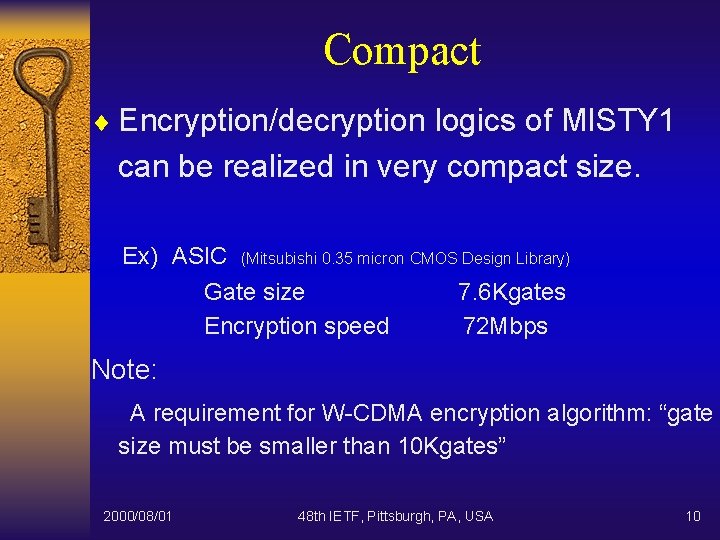
Compact ¨ Encryption/decryption logics of MISTY 1 can be realized in very compact size. Ex) ASIC (Mitsubishi 0. 35 micron CMOS Design Library) Gate size 7. 6 Kgates Encryption speed 72 Mbps Note: A requirement for W-CDMA encryption algorithm: “gate size must be smaller than 10 Kgates” 2000/08/01 48 th IETF, Pittsburgh, PA, USA 10
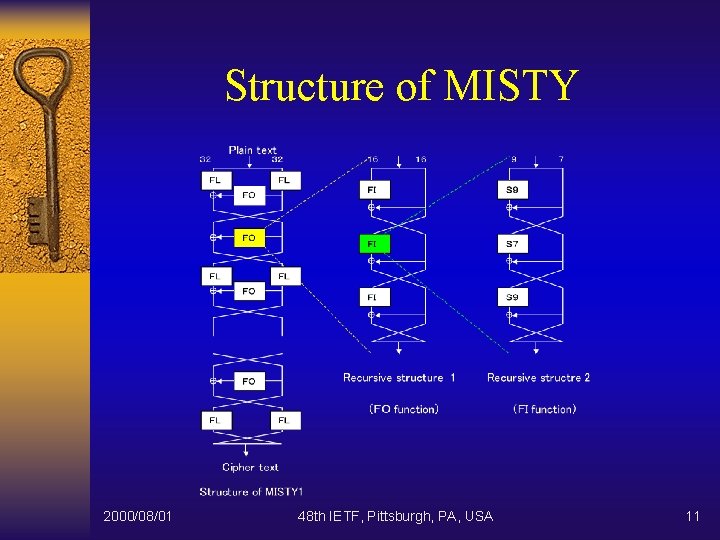
Structure of MISTY 2000/08/01 48 th IETF, Pittsburgh, PA, USA 11
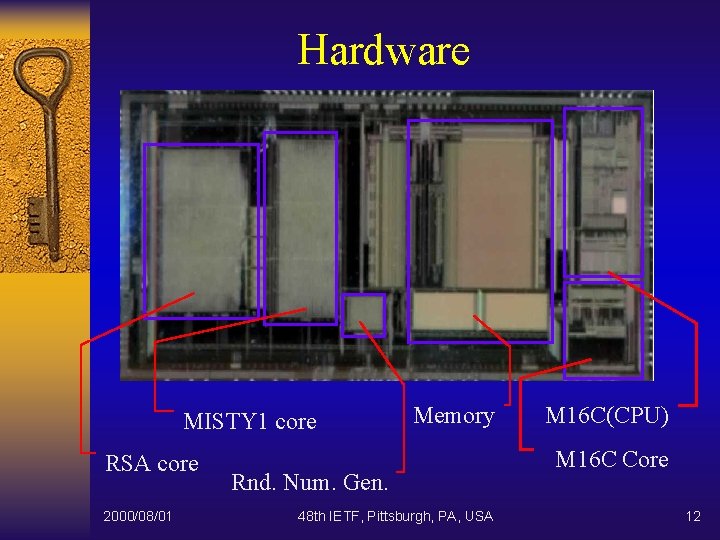
Hardware MISTY 1 core RSA core 2000/08/01 Memory Rnd. Num. Gen. 48 th IETF, Pittsburgh, PA, USA M 16 C(CPU) M 16 C Core 12

Current Status and Next Steps of MISTY 1 to support TLS Hirosato Tsuji Mitsubishi Electric Corporation <hirosato@iss. isl. melco. jp> 2000/08/01 48 th IETF, Pittsburgh, PA, USA
Summary ¨ What is MISTY 1? – High security, Multi platform, Compact, Block cipher ¨ In – – this presentation Actual Application of MISTY 1 Proposal of MISTY 1 Current Status to support TLS Next Steps to support TLS 2000/08/01 48 th IETF, Pittsburgh, PA, USA 14
Actual Application of MISTY 1 (1) Secure E-mail Systems ¨ S/MIME-based e-mail application ¨ Extended S/MIME V 2 specification ¨ Implemented by Mitsubishi and other Japanese venders ¨ Interoperability had been confirmed between these venders 2000/08/01 48 th IETF, Pittsburgh, PA, USA 15
Actual Application of MISTY 1 (2) Secure Web Access Systems ¨ Secure Web Access Systems – provide authentication, access control, integrity and confidentiality ¨ Implemented on the HTTP and TCP ( sorry, not on TLS ) ¨ Contents is encrypted by MISTY 1 2000/08/01 48 th IETF, Pittsburgh, PA, USA 16
Actual Application of MISTY 1 (3) Other Apps based on MISTY Toolkit ¨ MISTY Cryptographic / PKI Toolkit – Content Encryption Algorithm in PKCS #7 – Encryption Scheme ( Symmetric Cipher ) for PKCS #5 Password-based Encryption ¨ Other Apps implemented on Toolkit – Secure Contents Distribution Systems – Governmental Services 2000/08/01 48 th IETF, Pittsburgh, PA, USA 17
Proposal of MISTY 1 ¨ As ONE of block ciphers of Cipher Suites for TLS 1. 0 ¨ Reason to use MISTY 1 – Suitable Block Cipher – Royalty Free License – Applied to Actual Internet Applications 2000/08/01 48 th IETF, Pittsburgh, PA, USA 18
Current Status to support TLS ¨ Submit Internet Draft of Description of MISTY 1 – posted. ¨ Make a presentation of MISTY 1 at 48 th IETF, Pittsburgh, PA – now. 2000/08/01 48 th IETF, Pittsburgh, PA, USA 19
Next Steps to support TLS ¨ Proceed Internet Draft of Description of MISTY 1 to Informational RFC ¨ Submit Internet Draft of MISTY 1 -based Cipher Suites for TLS 1. 0 ¨ Request TLS WG to assign the Register Number of these Cipher Suites 2000/08/01 48 th IETF, Pittsburgh, PA, USA 20
Next Steps to support TLS (continued) ¨ Implementing TLS 1. 0 with MISTY 1 – processing now with Open. SSL 2000/08/01 48 th IETF, Pittsburgh, PA, USA 21
- Slides: 21