Program Execution Time Reliability and Queueing Analysis in
Program Execution Time, Reliability, and Queueing Analysis in Mobile Environments Chen Xinyu 2003 -12 -08 Term Presentation
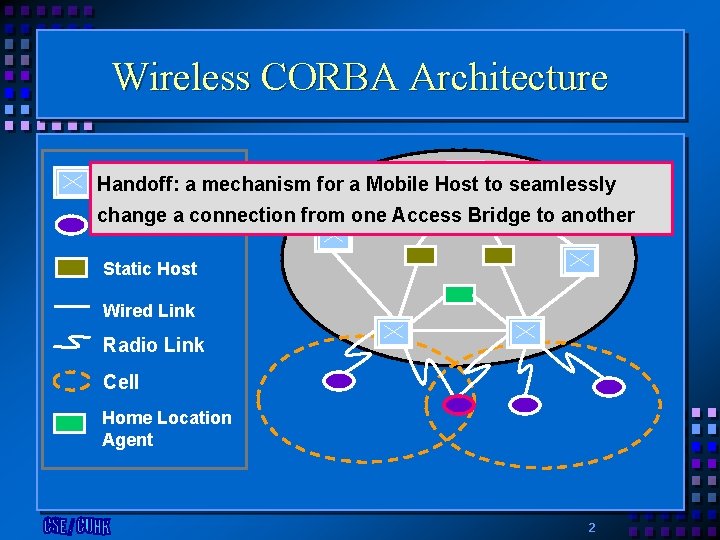
Wireless CORBA Architecture Access Bridge Handoff: a mechanism for a Mobile Host to seamlessly change a connection from one Access Bridge to another Wired Network Mobile Host Static Host Wired Link Radio Link Cell Home Location Agent 2
Outline • Analysis of Program Execution Time Based • • • on Various Checkpointing Strategies Expected-Reliability Analysis of Message Sojourn Time in Access Bridge Conclusions and Future Work 3
Program Execution Time • Motivation • Previous work • program execution time with and without checkpointing in the presence of failures on Static Hosts with given time requirement without failures • Mobile Environments • Underlying message-passing mechanism • • • Interactions with other hosts Network communications Discrete message exchange • Handoff 4
The Program’s Termination Condition • A program on a Mobile Host is successfully terminated if it continuously receives n computational messages 5
Objective • To derive the cumulative distribution function of the program execution time on a Mobile Host and its expectation with message number n in the advent of failures, handoffs, and checkpointings • Deterministic checkpointing strategy • Random checkpointing strategy 6
Deterministic Checkpointing Strategy • Deterministic: • Take a checkpoint when receiving a messages, a is a constant • The program execution is broken into intervals • The ith, i=1, 2, …, m-1, interval contains a messages and a checkpoint • The message number in the mth interval is given by 7
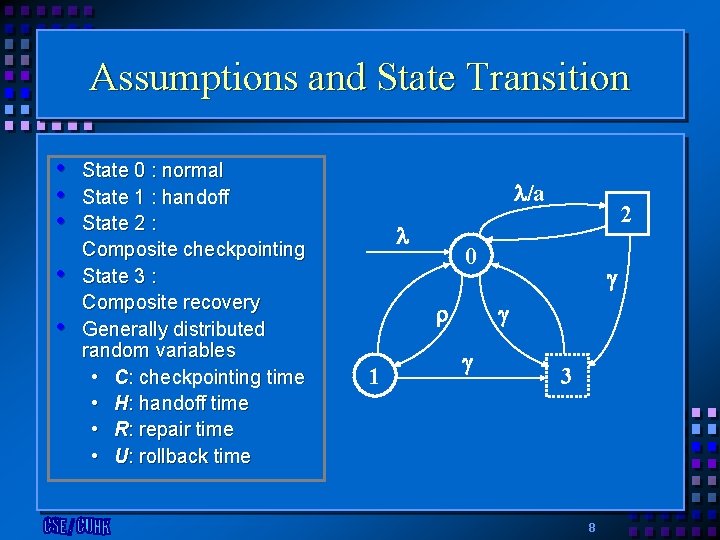
Assumptions and State Transition • • • State 0 : normal State 1 : handoff State 2 : Composite checkpointing State 3 : Composite recovery Generally distributed random variables • C: checkpointing time • H: handoff time • R: repair time • U: rollback time /a 0 1 2 3 8
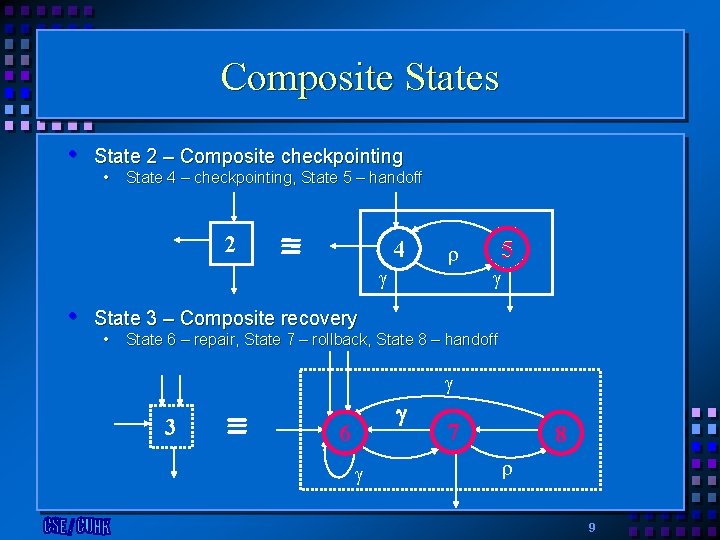
Composite States • State 2 – Composite checkpointing • State 4 – checkpointing, State 5 – handoff 2 4 • 5 State 3 – Composite recovery • State 6 – repair, State 7 – rollback, State 8 – handoff 3 6 7 8 9
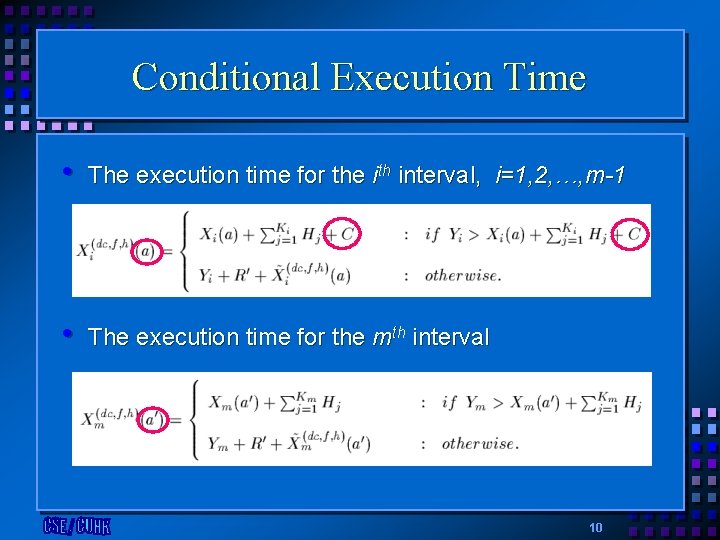
Conditional Execution Time • The execution time for the ith interval, i=1, 2, …, m-1 • The execution time for the mth interval 10
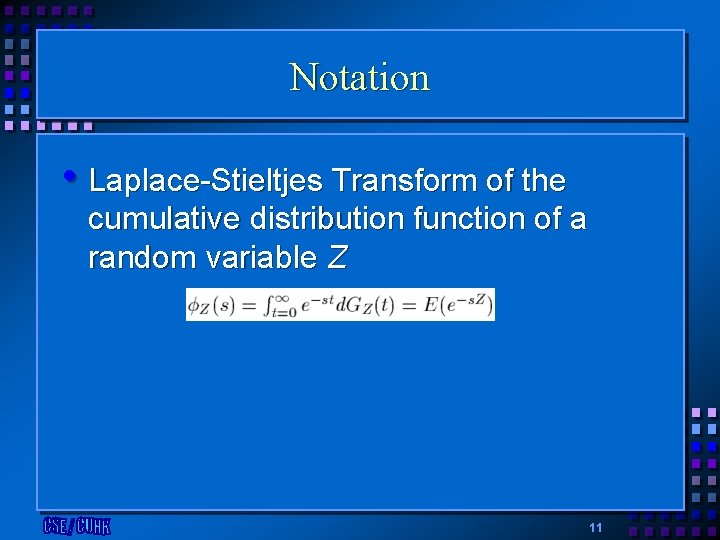
Notation • Laplace-Stieltjes Transform of the cumulative distribution function of a random variable Z 11
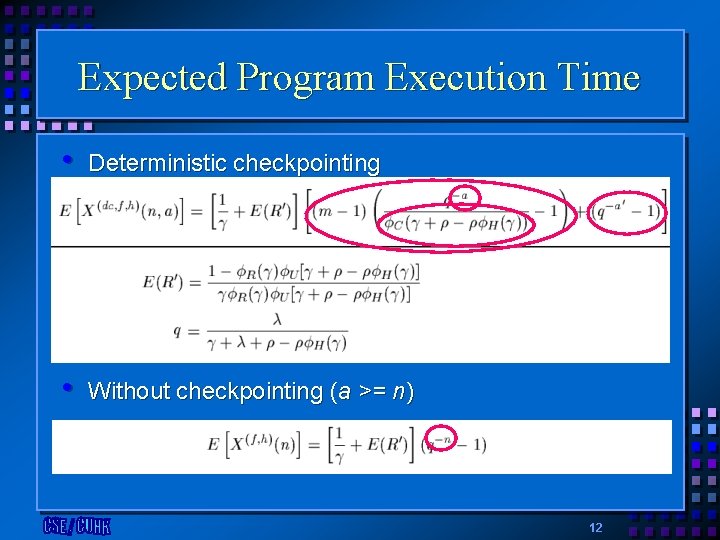
Expected Program Execution Time • Deterministic checkpointing • Without checkpointing (a >= n) 12
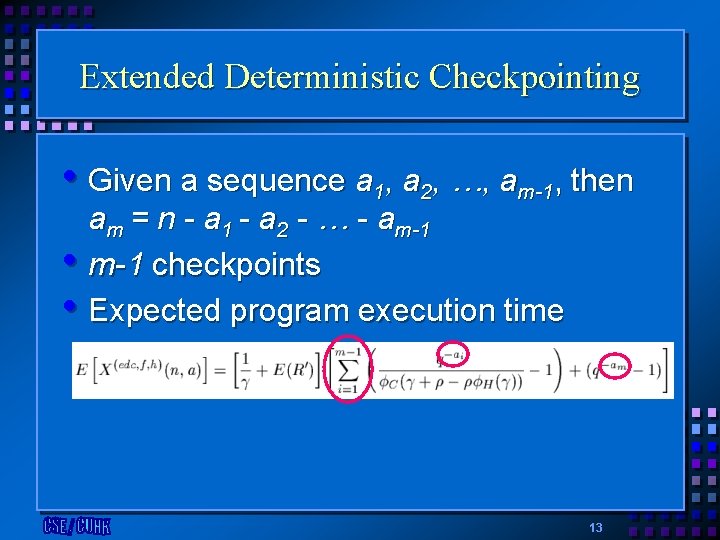
Extended Deterministic Checkpointing • Given a sequence a 1, a 2, …, am-1, then am = n - a 1 - a 2 - … - am-1 • m-1 checkpoints • Expected program execution time 13
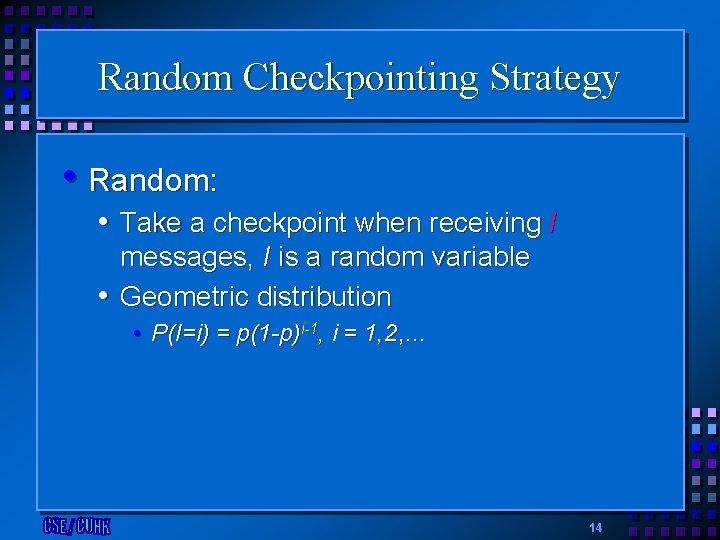
Random Checkpointing Strategy • Random: • Take a checkpoint when receiving I messages, I is a random variable • Geometric distribution • P(I=i) = p(1 -p)i-1, i = 1, 2, … 14
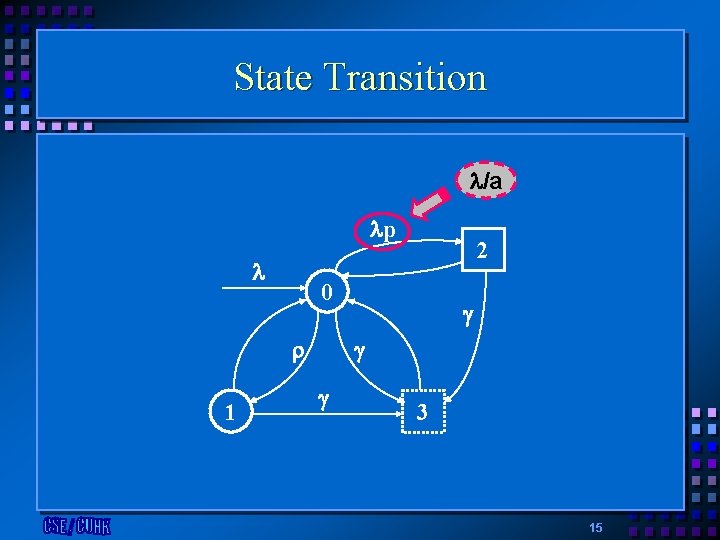
State Transition /a p 0 1 2 3 15
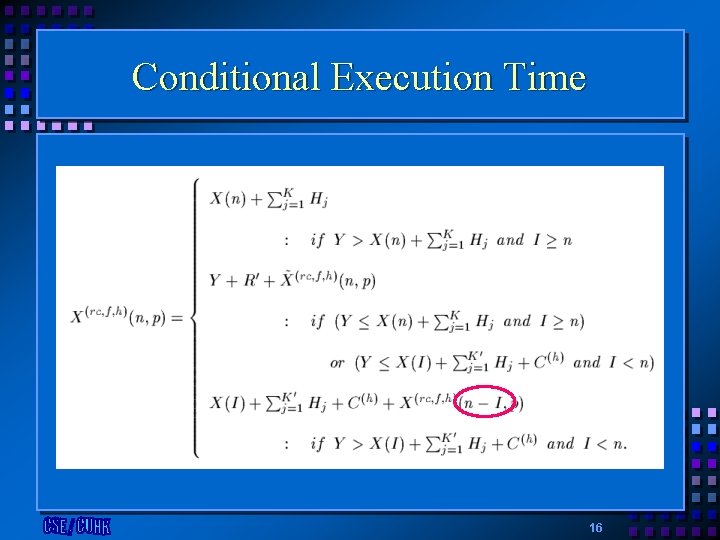
Conditional Execution Time 16
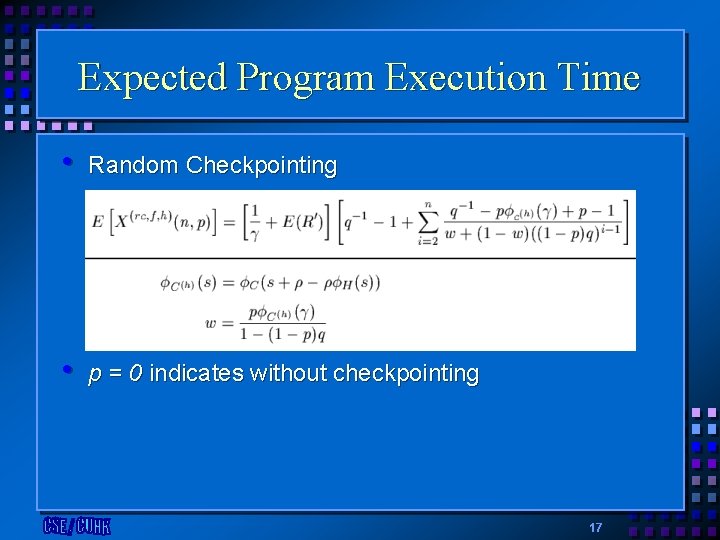
Expected Program Execution Time • Random Checkpointing • p = 0 indicates without checkpointing 17
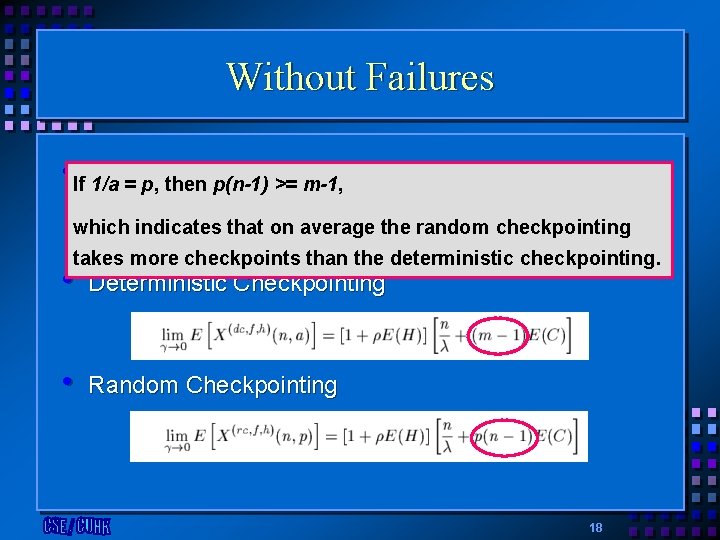
Without Failures • If Without Checkpointing 1/a = p, then p(n-1) >= m-1, which indicates that on average the random checkpointing takes more checkpoints than the deterministic checkpointing. • Deterministic Checkpointing • Random Checkpointing 18
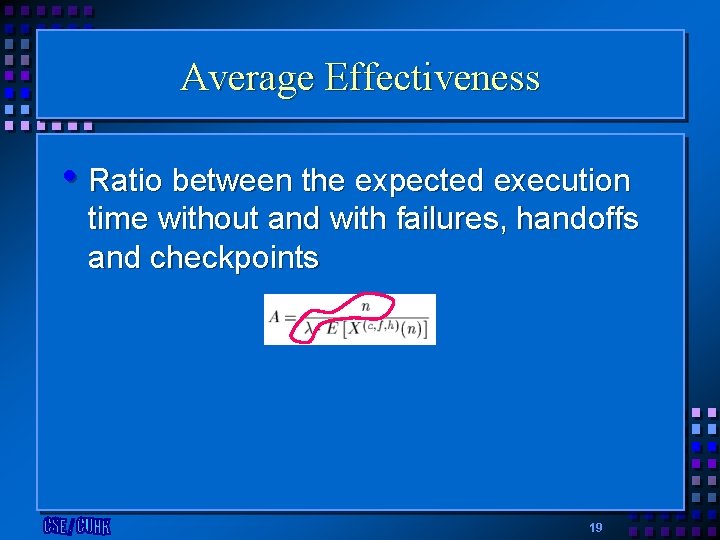
Average Effectiveness • Ratio between the expected execution time without and with failures, handoffs and checkpoints 19
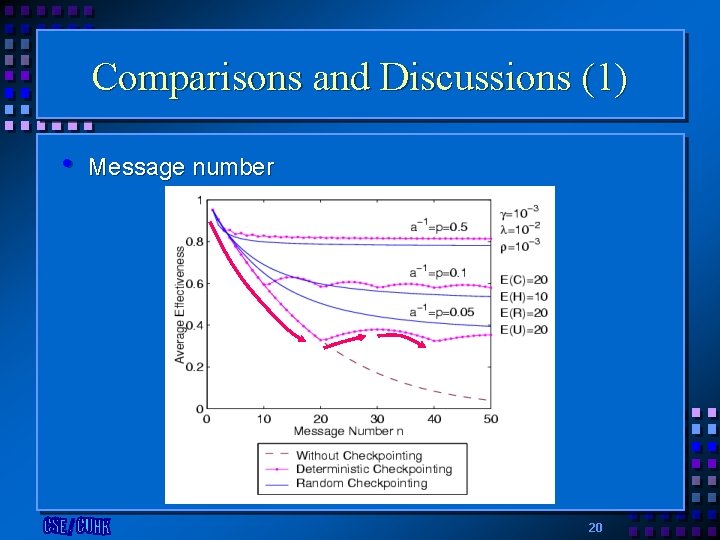
Comparisons and Discussions (1) • Message number 20
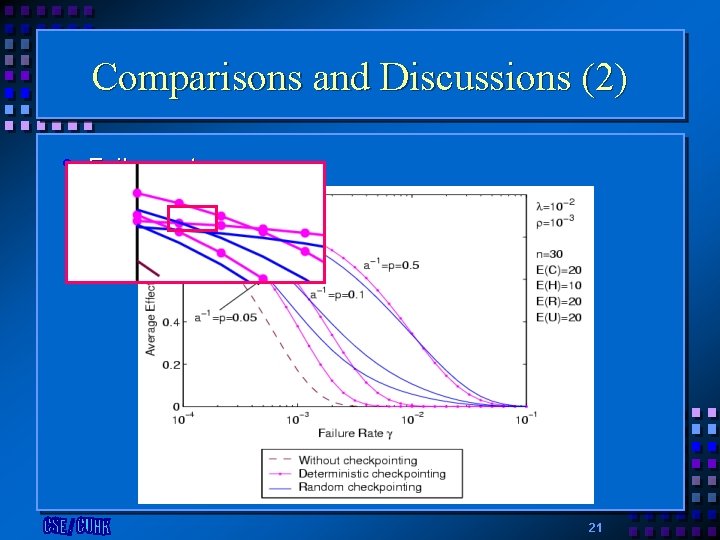
Comparisons and Discussions (2) • Failure rate 21
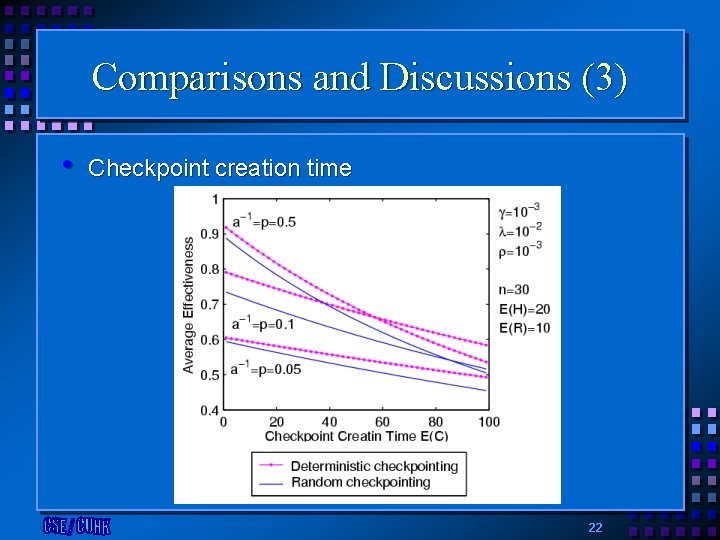
Comparisons and Discussions (3) • Checkpoint creation time 22
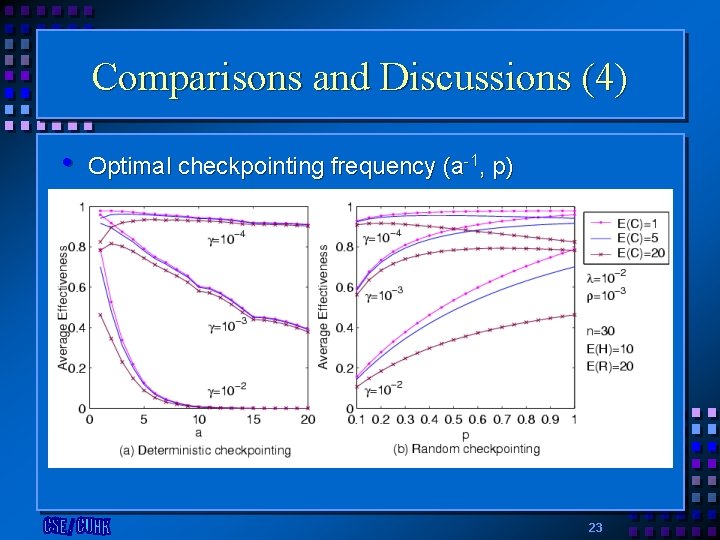
Comparisons and Discussions (4) • Optimal checkpointing frequency (a-1, p) 23
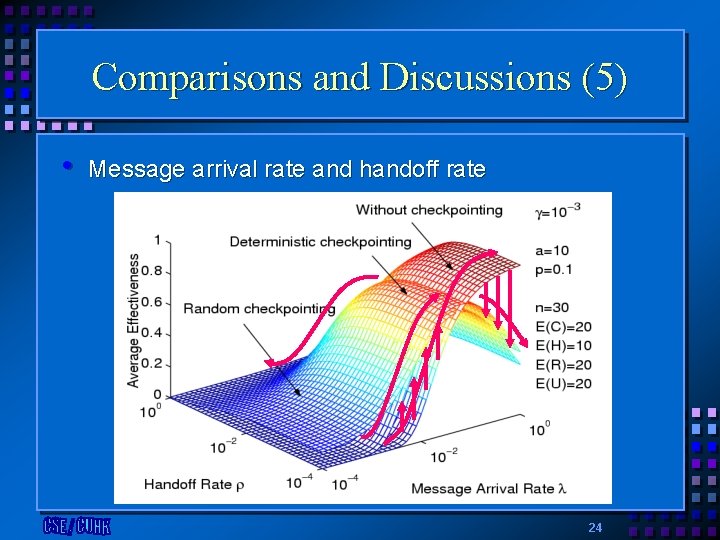
Comparisons and Discussions (5) • Message arrival rate and handoff rate 24
Expected-Reliability Analysis • Motivation • Previous work • Two-terminal reliability: the probability of successful communication between the source node and the target node • Mobile Environments • Handoff causes the change of number and type of engaged communication components 25
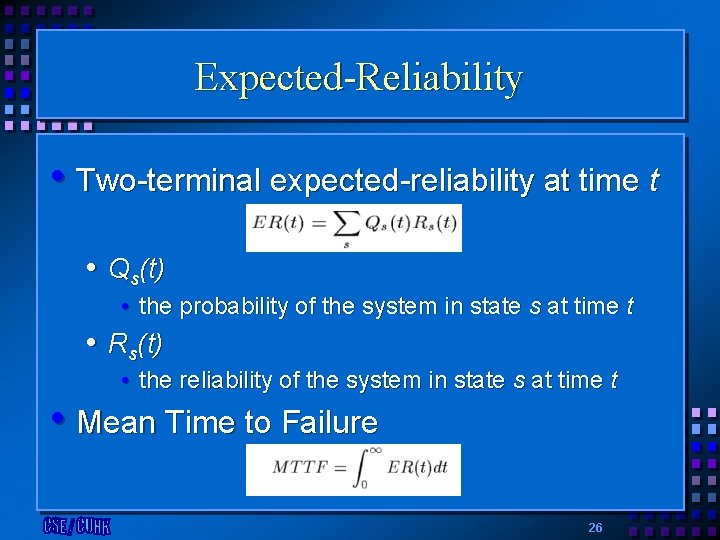
Expected-Reliability • Two-terminal expected-reliability at time t • Qs(t) • the probability of the system in state s at time t • Rs(t) • the reliability of the system in state s at time t • Mean Time to Failure 26
Four Communication Schemes • Static Host to Static Host (SS) • Traditional communication scheme • Mobile Host to Static Host (MS) • 2 system states • Static Host to Mobile Host (SM) • 4 system states • Mobile Host to Mobile Host (MM) • 8 system states 27
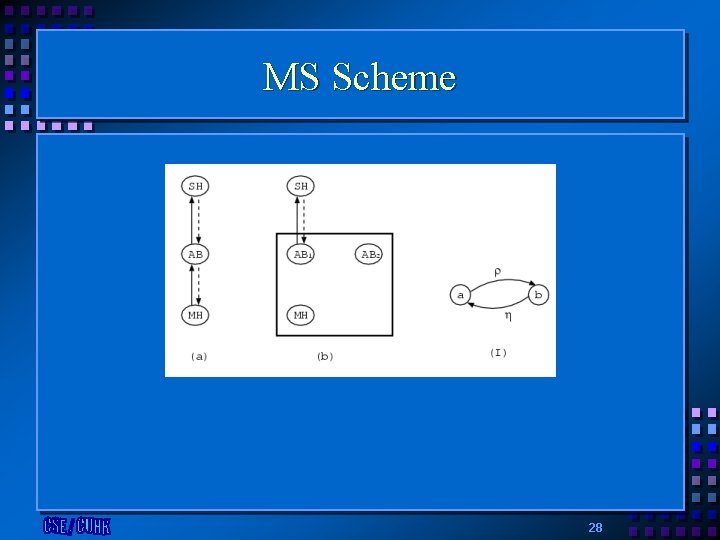
MS Scheme 28
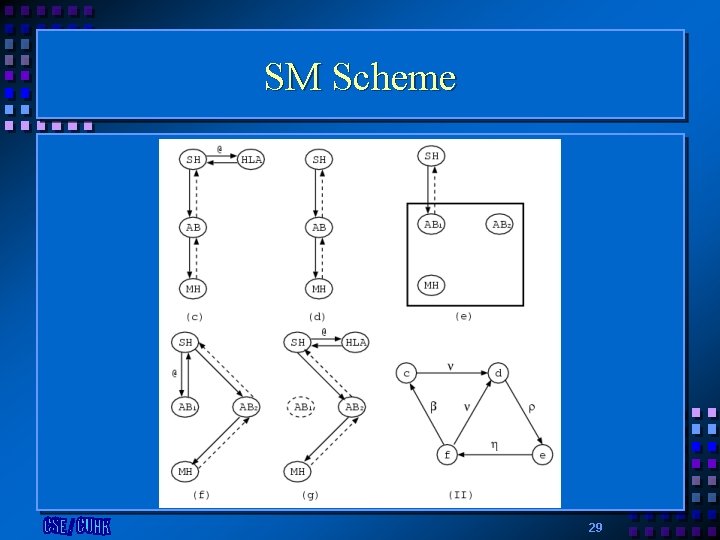
SM Scheme 29
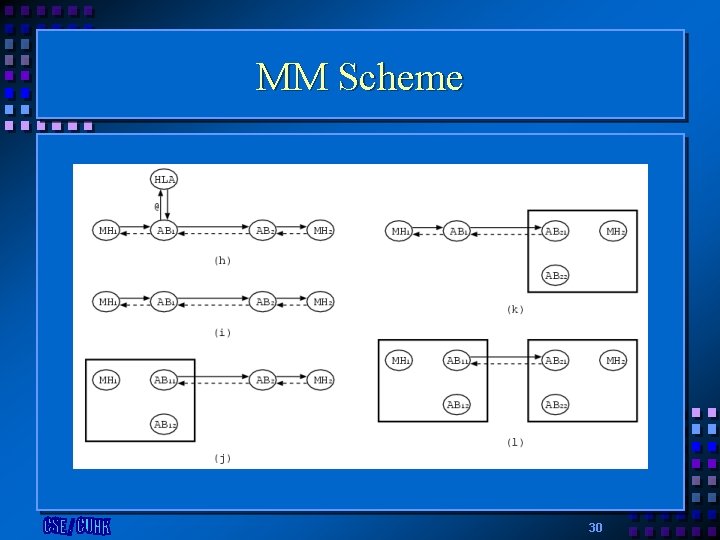
MM Scheme 30
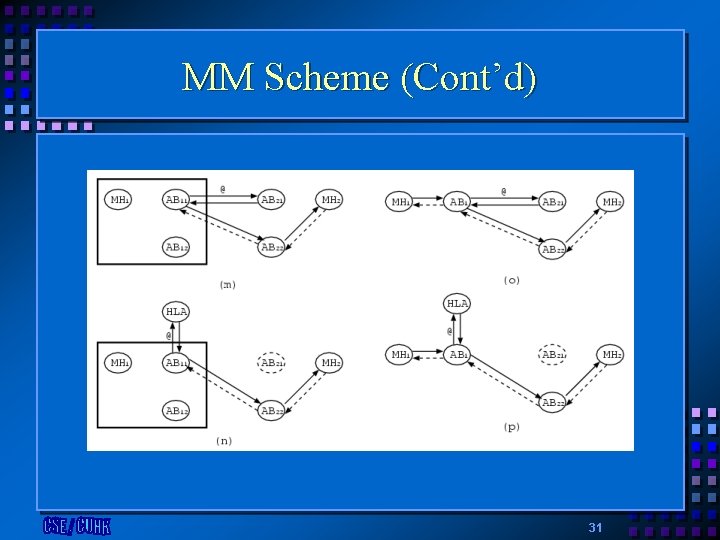
MM Scheme (Cont’d) 31
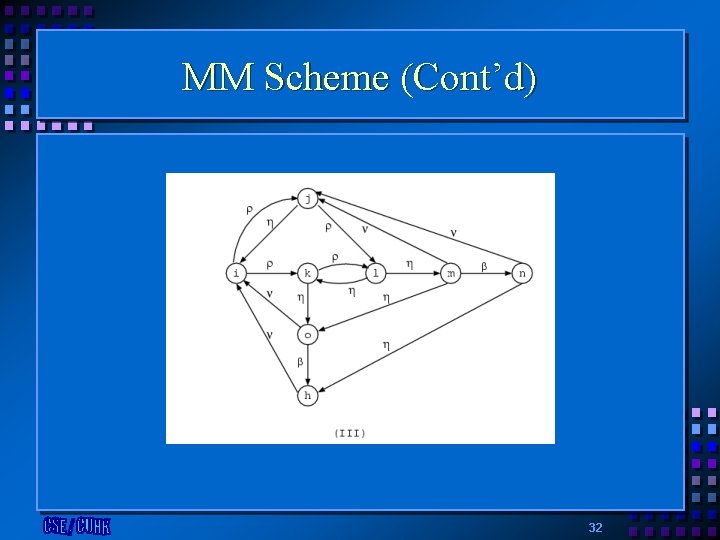
MM Scheme (Cont’d) 32
Message Sojourn Time in Access Bridge • Motivation • Previous work • Task sojourn time in the presence of server breakdowns • Mobile Environments • Due to failures and handoffs of Mobile Hosts, the messages in Access Bridge cannot be dispatched 33
Objective • To derive the expected message sojourn time in an Access Bridge with different dispatch strategies in the presence of failures and handoffs of Mobile Hosts 34
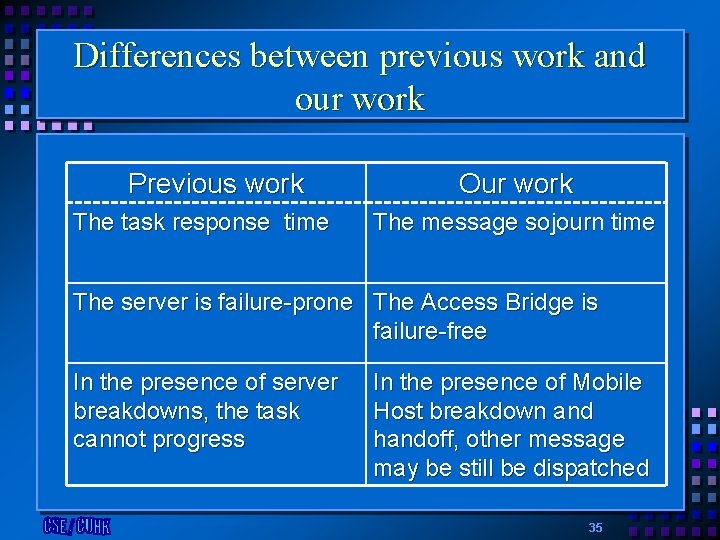
Differences between previous work and our work Previous work The task response time Our work The message sojourn time The server is failure-prone The Access Bridge is failure-free In the presence of server breakdowns, the task cannot progress In the presence of Mobile Host breakdown and handoff, other message may be still be dispatched 35
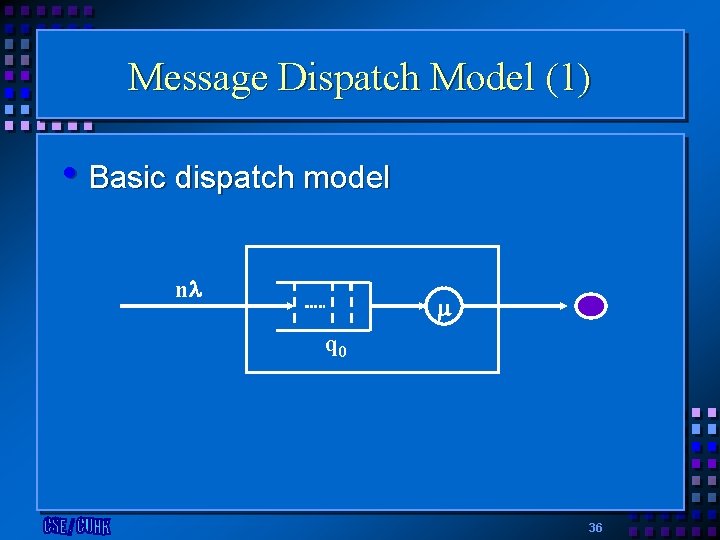
Message Dispatch Model (1) • Basic dispatch model n q 0 36
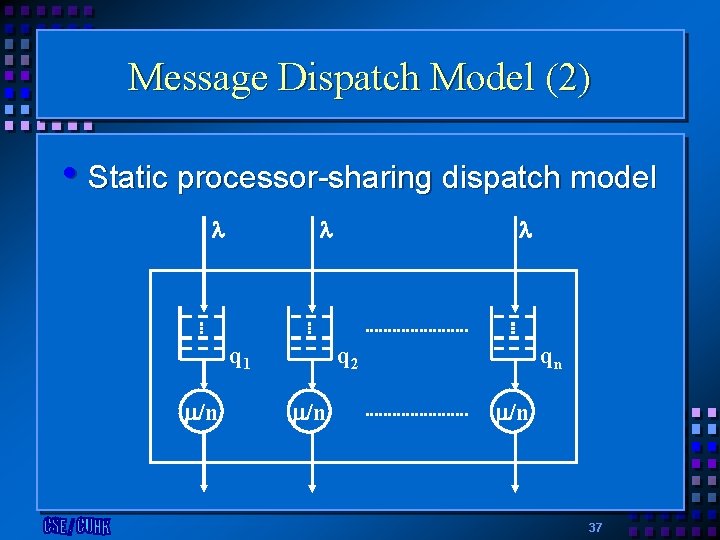
Message Dispatch Model (2) • Static processor-sharing dispatch model q 1 /n q 2 /n qn /n 37
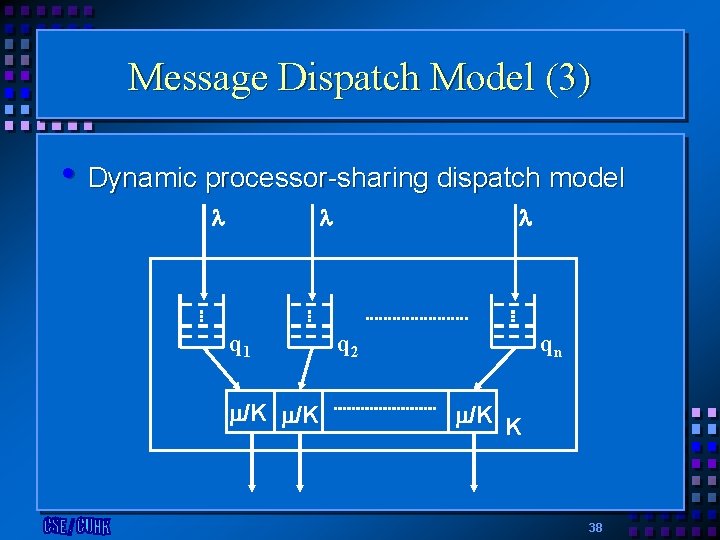
Message Dispatch Model (3) • Dynamic processor-sharing dispatch model q 1 /K /K q 2 qn /K K 38
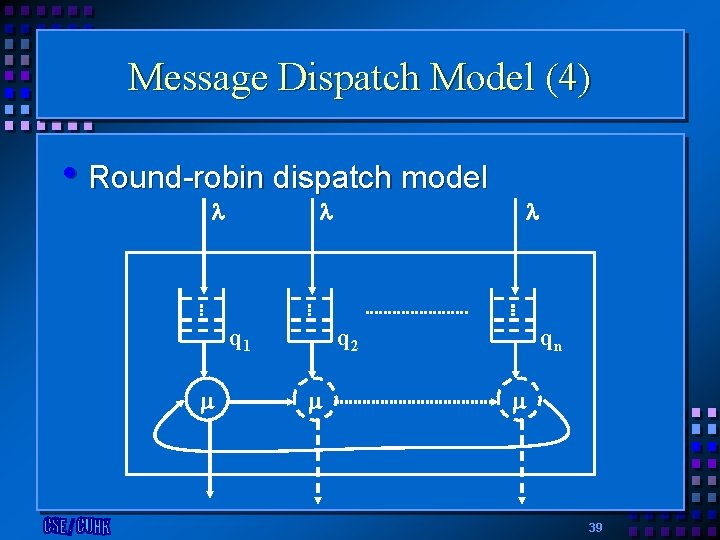
Message Dispatch Model (4) • Round-robin dispatch model q 1 q 2 qn 39
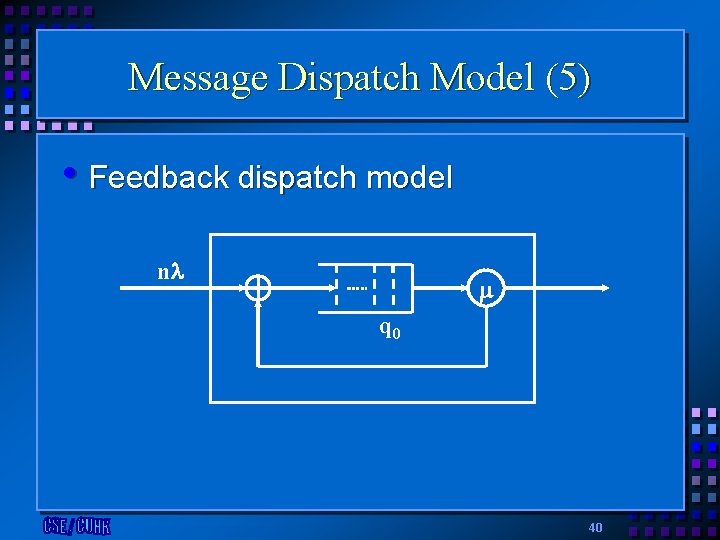
Message Dispatch Model (5) • Feedback dispatch model n q 0 40
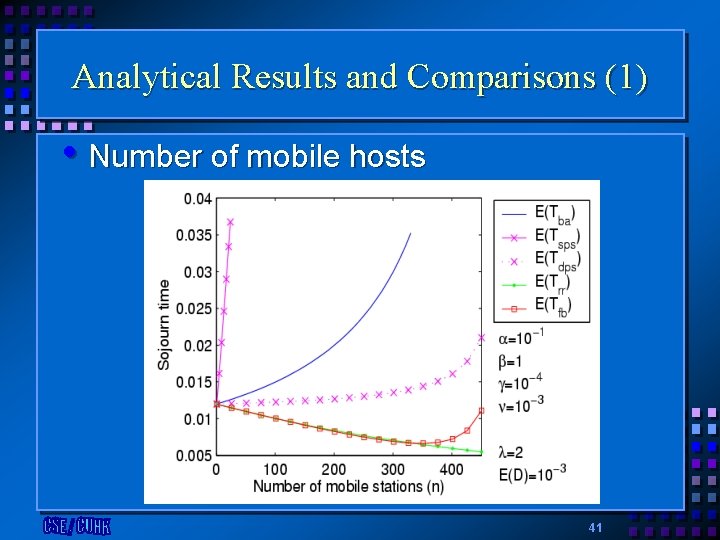
Analytical Results and Comparisons (1) • Number of mobile hosts 41
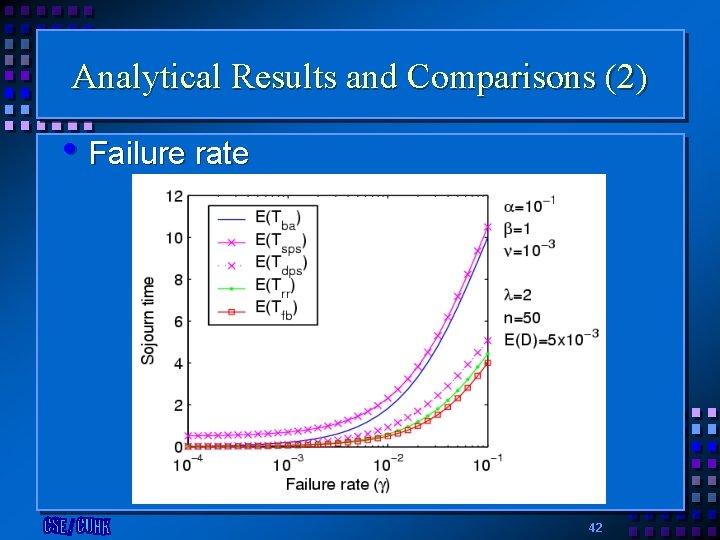
Analytical Results and Comparisons (2) • Failure rate 42
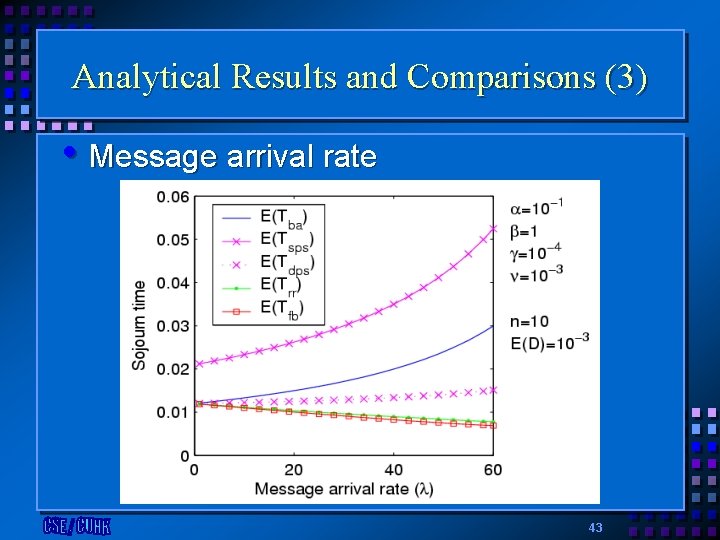
Analytical Results and Comparisons (3) • Message arrival rate 43
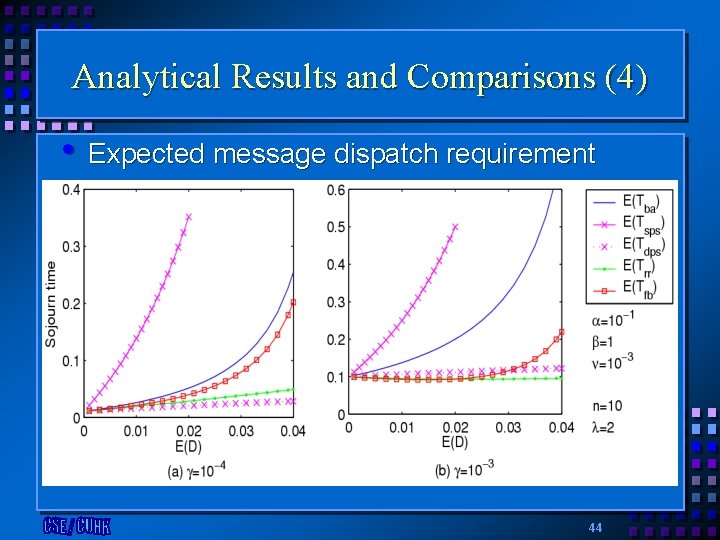
Analytical Results and Comparisons (4) • Expected message dispatch requirement 44
Conclusions • Derive the cumulative distribution function of the program execution time with various checkpointing strategies and its expectation • Observe that random checkpointing is more stable against the variation of parameters than deterministic checkpointing • Define expected-reliability to embody the • mobility characteristic introduced by handoff Analyze the message sojourn time in Access Bridge with fives dispatch models 45
Future Work • Relax some assumptions to derive more • • general program execution time • Failures may not be detected instantly Further the expected-reliability analysis to include links failures. The reliability with multiple terminals will be considered Provide fault tolerance mechanism for other mobile environments, such as ad-hoc mobile networks and sensor networks 46
- Slides: 46