Process Mining for Ubiquitous Mobile Systems An Overview
Process Mining for Ubiquitous Mobile Systems An Overview and a Concrete Algorithm Prof. dr. ir. Wil van der Aalst Eindhoven University of Technology Department of Information and Technology P. O. Box 513, 5600 MB Eindhoven The Netherlands w. m. p. v. d. aalst@tm. tue. nl Joint work with Ana Karla Alves de Medeiros, Boudewijn van Dongen, and Ton Weijters.
Outline • Motivation: Process mining in the context of UMSs • Process mining – An overview – The alpha algorithm – The alpha+ algorithm • Applications • Conclusion
Motivation • Human activities are increasingly supported by electronic tools. • These tools are increasingly mobile and ubiquitous, cf. PDAs, Bluetooth, WLAN, smart clothes, etc. • Tracing human behavior/processes will become easier, cf. RFID, GSM, etc.
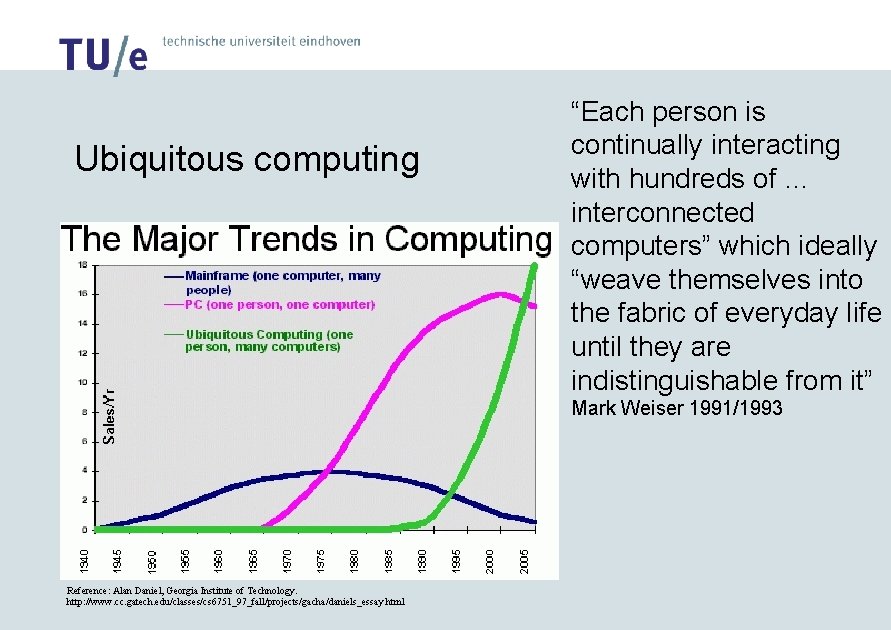
Ubiquitous computing “Each person is continually interacting with hundreds of … interconnected computers” which ideally “weave themselves into the fabric of everyday life until they are indistinguishable from it” Mark Weiser 1991/1993 Reference: Alan Daniel, Georgia Institute of Technology. http: //www. cc. gatech. edu/classes/cs 6751_97_fall/projects/gacha/daniels_essay. html
Assumptions • Increasingly information systems are composed of autonomous components/agents/… thus allowing for more flexibility and mobility. – This will trigger the need for monitoring processes/human behavior. • Information systems will be ubiquitous. – This will allow for the collection of event data. Process Mining (PM) Ubiquitous Mobile Systems (UMS)
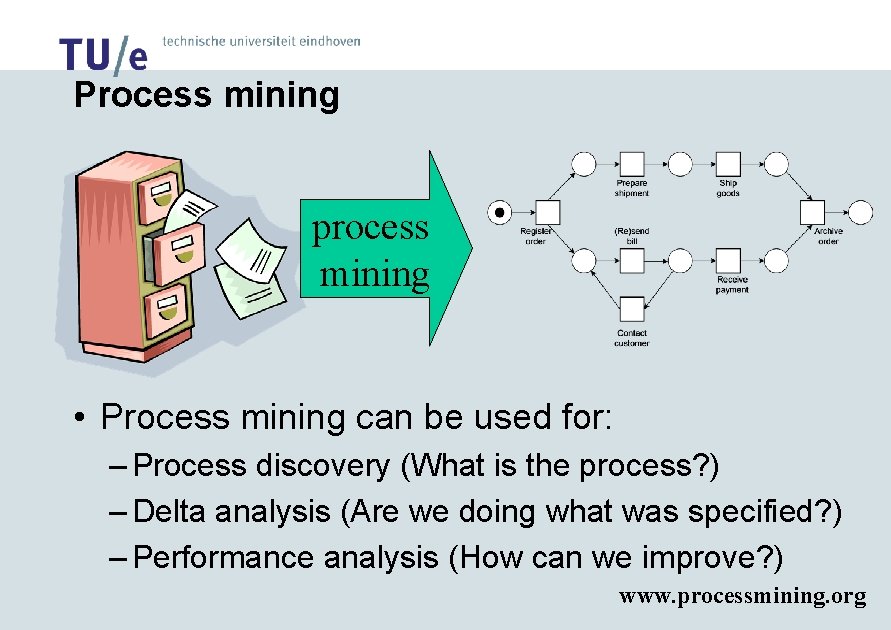
Process mining process mining • Process mining can be used for: – Process discovery (What is the process? ) – Delta analysis (Are we doing what was specified? ) – Performance analysis (How can we improve? ) www. processmining. org
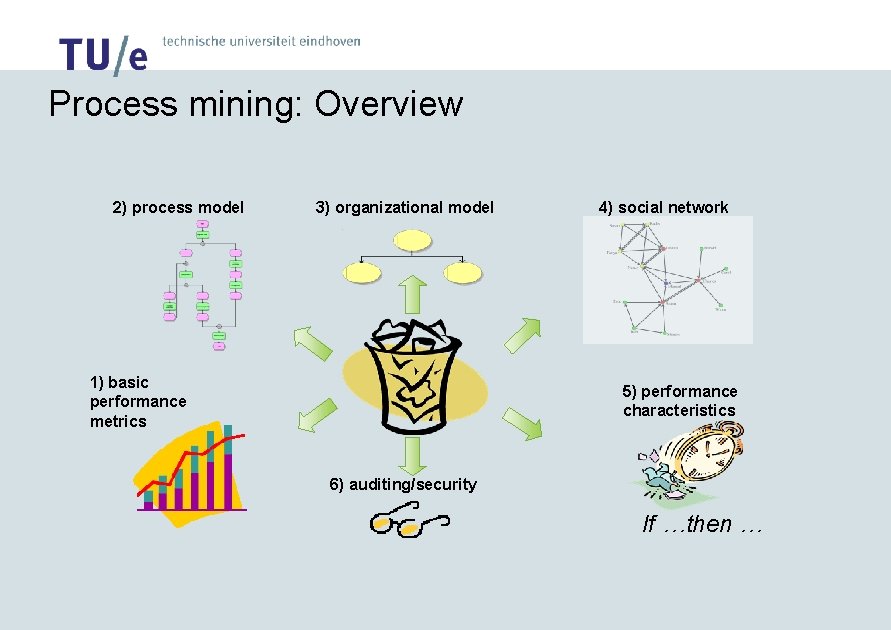
Process mining: Overview 2) process model 3) organizational model 1) basic performance metrics 4) social network 5) performance characteristics 6) auditing/security If …then …
Process Mining: The alpha algorithm
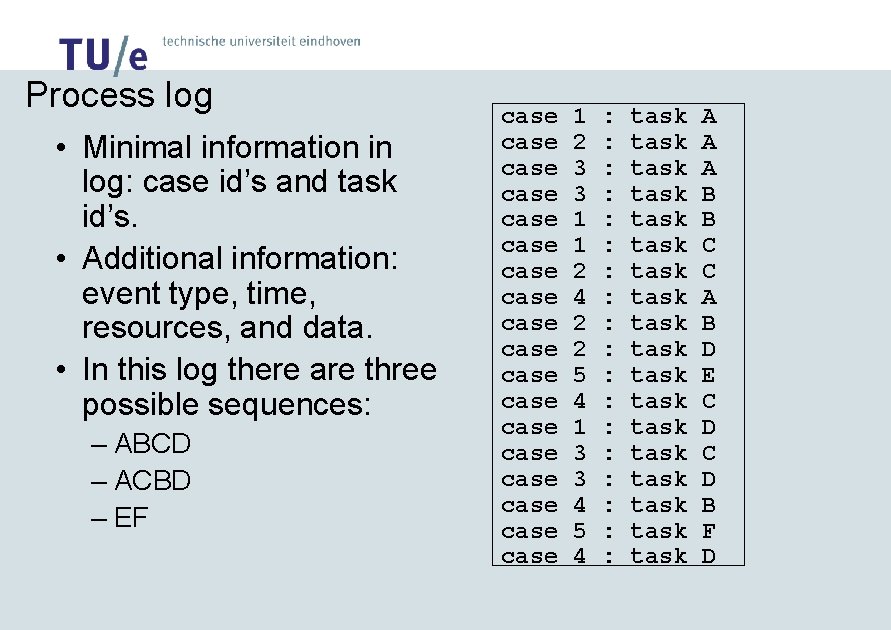
Process log • Minimal information in log: case id’s and task id’s. • Additional information: event type, time, resources, and data. • In this log there are three possible sequences: – ABCD – ACBD – EF case case case case case 1 2 3 3 1 1 2 4 2 2 5 4 1 3 3 4 5 4 : : : : : task task task task task A A A B B C C A B D E C D B F D
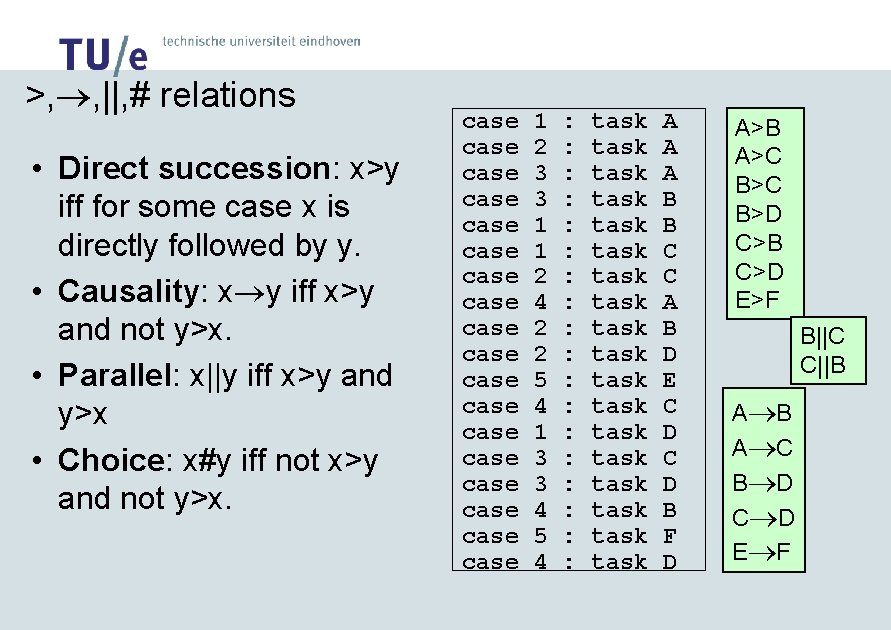
>, , ||, # relations • Direct succession: x>y iff for some case x is directly followed by y. • Causality: x y iff x>y and not y>x. • Parallel: x||y iff x>y and y>x • Choice: x#y iff not x>y and not y>x. case case case case case 1 2 3 3 1 1 2 4 2 2 5 4 1 3 3 4 5 4 : : : : : task task task task task A A A B B C C A B D E C D B F D A>B A>C B>D C>B C>D E>F B||C C||B A C B D C D E F
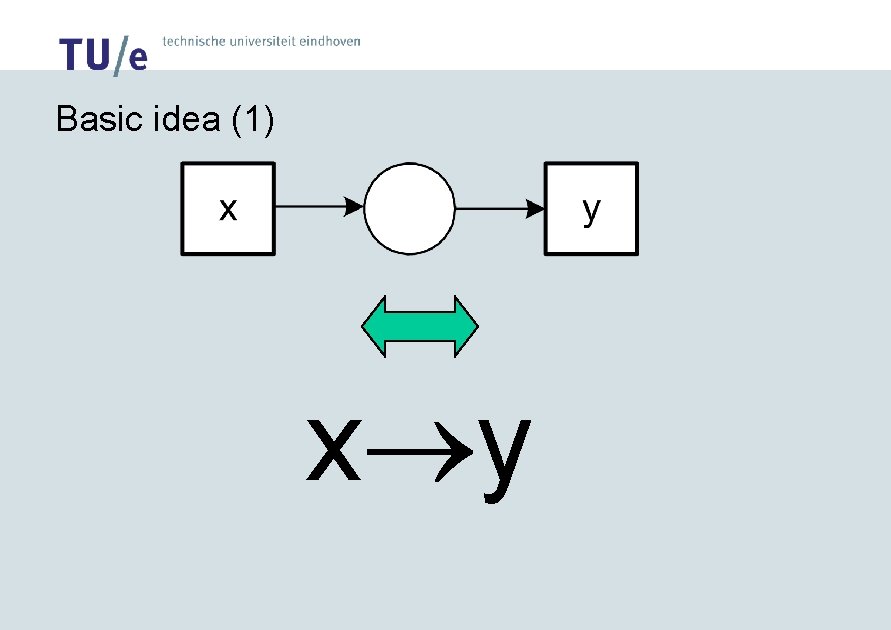
Basic idea (1) x y
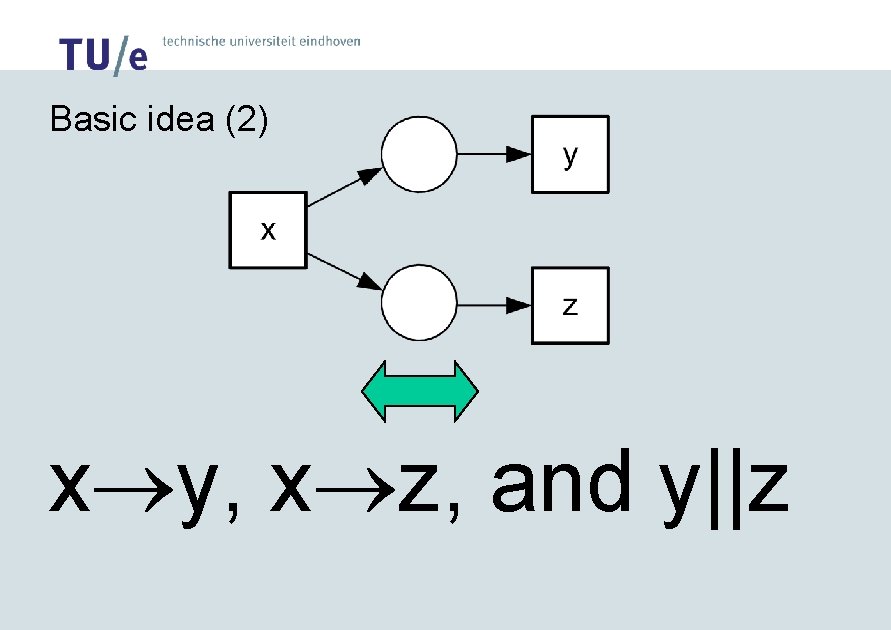
Basic idea (2) x y, x z, and y||z
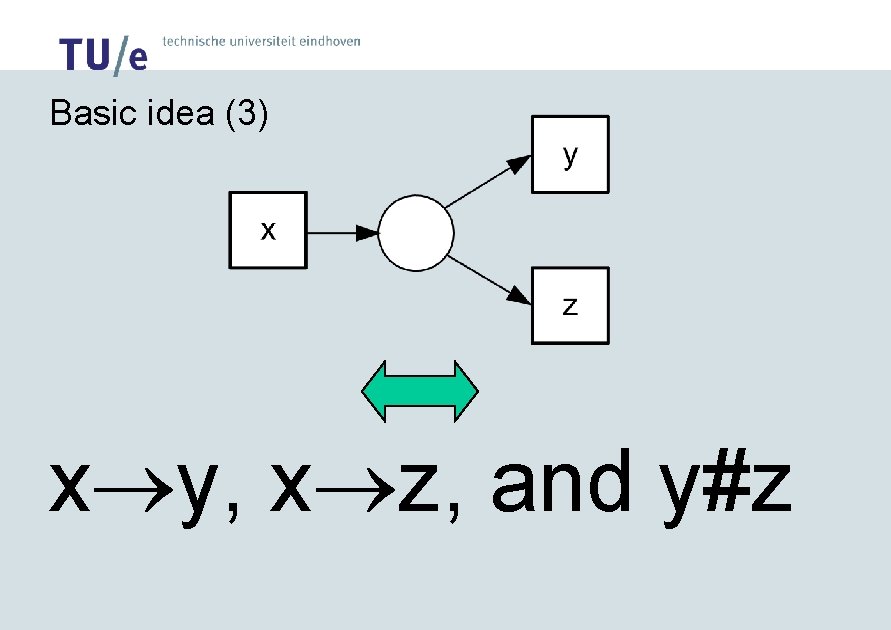
Basic idea (3) x y, x z, and y#z
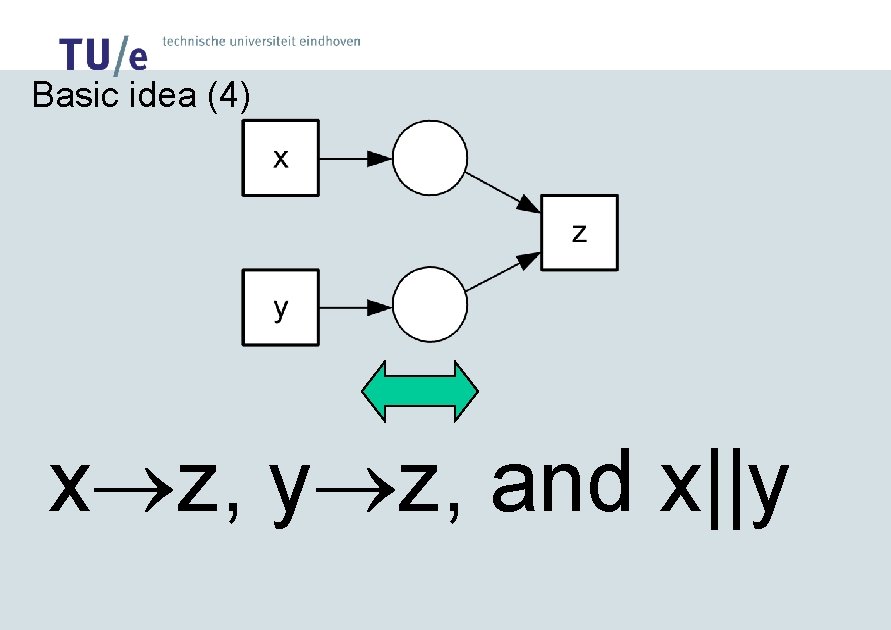
Basic idea (4) x z, y z, and x||y
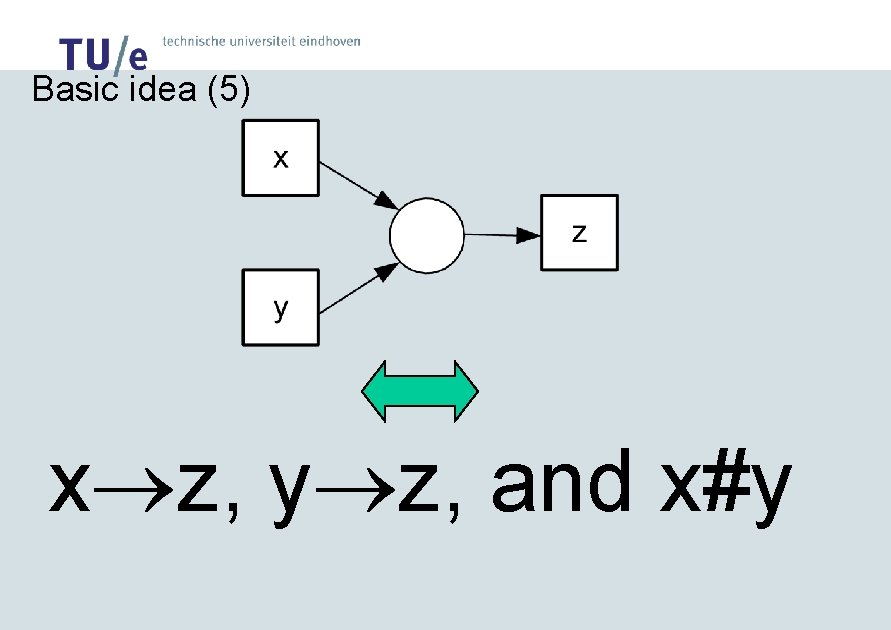
Basic idea (5) x z, y z, and x#y
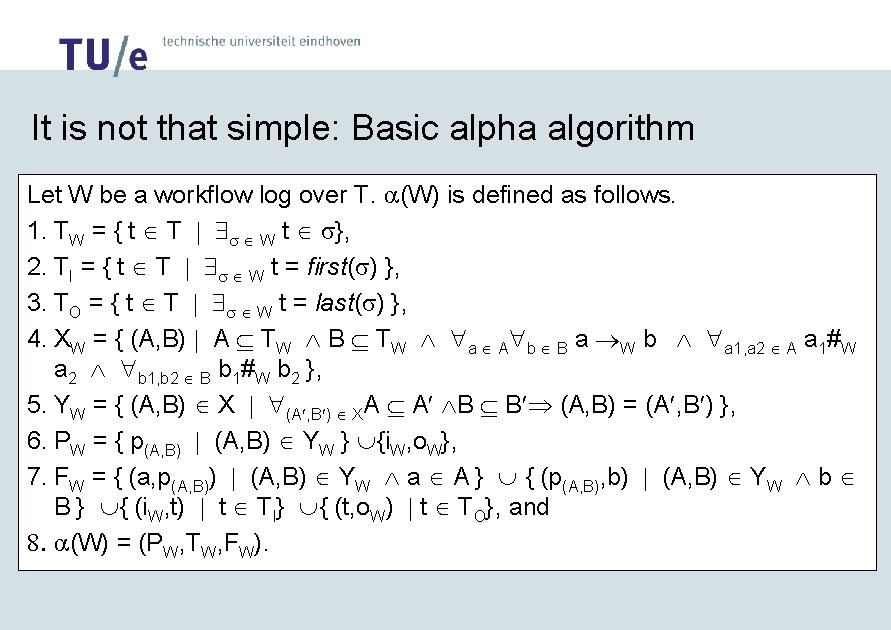
It is not that simple: Basic alpha algorithm Let W be a workflow log over T. a(W) is defined as follows. 1. TW = { t Î T | $s Î W t Î s}, 2. TI = { t Î T | $s Î W t = first(s) }, 3. TO = { t Î T | $s Î W t = last(s) }, 4. XW = { (A, B) | A Í TW Ù B Í TW Ù "a Î A"b Î B a W b Ù "a 1, a 2 Î A a 1#W a 2 Ù "b 1, b 2 Î B b 1#W b 2 }, 5. YW = { (A, B) Î X | "(A¢, B¢) Î XA Í A¢ ÙB Í B¢Þ (A, B) = (A¢, B¢) }, 6. PW = { p(A, B) | (A, B) Î YW } È{i. W, o. W}, 7. FW = { (a, p(A, B)) | (A, B) Î YW Ù a Î A } È { (p(A, B), b) | (A, B) Î YW Ù b Î B } È{ (i. W, t) | t Î TI} È{ (t, o. W) | t Î TO}, and 8. a(W) = (PW, TW, FW).
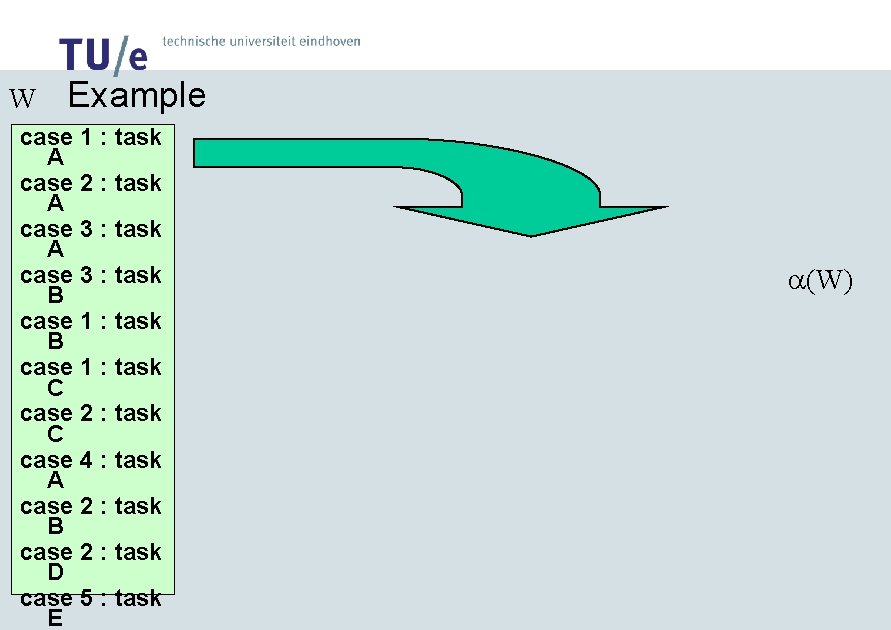
W Example case 1 : task A case 2 : task A case 3 : task B case 1 : task C case 2 : task C case 4 : task A case 2 : task B case 2 : task D case 5 : task E a(W)
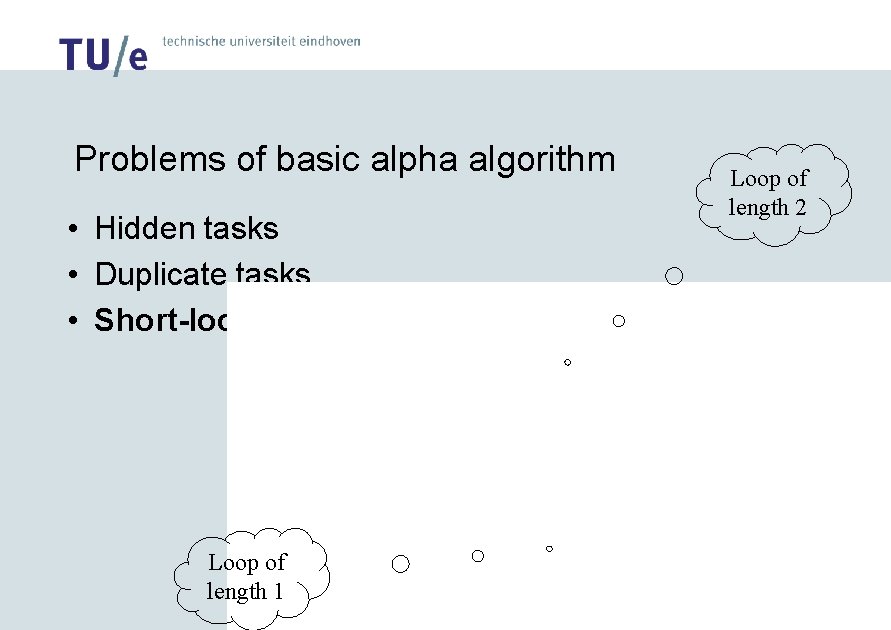
Problems of basic alpha algorithm • Hidden tasks • Duplicate tasks • Short-loops Loop of length 1 Loop of length 2
Dealing with short loops: The alpha+ algorithm This paper deals with short loops. • Loops of length 2 are addressed by refining the ordering relations (look for xyx to distinguish a loop from x||y). • Loops of length 1 are addressed by a preprocessing step where they are first removed and then added in a post-processing step. (For details, see paper. ) (Approach has been implemented and tested. )
Process Mining: Tooling
Applications • We have applied/are applying our process mining techniques within several organizations (CJIB, RWS, UWV, …). • We did not apply them in the context of Ubiquitous Mobile Systems (UMSs) yet, therefore we present some application scenarios.
Application scenario: Clinical information systems • Use of PDAs for personnel, RFID tags for equipment, etc. • Process mining can be used to support evidencebased medicine. http: //www. handheldmed. com
Application scenario: Web services http: //xml. ahg. com/ • Are organizations working the way they should? • See BPEL 4 WS: “Business processes can be described in two ways. Executable business processes model actual behavior of a participant in a business interaction. Business protocols, in contrast, use process descriptions that specify the mutually visible message exchange behavior of each of the parties involved in the protocol, without revealing their internal behavior. The process descriptions for business protocols are called abstract processes. BPEL 4 WS is meant to be used to model the behavior of both executable and abstract processes. ” http: //www. ibm. com/developerworks/library/ws-bpel/
Application scenario: Wireless gallery information system • Use of PDAs for providing content based on proximity. • Process mining can be used to monitor the interests of visitors. e. Docent™ American Museum of the Moving Image www. ammi. org/site/extrapages/edoctext. html
Conclusion • Process mining seems to be interesting in the context of Ubiquitous Mobile Systems (UMSs). • There are many challenges: – Improving the algorithms (hidden/duplicate tasks, …) – Gathering the data – Visualizing the results – Etc. • In this paper we “solved” one of these problems: short loops. • Join us at www. processmining. org
- Slides: 26