PrivacyPreserving Reachability Query Services for Massive Networks Presenter
Privacy-Preserving Reachability Query Services for Massive Networks Presenter: JIANG Jiaxin 1 Joint work with Peipei Yi 1, Byron Choi 1, Zhiwei Zhang 1, Xiaohui Yu 2 Department of Computer Science, Hong Kong Baptist University, Hong Kong, China 1 School of Computer Science, Shandong University, Jinan, China 2 Privacy-Preserving Reachability Query Services for Massive Networks 1
Agenda • Query Services for Large Networks • Related Work • Privacy-Preserving Query Services • Experimental Results • Future Work Privacy-Preserving Reachability Query Services for Massive Networks 2
Types of Real Graph Data Two typical types of graph data: • Large numbers of graphs with modest sizes (102 vertices) • protein database, • GENE database • One large graph, e. g. , social network, road network, knowledge network and communication network. Privacy-Preserving Reachability Query Services for Massive Networks 3
Why Query Services Challenges of hosting querying systems for graph data: • The increasing volume of graph data • Facebook social graph grows over 1 billions vertices • The high computation of numerous graph queries. • Limited IT resources of data owners Solution: the employment of the third-party query services, backed up by high performance computing capabilities Privacy-Preserving Reachability Query Services for Massive Networks 4
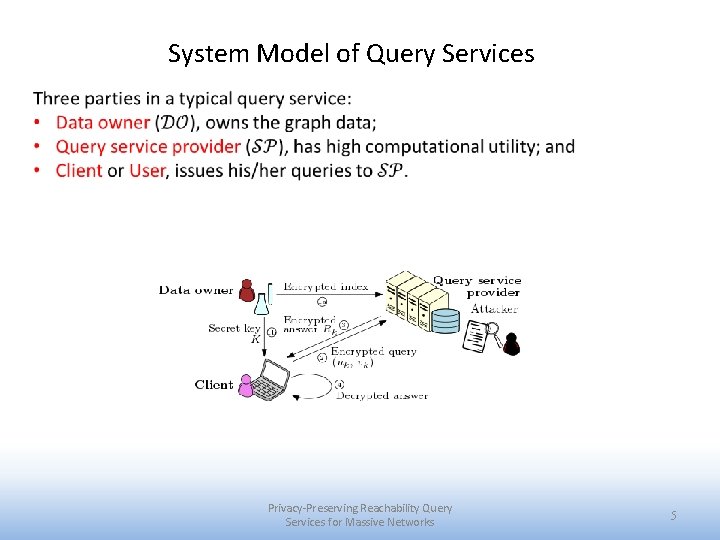
System Model of Query Services Privacy-Preserving Reachability Query Services for Massive Networks 5
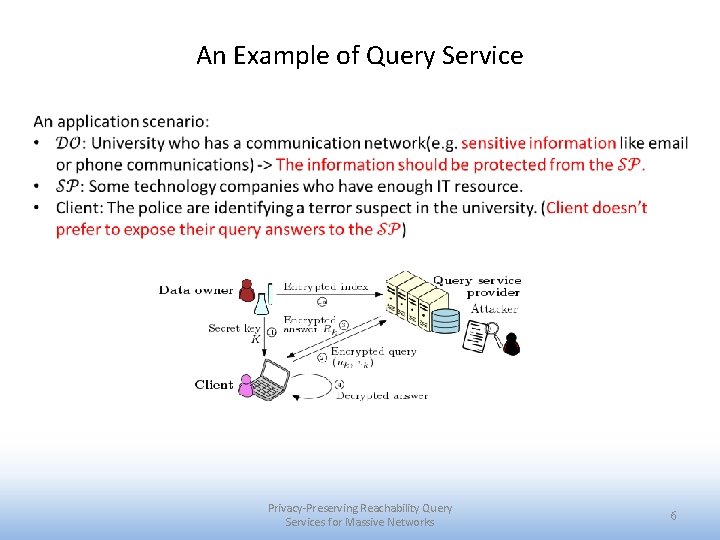
An Example of Query Service Privacy-Preserving Reachability Query Services for Massive Networks 6
Main Challenge -- Privacy How can we exploit those query services while keeping the data and queries secret? Privacy-Preserving Reachability Query Services for Massive Networks 7
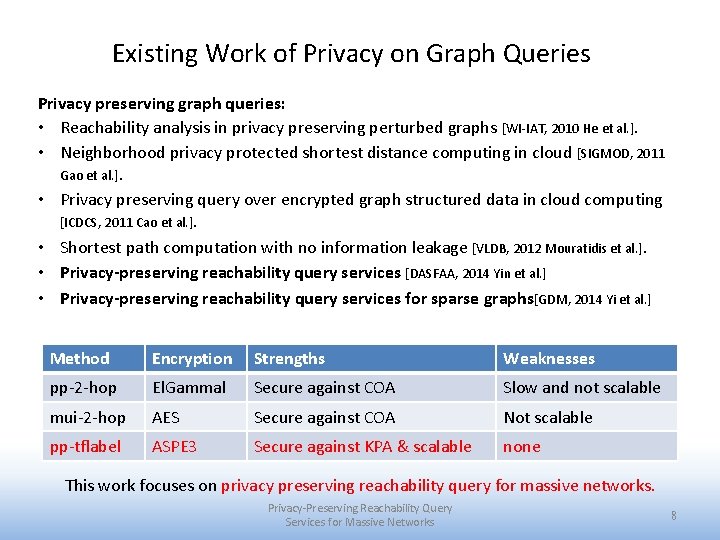
Existing Work of Privacy on Graph Queries Privacy preserving graph queries: • Reachability analysis in privacy preserving perturbed graphs [WI-IAT, 2010 He et al. ]. • Neighborhood privacy protected shortest distance computing in cloud [SIGMOD, 2011 Gao et al. ]. • Privacy preserving query over encrypted graph structured data in cloud computing [ICDCS, 2011 Cao et al. ]. • Shortest path computation with no information leakage [VLDB, 2012 Mouratidis et al. ]. • Privacy-preserving reachability query services [DASFAA, 2014 Yin et al. ] • Privacy-preserving reachability query services for sparse graphs[GDM, 2014 Yi et al. ] Method Encryption Strengths Weaknesses pp-2 -hop El. Gammal Secure against COA Slow and not scalable mui-2 -hop AES Secure against COA Not scalable pp-tflabel ASPE 3 Secure against KPA & scalable none This work focuses on privacy preserving reachability query for massive networks. Privacy-Preserving Reachability Query Services for Massive Networks 8
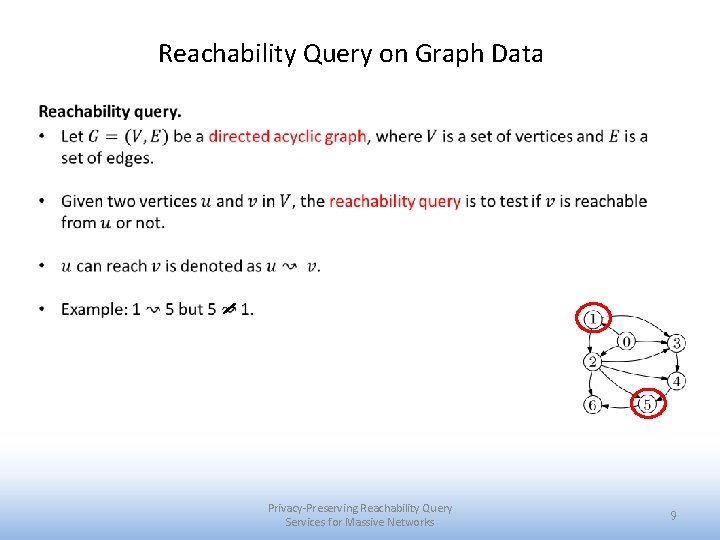
Reachability Query on Graph Data Privacy-Preserving Reachability Query Services for Massive Networks 9
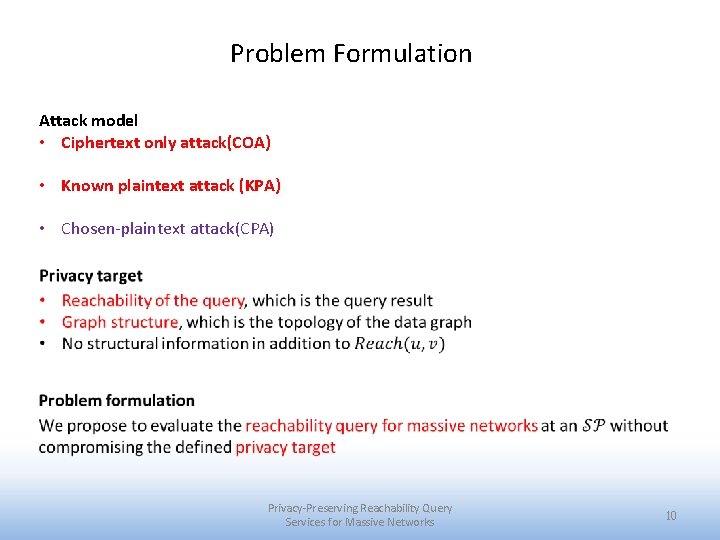
Problem Formulation Attack model • Ciphertext only attack(COA) • Known plaintext attack (KPA) • Chosen-plaintext attack(CPA) Privacy-Preserving Reachability Query Services for Massive Networks 10
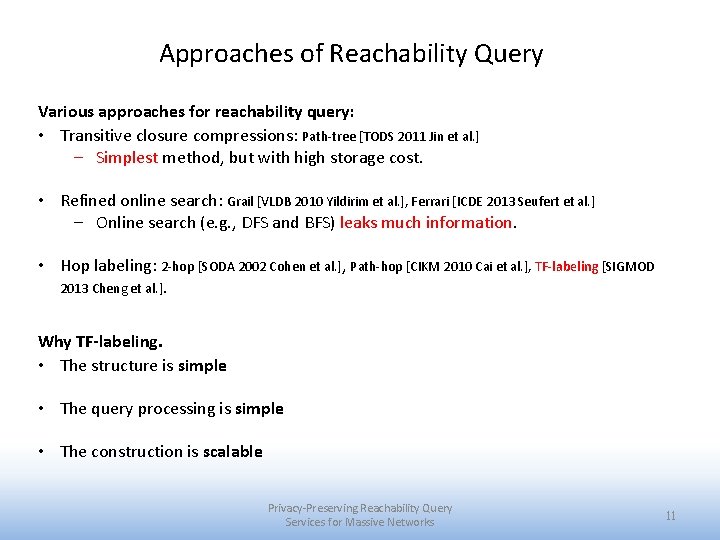
Approaches of Reachability Query Various approaches for reachability query: • Transitive closure compressions: Path-tree [TODS 2011 Jin et al. ] – Simplest method, but with high storage cost. • Refined online search: Grail [VLDB 2010 Yildirim et al. ], Ferrari [ICDE 2013 Seufert et al. ] – Online search (e. g. , DFS and BFS) leaks much information. • Hop labeling: 2 -hop [SODA 2002 Cohen et al. ], Path-hop [CIKM 2010 Cai et al. ], TF-labeling [SIGMOD 2013 Cheng et al. ]. Why TF-labeling. • The structure is simple • The query processing is simple • The construction is scalable Privacy-Preserving Reachability Query Services for Massive Networks 11
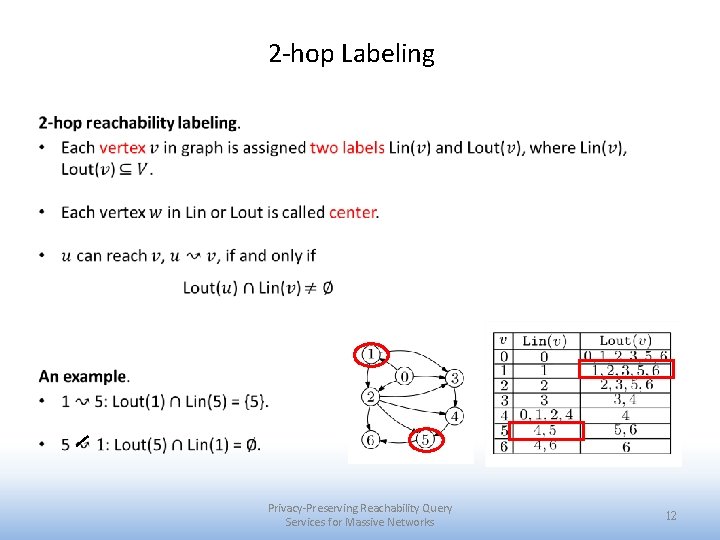
2 -hop Labeling Privacy-Preserving Reachability Query Services for Massive Networks 12
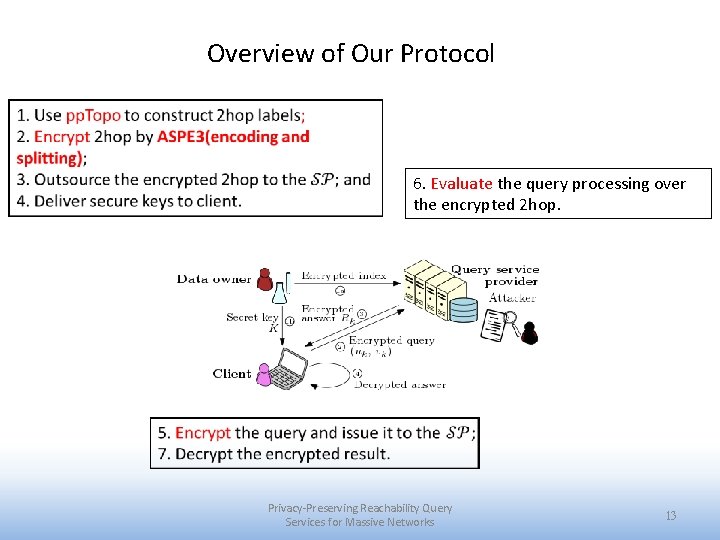
Overview of Our Protocol 6. Evaluate the query processing over the encrypted 2 hop. Privacy-Preserving Reachability Query Services for Massive Networks 13
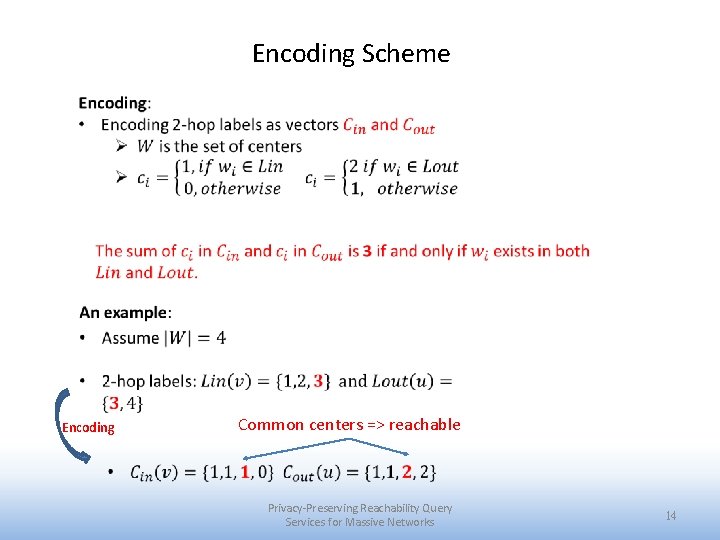
Encoding Scheme Encoding Common centers => reachable Privacy-Preserving Reachability Query Services for Massive Networks 14
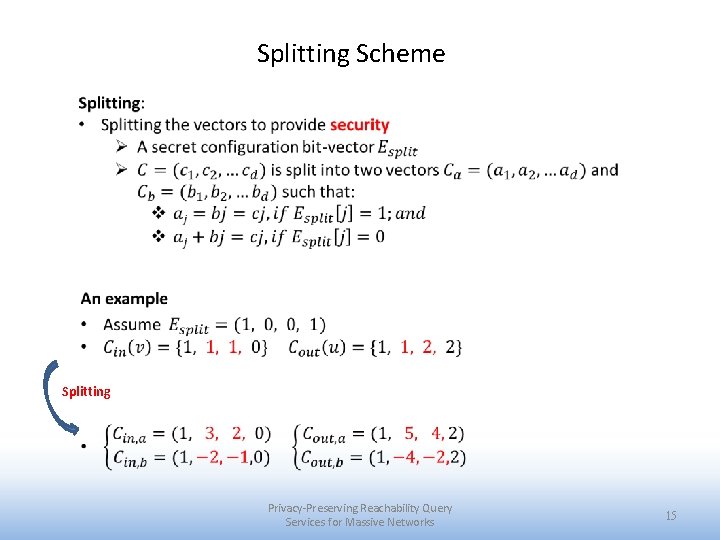
Splitting Scheme Splitting Privacy-Preserving Reachability Query Services for Massive Networks 15
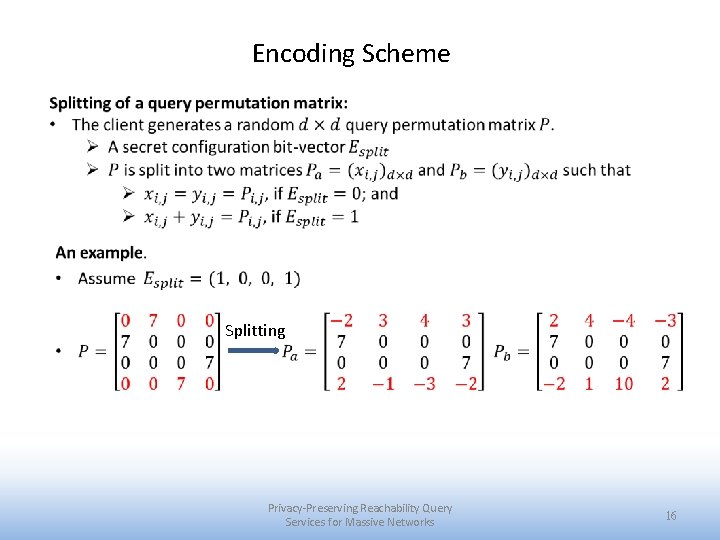
Encoding Scheme Splitting Privacy-Preserving Reachability Query Services for Massive Networks 16
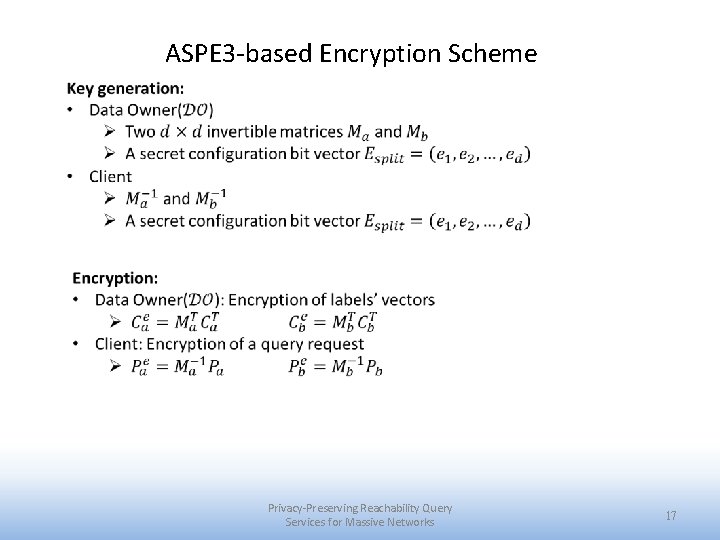
ASPE 3 -based Encryption Scheme Privacy-Preserving Reachability Query Services for Massive Networks 17
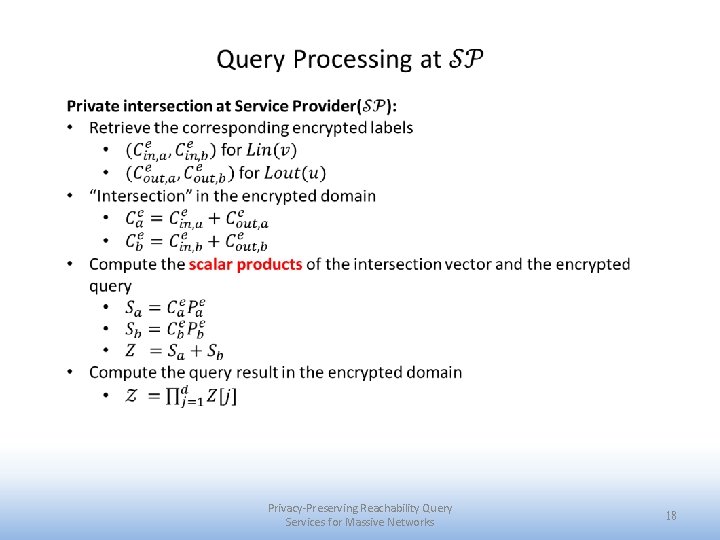
Privacy-Preserving Reachability Query Services for Massive Networks 18
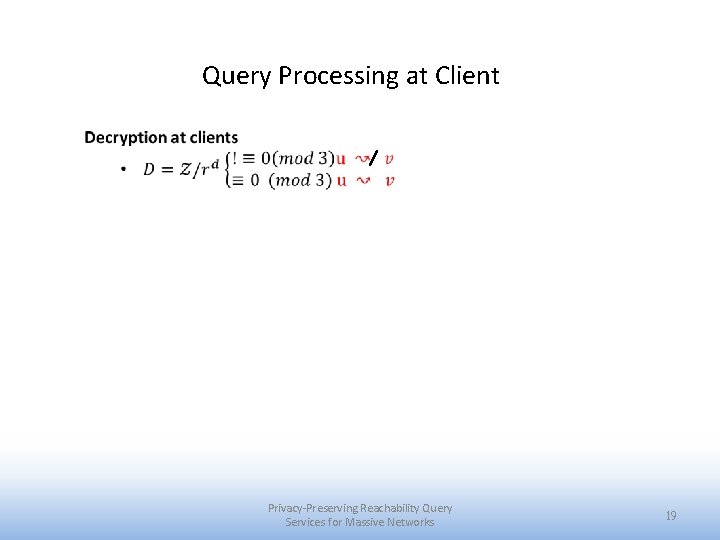
Query Processing at Client Privacy-Preserving Reachability Query Services for Massive Networks 19
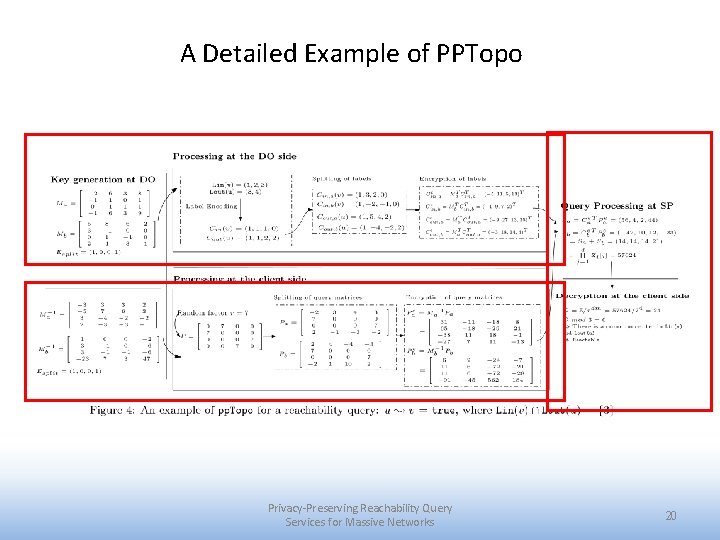
A Detailed Example of PPTopo Privacy-Preserving Reachability Query Services for Massive Networks 20
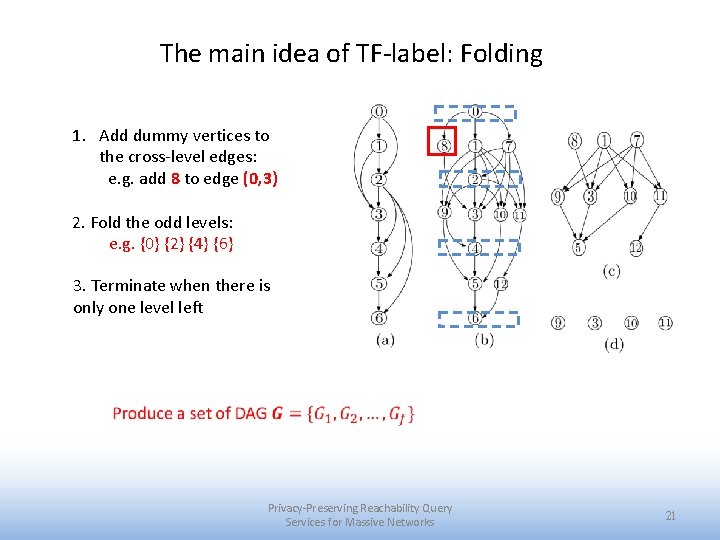
The main idea of TF-label: Folding 1. Add dummy vertices to the cross-level edges: e. g. add 8 to edge (0, 3) 2. Fold the odd levels: e. g. {0} {2} {4} {6} 3. Terminate when there is only one level left Privacy-Preserving Reachability Query Services for Massive Networks 21
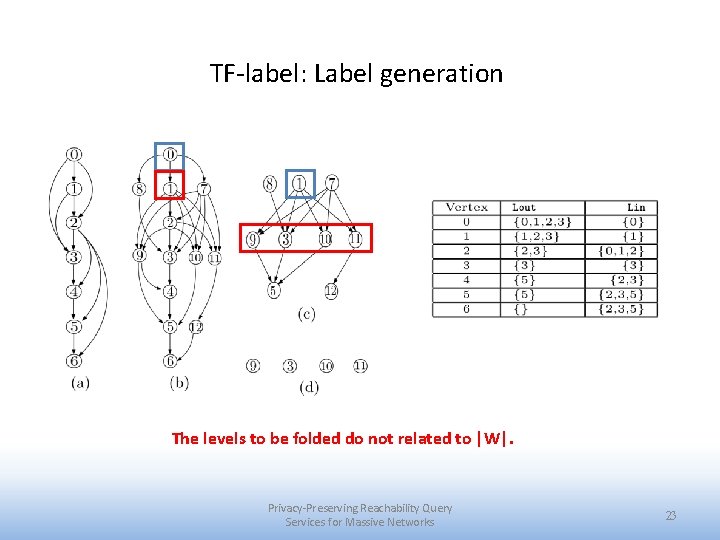
TF-label: Label generation The levels to be folded do not related to |W|. Privacy-Preserving Reachability Query Services for Massive Networks 23
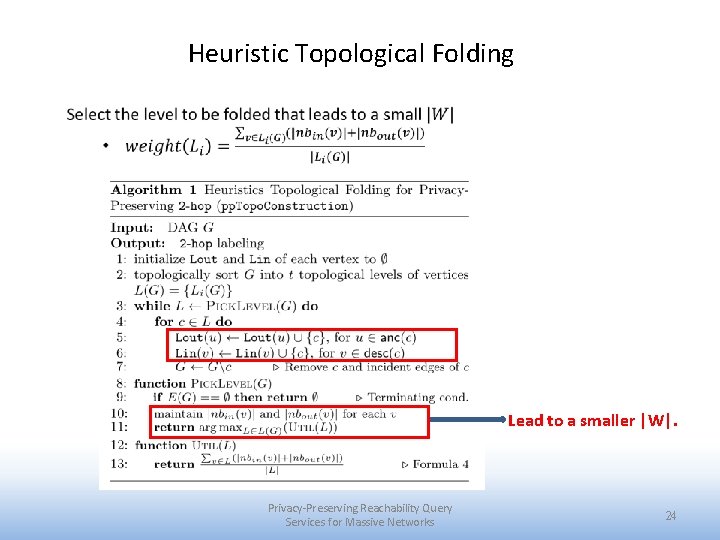
Heuristic Topological Folding Lead to a smaller |W|. Privacy-Preserving Reachability Query Services for Massive Networks 24
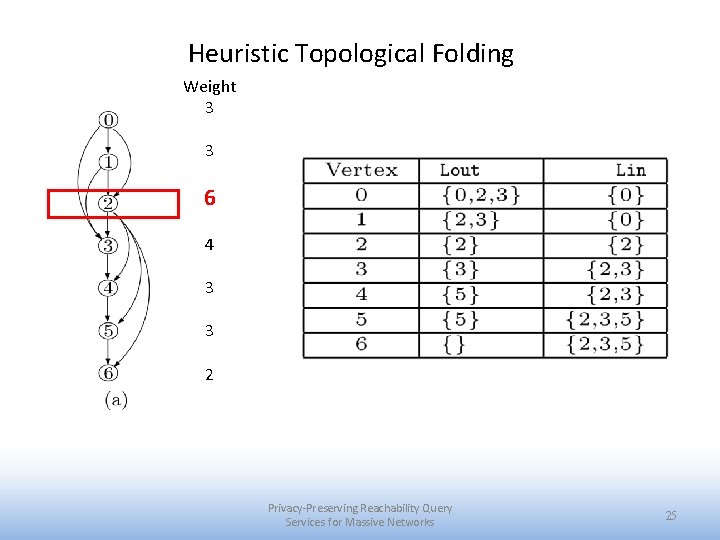
Heuristic Topological Folding Weight 3 3 6 4 3 3 2 Privacy-Preserving Reachability Query Services for Massive Networks 25
Privacy Analysis Privacy guarantee. We have proven that PPTopo preserves the reachability of query and the graph structure under the predefined attack model. Privacy-Preserving Reachability Query Services for Massive Networks 26
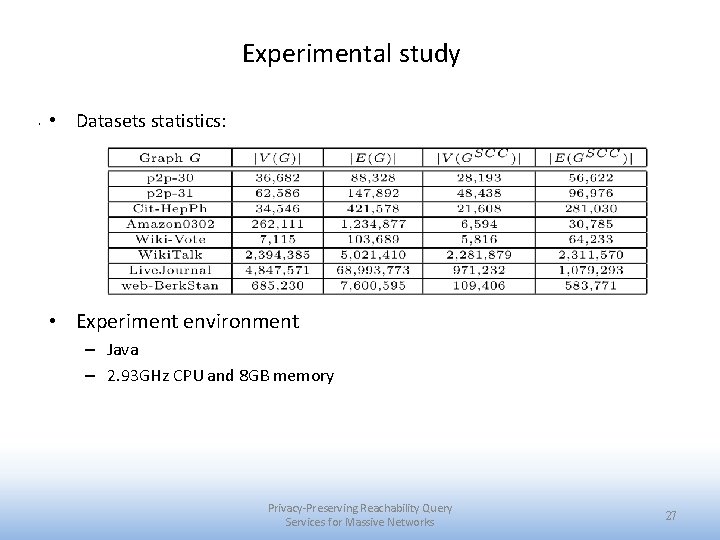
Experimental study. • Datasets statistics: • Experiment environment – Java – 2. 93 GHz CPU and 8 GB memory Privacy-Preserving Reachability Query Services for Massive Networks 27
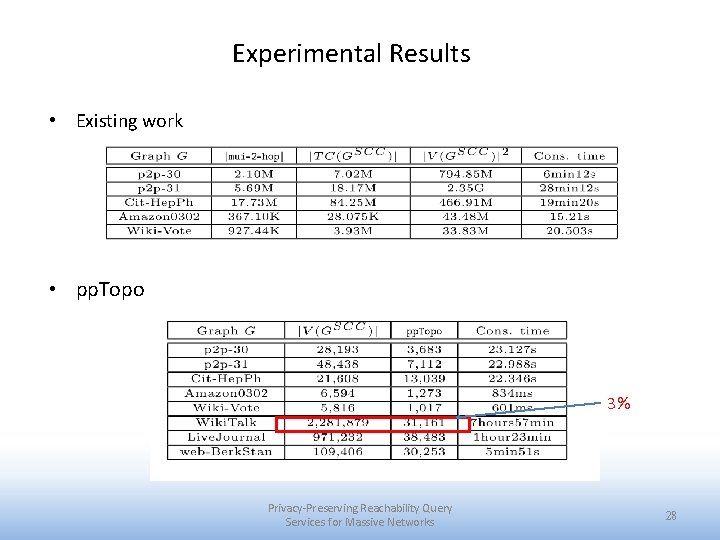
Experimental Results • Existing work • pp. Topo 3% Privacy-Preserving Reachability Query Services for Massive Networks 28
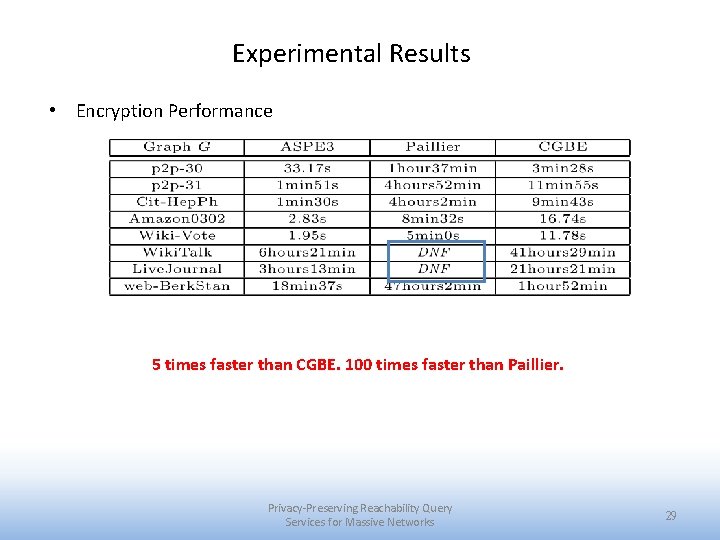
Experimental Results • Encryption Performance 5 times faster than CGBE. 100 times faster than Paillier. Privacy-Preserving Reachability Query Services for Massive Networks 29
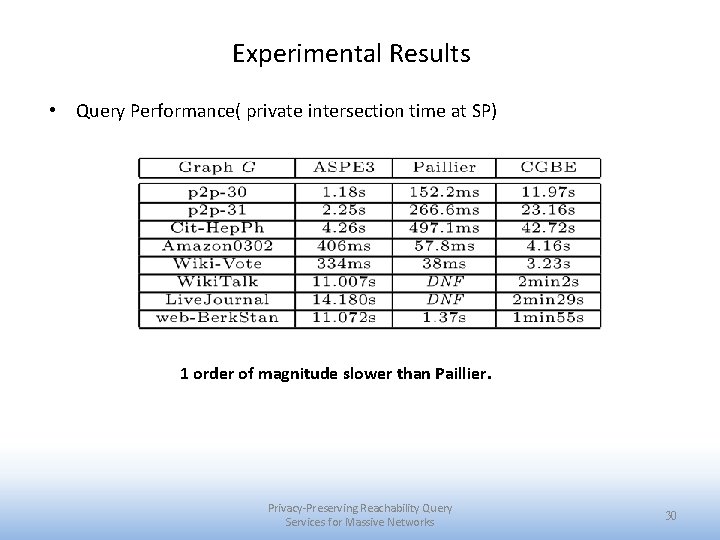
Experimental Results • Query Performance( private intersection time at SP) 1 order of magnitude slower than Paillier. Privacy-Preserving Reachability Query Services for Massive Networks 30
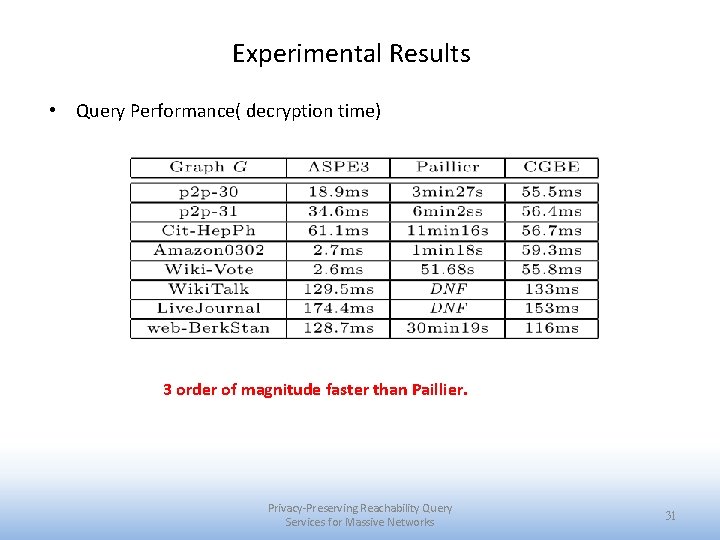
Experimental Results • Query Performance( decryption time) 3 order of magnitude faster than Paillier. Privacy-Preserving Reachability Query Services for Massive Networks 31
Conclusions • This paper is the first work that can construct privacy-preserving index for reachability query over large networks. • Private reachability query processing is done by private intersections. (ASPE 3) • Our techniques are efficient and effective on large networks. • ASPE 3 is efficient compared with related encryptions including Paillier and CGBE. Privacy-Preserving Reachability Query Services for Massive Networks 32
Future works • Label-constraint reachability queries • Privacy-preserving queries like BFS or DFS in bounded hops. Privacy-Preserving Reachability Query Services for Massive Networks 33
![References I [1] J. Cai and C. K. Poon. Path-hop: efficiently indexing large graphs References I [1] J. Cai and C. K. Poon. Path-hop: efficiently indexing large graphs](http://slidetodoc.com/presentation_image_h/dec005c079d98496aad601dddf2c0d8d/image-33.jpg)
References I [1] J. Cai and C. K. Poon. Path-hop: efficiently indexing large graphs for reachability queries. In CIKM, pages 119– 128, 2010. [2] N. Cao, Z. Yang, C. Wang, K. Ren, and W. Lou. Privacy-preserving query over encrypted graph-structured data in cloud computing. In ICDCS, pages 393– 402, 2011. [3] J. Cheng, S. Huang, H. Wu, and A. Fu. Tf-label: a topological-folding labeling scheme for reachabilityquerying in a large graph. In SIGMOD, pages 193 – 204, 2013. [4] E. Cohen, E. Halperin, H. Kaplan, and U. Zwick. Reachability and distance queries via 2 -hop labels. In SODA, 2002. [5] J. Gao, J. X. Yu, R. Jin, J. Zhou, T. Wang, and D. Yang. Neighborhoodprivacy protected shortest distance computing in cloud. In SIGMOD, 2011. [6] X. He, J. Vaidya, B. Shafiq, N. Adam, and X. Lin. Reachability analysis in privacy-preserving perturbed graphs. In WI-IAT, pages 691– 694, 2010. Privacy-Preserving Reachability Query Services for Massive Networks 34
![References II [7] R. Jin, N. Ruan, Y. Xiang, and H. Wang. Path-tree: An References II [7] R. Jin, N. Ruan, Y. Xiang, and H. Wang. Path-tree: An](http://slidetodoc.com/presentation_image_h/dec005c079d98496aad601dddf2c0d8d/image-34.jpg)
References II [7] R. Jin, N. Ruan, Y. Xiang, and H. Wang. Path-tree: An efficient reachability indexing scheme for large directed graphs. TODS, pages 7: 1– 7: 44, 2011. [8] K. Mouratidis and M. L. Yiu. Shortest path computation with no information leakage. PVLDB, 5(8): 692– 703, 2012. [9] S. Seufert, A. Anand, S. Bedathur, and G. Weikum. Ferrari: Flexible and efficient reachability range assignment for graph indexing. In ICDE, pages 1009 – 1020, 2013. [10] P. Yi, Z. Fan, and S. Yin. Privacy-preserving reachability query services for sparse graphs. In ICDE Workshops (GDM), pages 32– 35, 2014. [11] S. Yin, Z. Fan, P. Yi, B. Choi, J. Xu, and S. Zhou. Privacy-preserving reachability query services. In DASFAA, pages 203– 219, 2014. Privacy-Preserving Reachability Query Services for Massive Networks 35
Thank You! Privacy-Preserving Reachability Query Services for Massive Networks 36
- Slides: 35