PrivacyFriendly and Trustworthy Identity Management with AttributeBased Credentials

Privacy-Friendly and Trustworthy Identity Management with Attribute-Based Credentials NITC / SEARCC Conference 2017 Colombo, Sri Lanka 2017 -09 -14 Prof. Dr. Kai Rannenberg Deutsche Telekom Chair of Mobile Business & Multilateral Security Goethe University Frankfurt www. m-chair. de
…… Agenda § Privacy (and security) issues of typical federated Identity Management architectures § Identity Management and Overidentification § Identity Assurance and the “Calling Home” problem § Solution approaches § Partial Identities § Attribute Based Credentials (Privacy-ABCs) § Application examples § Using Privacy-ABCs in the ABC 4 Trust Project § Redactable Signatures for Cloud Identity Management § Conclusions & Outlook . . . 2
…… Agenda § Privacy (and security) issues of typical federated Identity Management architectures § Identity Management and Overidentification § Identity Assurance and the “Calling Home” problem § Solution approaches § Partial Identities § Attribute Based Credentials (Privacy-ABCs) § Application examples § Using Privacy-ABCs in the ABC 4 Trust Project § Redactable Signatures for Cloud Identity Management § Conclusions & Outlook . . . 3
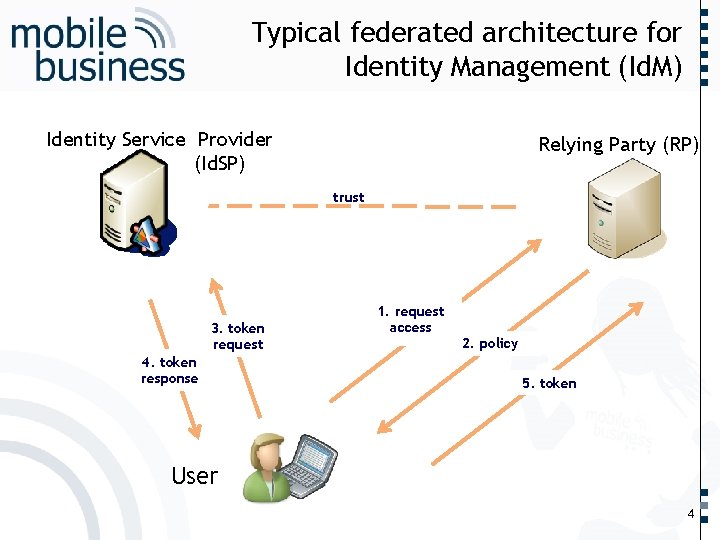
Identity Service Provider (Id. SP) …… Typical federated architecture for Identity Management (Id. M) Relying Party (RP) trust 3. token request 4. token response 2. policy 5. token . . . User 1. 1. request Request access 4
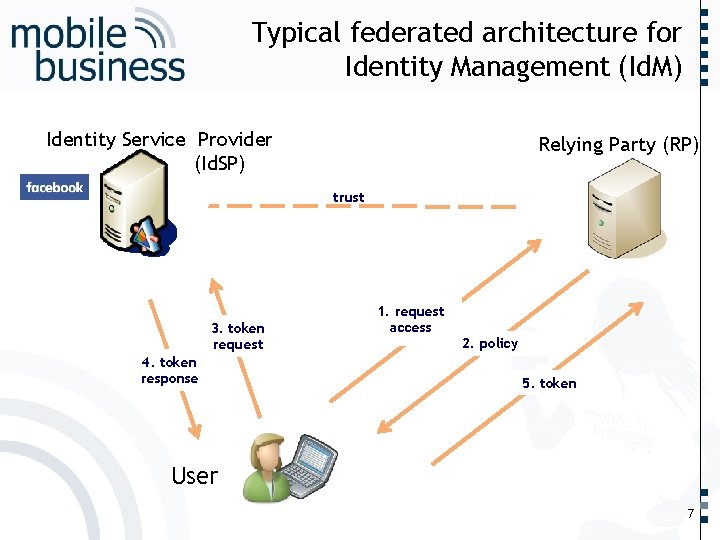
Identity Service Provider (Id. SP) …… Typical federated architecture for Identity Management (Id. M) Relying Party (RP) trust 3. token request 4. token response 2. policy 5. token . . . User 1. 1. request Request access 7
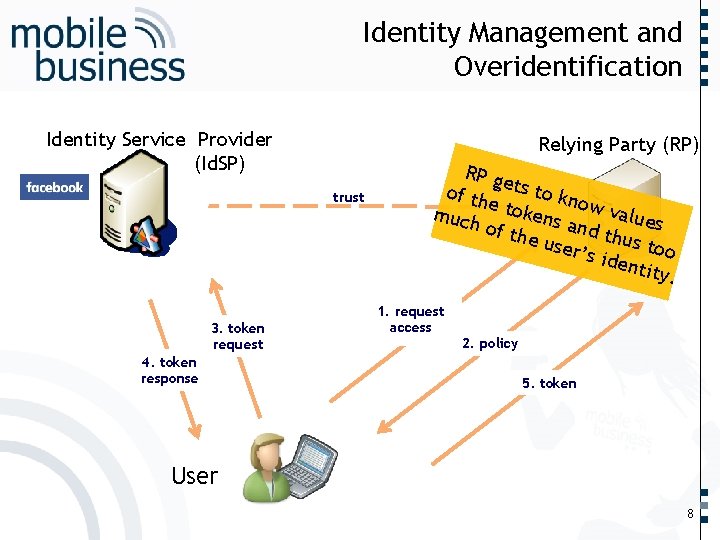
Identity Service Provider (Id. SP) Relying Party (RP) trust 3. token request 4. token response RP g of th ets to kn o e much tokens w values and t of th hus t e use oo r’s id entit y. 1. 1. request Request access 2. policy 5. token . . . User …… Identity Management and Overidentification 8
…… Agenda § Privacy (and security) issues of typical federated Identity Management architectures § Identity Management and Overidentification § Identity Assurance and the “Calling Home” problem § Solution approaches § Partial Identities § Attribute Based Credentials (Privacy-ABCs) § Application examples § Using Privacy-ABCs in the ABC 4 Trust Project § Redactable Signatures for Cloud Identity Management § Conclusions & Outlook . . . 9
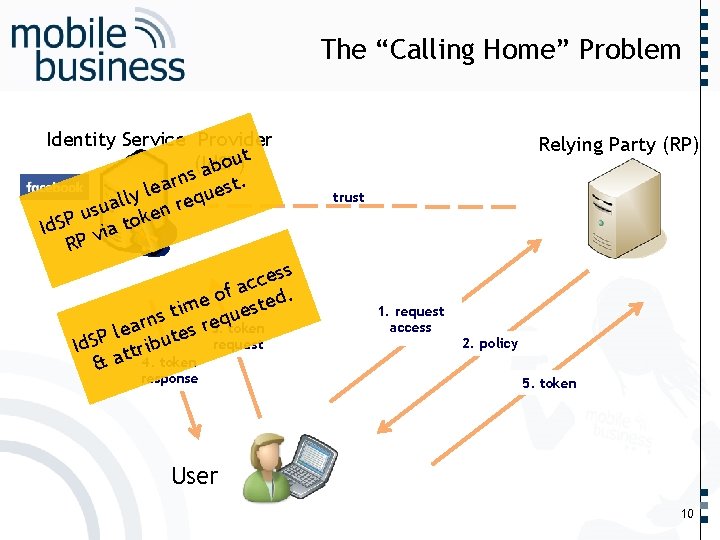
Identity Service Provider ut o (Id. SP) b s a t. n r a le es u y l q l re ua s n u e k Id. SP via to RP ess c c of a ted. e tim ques s n e token r 3. ar e s l e t request Id. SP ttribu & a 4. token response Relying Party (RP) trust 1. 1. request Request access 2. policy 5. token . . . User …… The “Calling Home” Problem 10
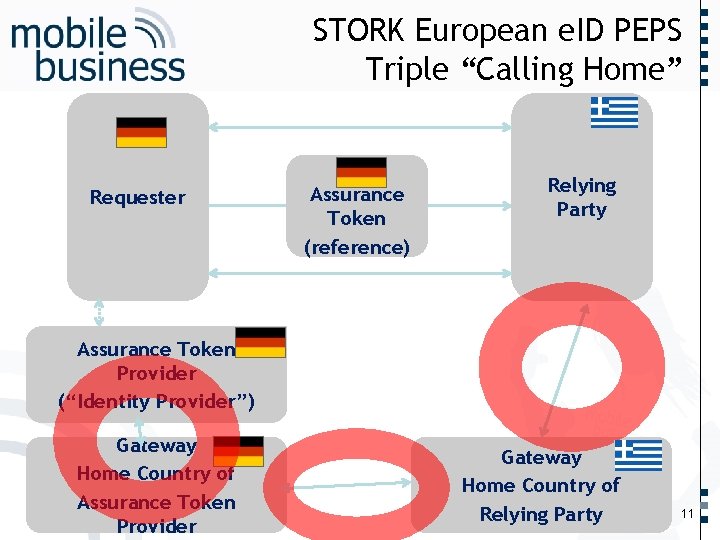
Requester Assurance Token (reference) …… STORK European e. ID PEPS Triple “Calling Home” Relying Party Assurance Token Provider (“Identity Provider”) Gateway Home Country of Relying Party . . . Gateway Home Country of Assurance Token Provider 11
…… Agenda § Privacy (and security) issues of typical federated Identity Management architectures § Identity Management and Overidentification § Identity Assurance and the “Calling Home” problem § Solution approaches § Partial Identities § Attribute Based Credentials (Privacy-ABCs) § Application examples § Using Privacy-ABCs in the ABC 4 Trust Project § Redactable Signatures for Cloud Identity Management § Conclusions & Outlook . . . 12
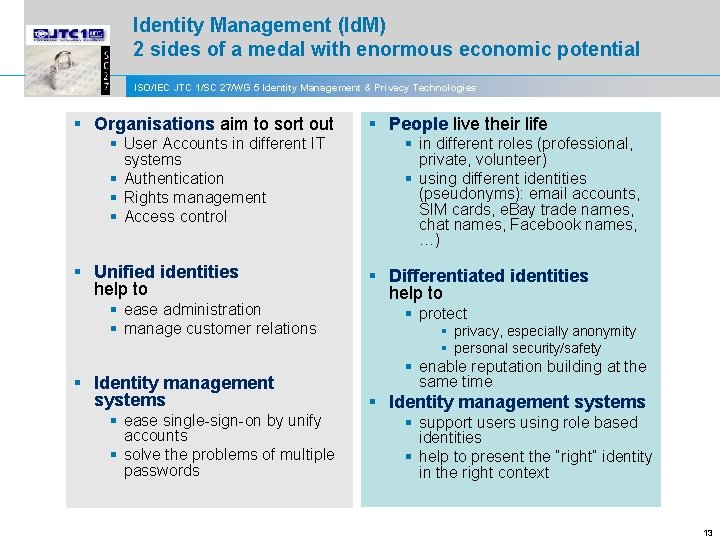
Identity Management (Id. M) 2 sides of a medal with enormous economic potential ISO/IEC JTC 1/SC 27/WG 5 Identity Management & Privacy Technologies § Organisations aim to sort out § User Accounts in different IT systems § Authentication § Rights management § Access control § Unified identities help to § ease administration § manage customer relations § Identity management systems § ease single-sign-on by unify accounts § solve the problems of multiple passwords § People live their life § in different roles (professional, private, volunteer) § using different identities (pseudonyms): email accounts, SIM cards, e. Bay trade names, chat names, Facebook names, …) § Differentiated identities help to § protect § privacy, especially anonymity § personal security/safety § enable reputation building at the same time § Identity management systems § support users using role based identities § help to present the “right” identity in the right context 13
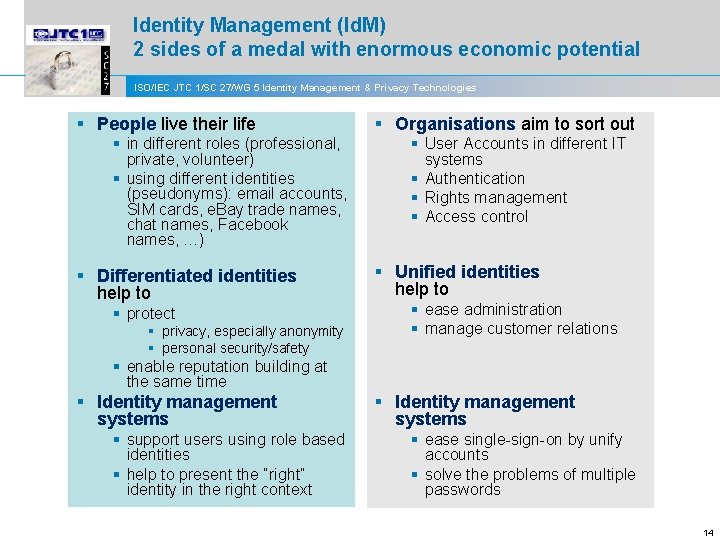
Identity Management (Id. M) 2 sides of a medal with enormous economic potential ISO/IEC JTC 1/SC 27/WG 5 Identity Management & Privacy Technologies § People live their life § in different roles (professional, private, volunteer) § using different identities (pseudonyms): email accounts, SIM cards, e. Bay trade names, chat names, Facebook names, …) § Differentiated identities help to § protect § privacy, especially anonymity § personal security/safety § Organisations aim to sort out § User Accounts in different IT systems § Authentication § Rights management § Access control § Unified identities help to § ease administration § manage customer relations § enable reputation building at the same time § Identity management systems § support users using role based identities § help to present the “right” identity in the right context § Identity management systems § ease single-sign-on by unify accounts § solve the problems of multiple passwords 14
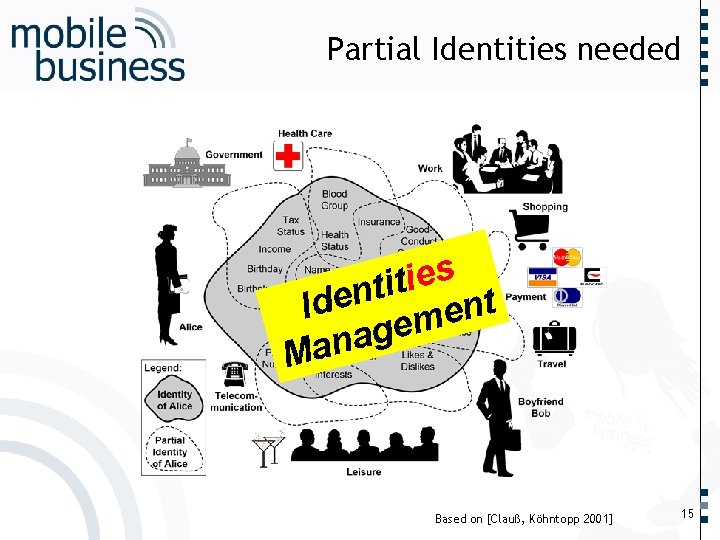
…… Partial Identities needed s e i t n e t Id n e m e g a n a M . . . Based on [Clauß, Köhntopp 2001] 15
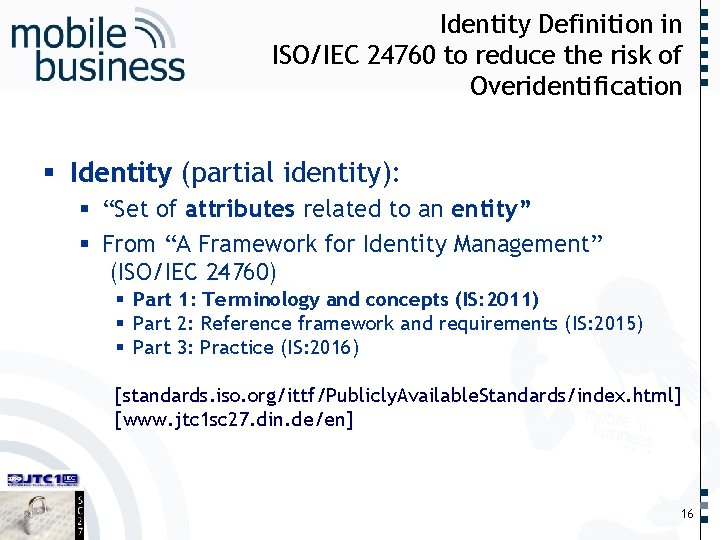
…… Identity Definition in ISO/IEC 24760 to reduce the risk of Overidentification § Identity (partial identity): § “Set of attributes related to an entity” § From “A Framework for Identity Management” (ISO/IEC 24760) § Part 1: Terminology and concepts (IS: 2011) § Part 2: Reference framework and requirements (IS: 2015) § Part 3: Practice (IS: 2016) [standards. iso. org/ittf/Publicly. Available. Standards/index. html] [www. jtc 1 sc 27. din. de/en] . . . 16
…… Agenda § Privacy (and security) issues of typical federated Identity Management architectures § Identity Management and Overidentification § Identity Assurance and the “Calling Home” problem § Solution approaches § Partial Identities § Attribute Based Credentials (Privacy-ABCs) § Application examples § Using Privacy-ABCs in the ABC 4 Trust Project § Redactable Signatures for Cloud Identity Management § Conclusions & Outlook . . . 17
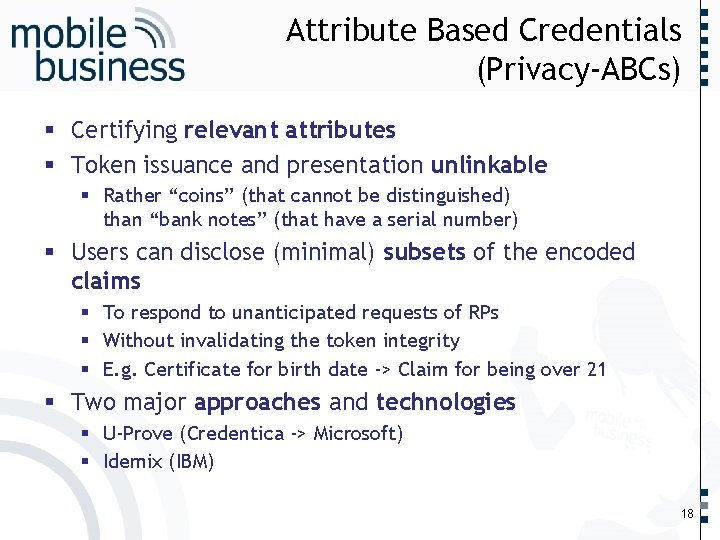
…… Attribute Based Credentials (Privacy-ABCs) § Certifying relevant attributes § Token issuance and presentation unlinkable § Rather “coins” (that cannot be distinguished) than “bank notes” (that have a serial number) § Users can disclose (minimal) subsets of the encoded claims § To respond to unanticipated requests of RPs § Without invalidating the token integrity § E. g. Certificate for birth date -> Claim for being over 21 § Two major approaches and technologies § U-Prove (Credentica -> Microsoft) § Idemix (IBM) . . . 18
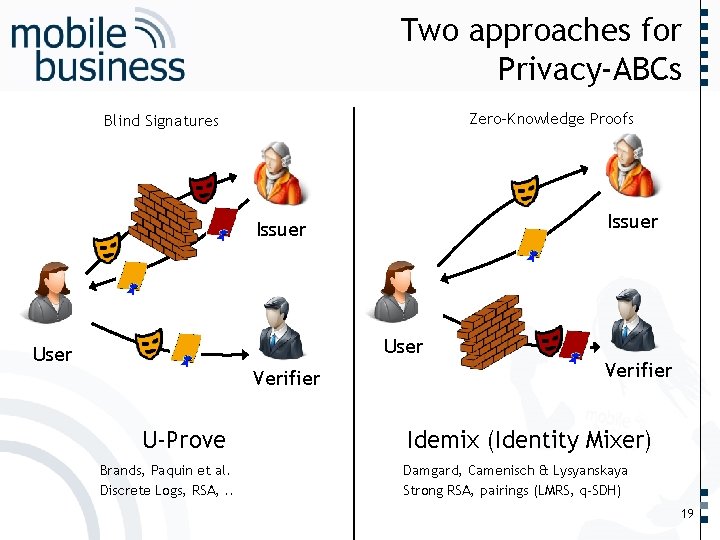
…… Two approaches for Privacy-ABCs Zero-Knowledge Proofs Blind Signatures Issuer User Verifier U-Prove Idemix (Identity Mixer) Damgard, Camenisch & Lysyanskaya Strong RSA, pairings (LMRS, q-SDH) . . . Brands, Paquin et al. Discrete Logs, RSA, . . Verifier 19
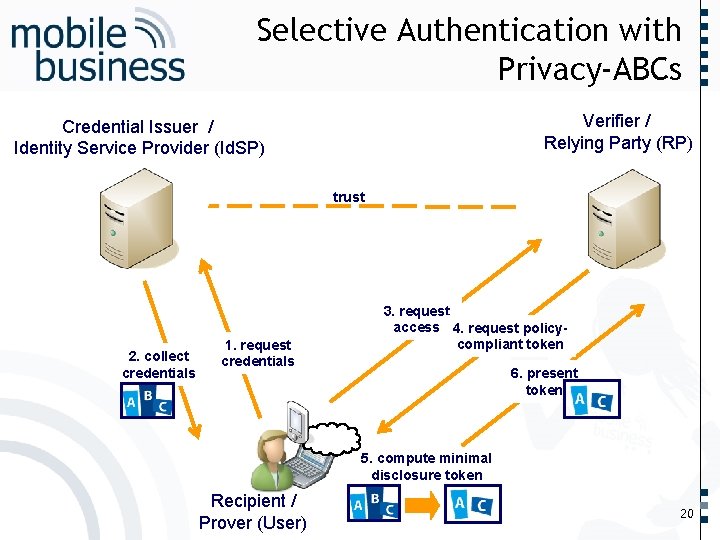
…… Selective Authentication with Privacy-ABCs Verifier / Relying Party (RP) Credential Issuer / Identity Service Provider (Id. SP) trust 2. collect credentials 1. request credentials 3. request access 4. request policycompliant token 6. present token 5. compute minimal disclosure token . . . Recipient / Prover (User) 20
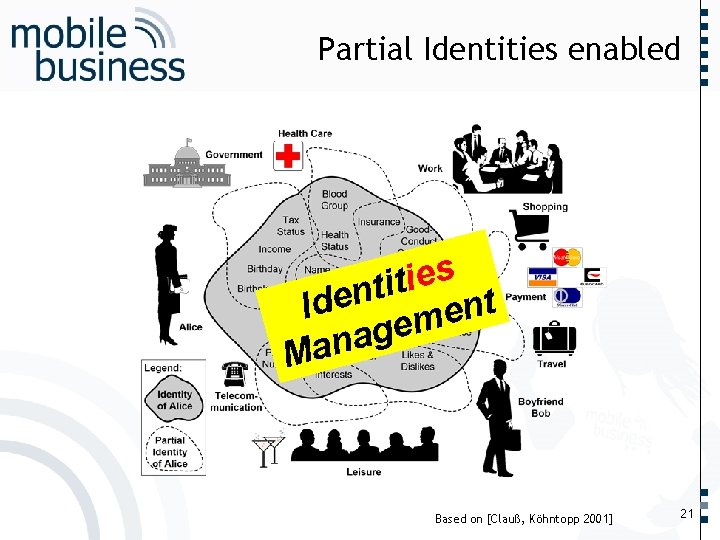
…… Partial Identities enabled s e i t n e t Id n e m e g a n a M . . . Based on [Clauß, Köhntopp 2001] 21
…… Agenda § Privacy (and security) issues of typical federated Identity Management architectures § Identity Management and Overidentification § Identity Assurance and the “Calling Home” problem § Solution approaches § Partial Identities § Attribute Based Credentials (Privacy-ABCs) § Application examples § Using Privacy-ABCs in the ABC 4 Trust Project § Redactable Signatures for Cloud Identity Management § Conclusions & Outlook . . . 22
…… ABC 4 Trust Objectives § A common, unified architecture for ABC systems to enable § Comparing their respective features § Combining them on common platforms § “Lock-In” free usage of ABC systems § Open reference implementations of selected ABC systems § Deployments in actual production enabling § Minimal disclosure § Provision of anonymous feedback to a community to one is accredited as a member § Relevant Standards § e. g. in ISO/IEC JTC 1/SC 27/WG 5 “Identity Management and Privacy Technologies” . . . 23
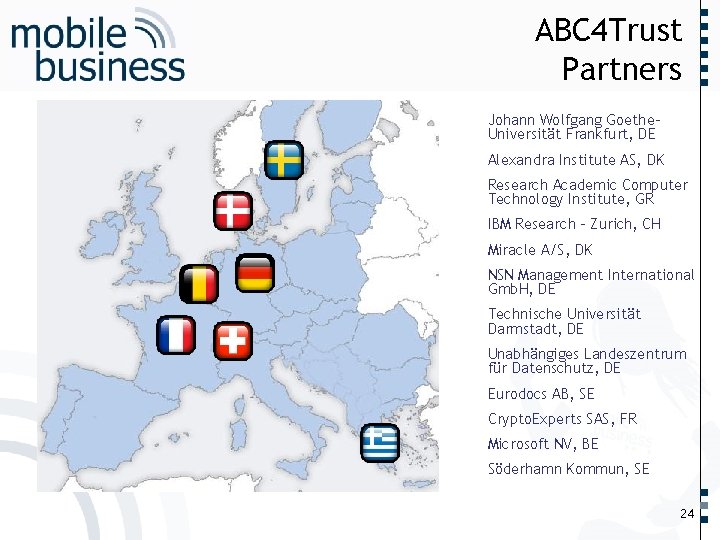
…… ABC 4 Trust Partners Johann Wolfgang Goethe. Universität Frankfurt, DE Alexandra Institute AS, DK Research Academic Computer Technology Institute, GR IBM Research - Zurich, CH Miracle A/S, DK NSN Management International Gmb. H, DE Technische Universität Darmstadt, DE Unabhängiges Landeszentrum für Datenschutz, DE Eurodocs AB, SE Crypto. Experts SAS, FR Microsoft NV, BE Söderhamn Kommun, SE . . . 24
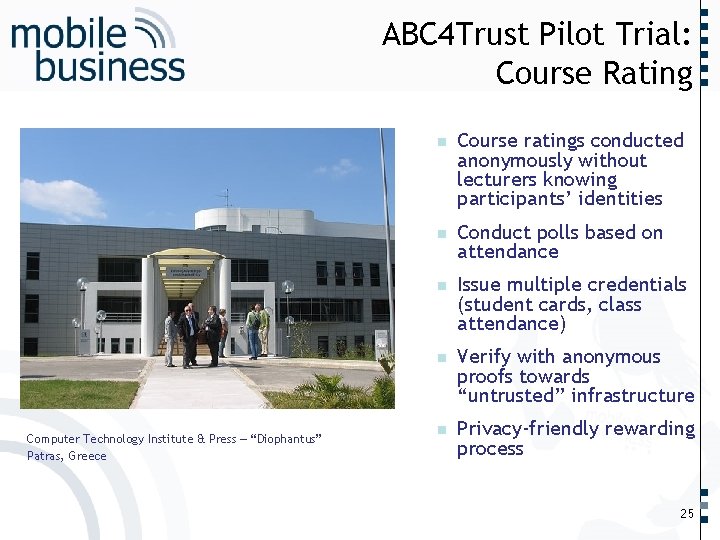
…… ABC 4 Trust Pilot Trial: Course Rating Computer Technology Institute & Press – “Diophantus” Patras, Greece n Course ratings conducted anonymously without lecturers knowing participants’ identities n Conduct polls based on attendance n Issue multiple credentials (student cards, class attendance) n Verify with anonymous proofs towards “untrusted” infrastructure n Privacy-friendly rewarding process . . . 25
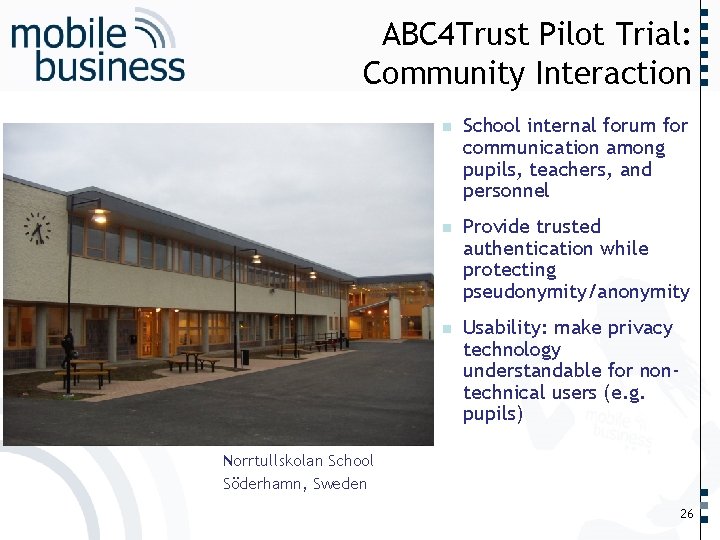
…… ABC 4 Trust Pilot Trial: Community Interaction School internal forum for communication among pupils, teachers, and personnel n Provide trusted authentication while protecting pseudonymity/anonymity n Usability: make privacy technology understandable for nontechnical users (e. g. pupils) . . . Norrtullskolan School Söderhamn, Sweden n 26
![Issuer …… ABC 4 Trust Architecture Entities and Interactions Revocation Authority [Optional] Credential Revocation Issuer …… ABC 4 Trust Architecture Entities and Interactions Revocation Authority [Optional] Credential Revocation](http://slidetodoc.com/presentation_image/ffd08ec40bd87e914a7279c8a0c29313/image-27.jpg)
Issuer …… ABC 4 Trust Architecture Entities and Interactions Revocation Authority [Optional] Credential Revocation info retrieval Credential Issuance Revocation Info Retrieval User Presentation Token Inspector [Optional] Token Inspection Relying Party (Verifier) . . . 27
…… Agenda § Privacy (and security) issues of typical federated Identity Management architectures § Identity Management and Overidentification § Identity Assurance and the “Calling Home” problem § Solution approaches § Partial Identities § Attribute Based Credentials (Privacy-ABCs) § Application examples § Using Privacy-ABCs in the ABC 4 Trust Project § Redactable Signatures for Cloud Identity Management § Conclusions & Outlook . . . 28
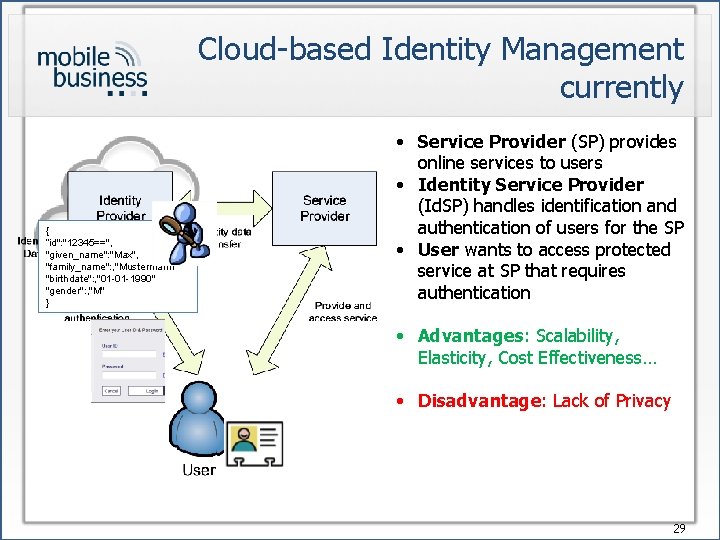
Cloud-based Identity Management currently { “id": "12345==", "given_name": "Max", "family_name": , "Mustermann" "birthdate": , "01 -01 -1990" "gender": , "M" } • Service Provider (SP) provides online services to users • Identity Service Provider (Id. SP) handles identification and authentication of users for the SP • User wants to access protected service at SP that requires authentication • Advantages: Scalability, Elasticity, Cost Effectiveness… • Disadvantage: Lack of Privacy 29
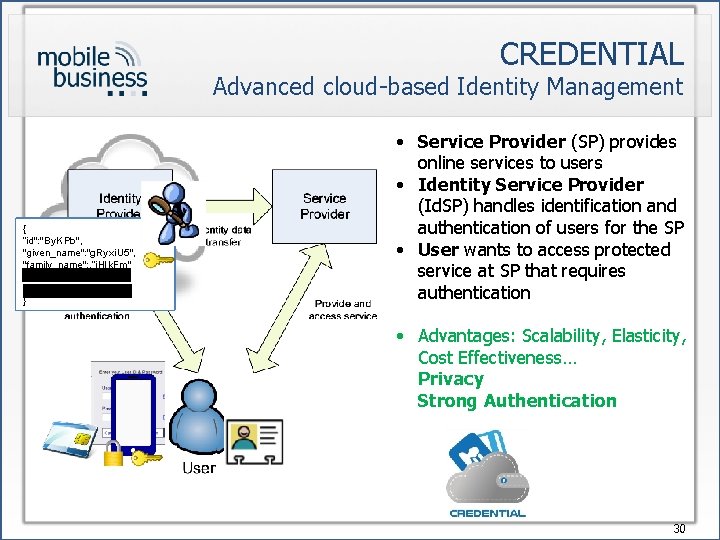
CREDENTIAL Advanced cloud-based Identity Management {{ “id": "12345==", “id": "By. KPb", "given_name": "Max", "given_name": "g. Ryxi. U 5", "family_name": , "Mustermann" "family_name": , “j. Hlk. Fm" "birthdate": , "01 -01 -1990" "birthdate": , “df. GTr. Fd" "gender": , "M" "gender": , “Lm. No. P" }} • Service Provider (SP) provides online services to users • Identity Service Provider (Id. SP) handles identification and authentication of users for the SP • User wants to access protected service at SP that requires authentication • Advantages: Scalability, Elasticity, Cost Effectiveness… Privacy Strong Authentication 30
…… Agenda § Privacy (and security) issues of typical federated Identity Management architectures § Identity Management and Overidentification § Identity Assurance and the “Calling Home” problem § Solution approaches § Partial Identities § Attribute Based Credentials (Privacy-ABCs) § Application examples § Using Privacy-ABCs in the ABC 4 Trust Project § Redactable Signatures for cloud-based Identity Management . . . § Conclusions & Outlook 31
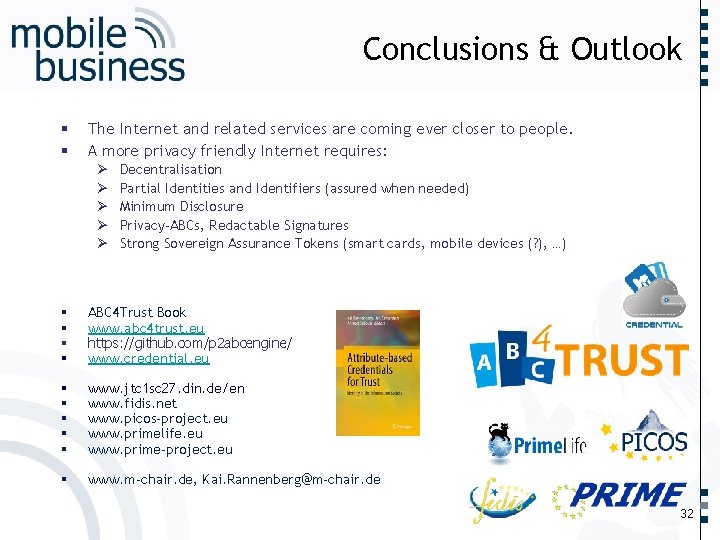
§ § …… Conclusions & Outlook The Internet and related services are coming ever closer to people. A more privacy friendly Internet requires: Ø Ø Ø Decentralisation Partial Identities and Identifiers (assured when needed) Minimum Disclosure Privacy-ABCs, Redactable Signatures Strong Sovereign Assurance Tokens (smart cards, mobile devices (? ), …) ABC 4 Trust Book www. abc 4 trust. eu https: //github. com/p 2 abcengine/ www. credential. eu § § § www. jtc 1 sc 27. din. de/en www. fidis. net www. picos-project. eu www. primelife. eu www. prime-project. eu § www. m-chair. de, Kai. Rannenberg@m-chair. de . . . § § 32

…… Deutsche Telekom Chair of Mobile Business & Multilateral Security Prof. Dr. Kai Rannenberg Goethe University Frankfurt Theodor-Adorno-Platz 4 60629 Frankfurt, Germany . . . Phone +49 (0)69 798 34701 Fax +49 (0)69 798 35004 33
References 1 § § § ABC 4 Trust: www. abc 4 trust. eu § Sebastian Clauß, Marit Köhntopp: Identity management and its support of multilateral security. Computer Networks, Volume 37, Issue 2, October 2001, Pages 205 -219 § § FIDIS: Future of Identity in the Information Society; www. fidis. net § Ioannis Krontiris, Herbert Leitold, Reinhard Posch, Kai Rannenberg: e. ID Interoperability; Pp. 167 -186 in: Walter Fumy, Manfred Paeschke (Eds. ): Handbook of e. ID Security – Concepts, Practical Experiences, Technologies, Publicis, ISBN 978 -3 -89578 -379 -1 § § ISO/IEC JTC 1/SC 27/WG 5: Identity Management and Privacy Technologies; www. jtc 1 sc 27. din. de ABC 4 Trust video: https: //abc 4 trust. eu/index. php/press/2011 -11 -08 -14 -42 -18 Kim Cameron, Reinhard Posch, Kai Rannenberg: Proposal for a common identity framework: A User-Centric Identity Metasystem; Pp. 477 – 500 in [Rannenberg, Royer, Deuker 2009] Christian Kahl, Katja Böttcher, Markus Tschersich, Stephan Heim, Kai Rannenberg: How to enhance Privacy and Identity Management for Mobile Communities: Approach and User driven Concepts of the PICOS Project; Pp. 277 -288 in: Kai Rannenberg, Vijay Varadharajan, Christian Weber: Security and Privacy – Silver Linings in the Cloud; Proceedings of 25 th IFIP International Information Security Conference (IFIP SEC 2010), 20 -23 September 2010, Brisbane, Australia, Springer IFIP Advances in Information and Communication Technology Series, Vol. 330, ISBN 978 -3 -642 -15256 -6 PICOS: Privacy and Identity Management for Community Services; www. picos-project. eu PRIME: Privacy and Identity Management for Europe; www. prime-project. eu Prime. Life: Privacy and Identity Management for Life; www. primelife. eu 34
References 2 § Kai Rannenberg: Multilateral Security – A concept and examples for balanced security; Pp. 151 -162 in: Proceedings of the 9 th ACM New Security Paradigms Workshop 2000, September 19 -21, 2000 Cork, Ireland; ACM Press; ISBN 1 -58113 -260 -3 § Kai Rannenberg: Cam. Web. Sim and Friends: Steps towards Personal Security Assistants; Pp. 173 - 176 in Viktor Seige et al. : The Trends and Challenges of Modern Financial Services – Proceedings of the Information Security Summit; May 29 -30, 2002, Prague; Tate International; ISBN 80 -902858 -5 -6 § Kai Rannenberg: Identity management in mobile cellular networks and related applications; Information Security Technical Report; Vol. 9, No. 1; 2004; pp. 77 – 85; ISSN 1363 -4127 § Kai Rannenberg, Jan Camenisch, Ahmad Sabouri: Attribute-based Credentials for Trust - Identity in the Information Society– § Kai Rannenberg, Denis Royer, Andre Deuker: The Future of Identity in the Information Society – Opportunities and Challenges; Springer 2009, ISBN 978 -3 -540 -88480 -4 § § Deutsche Telekom Chair for Mobile Business & Multilateral Security; www. m-chair. de § Jan Zibuschka, Lothar Fritsch, Mike Radmacher, Tobias Scherner, Kai Rannenberg: Enabling Privacy of Real -Life LBS: A Platform for Flexible Mobile Service Provisioning; in Proceedings of the 22 nd IFIP TC-11 International Information Security Conference 2007; 14 -16 May 2007, Sandton, South Africa; Springer IFIP Series Daniel Villatoro, Jetzabel Serna, Víctor Rodríguez, Marc Torrent-Moreno: The Tweet. Beat of the City: Microblogging Used for Discovering Behavioural Patterns during the MWC 2012; p. P. 43 -56 in: Jordi Nin, Daniel Villatoro: Citizen in Sensor Networks; LFirst International Workshop, Citi. Sens 2012, Montpellier, France, August 27, 2012, Revised Selected Papers, Lecture Notes in Computer Science, Volume 7685, 2013 35
About the speaker “Master” TU Berlin (Dipl. -Inform. ) 1989 Technical data protection in distributed systems Ph. D: Freiburg University (Dr. rer. pol. ) 1997 “Criteria and Certification of multilateral IT-Security“ -> Standardization at ISO/IEC JTC 1/SC 27 and DIN NI-27 Kolleg “Sicherheit in der Kommunikationstechnik“ Gottlieb Daimler- and Karl Benz-Foundation 1993 – 1999 -> Multilateral Security: “Empowering Users, Enabling Applications“ Microsoft Research Cambridge 1999 – 2002 Goethe University Frankfurt since 2002 ISO/IEC JTC 1/SC 27/WG 5 since 2006: Identity Management and Privacy Technologies 36
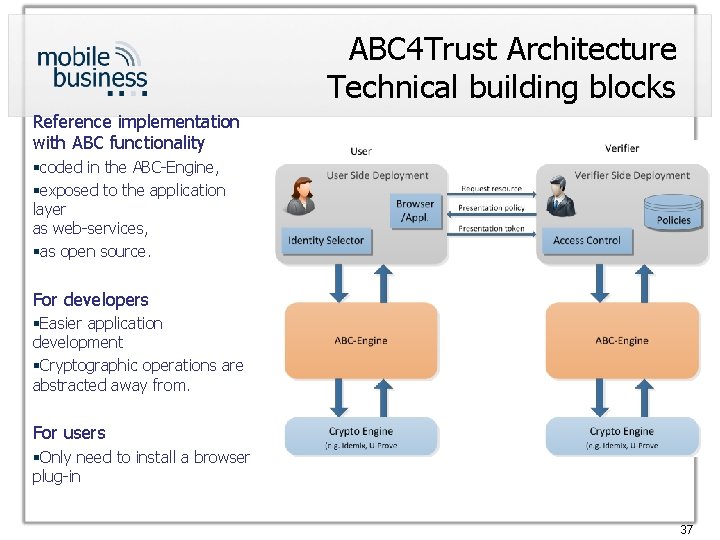
ABC 4 Trust Architecture Technical building blocks Reference implementation with ABC functionality §coded in the ABC-Engine, §exposed to the application layer as web-services, §as open source. For developers §Easier application development §Cryptographic operations are abstracted away from. For users §Only need to install a browser plug-in 37
§ Unification of features ABC 4 Trust Architecture Characteristics § Selective disclosure, pseudonymity, unlinkability, … § XML specification of the data exchange between e. g. Issuer, User, Verifier, Revocation Authority § Crypto Architecture § Allows seamless integration of cryptographic primitives § Encapsulated in components with common interfaces, allowing the rest of the cryptographic layer to be implementation-agnostic § Users can § obtain credentials for more than one Privacy-ABC technology and § use them on the same hardware and software platforms. § Service providers and Identity Service Providers can § adopt whatever Privacy-ABC technology best suits their needs. § Open source implementation available on Github Ø Avoid technology lock-in Ø Raise trust in Privacy-ABC technologies 38
ABC 4 Trust @Git. Hub § https: //github. com/p 2 abcen gine/ § Source codes available under Apache license § Documentation, installation guide and wiki pages 39
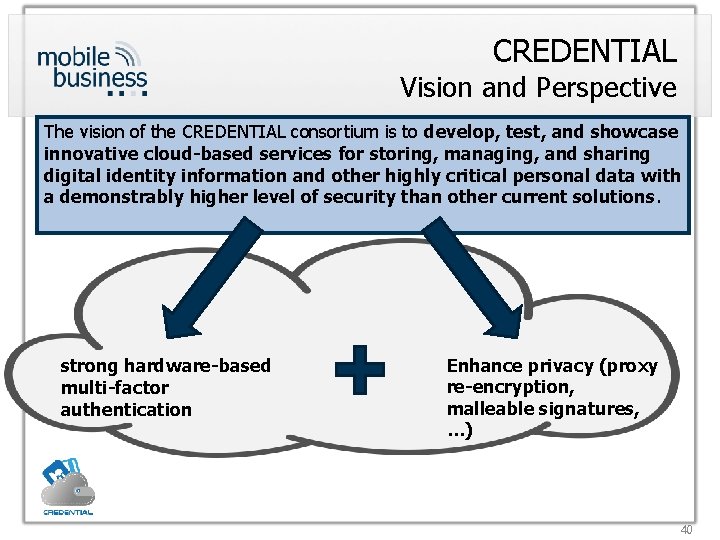
CREDENTIAL Vision and Perspective The vision of the CREDENTIAL consortium is to develop, test, and showcase innovative cloud-based services for storing, managing, and sharing digital identity information and other highly critical personal data with a demonstrably higher level of security than other current solutions. strong hardware-based multi-factor authentication Enhance privacy (proxy re-encryption, malleable signatures, …) 40
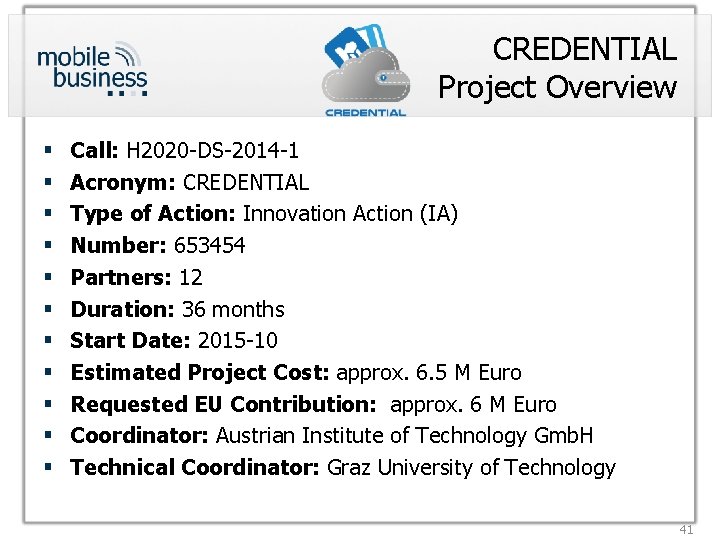
CREDENTIAL Project Overview § § § Call: H 2020 -DS-2014 -1 Acronym: CREDENTIAL Type of Action: Innovation Action (IA) Number: 653454 Partners: 12 Duration: 36 months Start Date: 2015 -10 Estimated Project Cost: approx. 6. 5 M Euro Requested EU Contribution: approx. 6 M Euro Coordinator: Austrian Institute of Technology Gmb. H Technical Coordinator: Graz University of Technology 41
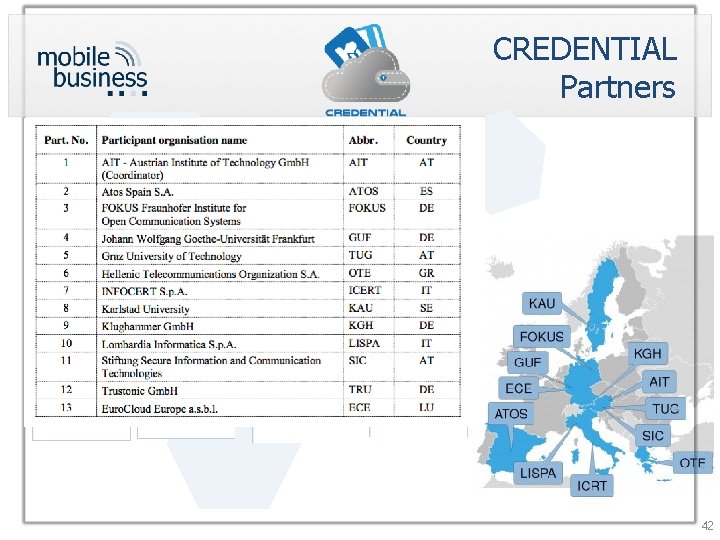
CREDENTIAL Partners 42
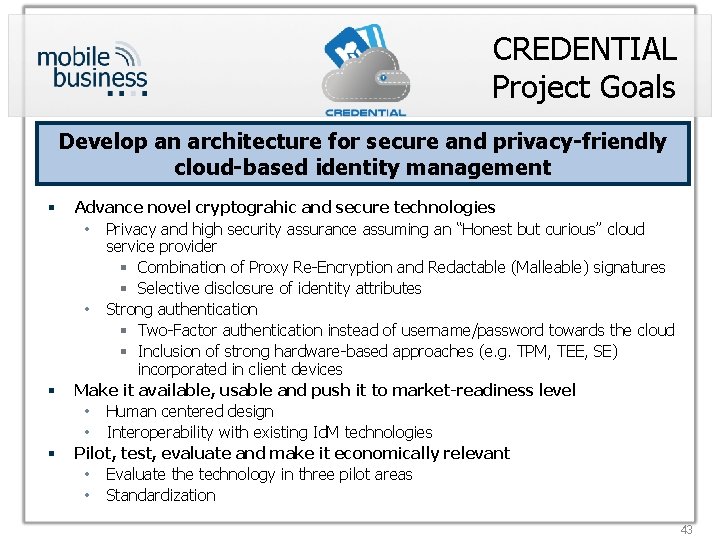
CREDENTIAL Project Goals Develop an architecture for secure and privacy-friendly cloud-based identity management § § § Advance novel cryptograhic and secure technologies • Privacy and high security assurance assuming an “Honest but curious” cloud service provider § Combination of Proxy Re-Encryption and Redactable (Malleable) signatures § Selective disclosure of identity attributes • Strong authentication § Two-Factor authentication instead of username/password towards the cloud § Inclusion of strong hardware-based approaches (e. g. TPM, TEE, SE) incorporated in client devices Make it available, usable and push it to market-readiness level • Human centered design • Interoperability with existing Id. M technologies Pilot, test, evaluate and make it economically relevant • Evaluate the technology in three pilot areas • Standardization 43
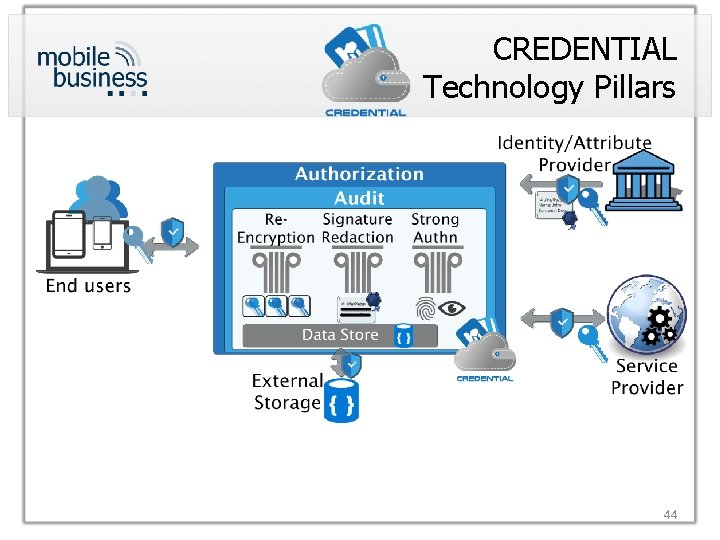
CREDENTIAL Technology Pillars 44
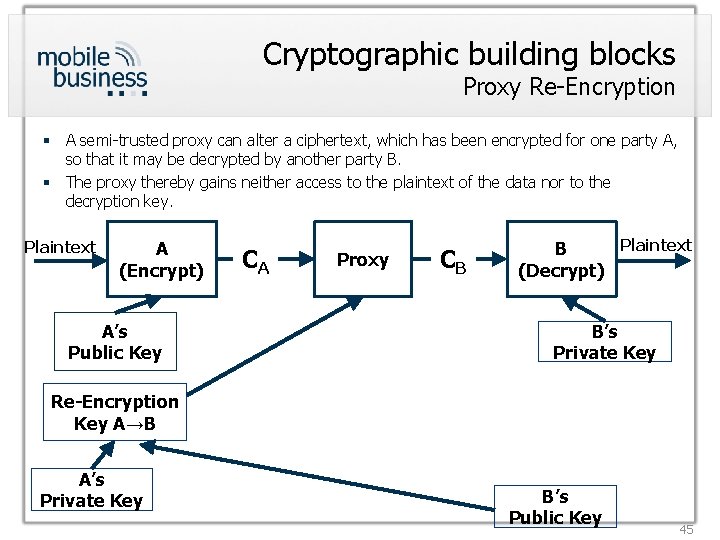
Cryptographic building blocks Proxy Re-Encryption § A semi-trusted proxy can alter a ciphertext, which has been encrypted for one party A, so that it may be decrypted by another party B. § The proxy thereby gains neither access to the plaintext of the data nor to the decryption key. Plaintext A (Encrypt) A’s Public Key CA Proxy CB Plaintext B (Decrypt) B’s Private Key Re-Encryption Key A→B A’s Private Key B’s Public Key 45
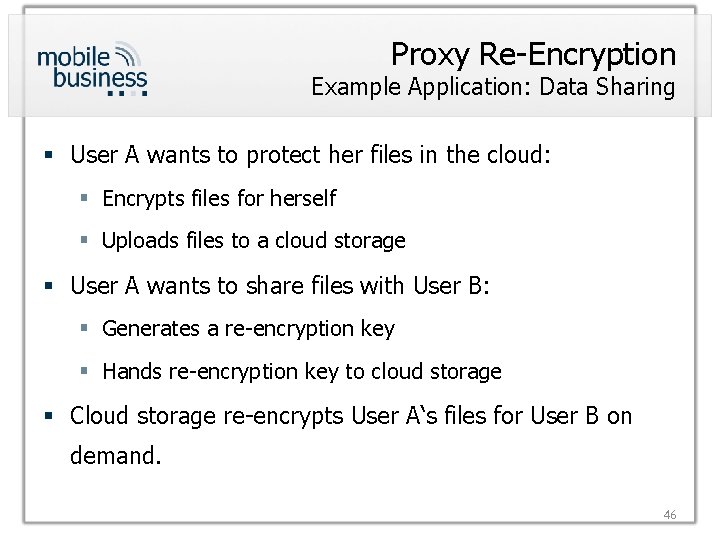
Proxy Re-Encryption Example Application: Data Sharing § User A wants to protect her files in the cloud: § Encrypts files for herself § Uploads files to a cloud storage § User A wants to share files with User B: § Generates a re-encryption key § Hands re-encryption key to cloud storage § Cloud storage re-encrypts User A‘s files for User B on demand. 46
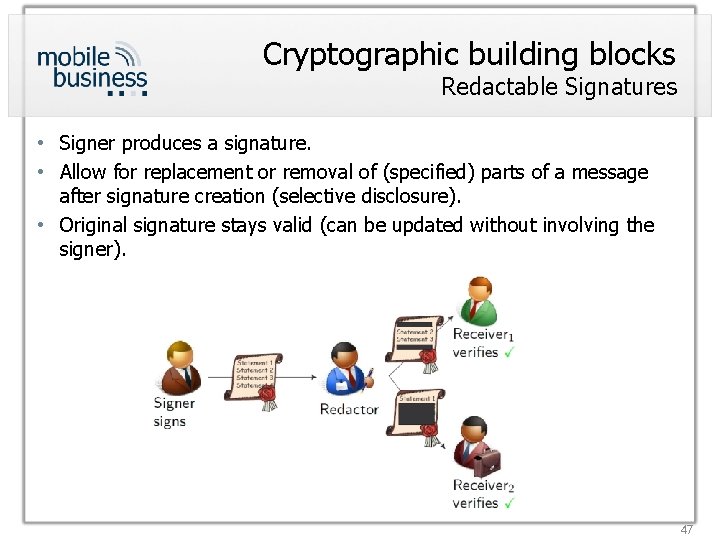
Cryptographic building blocks Redactable Signatures • Signer produces a signature. • Allow for replacement or removal of (specified) parts of a message after signature creation (selective disclosure). • Original signature stays valid (can be updated without involving the signer). 47
Proxy re-encryption + redactable signatures § Combination of Proxy Re-Encryption and Redactable Signatures to achieve: § Confidentiality and Secure Data Sharing § Integrity/Authenticity and Selective Disclosure § 3 rd party redacts without seeing underlying plaintext § Data provider not directly involved 48
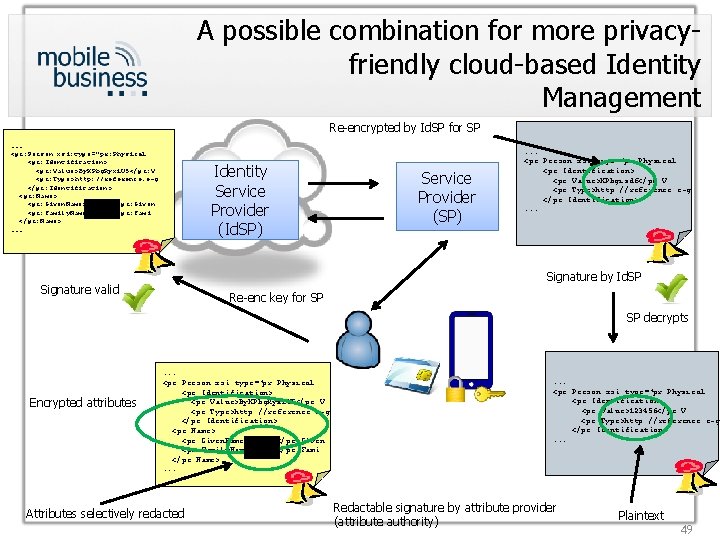
A possible combination for more privacyfriendly cloud-based Identity Management Re-encrypted by Id. SP for SP . . . <pr: Person xsi: type=" pr: Physical <pr: Identification> <pr: Value> By. KPbg. Ryxi. U 5</pr: V <pr: Type>http: //reference. e-g </pr: Identification> <pr: Name> <pr: Given. Name> By. KPbg</pr: Given <pr: Family. Name> Bxi. U 5</pr: Fami </pr: Name>. . . Identity Service Provider (Id. SP) Service Provider (SP) . . . <pr: Person xsi: type="pr: Physical <pr: Identification> <pr: Value>KPbgisdf</pr: V <pr: Type>http: //reference. e-g </pr: Identification>. . . Signature by Id. SP Signature valid Re-enc key for SP SP decrypts Encrypted attributes . . . <pr: Person xsi: type="pr: Physical <pr: Identification> <pr: Value>By. KPbg. Ryxi. U 5</pr: V <pr: Type>http: //reference. e-g </pr: Identification> <pr: Name> <pr: Given. Name>By. KPbg</pr: Given <pr: Family. Name>Bxi. U 5</pr: Fami </pr: Name>. . . Attributes selectively redacted . . . <pr: Person xsi: type="pr: Physical <pr: Identification> <pr: Value>123456</pr: V <pr: Type>http: //reference. e-g </pr: Identification>. . . Redactable signature by attribute provider (attribute authority) Plaintext 49
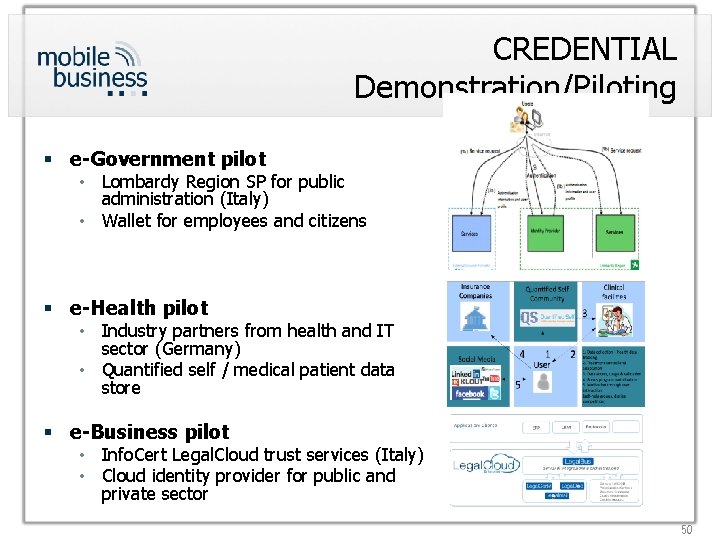
CREDENTIAL Demonstration/Piloting § e-Government pilot • Lombardy Region SP for public administration (Italy) • Wallet for employees and citizens § e-Health pilot • Industry partners from health and IT sector (Germany) • Quantified self / medical patient data store § e-Business pilot • Info. Cert Legal. Cloud trust services (Italy) • Cloud identity provider for public and private sector 50
CREDENTIAL M-Chair main focus Privacy o o Defining privacy requirements Identifying privacy risks in the architecture and pilots Recommending privacy-enhancing technologies Continuous monitoring of addressing privacy issues (privacy by design) Usability and user-adoption o Identifying user preferences and needs o User studies regarding acceptance factors and mental models o User-centred design of the prototypes 51
- Slides: 51