Privacy and technology Week 13 November 23 Privacy
Privacy and technology Week 13 - November 23 Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2004 • Lorrie Cranor • http: //lorrie. cranor. org/courses/fa 04/ 1
Administrivia n Returning rough drafts today « Please follow our suggestions « If we wrote that you have a lot of work left to do, we really mean it « I will try to review 2 nd drafts if you send them to me n Homework 13 (last homework!) will be reading and summary/highlight only - Due November 30 « http: //lorrie. cranor. org/courses/fa 04/hw 13. html n November 30: Current issues discussion, will probably focus on issues that have been raised on class mailing list n December 2: Assemble posters in class n December 3: Poster session 3 -5 pm n Please fill out faculty course evaluations! I would also like feedback on books and guest speakers Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2004 • Lorrie Cranor • http: //lorrie. cranor. org/courses/fa 04/ 2
Homework 11 Discussion n http: //lorrie. cranor. org/courses/fa 04/hw 11. html n Cases where US government used personal data to violate civil liberties of US citizens n Brin: “Can we stand living our lives exposed to scrutiny. . . if in return we get flashlights of our own? ” Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2004 • Lorrie Cranor • http: //lorrie. cranor. org/courses/fa 04/ 3
Privacy invasive technologies n Location tracking (cell phones, GPS devices that phone home, etc. ) n RFID n Transit cards n Computer software that phones home n Devices that phone home n Video cameras (hidden cameras, cell phones) n Personalized ecommerce sites n Automobile data recorders n Face recognition Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2004 • Lorrie Cranor • http: //lorrie. cranor. org/courses/fa 04/ 4
The Global Positioning System (GPS) n Radio-navigation system operated by US Do. D n Comprised of 24 satellites and 5 ground stations n Uses satellites like “man-made stars” to triangulate and calculate 3 D position from 4 satellite signals n Receivers listen for radio beacons and triangulate their position n Typical accuracy in meters, cm accuracy possible « Do. D intentionally degraded accuracy until May 2000 n One-way system « If receivers are to report their location back they must use another system, for example cellular phone network n Does not work indoors Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2004 • Lorrie Cranor • http: //lorrie. cranor. org/courses/fa 04/ 5
Radio-frequency identification (RFID) n Tags « Antenna bonded to small silicon chip encapsulated in glass or plastic (as small as grain of rice) « Unpowered (passive) tags and powered (active) tags n Readers « Broadcast energy to tags, causing tags to broadcast data « Energy from readers can also power onboard sensors or cause tag to write new data to memory « Read ranges currently a few centimeters up to a few meters Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2004 • Lorrie Cranor • http: //lorrie. cranor. org/courses/fa 04/ 6
Current and near term uses of RFID n Automobile immobilizers n Animal tracking n Building proximity cards n Payment systems n Automatic toll collection n Inventory management (mostly at pallet level) «Prevent drug counterfeiting n Passports Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2004 • Lorrie Cranor • http: //lorrie. cranor. org/courses/fa 04/ 7
Electronic Product Code n Standard managed by EPCglobal n Relatively small tags «Inexpensive «No encryption, limited security «Kill feature «Password feature n Designed to replace UPC bar codes n 96 -bit+ serial number n Object Name Service (ONS) database operated by EPCglobal Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2004 • Lorrie Cranor • http: //lorrie. cranor. org/courses/fa 04/ 8
Ecommerce personalization n Ecommerce web sites increasingly offer personalized features «Targeted marketing «Build relationships with customers n Personalization may be: «Based on explicit or implicit data «Task/session focused or profile based «User initiated or system initiated «Prediction based or content based Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2004 • Lorrie Cranor • http: //lorrie. cranor. org/courses/fa 04/ 9
Problems n Ecommerce personalization may not actually work for most sites n Jupiter report says «Personalization features can quadruple site costs «Most consumers have never customized a site «Consumers say personalization not a factor in purchase decisions «Consumers concerned about privacy issues «More cost effective ways of achieving goals Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2004 • Lorrie Cranor • http: //lorrie. cranor. org/courses/fa 04/ 10
Privacy risks n Unsolicited marketing n Computer can “figure things out about me” « Inaccurate inferences -“My Ti. Vo thinks I’m gay!” « Surprisingly accurate inferences n Profiles may facilitate price discrimination « Concern about being charged higher prices « Concern about being treated differently n Revealing personal info to other users of a computer « Revealing info to family members or co-workers « Revealing secrets that can unlock many accounts n Exposing secrets to criminals n Info may be subpoenaed n Info may be used for government surveillance Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2004 • Lorrie Cranor • http: //lorrie. cranor. org/courses/fa 04/ 11
Risks may be magnified in future n Wireless location tracking n Semantic web applications n Ubiquitous computing n (Maybe personalization will be more effective in these contexts than it is for today’s ecommerce web sites? ) Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2004 • Lorrie Cranor • http: //lorrie. cranor. org/courses/fa 04/ 12
Privacy risks from RFID? Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2004 • Lorrie Cranor • http: //lorrie. cranor. org/courses/fa 04/ 13
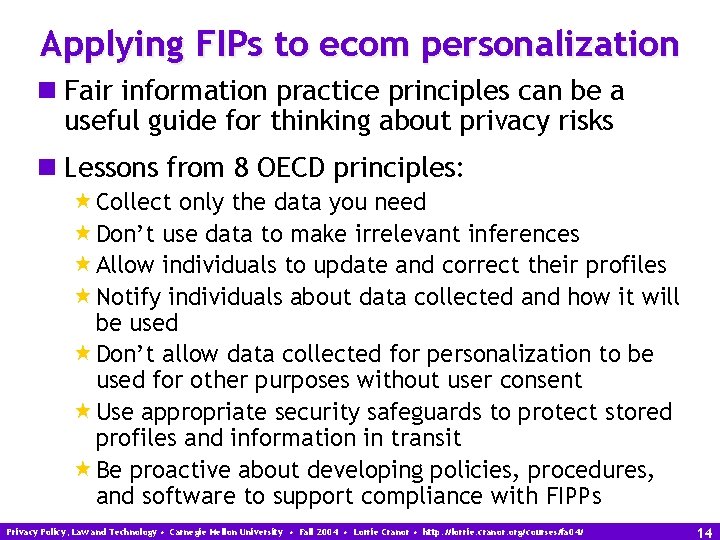
Applying FIPs to ecom personalization n Fair information practice principles can be a useful guide for thinking about privacy risks n Lessons from 8 OECD principles: «Collect only the data you need «Don’t use data to make irrelevant inferences «Allow individuals to update and correct their profiles «Notify individuals about data collected and how it will be used «Don’t allow data collected for personalization to be used for other purposes without user consent «Use appropriate security safeguards to protect stored profiles and information in transit «Be proactive about developing policies, procedures, and software to support compliance with FIPPs Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2004 • Lorrie Cranor • http: //lorrie. cranor. org/courses/fa 04/ 14
Applying FIPs to RFID? Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2004 • Lorrie Cranor • http: //lorrie. cranor. org/courses/fa 04/ 15

Relevant laws and self regulation n US has mostly sector-specific privacy laws «Financial, healthcare, and childrens’ sites most affected by privacy laws «Industry guidelines may require privacy notices or optouts or limit what may be included in a profile n European countries have more comprehensive privacy laws «Privacy notices and access provisions required «Limitations on secondary uses and data sharing «In some cases, limitations on use of server logs and on automated use of profile data for decision-making «In some cases pseudonymous services required Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2004 • Lorrie Cranor • http: //lorrie. cranor. org/courses/fa 04/ 16
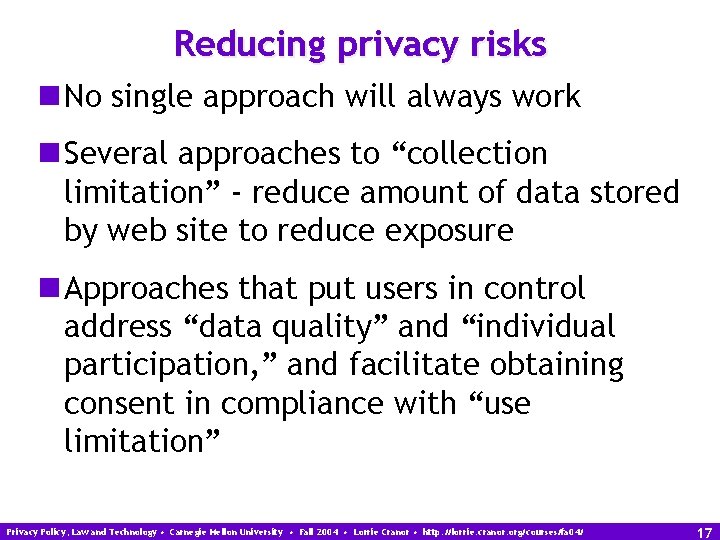
Reducing privacy risks n No single approach will always work n Several approaches to “collection limitation” - reduce amount of data stored by web site to reduce exposure n Approaches that put users in control address “data quality” and “individual participation, ” and facilitate obtaining consent in compliance with “use limitation” Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2004 • Lorrie Cranor • http: //lorrie. cranor. org/courses/fa 04/ 17
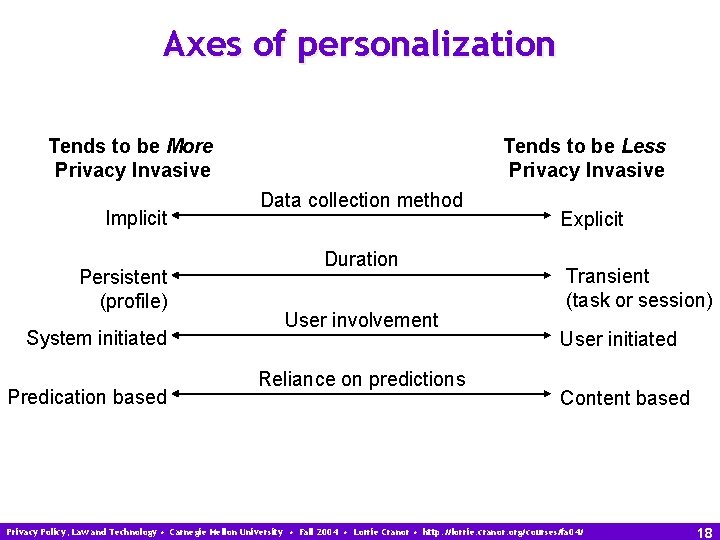
Axes of personalization Tends to be More Privacy Invasive Implicit Persistent (profile) System initiated Predication based Tends to be Less Privacy Invasive Data collection method Duration User involvement Reliance on predictions Explicit Transient (task or session) User initiated Content based Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2004 • Lorrie Cranor • http: //lorrie. cranor. org/courses/fa 04/ 18
Pseudonymous profiles n Useful for reducing risk and complying with privacy laws when personal info is not needed for personalization n But, profile may become identifiable because of unique combinations of info, links with log data, unauthorized access to user’s computer, etc. n Profile info should always be stored separately from web usage logs and transaction records that might contain IP addresses or PII n Architectures for pseudonymous profiles across web sites proposed by « Arlein, Jaobsson, Monrose, and Reiter (EC’ 00) « Kobsa and Schreck (TOIT 2003) Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2004 • Lorrie Cranor • http: //lorrie. cranor. org/courses/fa 04/ 19
Client-side profiles n Useful for reducing risk and complying with laws n But risk of exposure to other users of computer remains; storing profiles in encrypted form on user’s computer can help n Client-side profiles may be stored in cookies that are replayed to the server, which discards them after use n Client-side scripting may allow personalization without ever sending personal info to the server n Architecture for recommendation system in which individuals compute their own recommendations without revealing their individual data proposed by « Canny (IEEE Symposium on Security and Privacy 2002) Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2004 • Lorrie Cranor • http: //lorrie. cranor. org/courses/fa 04/ 20
Task-based personalization n Focus on data associated with current session or task - no user profile need be stored anywhere n May allow for simpler (and less expensive) system architecture too! n May eliminate problem of system making recommendations that are not relevant to current task n Less “spooky” to users - relationship between current task and resultant personalization usually obvious Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2004 • Lorrie Cranor • http: //lorrie. cranor. org/courses/fa 04/ 21
Putting users in control n Users should be able to control « what information is stored in their profile « how it may be used and disclosed n Developing a good user interface to do this is complicated « Setting preferences can be tedious « Creating overall rules that can be applied on the fly as new profile data is collected requires deep understanding and ability to anticipate privacy concerns « Approach that provides reasonable default rules with the ability to add/change them for all data or on a case-by-case basis seems promising « Privacy preference prompts in transaction process may help « Use of multiple personae may help Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2004 • Lorrie Cranor • http: //lorrie. cranor. org/courses/fa 04/ 22
Amazon critique n Customizing profile requires navigating through several menus « There should be easier ways of getting to this info at the times when it is likely to be most relevant n Users can rate purchases or have them excluded from recommendations, but not removed from profile « If items must remain in profile for legal reasons, users should be able to request that they not be accessible online n Every time a user makes a new purchase that they want to rate or exclude they have to edit profile info « There should be a way to set up default rules n Amazon already allows users to store multiple credit cards and addresses - why not allow users to create personae linked to each with option of keeping recommendations separate (would allow easy way to separate work/home/gift personae)? n Likewise, how about an “I didn’t buy it for myself” check-off box (perhaps automatically checked if gift wrapping is requested) Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2004 • Lorrie Cranor • http: //lorrie. cranor. org/courses/fa 04/ 23
RFID privacy proposals Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2004 • Lorrie Cranor • http: //lorrie. cranor. org/courses/fa 04/ 24
Happy Thanksgiving! Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2004 • Lorrie Cranor • http: //lorrie. cranor. org/courses/fa 04/ 25
- Slides: 25