Prevention Protection Identity Theft WiFi cookies Cyber Crime
Prevention Protection Identity Theft Wi-Fi "cookies“ Cyber. Crime / Hacking Viruses Fraud Intelligence & Awareness #Teens! @EH Natina Thalien - MBA, CFE (Certified Fraud Examiner) Date: November 20, 2017 1 Social Media
So, what is Fraud? FRAUD q Generally, Fraud is: § any dishonest activity § causing actual or potential financial loss to any person or entity § Including theft of money or property § whether or not by use of deception § includes deliberate falsification, concealment, destruction, or use of a falsified document. § Improper use of information or position q General elements of Fraud: § Knowledge that the statement was false when uttered § Material false statement § Reliance on the false statement by the victim § Damages as a result 2 ………. . so, is corruption the same as fraud?
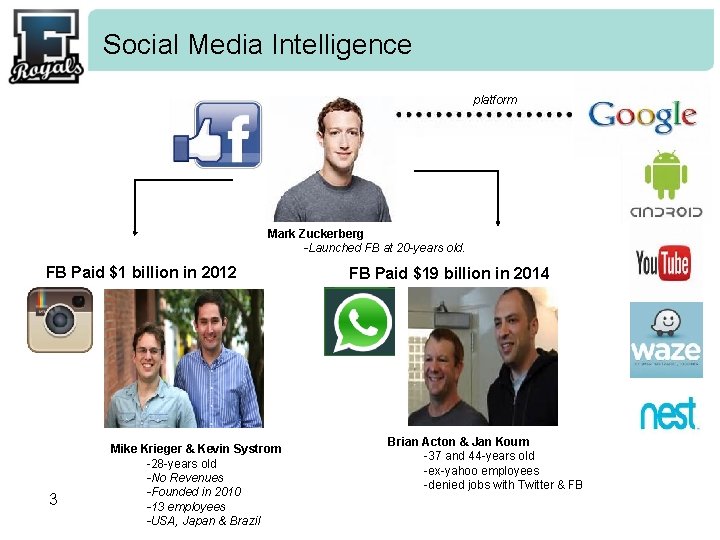
Social Media Intelligence platform Mark Zuckerberg -Launched FB at 20 -years old. FB Paid $1 billion in 2012 3 Mike Krieger & Kevin Systrom -28 -years old -No Revenues -Founded in 2010 -13 employees -USA, Japan & Brazil FB Paid $19 billion in 2014 Brian Acton & Jan Koum -37 and 44 -years old -ex-yahoo employees -denied jobs with Twitter & FB
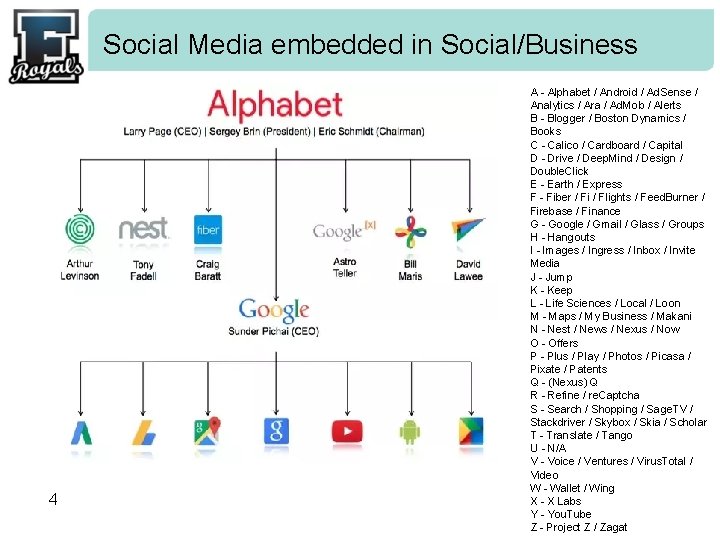
Social Media embedded in Social/Business 4 A - Alphabet / Android / Ad. Sense / Analytics / Ara / Ad. Mob / Alerts B - Blogger / Boston Dynamics / Books C - Calico / Cardboard / Capital D - Drive / Deep. Mind / Design / Double. Click E - Earth / Express F - Fiber / Fi / Flights / Feed. Burner / Firebase / Finance G - Google / Gmail / Glass / Groups H - Hangouts I - Images / Ingress / Inbox / Invite Media J - Jump K - Keep L - Life Sciences / Local / Loon M - Maps / My Business / Makani N - Nest / News / Nexus / Now O - Offers P - Plus / Play / Photos / Picasa / Pixate / Patents Q - (Nexus) Q R - Refine / re. Captcha S - Search / Shopping / Sage. TV / Stackdriver / Skybox / Skia / Scholar T - Translate / Tango U - N/A V - Voice / Ventures / Virus. Total / Video W - Wallet / Wing X - X Labs Y - You. Tube Z - Project Z / Zagat
Social Media – Facebook #didyouknow? Exposure of Personal Life Free & open to anyone Privacy Controls Be Aware: q Facebook does not share with users who is looking at their profile. q Access to listed friends, family and colleagues. q If you look at someone’s profile often enough, FB assumes you are acquainted and starts to recommend you to that person. (stalkers) – Careful!!! q Facebook will pay YOU between $500 - $10 K if you find a ‘bug’ or can hack your way ‘’in’’; you’ve saved them the trouble of locating this themselves. q Whats. App (which can also be used on your computer) allows access to a users entire contact list, which is a valuable target for hackers. Status: continues to rely on open sourcing in order to allow programs to fix bugs & improve security. § Criticism: Security Terrorism 5 Privacy
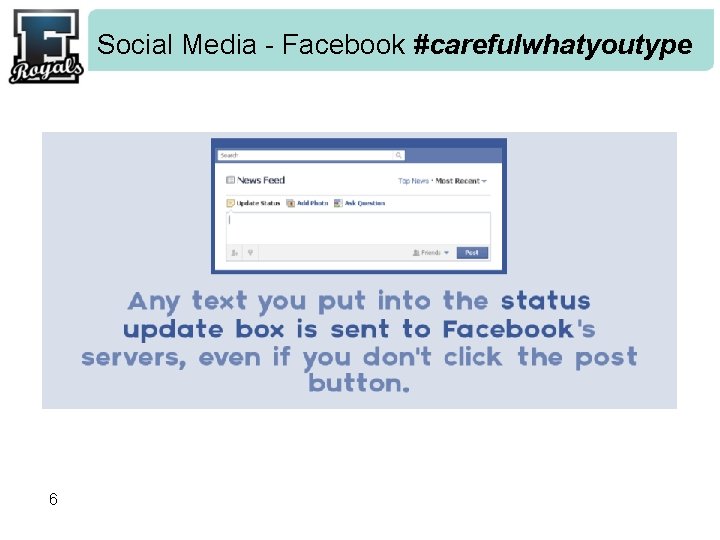
Social Media - Facebook #carefulwhatyoutype 6
Social Media - Facebook #dontbeavictim #showmethemoney: $500 - $10, 000 if you can HACK Facebook Attention: if you cause harm to another –it’s FRAUD 7
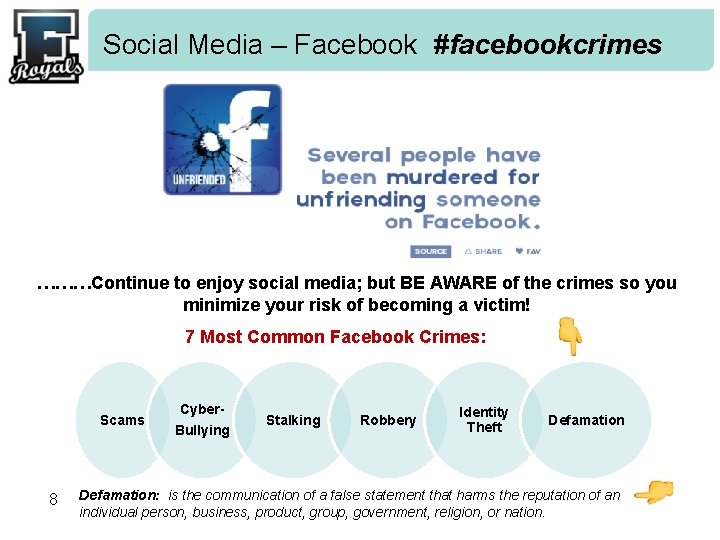
Social Media – Facebook #facebookcrimes ………Continue to enjoy social media; but BE AWARE of the crimes so you minimize your risk of becoming a victim! 7 Most Common Facebook Crimes: Scams 8 Cyber. Bullying Stalking Robbery Identity Theft Defamation: is the communication of a false statement that harms the reputation of an individual person, business, product, group, government, religion, or nation.
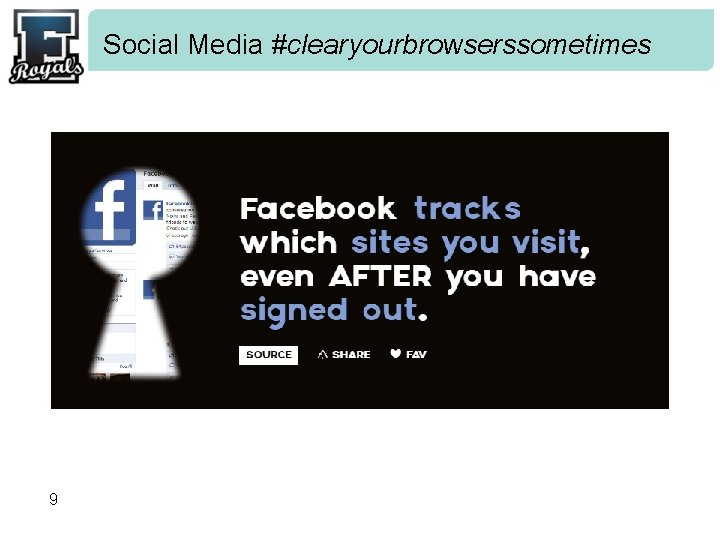
Social Media #clearyourbrowserssometimes 9
Social Media #whydo’’I’’usefacebook? 1. Can’t remember birthdays 2. People want to read the news 3. Feel as though it’s a ‘duty’ to like something and post something 4. Attention Seekers 5. Watch people Secretly 6. Boredom 7. Need Facebook to promote my work 8. Support a Social cause 9. Remain connected with Friends 10. Suffer from ‘FAD’ – Facebook Addiction Disorder (can’t resist) 10
Social Media - Facebook 11

Social Media - Facebook #dontbenaive …. on-line Stranger contact. 12

Social Media - Facebook 13
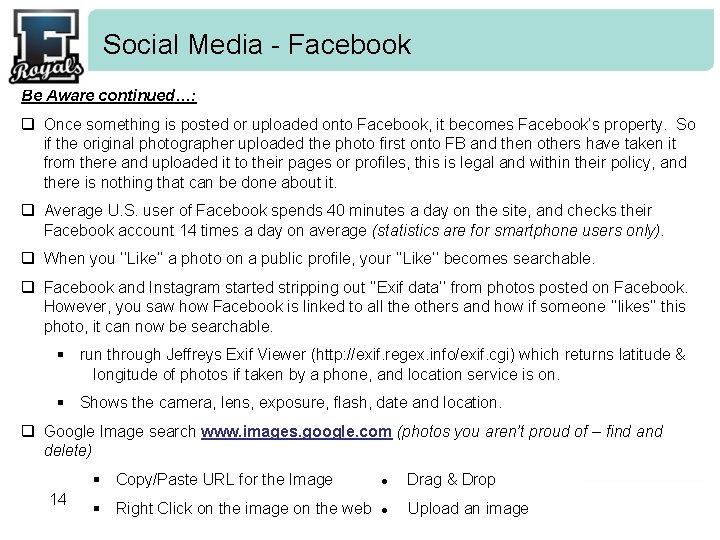
Social Media - Facebook Be Aware continued…: q Once something is posted or uploaded onto Facebook, it becomes Facebook’s property. So if the original photographer uploaded the photo first onto FB and then others have taken it from there and uploaded it to their pages or profiles, this is legal and within their policy, and there is nothing that can be done about it. q Average U. S. user of Facebook spends 40 minutes a day on the site, and checks their Facebook account 14 times a day on average (statistics are for smartphone users only). q When you ‘’Like’’ a photo on a public profile, your ‘’Like’’ becomes searchable. q Facebook and Instagram started stripping out ‘’Exif data’’ from photos posted on Facebook. However, you saw how Facebook is linked to all the others and how if someone ‘’likes’’ this photo, it can now be searchable. § run through Jeffreys Exif Viewer (http: //exif. regex. info/exif. cgi) which returns latitude & longitude of photos if taken by a phone, and location service is on. § Shows the camera, lens, exposure, flash, date and location. q Google Image search www. images. google. com (photos you aren’t proud of – find and delete) 14 § Copy/Paste URL for the Image ● Drag & Drop § Right Click on the image on the web ● Upload an image
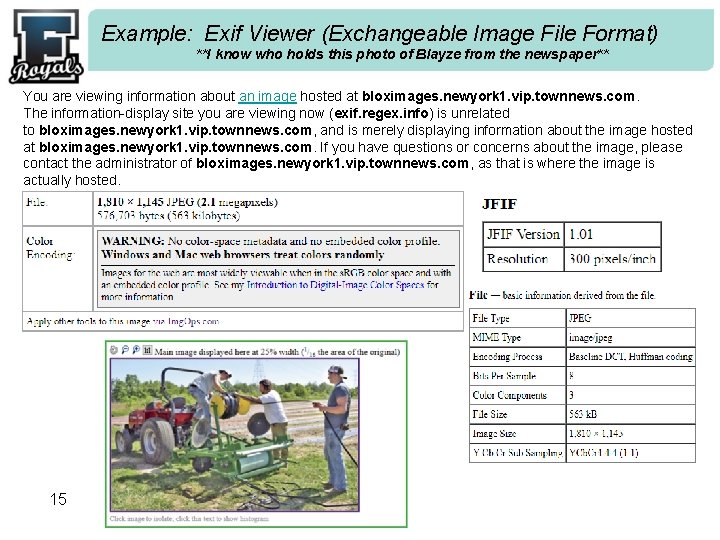
Example: Exif Viewer (Exchangeable Image File Format) **I know who holds this photo of Blayze from the newspaper** You are viewing information about an image hosted at bloximages. newyork 1. vip. townnews. com. The information-display site you are viewing now (exif. regex. info) is unrelated to bloximages. newyork 1. vip. townnews. com, and is merely displaying information about the image hosted at bloximages. newyork 1. vip. townnews. com. If you have questions or concerns about the image, please contact the administrator of bloximages. newyork 1. vip. townnews. com, as that is where the image is actually hosted. 15
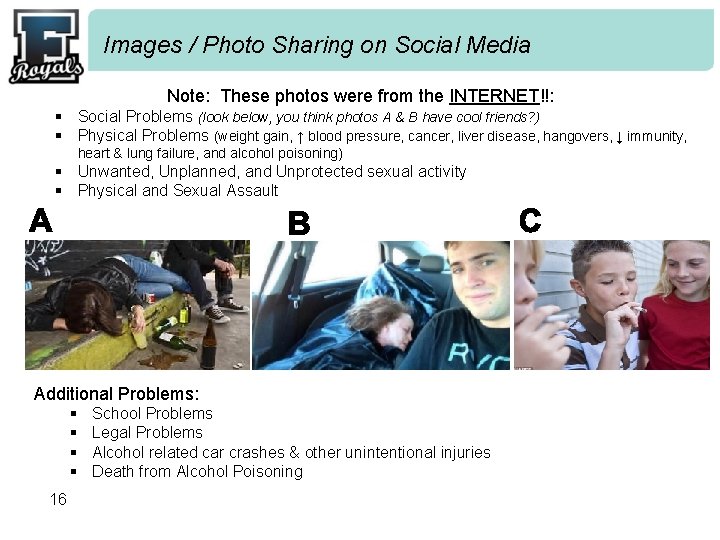
Images / Photo Sharing on Social Media Note: These photos were from the INTERNET!!: § Social Problems (look below, you think photos A & B have cool friends? ) § Physical Problems (weight gain, ↑ blood pressure, cancer, liver disease, hangovers, ↓ immunity, heart & lung failure, and alcohol poisoning) § Unwanted, Unplanned, and Unprotected sexual activity § Physical and Sexual Assault Additional Problems: § § 16 School Problems Legal Problems Alcohol related car crashes & other unintentional injuries Death from Alcohol Poisoning
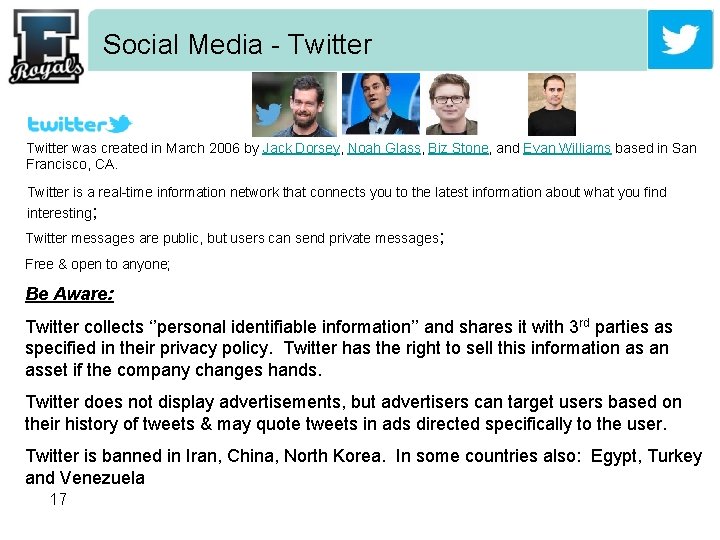
Social Media - Twitter was created in March 2006 by Jack Dorsey, Noah Glass, Biz Stone, and Evan Williams based in San Francisco, CA. Twitter is a real-time information network that connects you to the latest information about what you find interesting; Twitter messages are public, but users can send private messages; Free & open to anyone; Be Aware: Twitter collects ‘’personal identifiable information’’ and shares it with 3 rd parties as specified in their privacy policy. Twitter has the right to sell this information as an asset if the company changes hands. Twitter does not display advertisements, but advertisers can target users based on their history of tweets & may quote tweets in ads directed specifically to the user. Twitter is banned in Iran, China, North Korea. In some countries also: Egypt, Turkey and Venezuela 17
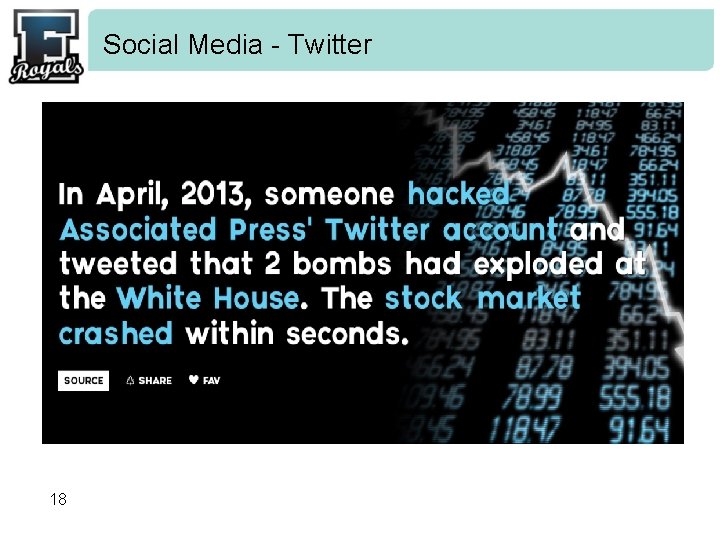
Social Media - Twitter 18

Social Media - Twitter 19
Social Media - Twitter 20
Social Media - Twitter 21
Cyber. Security #passwordsecurity 22
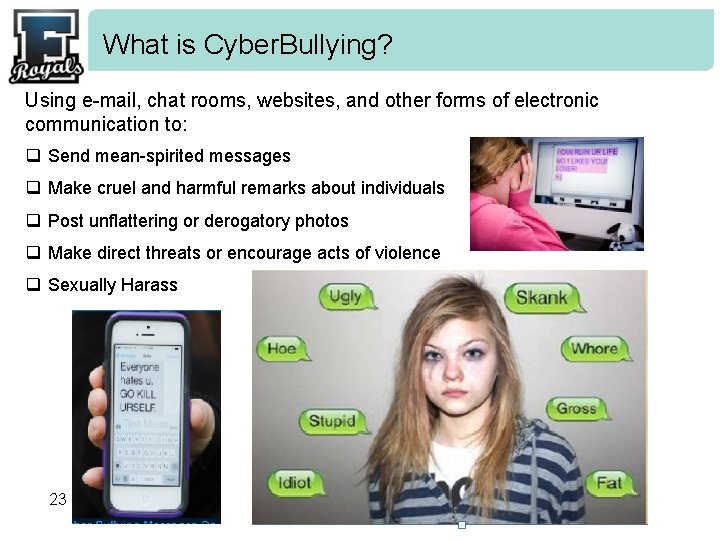
What is Cyber. Bullying? Using e-mail, chat rooms, websites, and other forms of electronic communication to: q Send mean-spirited messages q Make cruel and harmful remarks about individuals q Post unflattering or derogatory photos q Make direct threats or encourage acts of violence q Sexually Harass 23
Cyberbullying #betrayel 24
Cyberbullying #breachofprivacy 25
Cyberbullying #postings 26
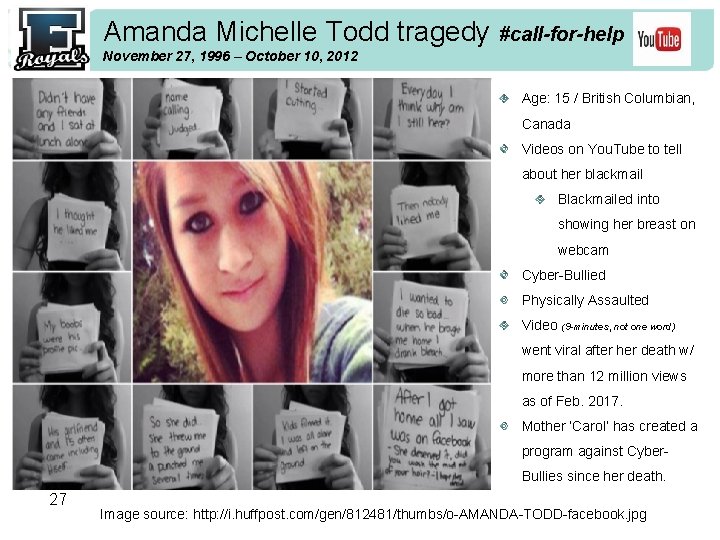
Amanda Michelle Todd tragedy #call-for-help November 27, 1996 – October 10, 2012 Age: 15 / British Columbian, Canada Videos on You. Tube to tell about her blackmail Blackmailed into showing her breast on webcam Cyber-Bullied Physically Assaulted Video (9 -minutes, not one word) went viral after her death w/ more than 12 million views as of Feb. 2017. Mother ‘Carol’ has created a program against Cyber. Bullies since her death. 27 Image source: http: //i. huffpost. com/gen/812481/thumbs/o-AMANDA-TODD-facebook. jpg
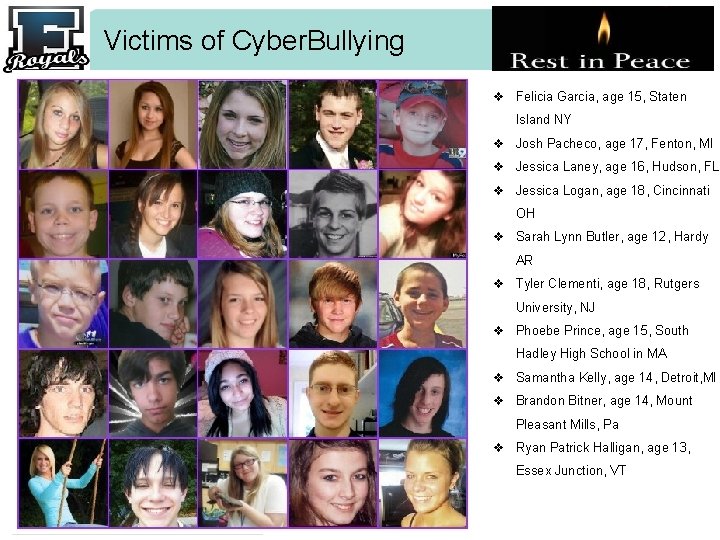
Victims of Cyber. Bullying v Felicia Garcia, age 15, Staten Island NY v Josh Pacheco, age 17, Fenton, MI v Jessica Laney, age 16, Hudson, FL v Jessica Logan, age 18, Cincinnati OH v Sarah Lynn Butler, age 12, Hardy AR v Tyler Clementi, age 18, Rutgers University, NJ v Phoebe Prince, age 15, South Hadley High School in MA v Samantha Kelly, age 14, Detroit, MI v Brandon Bitner, age 14, Mount Pleasant Mills, Pa v Ryan Patrick Halligan, age 13, Essex Junction, VT 28
Before you Post or Send Remember…. . Think about whether you would want your: Family Friends Principal or Future Employer to see it. Statistically speaking…. . q Nearly 1 in 3 children have been a victim of cyberbullying q Half of the suicides among 10 – 14 year olds are due to bullying q Nearly 1 in 7 teachers are is a victim of cyberbullying ‘LIKING’ in a cyberbully posting, makes YOU a cyberbully too; even without your words 29
What to do if you are Cyber. Bullied q. Do NOT reply back to the bully q. Tell Someone, such as an adult q. Use Online Blocking Features q. Adjust Security Settings q. Threaten Action q. Report them to a site, school, parents or law enforcement 30
Indiana Law on Cyberbullying Criminal Harassment: Stalking Someone who uses an electronic device to threaten or stalk another person commits a more serious crime. Under Indiana law, it is a Level 6 felony for to stalk another person or make a threat intended to cause the victim to reasonably fear sexual battery, serious bodily injury, or death. (Ind. Code Ann. § 35 -45 -10 -5. ) Indiana law defines “stalking” as: a knowing or intentional course of conduct involving repeated or continuous harassment that would cause a reasonable person to feel terrorized, frightened, intimidated, or threatened, and that actually does cause the victim to feel that way. (Ind. Code Ann. § 35 -45 -10 -1. ) Cyberbullying Punishment A person convicted of Level 6 felony stalking faces imprisonment of six months to two and a half years, a fine of up to $10, 000, or both. (Ind. Code Ann. § 35 -50 -2 -7. ) A person convicted of Class B misdemeanor harassment by obscene message faces incarceration of 180 days, a fine of up to $1, 000, or both. (Ind. Code Ann. § 35 -50 -3 -3. ) 31 http: //www. criminaldefenselawyer. com/resources/cyberbullying-laws-indiana. htm
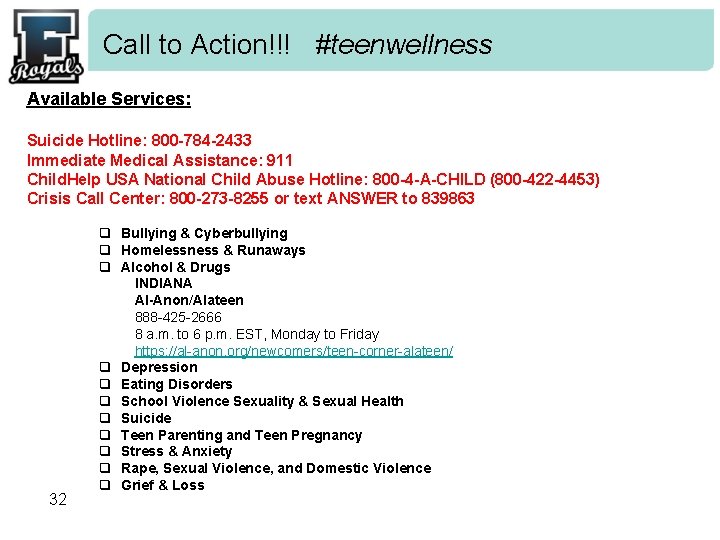
Call to Action!!! #teenwellness Available Services: Suicide Hotline: 800 -784 -2433 Immediate Medical Assistance: 911 Child. Help USA National Child Abuse Hotline: 800 -4 -A-CHILD (800 -422 -4453) Crisis Call Center: 800 -273 -8255 or text ANSWER to 839863 32 q Bullying & Cyberbullying q Homelessness & Runaways q Alcohol & Drugs INDIANA Al-Anon/Alateen 888 -425 -2666 8 a. m. to 6 p. m. EST, Monday to Friday https: //al-anon. org/newcomers/teen-corner-alateen/ q Depression q Eating Disorders q School Violence Sexuality & Sexual Health q Suicide q Teen Parenting and Teen Pregnancy q Stress & Anxiety q Rape, Sexual Violence, and Domestic Violence q Grief & Loss
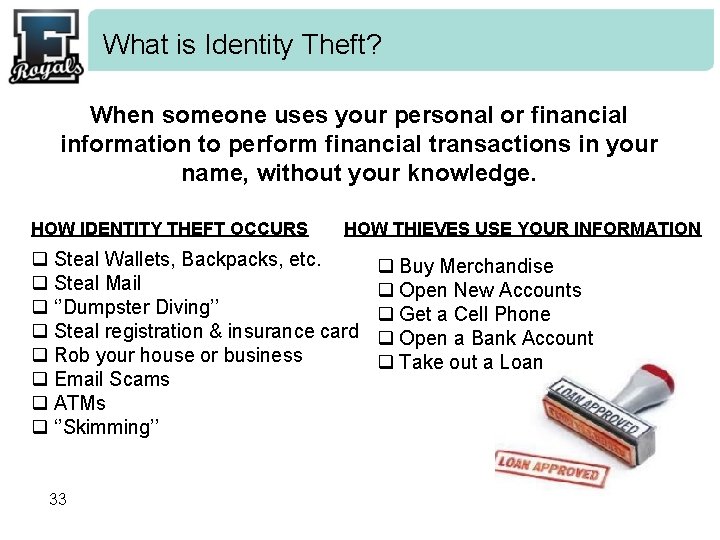
What is Identity Theft? When someone uses your personal or financial information to perform financial transactions in your name, without your knowledge. HOW IDENTITY THEFT OCCURS HOW THIEVES USE YOUR INFORMATION q Steal Wallets, Backpacks, etc. q Steal Mail q ‘’Dumpster Diving’’ q Steal registration & insurance card q Rob your house or business q Email Scams q ATMs q ‘’Skimming’’ 33 q Buy Merchandise q Open New Accounts q Get a Cell Phone q Open a Bank Account q Take out a Loan
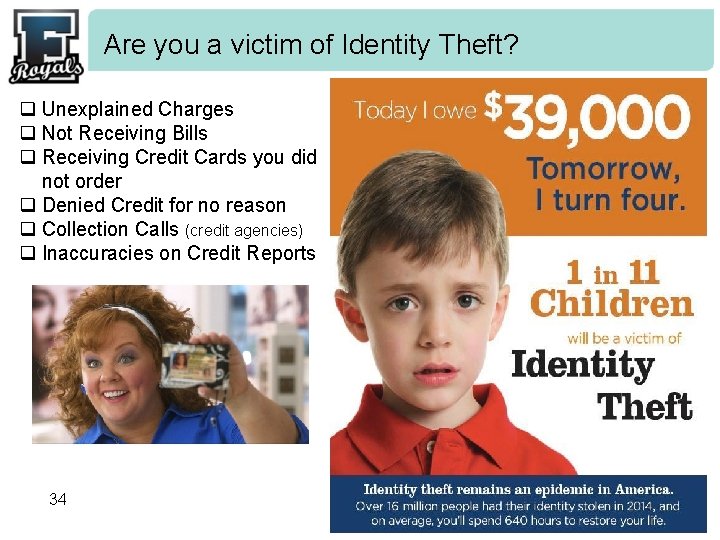
Are you a victim of Identity Theft? q Unexplained Charges q Not Receiving Bills q Receiving Credit Cards you did not order q Denied Credit for no reason q Collection Calls (credit agencies) q Inaccuracies on Credit Reports 34
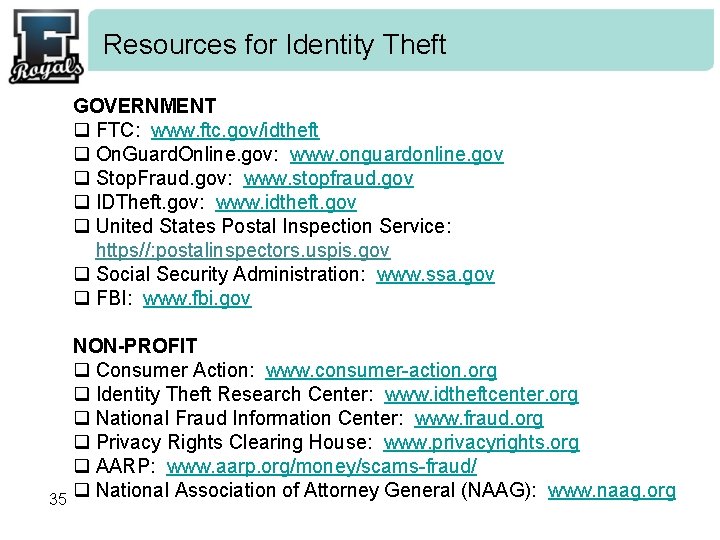
Resources for Identity Theft GOVERNMENT q FTC: www. ftc. gov/idtheft q On. Guard. Online. gov: www. onguardonline. gov q Stop. Fraud. gov: www. stopfraud. gov q IDTheft. gov: www. idtheft. gov q United States Postal Inspection Service: https//: postalinspectors. uspis. gov q Social Security Administration: www. ssa. gov q FBI: www. fbi. gov 35 NON-PROFIT q Consumer Action: www. consumer-action. org q Identity Theft Research Center: www. idtheftcenter. org q National Fraud Information Center: www. fraud. org q Privacy Rights Clearing House: www. privacyrights. org q AARP: www. aarp. org/money/scams-fraud/ q National Association of Attorney General (NAAG): www. naag. org
Web. Cam Hacking #cybersecurity Today webcams are present natively in most of our devices such as our laptops, even duplicate on smartphones or tablets and systematically accompanied by microphone. What can be Hacked? q Camera’s in laptops q Baby Monitors q Wireless Security Systems q Any Camera with network capability A few crimes to mention (there are thousands……): q A number of wireless Foscam baby monitor cameras were hacked. q A class action lawsuit against ADT Security alleged that the company’s wireless security systems were susceptible to easy exploits. q Cyber. Blackmail: q Miss Teen USA, Cassidy Wolf was hacked for one year (hacker was 19) q Ransoms to unlock files 36
Web. Cam Hacking #cybersecurity Cameras are Hacked by: q Wi. Fi that is not password protected q An open device with no password q A malware attack (malware = malicious software) Ø computer virus, worms, trojan horses, ransom ware, etc… Tips to keep yourself from being camera hacked: q Keep your Internet private ü Install a full-service internet security suite and keep it updated. ü Protect your wireless network with a strong password. q Create Secured Passwords. ü Change the default password that comes with your wireless network and devices. 37 ü Incorporate numbers and capital letters. ü If punctuation marks are allowed, use multiple
Web. Cam Hacking #cybersecurity ü Try to use 12 digits ü Avoid names and places ü Use a password checker to see how strong your password is. q Keep your software up-to-date. ü This can help patch software vulnerabilities that enable hackers to gain access. q Monitor the Indicator Light ü If the camera indicator light goes on w/out your permission, there is a high chance that your computer has been compromised. q Don’t click on suspicious links. 38
Web. Cam Hacking #cybersecurity ü If you’re unsure of a link in an e-mail, don’t click on it. ü Only download attachments & click links from people you trust. q Avoid using unsecured Wi. Fi. q Check your camera log. q For many security systems, users can check the IP addresses that accessed the cameras. q If a suspicious IP address, change access codes immediately and notify the security company. q Manage your camera settings. q Consider a separate network q Consider using a network for your phone & computers and a separate network for your for security systems & other monitors. q Cover your cameras when they are not in use. 39
Mark Zuckerberg (posted photo on his FB account) 40
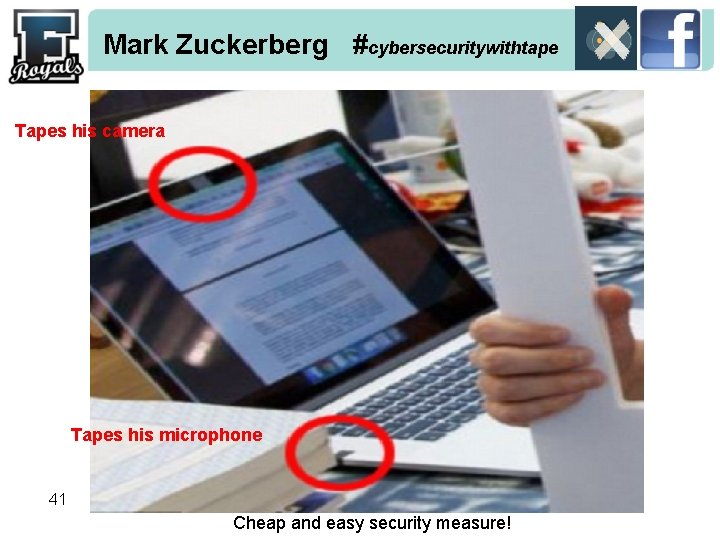
Mark Zuckerberg #cybersecuritywithtape Tapes his camera Tapes his microphone 41 Cheap and easy security measure!
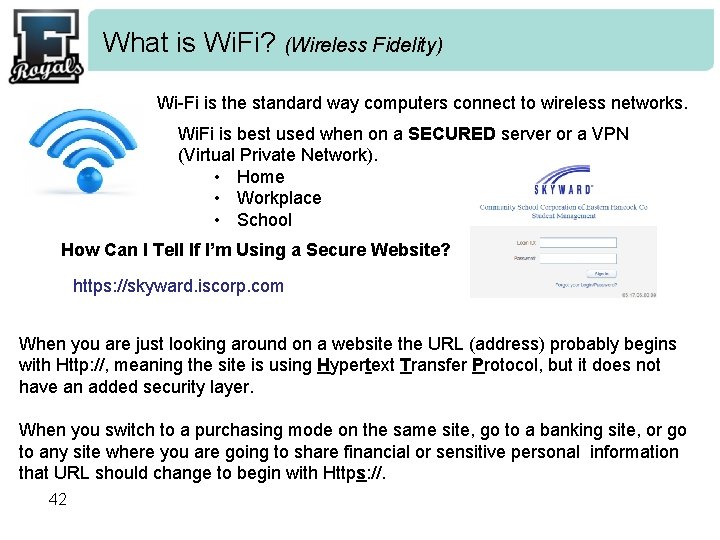
What is Wi. Fi? (Wireless Fidelity) Wi-Fi is the standard way computers connect to wireless networks. Wi. Fi is best used when on a SECURED server or a VPN (Virtual Private Network). • Home • Workplace • School How Can I Tell If I’m Using a Secure Website? https: //skyward. iscorp. com When you are just looking around on a website the URL (address) probably begins with Http: //, meaning the site is using Hypertext Transfer Protocol, but it does not have an added security layer. When you switch to a purchasing mode on the same site, go to a banking site, or go to any site where you are going to share financial or sensitive personal information that URL should change to begin with Https: //. 42
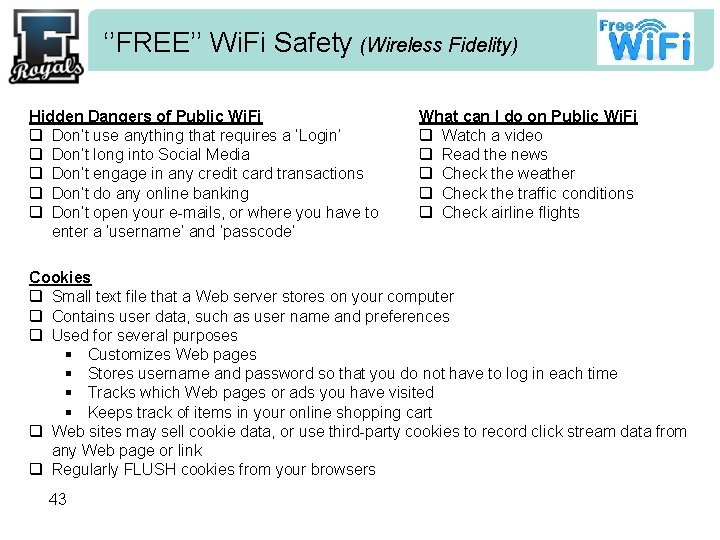
‘’FREE’’ Wi. Fi Safety (Wireless Fidelity) Hidden Dangers of Public Wi. Fi q Don’t use anything that requires a ‘Login’ q Don’t long into Social Media q Don’t engage in any credit card transactions q Don’t do any online banking q Don’t open your e-mails, or where you have to enter a ‘username’ and ‘passcode’ What can I do on Public Wi. Fi q Watch a video q Read the news q Check the weather q Check the traffic conditions q Check airline flights Cookies q Small text file that a Web server stores on your computer q Contains user data, such as user name and preferences q Used for several purposes § Customizes Web pages § Stores username and password so that you do not have to log in each time § Tracks which Web pages or ads you have visited § Keeps track of items in your online shopping cart q Web sites may sell cookie data, or use third-party cookies to record click stream data from any Web page or link q Regularly FLUSH cookies from your browsers 43
Attention with Public Charging Stations!! Your smartphone can be easily hacked, if you plug it in to charge via USB at a public place like an airport, café or on public transport. There are (2) ways to charge a mobile phone’s battery. : 1. Use a power cord directly into an outlet 2. Use a USB that draws power from a computer’s USB port. If you begin to ‘’panic’’ because you really can’t wait to charge your phone at an electrical outlet, turn your phone completely OFF and plug it in to a charging station. 44
False Documents (Drivers License, Passports, etc…) #FRAUD FELONY: Convicted crimes can be Jail, Fines and Probation depending on the defense. (i. e. – buy alcohol, cigarettes, or used to buy a firearm) Class 1 misdeamenor for possession, distribution or usage vs. Class 6 felony for firearms. NOTE: Facial Recognition in Indiana by BMV helps secure Driver’s License § L-1 identity solutions – ‘cleanses’ Indiana’s database of duplicate photos § Mulitple photos for a single DL because of license renewals & than they match each license holder. § 140 branches in Indiana, review 500/daily and it gives 2/3 suspects a day. Fraudulent documents are used to facilitate terrorism, smuggling, drug trafficking, immigration violations, and many other crimes. In fact, some of the most significant crimes and terrorist events of the past few decades, including the September 11, 2001 terrorist attacks, were made possible by the use of fake identification documents. These and other fraudulent documents enable criminals to escape detection, conceal their true identities, and pass through borders undetected. Possession of a “fake id” is serious. Criminal charges have long lasting affects on your future, affects your ability to concentrate on work and school and can cost you time and money in attorney fees and possibly fines. Though everyone seems to do it you can make a decision for yourself. Avoid the possible consequences and use only your own valid identification or driver’s license. 45
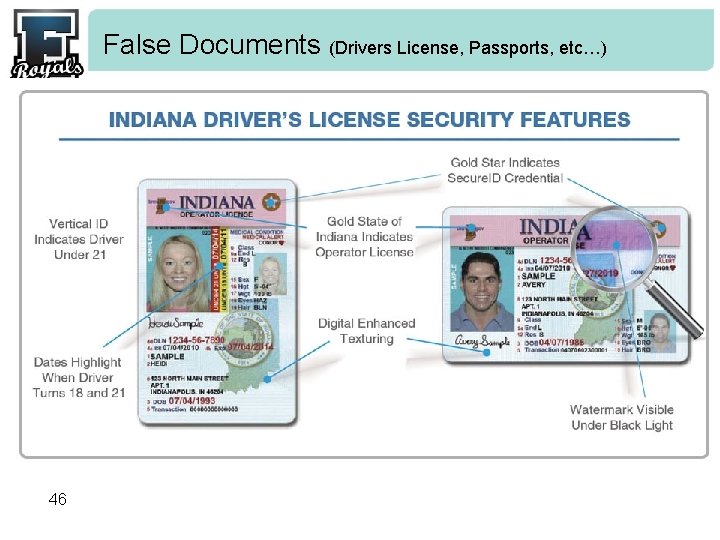
False Documents (Drivers License, Passports, etc…) 46
The World is Watching You! #protectyourself q Perform a Self-Audit § (3) credit reporting agencies: Experian – Trans. Union – Equifax q Search engines to find people for YOURSELF: ‘’Your Name’’ § Google (google. com) § Bing (bing. com) § Pipl (pipl. com) § Yasni (yasni. com) § Yatedo (yatedo. com) § Spokeo (spokeo. com) § Peekyou (peekyou. com) § Foupas (foupas. com) § yo. Name (yo. Name. com) § Name. Chk (namechk. com) 47
The World is Watching You! …. continued q Maximize your security settings on every device and computer used. q Turn OFF your phone and shut-down your computer often. § Clear your browser’s history often. q Passwords - check the strength of your passwords: • www. passwordmeter. com (it’s not https: (so, again…careful / alter something) q Stand up to Cyber. Bullies! q Shred your mail if not used…. if you have bank offers, credit card offers, etc… q Have an e-mail address that isn’t your full name. 48
What NOT to do while ‘online’. • Don’t put information out there that can haunt you later. • Jeopardize college scholarships and future jobs. • Be aware of what others could write about you (future x-friend) and use a photo that perhaps shows you in a ‘less flattering light’. • Don’t take other people’s personal contact information and put them on inappropriate sites. (i. e. – x-rated sites, dating sites, etc…) • Serious consequences to both the person you are victimizing and possibly legal constraints against you. • Never (1000 x) meet with someone you met online. • Never give out your personal information (Such as phone number, address, passwords or photos. ) • Don’t accept or open e-mails, IM Messages, File attachments, Pictures or Texts from people you do not know. 49
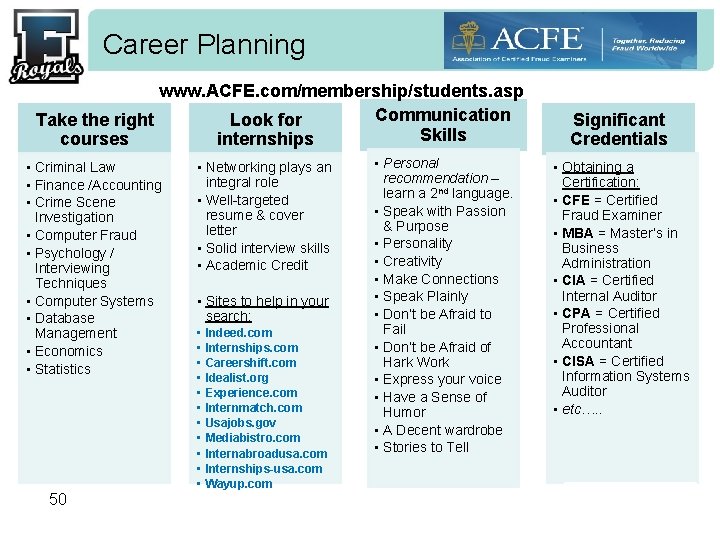
Career Planning www. ACFE. com/membership/students. asp Communication Take the right Look for courses Skills internships • Criminal Law • Finance /Accounting • Crime Scene Investigation • Computer Fraud • Psychology / Interviewing Techniques • Computer Systems • Database Management • Economics • Statistics 50 • Networking plays an integral role • Well-targeted resume & cover letter • Solid interview skills • Academic Credit • Sites to help in your search: • • • Indeed. com Internships. com Careershift. com Idealist. org Experience. com Internmatch. com Usajobs. gov Mediabistro. com Internabroadusa. com Internships-usa. com Wayup. com • Personal recommendation – learn a 2 nd language. • Speak with Passion & Purpose • Personality • Creativity • Make Connections • Speak Plainly • Don’t be Afraid to Fail • Don’t be Afraid of Hark Work • Express your voice • Have a Sense of Humor • A Decent wardrobe • Stories to Tell Significant Credentials • Obtaining a Certification: • CFE = Certified Fraud Examiner • MBA = Master’s in Business Administration • CIA = Certified Internal Auditor • CPA = Certified Professional Accountant • CISA = Certified Information Systems Auditor • etc…. .
Questions & Answering Contact information: Natina Thalien indianafemme@gmail. com +33(0)643. 161. 385 51
- Slides: 51