PREVENT BREACH ASSUME BREACH Typical Attack Timeline Observations

PREVENT BREACH + ASSUME BREACH


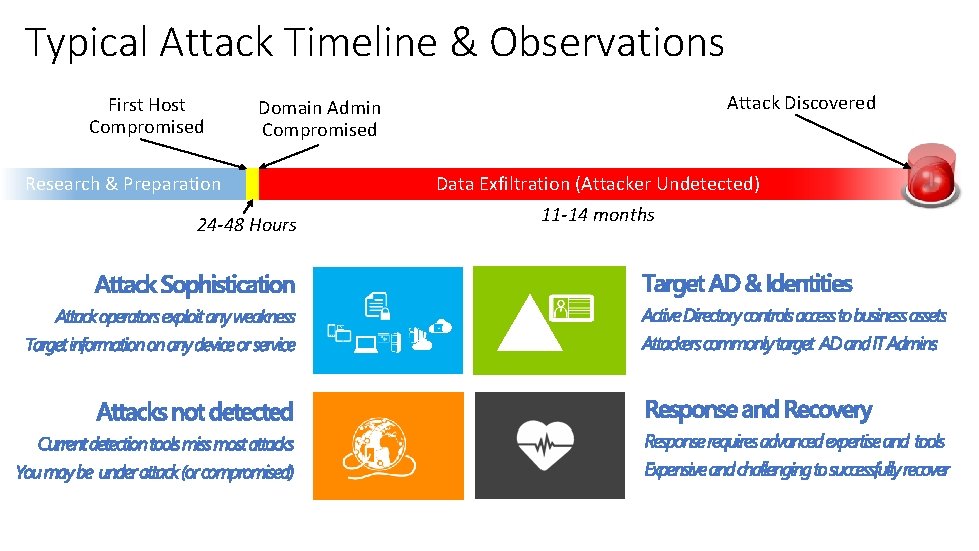
Typical Attack Timeline & Observations First Host Compromised Domain Admin Compromised Research & Preparation 24 -48 Hours Attack Discovered Data Exfiltration (Attacker Undetected) 11 -14 months
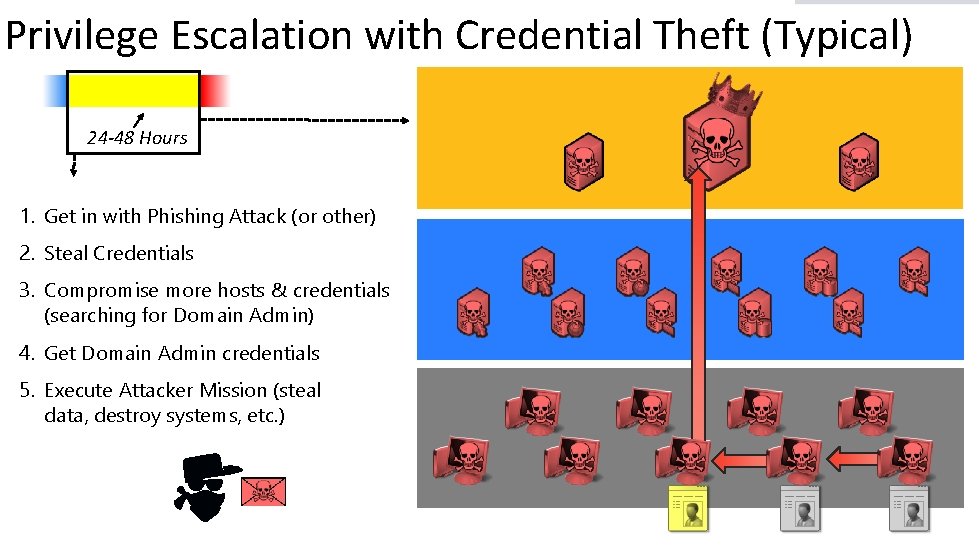
Modern Attack T Privilege Escalation with Credential Theft (Typical) 24 -48 Hours 1. Get in with Phishing Attack (or other) 2. Steal Credentials 3. Compromise more hosts & credentials (searching for Domain Admin) 4. Get Domain Admin credentials 5. Execute Attacker Mission (steal data, destroy systems, etc. )

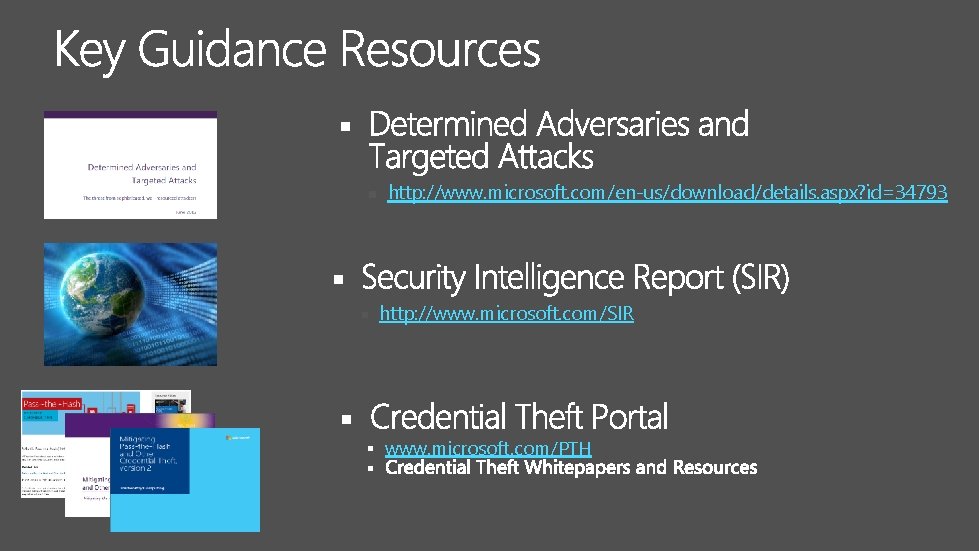
§ http: //www. microsoft. com/en-us/download/details. aspx? id=34793 § http: //www. microsoft. com/SIR § § www. microsoft. com/PTH §
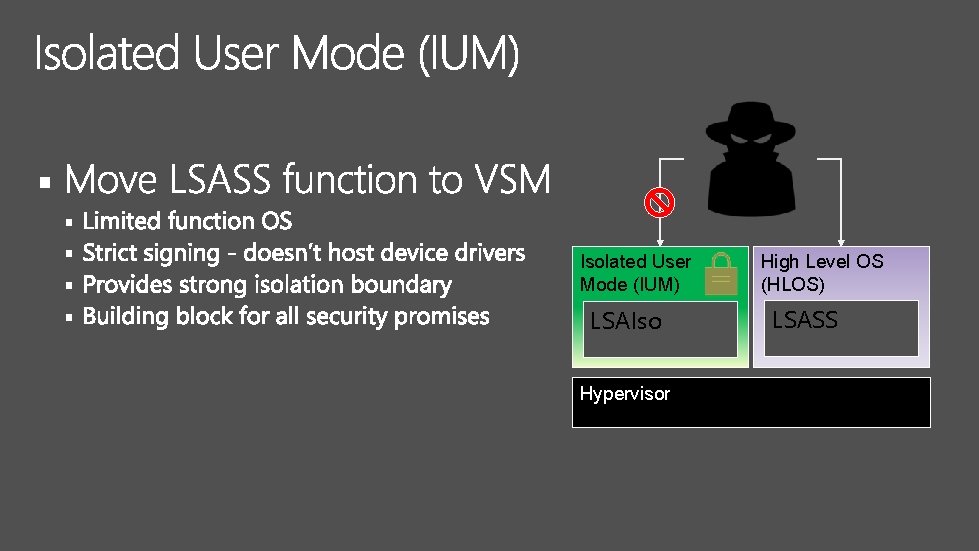
§ § § Isolated User Mode (IUM) LSAIso Hypervisor High Level OS (HLOS) LSASS
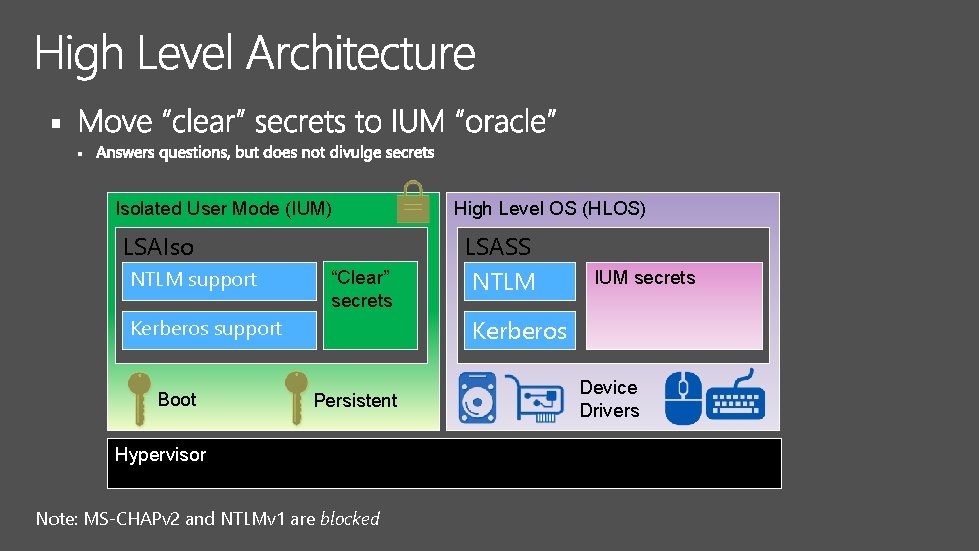
§ § Isolated User Mode (IUM) LSAIso NTLM support “Clear” secrets LSASS NTLM “Clear” IUM secrets Kerberos support Boot High Level OS (HLOS) Persistent Hypervisor Note: MS-CHAPv 2 and NTLMv 1 are blocked Device Drivers


Tier 0 1. Privilege escalation • Credential Theft • Application Agents • Service Accounts 2. Lateral traversal • Credential Theft • Application Agents • Service Accounts Tier 1 Tier 2
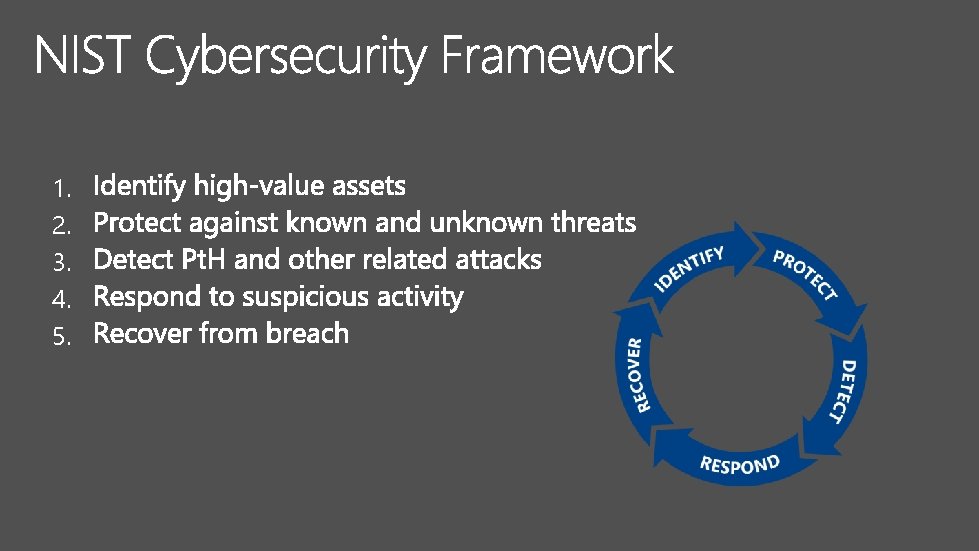
1. 2. 3. 4. 5.
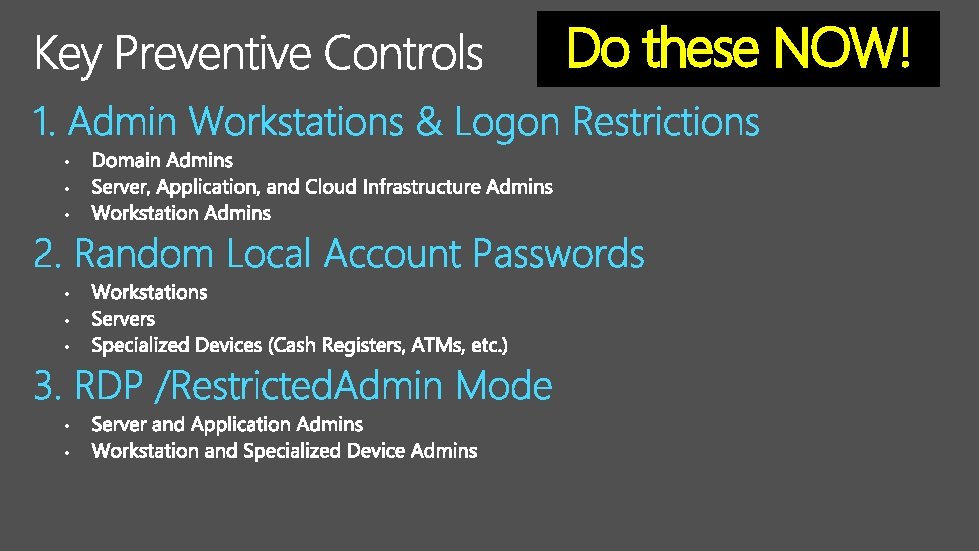
Do these NOW! • •
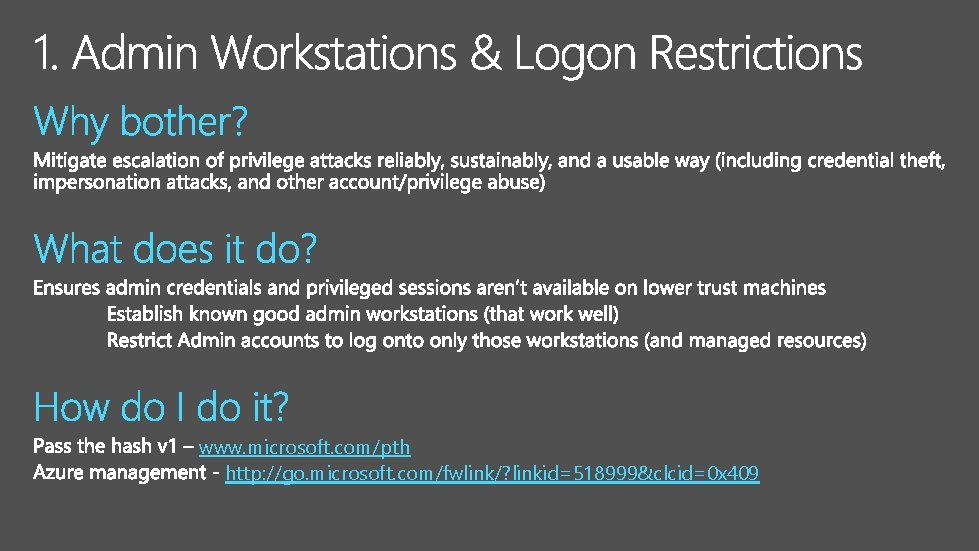
www. microsoft. com/pth http: //go. microsoft. com/fwlink/? linkid=518999&clcid=0 x 409
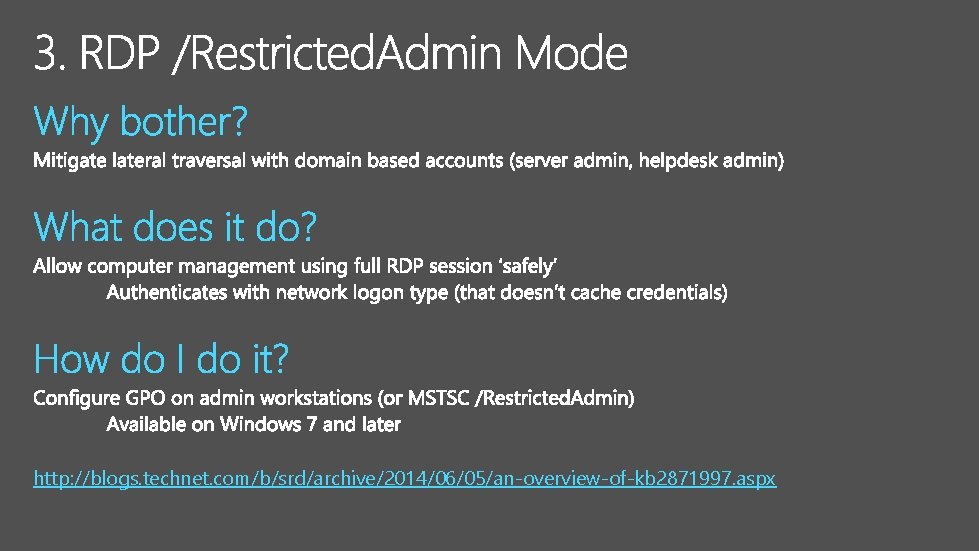
http: //blogs. technet. com/b/srd/archive/2014/06/05/an-overview-of-kb 2871997. aspx
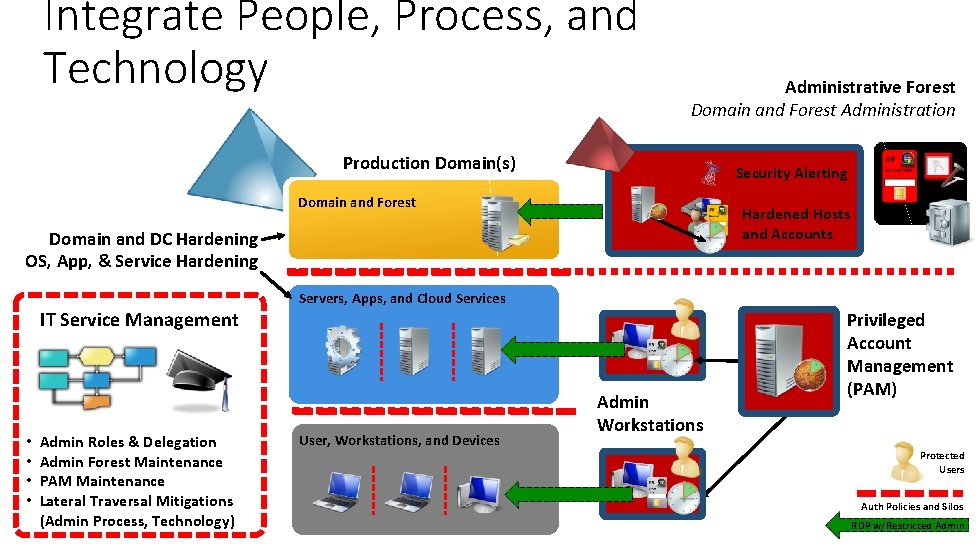
Integrate People, Process, and Technology Administrative Forest Domain and Forest Administration Production Domain(s) Security Alerting Domain and Forest Hardened Hosts and Accounts Domain and DC Hardening OS, App, & Service Hardening IT Service Management • • Admin Roles & Delegation Admin Forest Maintenance PAM Maintenance Lateral Traversal Mitigations (Admin Process, Technology) Servers, Apps, and Cloud Services User, Workstations, and Devices Admin Workstations Privileged Account Management (PAM) Protected Users Auth Policies and Silos RDP w/Restricted Admin
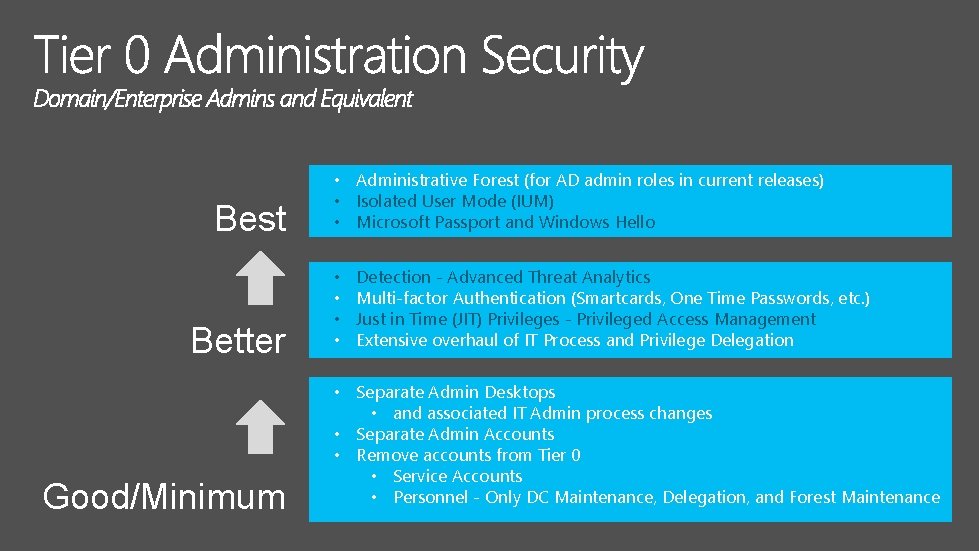
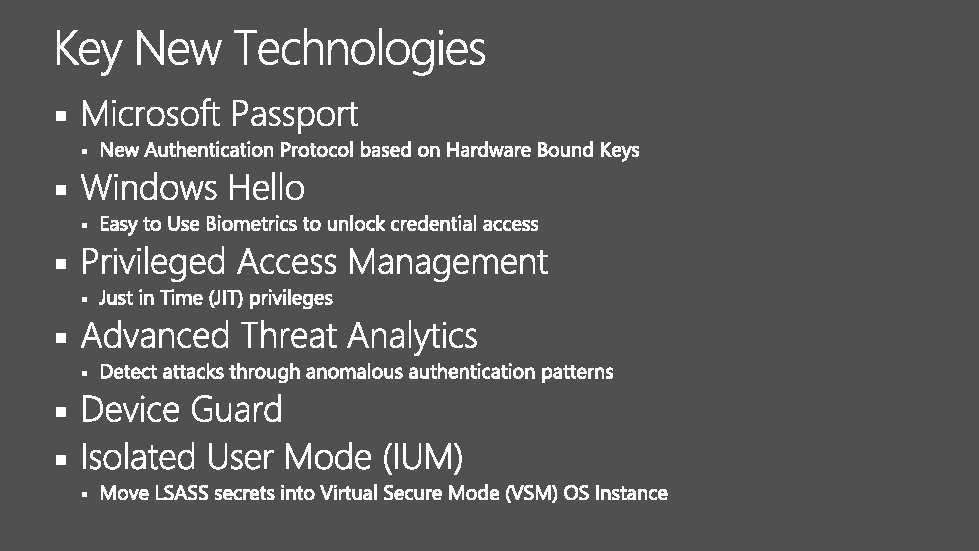
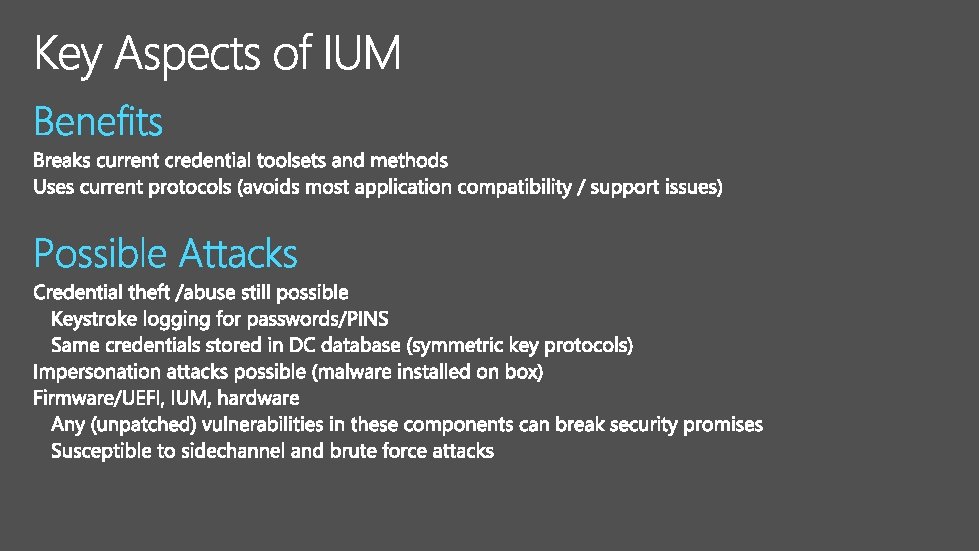
Best Better Good/Minimum • Administrative Forest (for AD admin roles in current releases) • Isolated User Mode (IUM) • Microsoft Passport and Windows Hello • • Detection - Advanced Threat Analytics Multi-factor Authentication (Smartcards, One Time Passwords, etc. ) Just in Time (JIT) Privileges - Privileged Access Management Extensive overhaul of IT Process and Privilege Delegation • Separate Admin Desktops • and associated IT Admin process changes • Separate Admin Accounts • Remove accounts from Tier 0 • Service Accounts • Personnel - Only DC Maintenance, Delegation, and Forest Maintenance
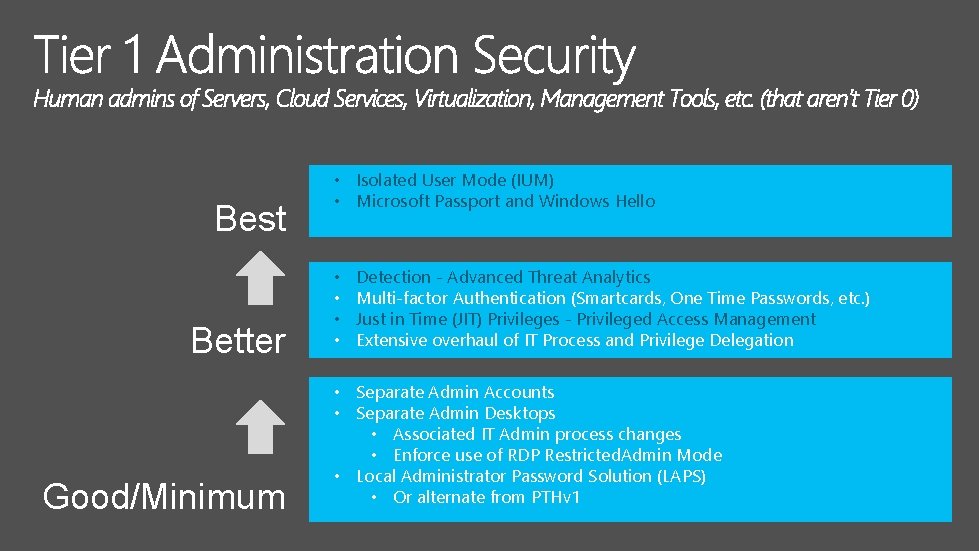
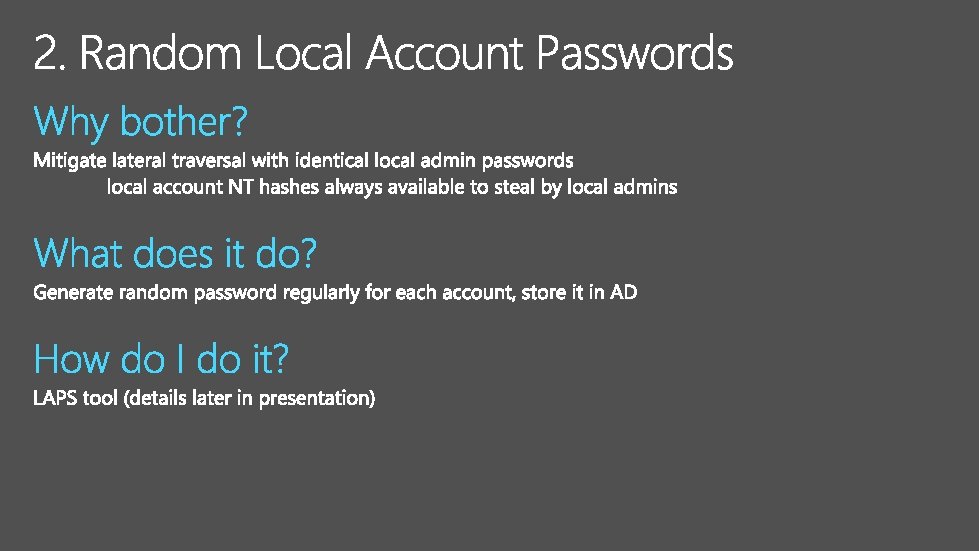
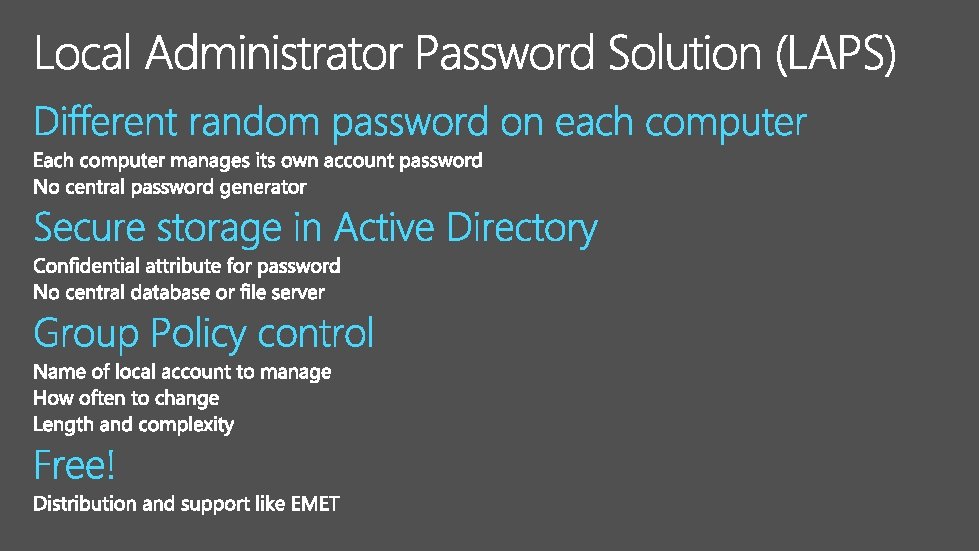
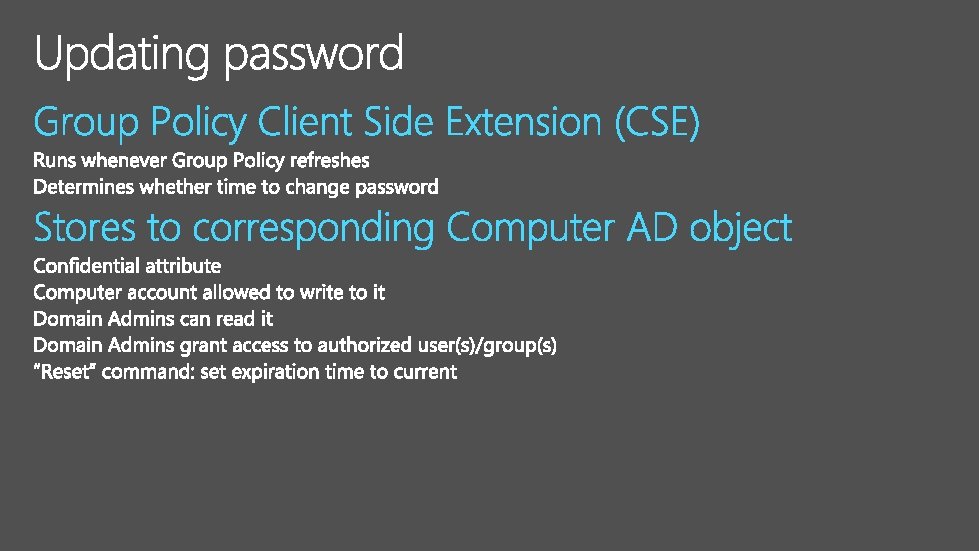
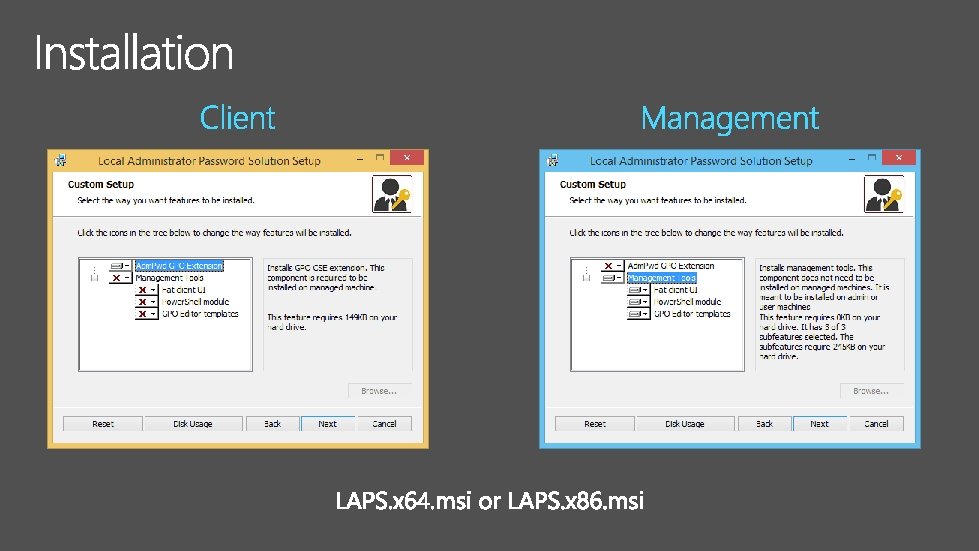
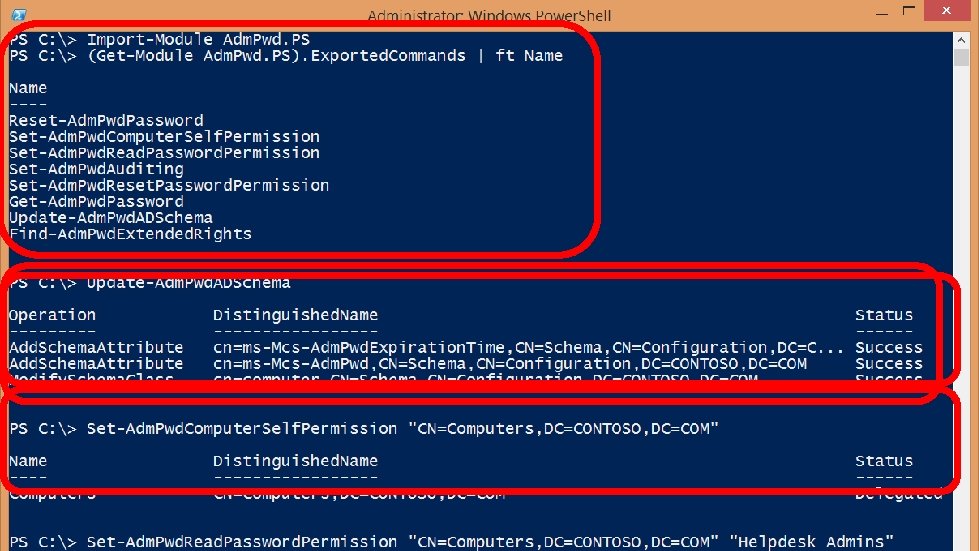
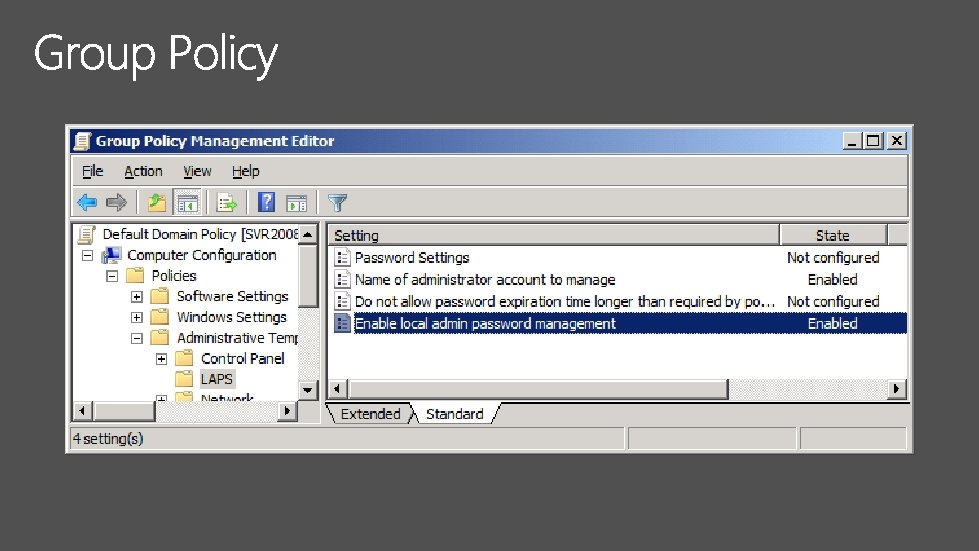
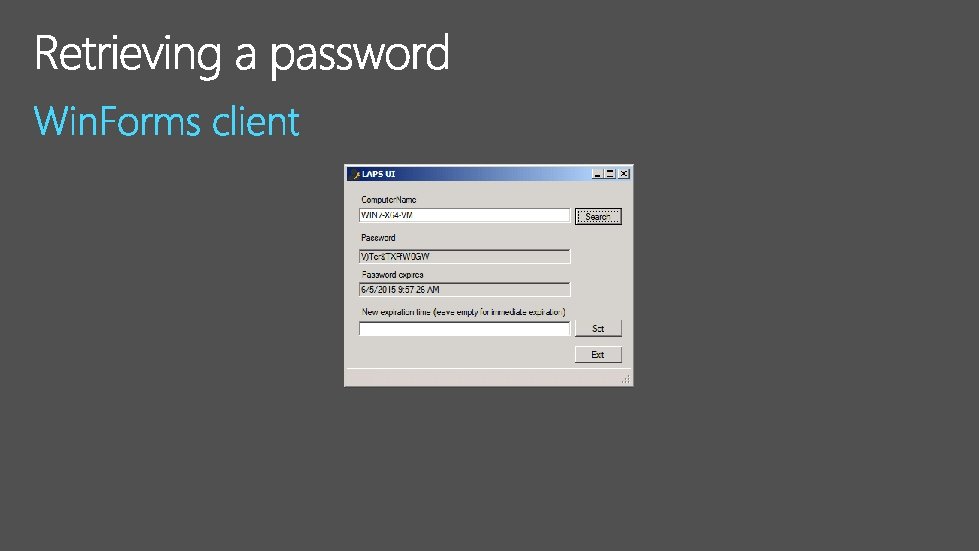
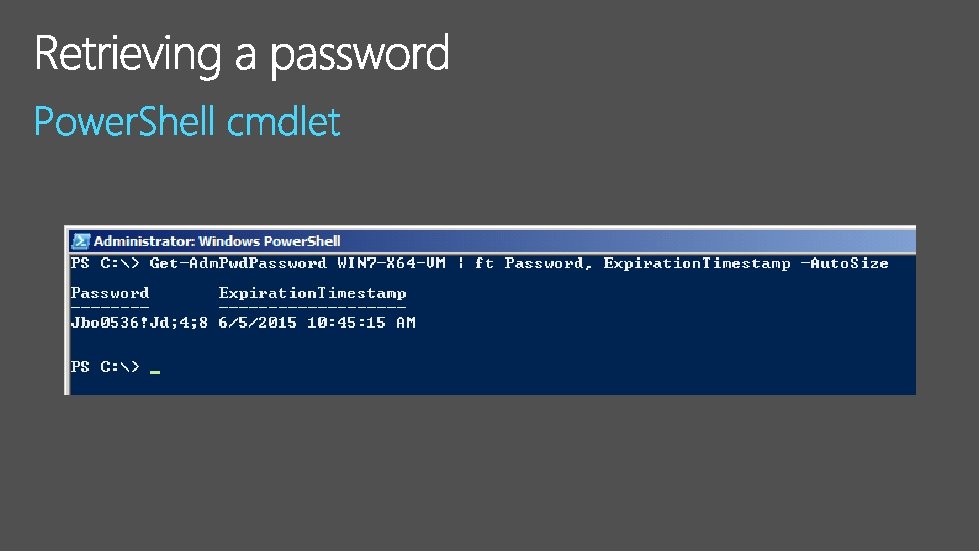
Best Better Good/Minimum • Isolated User Mode (IUM) • Microsoft Passport and Windows Hello • • Detection - Advanced Threat Analytics Multi-factor Authentication (Smartcards, One Time Passwords, etc. ) Just in Time (JIT) Privileges - Privileged Access Management Extensive overhaul of IT Process and Privilege Delegation • Separate Admin Accounts • Separate Admin Desktops • Associated IT Admin process changes • Enforce use of RDP Restricted. Admin Mode • Local Administrator Password Solution (LAPS) • Or alternate from PTHv 1
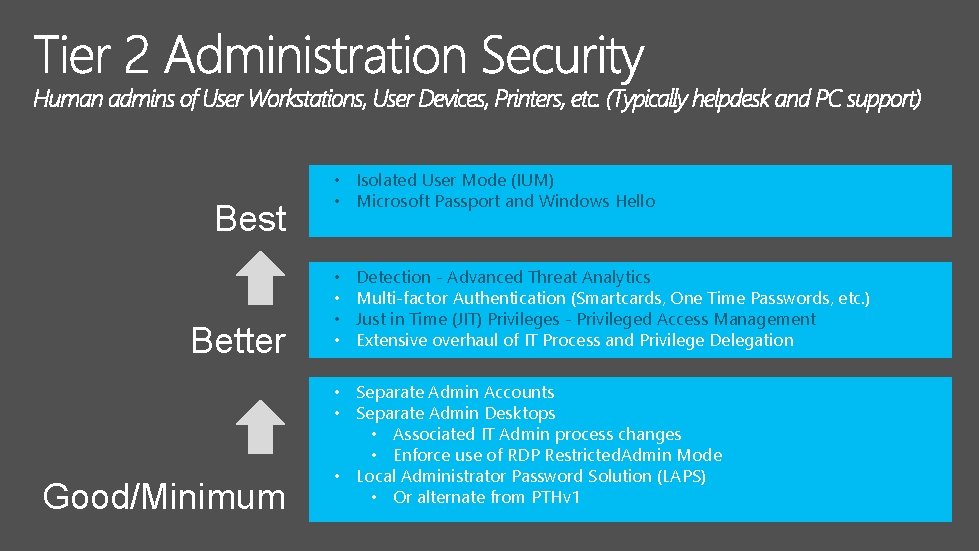
Best Better Good/Minimum • Isolated User Mode (IUM) • Microsoft Passport and Windows Hello • • Detection - Advanced Threat Analytics Multi-factor Authentication (Smartcards, One Time Passwords, etc. ) Just in Time (JIT) Privileges - Privileged Access Management Extensive overhaul of IT Process and Privilege Delegation • Separate Admin Accounts • Separate Admin Desktops • Associated IT Admin process changes • Enforce use of RDP Restricted. Admin Mode • Local Administrator Password Solution (LAPS) • Or alternate from PTHv 1

1 Implement Mitigations Now! A. B. C. 2 Revamp your culture and support processes 3 Plan to adopt Windows 10 Features § § 37

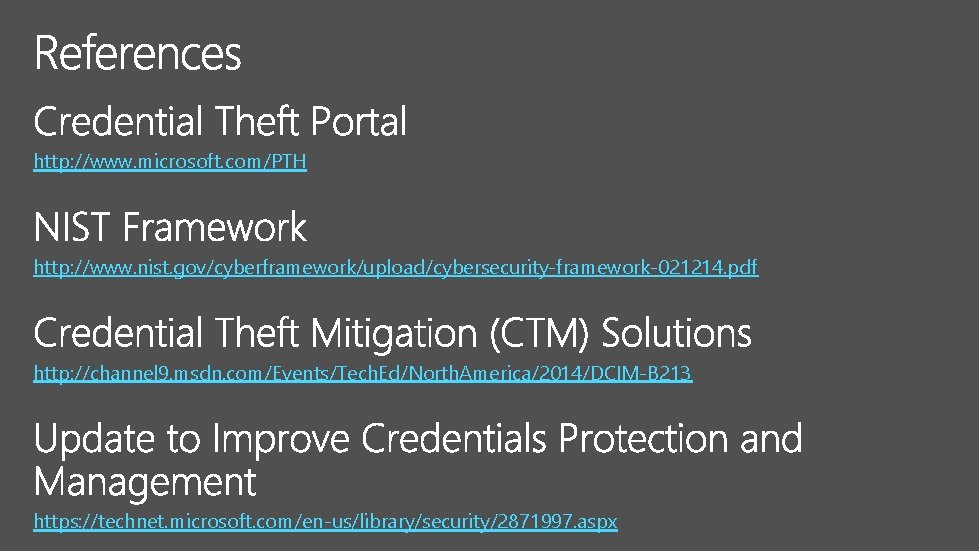
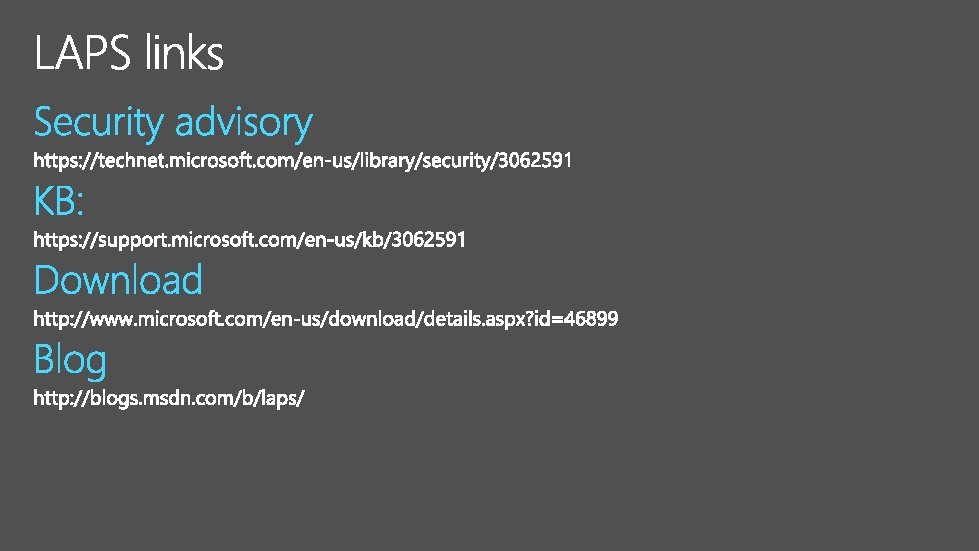
http: //www. microsoft. com/PTH http: //www. nist. gov/cyberframework/upload/cybersecurity-framework-021214. pdf http: //channel 9. msdn. com/Events/Tech. Ed/North. America/2014/DCIM-B 213 https: //technet. microsoft. com/en-us/library/security/2871997. aspx
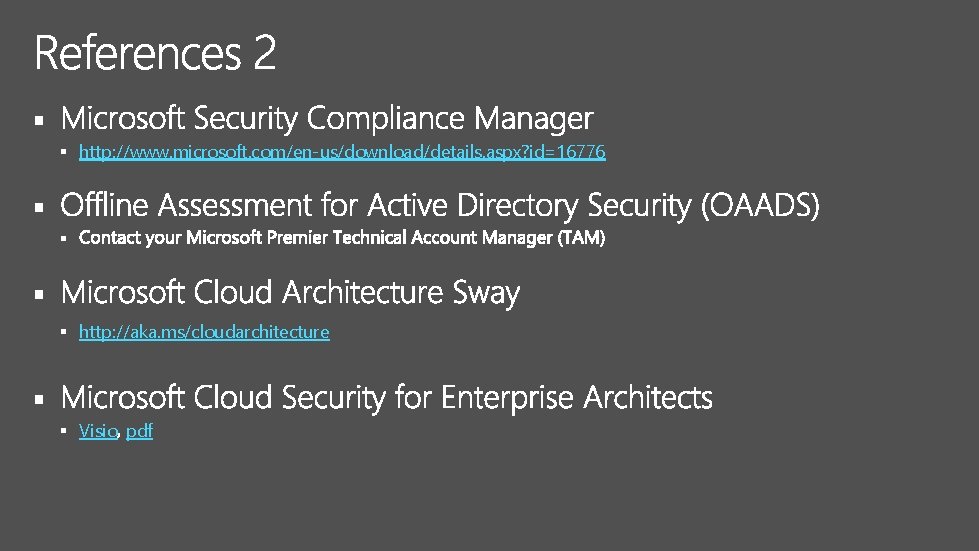
§ § http: //www. microsoft. com/en-us/download/details. aspx? id=16776 § § http: //aka. ms/cloudarchitecture § § Visio pdf
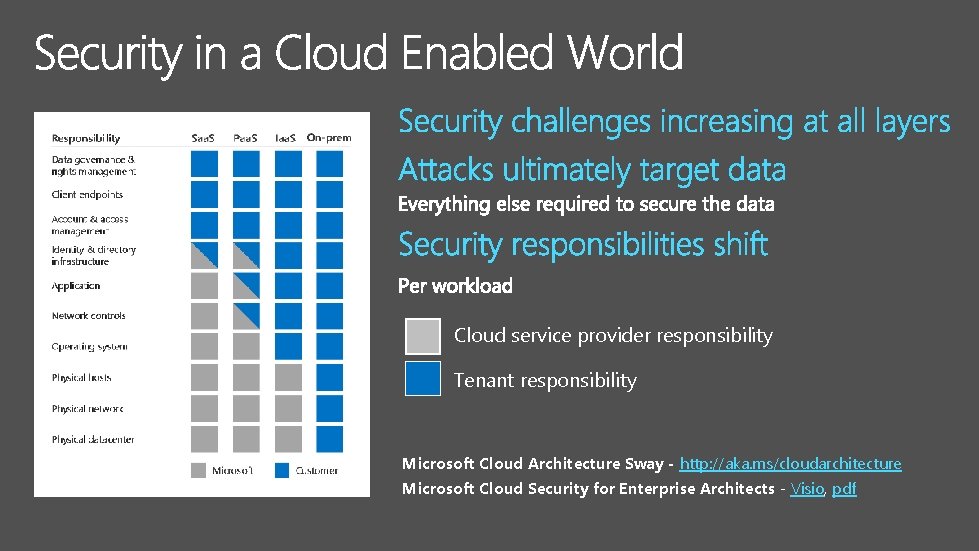
Cloud service provider responsibility Tenant responsibility Microsoft Cloud Architecture Sway - http: //aka. ms/cloudarchitecture Microsoft Cloud Security for Enterprise Architects - Visio, pdf
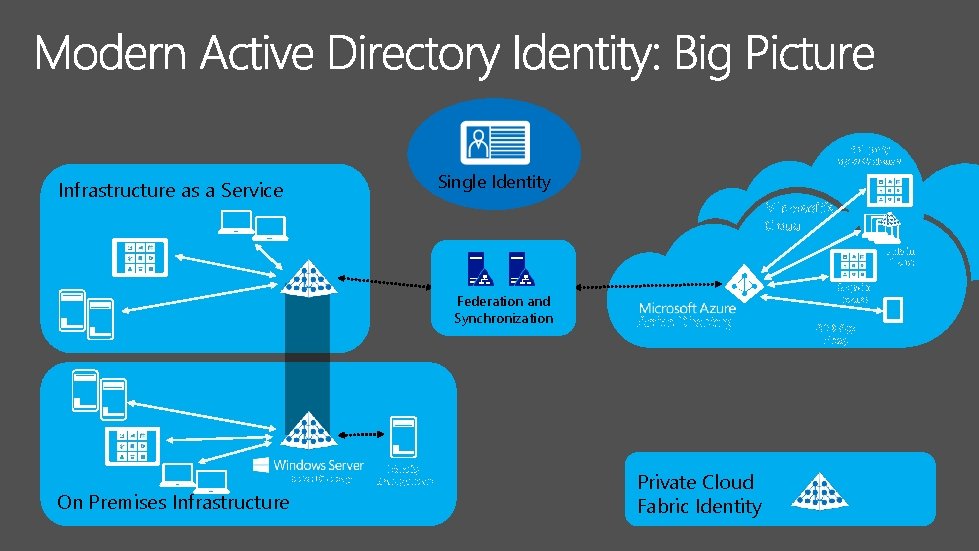
3 rd party apps & clouds Single Identity Infrastructure as a Service Microsoft’s Cloud VMs in Azure Federation and Synchronization Active Directory On Premises Infrastructure Identity Management Apps in Azure Active Directory Private Cloud Fabric Identity AAD App Proxy
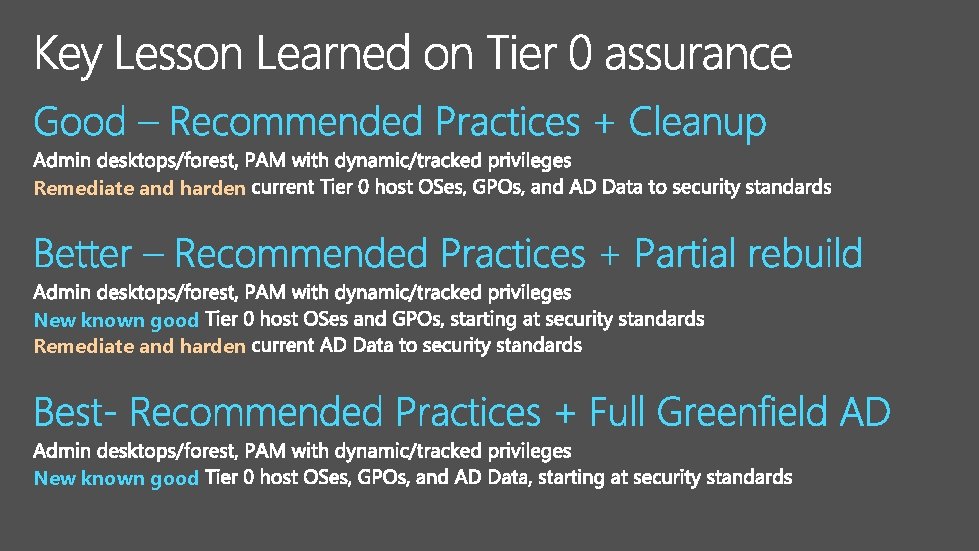
Remediate and harden New known good
- Slides: 43