Prepare by Salameh ahmad alkhawaldeh Layth ahmad alrababah
Prepare by : Salameh ahmad al_khawaldeh Layth ahmad al_rababah WWW
Objective l Ethical Issues l l l Information Technology Ethical challenges l Challenges: Web Design Challenges: Commerce Challenges: Workplace Challenges: Speech Challenges: Computing Resource Abuse Challenges: Privacy Challenges: Intellectual Property Challenges: Other l l WWW l l Legal Issues l What is Ethics? Major Threats Improving the Climate Code of Ethics Self-Assessment Privacy Factor l l l l l Liability Question Basis of Liability Copyrights & Trademarks Website – Product / Service? Warranties Strict Liability Taxation Issues New technology new ethical problems l Example 2
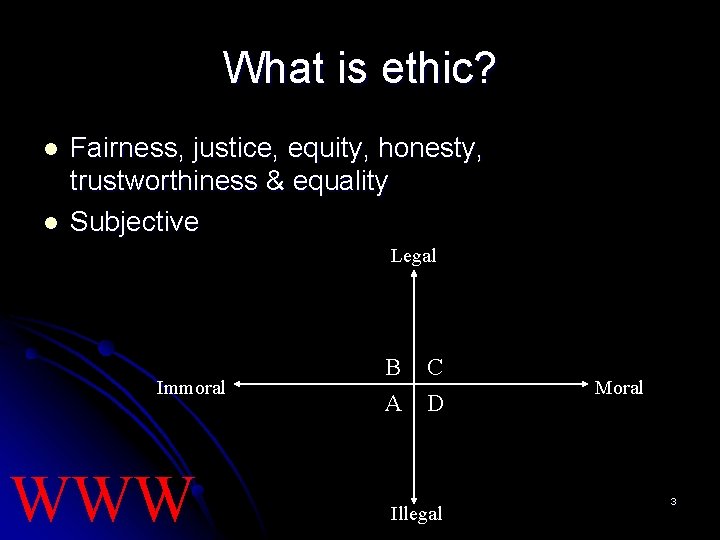
What is ethic? l l Fairness, justice, equity, honesty, trustworthiness & equality Subjective Legal Immoral WWW B A C D Illegal Moral 3
Major threats l l l Faster computers & networks Sophisticated telecommunications & routers Massive distributed databases Eases of access to information & knowledge base Transparency of software WWW 4
Improving the climates l l Top management support Code of ethics Ethics training program Motivation to focus on honesty & integrity WWW 5
WHERE TO START l Bottom-up l l Inculcates ethics behavior at the employee level with full support of top management Top-down l l The actions of the company start with the CEO Extend to a variety of stakeholders WWW 6
Code of ethics l l l A declaration of principles and beliefs that govern how employees of a corporation are to behave Inspirational & disciplinary All-compassing & stable over time WWW 7
Self- Assessment l l l A question-and-answer procedure Allows individuals to appraise & understand their personal knowledge about a particular topic An educational experience WWW 8
Privacy factor l Notice l l Right to be told in advance Choice Final say regarding the use of personal info Access l Access & correct any personal info l Security/integrity l Enforcement l Backed by the courts if any principles are violated WWW 9
THE LIABILITY QUESTION l Liability of Designer l l l Liability of User l l Nontrivial errors Out-of-bound errors Passive negligence Basis of Liability l l Tort law Product liability WWW 10
TORT LAWS ON INTERNET l l l Settling contract problems between e-merchants & ISP Fraud – intent to deceive Negligence – failing to make certain action causing injury / material losses False advertising Misrepresentation – claiming a product will perform certain functions when it could not Trademark violations – under intellectual property law WWW 11
COPYRIGHT l Copyrights l l Ownership of an original work created by an author A form of intellectual property protection covers the ‘look & feel’ and content of printed media Gives author the right to exclude others from using the finished work Good for life of its author + 70 years WWW 12
TRADEMARK / TRADE NAME l l l A word / symbol distinguishing a good from other goods in the market A maze of federal & state laws Web designer – ‘work made for hire’ WWW 13
WEBSITE – PRODUCT/SERVICE? l Product l l l Software sold off the shelf Uniform Commercial Code (UCC) allows developer to limit liability for defective websites though a disclaimer of warranties Service l l Custom-designed software Negligence principles should be usede WWW 14
WARRANTIES l l Assurance made by seller about the goods sold Express warranty l l Implied warranty l l l Offered orally or in writing by maker of products Arises automatically when a sale is made Merchantability Disclaimer l Seller’s intention to protect the business from unwanted liability l http: //www. microsoft. com/misc/info/cpyright. htm WWW 15
STRICT LIABILITY l Joint & several liability for developers, manufacturers & distributors if tort theory applies l Protects web visitor regardless of whether anyone is at fault WWW 16
TAXATION ISSUES l Controversial l Different jurisdiction l Consumers’ reaction WWW 17
New technology = new ethical problems l Traditional rules of conduct are not always applicable to a new medium l A question that often arises: Should a device, a technique or technology be restricted because people can use it for illegal or harmful actions as well as beneficial ones? WWW 18
Example Mobile phones with cameras. Pupils at school take photos of other pupils in the shower, and publish the pictures on the Internet. l Discuss. How to deal with this? WWW 19
Information Technology Ethical Challenges WWW
Challenges: Code of Ethics l No Form of licensing for computer professionals l l Results in no real way to enforce ethical standards within the computing field There is movement within the industry to create a licensing process but there are many issues to be resolved l l l What will be included on the exam? How often will an IT professional be required to renew the license? Developed by several organizations l l Adoption Implementation Monitoring Example: http: //www. acm. org/constitution/code. html WWW 21
Challenges: Web Design l Implementation of features l l l l Pop ups Blocking/filters Aliases and redirecting Cookies Privacy policies Security policies Spyware Use of other design features l l l Javascript Graphics - pictures, buttons, logos, icons Content Design layout Accountability/responsibility Outdated material, inaccurate material WWW 22
Challenges: Commerce l l l Fraud Taxation Free Trade Gambling Auctions Spamming l l l Who were Canter and Siegel? Spamming cell phones? Term papers for sale l Atlanta Journal Constitution article WWW 23
Challenges: Workplace l l l l Accessibility Ergonomics Outsourcing Telecommuting Customer relationships – Vendor relationships Should IT professionals be in the ethics business or should other areas of the business handle these issues? Monitoring l l Should your employer have the right to monitor private email messages? What are the two most popular Web sites for American workers? Playboy and ESPN WWW 24
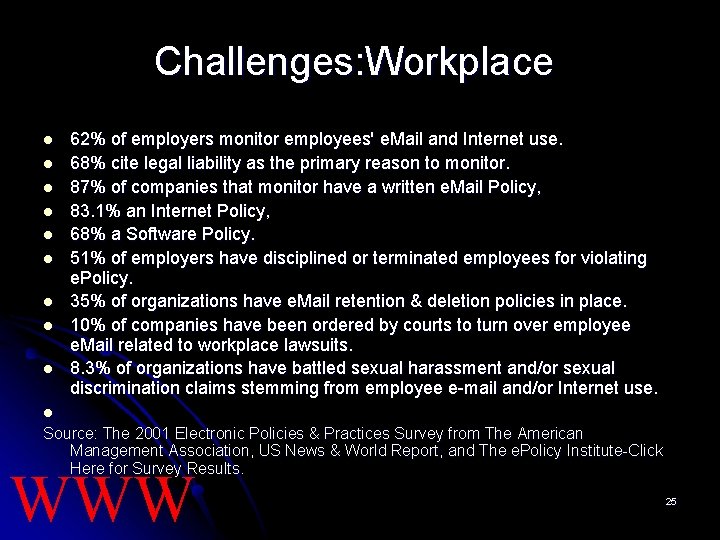
Challenges: Workplace l l l l l 62% of employers monitor employees' e. Mail and Internet use. 68% cite legal liability as the primary reason to monitor. 87% of companies that monitor have a written e. Mail Policy, 83. 1% an Internet Policy, 68% a Software Policy. 51% of employers have disciplined or terminated employees for violating e. Policy. 35% of organizations have e. Mail retention & deletion policies in place. 10% of companies have been ordered by courts to turn over employee e. Mail related to workplace lawsuits. 8. 3% of organizations have battled sexual harassment and/or sexual discrimination claims stemming from employee e-mail and/or Internet use. l Source: The 2001 Electronic Policies & Practices Survey from The American Management Association, US News & World Report, and The e. Policy Institute-Click Here for Survey Results. WWW 25
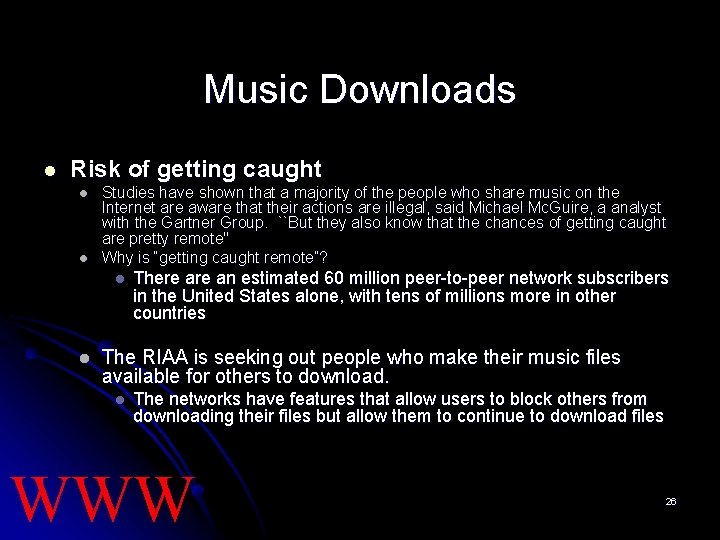
Music Downloads l Risk of getting caught l l Studies have shown that a majority of the people who share music on the Internet are aware that their actions are illegal, said Michael Mc. Guire, a analyst with the Gartner Group. ``But they also know that the chances of getting caught are pretty remote'' Why is “getting caught remote”? l l There an estimated 60 million peer-to-peer network subscribers in the United States alone, with tens of millions more in other countries The RIAA is seeking out people who make their music files available for others to download. l The networks have features that allow users to block others from downloading their files but allow them to continue to download files WWW 26
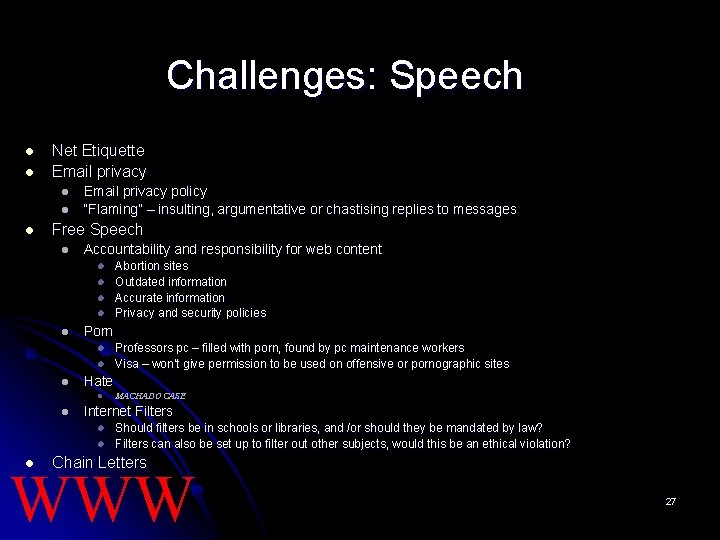
Challenges: Speech l l Net Etiquette Email privacy l l l Email privacy policy “Flaming” – insulting, argumentative or chastising replies to messages Free Speech l Accountability and responsibility for web content l l l Porn l l l MACHADO CASE Internet Filters l l l Professors pc – filled with porn, found by pc maintenance workers Visa – won’t give permission to be used on offensive or pornographic sites Hate l l Abortion sites Outdated information Accurate information Privacy and security policies Should filters be in schools or libraries, and /or should they be mandated by law? Filters can also be set up to filter out other subjects, would this be an ethical violation? Chain Letters WWW 27
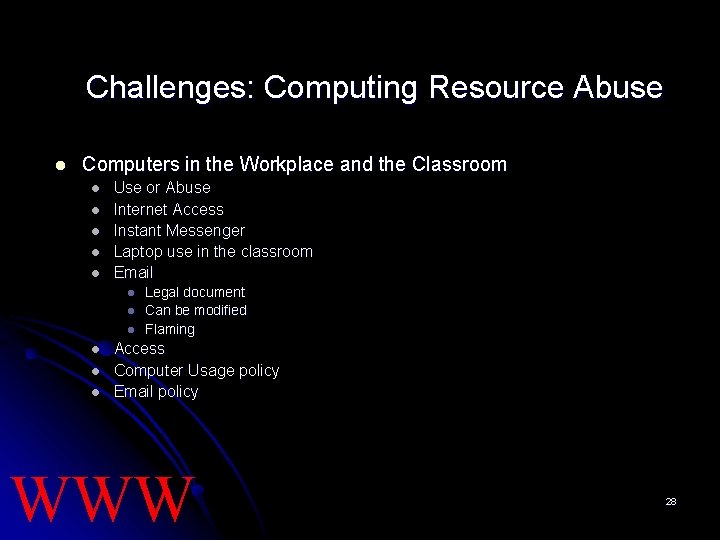
Challenges: Computing Resource Abuse l Computers in the Workplace and the Classroom l l l Use or Abuse Internet Access Instant Messenger Laptop use in the classroom Email l l l Legal document Can be modified Flaming Access Computer Usage policy Email policy WWW 28
Challenges: Computing Resource Abuse l Computer Crime l Viruses l Hackers l Theft l “These cyber swindles and dot-cons present new challenges to law enforcement” said John Ashcroft l US Charges 135 With Net Crimes WWW 29
Challenges: Privacy l Privacy issues are at the top of the list in regards to ethical use of information. l l l USA Patriot Act (post 9/11) l l Loss of control Misuse of information Risk to physical privacy Risk of identity theft (video) Unwanted intrusions into daily life Efforts to detect and deter terrorist activity Datamining corporate data Loss of business and risk of lawsuits due customers being outraged at their loss of data privacy Cookies Privacy policies WWW l 30
Challenges: intellectual Property l l Electronic Copyright Licensing Interoperability Licensing l l l MP 3 l l l Cyberlicenses Shrinkwrap Shareware Freeware RIAA court case against college students University Internet Usage policies Internet Downloads l l Files Graphics Text WWW l 31
Challenges: Intellectual Property l Patent, trade secrets, and copyright law l l l Software Piracy l l l l Who owns the program Who owns the algorithm Why shouldn't I use pirated software? Who am I hurting by doing so? Piracy exists in everywhere. Loss of revenue hurts everyone. All software piracy is illegal and Software piracy is unethical. Various studies have found that the software industry loses approximately $12 billion every year. State Industry Study CD-RW WWW 32
Challenges: Other l l l Decision making using Expert Systems Network Security Software accuracy and reliability who is ethically responsible? l Therac-25 Accidents Killer Robots l The Hughes Whistleblowing Case l WWW 33
Conclusion: Some Ideas to Ponder l Computer ethics today is now a global effort l l What happened? Where did our knowing right from wrong go too? l l l The gap among the rich and poor nations, rich and poor citizens exists. How can it be eliminated or reduced eithically and morally to provide information and services that will move them to into the world of cyberspace? Will the poor be cut off from job opportunities, education, entertainment, medical care, shopping, voting - because they cannot afford a connection to the global information network? Whose laws will apply in cyberspace when hundreds of countries are incorporated into the global network? Are we missing an opportunity to introduce ethics at an early age in children by not integrating these thoughts and practices in video games? Should more controls and regulations be introduced into the system? Will they actually help to improve our moral and ethical behavior? Unethical behavior continues to permeate industry, what measures, policies, codes of conduct be changed to change this behavior? WWW 34
Works Cited: l l l l http: //www. brook. edu/dybdocroot/its/cei/overview/Ten_Com manments_of_Computer_Ethics. htm http: //www. computingcases. org/case_materials/case_mate rials. html http: //www. epolicyinstitute. com/ http: //legacy. eos. ncsu. edu/eos/info/computer_ethics/ http: //www. spa. org/piracy/ http: //www. nd. edu/~rbarger/cases. html http: //ksuweb. kennesaw. edu/~kschwaig/present. ppt WWW 35
- Slides: 35