Predicate Abstraction and Canonical Abstraction for Singlylinked Lists
Predicate Abstraction and Canonical Abstraction for Singly-linked Lists Roman Manevich Mooly Sagiv Tel Aviv University Eran Yahav G. Ramalingam IBM T. J. Watson
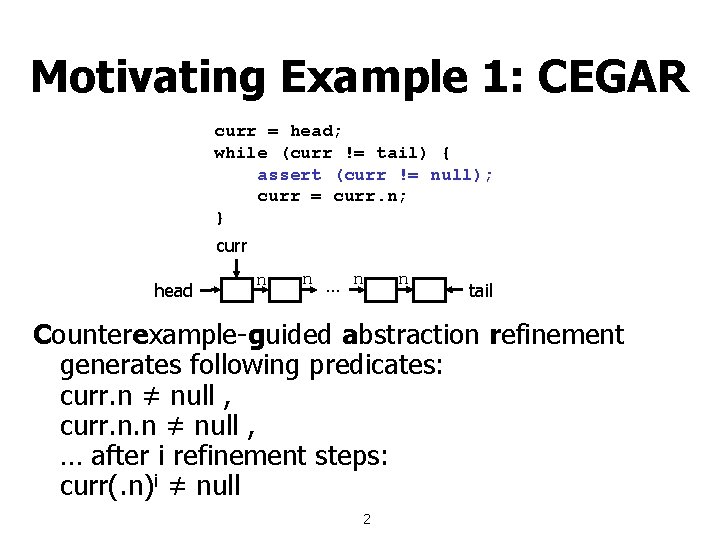
Motivating Example 1: CEGAR curr = head; while (curr != tail) { assert (curr != null); curr = curr. n; } curr head n n … n n tail Counterexample-guided abstraction refinement generates following predicates: curr. n ≠ null , curr. n. n ≠ null , … after i refinement steps: curr(. n)i ≠ null 2
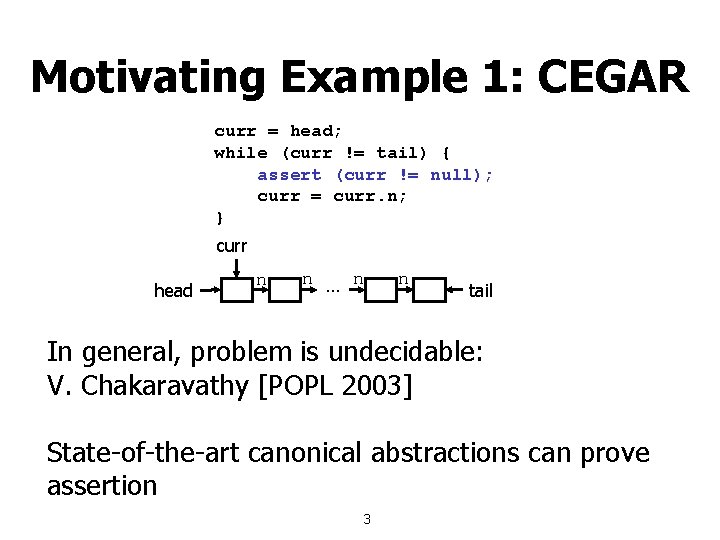
Motivating Example 1: CEGAR curr = head; while (curr != tail) { assert (curr != null); curr = curr. n; } curr head n n … n n tail In general, problem is undecidable: V. Chakaravathy [POPL 2003] State-of-the-art canonical abstractions can prove assertion 3
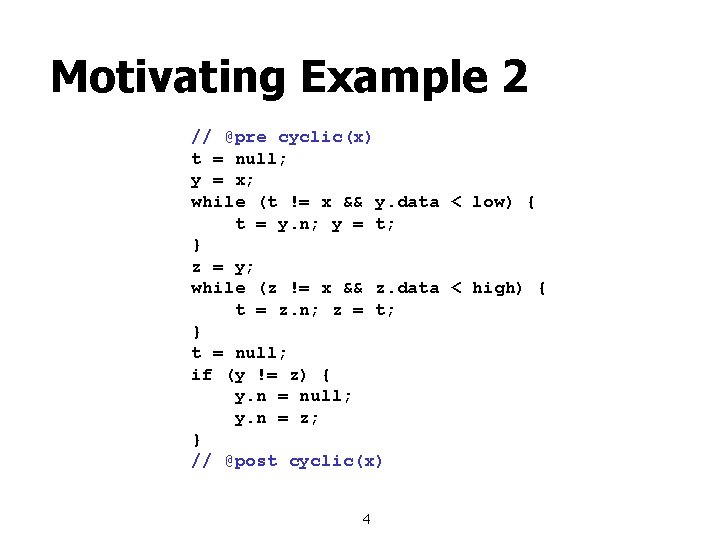
Motivating Example 2 // @pre cyclic(x) t = null; y = x; while (t != x && y. data < low) { t = y. n; y = t; } z = y; while (z != x && z. data < high) { t = z. n; z = t; } t = null; if (y != z) { y. n = null; y. n = z; } // @post cyclic(x) 4

Motivating Example 2 @pre cyclic(x) @post cyclic(x) z z n n n x x n n n n y y 5
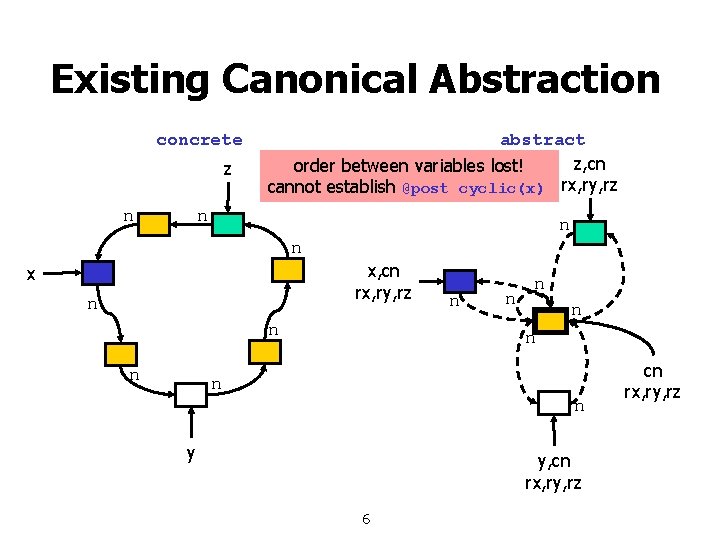
Existing Canonical Abstraction concrete z n abstract z, cn order between variables lost! cannot establish @post cyclic(x) rx, ry, rz n n n x, cn rx, ry, rz x n n n n n y y, cn rx, ry, rz 6 cn rx, ry, rz
Overview and Main Results n n Current predicate abstraction refinement methods not adequate for analyzing heaps Predicate abstraction can simulate arbitrary finite abstract domains n n New family of abstractions for lists n n n Often requires too many predicates Bounded number of sharing patterns Handles cycles more precisely than existing canonical abstractions Encode abstraction with two methods: n n Canonical abstraction Polynomial predicate abstraction 7
Outline n New abstractions for lists n n n n Observations on concrete shapes Static naming scheme Encoding via predicate abstraction Encoding via canonical abstraction Controlling the number of predicates via heap-sharing depth parameter Experimental results Related work Conclusion 8
Concrete Shapes n Assume the following class of (list-) heaps n n n Heap contains only singly-linked lists No garbage (easy to handle) A heap can be decomposed into n n Basic shape (sharing pattern) List lengths 9
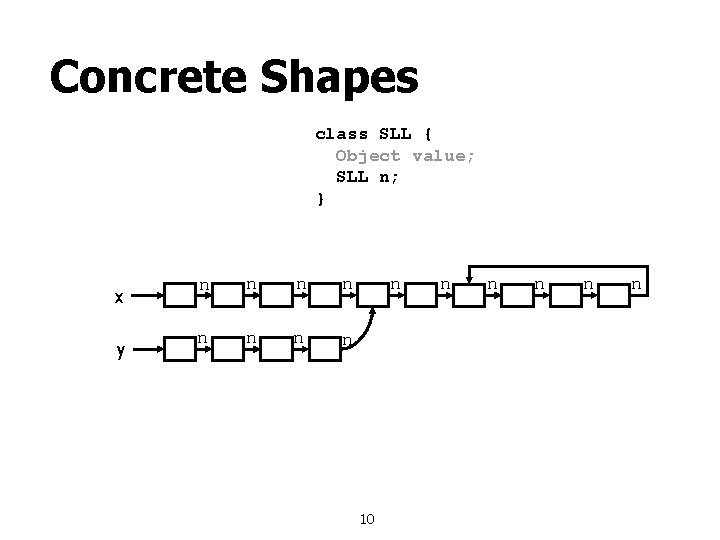
Concrete Shapes class SLL { Object value; SLL n; } x y n n n n n 10 n n n
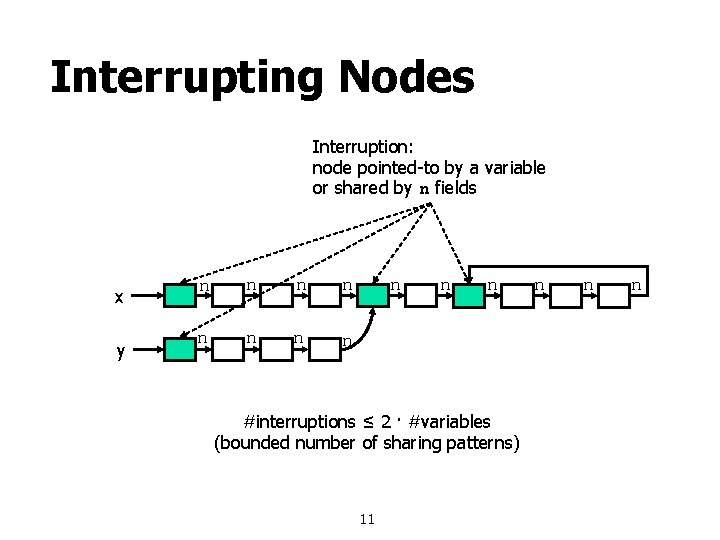
Interrupting Nodes Interruption: node pointed-to by a variable or shared by n fields x y n n n #interruptions ≤ 2 · #variables (bounded number of sharing patterns) 11 n n n
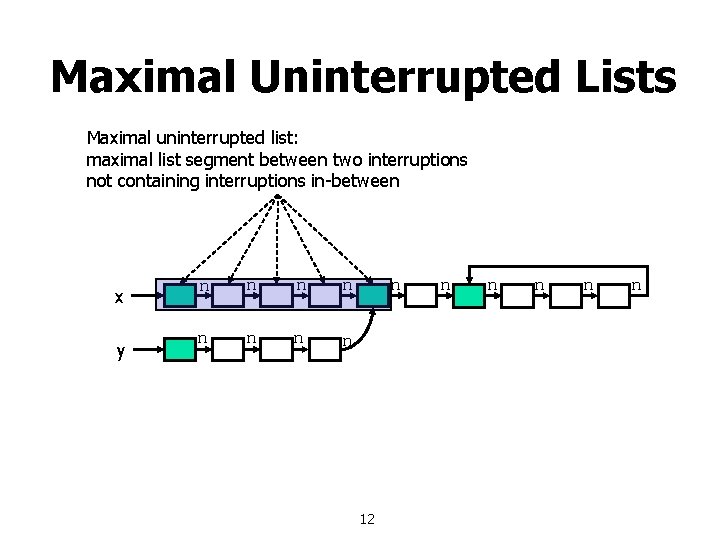
Maximal Uninterrupted Lists Maximal uninterrupted list: maximal list segment between two interruptions not containing interruptions in-between x y n n n n n 12 n n n
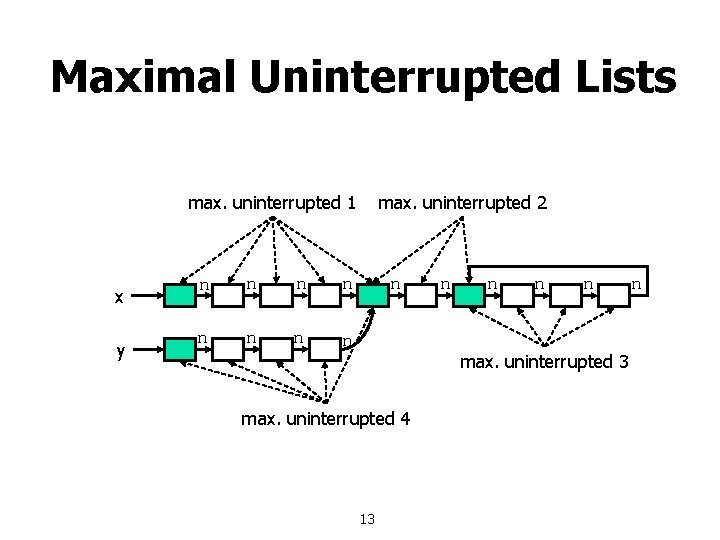
Maximal Uninterrupted Lists max. uninterrupted 1 x y n n n n max. uninterrupted 2 n n n max. uninterrupted 3 max. uninterrupted 4 13 n

Maximal Uninterrupted Lists number of links x y n n 4 4 n n 2 n n 4 n 14 n
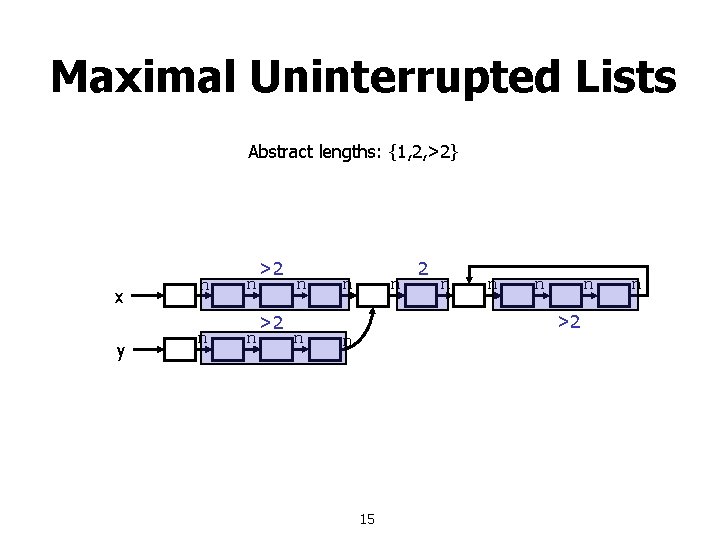
Maximal Uninterrupted Lists Abstract lengths: {1, 2, >2} x y n n >2 >2 n n n n >2 n 15 n
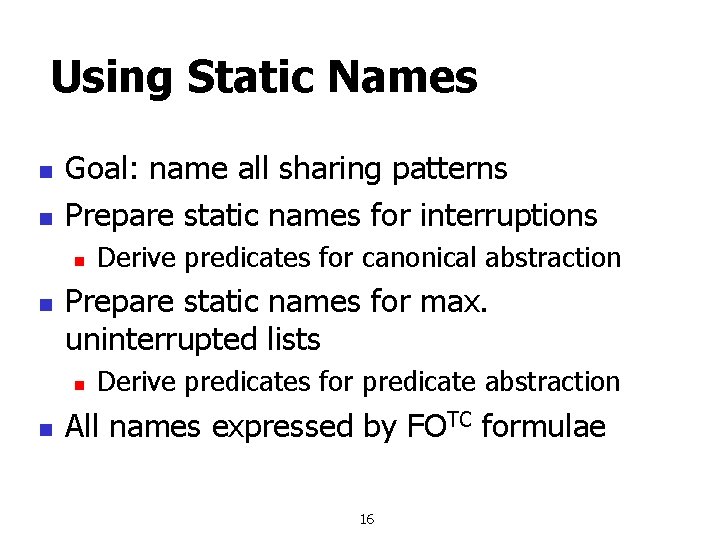
Using Static Names n n Goal: name all sharing patterns Prepare static names for interruptions n n Prepare static names for max. uninterrupted lists n n Derive predicates for canonical abstraction Derive predicates for predicate abstraction All names expressed by FOTC formulae 16
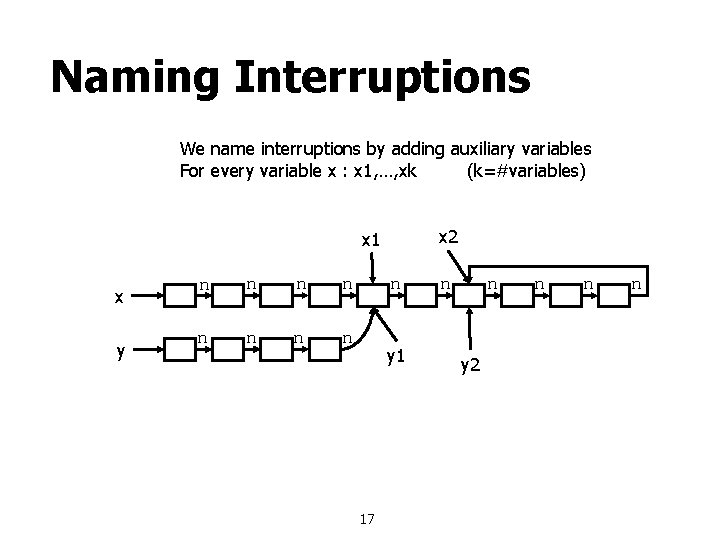
Naming Interruptions We name interruptions by adding auxiliary variables For every variable x : x 1, …, xk (k=#variables) x 2 x 1 x y n n n n n y 1 17 n n y 2 n n n
![Naming Max. Uninterrupted Lists [x 1, x 2] [x 1, y 2] [y 1, Naming Max. Uninterrupted Lists [x 1, x 2] [x 1, y 2] [y 1,](http://slidetodoc.com/presentation_image_h2/6926ce8f14a39a9c5f1ac366b0e10817/image-18.jpg)
Naming Max. Uninterrupted Lists [x 1, x 2] [x 1, y 2] [y 1, x 2] [y 1, y 2] [x, x 1] [x, y 1] x y x 2 x 1 n n n n n y 1 [y, x 1] [y, y 1] 18 n n y 2 n [x 2, x 2] [x 2, y 2] [y 2, x 2] [y 2, y 2] n n

A Predicate Abstraction n For every pair of variables x, y (regular and auxiliary) n n n For every variable x (regular and auxiliary) n n Aliased[x, y] = x and y point to same node UList 1[x, y] = max. uninterrupted list of length 1 UList 2[x, y] = max. uninterrupted list of length 2 UList[x, y] = max. uninterrupted list of any length UList 1[x, null] = max. uninterrupted list of length 1 UList 2[x, null] = max. uninterrupted list of length 2 UList[x, null] = max. uninterrupted list of any length Predicates expressed by FOTC formulae 19
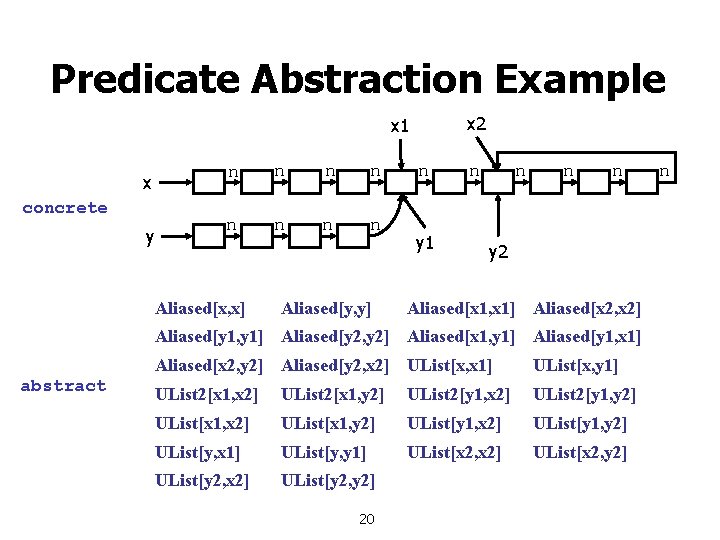
Predicate Abstraction Example x 2 x 1 x concrete y n n n n Aliased[x, x] Aliased[y, y] n y 1 n n y 2 Aliased[x 1, x 1] Aliased[x 2, x 2] Aliased[y 1, y 1] Aliased[y 2, y 2] Aliased[x 1, y 1] Aliased[y 1, x 1] abstract Aliased[x 2, y 2] Aliased[y 2, x 2] UList[x, x 1] UList[x, y 1] UList 2[x 1, x 2] UList 2[x 1, y 2] UList 2[y 1, x 2] UList 2[y 1, y 2] UList[x 1, x 2] UList[x 1, y 2] UList[y 1, x 2] UList[y 1, y 2] UList[y, x 1] UList[y, y 1] UList[x 2, x 2] UList[x 2, y 2] UList[y 2, x 2] UList[y 2, y 2] 20 n
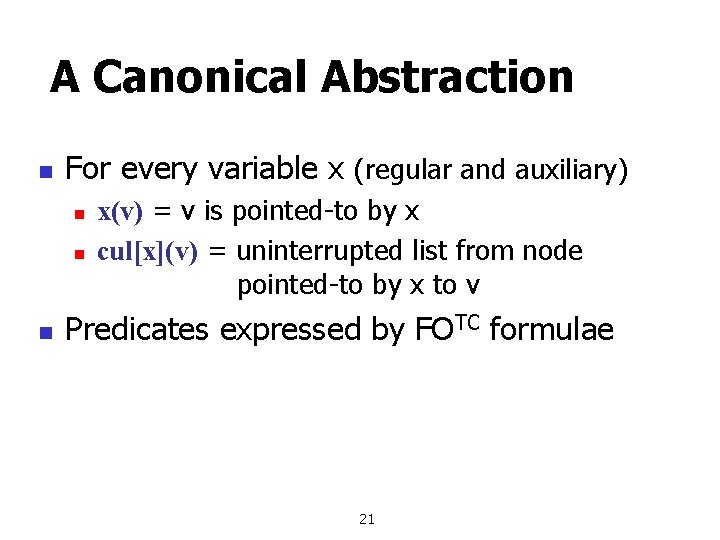
A Canonical Abstraction n For every variable x (regular and auxiliary) n n n x(v) = v is pointed-to by x cul[x](v) = uninterrupted list from node pointed-to by x to v Predicates expressed by FOTC formulae 21
![Canonical Abstraction Example concrete cul[x 1] cul[y 1] cul[x] x y x 2 x Canonical Abstraction Example concrete cul[x 1] cul[y 1] cul[x] x y x 2 x](http://slidetodoc.com/presentation_image_h2/6926ce8f14a39a9c5f1ac366b0e10817/image-22.jpg)
Canonical Abstraction Example concrete cul[x 1] cul[y 1] cul[x] x y x 2 x 1 n n n n n y 1 cul[y] 22 cul[x 2] cul[y 2] n n y 2 n n n
![Canonical Abstraction Example abstract cul[x 1] cul[y 1] cul[x] x y x 2 x Canonical Abstraction Example abstract cul[x 1] cul[y 1] cul[x] x y x 2 x](http://slidetodoc.com/presentation_image_h2/6926ce8f14a39a9c5f1ac366b0e10817/image-23.jpg)
Canonical Abstraction Example abstract cul[x 1] cul[y 1] cul[x] x y x 2 x 1 n n cul[x 2] cul[y 2] n n n n y 1 n cul[y] 23 y 2
![Canonical Abstraction of Cyclic List concrete abstract cul[z] z n n n n x Canonical Abstraction of Cyclic List concrete abstract cul[z] z n n n n x](http://slidetodoc.com/presentation_image_h2/6926ce8f14a39a9c5f1ac366b0e10817/image-24.jpg)
Canonical Abstraction of Cyclic List concrete abstract cul[z] z n n n n x x n n n n n cul[x] cul[y] y y 24
![Canonical Abstraction of Cyclic List abstract pre cul[z] abstract post cul[z] z n n Canonical Abstraction of Cyclic List abstract pre cul[z] abstract post cul[z] z n n](http://slidetodoc.com/presentation_image_h2/6926ce8f14a39a9c5f1ac366b0e10817/image-25.jpg)
Canonical Abstraction of Cyclic List abstract pre cul[z] abstract post cul[z] z n n n x n n n n cul[x] z n cul[x] cul[y] y y 25

Heap-sharing Depth In this example the heap-sharing depth is 2 In practice depth expected to be low (≤ 1) x 2 x 1 x y n n n n n y 1 26 n n y 2 n n n
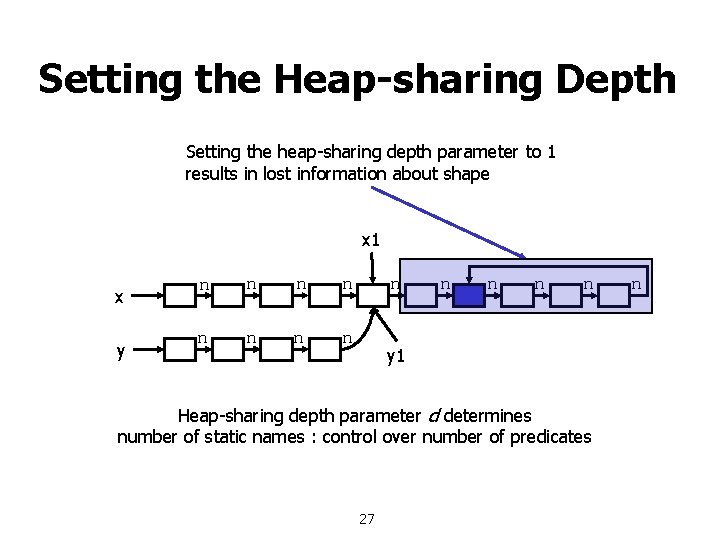
Setting the Heap-sharing Depth Setting the heap-sharing depth parameter to 1 results in lost information about shape x 1 x y n n n n y 1 Heap-sharing depth parameter d determines number of static names : control over number of predicates 27 n
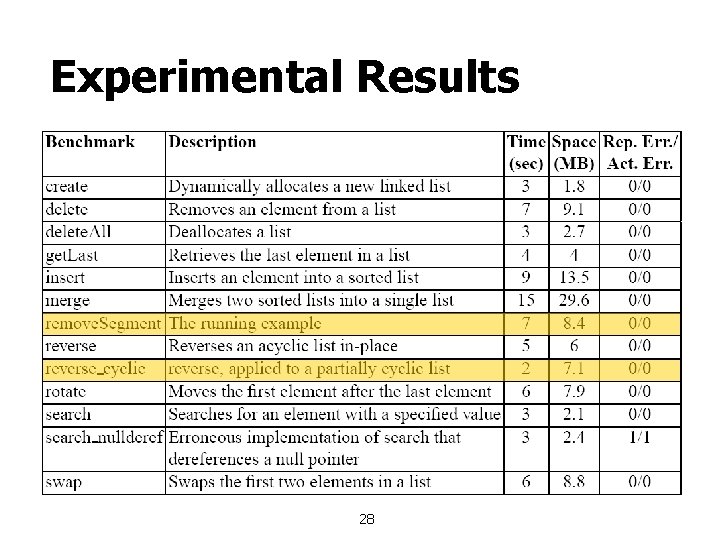
Experimental Results 28
![Related Work n Dor, Rode and Sagiv [SAS ’ 00] n n Sagiv, Reps Related Work n Dor, Rode and Sagiv [SAS ’ 00] n n Sagiv, Reps](http://slidetodoc.com/presentation_image_h2/6926ce8f14a39a9c5f1ac366b0e10817/image-29.jpg)
Related Work n Dor, Rode and Sagiv [SAS ’ 00] n n Sagiv, Reps and Wilhelm [TOPLAS ‘ 02] n n Semi-automatic predicate abstraction for shape analysis Balaban, Pnueli and Zuck [VMCAI ’ 05] n n General framework + abstractions for lists Dams and Namjoshi [VMCAI ’ 03] n n Checking cleanness in lists Predicate abstraction for shapes via small models Deutsch [PLDI ’ 94] n Symbolic access paths with lengths 29
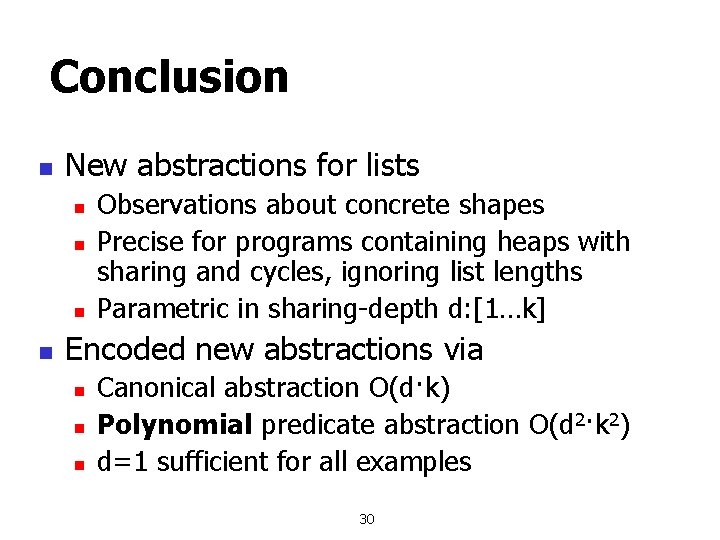
Conclusion n New abstractions for lists n n Observations about concrete shapes Precise for programs containing heaps with sharing and cycles, ignoring list lengths Parametric in sharing-depth d: [1…k] Encoded new abstractions via n n n Canonical abstraction O(d·k) Polynomial predicate abstraction O(d 2·k 2) d=1 sufficient for all examples 30

Missing from Talk n n n Simulating abstract domains by pred. abs. Formal definition of abstractions Abstract transformers n n n Decidable logic can be automatically derived Abstraction equivalence: for every two concrete heaps H 1, H 2 βPA(H 1)=βPA(H 2) iff βC(H 1)=βC(H 2) Abstractions with less predicates n n Cycle breaking Linear static naming scheme 31
Merci 32
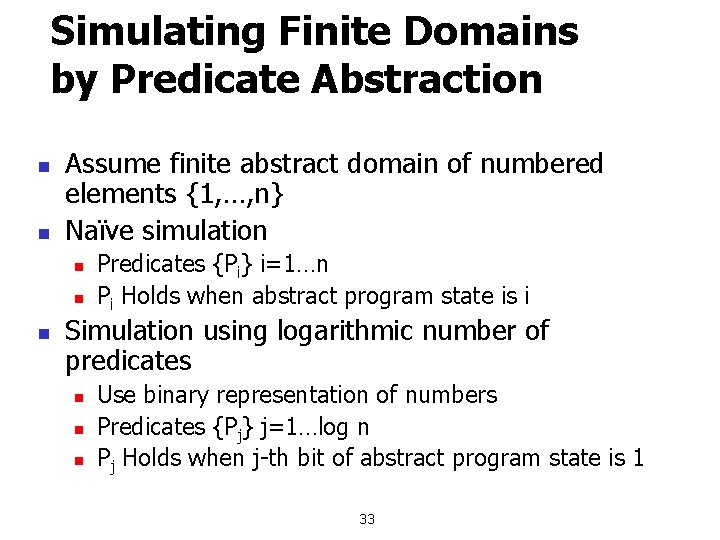
Simulating Finite Domains by Predicate Abstraction n n Assume finite abstract domain of numbered elements {1, …, n} Naïve simulation n Predicates {Pi} i=1…n Pi Holds when abstract program state is i Simulation using logarithmic number of predicates n n n Use binary representation of numbers Predicates {Pj} j=1…log n Pj Holds when j-th bit of abstract program state is 1 33
- Slides: 33