Practical Session 10 Error Detecting and Correcting Codes
- Slides: 19
Practical Session 10 Error Detecting and Correcting Codes
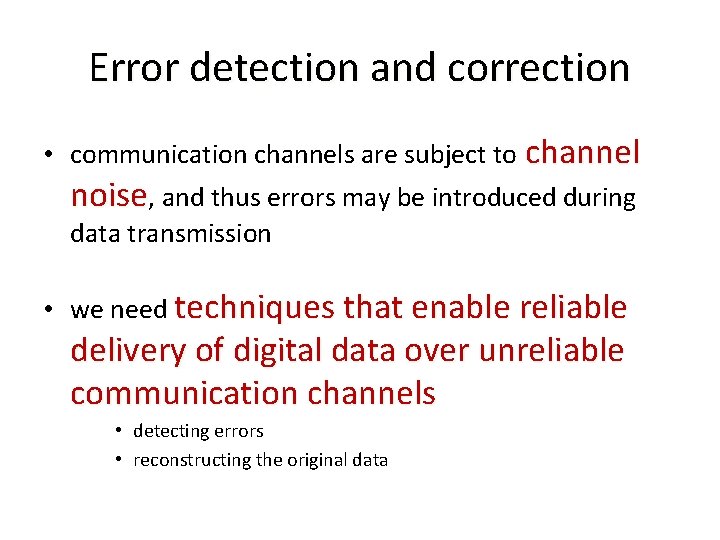
Error detection and correction • communication channels are subject to channel noise, and thus errors may be introduced during data transmission • we need techniques that enable reliable delivery of digital data over unreliable communication channels • detecting errors • reconstructing the original data
Error detection and correction • General idea: add some redundancy (i. e. some extra data) to a message extra data • This extra data is used – to check consistency of the delivered message – to recover data determined to be corrupted
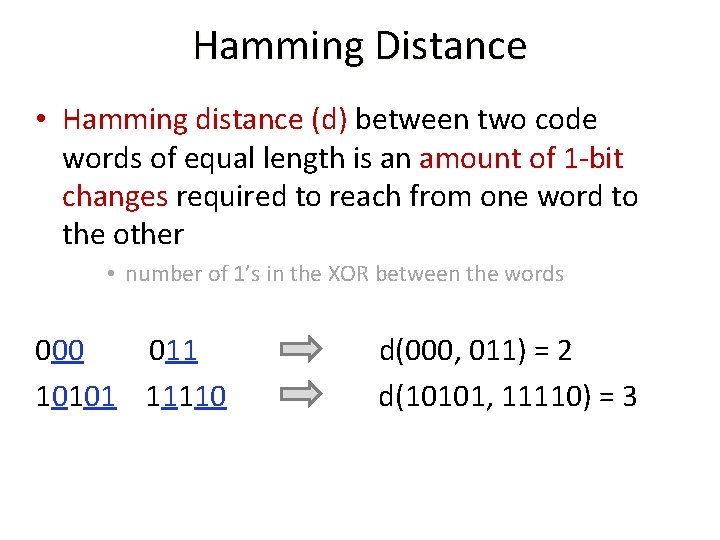
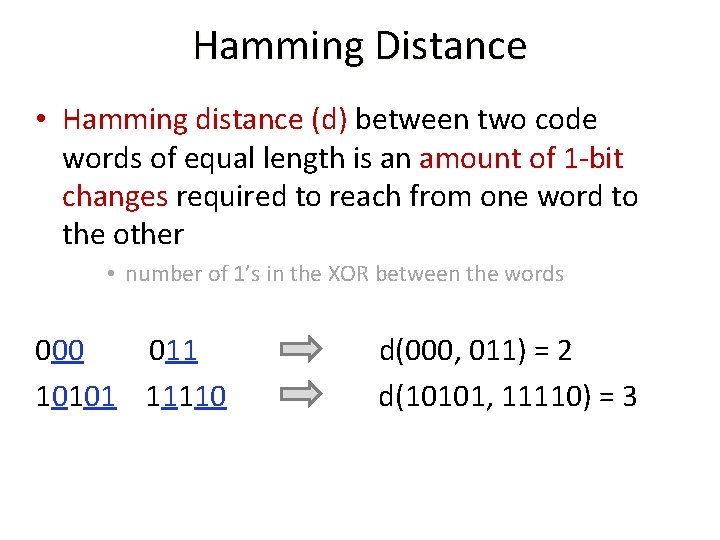
Hamming Distance • Hamming distance (d) between two code Hamming distance (d) words of equal length is an amount of 1 -bit changes required to reach from one word to changes the other • number of 1’s in the XOR between the words 000 011 d(000, 011) = 2 10101 11110 d(10101, 11110) = 3
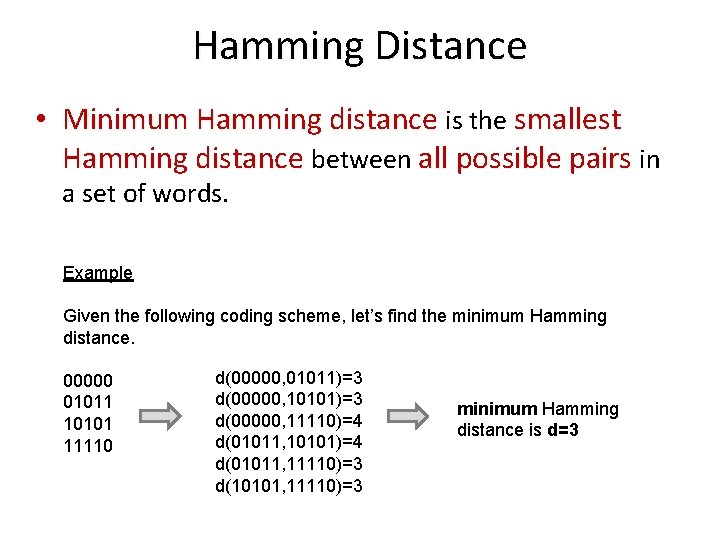
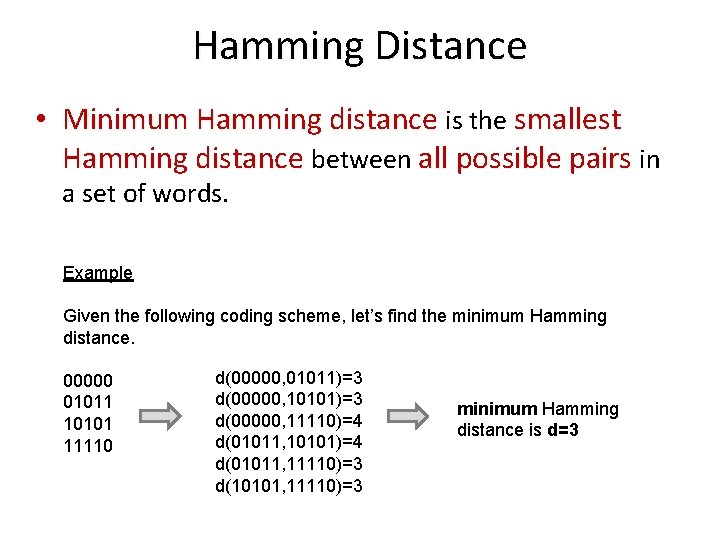
Hamming Distance • Minimum Hamming distance is the smallest Hamming distance between all possible pairs in a set of words. Example Given the following coding scheme, let’s find the minimum Hamming distance. 00000 01011 10101 11110 d(00000, 01011)=3 d(00000, 10101)=3 d(00000, 11110)=4 d(01011, 10101)=4 d(01011, 11110)=3 d(10101, 11110)=3 minimum Hamming distance is d=3
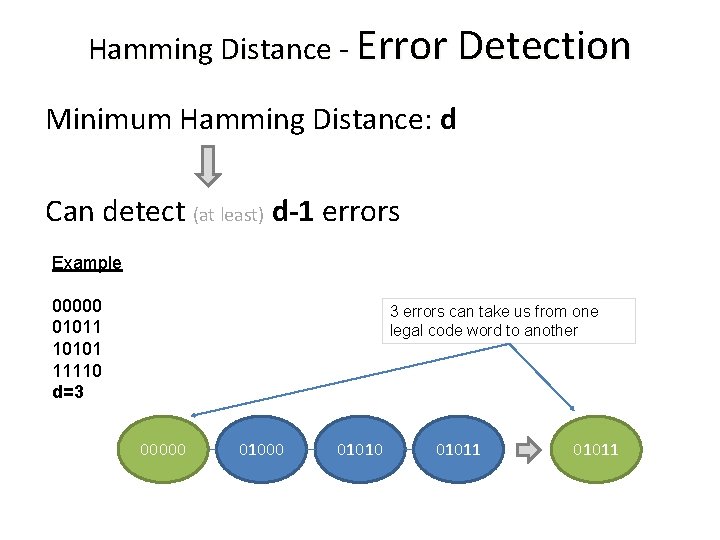
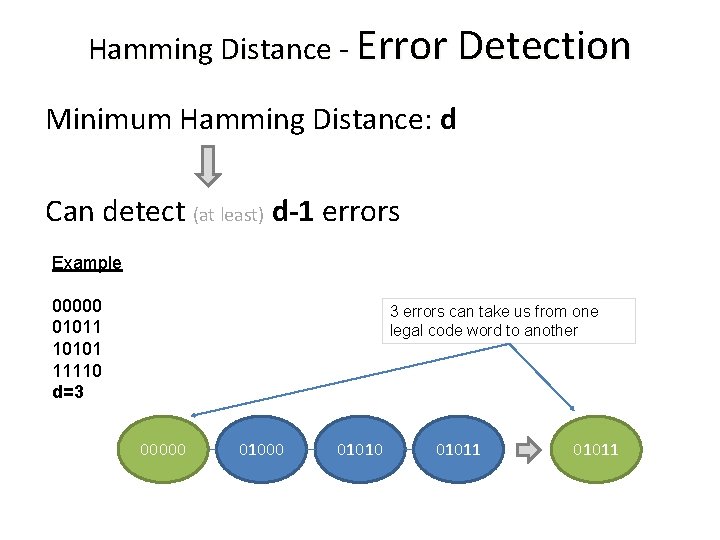
Hamming Distance - Error Detection Minimum Hamming Distance: d Can detect (at least) d-1 errors Example 00000 01011 10101 11110 d=3 3 errors can take us from one legal code word to another 00000 01010 01011
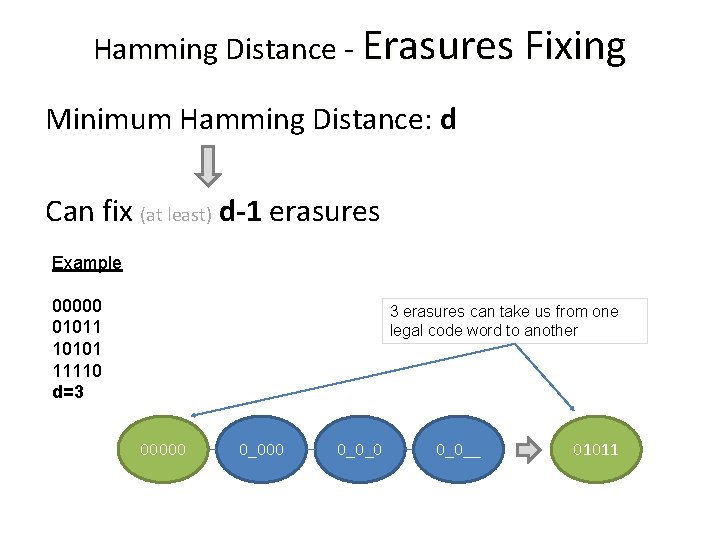
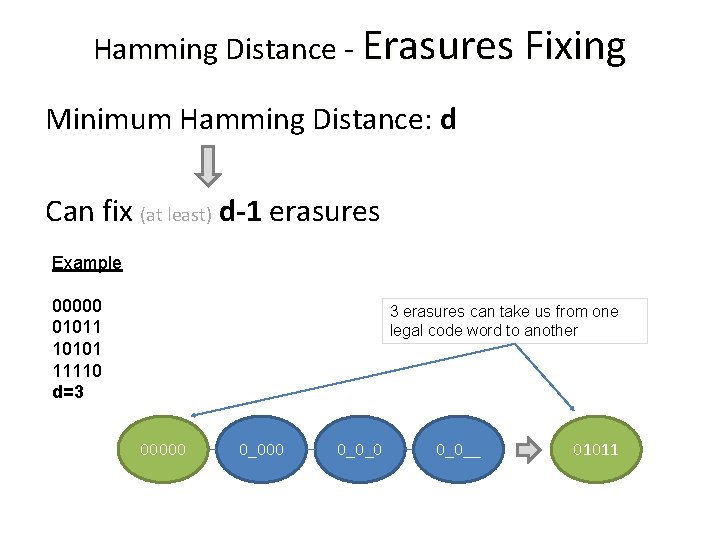
Hamming Distance - Erasures Fixing Minimum Hamming Distance: d Can fix (at least) d-1 erasures Example 00000 01011 10101 11110 d=3 3 erasures can take us from one legal code word to another 00000 0_0_0 0_0__ 01011
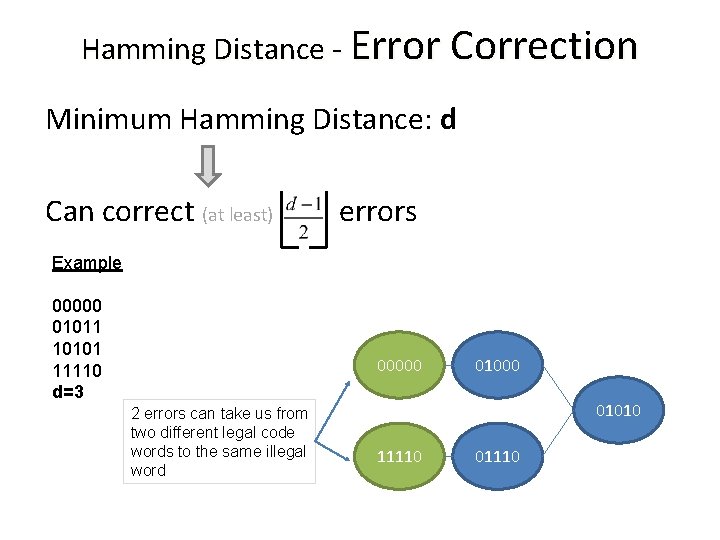
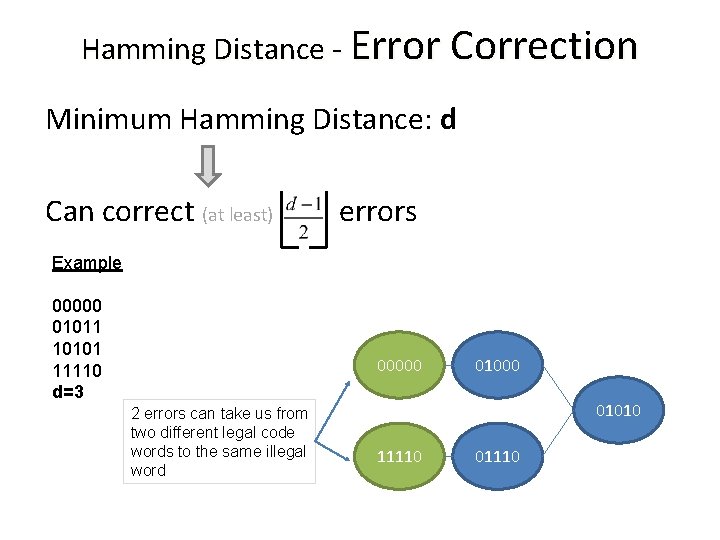
Hamming Distance - Error Correction Minimum Hamming Distance: d Can correct (at least) errors Example 00000 01011 10101 11110 d=3 00000 2 errors can take us from two different legal code words to the same illegal word 01000 01010 11110 01110
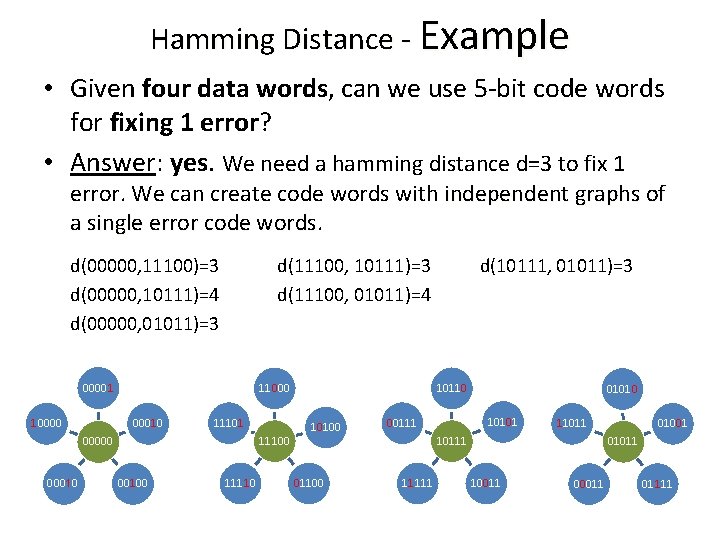
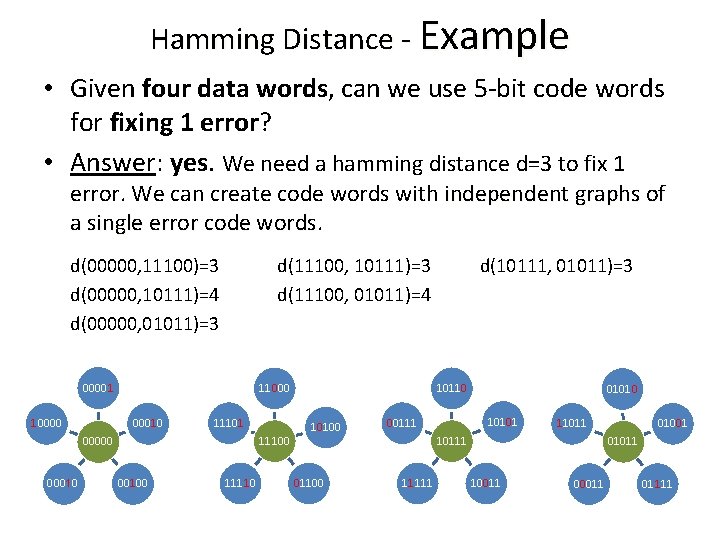
Hamming Distance - Example • Given four data words, can we use 5 -bit code words for fixing 1 error? • Answer: yes. We need a hamming distance d=3 to fix 1 error. We can create code words with independent graphs of a single error code words d(00000, 11100)=3 d(00000, 10111)=4 d(00000, 01011)=3 d(11100, 10111)=3 d(11100, 01011)=4 00001 10000 11101 11100 00010 10110 11000 000100 11110 d(10111, 01011)=3 10100 010101 00111 11111 01001 11011 01011 10011 01111
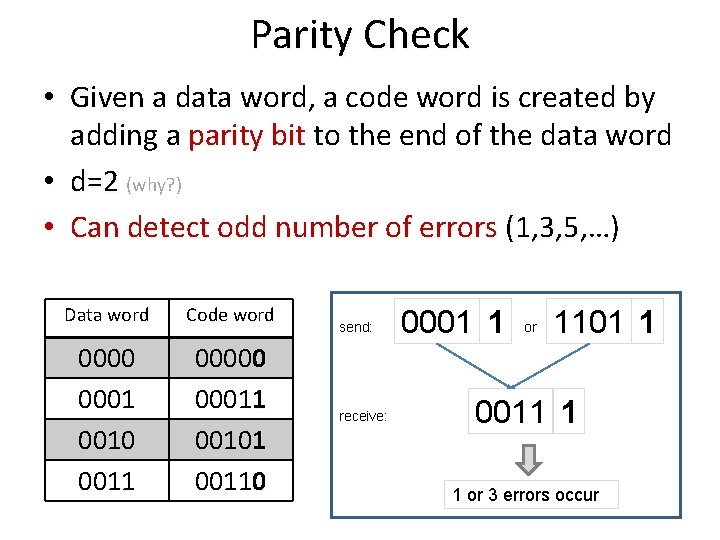
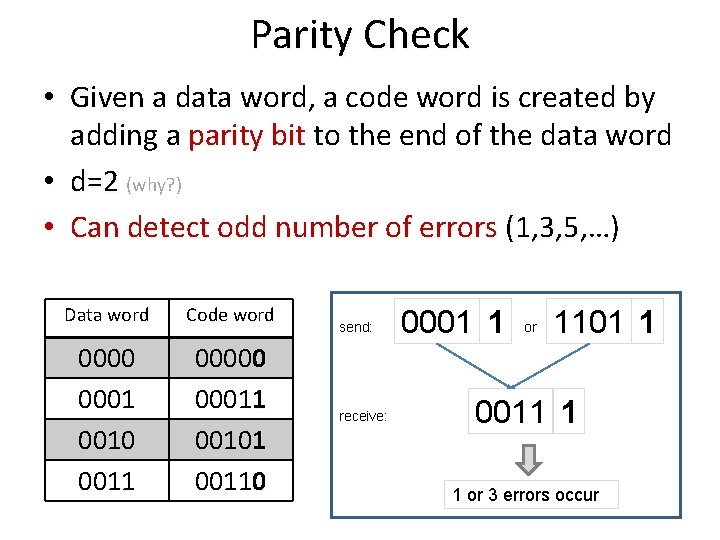
Parity Check • Given a data word, a code word is created by adding a parity bit to the end of the data word parity bit • d=2 (why? ) • Can detect odd number of errors (1, 3, 5, …) Data word Code word 0000 0001 0010 0011 00000 00011 00101 00110 send: receive: 0001 1 or 1101 1 0011 1 1 or 3 errors occur
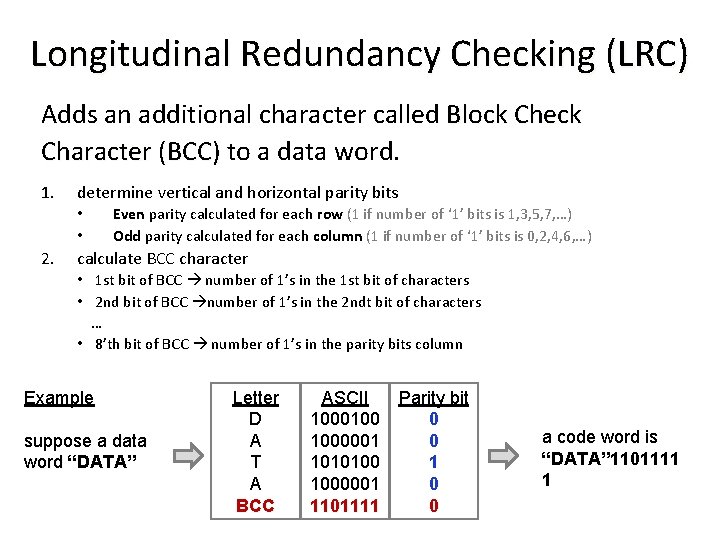
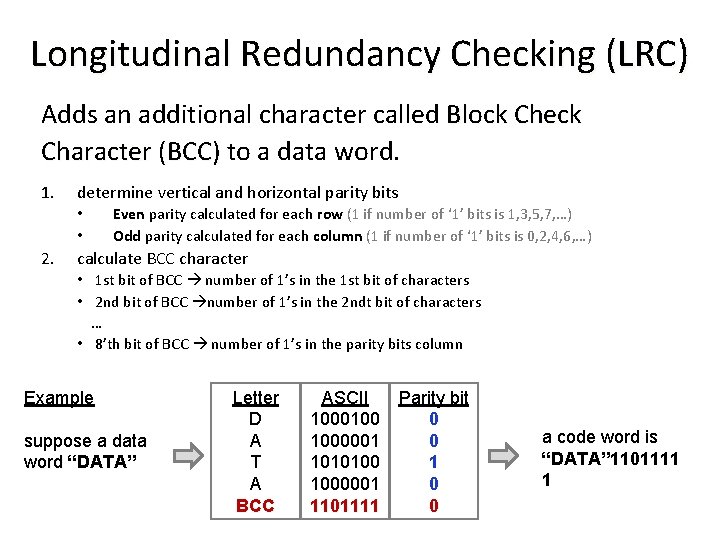
Longitudinal Redundancy Checking (LRC) Adds an additional character called Block Check Character (BCC) to a data word. Character (BCC) 1. determine vertical and horizontal parity bits • • 2. Even parity calculated for each row (1 if number of ‘ 1’ bits is 1, 3, 5, 7, …) Odd parity calculated for each column (1 if number of ‘ 1’ bits is 0, 2, 4, 6, …) calculate BCC character • 1 st bit of BCC number of 1’s in the 1 st bit of characters • 2 nd bit of BCC number of 1’s in the 2 ndt bit of characters … • 8’th bit of BCC number of 1’s in the parity bits column Example suppose a data word “DATA” Letter D A T A BCC ASCII 1000100 1000001 1010100 1000001 1101111 Parity bit 0 0 1 0 0 a code word is “DATA” 1101111 1
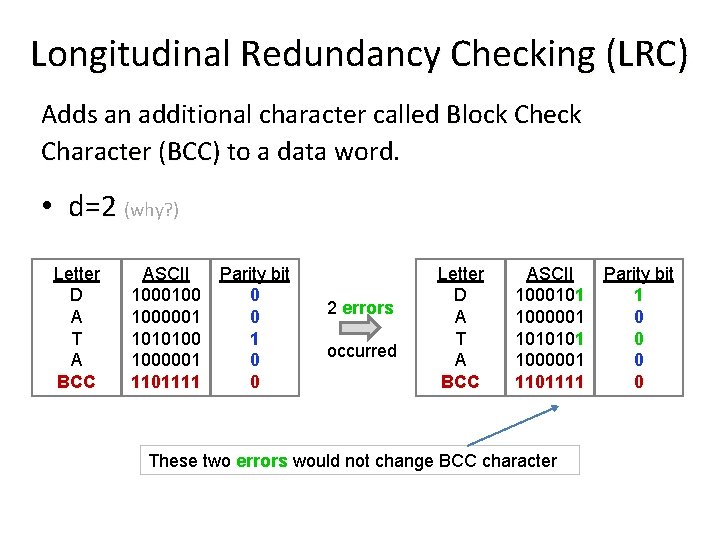
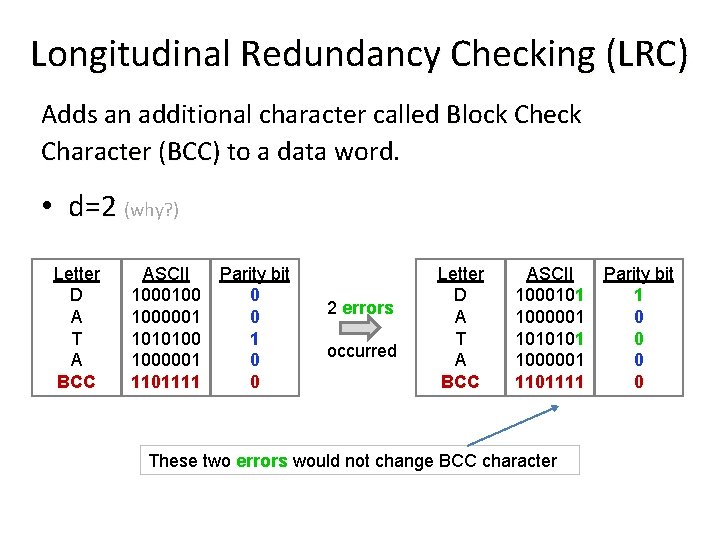
Longitudinal Redundancy Checking (LRC) Adds an additional character called Block Check Character (BCC) to a data word. Character (BCC) • d=2 (why? ) Letter D A T A BCC ASCII 1000100 1000001 1010100 1000001 1101111 Parity bit 0 0 1 0 0 2 errors occurred Letter D A T A BCC ASCII 1000101 1000001 1010101 1000001 1101111 These two errors would not change BCC character Parity bit 1 0 0
Cyclic Redundancy Check • CRC is an error-detecting code • Given a data, its non trivial (cryptographic) challenge to find another data with the same CRC code. CRC can protect data (even from deliberate damage)
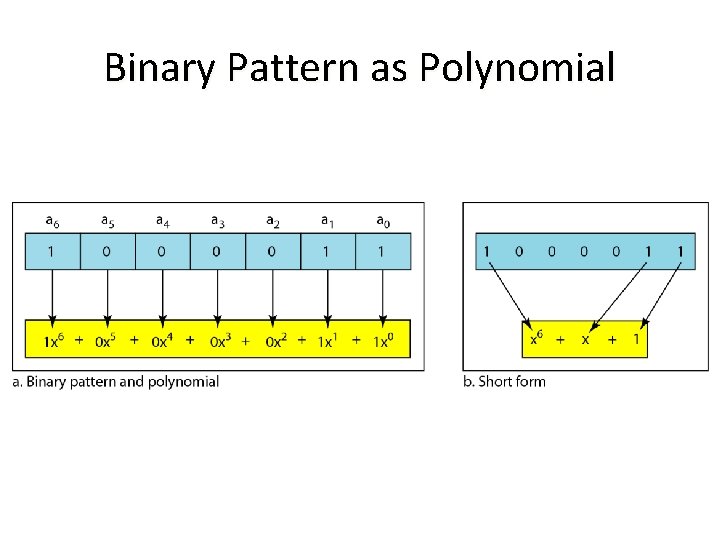
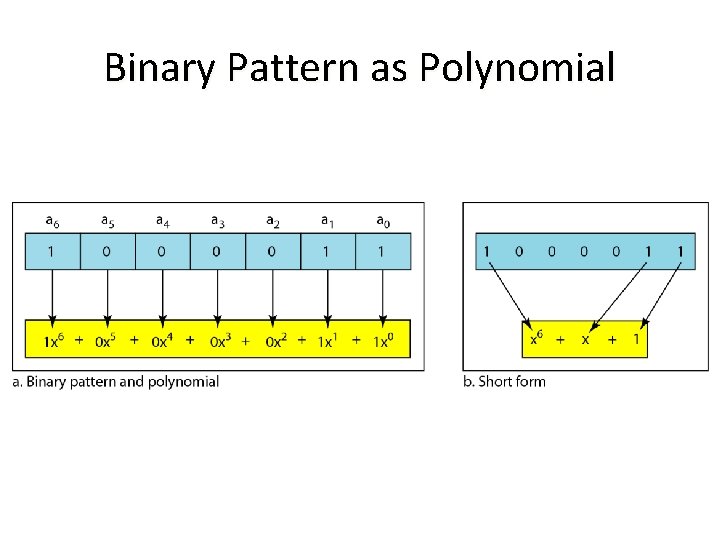
Binary Pattern as Polynomial
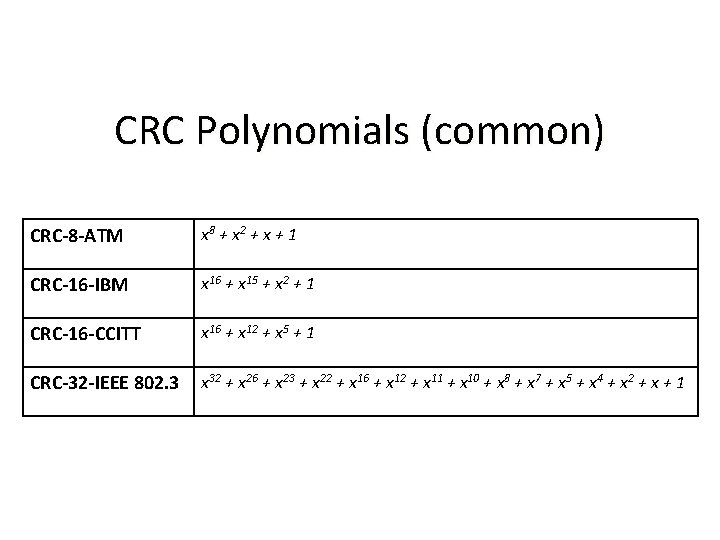
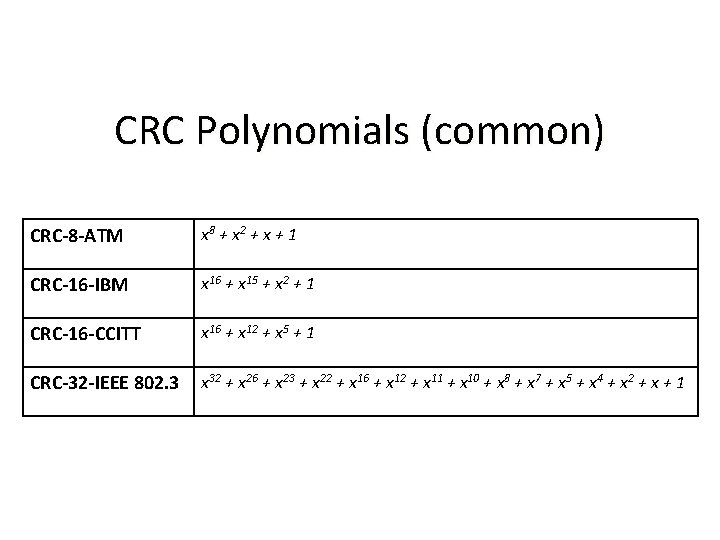
CRC Polynomials (common) CRC-8 -ATM x 8 + x 2 + x + 1 CRC-16 -IBM x 16 + x 15 + x 2 + 1 CRC-16 -CCITT x 16 + x 12 + x 5 + 1 CRC-32 -IEEE 802. 3 x 32 + x 26 + x 23 + x 22 + x 16 + x 12 + x 11 + x 10 + x 8 + x 7 + x 5 + x 4 + x 2 + x + 1
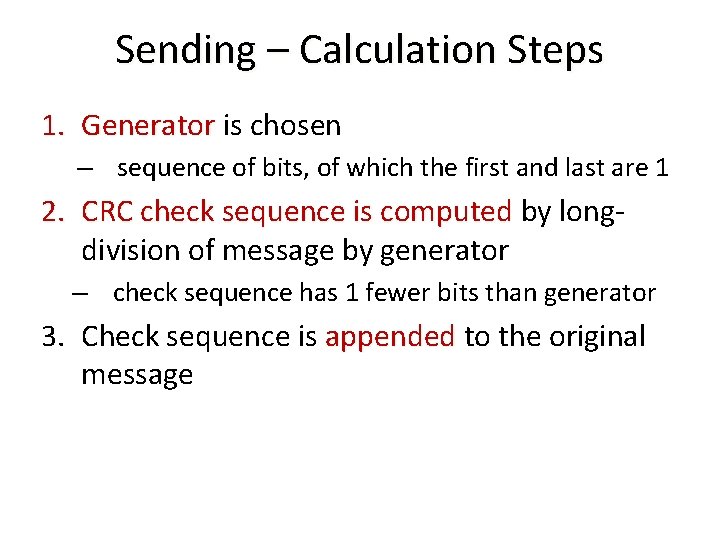
Sending – Calculation Steps 1. Generator is chosen – sequence of bits, of which the first and last are 1 2. CRC check sequence is computed by long. CRC check sequence is computed division of message by generator – check sequence has 1 fewer bits than generator 3. Check sequence is appended to the original message
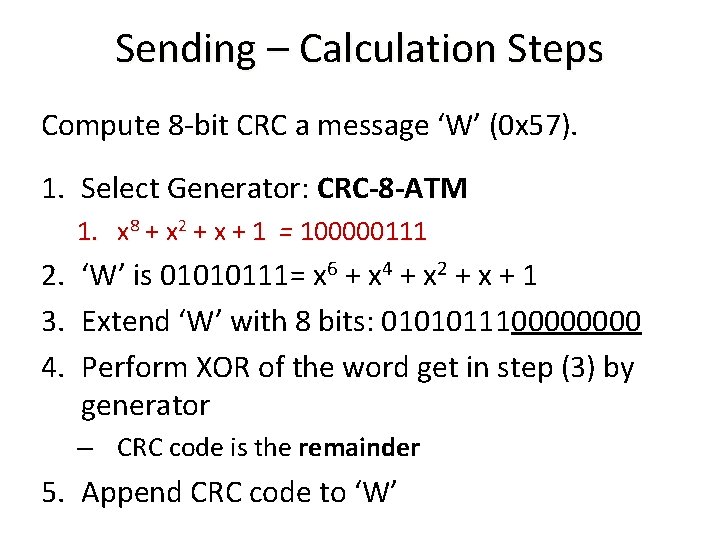
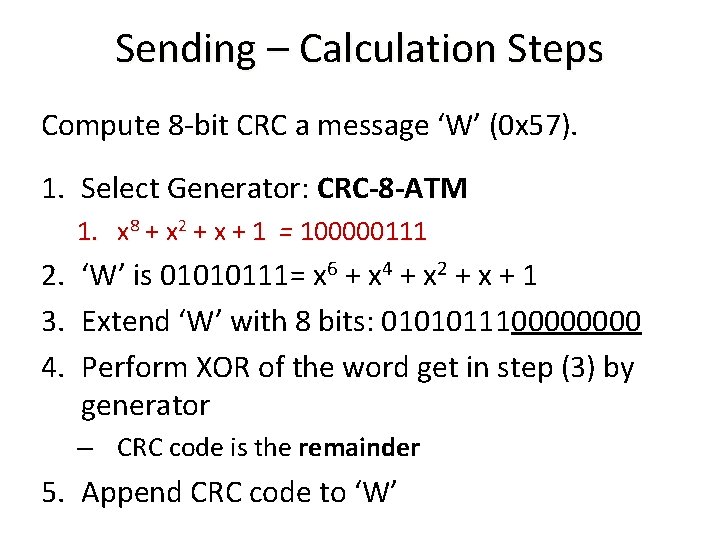
Sending – Calculation Steps Compute 8 -bit CRC a message ‘W’ (0 x 57). 1. Select Generator: CRC-8 -ATM 1. x 8 + x 2 + x + 1 = 100000111 2. ‘W’ is 01010111= x 6 + x 4 + x 2 + x + 1 3. Extend ‘W’ with 8 bits: 010101110000 4. Perform XOR of the word get in step (3) by generator – CRC code is the remainder 5. Append CRC code to ‘W’
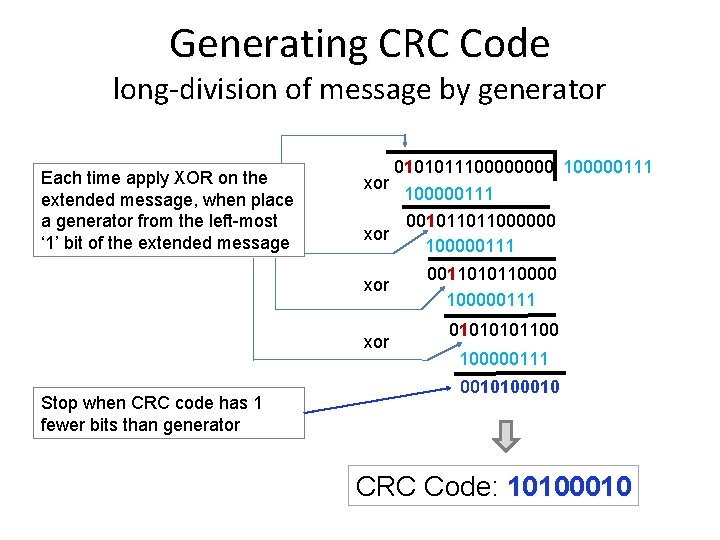
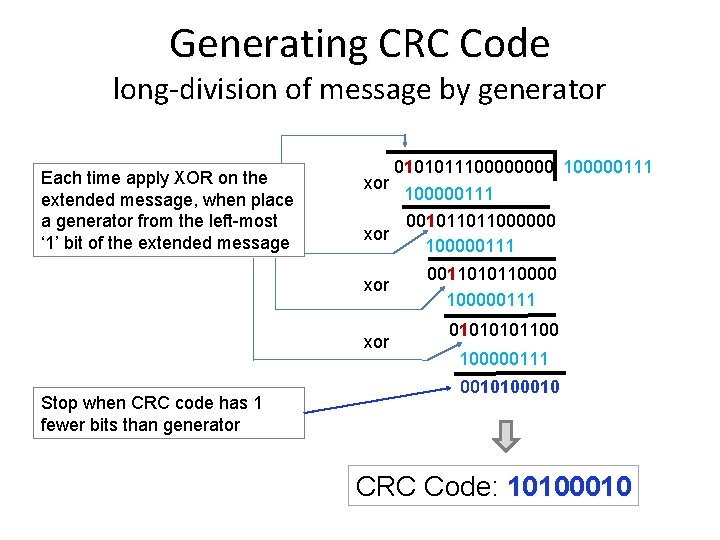
Generating CRC Code long-division of message by generator Each time apply XOR on the extended message, when place a generator from the left-most ‘ 1’ bit of the extended message xor 100000111 001011011000000 xor 100000111 xor Stop when CRC code has 1 fewer bits than generator 0101011100000111 00110101100000111 0101100 100000111 0010100010 CRC Code: 10100010
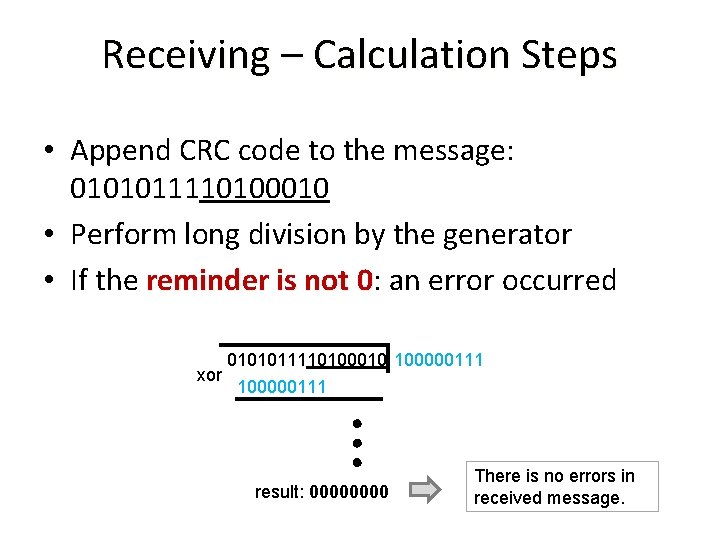
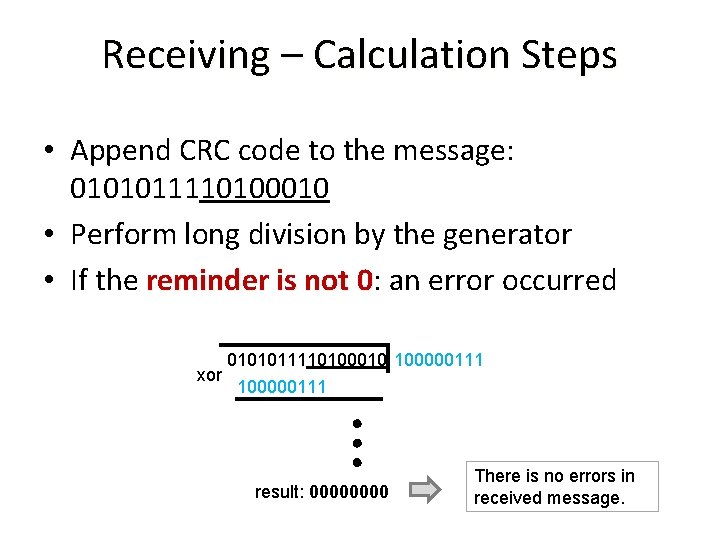
Receiving – Calculation Steps • Append CRC code to the message: 0101011110100010 • Perform long division by the generator • If the reminder is not 0: an error occurred 0 0101011110100010 100000111 xor 100000111 result: 0000 There is no errors in received message.