PostSilicon Verification under Limited Observability Ganesh Gopalakrishnan School
Post-Silicon Verification under Limited Observability Ganesh Gopalakrishnan School of Computing, University of Utah, Salt Lake City, UT 84112 Ching Tsun Chou Intel Corporation, 3600 Juliette Lane, Santa Clara, CA Supported in part by NSF award CCR 0219805 1
Why Post-Silicon Verification? n Why verify the silicon? Isn’t doing FV enough? (!) – FV cannot be applied to entire MP systems yet • n MP systems contain several CPUs and several “chip-sets” We cannot verify the silicon exhaustively - so why bother? – Formal analysis applied to particular executions can yield far more insights than ad hoc criteria applied to executions • e. g. “Runtime Verification” of software (Havelund, Rosu, Lee , . . ) 2
Why Post-Silicon Verification? Runtime verification can cover more! n – – 1 GHz in silicon instead of 100 Hz during simulation With well-designed “stress tests” one often finds out a lot 3
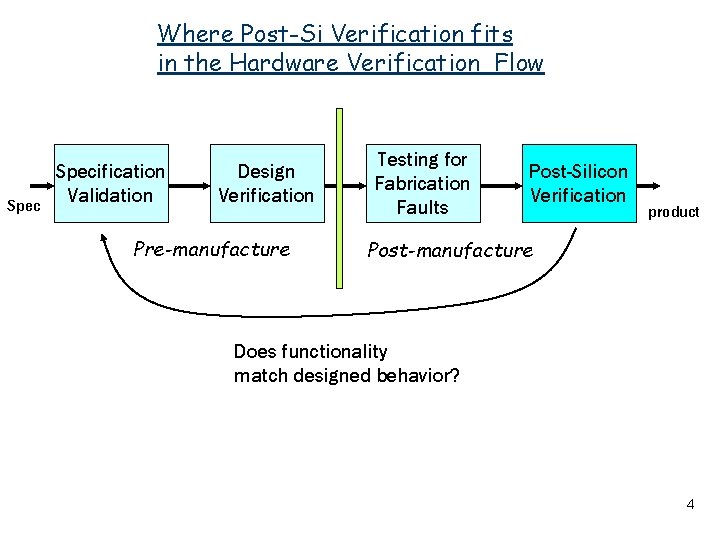
Where Post-Si Verification fits in the Hardware Verification Flow Specification Validation Design Verification Pre-manufacture Testing for Fabrication Faults Post-Silicon Verification product Post-manufacture Does functionality match designed behavior? 4
More Facts about Post-Silicon Verification • Post-Si Verification can be for uniprocessor functionality • . . or to determine if MP Orderings are being obeyed • . . . or to check if cache coherence protocols are behaving • Directly impacts the time to market • The industry spends huge amounts of effort in this area • Great opportunities to apply FV 5
How Formal Methods can enhance Post-Si Verification • Reduces manual effort • Helps in test-case selection • Helps analyze execution results comprehensively 6
Overview of the talk • How the paradigm for post-Si verification must change • How Limited Observability impacts post-Si verification • The use of Constraints • A paper design for a Post-Si verification system based on constraints - based on actual experience developing prototypes in an industrial context • Concluding Remarks 7
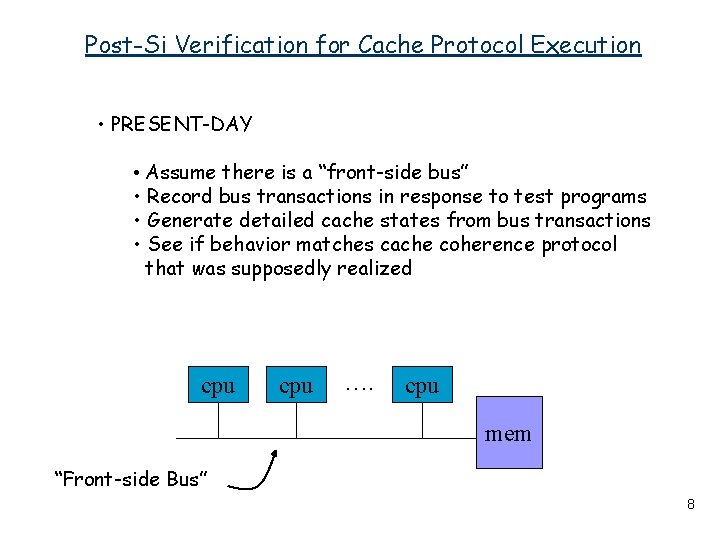
Post-Si Verification for Cache Protocol Execution • PRESENT-DAY • Assume there is a “front-side bus” • Record bus transactions in response to test programs • Generate detailed cache states from bus transactions • See if behavior matches cache coherence protocol that was supposedly realized cpu …. cpu mem “Front-side Bus” 8
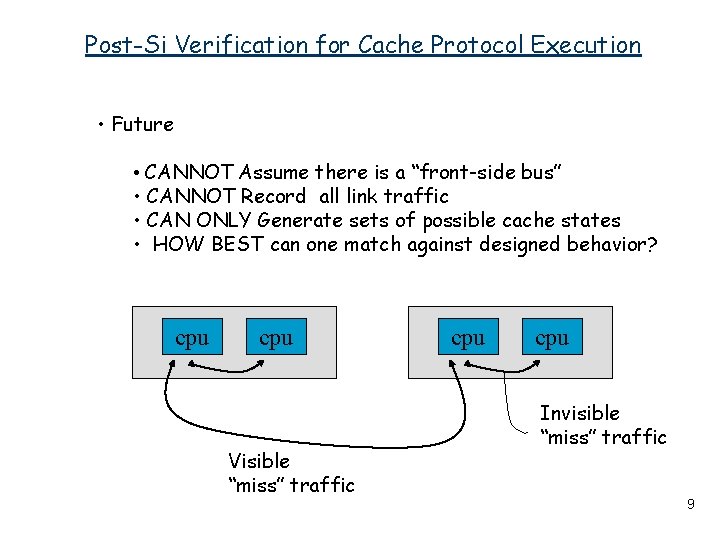
Post-Si Verification for Cache Protocol Execution • Future • CANNOT Assume there is a “front-side bus” • CANNOT Record all link traffic • CAN ONLY Generate sets of possible cache states • HOW BEST can one match against designed behavior? cpu Visible “miss” traffic cpu Invisible “miss” traffic 9
Potential Carry-over of Techniques Runtime verification of distributed embedded systems • Hundreds of processors, FPGAs, So. Cs, . . . interacting • Cannot assume system will work correctly on its own • Must detect onset of crashes, intrusions, . . . EARLY • Cannot easily observe all the nodes • Even if observable, information corrupts - bandwidth limitations (need to compress / discard) - time uncertainties 10
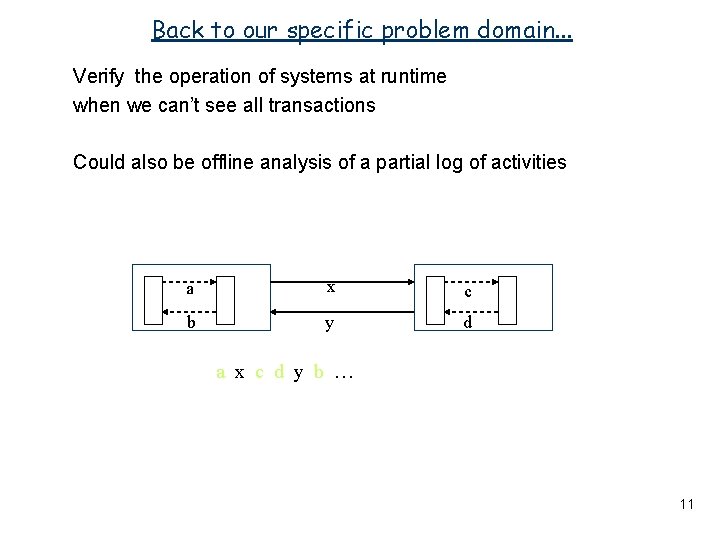
Back to our specific problem domain. . . Verify the operation of systems at runtime when we can’t see all transactions Could also be offline analysis of a partial log of activities a x c b y d a x c d y b … 11
Possible Outcomes of Post-Si Verification n Observed Behavior is “Definitely wrong” n “Potentially dangerous” (rely on statistics to give this verdict? ) n “Worth noting” (based on past experience and bug logs? ) n …. . n “Totally benign” (not even worth noting event) n Caveat: we are partially observing a potentially incorrect system 12
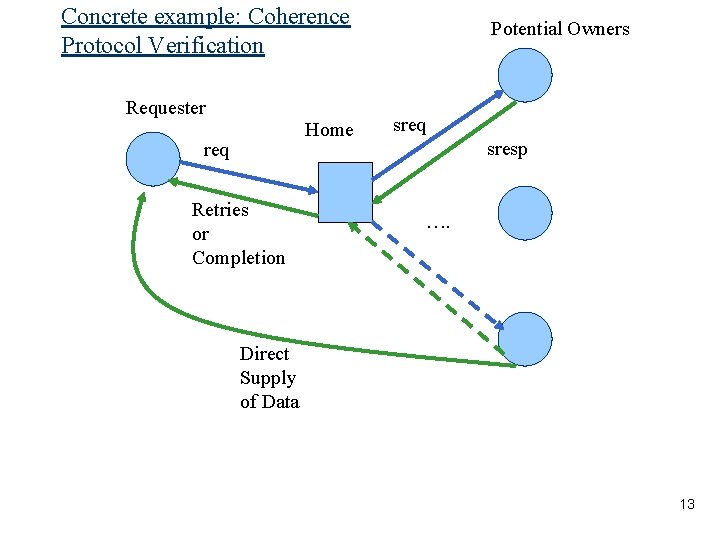
Concrete example: Coherence Protocol Verification Requester Home req Retries or Completion Potential Owners sreq sresp …. Direct Supply of Data 13
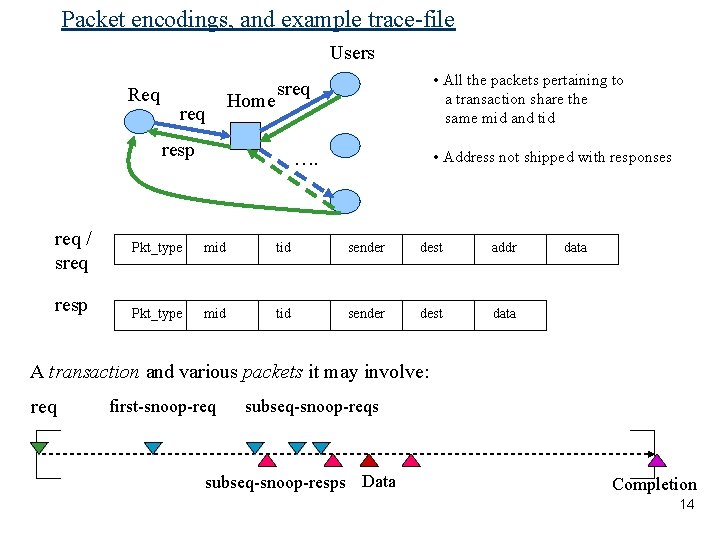
Packet encodings, and example trace-file Users Req req Home resp req / sreq resp • All the packets pertaining to a transaction share the same mid and tid sreq • Address not shipped with responses …. Pkt_type mid tid sender dest addr Pkt_type mid tid sender dest data A transaction and various packets it may involve: req first-snoop-req subseq-snoop-reqs subseq-snoop-resps Data Completion 14
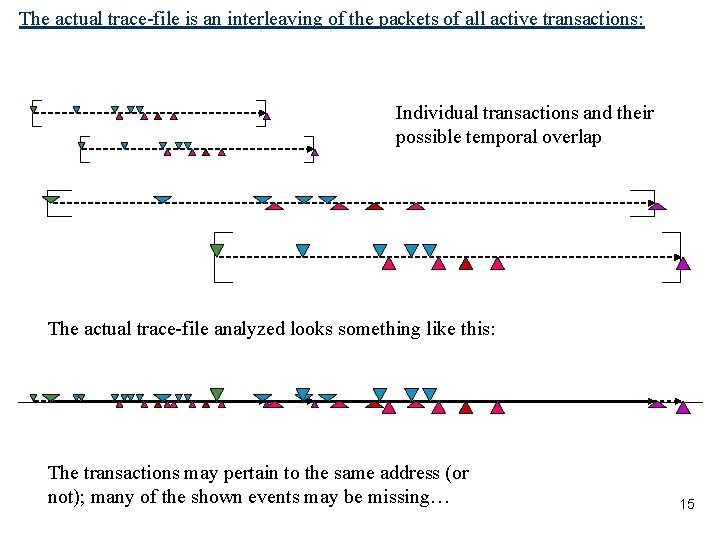
The actual trace-file is an interleaving of the packets of all active transactions: Individual transactions and their possible temporal overlap The actual trace-file analyzed looks something like this: The transactions may pertain to the same address (or not); many of the shown events may be missing… 15
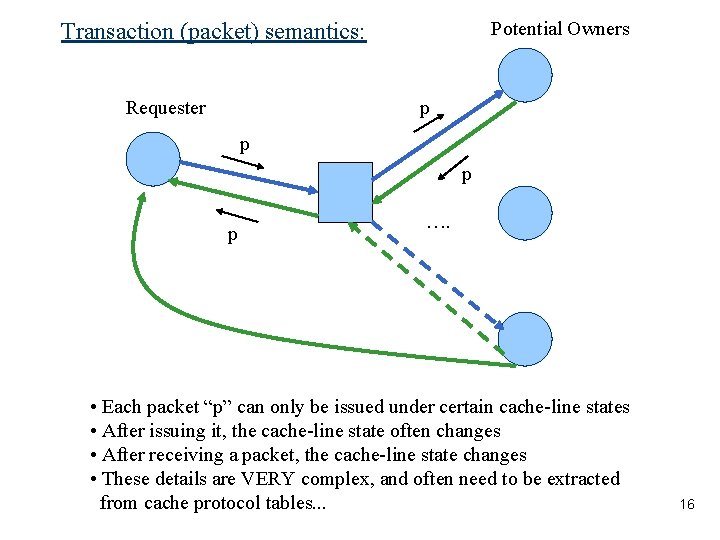
Potential Owners Transaction (packet) semantics: p Requester p p p …. • Each packet “p” can only be issued under certain cache-line states • After issuing it, the cache-line state often changes • After receiving a packet, the cache-line state changes • These details are VERY complex, and often need to be extracted from cache protocol tables. . . 16
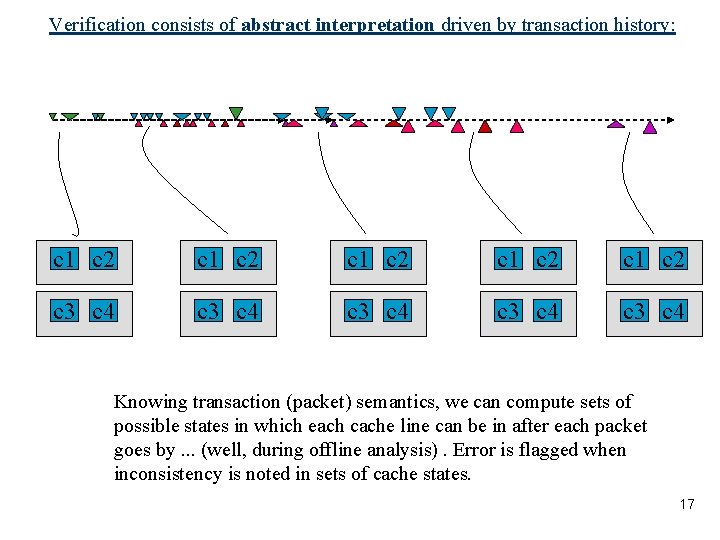
Verification consists of abstract interpretation driven by transaction history: c 1 c 2 c 1 c 2 c 3 c 4 c 3 c 4 Knowing transaction (packet) semantics, we can compute sets of possible states in which each cache line can be in after each packet goes by. . . (well, during offline analysis). Error is flagged when inconsistency is noted in sets of cache states. 17
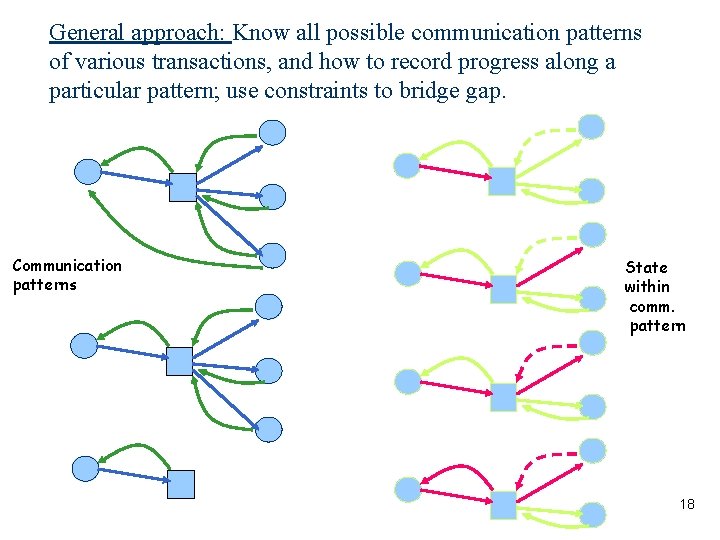
General approach: Know all possible communication patterns of various transactions, and how to record progress along a particular pattern; use constraints to bridge gap. Communication patterns State within comm. pattern 18
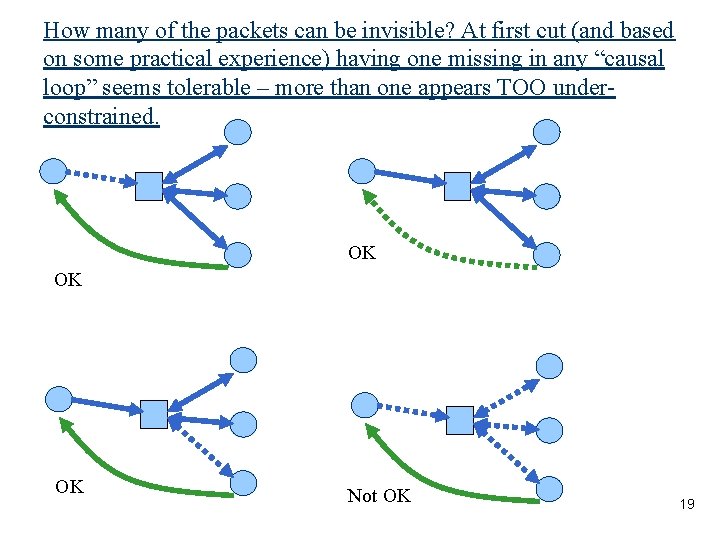
How many of the packets can be invisible? At first cut (and based on some practical experience) having one missing in any “causal loop” seems tolerable – more than one appears TOO underconstrained. OK OK OK Not OK 19
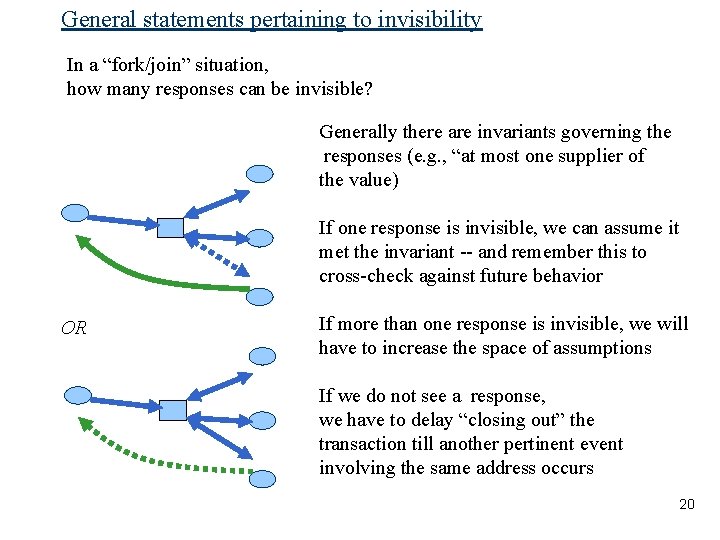
General statements pertaining to invisibility In a “fork/join” situation, how many responses can be invisible? Generally there are invariants governing the responses (e. g. , “at most one supplier of the value) If one response is invisible, we can assume it met the invariant -- and remember this to cross-check against future behavior OR If more than one response is invisible, we will have to increase the space of assumptions If we do not see a response, we have to delay “closing out” the transaction till another pertinent event involving the same address occurs 20
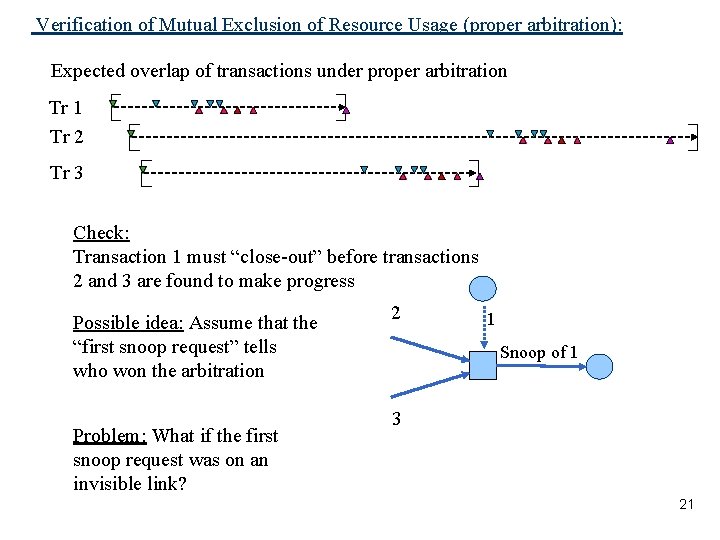
Verification of Mutual Exclusion of Resource Usage (proper arbitration): Expected overlap of transactions under proper arbitration Tr 1 Tr 2 Tr 3 Check: Transaction 1 must “close-out” before transactions 2 and 3 are found to make progress Possible idea: Assume that the “first snoop request” tells who won the arbitration Problem: What if the first snoop request was on an invisible link? 2 1 Snoop of 1 3 21
Approach initially tried n Wrote a prototype in Ocaml to analyze given cache protocol execution trace n For each new packet read, its corresponding communication pattern and state within communication pattern was determined n For each packet, we obtained WP and SP – – WP : Weakest Precondition (in a sense) The most general set of cache states under which packet could be generated – – SP ; Strongest Postcondition (in a sense) The tightest set of states the cache could be after the packet is sent – Many transaction-types and “conflict situations” made state maintenance and update highly unstructured (about 8 versions of the code were written, with each version becoming soon ugly) 22
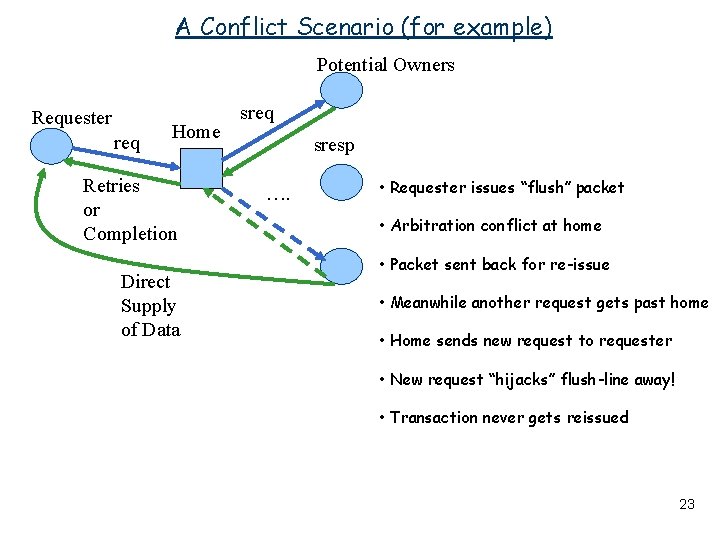
A Conflict Scenario (for example) Potential Owners Requester req Home Retries or Completion Direct Supply of Data sreq sresp …. • Requester issues “flush” packet • Arbitration conflict at home • Packet sent back for re-issue • Meanwhile another request gets past home • Home sends new request to requester • New request “hijacks” flush-line away! • Transaction never gets reissued 23
Constraints to the rescue. . but. . n n Constraint-programming was viewed as a possible solution – Would permit local behavior to be expressed in terms of constraints – Constraint formalisms can “solve” for missing information But, traditional constraint frameworks found inadequate – After extensive search, we could not find a constraint paradigm that can deal with interacting automata – What we need is a method for back-tracing precursors to observed actions – When multiple observations trace back to the same precursor, we can ‘vote the precursor up or down’ – Conditional probabilities of events are involved in guiding search 24
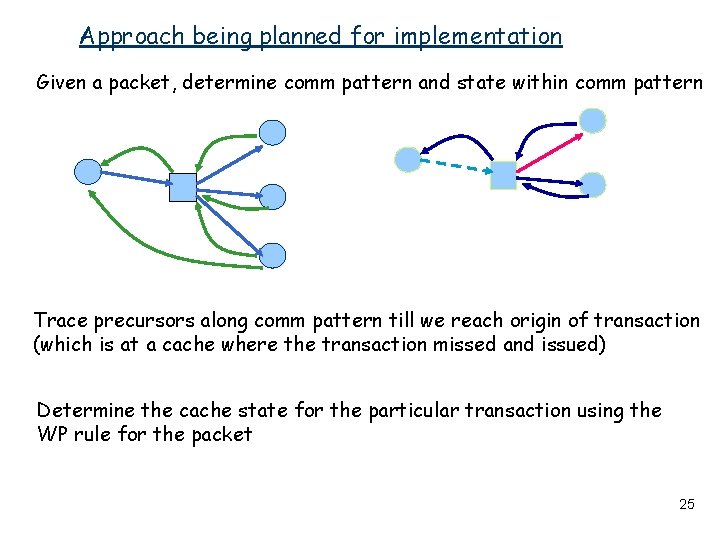
Approach being planned for implementation Given a packet, determine comm pattern and state within comm pattern Trace precursors along comm pattern till we reach origin of transaction (which is at a cache where the transaction missed and issued) Determine the cache state for the particular transaction using the WP rule for the packet 25
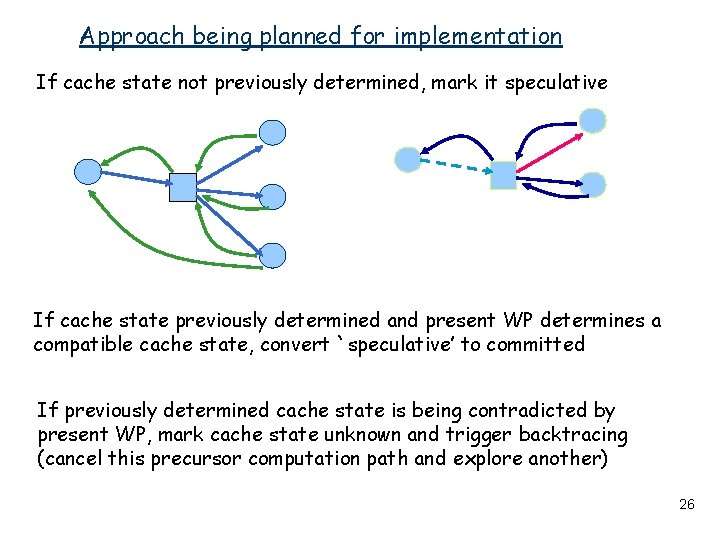
Approach being planned for implementation If cache state not previously determined, mark it speculative If cache state previously determined and present WP determines a compatible cache state, convert `speculative’ to committed If previously determined cache state is being contradicted by present WP, mark cache state unknown and trigger backtracing (cancel this precursor computation path and explore another) 26
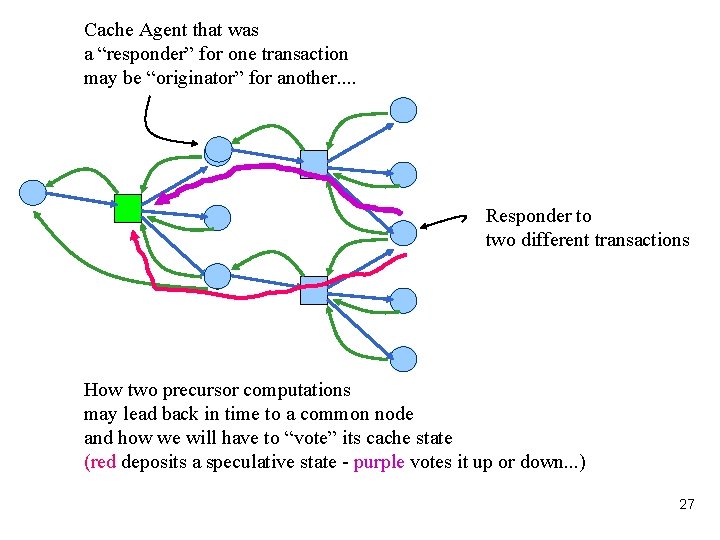
Cache Agent that was a “responder” for one transaction may be “originator” for another. . Responder to two different transactions How two precursor computations may lead back in time to a common node and how we will have to “vote” its cache state (red deposits a speculative state - purple votes it up or down. . . ) 27
Why today’s constraint approaches don’t give these capabilities readily. . n Today’s constraint solving approaches (“CSP”) appear to be about “static” situations n Various algorithms based on arc consistency and propagators can be found in the literature n Temporal Concurrent Constraint Programming is in its infancy n (I also don’t know much about these areas. . . tell me if I’m wrong! But I’ve not seen very much despite intense literature searches. . . ) n Constraint Solving in the context of Coupled Reactive Processes can be have multiple uses n Environments such as Comet (van Hentenryck) may offer a powerful way to organize such a constraint-based system 28
Constraint Languages Surveyed (and some evaluated. . . ) n n n Gnu. Prolog Sicstus Prolog Mozart / Oz Erlang Fa. Cile. . or even Murphi perhaps? Reading List (Books / Papers. . . ) n Stuckey’s book on Constraint Logic Programming Dechter’s book on Constraints Modeler++ / Localizer++ / Comet n Ultimately will roll our own constraint system n n 29
Concluding Remarks n Limited Observability is going to be a central concern in future system verification n Plenty of opportunities formal methods, constraint-solving methods, and abstract interpretation methods to work in concert n Formal Methods communities must talk to other communities to significantly enhance the scope and relevance of what they are doing – testing communities – diagnosis communities 30
- Slides: 30