Portcullis Protecting Connection Setup from DenialofCapability Attacks Paper
Portcullis: Protecting Connection Setup from Denial-of-Capability Attacks Paper by: Bryan Parno et al. (CMU) Presented by: Ionut Trestian Gergely Biczók (Slides in courtesy of: Bryan Parno)
Network-Level Distributed Denial of Service Attacks l l Distributed Do. S attack exhausts bandwidth of links leading to victim Recent example: Estonian government and bank sites attacked by Russian hackers (dispute over Soviet statue) Key issue: receiver has no control over incoming traffic! Several capability systems are proposed to alleviate this problem [e. g. SIFF, TVA, …]
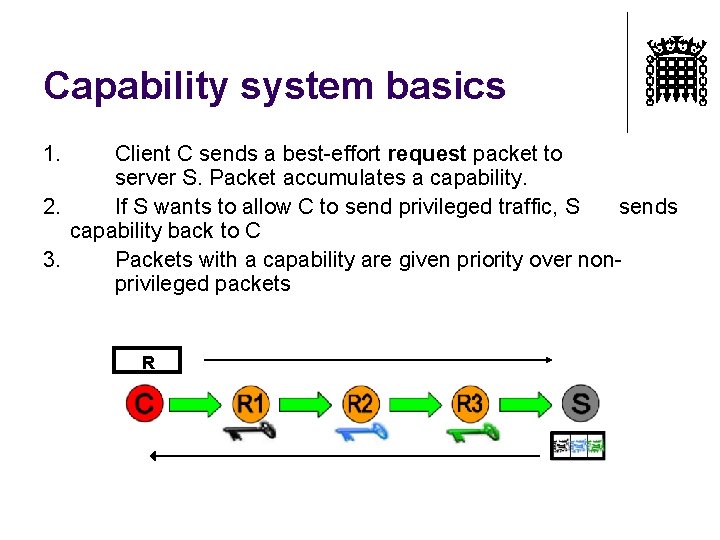
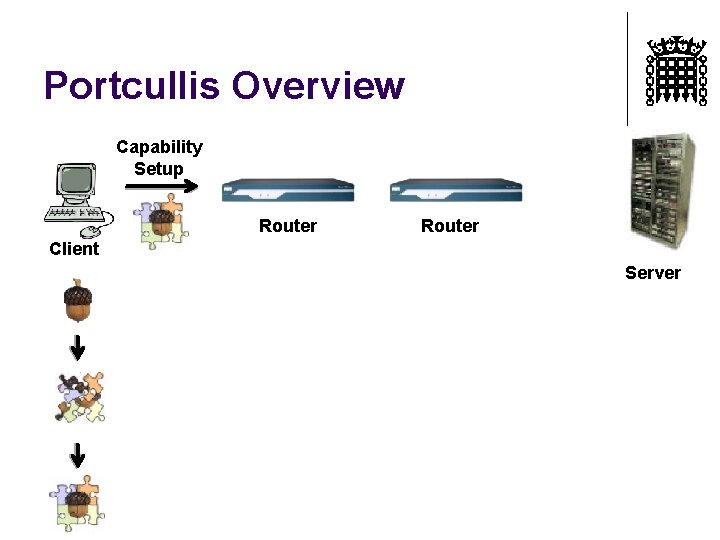
Capability system basics 1. Client C sends a best-effort request packet to server S. Packet accumulates a capability. 2. If S wants to allow C to send privileged traffic, S sends capability back to C 3. Packets with a capability are given priority over nonprivileged packets R
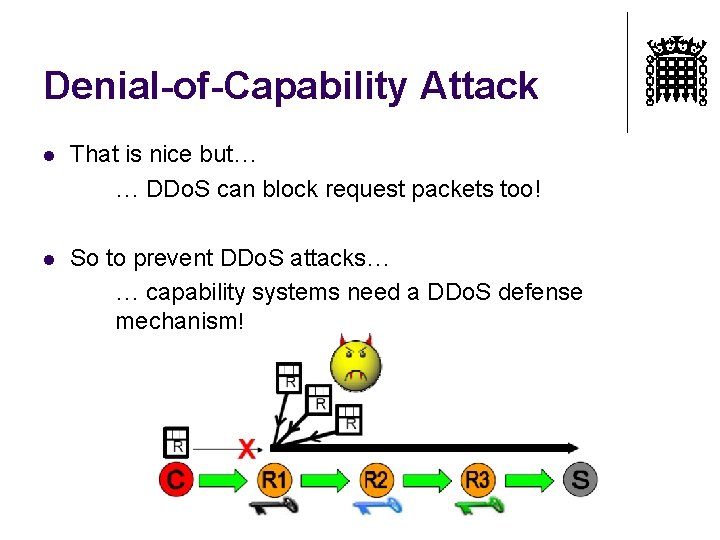
Denial-of-Capability Attack l That is nice but… … DDo. S can block request packets too! l So to prevent DDo. S attacks… … capability systems need a DDo. S defense mechanism!
Our starting claim l Capability setup is fundamentally different from normal data traffic l l l If one request goes through we succeed It can sustain more losses and higher cost (of any kind) Portcullis exploits this difference l l Setup is worth a reasonable cost to be safe from DDo. S Cost is spread over all packets between source and destination l Recall the definition of capability from [TVA]
Design Goals l Network cannot distinguish attackers from defenders Best feasible solution: allocate bandwidth fairly l Also, we need to bound the capability setup delay l l Setup time still depends on number of users/attackers and network capacity
How to Allocate Bandwidth Fairly? l Identity-based fairness l Per-source (e. g. , IP address) l l Per-path l l l SIFF: hurting legitimate senders TVA: coarse-grained (per-interface) Per-destination l l NATs, spoofed addresses Attacker can flood all destinations sharing the victm’s bottleneck link Legitimate user send packets only to single host Actually amplifies the power of attacker! We need something better!
Proof-of-Work Schemes l Demonstrate the use of a limited resource Access to network resources proportonal to work done l Per-bandwidth fairness l l Only demonstrated on end-host resources, and on an uncongested network Large disparities bw legitimate users (modem vs. fibre) Per-computation fairness l Probability of request packet delivery ~ computational effort of sender
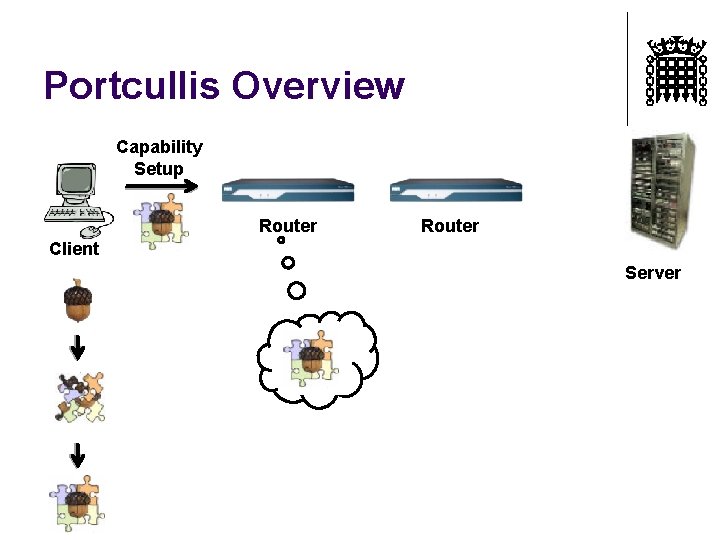
Per-computation fairness – puzzles l l Measure work with solving puzzles Work is performed at the end-host, not in the network l l l Smaller disparities in computational power (PC vs. cellphone) Work is verifiable, unlike identifiers Our work addresses limitations of previous puzzle systems l l Clients can create and solve variable-difficulty puzzles without contacting the victim Each router on the path can independently verify the work performed
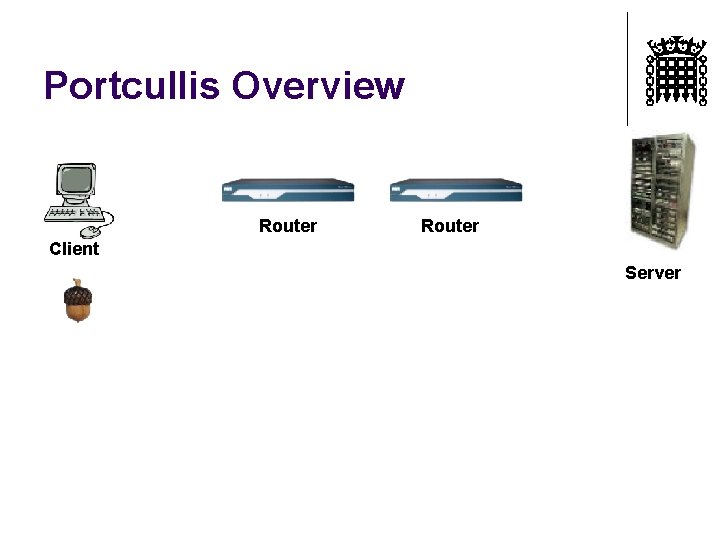
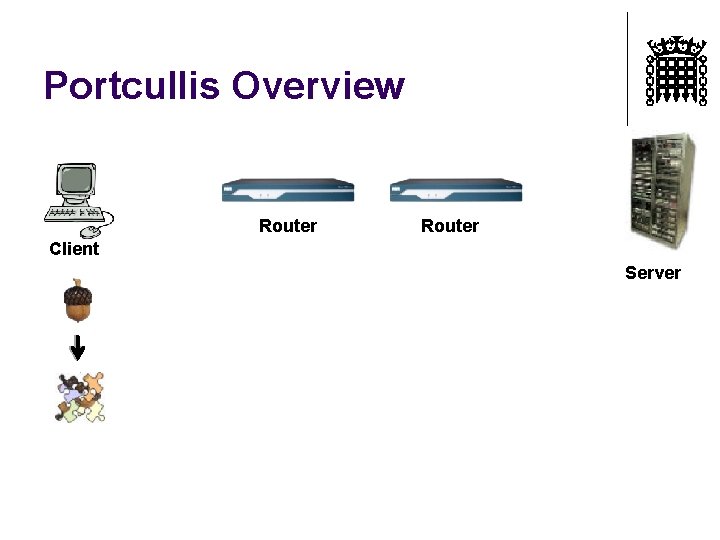
Portcullis Overview Router Client Server
Portcullis Overview Router Client Server
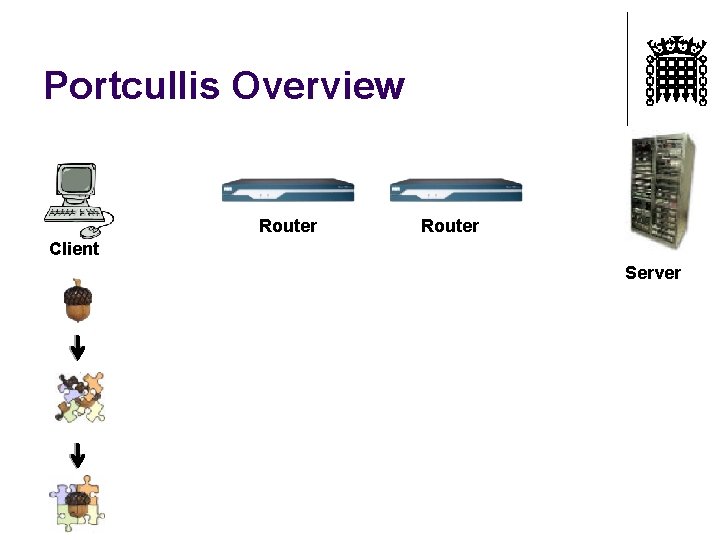
Portcullis Overview Router Client Server
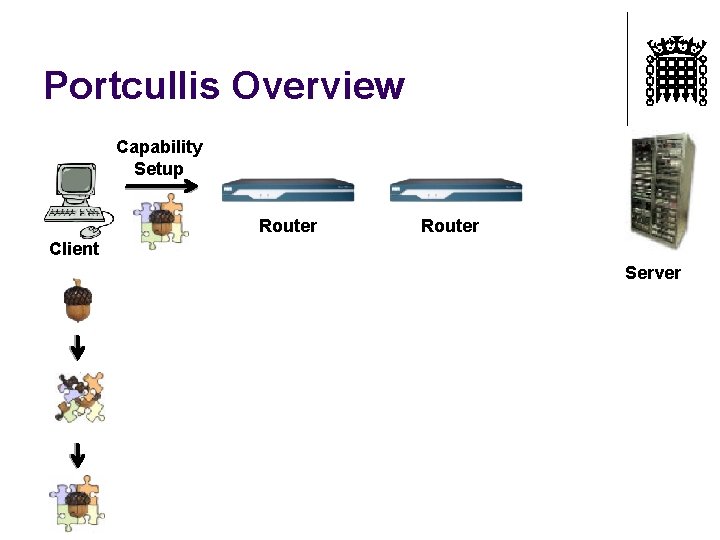
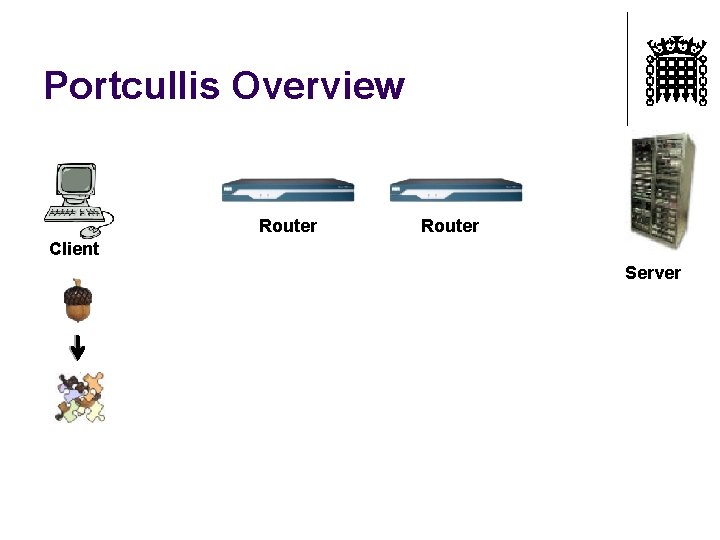
Portcullis Overview Capability Setup Router Client Server
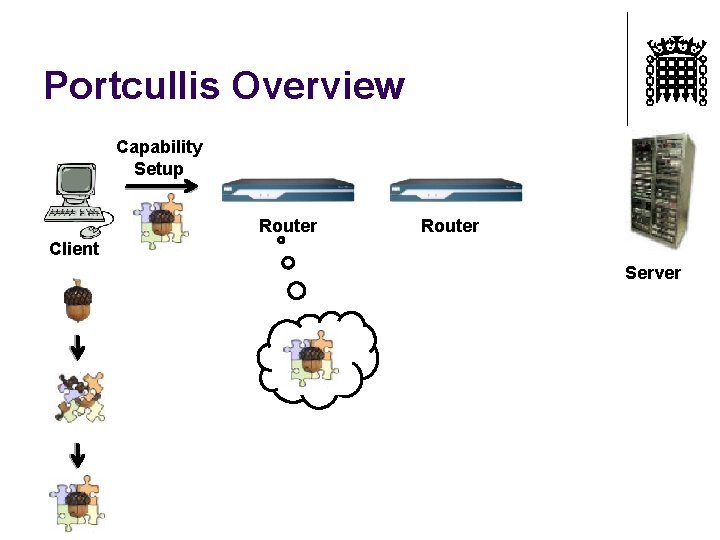
Portcullis Overview Capability Setup Router Client Server
Portcullis Overview Capability Setup Router Client Server
Portcullis Overview Capability Setup Router Client Server
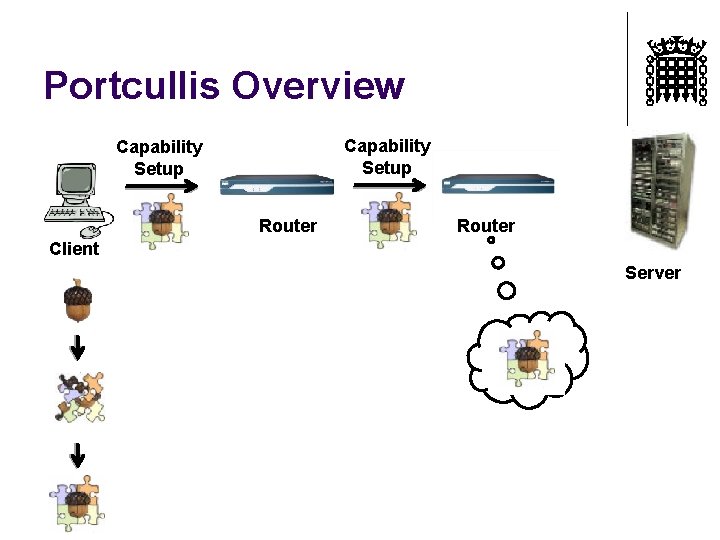
Portcullis Overview Capability Setup Router Client Server
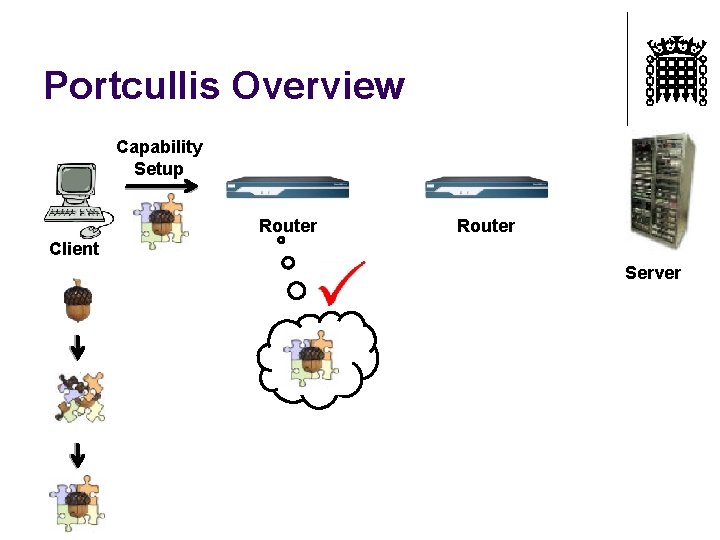
Portcullis Overview Capability Setup Router Client Server
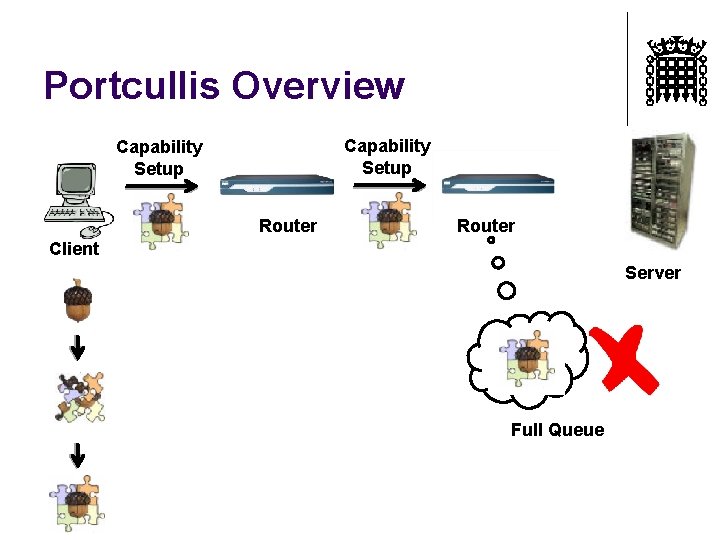
Portcullis Overview Capability Setup Router Client Server Full Queue
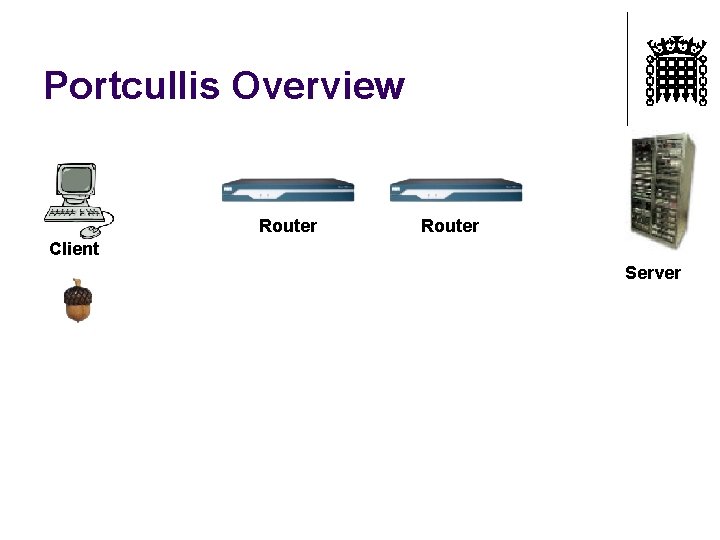
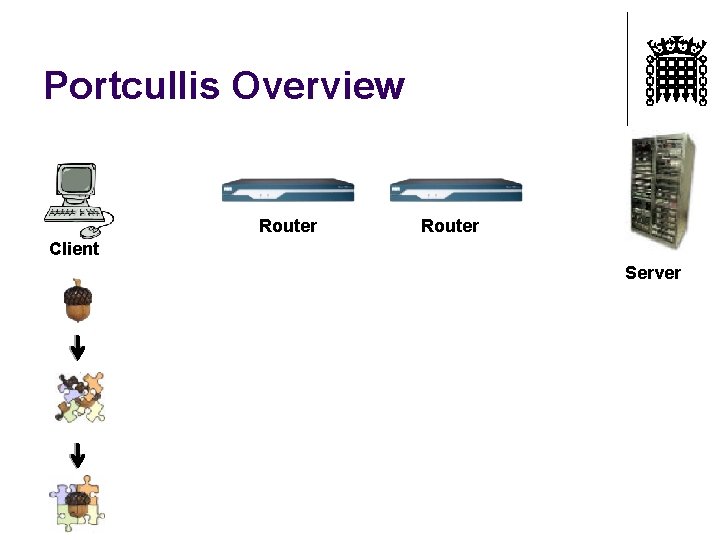
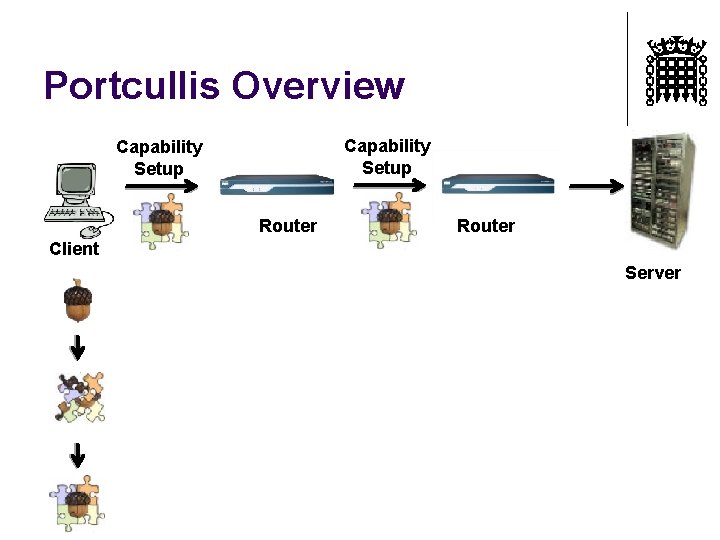
Portcullis Overview Router Client Server
Portcullis Overview Router Client Server
Portcullis Overview Router Client Server
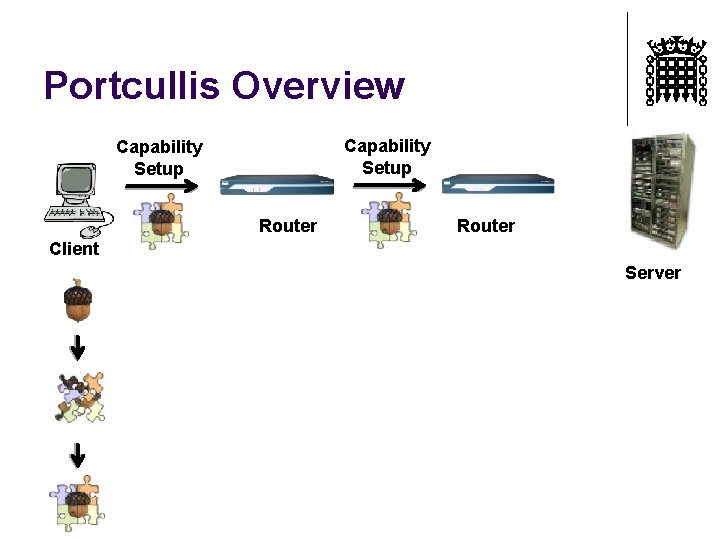
Portcullis Overview Capability Setup Router Client Server
Portcullis Overview Capability Setup Router Client Server
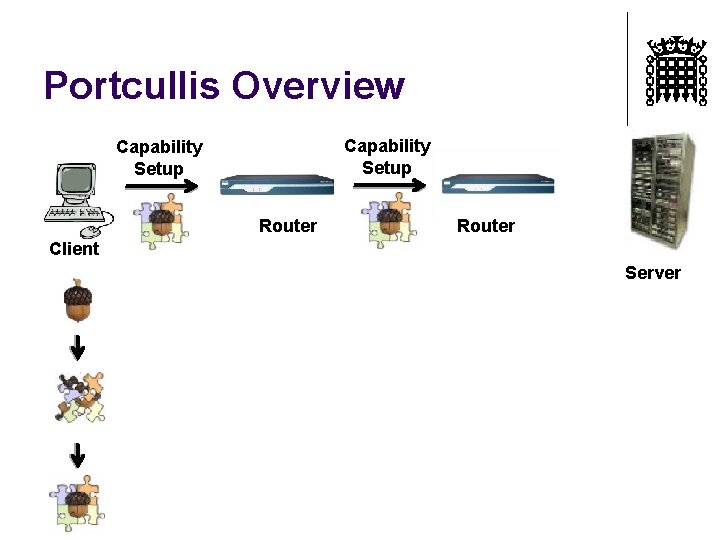
Portcullis Overview Capability Setup Router Client Server
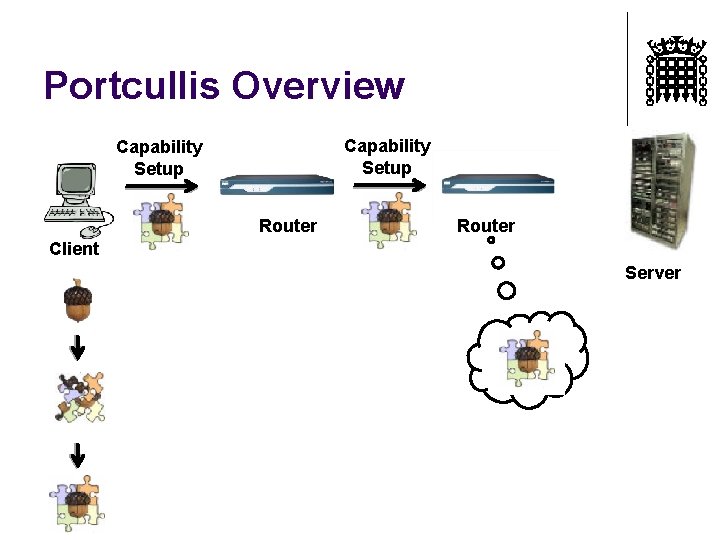
Portcullis Overview Capability Setup Router Client Server
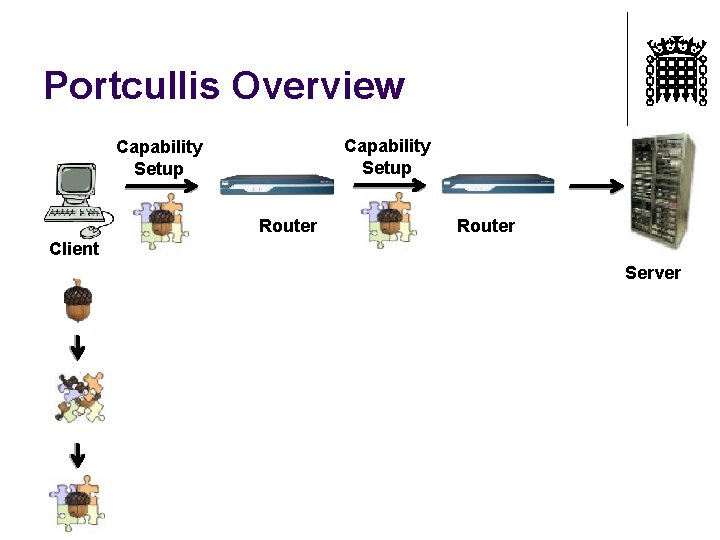
Portcullis Overview Capability Setup Router Client Server
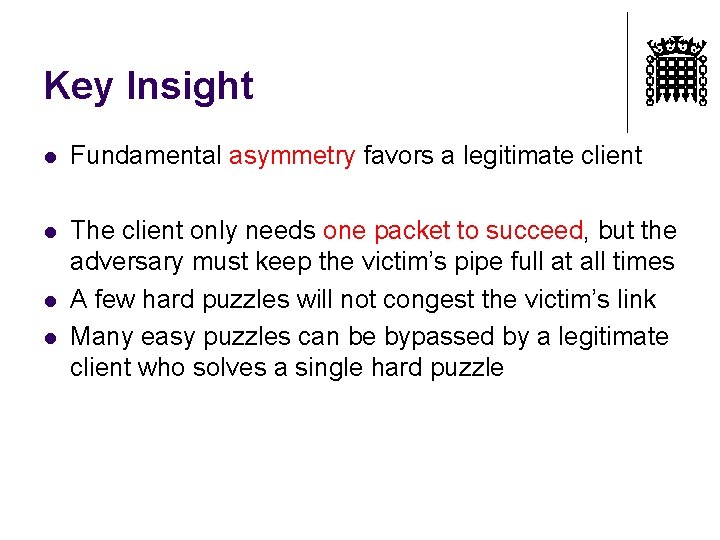
Key Insight l Fundamental asymmetry favors a legitimate client l The client only needs one packet to succeed, but the adversary must keep the victim’s pipe full at all times A few hard puzzles will not congest the victim’s link Many easy puzzles can be bypassed by a legitimate client who solves a single hard puzzle l l
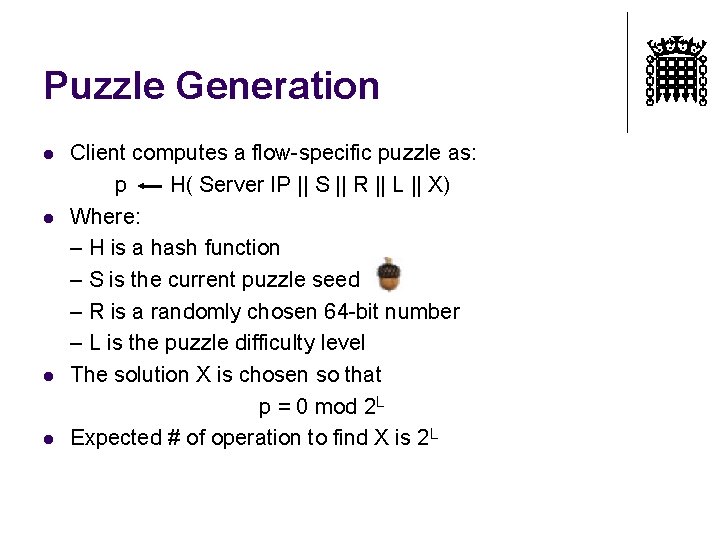
Puzzle Generation l l Client computes a flow-specific puzzle as: p H( Server IP || S || R || L || X) Where: – H is a hash function – S is the current puzzle seed – R is a randomly chosen 64 -bit number – L is the puzzle difficulty level The solution X is chosen so that p = 0 mod 2 L Expected # of operation to find X is 2 L
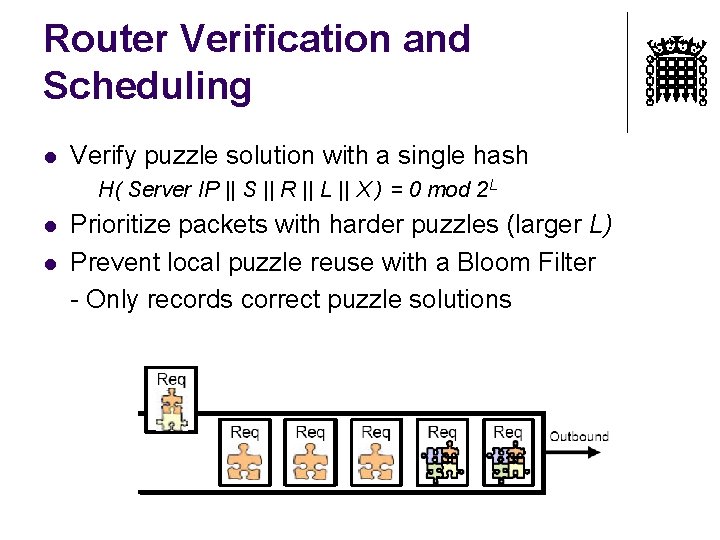
Router Verification and Scheduling l Verify puzzle solution with a single hash H( Server IP || S || R || L || X ) = 0 mod 2 L l l Prioritize packets with harder puzzles (larger L) Prevent local puzzle reuse with a Bloom Filter - Only records correct puzzle solutions
Legitimate Client Strategy l l Double the computational work included in each subsequent request Continue doubling until a request succeeds Our results show that this strategy succeeds regardless of attacker’s resources Knowledge of network congestion levels or attacker’s resources allows optimization
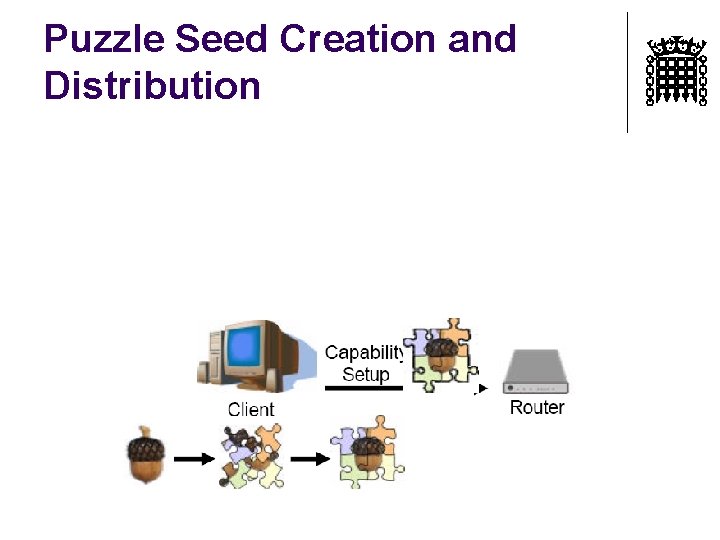
Puzzle Seed Creation and Distribution
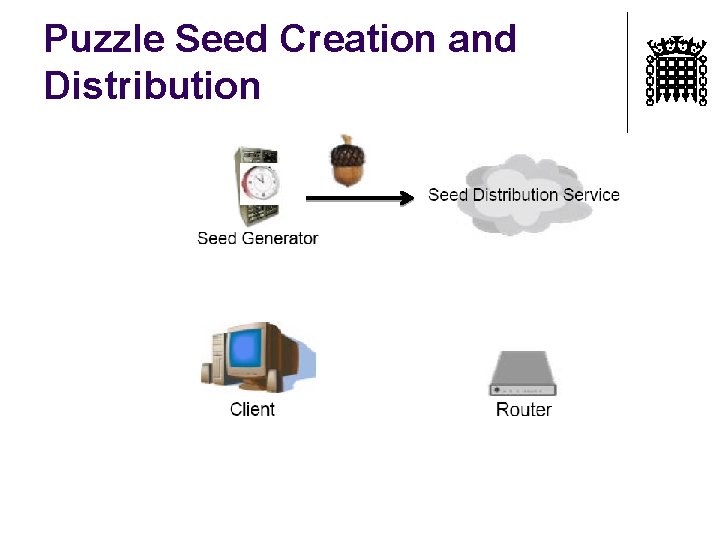
Puzzle Seed Creation and Distribution
Puzzle Seed Creation and Distribution
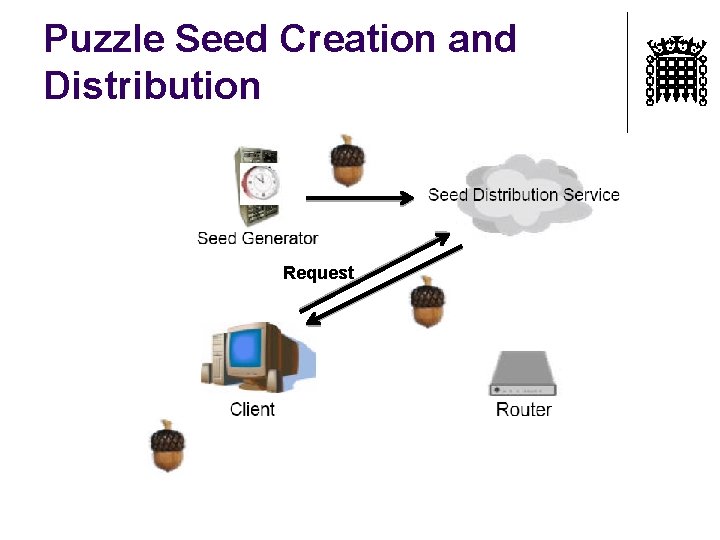
Puzzle Seed Creation and Distribution Request
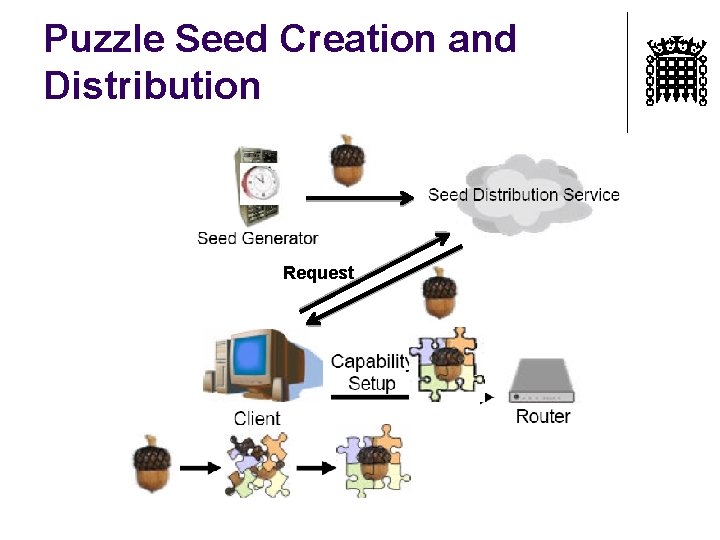
Puzzle Seed Creation and Distribution Request
Seed Generation and Verification l l l Trusted seed generator releases a new puzzle seed every 5 minutes Puzzle seeds must be: – Unpredictable – Easily verified by hosts and routers Naïve implementation: – Seed generator: • Picks a random number for the puzzle seed • Uses a public key to sign the seed – Hosts and routers verify each signature
Seed Distribution Service l l Takes puzzle seeds and makes them available to clients Requires distributed, well-provisioned Servers l E. g. , CDN or DNS
Evaluation Theoretical Result #1 l l l Proof that legitimate clients succeed in time O(M) M = Number of malicious machines Intuition l l Attacker can either fill the victim’s pipe or solve hard puzzles A legitimate client quickly sends a request at a level higher than the attacker can "afford"
Evaluation Theoretical Result #2 l l Proof that for any routing policy, the time needed for capability setup is O(M) Intuition l Subverted machines can behave just like legitimate machines
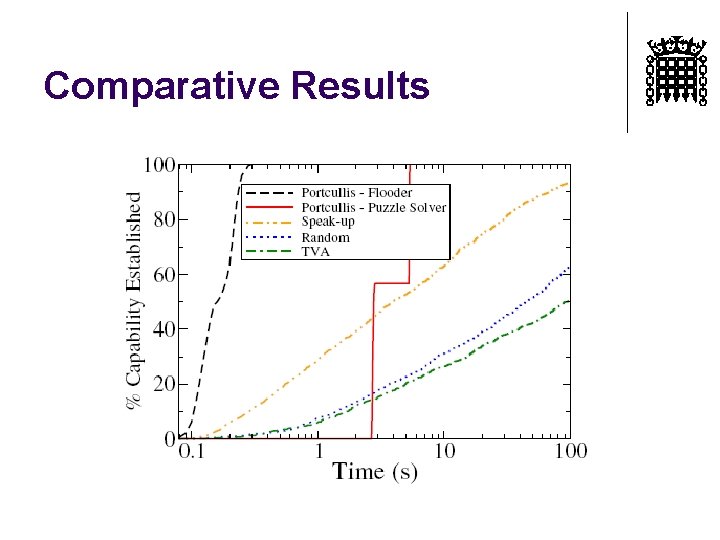
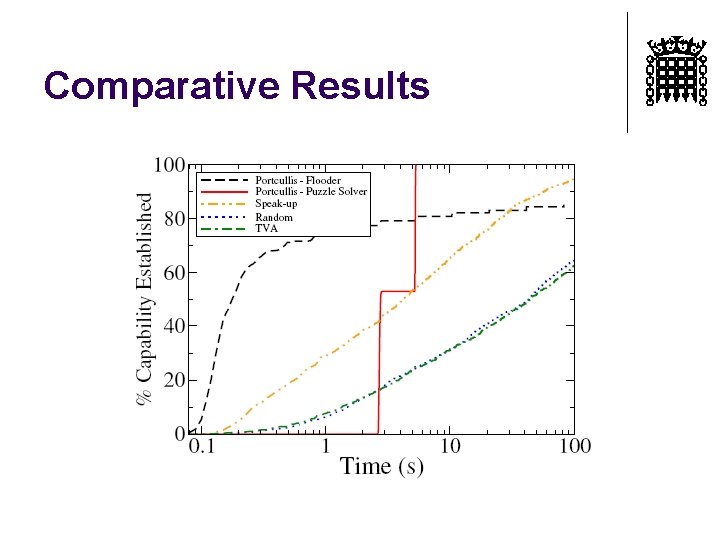
Evaluation l Simulation based on real Internet topology l l l CAIDA Skitter map of over 174, 000 networks Randomly placed legitimate clients and attackers at the edges Victim placed at the root Attackers establish DDo. S by flooding at max uplink capacity We measure the time needed for 1000 legitimate clients to establish a capability
Portcullis Attacker Strategies l l l Evaluate various adversarial strategies Naïve attacker simply floods without solving puzzles Puzzle solver: l l Chooses a flooding rate Pools all computational resources to solve the hardest puzzles possible while maintaining the chosen sending rate
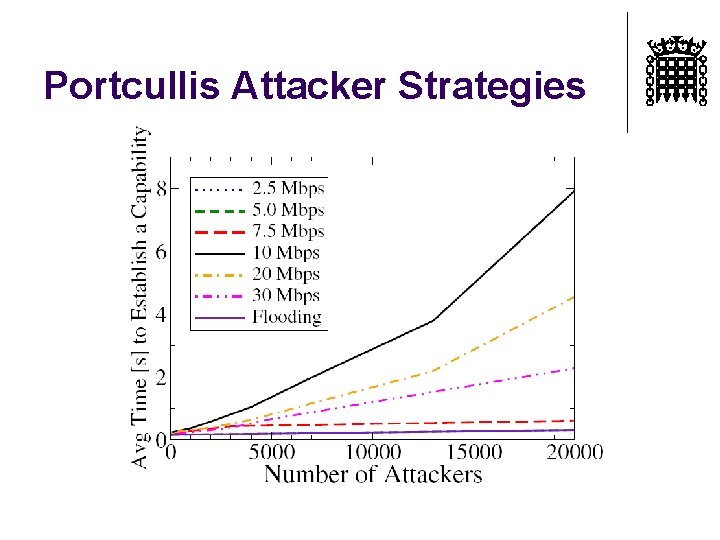
Portcullis Attacker Strategies
![Comparative Simulations Points of comparison: l Per-bandwidth fairness (Speak up) [Walfish et al. 2006] Comparative Simulations Points of comparison: l Per-bandwidth fairness (Speak up) [Walfish et al. 2006]](http://slidetodoc.com/presentation_image_h/2e5116d962bb27cde750d874832485dd/image-44.jpg)
Comparative Simulations Points of comparison: l Per-bandwidth fairness (Speak up) [Walfish et al. 2006] l l Per-path fairness (TVA) [Yang et al. 2005] l l Legitimate clients send requests at maximum uplink capacity Packets queued based on previous Autonomous System (AS) Legacy (Random) l Routers randomly select packets to forward and drop excess packets
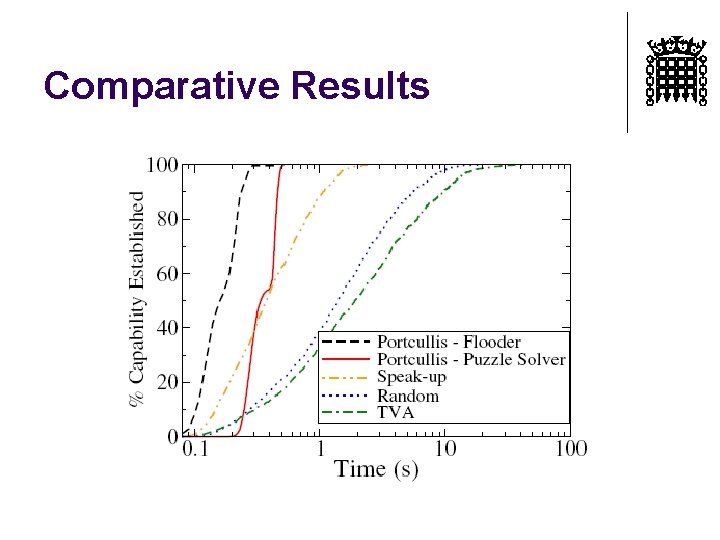
Comparative Results
Comparative Results
Comparative Results
Conclusions l Portcullis mitigates Do. C attacks by allocating bandwidth based on per-computation fairness l Novel puzzle mechanism strictly bounds the setup delay imposed by a given number of attackers l l Supported by proofs and simulations Makes capability systems a robust defense against DDo. S attacks
- Slides: 48