Port Scanning based on nmap tool Lecture 5
Port Scanning (based on nmap tool) Lecture – 5 NETW 4006 -Lecture 05 Part 2 1
Content o o o Definition Port Numbers TCP 3 Way-handshake Different Port Scanning Types Detecting Scan NETW 4006 -Lecture 05 Part 2 2
Port Scanning o Attackers: reconnaissance technique to discover available services/open ports n n send a packet to different ports response indicates state of ports o n open, closed, filtered type of response: different info about the system (OS) (fingerprinting) NETW 4006 -Lecture 05 Part 2 3
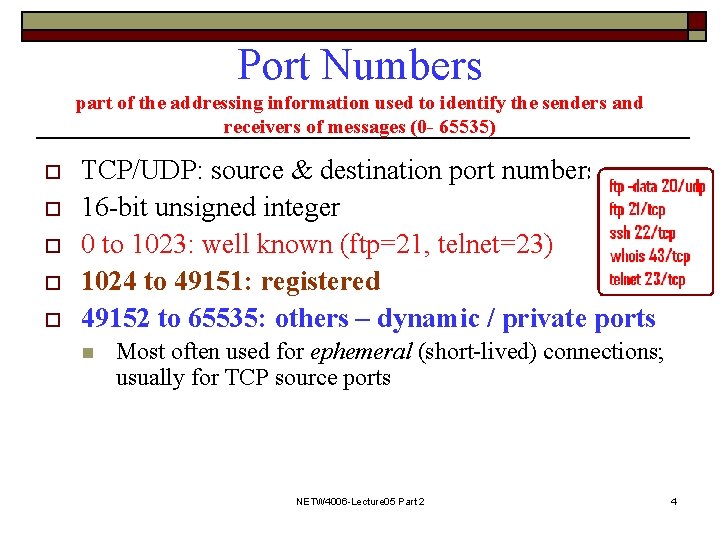
Port Numbers part of the addressing information used to identify the senders and receivers of messages (0 - 65535) o o o TCP/UDP: source & destination port numbers 16 -bit unsigned integer 0 to 1023: well known (ftp=21, telnet=23) 1024 to 49151: registered 49152 to 65535: others – dynamic / private ports n Most often used for ephemeral (short-lived) connections; usually for TCP source ports NETW 4006 -Lecture 05 Part 2 4
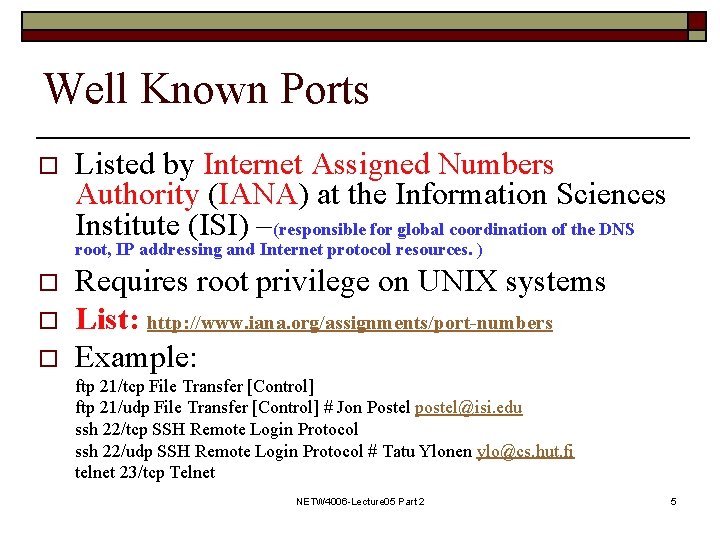
Well Known Ports o Listed by Internet Assigned Numbers Authority (IANA) at the Information Sciences Institute (ISI) –(responsible for global coordination of the DNS root, IP addressing and Internet protocol resources. ) o o o Requires root privilege on UNIX systems List: http: //www. iana. org/assignments/port-numbers Example: ftp 21/tcp File Transfer [Control] ftp 21/udp File Transfer [Control] # Jon Postel postel@isi. edu ssh 22/tcp SSH Remote Login Protocol ssh 22/udp SSH Remote Login Protocol # Tatu Ylonen ylo@cs. hut. fi telnet 23/tcp Telnet NETW 4006 -Lecture 05 Part 2 5
Registered Ports 1024 - 49151 o o o Listed by IANA, as a convenience to reduce any port number conflicts Used by ordinary user processes or programs executed by ordinary users Example: shockwave 2 1257/tcp Shockwave 2 NETW 4006 -Lecture 05 Part 2 6
Other Ports (Dynamic/Private 49152 - 65535) o o o Private and/or dynamic ports. Used by ordinary programs. Commonly used for ephemeral (short-lived) ports. n Most commonly for source ports on outgoing connections. NETW 4006 -Lecture 05 Part 2 7
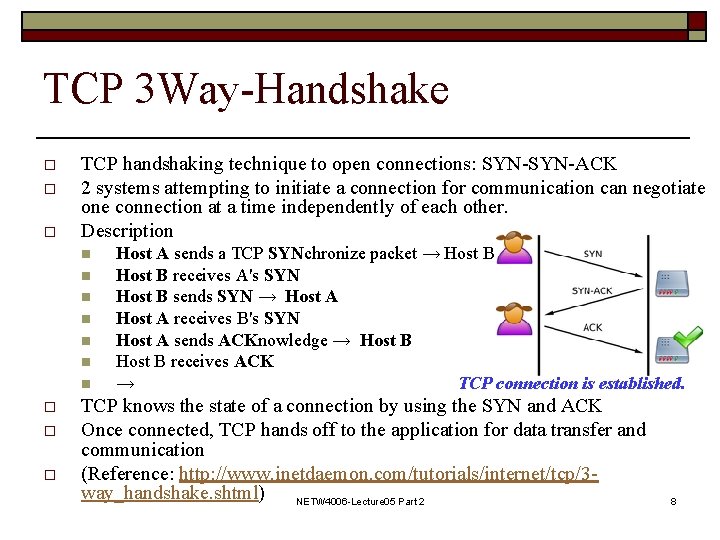
TCP 3 Way-Handshake o o o TCP handshaking technique to open connections: SYN-ACK 2 systems attempting to initiate a connection for communication can negotiate one connection at a time independently of each other. Description n n n o o o Host A sends a TCP SYNchronize packet → Host B receives A's SYN Host B sends SYN → Host A receives B's SYN Host A sends ACKnowledge → Host B receives ACK → TCP connection is established. TCP knows the state of a connection by using the SYN and ACK Once connected, TCP hands off to the application for data transfer and communication (Reference: http: //www. inetdaemon. com/tutorials/internet/tcp/3 way_handshake. shtml) NETW 4006 -Lecture 05 Part 2 8
TCP connect() Scan o o o With connect() call used by the operating system to initiate a normal TCP connection to a remote device (3 -way handshake) No need of any special privileged access: Any user can use it. TCP connect scan is often logged by target host service. NETW 4006 -Lecture 05 Part 2 9
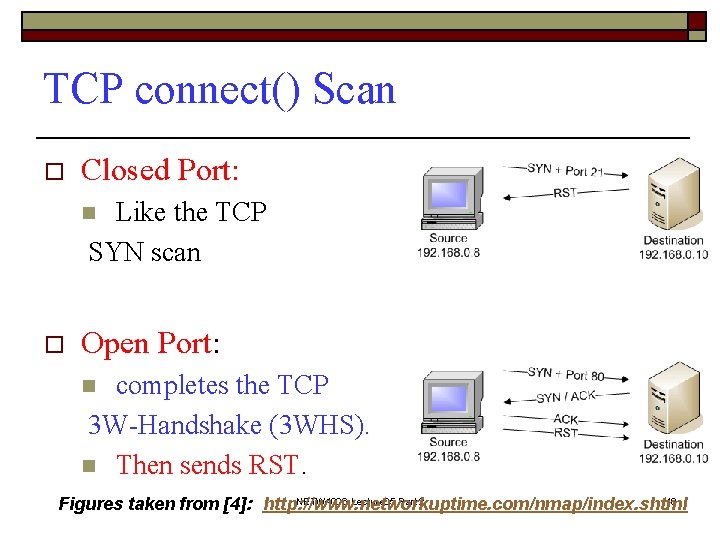
TCP connect() Scan o Closed Port: Like the TCP SYN scan n o Open Port: completes the TCP 3 W-Handshake (3 WHS). n Then sends RST. n NETW 4006 -Lecture 05 Part 2 10 Figures taken from [4]: http: //www. networkuptime. com/nmap/index. shtml
TCP SYN Scan/Half-Open Scan o o o Send a SYN packet , wait for a response & A SYN/ACK indicates the port is listening if a SYN. ACK is received, send an RST to tear down the connection immediately Requires Root privileges to create raw SYN Often not logged: 3 WHAS not completed NETW 4006 -Lecture 05 Part 2 11
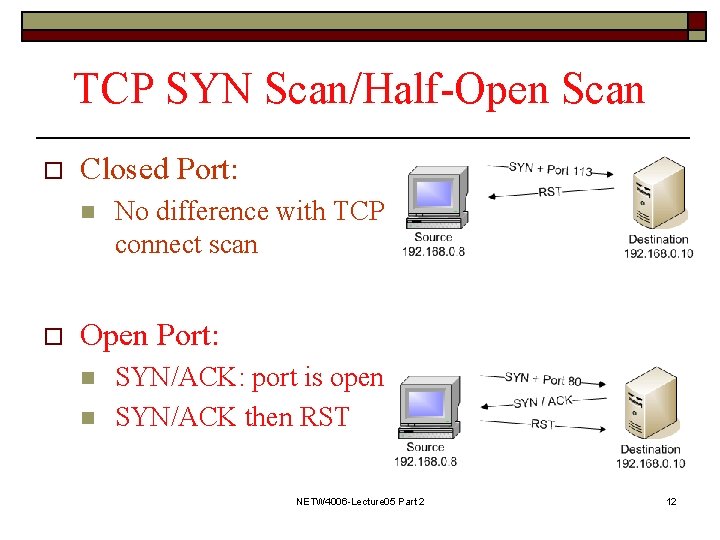
TCP SYN Scan/Half-Open Scan o Closed Port: n o No difference with TCP connect scan Open Port: n n SYN/ACK: port is open SYN/ACK then RST NETW 4006 -Lecture 05 Part 2 12
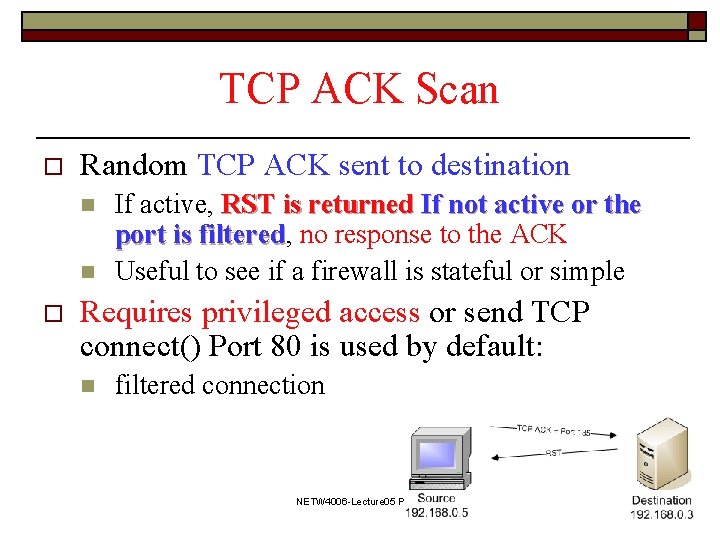
TCP ACK Scan o Random TCP ACK sent to destination n n o If active, RST is returned If not active or the port is filtered, filtered no response to the ACK Useful to see if a firewall is stateful or simple Requires privileged access or send TCP connect() Port 80 is used by default: n filtered connection NETW 4006 -Lecture 05 Part 2 13
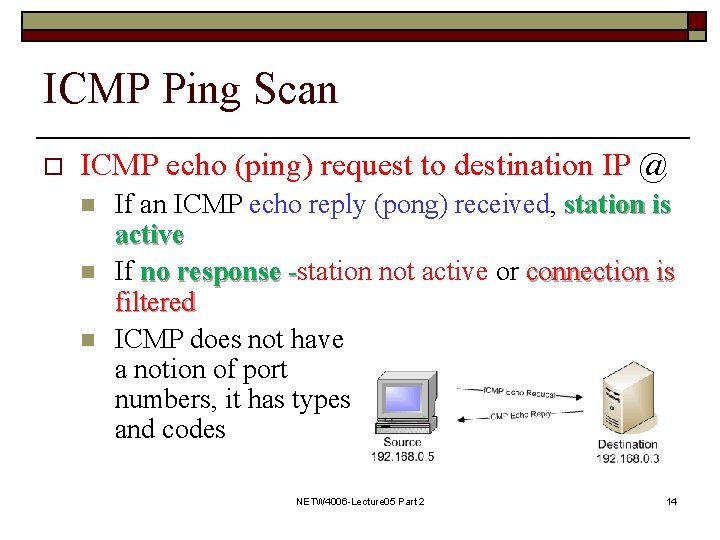
ICMP Ping Scan o ICMP echo (ping) request to destination IP @ n n n If an ICMP echo reply (pong) received, station is active If no response -station not active or connection is filtered ICMP does not have a notion of port numbers, it has types and codes NETW 4006 -Lecture 05 Part 2 14
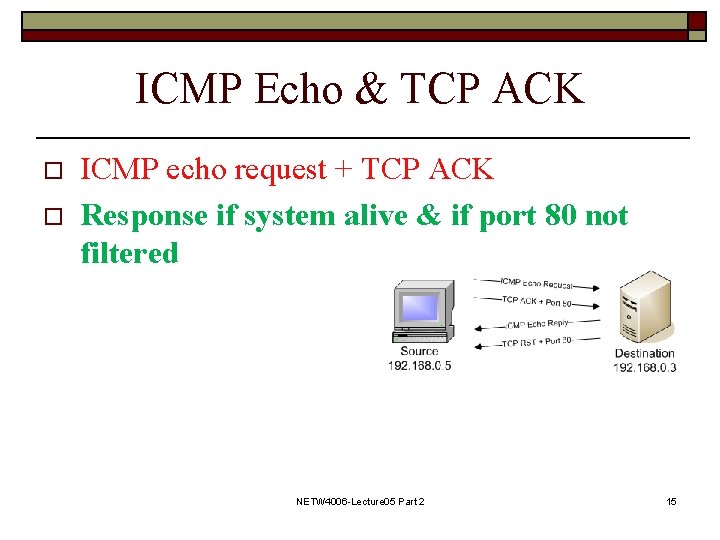
ICMP Echo & TCP ACK o o ICMP echo request + TCP ACK Response if system alive & if port 80 not filtered NETW 4006 -Lecture 05 Part 2 15
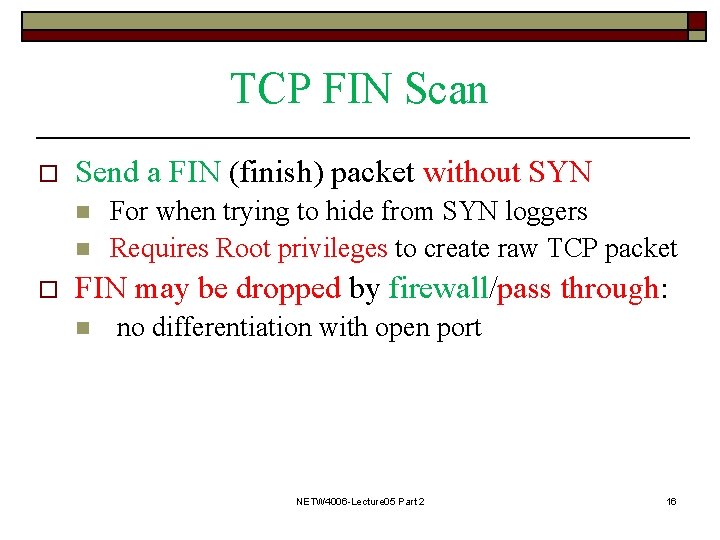
TCP FIN Scan o Send a FIN (finish) packet without SYN n n o For when trying to hide from SYN loggers Requires Root privileges to create raw TCP packet FIN may be dropped by firewall/pass through: n no differentiation with open port NETW 4006 -Lecture 05 Part 2 16
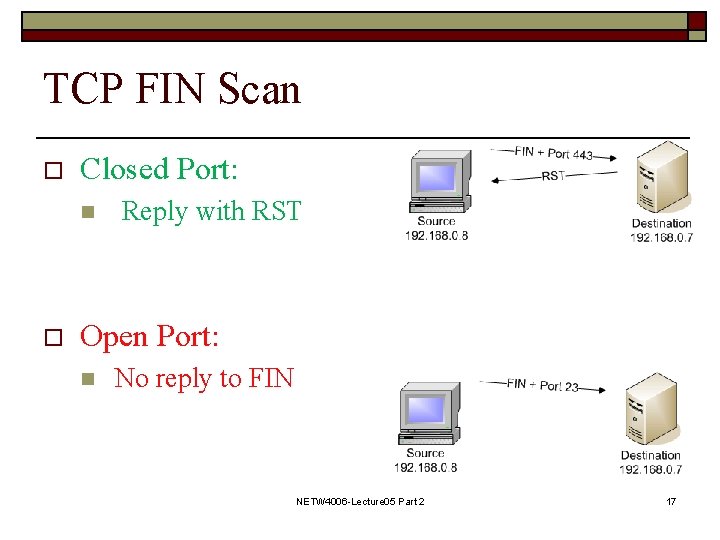
TCP FIN Scan o Closed Port: n o Reply with RST Open Port: n No reply to FIN NETW 4006 -Lecture 05 Part 2 17
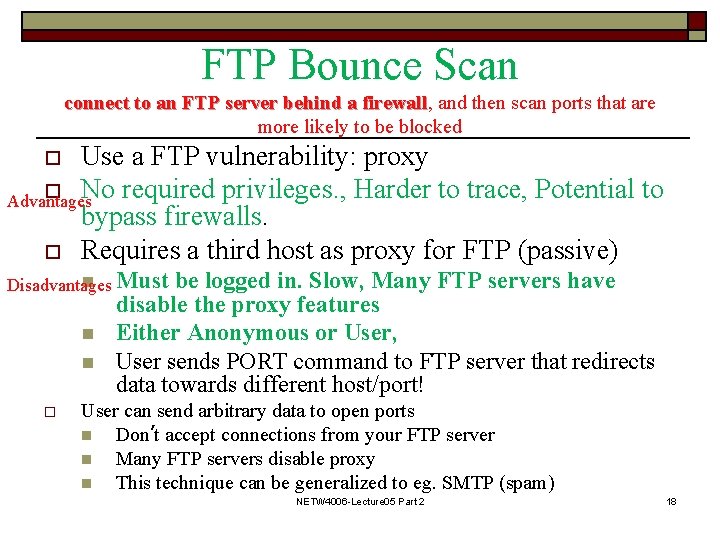
FTP Bounce Scan connect to an FTP server behind a firewall, firewall and then scan ports that are more likely to be blocked Use a FTP vulnerability: proxy o No required privileges. , Harder to trace, Potential to Advantages bypass firewalls. o Requires a third host as proxy for FTP (passive) o n Must Disadvantages n n o be logged in. Slow, Many FTP servers have disable the proxy features Either Anonymous or User, User sends PORT command to FTP server that redirects data towards different host/port! User can send arbitrary data to open ports n Don’t accept connections from your FTP server n Many FTP servers disable proxy n This technique can be generalized to eg. SMTP (spam) NETW 4006 -Lecture 05 Part 2 18
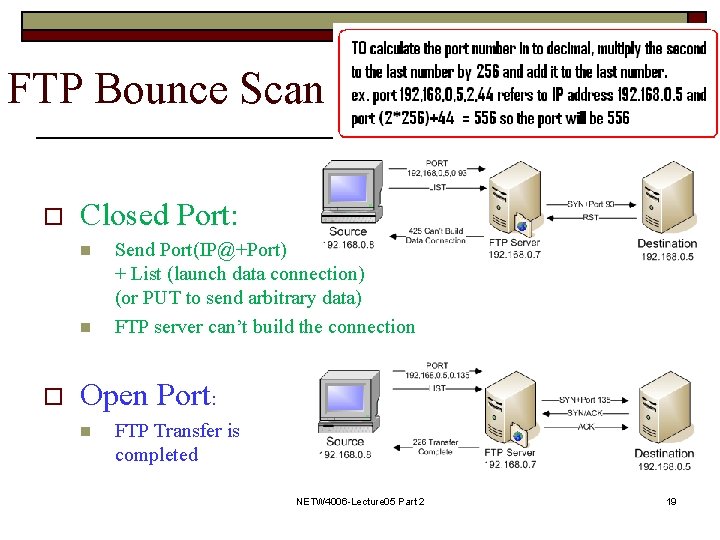
FTP Bounce Scan o Closed Port: n n o Send Port(IP@+Port) + List (launch data connection) (or PUT to send arbitrary data) FTP server can’t build the connection Open Port: n FTP Transfer is completed NETW 4006 -Lecture 05 Part 2 19
UDP Scan o o Scan is more difficult n No ACK from open ports n Most host send an ICMP_ Port_ Unreached error when you send a packet to a closed UDP port. Reading ICMP packets requires root privileges Can find out if system is alive If ICMP is filtered, no response to UDP ping NETW 4006 -Lecture 05 Part 2 20
UDP Ping Scan o Closed Port: UDP ping, If ICMP Port Unreachable system is alive n o Open Port: n n If no response: remote system unavailable. Could be incorrect because UDP applications don’t necessarily send a response to empty requests NETW 4006 -Lecture 05 Part 2 21
Other Scan Techniques o Stealth scan: refers to scanning techniques that can avoid being logged n o fragmented packets, SYN scanning, FIN scanning, scan slowly etc identd protocol: gives username of the owner of process connected via TCP n n Connect http port (80) + use identd Ident (aka auth) protocol use is uncommon NETW 4006 -Lecture 05 Part 2 22
Detect Scan o o Rapid Scan detected: several packets rapidly sent to different ports from same source SYN to a closed port Port scan logged by the services/application Firewall log scanning A detector can inform is that we have been port scanned, but the source address may have been spoofed. NETW 4006 -Lecture 05 Part 2 23
- Slides: 23