Polynomially Homomorphic Signatures Dan Boneh Stanford University Joint
Polynomially Homomorphic Signatures Dan Boneh Stanford University Joint work with David Freeman
![Recall: fully homomorphic encryption server PK, Epk[x] Epk[ f(x) ] For any function f Recall: fully homomorphic encryption server PK, Epk[x] Epk[ f(x) ] For any function f](http://slidetodoc.com/presentation_image_h/e6bbb5395bff2f344ba1fe41a92055cc/image-2.jpg)
Recall: fully homomorphic encryption server PK, Epk[x] Epk[ f(x) ] For any function f [G’ 09, SV’ 10, v. DGHV’ 10, …] Lots of excitement around this concept (FHE)
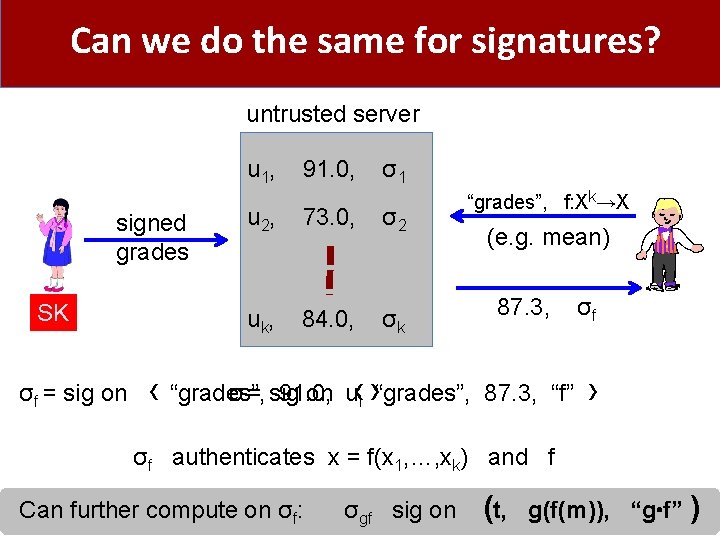
Can we do the same for signatures? untrusted server u 1, 91. 0, σ1 signed grades SK u 2, 73. 0, σ2 uk, 84. 0, σk “grades”, f: Xk→X (e. g. mean) 87. 3, σf σf = sig on ‹ “grades”, 91. 0, u σ = sig on ‹ “grades”, 87. 3, “f” › i › σf authenticates x = f(x 1, …, xk) and f Can further compute on σf: σgf sig on (t, g(f(m)), “g f” )
![more generally: Predicate Signatures [ABCHSW’ 10] • Homomorphic signature for relation P ⊆ 2 more generally: Predicate Signatures [ABCHSW’ 10] • Homomorphic signature for relation P ⊆ 2](http://slidetodoc.com/presentation_image_h/e6bbb5395bff2f344ba1fe41a92055cc/image-4.jpg)
more generally: Predicate Signatures [ABCHSW’ 10] • Homomorphic signature for relation P ⊆ 2 M × M’ m 1, sign(sk, m 1) S (m , sig. on m) ⇔ SK mk, sign(sk, mk) P*( (m 1, …, mk), m ) • S can generate Alice’s sig on P-approved msgs. and nothing else • Derived sigs should be “short” , “private” , and composable
![Unifies three lines of research • Quoting/Redaction [JMSW’ 02, …] : given (document, sig) Unifies three lines of research • Quoting/Redaction [JMSW’ 02, …] : given (document, sig)](http://slidetodoc.com/presentation_image_h/e6bbb5395bff2f344ba1fe41a92055cc/image-5.jpg)
Unifies three lines of research • Quoting/Redaction [JMSW’ 02, …] : given (document, sig) anyone can derive a signature on substring or subset of document • Linearly homomorphic (network coding) [KFM’ 04, …] : given signatures on vectors v 1, …, vk in Fn anyone can derive a sig on linear combination • Transitive signatures [MR’ 02, …] : given sigs on nodes and edges of graph G=(V, E) anyone can derive sig on (u, v) in V 2 if there is a path from u to v in G
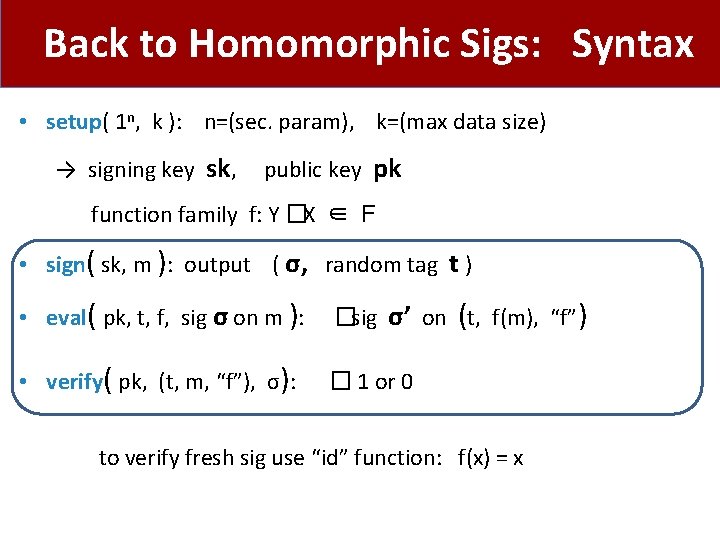
Back to Homomorphic Sigs: Syntax • setup( 1 n, k ): n=(sec. param), k=(max data size) → signing key sk, public key pk function family f: Y � X ∈ F • sign( sk, m ): output ( σ, random tag t ) • eval( pk, t, f, sig σ on m ): � sig σ’ on (t, f(m), “f”) • verify( pk, (t, m, “f”), σ): � 1 or 0 to verify fresh sig use “id” function: f(x) = x
Desirable properties: data m with tag t 1. Certified computation (existential unforgeability): given (σi, ti)�Sign( sk, {mi, 1. . . mi, k} ) for many i, can’t compute σ’ on (ti, x, “f”) for x ≠ f(mi, 1 … mi, k) 2. Private: Let σ’ be derived sig on (t, x, “f”) for x = f(m). given x and f, sig. σ’ reveals “no other info” about m 3. Short: the length of σ’ is at most ( log |m| ) × λO(1) 4. Composable
![Privacy: two definitions Weak context hiding [BBD…’ 10] (a la witness indistinguishability): derived sig. Privacy: two definitions Weak context hiding [BBD…’ 10] (a la witness indistinguishability): derived sig.](http://slidetodoc.com/presentation_image_h/e6bbb5395bff2f344ba1fe41a92055cc/image-8.jpg)
Privacy: two definitions Weak context hiding [BBD…’ 10] (a la witness indistinguishability): derived sig. does not help adv. distinguish compatible data sets f(m 1) = f(m 2) derived sig on f(m 1) derived sig on f(m 2) Strong context hiding [MR’ 02, ABCHSW’ 10] (a la zero knowledge): derived sigs look like fresh sigs (given sk and original sigs) m: ( sk, sign(sk, m) , sign(sk, f(m) ) ( sk, sign(sk, m) , eval( pk, , f, sig σ on m ) ) Key difference: original sigs remain hidden in weak context hiding (in both defs adv. can be given the secret key)
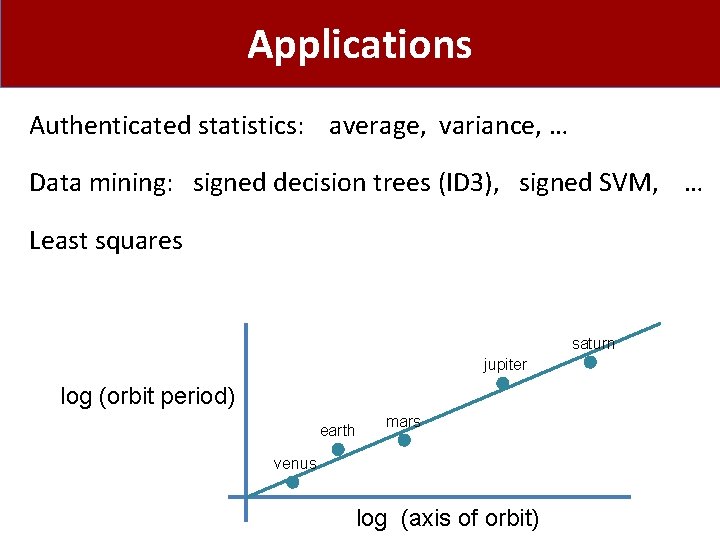
Applications Authenticated statistics: average, variance, … Data mining: signed decision trees (ID 3), signed SVM, … Least squares saturn jupiter log (orbit period) earth mars venus log (axis of orbit)
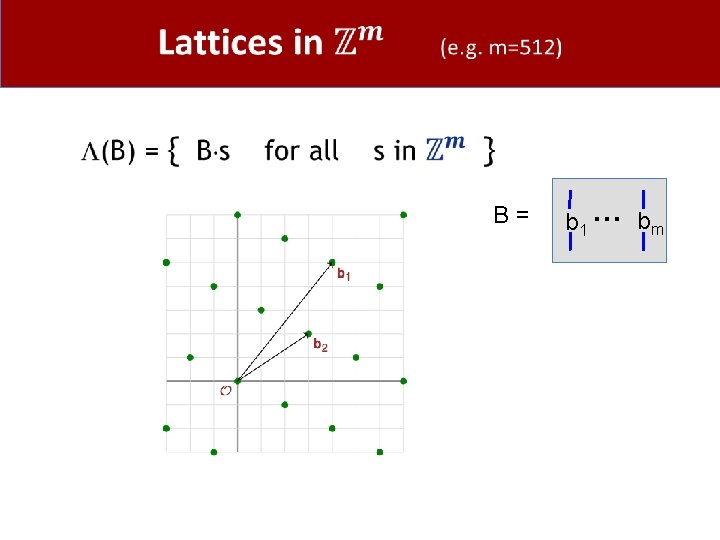
Signed least squares (ex: y = ax+b) Consider data set { (xi, yi) } i=1, …k of integers. Then: a = f(x , y) / h(x, y) and b = g(x, y) / h(x, y) where f, g, h are cubic integer polynomials Using a cubic homomorphic scheme: signed x 1, …, xk, y 1, …, yk ⇒ signed f(x, y), g(x, y), h(x, y)

Constructions
![Homomorphic systems Encryption Large p: [P’ 99, …] Signatures [KFM’ 04, CJL’ 06, BFKW’ Homomorphic systems Encryption Large p: [P’ 99, …] Signatures [KFM’ 04, CJL’ 06, BFKW’](http://slidetodoc.com/presentation_image_h/e6bbb5395bff2f344ba1fe41a92055cc/image-12.jpg)
Homomorphic systems Encryption Large p: [P’ 99, …] Signatures [KFM’ 04, CJL’ 06, BFKW’ 09] Linear functions Small p: [GM’ 82, …] Polynomials quadratic: [BGN’ 05, GHV’ 10] small degree: [G’ 09] Poly-size circuits [G’ 09, v. DGHV’ 10, SV’ 10] [BF’ 10, BF’ 11] [BF’ 11] (small degree) ? ?
![Homomorphic systems Encryption Large p: [P’ 99, …] Signatures [KFM’ 04, CJL’ 06, BFKW’ Homomorphic systems Encryption Large p: [P’ 99, …] Signatures [KFM’ 04, CJL’ 06, BFKW’](http://slidetodoc.com/presentation_image_h/e6bbb5395bff2f344ba1fe41a92055cc/image-13.jpg)
Homomorphic systems Encryption Large p: [P’ 99, …] Signatures [KFM’ 04, CJL’ 06, BFKW’ 09] Linear functions Small p: [GM’ 82, …] Polynomials quadratic: [BGN’ 05, GHV’ 10] small degree: [G’ 09] Poly-size circuits [G’ 09, v. DGHV’ 10, SV’ 10] [BF’ 10, BF’ 11] [BF’ 11] (small degree) ? ?
![Homomorphic systems Encryption Large p: [P’ 99, …] Signatures [KFM’ 04, CJL’ 06, BFKW’ Homomorphic systems Encryption Large p: [P’ 99, …] Signatures [KFM’ 04, CJL’ 06, BFKW’](http://slidetodoc.com/presentation_image_h/e6bbb5395bff2f344ba1fe41a92055cc/image-14.jpg)
Homomorphic systems Encryption Large p: [P’ 99, …] Signatures [KFM’ 04, CJL’ 06, BFKW’ 09] Linear functions Small p: [GM’ 82, …] Polynomials quadratic: [BGN’ 05, GHV’ 10] small degree: [G’ 09] Poly-size circuits [G’ 09, …] [BF’ 10, BF’ 11] [BF’ 11] (small degree) ? ?
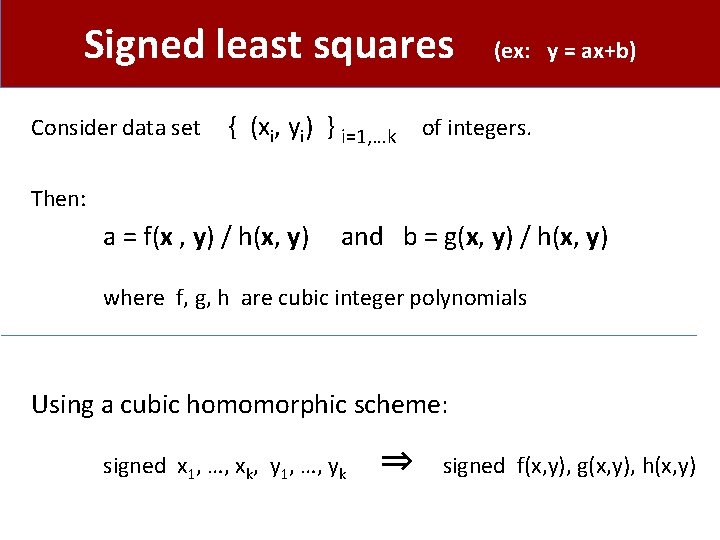
Linearly homomorphis sigs: options •
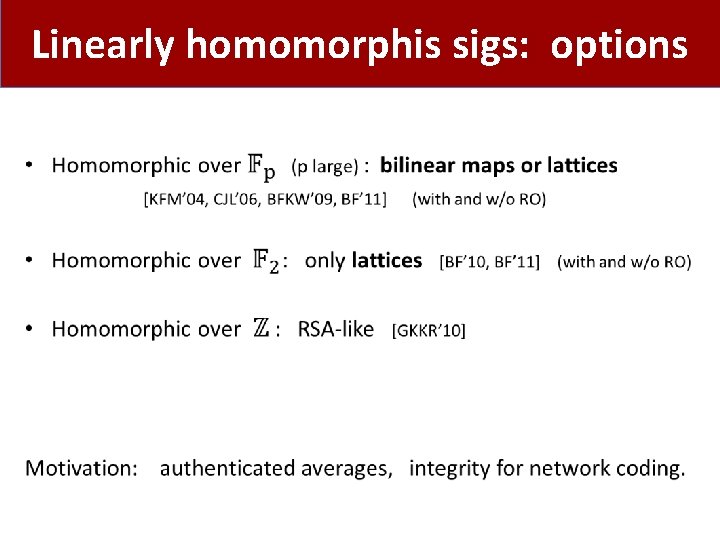
B = b 1 … bm
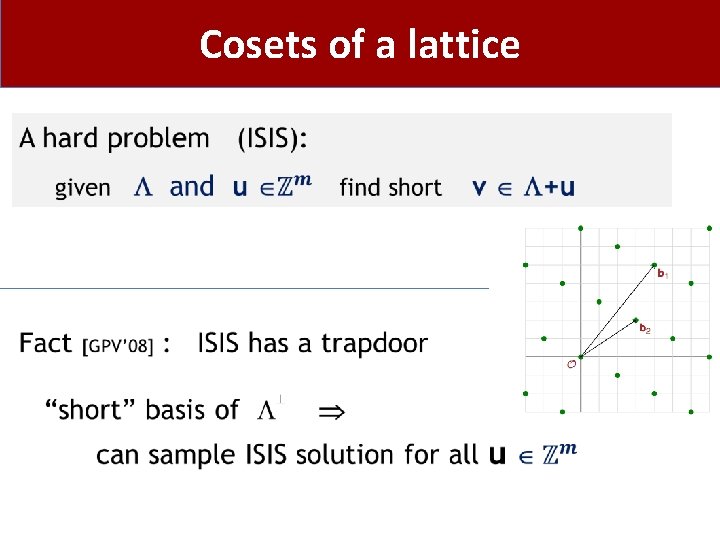
Cosets of a lattice
![Lattice-based signatures [GPV’ 08] • Lattice-based signatures [GPV’ 08] •](http://slidetodoc.com/presentation_image_h/e6bbb5395bff2f344ba1fe41a92055cc/image-18.jpg)
Lattice-based signatures [GPV’ 08] •
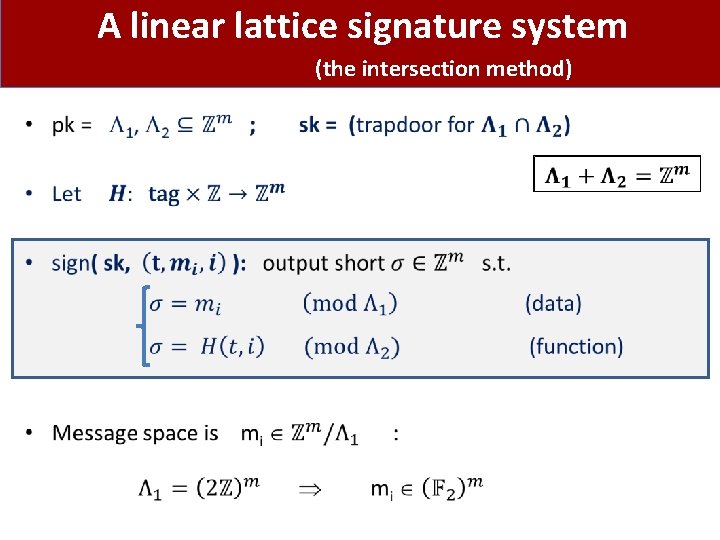
A linear lattice signature system (the intersection method) •
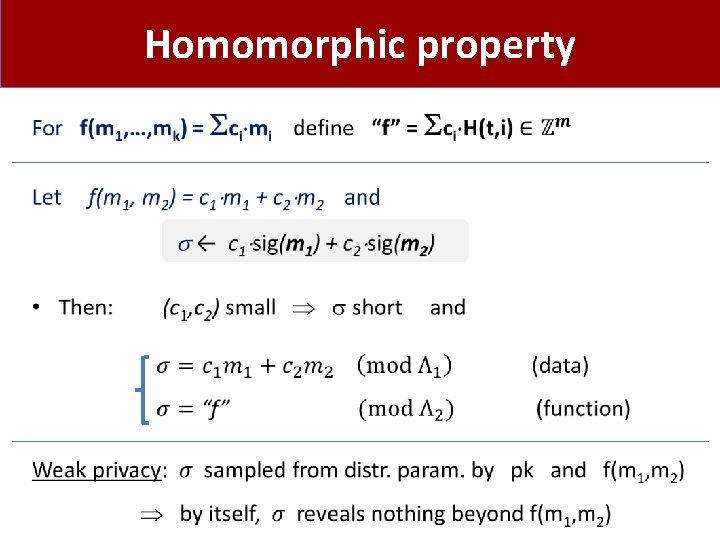
Homomorphic property •
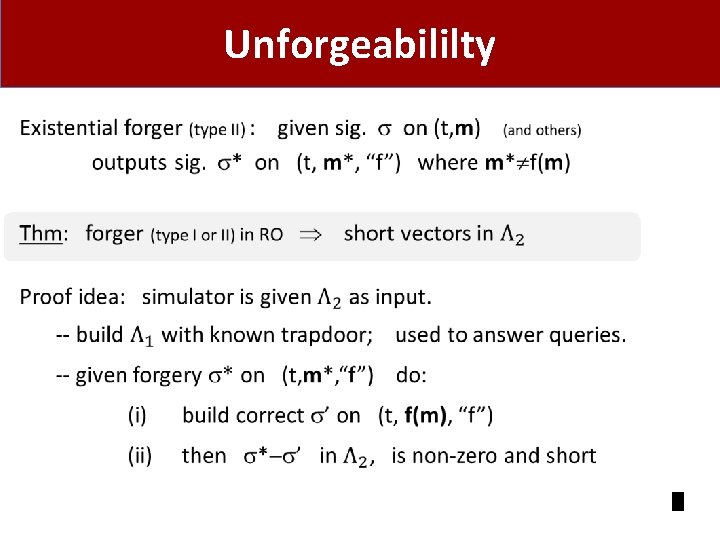
Unforgeabililty •
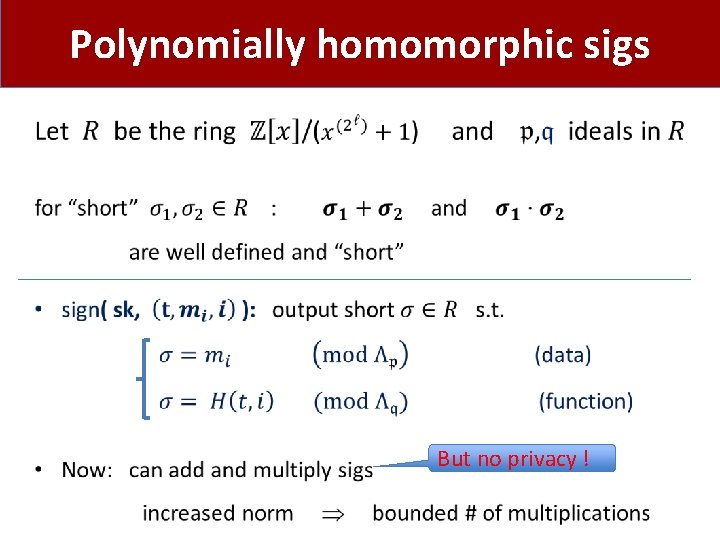
Polynomially homomorphic sigs • But no privacy !
![Summary Encryption Large p: [P’ 99, …] Signatures [KFM’ 04, CJL’ 06, BFKW’ 09] Summary Encryption Large p: [P’ 99, …] Signatures [KFM’ 04, CJL’ 06, BFKW’ 09]](http://slidetodoc.com/presentation_image_h/e6bbb5395bff2f344ba1fe41a92055cc/image-23.jpg)
Summary Encryption Large p: [P’ 99, …] Signatures [KFM’ 04, CJL’ 06, BFKW’ 09] Linear functions Small p: [GM’ 82, …] Polynomials quadratic: [BGN’ 05, GHV’ 10] small degree: [G’ 09] Poly-size circuits [G’ 09, …] [BF’ 10] [BF’ 11] (small degree) ? ?
![Alternate approaches Computationally Sound (CS) Proofs [Micali’ 00] m, t sign( sk, (t, m) Alternate approaches Computationally Sound (CS) Proofs [Micali’ 00] m, t sign( sk, (t, m)](http://slidetodoc.com/presentation_image_h/e6bbb5395bff2f344ba1fe41a92055cc/image-24.jpg)
Alternate approaches Computationally Sound (CS) Proofs [Micali’ 00] m, t sign( sk, (t, m) ) m, t σ t, f: Y → X x=f(m), proof π π: short proof of knowledge [V’ 07] that x = f(m), and (t, f, x) ∈ (t, f, x; m, σ) s. t. verify(PK, (t, m), σ) = 1 { Need PCP machinery. Harder to compose [V’ 07] Cannot build from falsifiable assumptions [GW’ 11] }
Many open problems • Fully homomorphic sigs (a la Gentry’s bootstrapping) • Or more than low-degree polynomials • Polynomially homomorphic sigs: • with privacy • without random oracles (can do for linear sigs)
THE END
Restricted Homomorphic Encryption Back in 2008: best homomorphic systems -- linear or quadratic operations Prabhakaran and Rosulek [PR’ 08] : • Built systems that provably support only linear operations. More generally: can we build systems that support a restricted set of homomorphisms F ?
![Applications [BSW’ 11] Network guards on encrypted traffic: Guard 1 Guard 2 With restricted Applications [BSW’ 11] Network guards on encrypted traffic: Guard 1 Guard 2 With restricted](http://slidetodoc.com/presentation_image_h/e6bbb5395bff2f344ba1fe41a92055cc/image-28.jpg)
Applications [BSW’ 11] Network guards on encrypted traffic: Guard 1 Guard 2 With restricted FHE: guard can implement policy, but nothing else Goal: restricted FHE that keeps ciphertext size short
![A New Construction [BSW’ 11] Fully Hom. Enc. for F func. family F • A New Construction [BSW’ 11] Fully Hom. Enc. for F func. family F •](http://slidetodoc.com/presentation_image_h/e6bbb5395bff2f344ba1fe41a92055cc/image-29.jpg)
A New Construction [BSW’ 11] Fully Hom. Enc. for F func. family F • Properties: no ciphertext expansion under constant iteration • Tools: a recent short NIZK due to Groth [G’ 10]
- Slides: 29