PoliceNCA Cybercrime Training Denis A Nicole danecs soton
Police/NCA Cybercrime Training Denis A Nicole dan@ecs. soton. ac. uk 2014 -08 -07
When the military’s top cyberwarriors gathered last year inside a secretive compound at Fort Meade, Maryland, for a classified war game exercise, a team of active-duty troops faced off against several teams of reservists. And the active-duty team apparently took a beating. “They were pretty much obliterated, ” said one Capitol Hill staffer who attended the exercise. “The active-duty team didn’t even know how they’d been attacked. ” http: //www. navytimes. com/article/20140804/NEWS 04/308040019 2
Congress has authorized the FBI to add 2, 000 personnel to its rolls this year, and many of those new recruits will be assigned to tackle cyber crimes, a growing priority for the agency. And that’s a problem, FBI Director Comey told the White Collar Crime Institute, an annual conference held at the New York City Bar Association in Manhattan. A lot of the nation’s top computer programmers and hacking gurus are also fond of marijuana. “I have to hire a great work force to compete with those cyber criminals and some of those kids want to smoke weed on the way to the interview, ” Mr. Comey said that the agency was “grappling with the question right now” of how to amend the agency’s marijuana policies, which excludes from consideration anyone who has smoked marijuana in the previous three years, according to the FBI’s Web site. One conference goer asked Mr. Comey about a friend who had shied away from applying because of the policy. “He should go ahead and apply, ” despite the marijuana use, Mr. Comey said. http: //blogs. wsj. com/law/2014/05/20/director-comey-fbi-grappling-with-hiringpolicy-concerning-marijuana/ 3
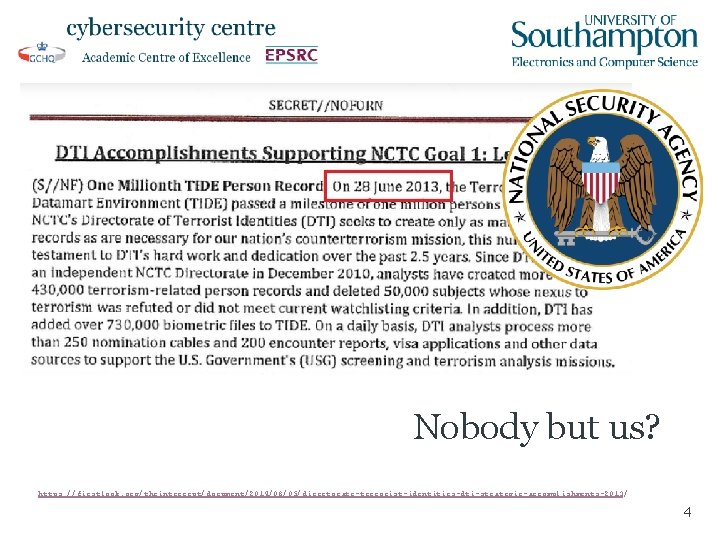
Nobody but us? https: //firstlook. org/theintercept/document/2014/08/05/directorate-terrorist-identities-dti-strategic-accomplishments-2013/ 4
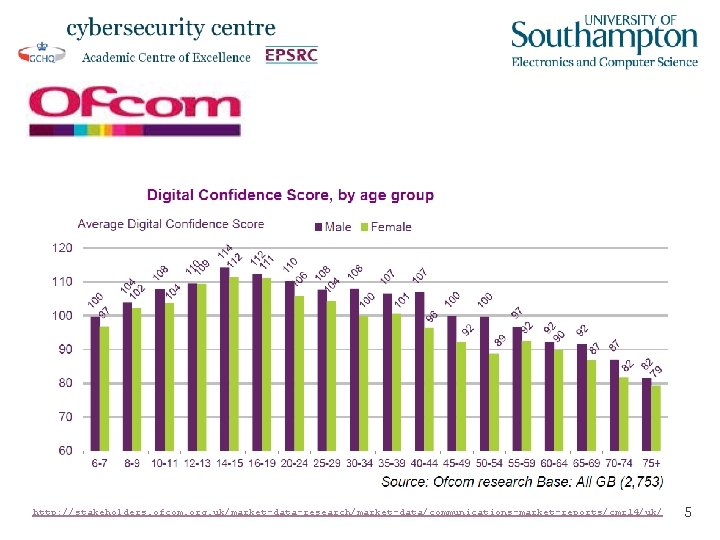
http: //stakeholders. ofcom. org. uk/market-data-research/market-data/communications-market-reports/cmr 14/uk/ 5
Year of Code Teachers could be trained how to educate students in computer programming “in a day” Lottie Dexter http: //www. bbc. co. uk/news/technology-26150717 6
1969 Toby Harris went on to be the first chair of the Metropolitan Police Authority. 7
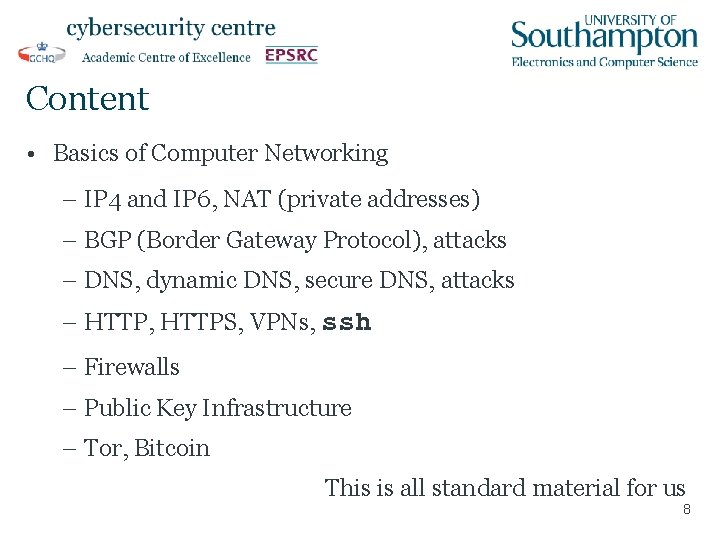
Content • Basics of Computer Networking – IP 4 and IP 6, NAT (private addresses) – BGP (Border Gateway Protocol), attacks – DNS, dynamic DNS, secure DNS, attacks – HTTP, HTTPS, VPNs, ssh – Firewalls – Public Key Infrastructure – Tor, Bitcoin This is all standard material for us 8
Cybercrime concepts • Basic: SQL injection, cross-site scripting, DDo. S. • Malware: viruses, attack surfaces (software and hardware). • Patching, antivirus, network monitoring. • Motivations, sophistication of attackers, insiders? • Forensic analysis: little real experience at Southampton. • Network traffic analysis: off-site specialists. 9
Types of Malware • Browser attacks • Application attacks • OS attacks • Rootkits • HW attacks 10
Basic Computer Forensics • Major tools are probably – En. Case: expensive, no experience in ECS https: //www. guidancesoftware. com/ – SANS: we have some experience here http: //digital-forensics. sans. org/community/cheat-sheets • More advanced techniques – Malware analysis (IDA Pro) https: //www. hex-rays. com/products/ida/ – Password Cracking http: //www. openwall. com/john/ 11
Hands-on laboratory work • RFID • CHIP AND PIN • Penetration testing: Ponzi. Bank • XSS • Side Channels • Malware analysis 12
Which do you trust? 13
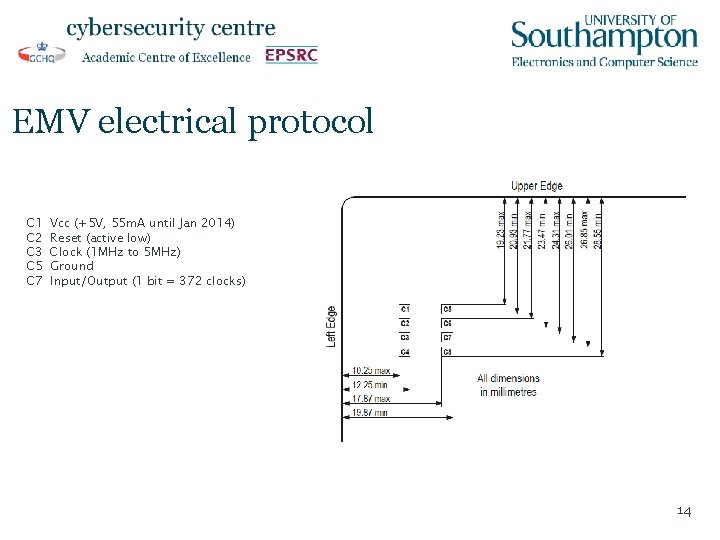
EMV electrical protocol C 1 C 2 C 3 C 5 C 7 Vcc (+5 V, 55 m. A until Jan 2014) Reset (active low) Clock (1 MHz to 5 MHz) Ground Input/Output (1 bit = 372 clocks) 14
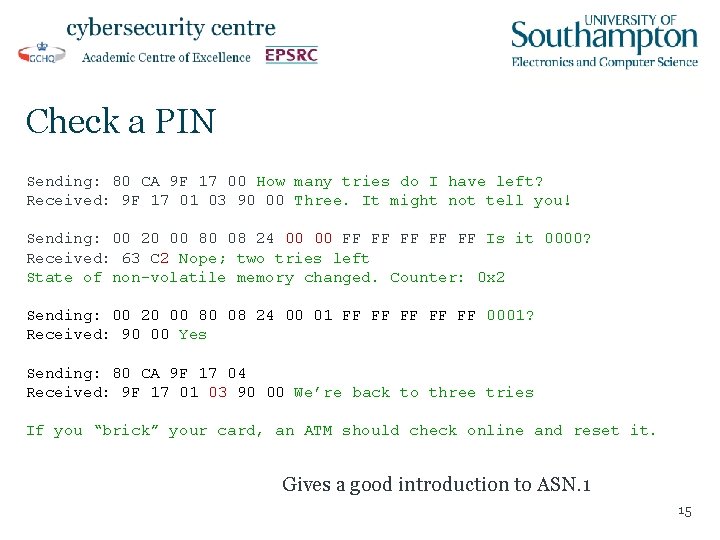
Check a PIN Sending: 80 CA 9 F 17 00 How many tries do I have left? Received: 9 F 17 01 03 90 00 Three. It might not tell you! Sending: 00 20 00 80 08 24 00 00 FF FF FF Is it 0000? Received: 63 C 2 Nope; two tries left State of non-volatile memory changed. Counter: 0 x 2 Sending: 00 20 00 80 08 24 00 01 FF FF FF 0001? Received: 90 00 Yes Sending: 80 CA 9 F 17 04 Received: 9 F 17 01 03 90 00 We’re back to three tries If you “brick” your card, an ATM should check online and reset it. Gives a good introduction to ASN. 1 15
Ponzi. Bank http: //xkcd. com/327/ 16
Research: C/C++ Verification Presentation to HP Denis A Nicole dan@ecs. soton. ac. uk 2014 -05 -07
Our contribution to security • A whole new class of software vulnerabilities arise in “multicore” chips: all modern phones, desktops and servers. • The vulnerabilities are timing-dependent and cannot usually be found by conventional testing. 18

ESBMC is a Collaboration between • University of Southampton – Jeremy Morse and Denis Nicole • Federal University of Amazonas, Brazil – Mikhail Ramalho, Mauro Freitas, Felipe Sousa, Hendrio Marques and Lucas Cordeiro • University of Stellenbosch, South Africa – Bernd Fischer 19
ESBMC is a bounded model checker • It exhaustively analyses all possible behaviours of a (multithreaded) C or C++ program up to a fixed depth of – loop iteration (including backward jumps and recursion), – thread interleaving. • Within these bounds, it checks for – C errors: pointer errors, arithmetic errors, array bounds, malloc()/free(), assert() failures, data races, etc. – Violation of Linear Temporal Logic specifications. 20
Model Checking is not Simulation • Simulation (testing) checks correctness for a particular input and a particular thread interleaving. • You need to run multiple simulations with different data and different timing before you get some assurance. • Model Checking exhaustively analyses all possible behaviours over a range of possible inputs and generates a witness, a trace of program state, if there any possible failures. • Good-coverage simulation may be effective against “random” errors; it offers little protection against tailored attacks. 21
Improvement by competition • The field of C model checking research is now large enough to support annual competitions; perhaps the best known is that held in conjunction with the International Conference on Tools and Algorithms for the Construction and Analysis of Systems (TACAS). • The team is proud to report that ESBMC v 1. 17 won the Gold Medal in the System. C and Concurrency categories and the Bronze Medal in the overall ranking of the first International Competition on Software Verification at TACAS 2012. • ESBMC v 1. 20 won the Bronze Medal in the overall ranking of the second competition at TACAS 2013. 22
- Slides: 22