PKI versus Private Credentials Stefan Brands ZeroKnowledge Systems
PKI versus Private Credentials Stefan Brands Zero-Knowledge Systems Inc. Montreal PKI versus Private Credentials 1
Digital Certificates: n n n sequences of zeros and ones (of a mathematical structure) verifiable with 100 % accuracy by computers transferable electronically (no human intervention, fast) unforgeable (crypto protection) can specify any kind of data PKI versus Private Credentials 2
Identity Certificates: n n CA digital signature binds public key to real name secret key signs message (prevents replay, non-repudiation) verify by applying CA's public key use as authenticated pointer into databases (like SSNs) PKI versus Private Credentials 3
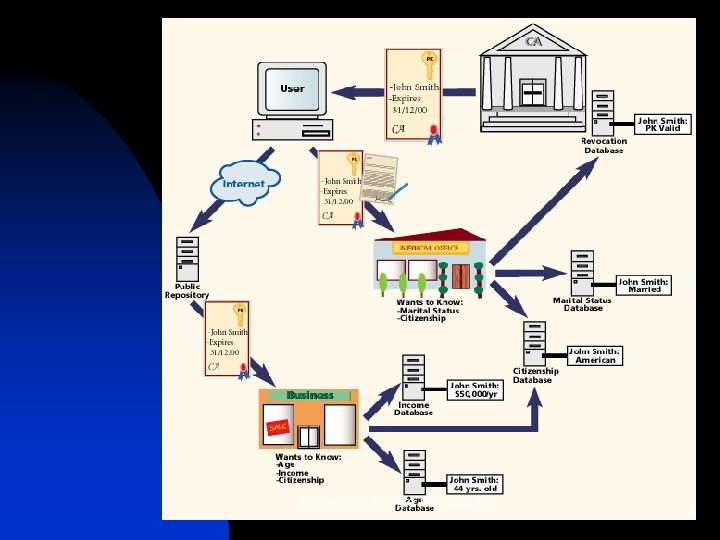
PKI versus Private Credentials 4
Federal PKIs: n n n USA (Access Certificates for Electronic Services, FPKI) United Kingdom (CLOUD COVER) Australia (Public Key Auth. Framework, Gatekeeper) Canada (Canada Public Key Infrastructure) Hong Kong (identity certificates to most residents) PKI versus Private Credentials 5
In the future: n n n mobile phones watches televisions cars computerized household appliances … PKI versus Private Credentials 6
Drawbacks to organizations: n n n transaction delays loose business (faulty/ irrelevant data, online connection fails) central database verification hard to protect databases against hackers and insiders privacy standards bring compliance costs Manage CRLs / online validation PKI versus Private Credentials 7
Privacy concerns: n n n n traceability (CA, verifiers, wiretappers, intel. agencies) linkability (in and across PKIs) non-repudiable evidence discrimination (consults any database) errors (database, identities) no control over secondary use revocation (CRL, online whitelists) PKI versus Private Credentials 8

Legislation ineffective: n n n n does not deter criminals stopping violations takes long legislation implemented ? technologies faster than law theft / modification by hackers ? misuse by employees ? laws may be amended, changed, exempted, overturned, or ignored database audits -> accessibility PKI versus Private Credentials 9

Privacy design goals: n n n control (selective disclosure) anonymity unlinkability no self-authenticating records smartcard implementations PKI versus Private Credentials 10
Private Credentials: n n similar to coins and public transport tickets (not identifiable) meet all privacy design goals practical security benefits PKI versus Private Credentials 11
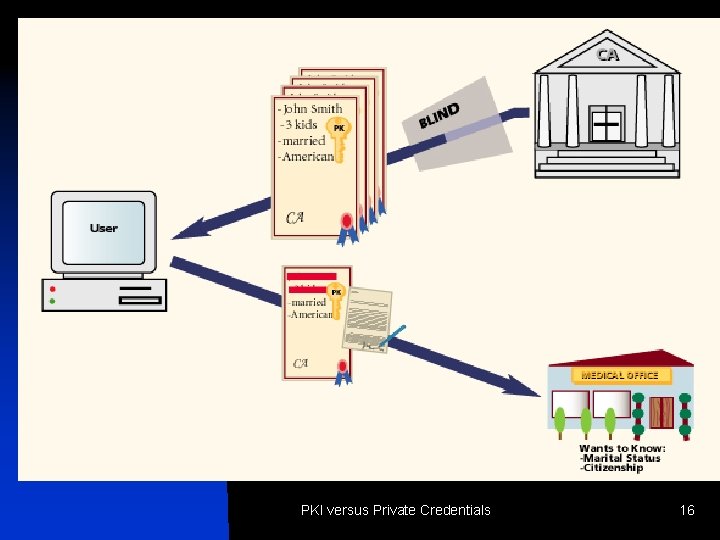
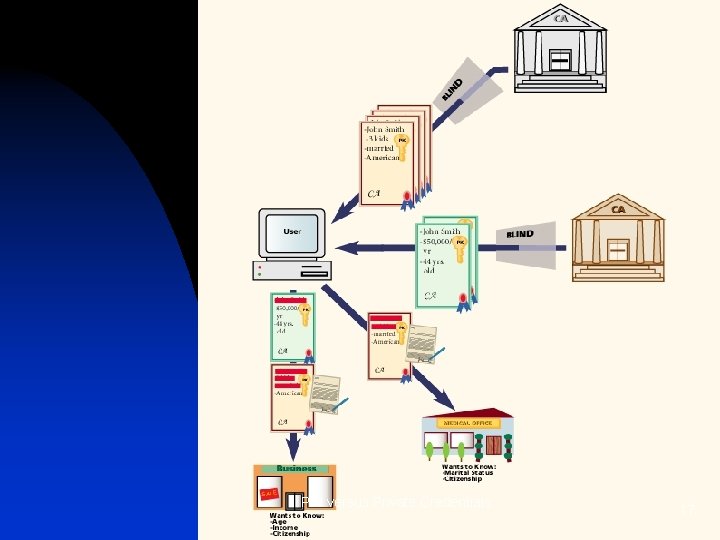
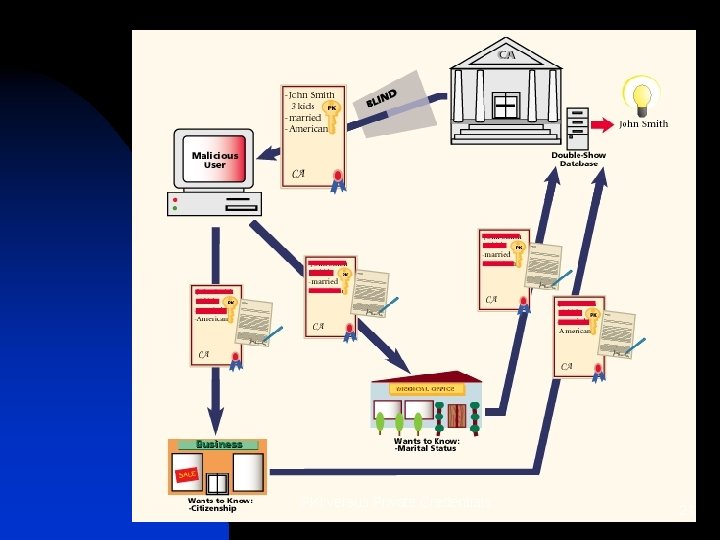
Issuing a Private Credential: n n n Certificate binds public key to attributes CA cannot learn user's public key and CA's signature (blinding) CA encodes attributes into user's secret key PKI versus Private Credentials 12
Showing a Private Credential: n n Send public key and CA signature selectively disclose property of attributes sign message (= authenticate property) replay prevention PKI versus Private Credentials 13
Note: n n n different attributes in different or same Private Credentials anyone can be CA one attribute may be identity selective disclosure unlinkability PKI versus Private Credentials 14
Selective disclosure: n n n show part of attribute data without revealing more (think: marker) more powerful than paper-based certificates (Boolean properties, n out of m, intervals) works across different Private Credentials PKI versus Private Credentials 15
PKI versus Private Credentials 16
PKI versus Private Credentials 17
Reissuance: n n refresh previously issued Credential without knowing attributes update Credential's attributes before refreshing PKI versus Private Credentials 18
Dossier-Resistance: n n n verifier gets zero evidence of transaction; or verifier gets self-authenticating evidence of a message or a part of the disclosed property self-authenticating evidence can be limited to designated parties PKI versus Private Credentials 19
Fraud protections: n n n reduce identity fraud eliminate central database risks limited-show property (identity computable if shown too often) discourage lending (encode secret of user) discourage discarding (tie unfavorable attributes in) PKI versus Private Credentials 20
PKI versus Private Credentials 21
Smartcard implementation: n n strong protection against loss, theft, extortion, lending, copying, discarding, etc can use standard 8 -bit chips use desktop computer, notebook, handheld, mobile phone, … user's computer protects privacy, smartcard cannot leak data PKI versus Private Credentials 22
Benefits to organizations: n n n n prevent unfair competition no law enforcement intrusions reduce identity fraud foster fair competition cheapest way to comply with privacy principles improve transaction finality cultivate goodwill PKI versus Private Credentials 23
Private Credentials can subsume X. 509: n n two attributes: certificate holder's X. 500 name, all other fields restrict entropy of X. 509 validity period restrict entropy of extension fields set serial number to hash of the public key or to zero PKI versus Private Credentials 24
Sample applications: n n n electronic cash digital pseudonyms for public forums and virtual communities access control (VPNs, subscription services, Web sites, databases) digital copyright protection (certificates permit use of works) electronic voting PKI versus Private Credentials 25

(continued) n n n n n electronic patient files electronic postage automated data bartering online auctions financial securities trading pay-per-view tickets public transport ticketing electronic food stamps road-toll pricing PKI versus Private Credentials 26

(continued) n n n n national ID cards (with privacy) permission-based marketing Web site personalization multi-agent systems collaborative filtering loyalty schemes electronic gambling medical prescriptions PKI versus Private Credentials 27
For more information: n n “Rethinking Public Key Infrastructures and Digital Certificates; Building in Privacy, ” ISBN 0 -262 -02491 -8, MIT Press August 2000, 356 pp. “Private Cedentials, ” whitepaper, Zero-Knowledge Systems, September 2000 brands@zeroknowledge. com www. xs 4 all. nl/~brands PKI versus Private Credentials 28
- Slides: 28