PKI Mobile Commerce Lisa Pretty PKI Forum Philip

PKI & Mobile Commerce Lisa Pretty, PKI Forum Philip Berton, Baltimore
Overview • m-Commerce needs for security • PKI Tutorial • Current Advancements in PKI • Q&A
Intro to PKI Forum “The PKI Forum is an international, notfor-profit, multi-vendor and end-user alliance whose purpose is to accelerate the adoption and use of Public-Key Infrastructure (PKI). The PKI Forum advocates industry cooperation and market awareness to enable organizations to understand exploit the value of PKI in their e-business applications. ”
State of Digital Mobile Telephony • Global System for Mobile Communications (GSM) has over 215 million subscribers • GSM alone has more subscribers than the Internet has users (210)
Examples of Wireless Applications • Top three uses of Internet enabled mobile phones: • Travel related uses • Online banking • Email
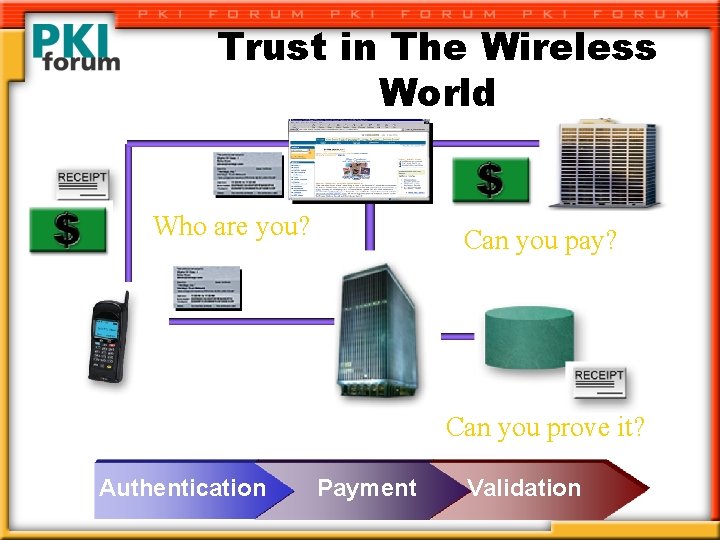
Trust in The Wireless World Who are you? Can you pay? Can you prove it? Authentication Payment Validation
What is Public Key Infrastructure • Public Key Infrastructure (PKI) is a combination of enabling technologies and practices which offer organizations and individual users ways to significantly enhance their security as well as protecting , identities, transactions and privacy on internal and public networks • It is essential for successfully deploying e-business applications
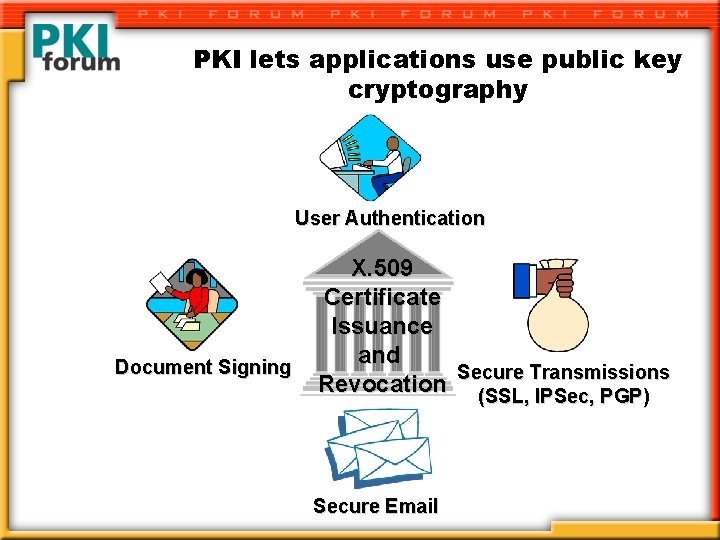
PKI lets applications use public key cryptography User Authentication Document Signing X. 509 Certificate Issuance and Secure Transmissions Revocation (SSL, IPSec, PGP) Secure Email
What PKI Provides u u Authentication to ensure parties are who they say they are Confidentiality to protect sensitive information Integrity to guarantee a transaction is not altered Non-repudiation to prove the transaction occurred – [to prevent any of the parties from reneging on a transaction]
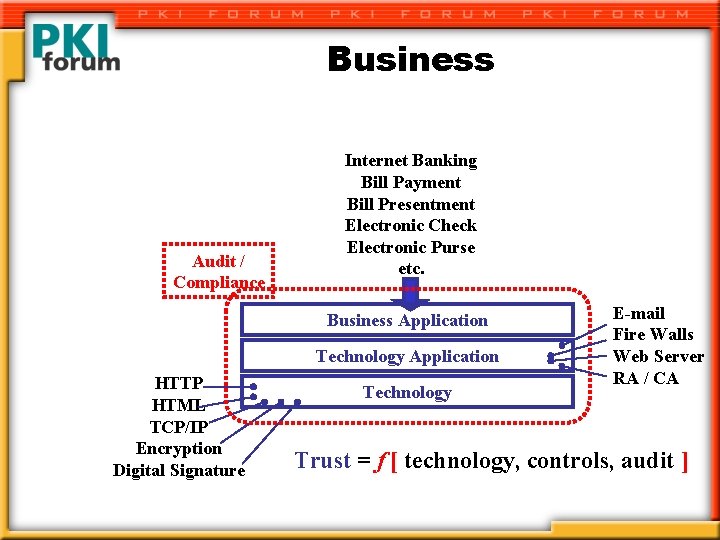
Business Audit / Compliance Internet Banking Bill Payment Bill Presentment Electronic Check Electronic Purse etc. Business Application Technology Application HTTP HTML TCP/IP Encryption Digital Signature Technology E-mail Fire Walls Web Server RA / CA Trust = f [ technology, controls, audit ]
Technology • PKI technologically rests on: – – Cryptography—symmetric, asymmetric and hash Directories and data bases IT security protocols (SSL, SMIME, IPSEC, etc. ) Communications/network substrate (TCP/IP, networking, telephony, etc. ) – Certificate interoperability, management • V 509 V 3, DCE, etc. • CRL, OCSP, ASN 1
Cryptography Is THE Basis for PKI • There are three types of Cryptosystems – Symmetric Key (sometimes called Secret Key) – Asymmetric Key (Public Private Key Pairs) – Message digests • The best systems use all 3 cryptosystems
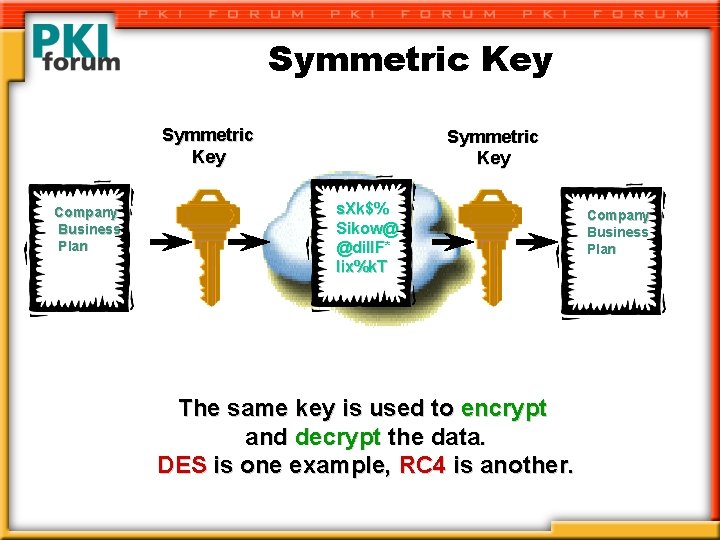
Symmetric Key Company Business Plan Symmetric Key s. Xk$% Sikow@ @dil. IF* lix%k. T The same key is used to encrypt and decrypt the data. DES is one example, RC 4 is another. Company Business Plan
Symmetric Key • The Advantages – Secure – Widely Used – The encrypted text is compact – Fast • The Disadvantages – Complex Admin – Requires Secret Key Sharing – Large Number of Keys – No non-repudiation – Subject to interception
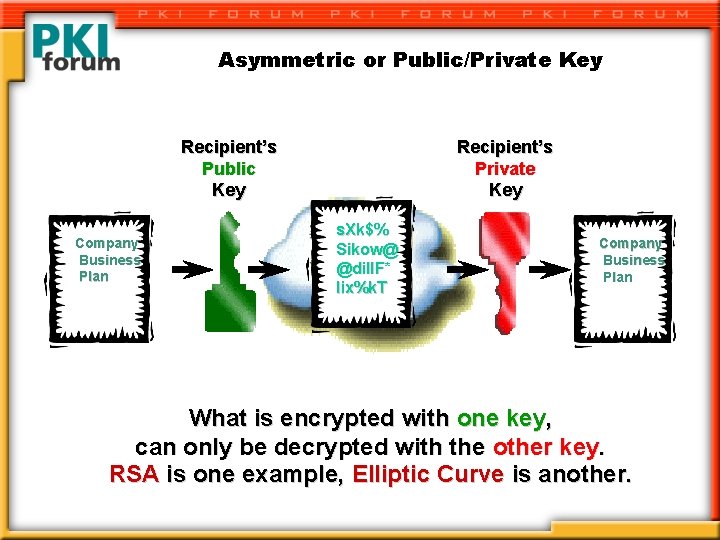
Asymmetric or Public/Private Key Recipient’s Public Key Company Business Plan Recipient’s Private Key s. Xk$% Sikow@ @dil. IF* lix%k. T Company Business Plan What is encrypted with one key, can only be decrypted with the other key. RSA is one example, Elliptic Curve is another.
Asymmetric or Public/Private Key • The Advantages – – – Secure No secret sharing No prior relationship Easier Admin Many fewer keys Supports non-repudiation • The Disadvantages – Slower than symmetric key – The encrypted text is larger than a symmetric version
Message Digest Algorithms • Hashes are also widely used in cryptography, but crypto hashes have some special properties: – They cannot be run backwards to learn something about the original plain text – The resulting hash does not tell you anything about the original plain text – You cannot easily identify a plain text which will hash to a specific hash value • SHA 1 and MD 5 are examples of crypto hashes
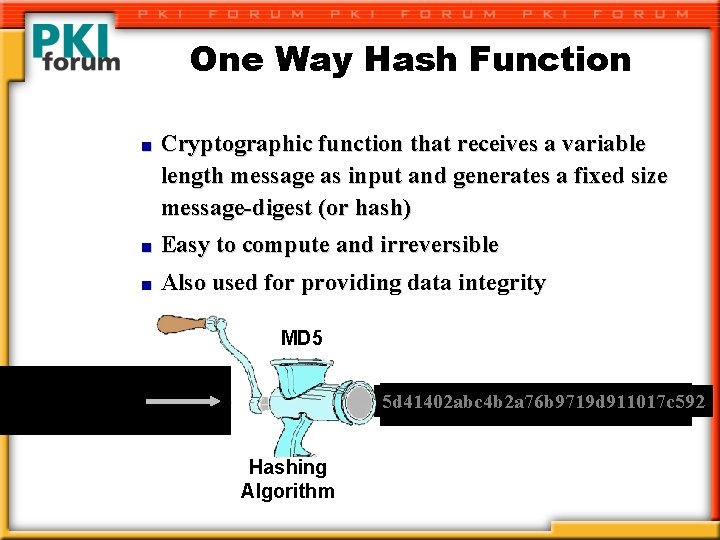
One Way Hash Function n Cryptographic function that receives a variable length message as input and generates a fixed size message-digest (or hash) n Easy to compute and irreversible n Also used for providing data integrity MD 5 This is a sample hello input message. 5 d 41402 abc 4 b 2 a 76 b 9719 d 911017 c 592 9 bcfacf 49 c 4636 ee 69 e 6 ca 22 aae 984 c 6 Hashing Algorithm
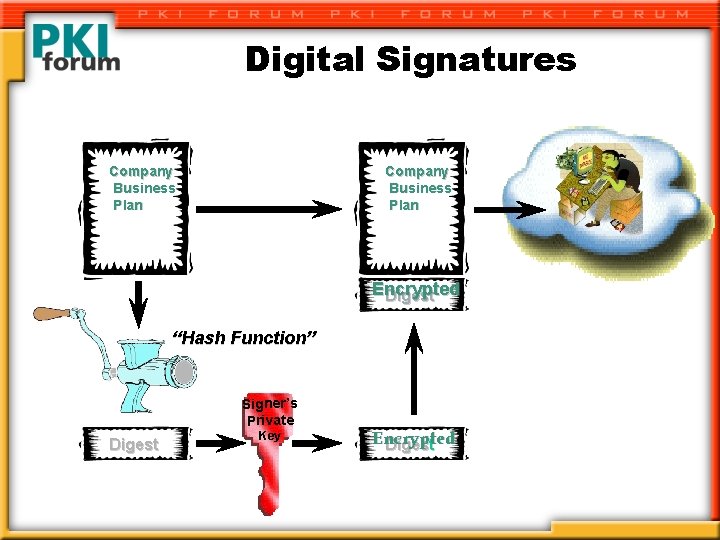
Digital Signatures Company Business Plan Encrypted Digest “Hash Function” Signer’s Private Digest Key Encrypted Digest
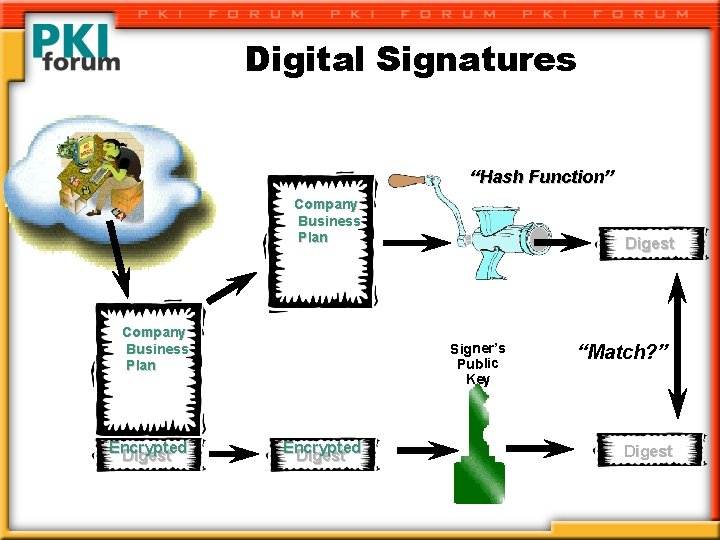
Digital Signatures “Hash Function” Company Business Plan Encrypted Digest Signer’s Public Key Encrypted Digest “Match? ” Digest
Cryptosystems Symmetric Key Encryption Public Key Encryption Message Digest
PKI Components • Public/private key pair • Digital certificate • Certificate authority • Repository • PKI Enabled Client • POLICY
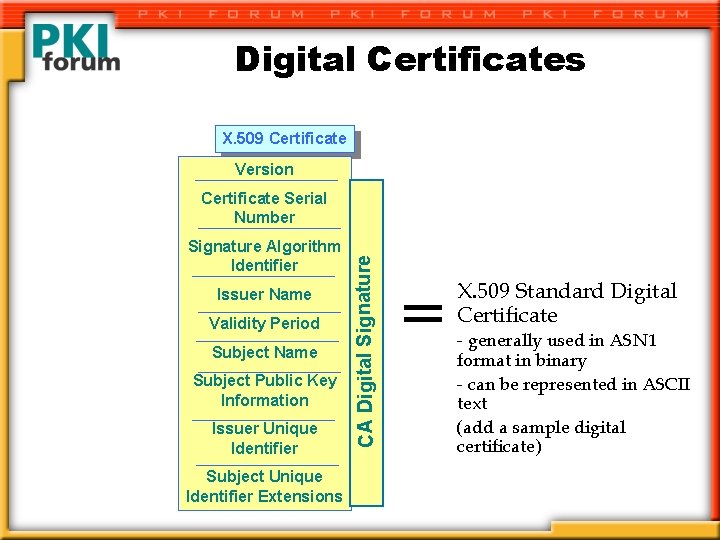
Digital Certificates X. 509 Certificate Version Signature Algorithm Identifier Issuer Name Validity Period Subject Name Subject Public Key Information Issuer Unique Identifier Subject Unique Identifier Extensions CA Digital Signature Certificate Serial Number = X. 509 Standard Digital Certificate - generally used in ASN 1 format in binary - can be represented in ASCII text (add a sample digital certificate)
Trusting the Public Key l a t i g i D 9 0 icate 5. X rtif y l l e C ficia f e o h t “I rize n a t o i o t n ia c s i o h s t as een r e s u w t r e a b l u c i t r pa d this an ular c ” i t y r e a K p c i l b u P
X. 509 What? ? “The International Telecommunications Union, ITU-T (formerly know as CCITT), is a multinational union that provides standards for telecommunication equipment and systems. ITU-T possesses a particular fashion for naming an ITU-T X. 500 directory [CCI 88 b], X. 509 certificates and Distinguished Names. Distinguished names are the standard form of naming… ITU-T Recommendation X. 509 [CCI 88 c] specifies the authentication service for X. 500 directories, as well as the widely adopted X. 509 certificate syntax. ” … in other words, a standards body
Standards • PKCS • IETF • ANSI X 9 F …
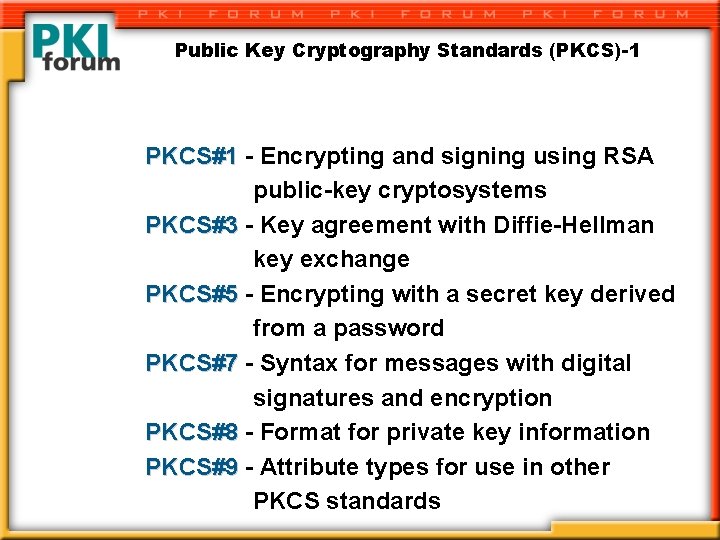
Public Key Cryptography Standards (PKCS)-1 PKCS#1 - Encrypting and signing using RSA public-key cryptosystems PKCS#3 - Key agreement with Diffie-Hellman key exchange PKCS#5 - Encrypting with a secret key derived from a password PKCS#7 - Syntax for messages with digital signatures and encryption PKCS#8 - Format for private key information PKCS#9 - Attribute types for use in other PKCS standards
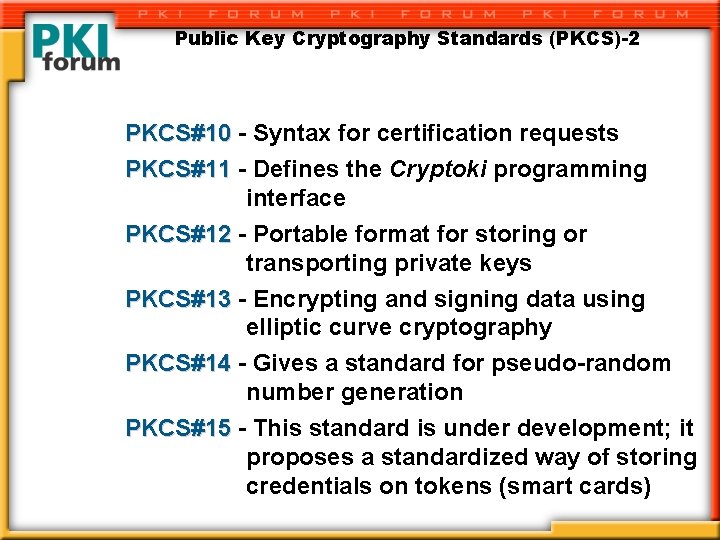
Public Key Cryptography Standards (PKCS)-2 PKCS#10 - Syntax for certification requests PKCS#11 - Defines the Cryptoki programming interface PKCS#12 - Portable format for storing or transporting private keys PKCS#13 - Encrypting and signing data using elliptic curve cryptography PKCS#14 - Gives a standard for pseudo-random number generation PKCS#15 - This standard is under development; it proposes a standardized way of storing credentials on tokens (smart cards)
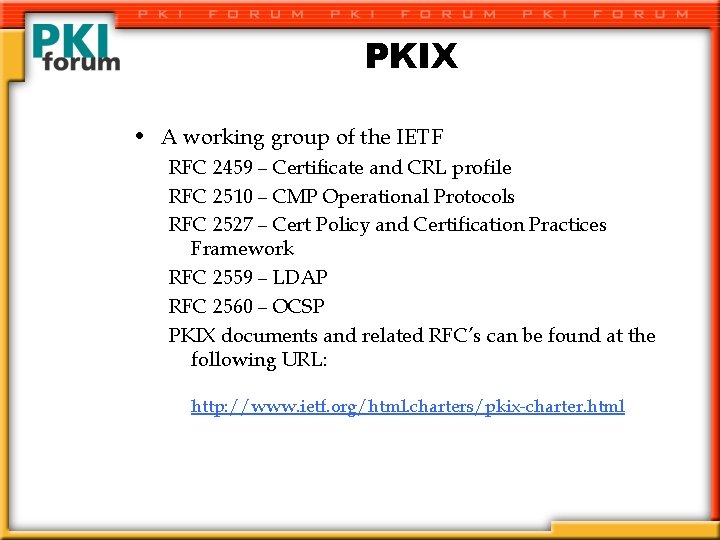
PKIX • A working group of the IETF RFC 2459 – Certificate and CRL profile RFC 2510 – CMP Operational Protocols RFC 2527 – Cert Policy and Certification Practices Framework RFC 2559 – LDAP RFC 2560 – OCSP PKIX documents and related RFC’s can be found at the following URL: http: //www. ietf. org/html. charters/pkix-charter. html
Certification Authority (CA) • An Entity Whose Public Key You Trust • Can be a Trusted Third Party • The CA Issues Credentials – Digital certificates is a form of credential • Types of Digital Certificates – Identity – Attribute • Role • Permission
What is a Registration Authority? • Definition: – “Entity that typically operates locally to collect validated subject information and perform subject/key binding for a certification authority. ’ • Functions: – Validate subjects identity – Generate and submit validated certification request to CA – Provide local certificate life-cycle management support – Optionally supports distribution of certificate to subject
What is a Directory/Repository? • Definition: – “Data structure associated with a Certification Authority(s) which hosts public key certificates for use by PKI population. ” Functions: – Support publication of certificates from CA(s) – Support publication of certificate revocation lists from CA(s) – Service subscriber/relying party requests for cert and CRL info – High availability – application transactional services – Trusted operations, high integrity
Security Policies • Corporate/business practices – General security policies and practices • Security policies and practices – Specific IT security policies • Cryptographic policies and practices – Uses of cryptography for authentication, authorization, signing, nonrepudiation, etc. • Certificates policies and practices – Certification Practices Statement (CPS • Characteristics of policies: – – Pertinent Actionable Enforceable Auditable
Legal Considerations • US: – Electronic Signatures in Global and National Commerce (E-SIGN) – US law, June 2000 • National Conference of Commissioners on Uniform State Laws (NCUSL)—Uniform Commercial Code • Government Paperwork Elimination Act 1998(GPEA) Title XVII of Public Law 105 -2 • EU – EU Directive on Electronic Signature • Directs all member states to establish laws following EU Directive by end of 2001. • Member states previous and current positions on cryptography, privacy and electronic signatures • Asia and Others: In development
Practical Steps for PKI Implementation A PKI solution should consist of: · · · A Security Policy Certificate Practice Statement (CPS) Certificate Authority (CA) Registration Authority (RA) Certificate Distribution System PKI-enabled Applications
Practical Steps for PKI Implementation There are several questions that need to be asked before starting: • What are you using PKI for? · There a rush of people wanting to use PKI · People just don’t understand PKI. . . · Most people who don't fully understand the technology, will not understand why major, complex issues still exist
Practical Steps for PKI Implementation • What goals do you hope to achieve with it? · Focus on defining the business requirements and the value that PKI will add to your business. · One of the largest issues in implementing PKI : It is how PKI affects the business practice and models in use today at their firms.
Practical Steps for PKI Implementation • Does scalability matter to you? · If you are only going to issue a small number of certificates - no problems · If you want to do tens of millions then you need to thoroughly investigate the options · Think about manageability, security and policies issues.
Practical Steps for PKI Implementation Basic Steps for Implementing a Secure Application in an Internet Environment: ·Identify the issues ·Define your requirements - short and longer term! ·Evaluate the security of your current application ·Establish security policies and procedures ·Define your Certification Practice Statement ·Select your security officers and administrators ·PKI-enable your applications ·Integrate your Directory · Set up a Certification Authority · Secure your CA facilities · Run a preliminary test · Launch your solution
Practical Steps for PKI Implementation Areas to think about I) Primary functional components: • Certificate application requests • Identity verification • Certificate issuance • Revocation and renewal • Interfaces • Standards support
Practical Steps for PKI Implementation Areas to think about II) Certificate management support: • Certificate Revocation Lists (CRL) vs Online. Certificate Status Protocol (OCSP) • Key escrow/recovery • Archiving • Logging • Directory services
Practical Steps for PKI Implementation Areas to think about III) Operational considerations: · · · · Availability Performance and capacity Security policies and procedures Insurance and bonding Reporting and alarms Customer service Product service and support Training and documentation · Cross-certification and interoperability
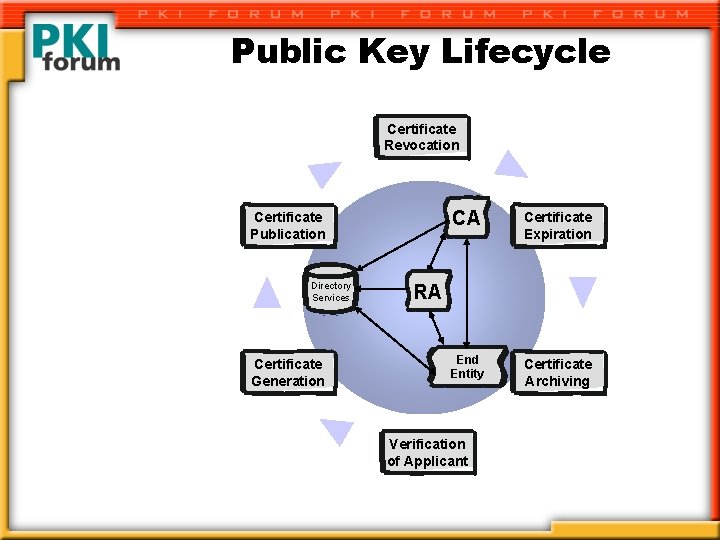
Public Key Lifecycle Certificate Revocation Certificate Publication Directory Services Certificate Generation CA Certificate Expiration End Entity Certificate Archiving RA Verification of Applicant
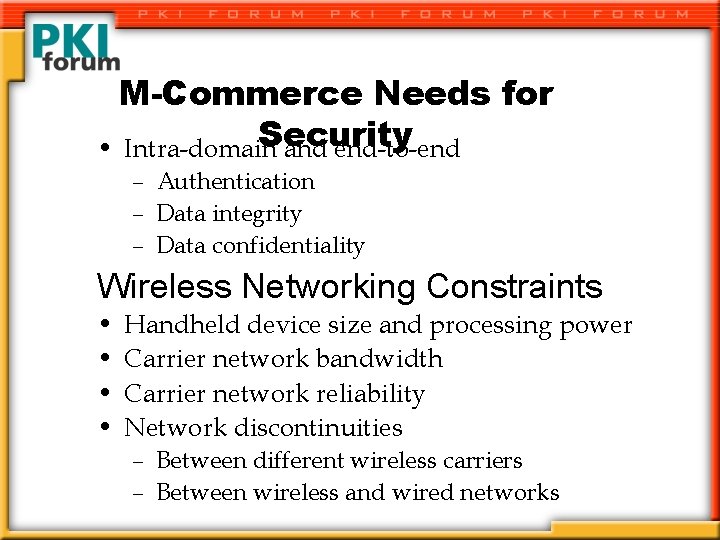
M-Commerce Needs for Security • Intra-domain and end-to-end – Authentication – Data integrity – Data confidentiality Wireless Networking Constraints • • Handheld device size and processing power Carrier network bandwidth Carrier network reliability Network discontinuities – Between different wireless carriers – Between wireless and wired networks
Current Advancements in PKI Philip Berton Director Market Development Baltimore Technologies
Agenda: 1. Who’s Baltimore 2. PKI Uptake: Integral for E/commerce – Catalysts – Example Applications 3. Seamless Security Integration 4. Wireless 5. Advancements – Smartcards & Over The Air Registration – Roaming Enterprise Solutions – Hybrid PKI/Biometric Models – Embedded PKI technology
Baltimore Technologies 1. 2. 3. 4. Global Company based in Dublin Ireland Over 1100 employees in 40 countries FY 2000 revenue $106 M Philosophy: Open protocols, standards based, create a foundation for widespread E/commerce 5. What Baltimore Does: – PKI: Unicert™-- Hardware/Software, Hosting, Consulting – Content Security-- MIME/Sweeper™ product family – Access Control and Authorization -- Select Access™ announced best in class by E-Week
PKI Uptake • “ 98% of Global 2000 Enterprises using PKI by 2003” - Data monitor 1999. • $280 M in 99 and Expected to be $3 B by 2004 • Australian Taxation Office (ATO) – More digital certificates in 6 months than the entire existing certificate industry • Being found in most Industries and applications: Banking, Gov’t, Enterprise, Technology, Communications, Health. Care, B 2 B, etc.
Catalysts • Growing Acceptance (Digital Signature laws) – Analysts & Technologists – Large Scale Business Deployments • Internet • Business Philosophy Shift (share vs. concealment) • Business Opportunities (HIPPA, E-Tax, E-Vote, etc. ) – Revolutionary – Increased Efficiency • Technology (Applications)
Legally Binding Digital Signatures • 50 US States now have enacted laws regarding the scope of digital signatures – http: //www. mbc. com/ecommerce/legis/table 01. ht ml • Germany, Italy, UK, EU and US Governments have enacted legislation Security continues to enable, more sophisticated, more valuable, more channels of electronic commerce
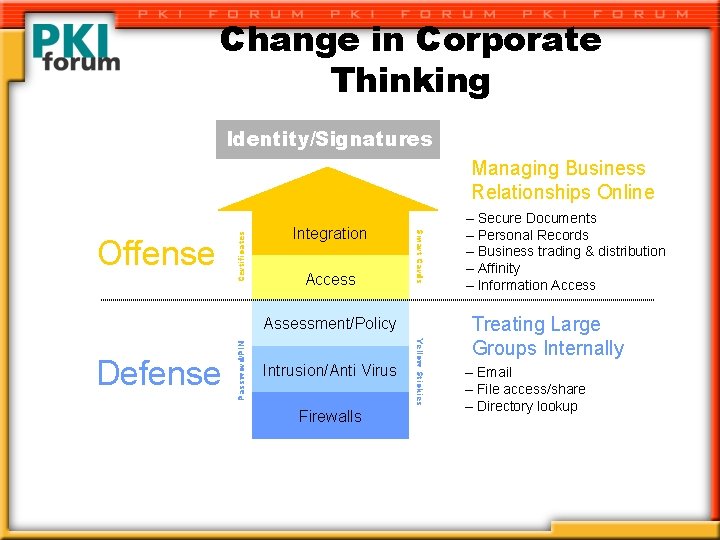
Change in Corporate Thinking Identity/Signatures Integration Access Smart Cards Offense Certificates Managing Business Relationships Online Intrusion/Anti Virus Firewalls Yellow Stickies Defense Password/PIN Assessment/Policy – Secure Documents – Personal Records – Business trading & distribution – Affinity – Information Access Treating Large Groups Internally – Email – File access/share – Directory lookup
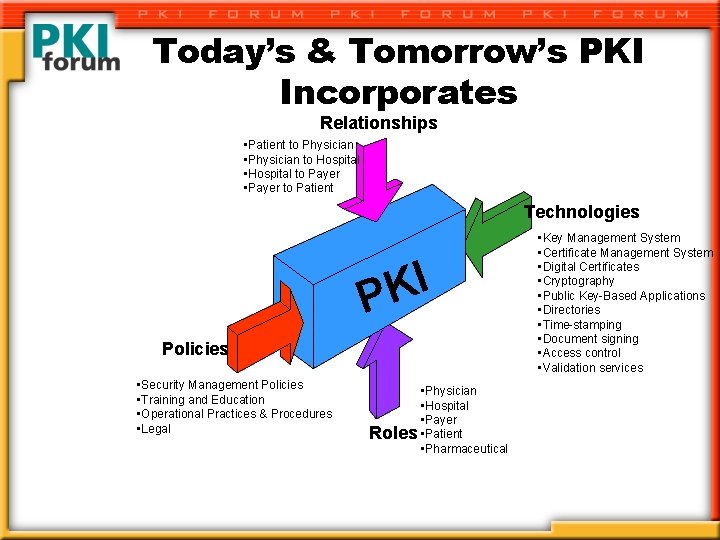
Today’s & Tomorrow’s PKI Incorporates Relationships • Patient to Physician • Physician to Hospital • Hospital to Payer • Payer to Patient Technologies I K P Policies • Security Management Policies • Training and Education • Operational Practices & Procedures • Legal • Physician • Hospital • Payer Roles • Patient • Pharmaceutical • Key Management System • Certificate Management System • Digital Certificates • Cryptography • Public Key-Based Applications • Directories • Time-stamping • Document signing • Access control • Validation services
PKI Enabling Developer tools used to enable and create all kinds of Applications. – – – XML (sign or verify) SSL (secure http, ftp, telnet) IP/Sec (VPN) WAP (authenticating and digital signing) S/MIME (email, EDI, legacy systems, storage) Java • PKI enabled E/commerce w/o client via applets
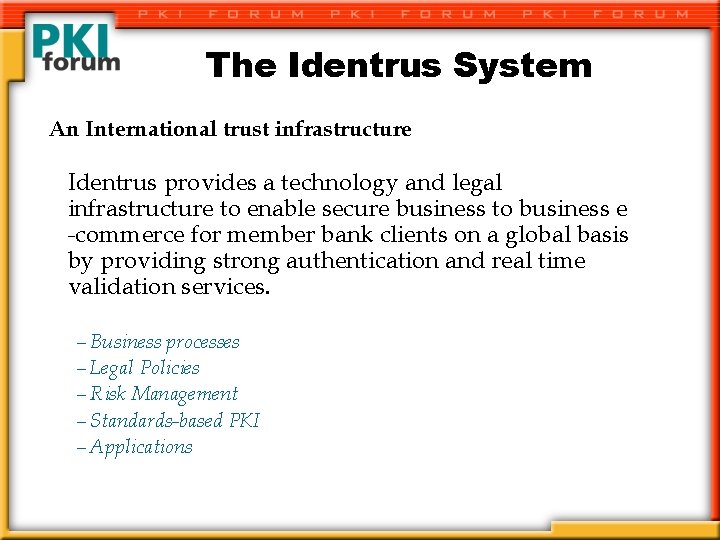
The Identrus System An International trust infrastructure Identrus provides a technology and legal infrastructure to enable secure business to business e -commerce for member bank clients on a global basis by providing strong authentication and real time validation services. – Business processes – Legal Policies – Risk Management – Standards-based PKI – Applications

Business Applications Electronic Commerce © © © Online Auction Markets Electronic Content Delivery Insurance Sales & Contract Securities Trading Government Filings, Procurement, etc. Financial Services © © © ACH Payments Corporate Purchasing International Trade Letter of Credit Bill Presentation Statement Delivery Identrus Certificate 7
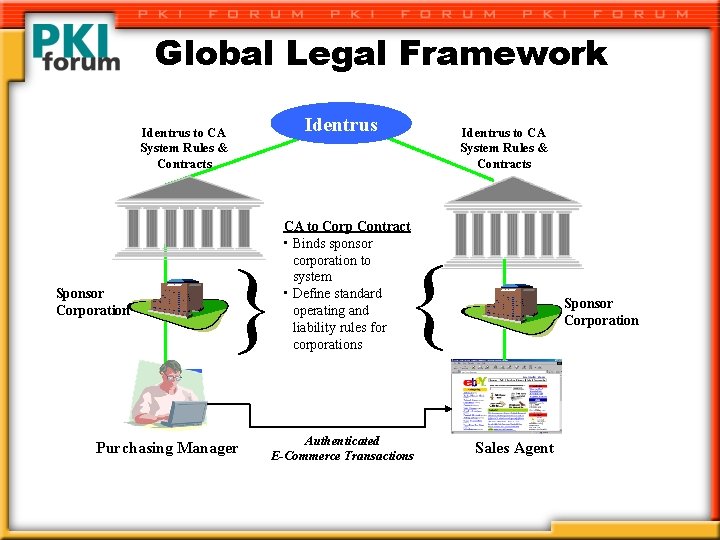
Global Legal Framework Identrus to CA System Rules & Contracts Purchasing Mgr. 2 { Sponsor Corporation Purchasing Manager Identrus to CA System Rules & Contracts CA to Corp Contract • Binds sponsor corporation to system • Define standard operating and liability rules for corporations { Authenticated E-Commerce Transactions Sponsor Corporation Sales Agent 2 Sales Agent
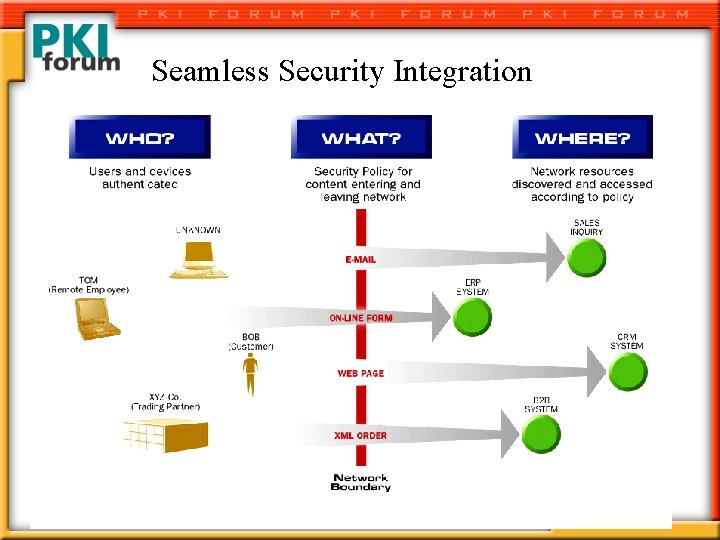
Seamless Security Integration
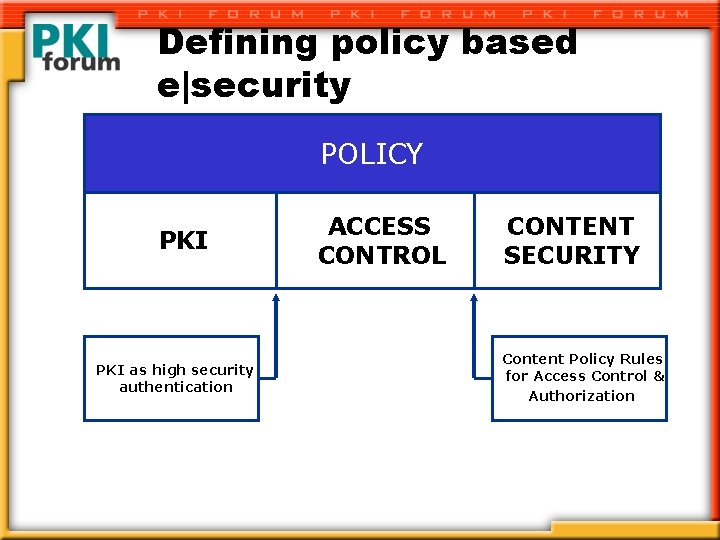
Defining policy based e|security POLICY PKI as high security authentication ACCESS CONTROL CONTENT SECURITY Content Policy Rules for Access Control & Authorization
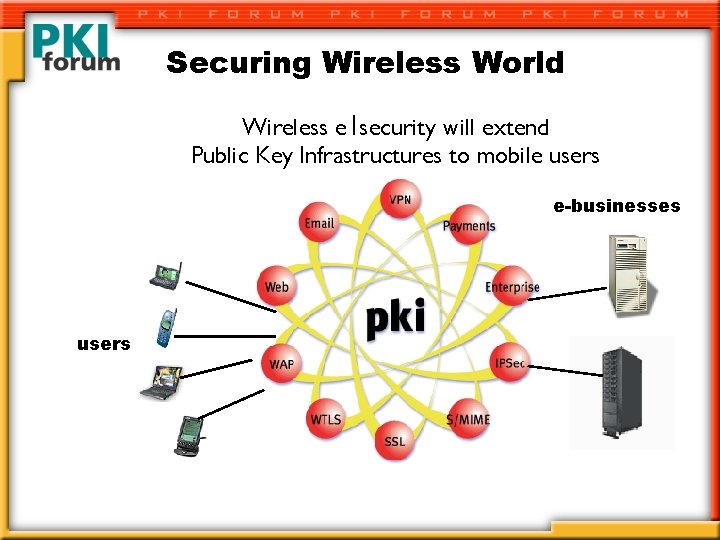
Securing Wireless World Wireless e|security will extend Public Key Infrastructures to mobile users e-businesses users
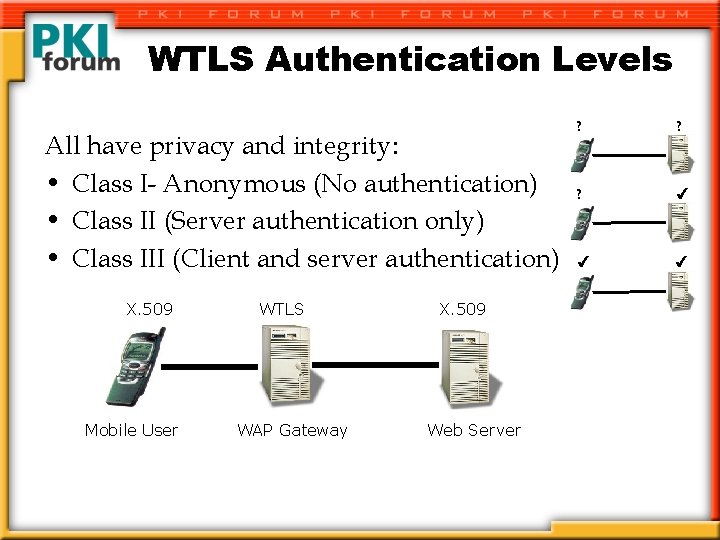
WTLS Authentication Levels All have privacy and integrity: • Class I- Anonymous (No authentication) • Class II (Server authentication only) • Class III (Client and server authentication) X. 509 Mobile User WTLS WAP Gateway X. 509 Web Server ? ? ?
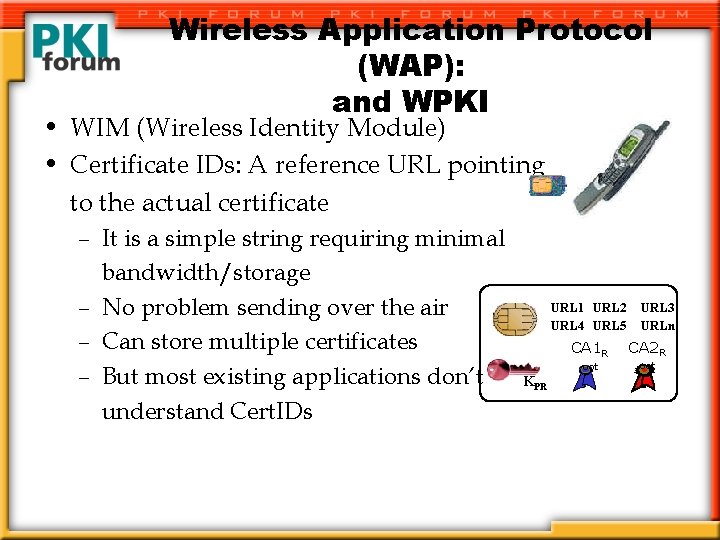
Wireless Application Protocol (WAP): and WPKI • WIM (Wireless Identity Module) • Certificate IDs: A reference URL pointing to the actual certificate – It is a simple string requiring minimal bandwidth/storage – No problem sending over the air – Can store multiple certificates – But most existing applications don’t understand Cert. IDs URL 1 URL 2 URL 4 URL 5 KPR URL 3 URLn CA 1 R CA 2 R oot
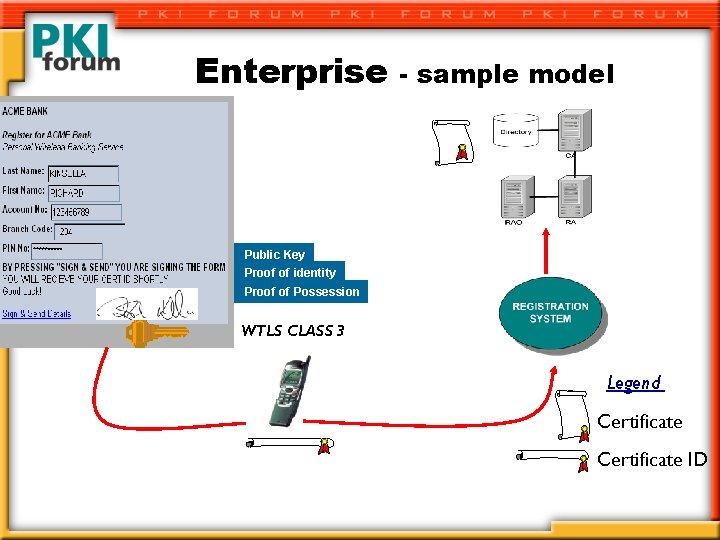
Enterprise - sample model Public Key Proof of identity Proof of Possession WTLS CLASS 3 Legend Certificate ID
PDA Market Forecasts “Within 2 -3 years 20 -25% of corporate knowledge workers will obtain a companion computing device (e. g. , PDA). . . ” - META Group Feb, 2000 “Almost a quarter of desktop management spending in 2003 will be allocated to the control of mobile and remote PCs and other handheld devices within the enterprise. . . ” - IDC 9/01/99 “Researchers predict global sales of hand-held computers hitting $7. 2 B in 2003, with unit sales increasing to 32. 5 M from the current 8. 2 M…” - Wall Street Journal April, 2000
Embedded PKI • Devices (phones, PDAs, appliances, satellites, cars, network devices, cable modems, etc. – Increasing Intelligence in these devices – Looking to include basic crypto and security functions like PKI which continues to build the foundation. • TCPA (Trusted Computing Platform Alliance) – Looking to complement standards such as VPN, IKE, PKI, SSL, IPSec, S/MIME, etc. by creating basic security functions into platform hardware, BIOS, system and operating software. • Moore’s Law For Another Decade– “Speed Doubles Every 18 Months”
Smart. Cards & PKI Expand the boundaries of what you can do – – – Bulk and Over the Air Registration Multiple factor authentication Increased Security (secure device) Feasibly integrated into any application with readers Allows for mobility– a personal take it with you device – Makes a roaming solution for Enterprise Road. Warriors obsolete– the use of kiosks, public or 3 rd party devices.
Hybrid Models– PKI/Biometrics • Biometrics identifying something unique to the individual; finger print, iris, retina, hand geometry, voice, handwriting, etc. • Biometrics being used in authentication into physical areas, onto networks, and onto personal/work devices. • Many Biometric (Service Providers) companies are looking to have PKI back-ends and use biometrics for 2 nd/3 rd factor authentication. Device or Server Centric. • There are issues in having the biometric data being communicated and compatible with PKI standards.
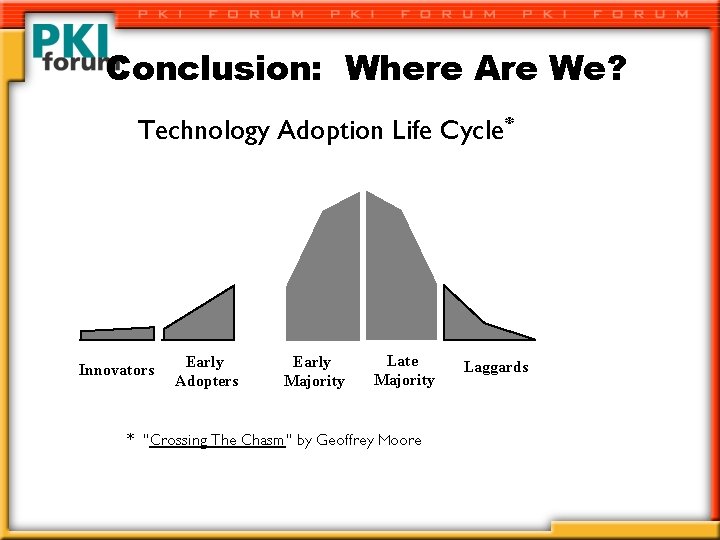
Conclusion: Where Are We? Technology Adoption Life Cycle* Innovators Early Adopters Early Majority Late Majority * “Crossing The Chasm” by Geoffrey Moore Laggards
Conclusion: The critical question-- What Needs to Happen for True “PKI enabled” E/Commerce? 1. The continued convergence of technologies in communications, affiliated technologies and simple useful applications to make security easy– “invisible. ” 2. Continued proof of efficiencies associated with the technology and the digital revolution.

Additional Information Website: www. pkiforum. org Email: info@pkiforum. org Phone: 781 -876 -8810
- Slides: 69