PKI Deployment and Application Issues A Public Key
PKI— Deployment and Application Issues A Public Key Infrastructure for Advanced Network Technologies Workshop April 27– 28, 2000, NIST James A. Rome Executive Secretary, IST Center for Information Infrastructure Technology DOE Y 12, Advanced Technology Directorate Oak Ridge, Tennessee 37830 -8027 (865) 574 -1306 jar@y 12. doe. gov http: //www. ornl. gov/~jar
Center for Information Infrastructure Technology Authorization is what counts PKI can provide strong authentication, but only the owners of resources can authorize their use l How do you use certificates in the authorization process? l Do you know which John Smith it is? l Can you guarantee that stakeholder rights are enforced? l Is their an audit trail for legal action in case of criminal activity? l Who determines and maintains the security policies? 2 9/25/2020
Center for Information Infrastructure Technology Web applications are “easy” l Server certificates allow w Encrypted data via SSL w “Assurance” of the server ID l Client certificates allow w Strong client authentication w S/Mime encrypted and/or signed e-mail l Object signing certificates allow w Assurance of Java applets, plug-ins, trusted code l COTS certificate issuance and management http: //mmc. ciit. y 12. doe. gov/jar/MMCCerts. html 3 9/25/2020
Center for Information Infrastructure Technology Client certificates stored in browsers l Hard to use on someone else’s computer (you cannot put the certificate on a floppy disk and use it directly) l Only the latest browsers can manage certificates l It is very difficult to create Web applications that can access the client certificate DN directly, so that you can use it to implement policy decisions w The usual APIs expect access via LDAP servers l It is almost impossible to allow a user to access his private key outside of the browser 4 9/25/2020
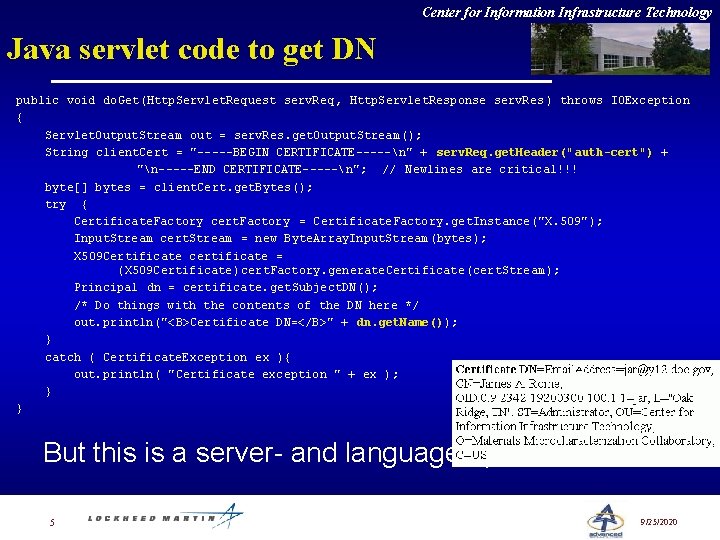
Center for Information Infrastructure Technology Java servlet code to get DN public void do. Get(Http. Servlet. Request serv. Req , Http. Servlet. Response serv. Res ) throws IOException { Servlet. Output. Stream out = serv. Res. get. Output. Stream(); String client. Cert = "-----BEGIN CERTIFICATE-----n" + serv. Req. get. Header("auth-cert") + "n-----END CERTIFICATE-----n"; // Newlines are critical!!! byte[] bytes = client. Cert. get. Bytes(); try { Certificate. Factory cert. Factory = Certificate. Factory. get. Instance("X. 509"); Input. Stream cert. Stream = new Byte. Array. Input. Stream(bytes); X 509 Certificate certificate = (X 509 Certificate)cert. Factory. generate. Certificate(cert. Stream); Principal dn = certificate. get. Subject. DN(); /* Do things with the contents of the DN here */ out. println("<B>Certificate DN=</B>" + dn. get. Name()); } catch ( Certificate. Exception ex ){ out. println( "Certificate exception " + ex ); } } But this is a server- and language-specific solution 5 9/25/2020
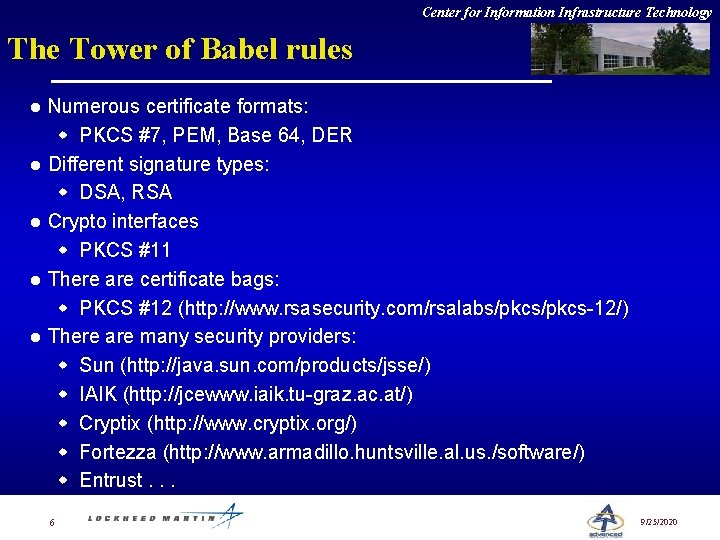
Center for Information Infrastructure Technology The Tower of Babel rules l l l Numerous certificate formats: w PKCS #7, PEM, Base 64, DER Different signature types: w DSA, RSA Crypto interfaces w PKCS #11 There are certificate bags: w PKCS #12 (http: //www. rsasecurity. com/rsalabs/pkcs-12/) There are many security providers: w Sun (http: //java. sun. com/products/jsse/) w IAIK (http: //jcewww. iaik. tu-graz. ac. at/) w Cryptix (http: //www. cryptix. org/) w Fortezza (http: //www. armadillo. huntsville. al. us. /software/) w Entrust. . . 6 9/25/2020
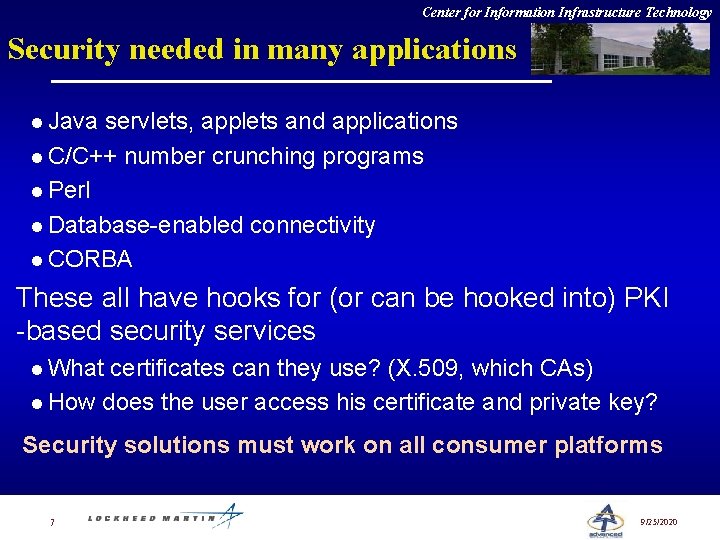
Center for Information Infrastructure Technology Security needed in many applications l Java servlets, applets and applications l C/C++ number crunching programs l Perl l Database-enabled connectivity l CORBA These all have hooks for (or can be hooked into) PKI -based security services l What certificates can they use? (X. 509, which CAs) l How does the user access his certificate and private key? Security solutions must work on all consumer platforms 7 9/25/2020
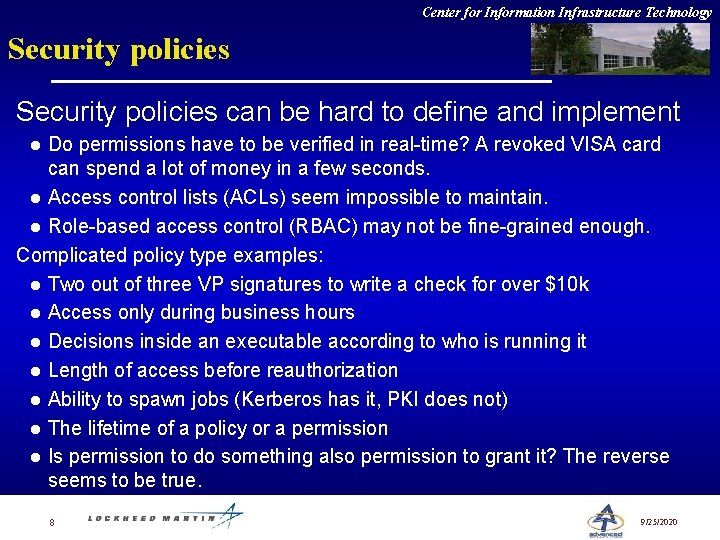
Center for Information Infrastructure Technology Security policies can be hard to define and implement Do permissions have to be verified in real-time? A revoked VISA card can spend a lot of money in a few seconds. l Access control lists (ACLs) seem impossible to maintain. l Role-based access control (RBAC) may not be fine-grained enough. Complicated policy type examples: l Two out of three VP signatures to write a check for over $10 k l Access only during business hours l Decisions inside an executable according to who is running it l Length of access before reauthorization l Ability to spawn jobs (Kerberos has it, PKI does not) l The lifetime of a policy or a permission l Is permission to do something also permission to grant it? The reverse seems to be true. l 8 9/25/2020
Center for Information Infrastructure Technology Stakeholder rights enforcement l We must obey regulations imposed by government, universities, companies w Sometimes we have to prove it! l Who owns the information and resources? l Who is responsible for maintaining these requirements and permissions? The standard Unix r, w, x permissions for owner, group, and world are too simplistic to express these constraints. ACLs are unmaintainable. 9 9/25/2020
Center for Information Infrastructure Technology Secure authorization l For simple applications, strong authentication of the user might suffice. l But in real life, various stakeholders have control over access to resources and data. w Access can only be allowed after approval by each stakeholder l The Akenti access control system (William Johnston — LBNL, NASA Ames) can solve this need. http: //www-itg. lbl. gov/security/Akenti/ 10 9/25/2020
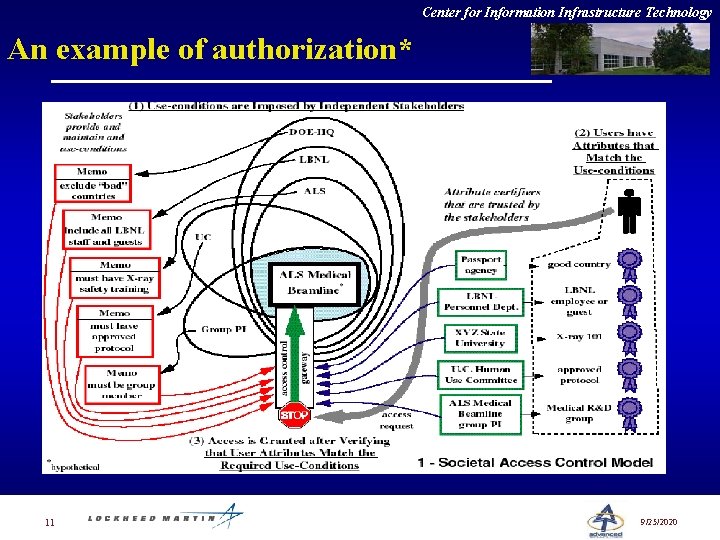
Center for Information Infrastructure Technology An example of authorization* 11 9/25/2020
Center for Information Infrastructure Technology Authorization in “real life” l Probably, the user is given one document attesting to his satisfaction of requirements. E. g. , DOE badge allows entrance to facility. l The access control enforcer — a door guard, the experiment PI, etc. — validates the capability (e. g. , checks the badge) when access is requested. Akenti implements this model in cyberspace. 12 9/25/2020
Center for Information Infrastructure Technology Akenti reflects current practice l Stakeholders independently make assertions about resource use l Trusted third-parties certify user attributes required for the use conditions l Authenticated users that posses the required attributes easily gain access More details available at: http: //www-itg. lbl. gov/security/Akenti 13 9/25/2020
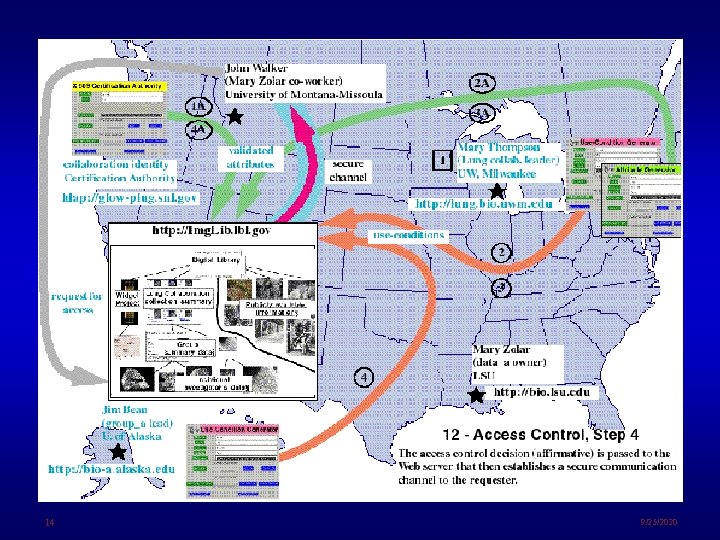
14 9/25/2020
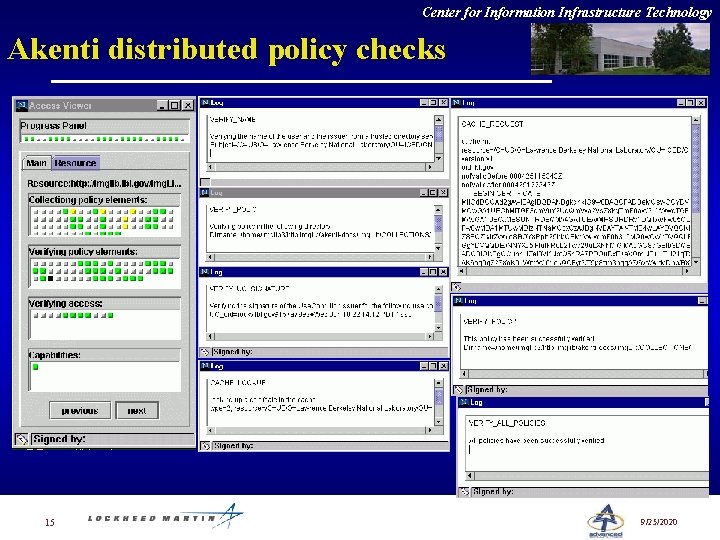
Center for Information Infrastructure Technology Akenti distributed policy checks 15 9/25/2020
Center for Information Infrastructure Technology Certificate requirements l Fast access to certificate servers w Certificates must be checked l Policy engines must check authorization l Reliability. If the servers are not up, the user is denied access. l What happens on a laptop with no networking? There can a significant amount of overhead to set up a circuit for a short transaction. 16 9/25/2020
Center for Information Infrastructure Technology Akenti summary Certificates can be used to express and enforce complicated and flexible security policies. l X. 509 identity certificates authorization l User attribute certificate l Use-condition certificates Akenti is just now in pilot phase. More details are available from William (Bill) Johnston 17 johnston@george. lbl. gov 9/25/2020
Center for Information Infrastructure Technology Good News: Things are changing Tools are just being made available to use certificates in end-user applications l Java JSSE (security extensions) toolkit (9/99) l Entrust toolkits are now free. l Enhydra (www. enhydra. org) open source servlet toolkit (even includes a Web server!) l Borland’s JBuilder 3. 5 is available for free l Akenti (DOE-developed distributed authorization) l Mozilla security tools (with source code) (http: //www. mozilla. org/projects/security/pki/nss/tools/) l JRun servlet environment (http: //www. allaire. com) 18 9/25/2020
- Slides: 18