PKCS 14 Status of Work Pseudo Random Number
PKCS #14 Status of Work Pseudo Random Number Generation Jan-Ove Larsson RSA Laboratories Europe jlarsson@rsasecurity. com PKCS Workshop ’ 99 Sep 29 - Oct 1 Stockholm, Sweden
Outline • Motivation for PRNG Standard • Design Criteria • Building Blocks • Set of Operations for PRNG • Model for PRNG • Basic Security Properties • Attacks on PRNG: s • Algo Proposals
Motivation for PRNG Standard • Increases Security • Complements Other Standards • Support to Developers - strength, correctness via testvectors • Legal Aspects - liability in cases of fraud • Public Trust - home-banking - e-commerce - other services
Design Criteria • Build On - proven security properties if possible - well-studied algorithms and primitives • Be Conservative • Promote Simplicity - better performance, easier to analyse
Building Blocks In Accordance With Our Design Criteria We Build the PRNG Using Well-Studied Algorithms and Primitives. There Are Several Possibilities Including: • Block Ciphers - CBCMAC: s • Stream Ciphers • Modular Exponentiation Based • Cryptographic Hash Functions - HMAC: s - NMAC: s
Set of Operations for PRNG • State Update from New Seed • State Advance after Output Generation • Output Generation • Save / Restore State • Self-Test ?
![Model for PRNG I X[ ] H F S G Y[ ] Variables: I, Model for PRNG I X[ ] H F S G Y[ ] Variables: I,](http://slidetodoc.com/presentation_image_h2/c2189614a877206ebfc08ccc38c6a36d/image-7.jpg)
Model for PRNG I X[ ] H F S G Y[ ] Variables: I, Input to Seed Array X[ ], Array of Blocks of Seed Bytes Y[ ], Array of Output Bytes S, Internal State Functions: H, State Update From Seed F, State Advance After Output G, Generation of Output Bytes
Basic Security Properties • Use Large Seed Blocks • Knowledge of Part of Seed Shall Be of No Help For an Adversary • Good Seed Usage: Make the State Depend on All Previous Seed • Large, Unbiased Internal State • Output Shall Pass Randomness Tests • Output Shall Be Unpredictable
![Attacks on PRNG: s 1 • Guessing of Seed - Entropy of X[i] Need Attacks on PRNG: s 1 • Guessing of Seed - Entropy of X[i] Need](http://slidetodoc.com/presentation_image_h2/c2189614a877206ebfc08ccc38c6a36d/image-9.jpg)
Attacks on PRNG: s 1 • Guessing of Seed - Entropy of X[i] Need to Be Large to Prevent an Exhaustive Search Attack. • Chosen Seed Input / State Cycle Shortening X[ i ] Old State H New State
Attacks on PRNG: s • Timing Attacks on State Advance Function - Ensure That the Advance Function Takes Constant Time. - If That Is Not Possible, Random Delays? Gives Worse Performance! 2
Attacks on PRNG: s • Direct Cryptanalytic Attacks on Output Generation Function - Strong Cipher or Preimage Resistant Hash - Truncate Output From Output Generation Function 3
Attacks on PRNG: s Attacks After a Compromise of State • Backward Tracking Attack: After a Compromise of State, Try to Determine Previous Outputs. • Forward Tracking 4
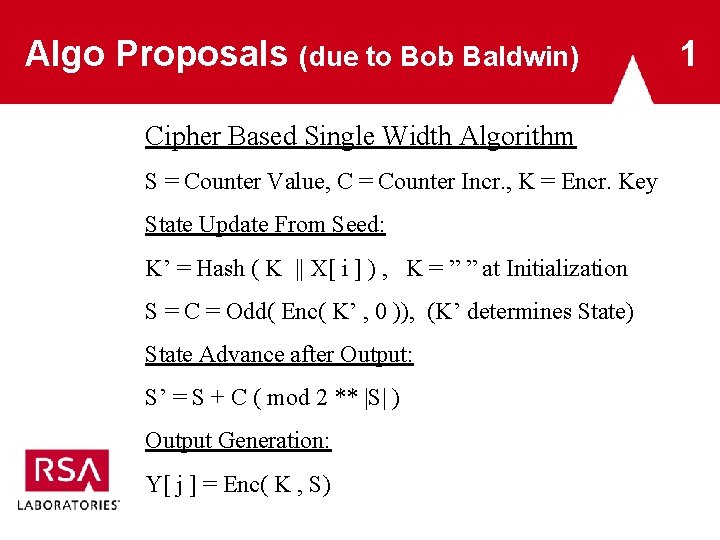
Algo Proposals (due to Bob Baldwin) Cipher Based Single Width Algorithm S = Counter Value, C = Counter Incr. , K = Encr. Key State Update From Seed: K’ = Hash ( K || X[ i ] ) , K = ” ” at Initialization S = C = Odd( Enc( K’ , 0 )), (K’ determines State) State Advance after Output: S’ = S + C ( mod 2 ** |S| ) Output Generation: Y[ j ] = Enc( K , S) 1
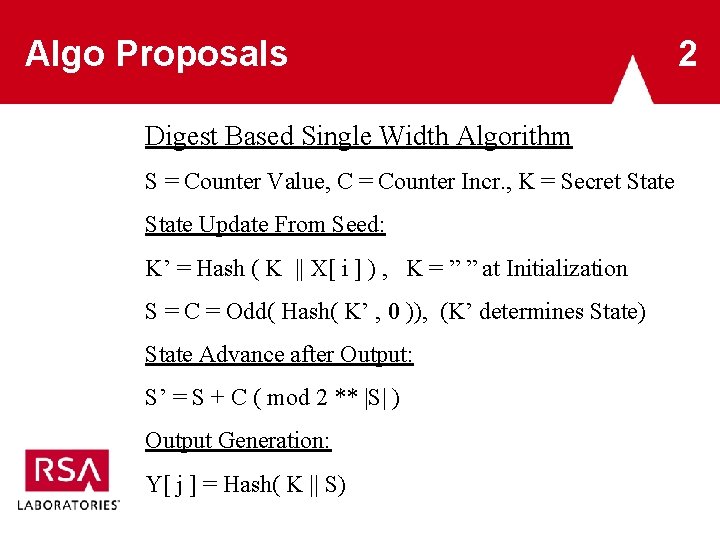
Algo Proposals Digest Based Single Width Algorithm S = Counter Value, C = Counter Incr. , K = Secret State Update From Seed: K’ = Hash ( K || X[ i ] ) , K = ” ” at Initialization S = C = Odd( Hash( K’ , 0 )), (K’ determines State) State Advance after Output: S’ = S + C ( mod 2 ** |S| ) Output Generation: Y[ j ] = Hash( K || S) 2
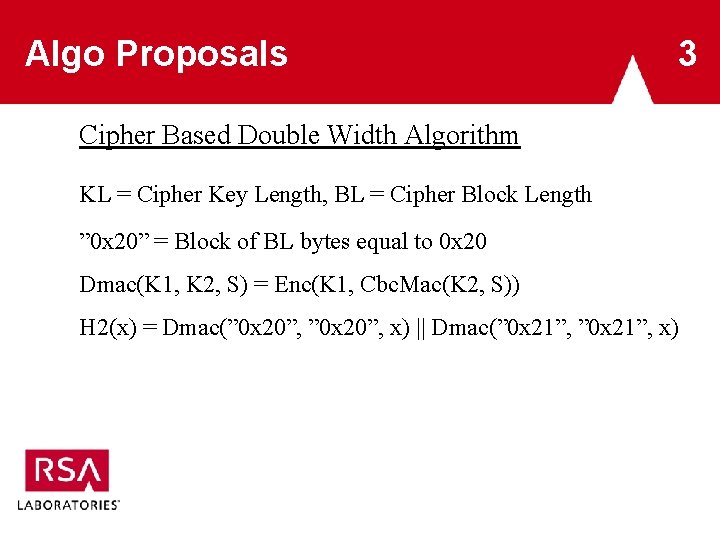
Algo Proposals 3 Cipher Based Double Width Algorithm KL = Cipher Key Length, BL = Cipher Block Length ” 0 x 20” = Block of BL bytes equal to 0 x 20 Dmac(K 1, K 2, S) = Enc(K 1, Cbc. Mac(K 2, S)) H 2(x) = Dmac(” 0 x 20”, x) || Dmac(” 0 x 21”, x)
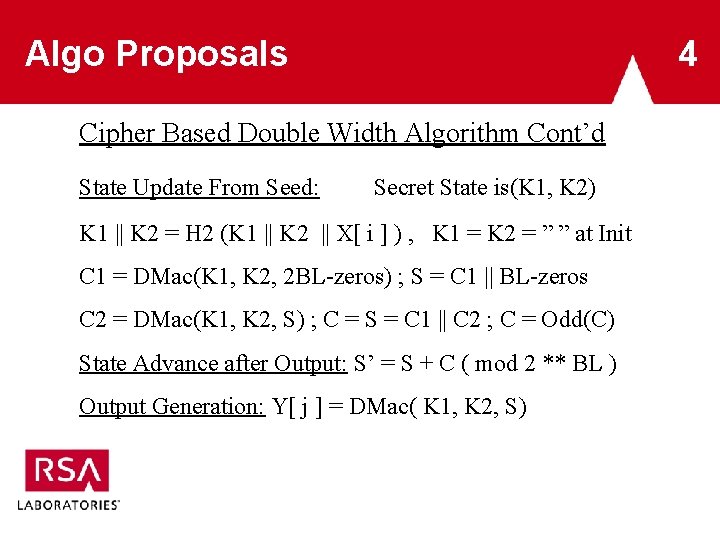
Algo Proposals 4 Cipher Based Double Width Algorithm Cont’d State Update From Seed: Secret State is(K 1, K 2) K 1 || K 2 = H 2 (K 1 || K 2 || X[ i ] ) , K 1 = K 2 = ” ” at Init C 1 = DMac(K 1, K 2, 2 BL-zeros) ; S = C 1 || BL-zeros C 2 = DMac(K 1, K 2, S) ; C = S = C 1 || C 2 ; C = Odd(C) State Advance after Output: S’ = S + C ( mod 2 ** BL ) Output Generation: Y[ j ] = DMac( K 1, K 2, S)
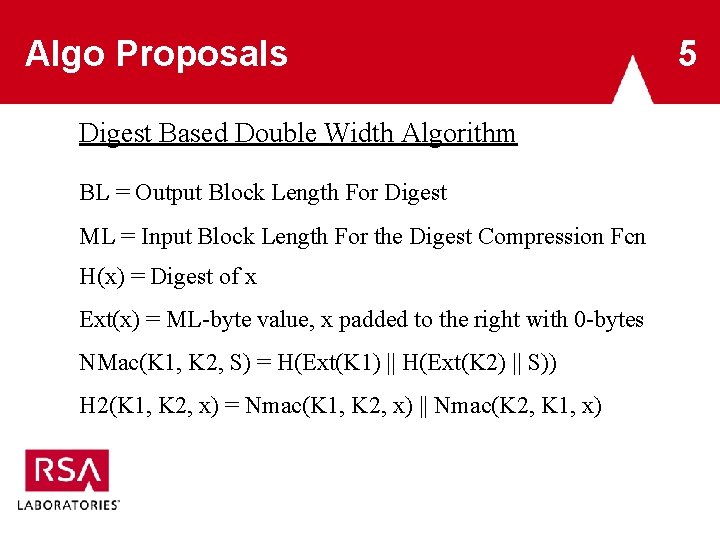
Algo Proposals Digest Based Double Width Algorithm BL = Output Block Length For Digest ML = Input Block Length For the Digest Compression Fcn H(x) = Digest of x Ext(x) = ML-byte value, x padded to the right with 0 -bytes NMac(K 1, K 2, S) = H(Ext(K 1) || H(Ext(K 2) || S)) H 2(K 1, K 2, x) = Nmac(K 1, K 2, x) || Nmac(K 2, K 1, x) 5
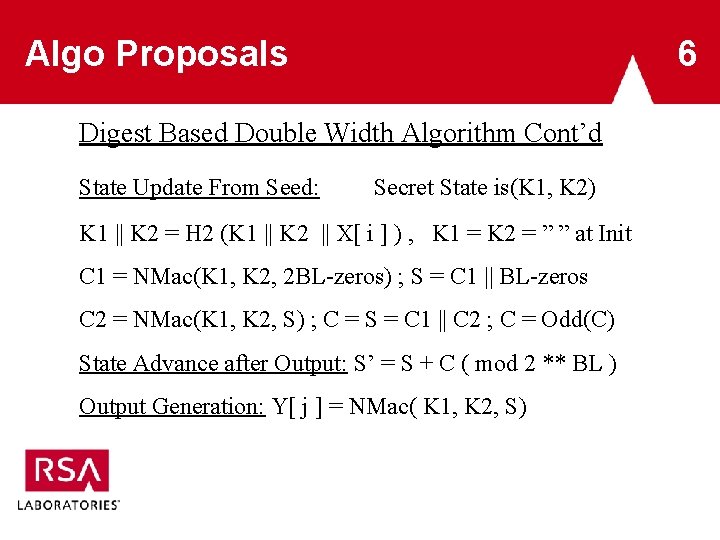
Algo Proposals 6 Digest Based Double Width Algorithm Cont’d State Update From Seed: Secret State is(K 1, K 2) K 1 || K 2 = H 2 (K 1 || K 2 || X[ i ] ) , K 1 = K 2 = ” ” at Init C 1 = NMac(K 1, K 2, 2 BL-zeros) ; S = C 1 || BL-zeros C 2 = NMac(K 1, K 2, S) ; C = S = C 1 || C 2 ; C = Odd(C) State Advance after Output: S’ = S + C ( mod 2 ** BL ) Output Generation: Y[ j ] = NMac( K 1, K 2, S)
- Slides: 18