PIPELINE QRA SEMINAR PIPELINE RISK ASSESSMENT INTRODUCTION TO






- Slides: 34

PIPELINE QRA SEMINAR
PIPELINE RISK ASSESSMENT INTRODUCTION TO RISK IDENTIFICATION 2
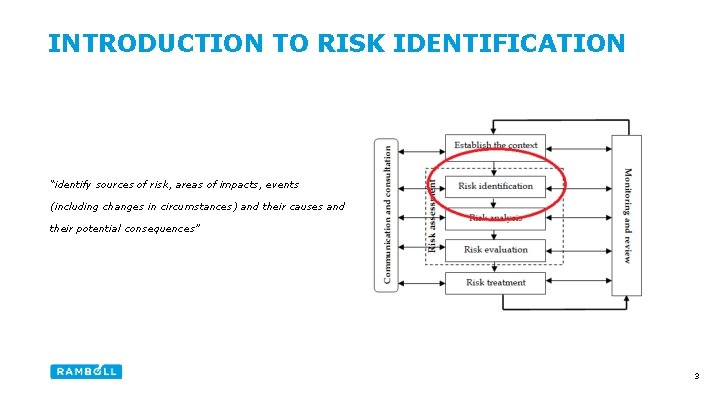
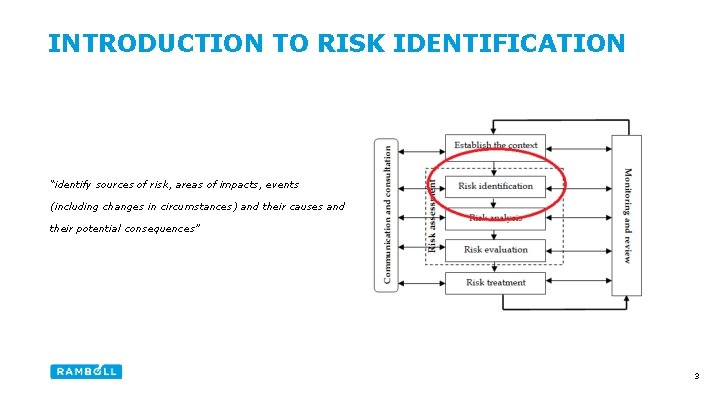
INTRODUCTION TO RISK IDENTIFICATION “identify sources of risk, areas of impacts, events (including changes in circumstances) and their causes and their potential consequences” 3
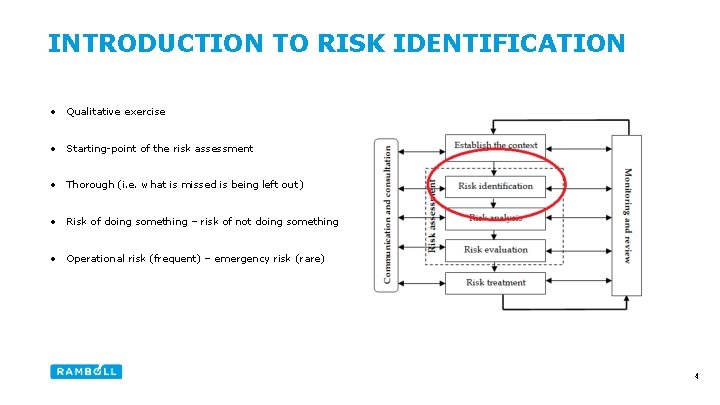
INTRODUCTION TO RISK IDENTIFICATION • Qualitative exercise • Starting-point of the risk assessment • Thorough (i. e. what is missed is being left out ) • Risk of doing something – risk of not doing something • Operational risk (frequent) – emergency risk (rare) 4
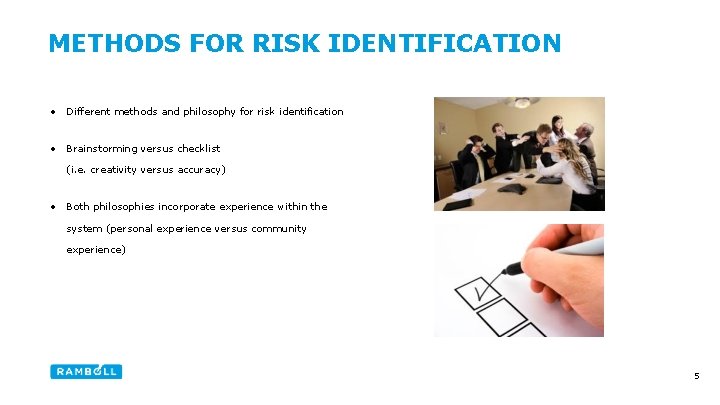
METHODS FOR RISK IDENTIFICATION • Different methods and philosophy for risk identification • Brainstorming versus checklist (i. e. creativity versus accuracy) • Both philosophies incorporate experience within the system (personal experience versus community experience) 5
METHODS FOR RISK IDENTIFICATION Advantages of checklist • Simple (understanding and execution) • Cover the most and/or major (consistent and practical) Disadvantages of checklist • Unspecific (not capturing project specific) 6
METHODS FOR RISK IDENTIFICATION Advantages of brainstorming • Specific (capturing project specific – outside the box) • Lessons learned (from previous projects) Disadvantages of brainstorming • Subjective (based on input from participants) • Approach (discussion on other concerns than risk) 7
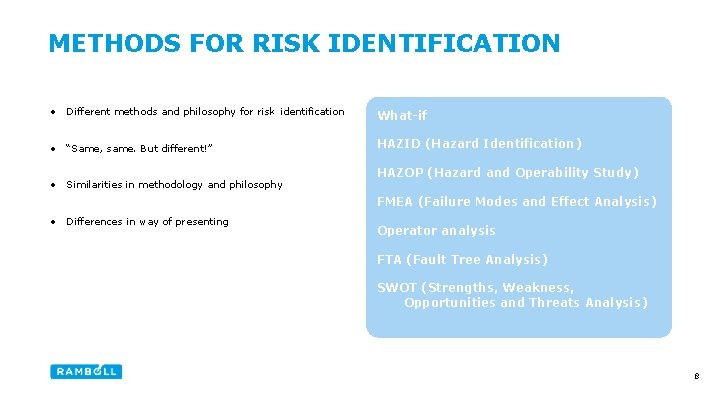
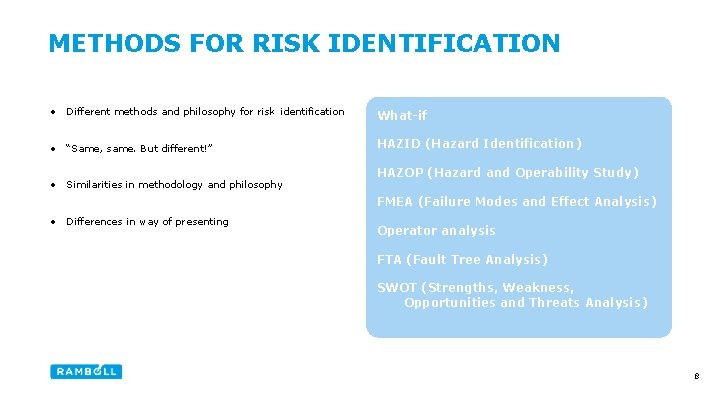
METHODS FOR RISK IDENTIFICATION • Different methods and philosophy for risk identification What-if • “Same, same. But different!” HAZID (Hazard Identification) • Similarities in methodology and philosophy HAZOP (Hazard and Operability Study) FMEA (Failure Modes and Effect Analysis) • Differences in way of presenting Operator analysis FTA (Fault Tree Analysis) SWOT (Strengths, Weakness, Opportunities and Threats Analysis) 8
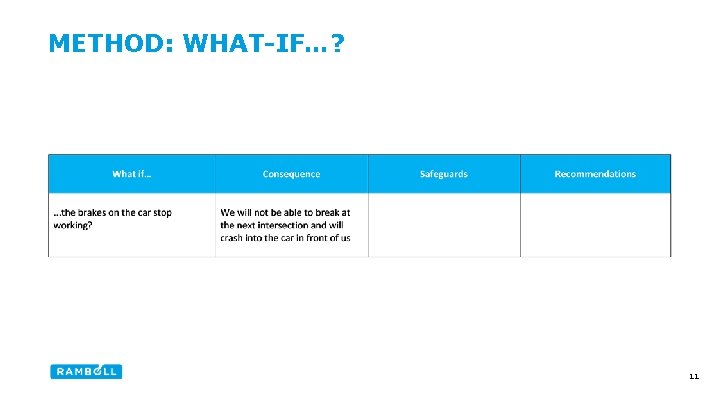
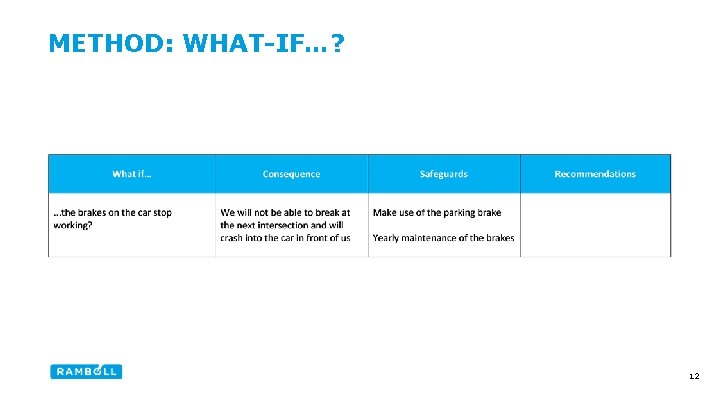
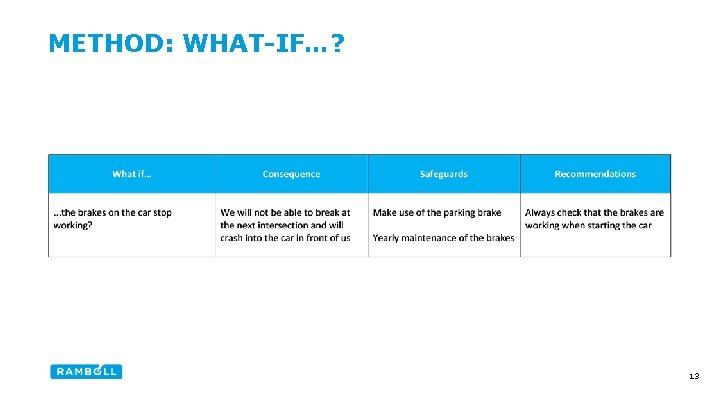
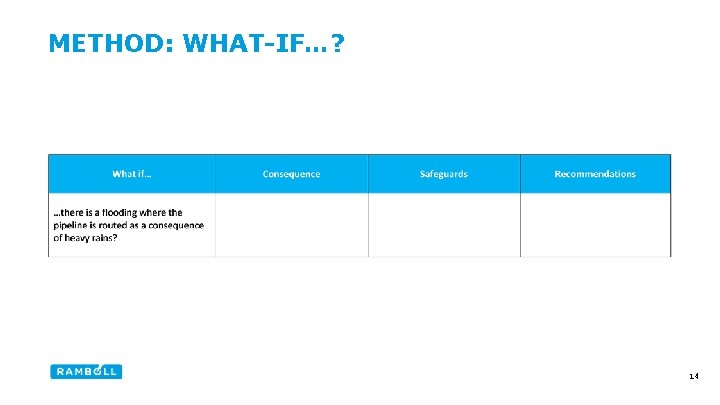
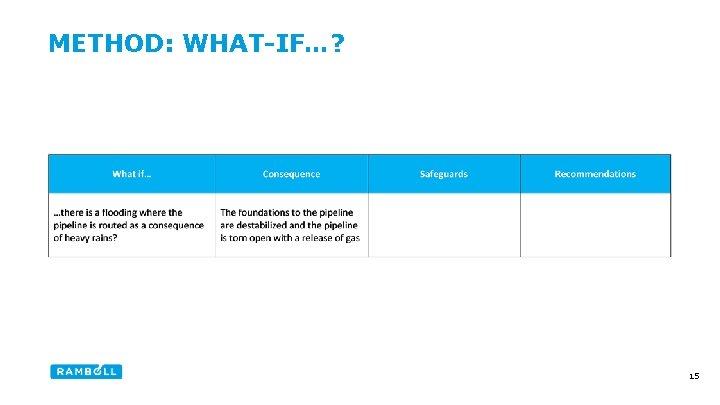
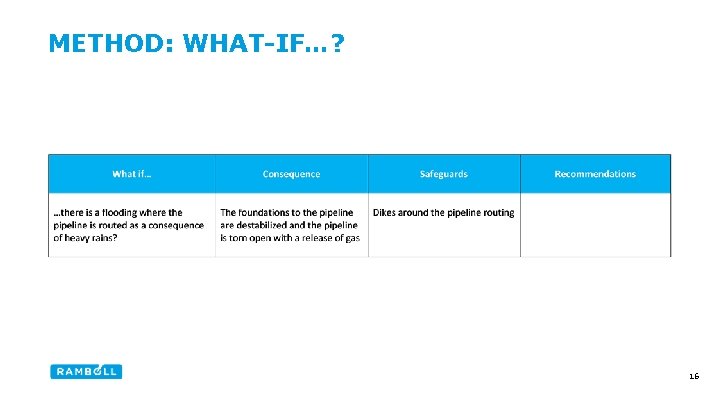
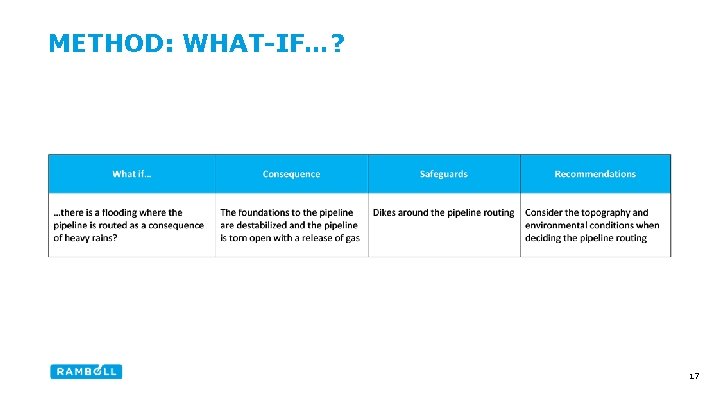
METHOD: WHAT-IF…? • Based on the question: what if…? • Primarily - brainstorming • Capturing deviation from the normal • Often used when analysing changes made • Focus on consequence (and avoiding the consequence) rather than focus on the actual cause 9

METHOD: WHAT-IF…? 10
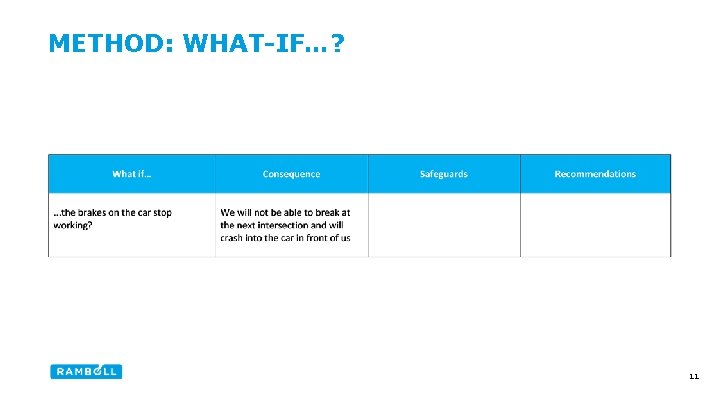
METHOD: WHAT-IF…? 11
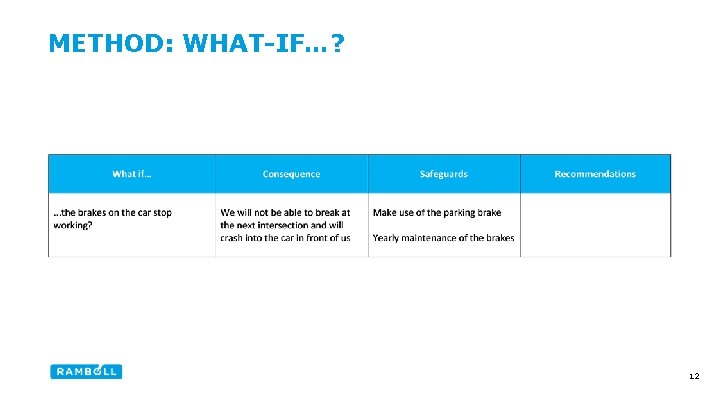
METHOD: WHAT-IF…? 12
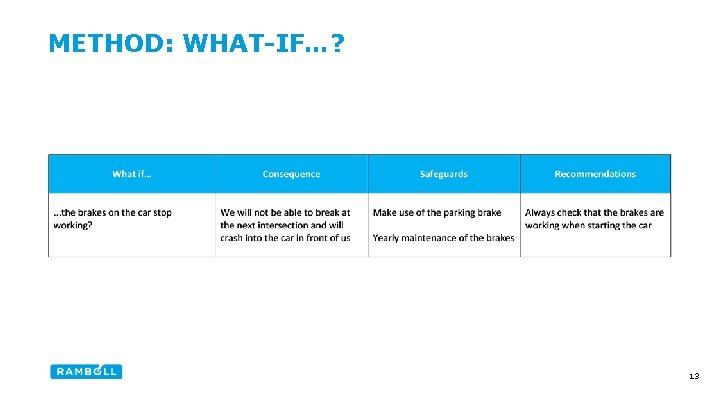
METHOD: WHAT-IF…? 13
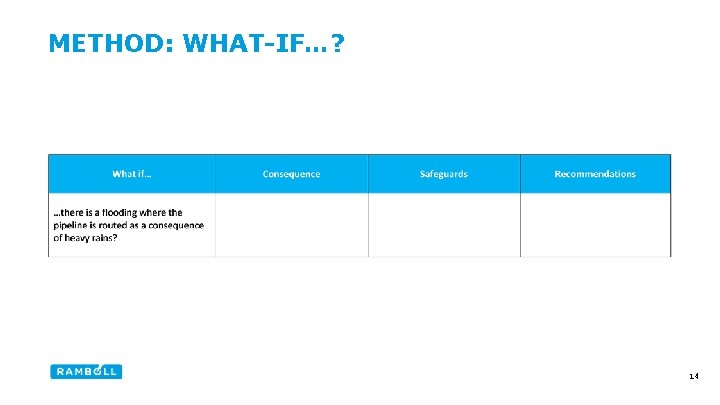
METHOD: WHAT-IF…? 14
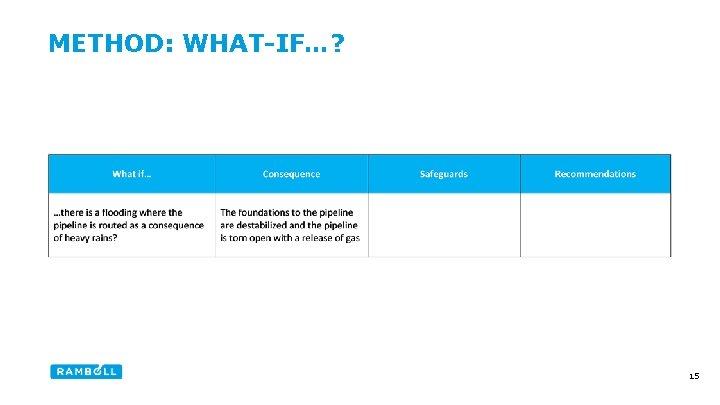
METHOD: WHAT-IF…? 15
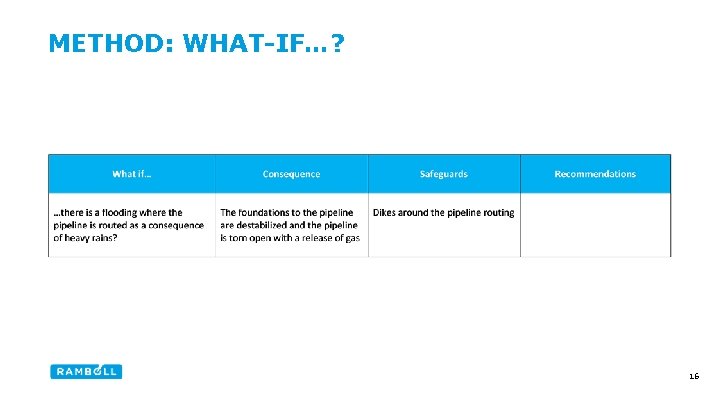
METHOD: WHAT-IF…? 16
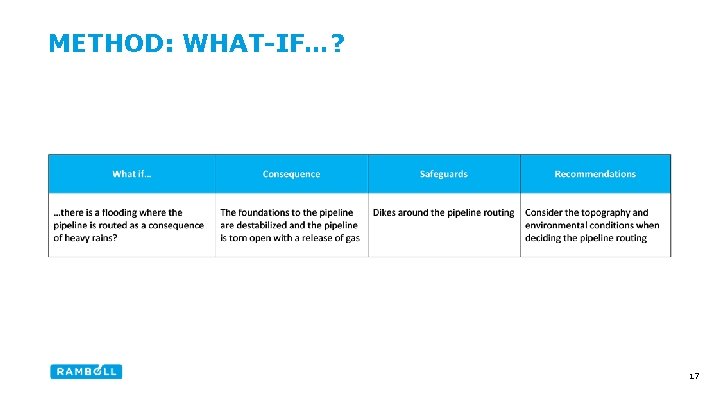
METHOD: WHAT-IF…? 17
METHOD: HAZID Description “HAZID is a structured, team based approach to identify hazards, their potential consequences, and requirements for risk reduction” • Systematic (e. g. use of guidewords) • All-round – from early stage of project to later stage of project • Separate presentation on HAZID 18
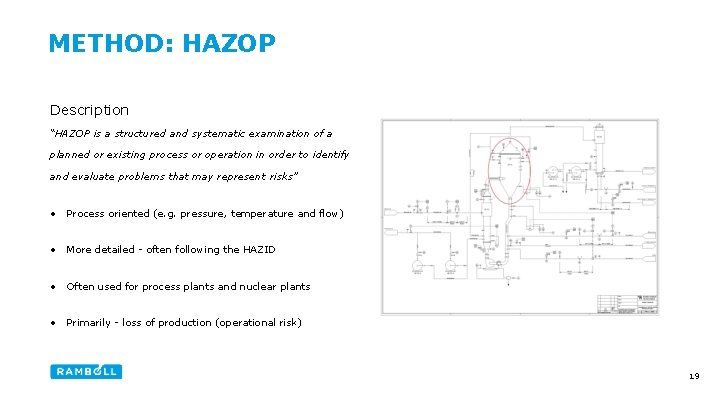
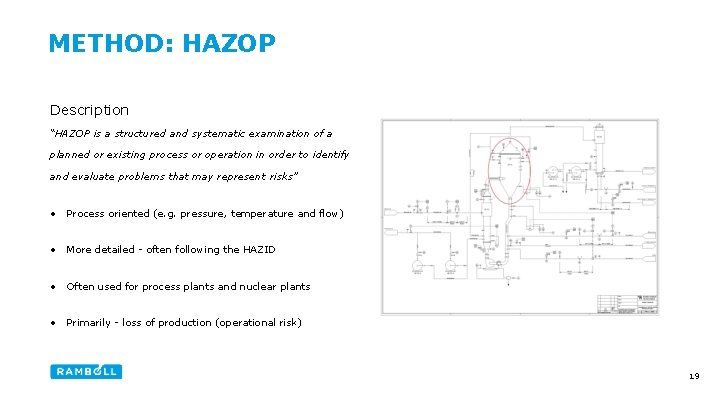
METHOD: HAZOP Description “HAZOP is a structured and systematic examination of a planned or existing process or operation in order to identify and evaluate problems that may represent risks” • Process oriented (e. g. pressure, temperature and flow) • More detailed - often following the HAZID • Often used for process plants and nuclear plants • Primarily - loss of production (operational risk) 19

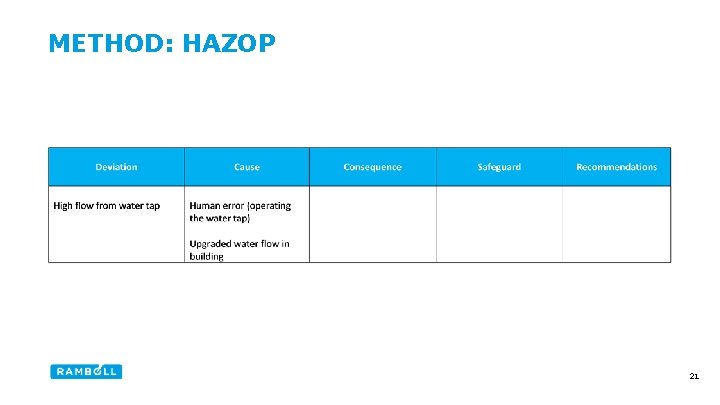
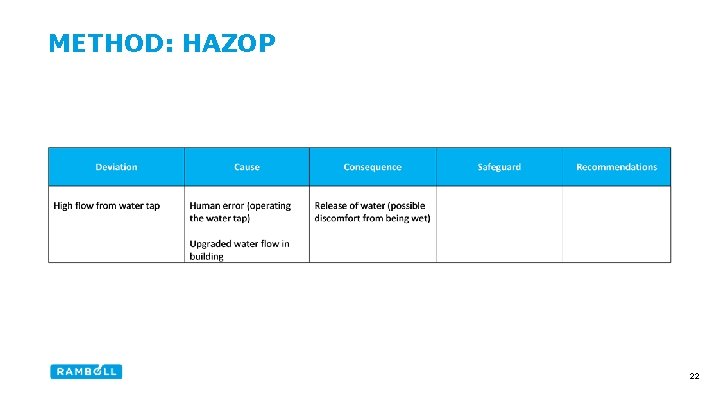
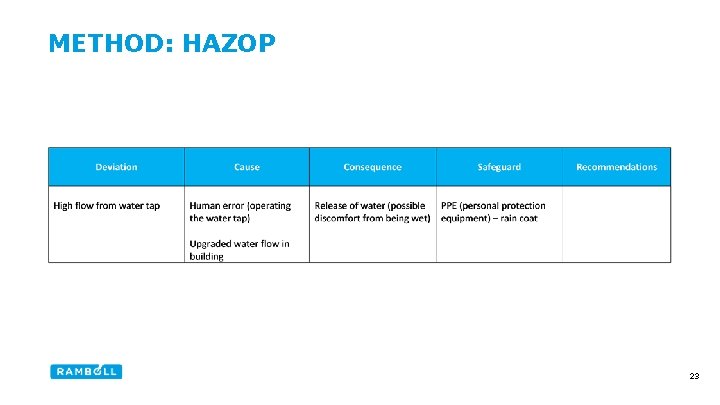
METHOD: HAZOP 20
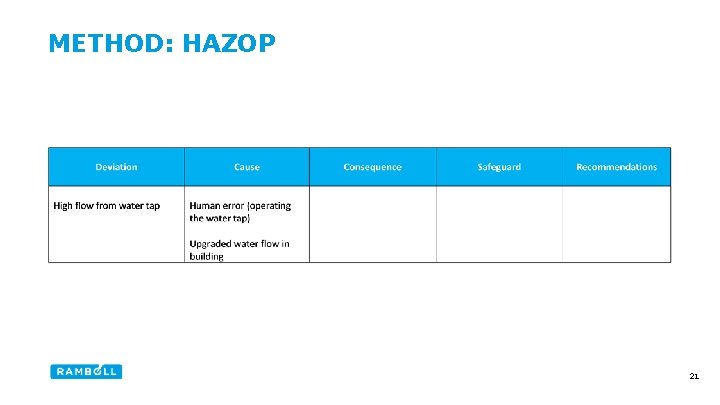
METHOD: HAZOP 21
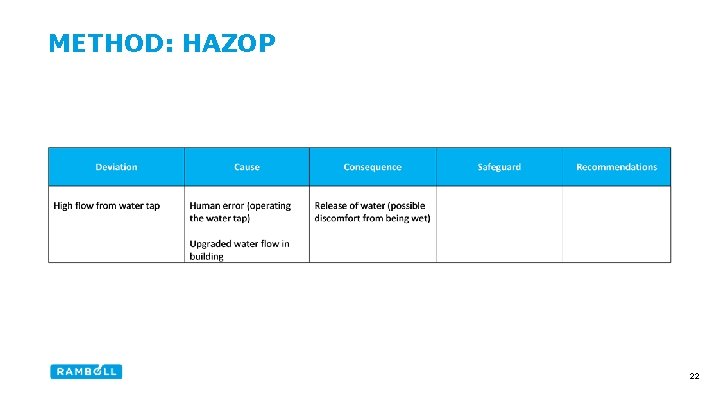
METHOD: HAZOP 22
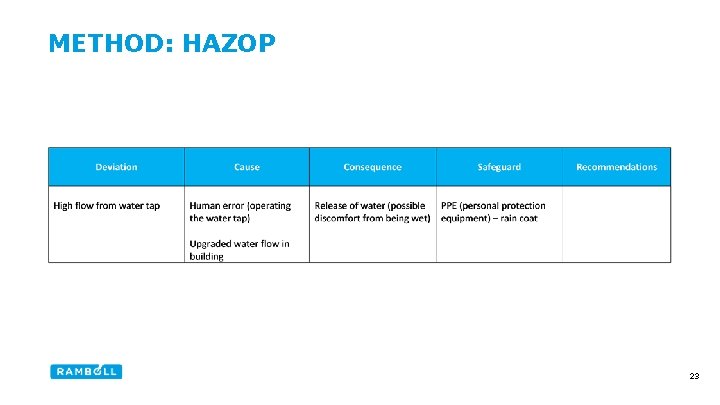
METHOD: HAZOP 23
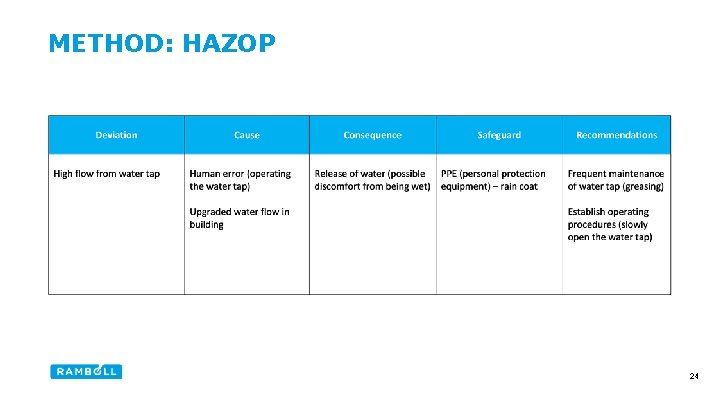
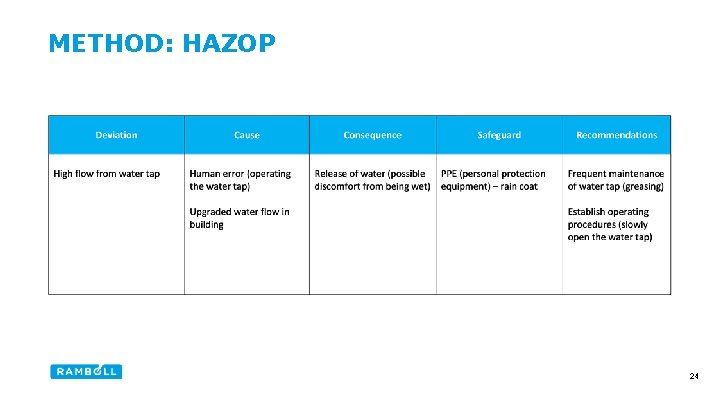
METHOD: HAZOP 24

METHOD: HAZOP 25

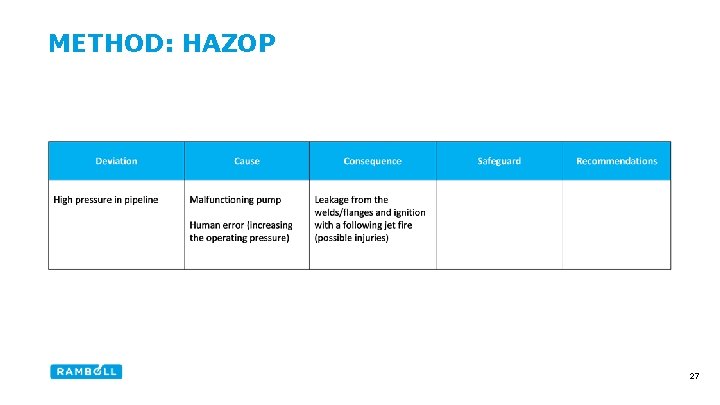
METHOD: HAZOP 26
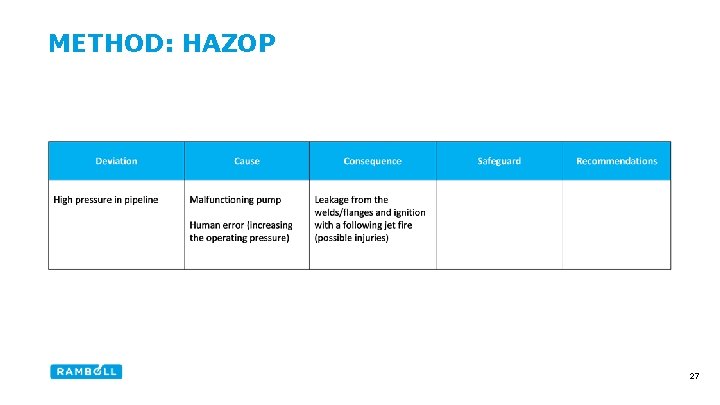
METHOD: HAZOP 27
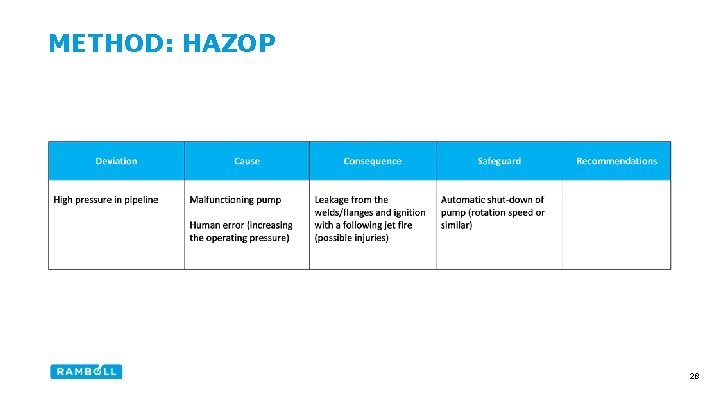
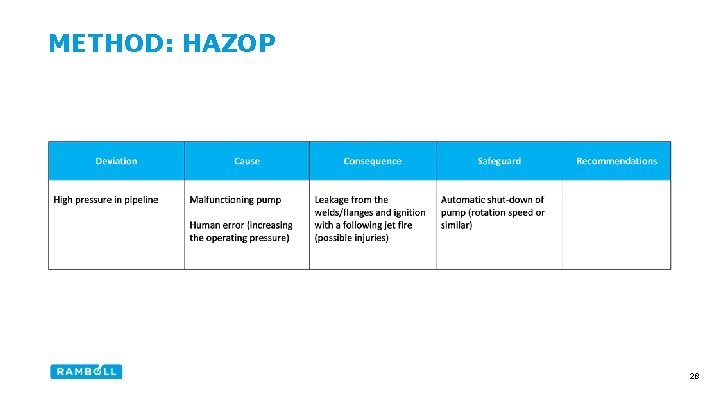
METHOD: HAZOP 28
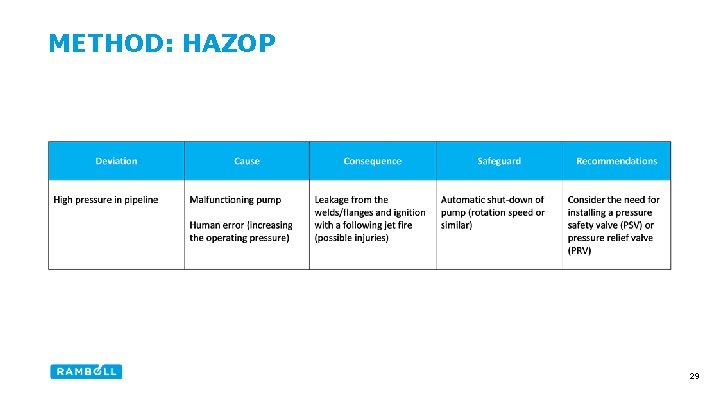
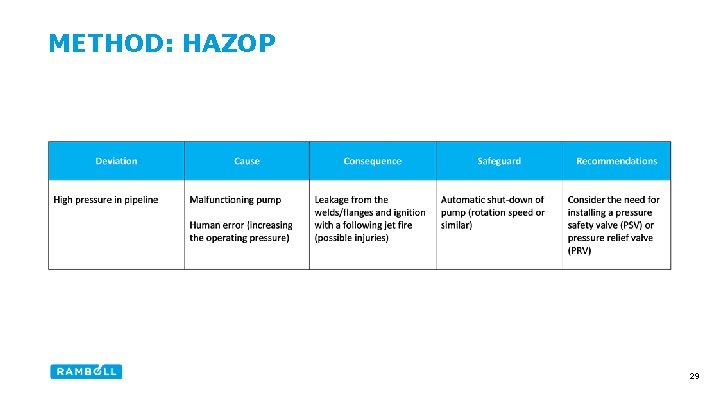
METHOD: HAZOP 29
METHOD: FAULT TREE ANALYSIS (FTA) Description “FTA is a top down, deductive failure analysis in which an undesired state of a system is analysed using Boolean logic to combine a series of lower-level events” • Often used for technical safety engineering and reliability engineering to understand how systems can fail and to quantify how often systems can fail • What is Boolean logic? - Boolean logic is a mathematical logic in which the values of the variables are the truth values (i. e. true and false) 30
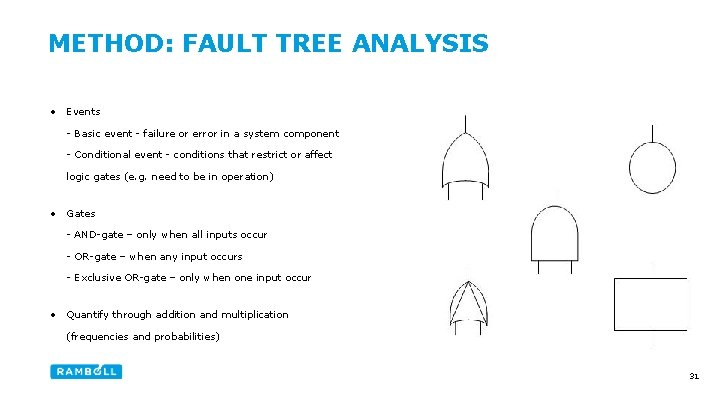
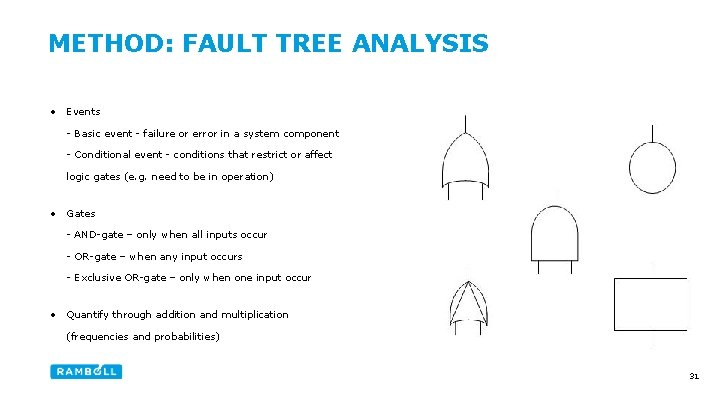
METHOD: FAULT TREE ANALYSIS • Events - Basic event - failure or error in a system component - Conditional event - conditions that restrict or affect logic gates (e. g. need to be in operation) • Gates - AND-gate – only when all inputs occur - OR-gate – when any input occurs - Exclusive OR-gate – only when one input occur • Quantify through addition and multiplication (frequencies and probabilities) 31
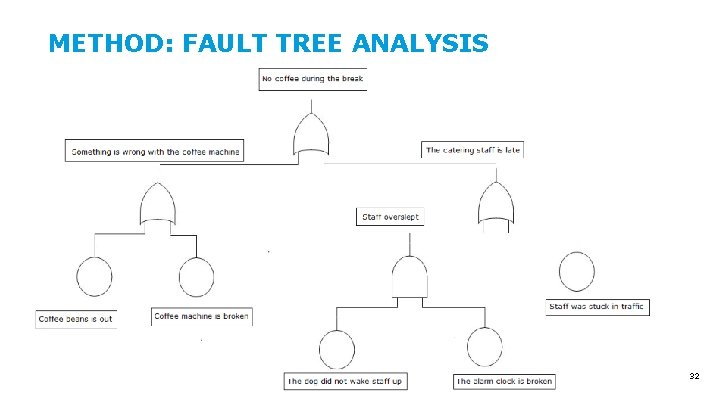
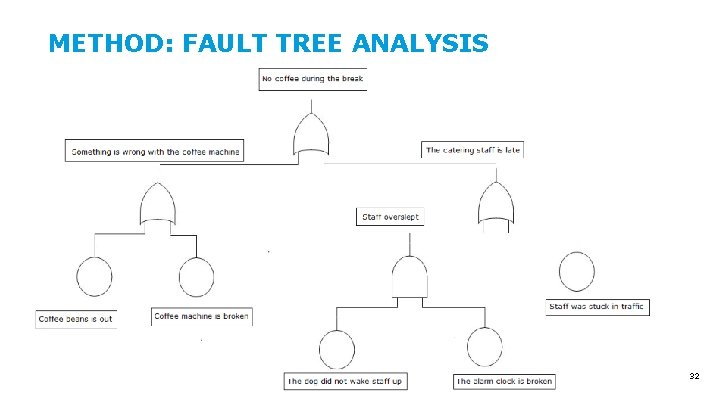
METHOD: FAULT TREE ANALYSIS 32
METHODS FOR RISK IDENTIFICATION • Which risk identification method should I choose? - method to feel comfortable with • Method depending on the situation (e. g. complexity, stage of project and time) • Method depending on the purpose (e. g. mapping of possible causes or consequences) • Risk identification could be applicable for all kind of situations and problems • Not just one time - never-ending process (i. e. changes) 33

QUESTIONS? 34