Picking Over The Corpse The Value Of Forensics

- Slides: 20
Picking Over The Corpse: The Value Of Forensics Matthijs van der Wel MBA CISSP® CISA® RON® QSA® QFI® Managing Principle Forensics EMEA Verizon Business Security Solutions Confidential and proprietary material for authorized Verizon Business personnel only. Use, disclosure or distribution of this material is not permitted to any unauthorized persons or third parties except by written agreement.
2009 Data Breach Investigations Report US TEAM EMEA TEAM Matthijs van der Wel Jelle Niemantsverdriet Thijs Bosschert Ben van Erck Paul Wright APAC TEAM Confidential and proprietary material for authorized Verizon Business personnel only. Use, disclosure or distribution of this material is not permitted to any unauthorized persons or third parties except by written agreement.
R I S K Team Response – Incident response and investigation services. Intelligence – Gather, analyze, and correlate intel from a wide range of sources and then provide appropriate data, alerts, analysis and recommendations to our clients. E S P O N S E N T E L L I G E N C E O N L O U W T L I E O D N G S E Solutions – Innovation and prototyping of new products and services. Knowledge – Develop and disseminate risk knowledge and capabilities throughout the company, to our customers, and to the public. The DBIR is the result of collaboration between the Response and Intelligence groups Confidential and proprietary material for authorized Verizon Business personnel only. Use, disclosure or distribution of this material is not permitted to any unauthorized persons or third parties except by written agreement. 4

Results and Analysis 2009 Data Breach Investigations Report Confidential and proprietary material for authorized Verizon Business personnel only. Use, disclosure or distribution of this material is not permitted to any unauthorized persons or third parties except by written agreement.
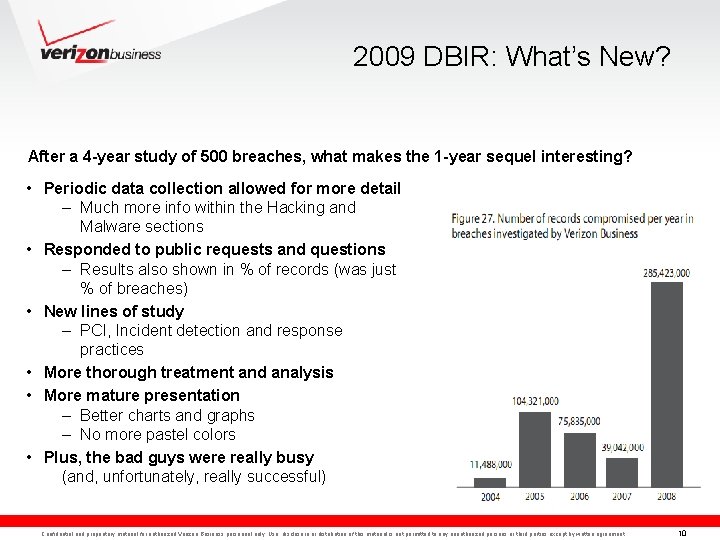
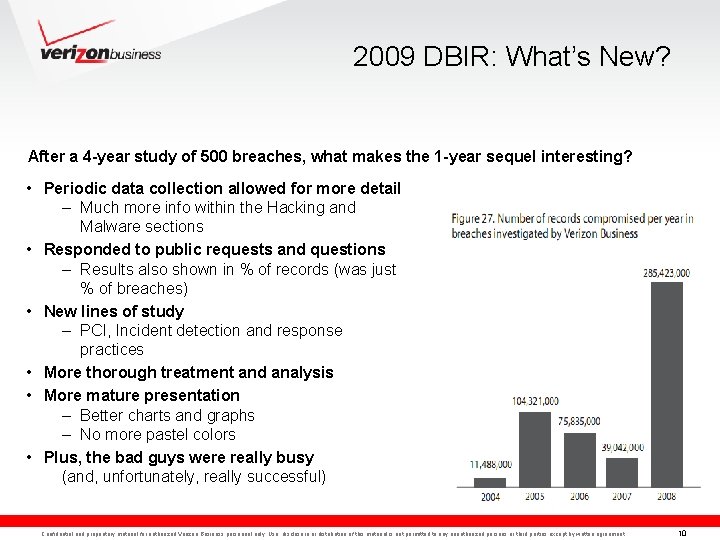
2009 DBIR: What’s New? After a 4 -year study of 500 breaches, what makes the 1 -year sequel interesting? • Periodic data collection allowed for more detail – Much more info within the Hacking and Malware sections • Responded to public requests and questions – Results also shown in % of records (was just % of breaches) • New lines of study – PCI, Incident detection and response practices • More thorough treatment and analysis • More mature presentation – Better charts and graphs – No more pastel colors • Plus, the bad guys were really busy (and, unfortunately, really successful) Confidential and proprietary material for authorized Verizon Business personnel only. Use, disclosure or distribution of this material is not permitted to any unauthorized persons or third parties except by written agreement. 10
IR Case Data All data collected during cases worked by the Verizon Business Investigative Response team during 2008 • Objective, credible, first-hand information on actual breaches 2008 Caseload: • 90 confirmed breaches (>150 total engagements) • 285 million compromised records (confirmed – not “data-at-risk”) • 1/3 of these cases have been publicly disclosed (so far) • About 50% of caseload comprised of sets of interrelated incidents – Same attacker(s), shared connections, identical circumstances, etc • 15 arrests (and counting) • 31% Retail, 30% Financial, 14% Food & Bev, remaining mixed • Over 1/3 of investigations conducted outside the US Confidential and proprietary material for authorized Verizon Business personnel only. Use, disclosure or distribution of this material is not permitted to any unauthorized persons or third parties except by written agreement. 11
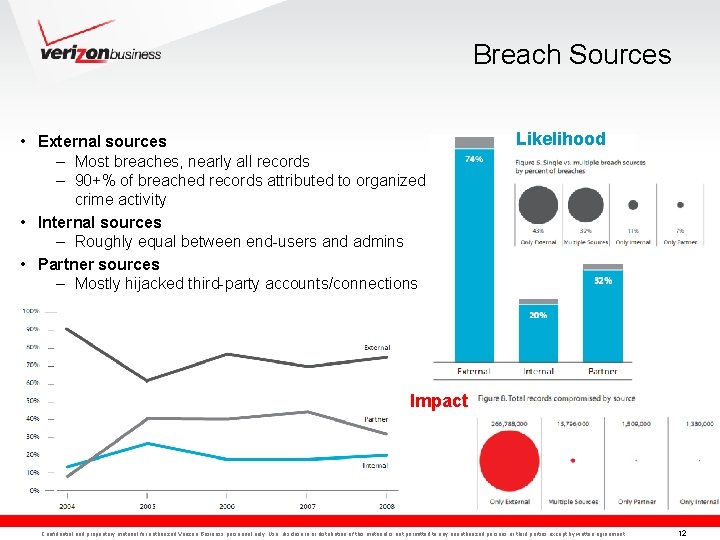
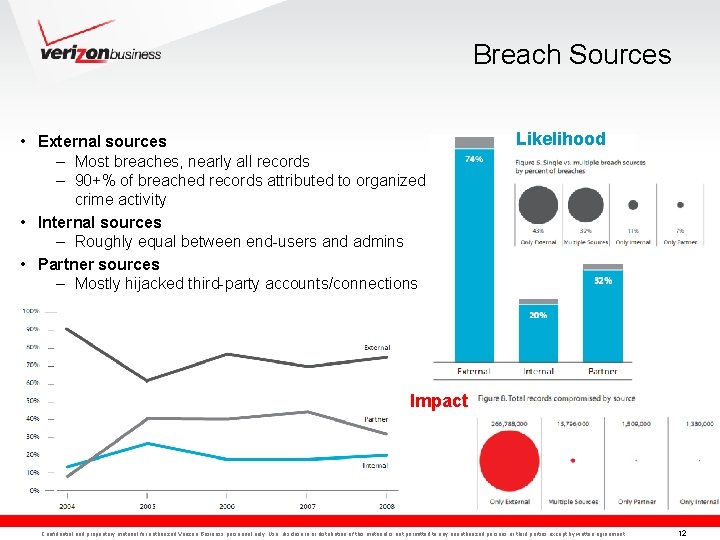
Breach Sources • External sources – Most breaches, nearly all records – 90+% of breached records attributed to organized crime activity • Internal sources – Roughly equal between end-users and admins • Partner sources – Mostly hijacked third-party accounts/connections Likelihood Impact Confidential and proprietary material for authorized Verizon Business personnel only. Use, disclosure or distribution of this material is not permitted to any unauthorized persons or third parties except by written agreement. 12
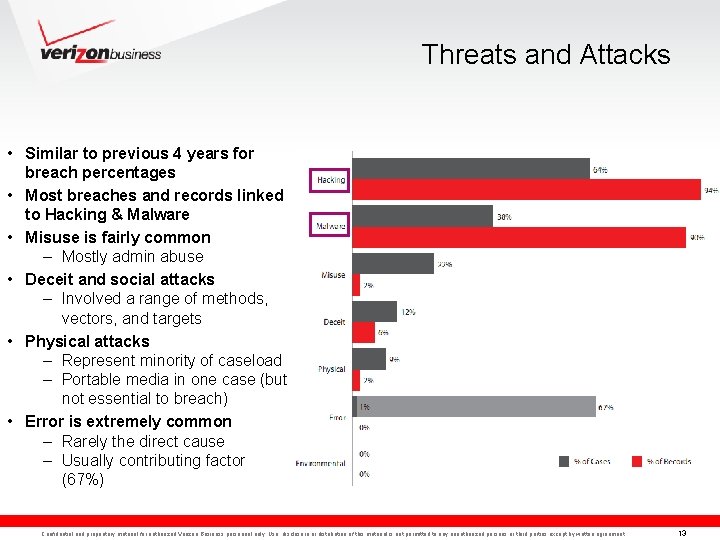
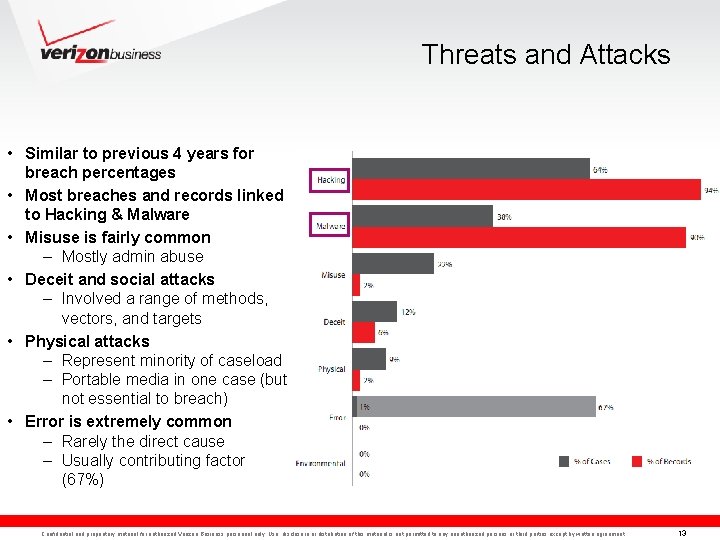
Threats and Attacks • Similar to previous 4 years for breach percentages • Most breaches and records linked to Hacking & Malware • Misuse is fairly common – Mostly admin abuse • Deceit and social attacks – Involved a range of methods, vectors, and targets • Physical attacks – Represent minority of caseload – Portable media in one case (but not essential to breach) • Error is extremely common – Rarely the direct cause – Usually contributing factor (67%) Confidential and proprietary material for authorized Verizon Business personnel only. Use, disclosure or distribution of this material is not permitted to any unauthorized persons or third parties except by written agreement. 13
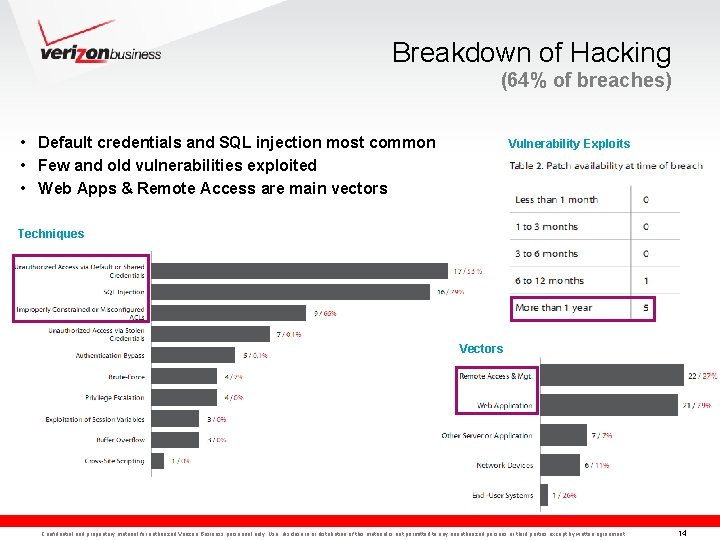
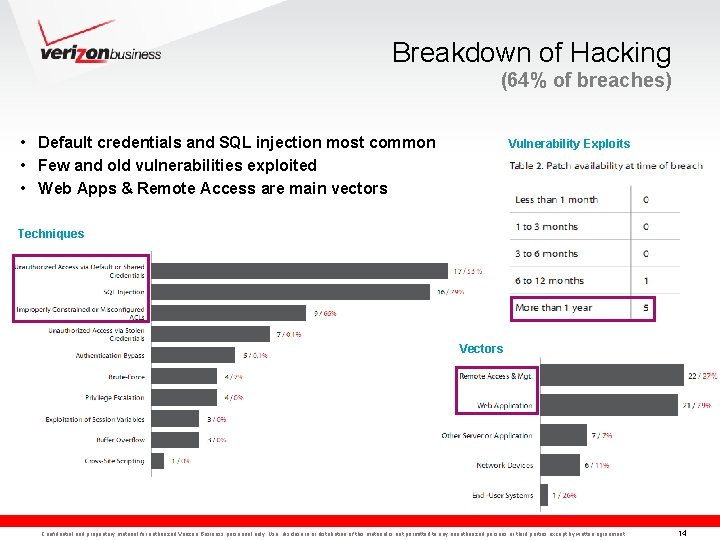
Breakdown of Hacking (64% of breaches) • Default credentials and SQL injection most common • Few and old vulnerabilities exploited • Web Apps & Remote Access are main vectors Vulnerability Exploits Techniques Vectors Confidential and proprietary material for authorized Verizon Business personnel only. Use, disclosure or distribution of this material is not permitted to any unauthorized persons or third parties except by written agreement. 14
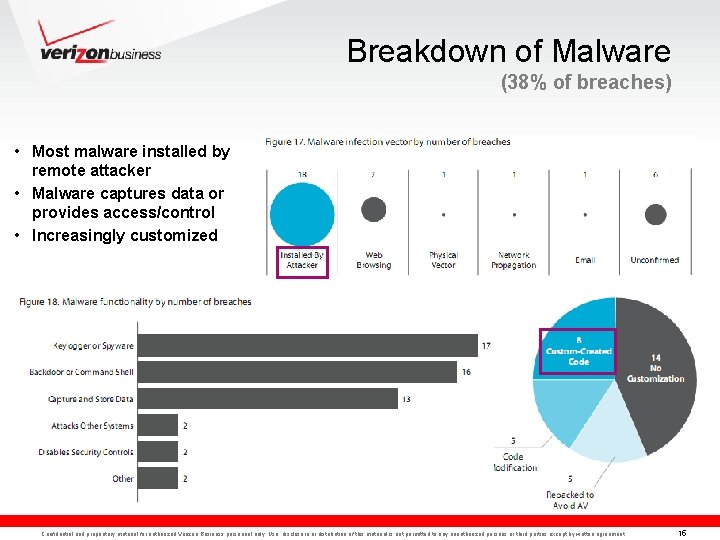
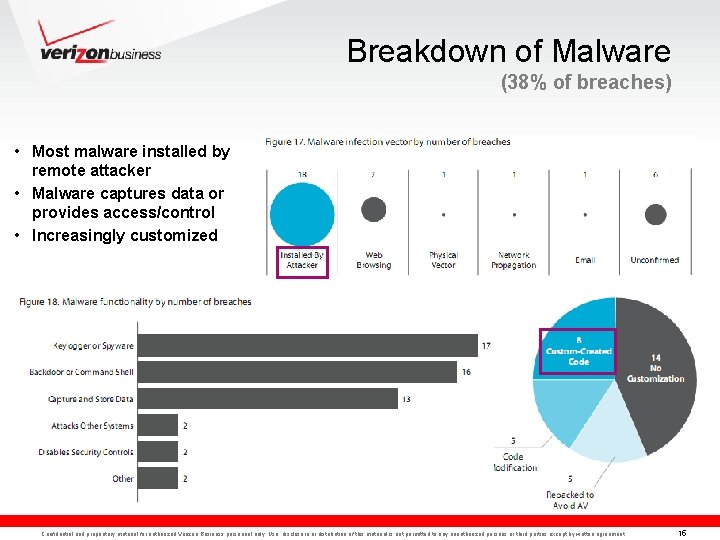
Breakdown of Malware (38% of breaches) • Most malware installed by remote attacker • Malware captures data or provides access/control • Increasingly customized Confidential and proprietary material for authorized Verizon Business personnel only. Use, disclosure or distribution of this material is not permitted to any unauthorized persons or third parties except by written agreement. 15
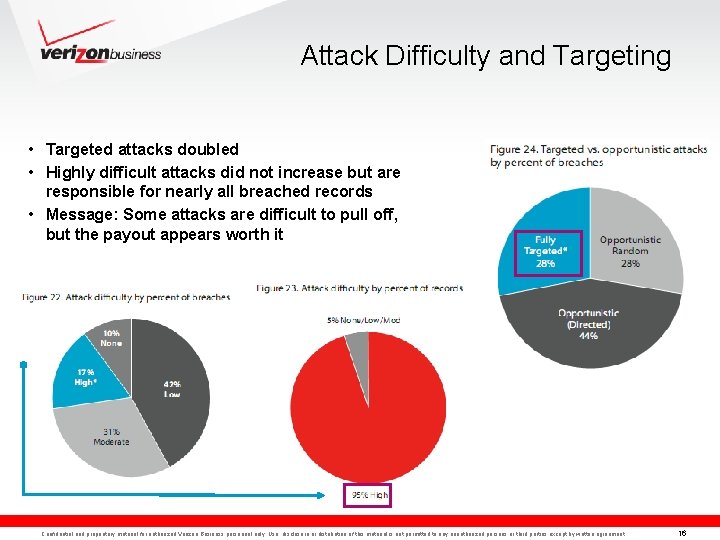
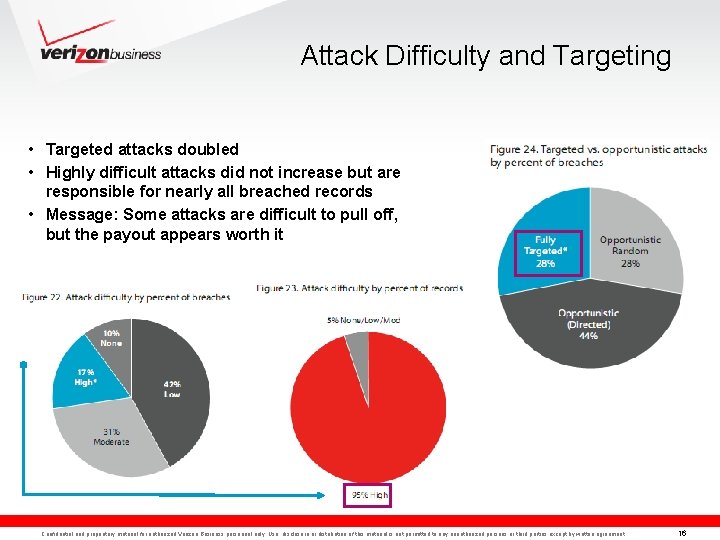
Attack Difficulty and Targeting • Targeted attacks doubled • Highly difficult attacks did not increase but are responsible for nearly all breached records • Message: Some attacks are difficult to pull off, but the payout appears worth it Confidential and proprietary material for authorized Verizon Business personnel only. Use, disclosure or distribution of this material is not permitted to any unauthorized persons or third parties except by written agreement. 16
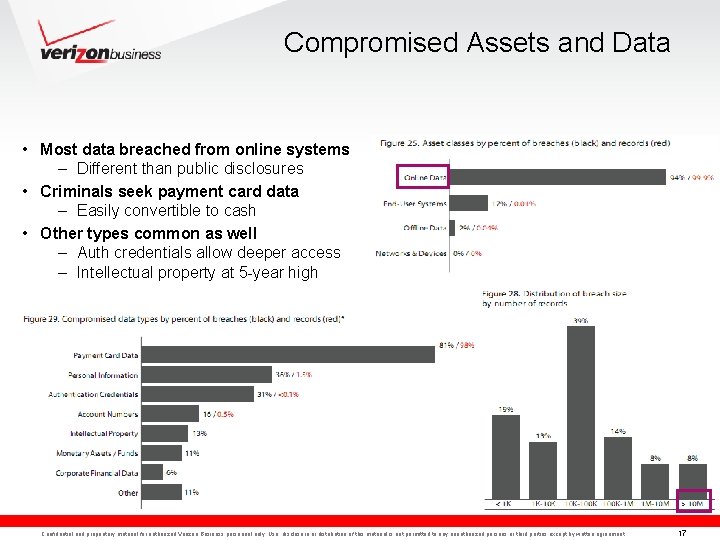
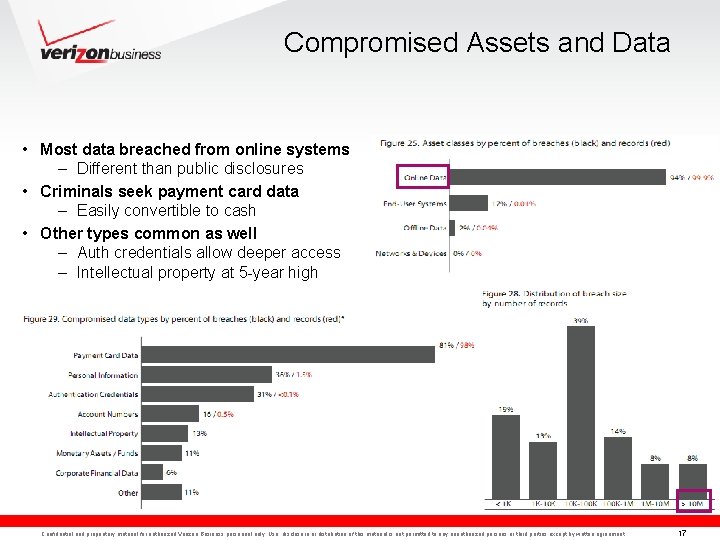
Compromised Assets and Data • Most data breached from online systems – Different than public disclosures • Criminals seek payment card data – Easily convertible to cash • Other types common as well – Auth credentials allow deeper access – Intellectual property at 5 -year high Confidential and proprietary material for authorized Verizon Business personnel only. Use, disclosure or distribution of this material is not permitted to any unauthorized persons or third parties except by written agreement. 17
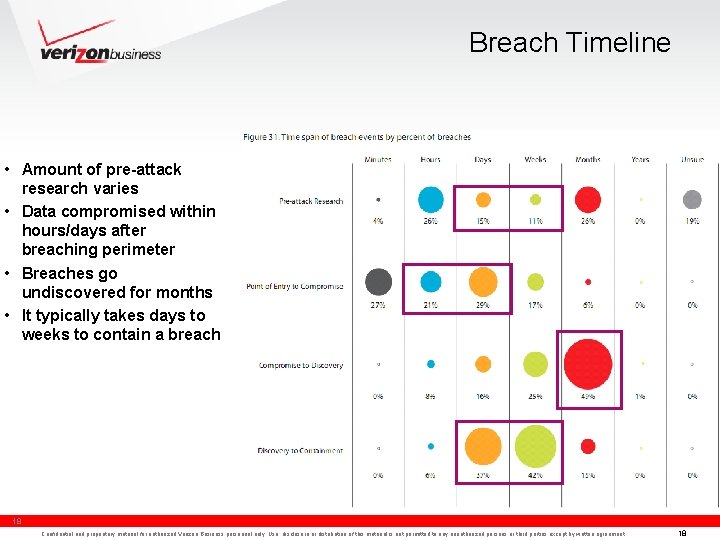
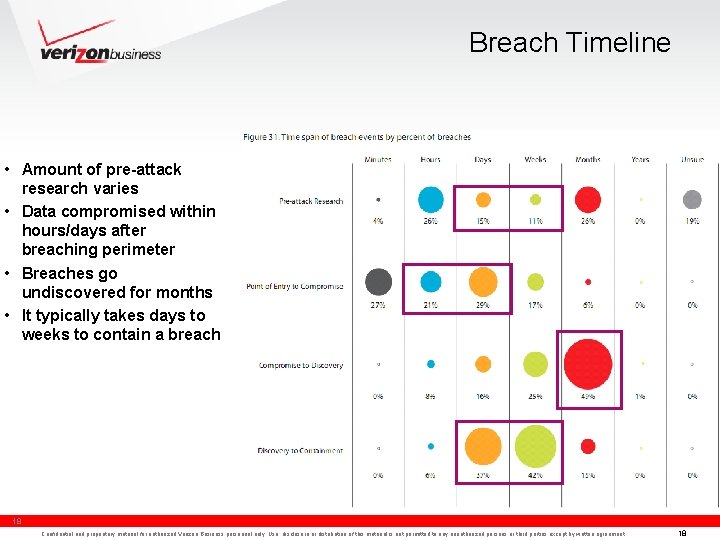
Breach Timeline • Amount of pre-attack research varies • Data compromised within hours/days after breaching perimeter • Breaches go undiscovered for months • It typically takes days to weeks to contain a breach 18 Confidential and proprietary material for authorized Verizon Business personnel only. Use, disclosure or distribution of this material is not permitted to any unauthorized persons or third parties except by written agreement. 18
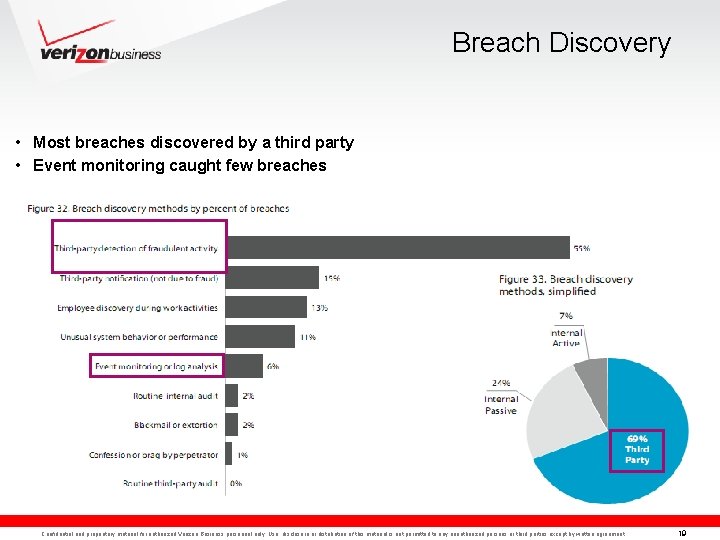
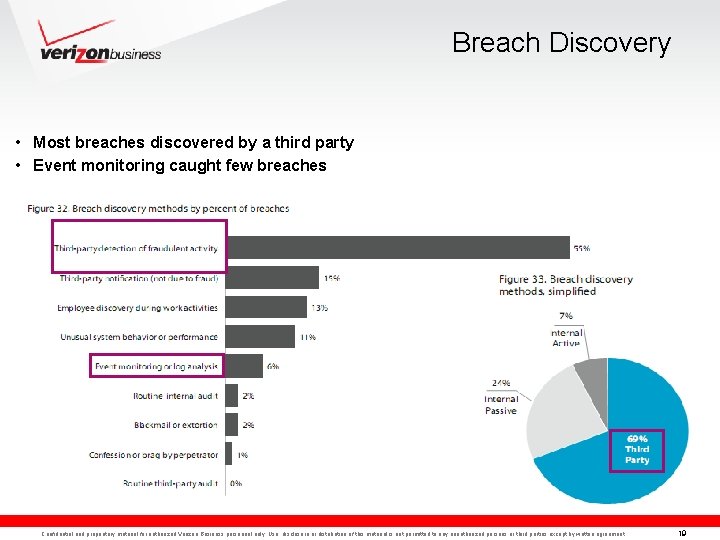
Breach Discovery • Most breaches discovered by a third party • Event monitoring caught few breaches Confidential and proprietary material for authorized Verizon Business personnel only. Use, disclosure or distribution of this material is not permitted to any unauthorized persons or third parties except by written agreement. 19
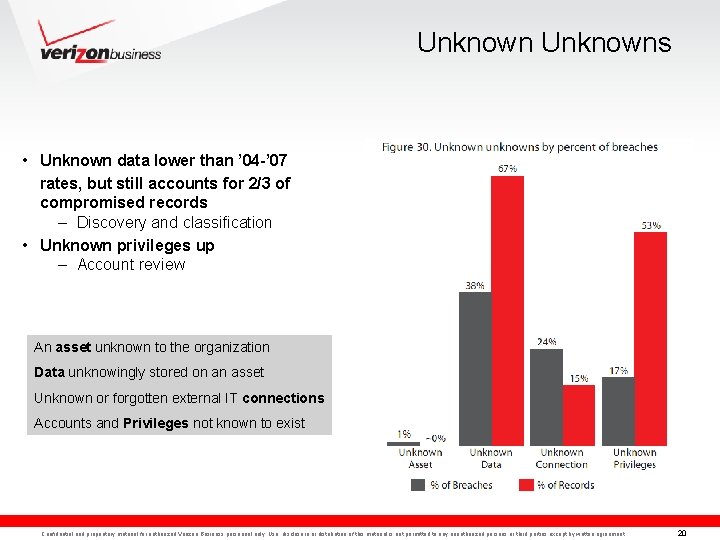
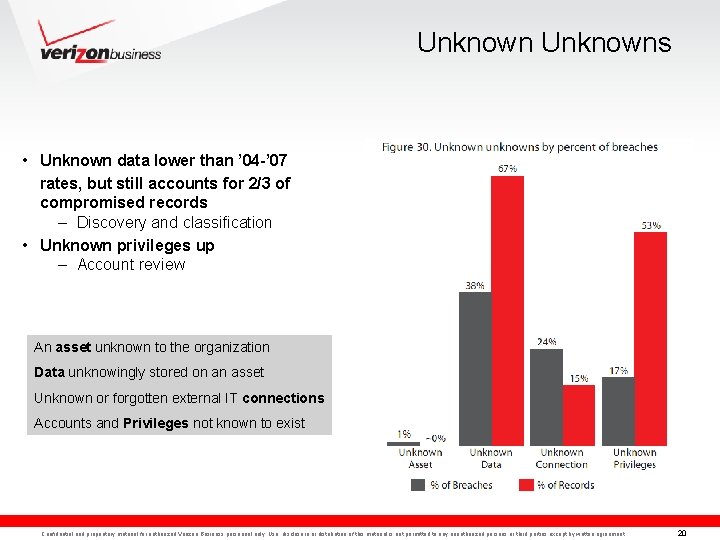
Unknowns • Unknown data lower than ’ 04 -’ 07 rates, but still accounts for 2/3 of compromised records – Discovery and classification • Unknown privileges up – Account review An asset unknown to the organization Data unknowingly stored on an asset Unknown or forgotten external IT connections Accounts and Privileges not known to exist Confidential and proprietary material for authorized Verizon Business personnel only. Use, disclosure or distribution of this material is not permitted to any unauthorized persons or third parties except by written agreement. 20
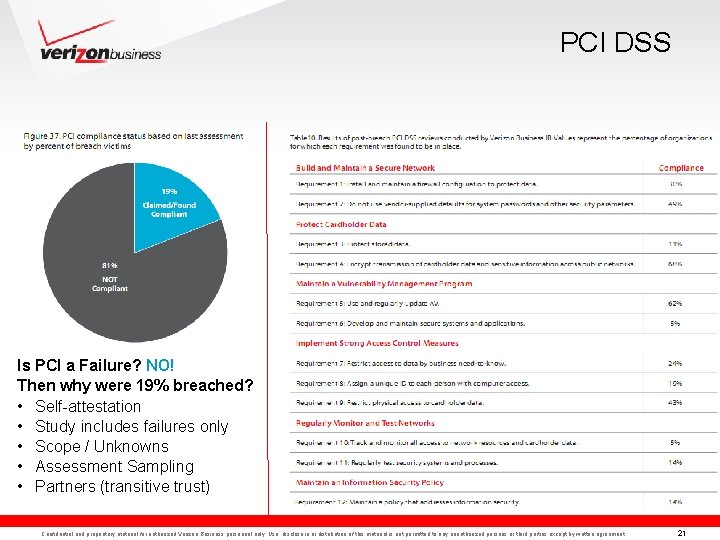
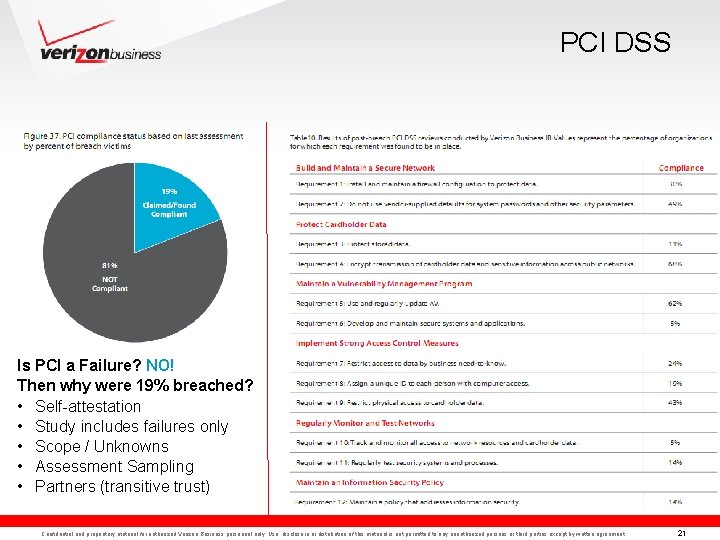
PCI DSS Is PCI a Failure? NO! Then why were 19% breached? • Self-attestation • Study includes failures only • Scope / Unknowns • Assessment Sampling • Partners (transitive trust) Confidential and proprietary material for authorized Verizon Business personnel only. Use, disclosure or distribution of this material is not permitted to any unauthorized persons or third parties except by written agreement. 21
Recommendations Recap from previous report (They still apply) • Align process with policy • Achieve “Essential” then worry about “Excellent” • Secure Business Partner Connections • Create a Data Retention Plan • Control data with transaction zones • Monitor event logs • Create an Incident Response Plan • Increase awareness • Engage in mock incident testing Confidential and proprietary material for authorized Verizon Business personnel only. Use, disclosure or distribution of this material is not permitted to any unauthorized persons or third parties except by written agreement. 22
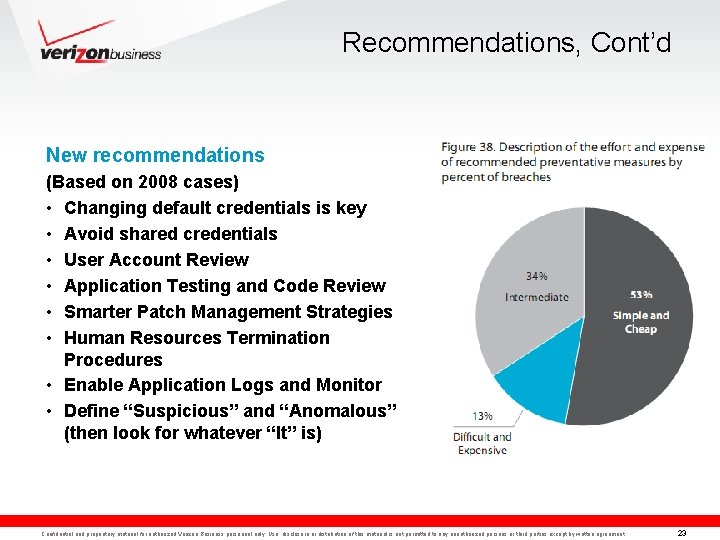
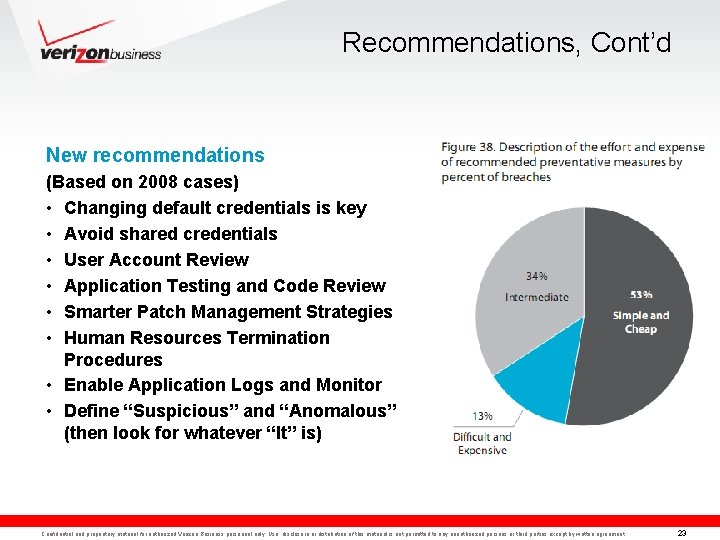
Recommendations, Cont’d New recommendations (Based on 2008 cases) • Changing default credentials is key • Avoid shared credentials • User Account Review • Application Testing and Code Review • Smarter Patch Management Strategies • Human Resources Termination Procedures • Enable Application Logs and Monitor • Define “Suspicious” and “Anomalous” (then look for whatever “It” is) Confidential and proprietary material for authorized Verizon Business personnel only. Use, disclosure or distribution of this material is not permitted to any unauthorized persons or third parties except by written agreement. 23
Summary 2008 saw much of the same, but new twists and trends were observed • Sources: Similar distribution; organized crime behind most large breaches – Organized criminal groups driving evolution of cybercrime • Attacks: Criminals exploit errors, hack into systems, install malware – 2008 saw more targeted attacks, especially against orgs processing or storing large volumes of desirable data – Highly difficult attacks not common but very damaging – Large increase in customized, intelligent malware • Assets and Data: Focus is online cashable data – Nearly all breached from servers & apps – New data types (PIN data) sought which requires new techniques and targets • Discovery: Takes months and is accomplished by 3 rd parties • Prevention: The basics–if done consistently–are effective in most cases – Increasing divergence between Targets of Opportunity and Targets of Choice • To. O: Remove blatant opportunities through basic controls • To. C: Same as above but prepare for very determined, very skilled attacks – Initial hack appears the easiest point of control Confidential and proprietary material for authorized Verizon Business personnel only. Use, disclosure or distribution of this material is not permitted to any unauthorized persons or third parties except by written agreement. 24
Questions? Confidential and proprietary material for authorized Verizon Business personnel only. Use, disclosure or distribution of this material is not permitted to any unauthorized persons or third parties except by written agreement. 25