Physically Unclonable Function Based Security and Privacy in
Physically Unclonable Function– Based Security and Privacy in RFID Systems Leonid Bolotnyy and Gabriel Robins Dept. of Computer Science University of Virginia www. cs. virginia. edu/robins
Contribution and Motivation Contribution • Privacy-preserving tag identification algorithm • Secure MAC algorithms • Comparison of PUF with digital hash functions Motivation • Digital crypto implementations require 1000’s of gates • Low-cost alternatives – Pseudonyms / one-time pads – Low complexity / power hash function designs – Hardware-based solutions
![PUF-Based Security • Physical Unclonable Function (PUF) [Gassend et al 2002] • PUF Security PUF-Based Security • Physical Unclonable Function (PUF) [Gassend et al 2002] • PUF Security](http://slidetodoc.com/presentation_image/1483c051a2ddf894f204934bfbffe08d/image-3.jpg)
PUF-Based Security • Physical Unclonable Function (PUF) [Gassend et al 2002] • PUF Security is based on – wire delays – gate delays – quantum mechanical fluctuations • PUF characteristics – uniqueness – reliability – unpredictability • PUF Assumptions – Infeasible to accurately model PUF – Pair-wise PUF output-collision probability is constant – Physical tampering will modify PUF
Privacy in RFID • Privacy A B Alice was here: A, B, C privacy C
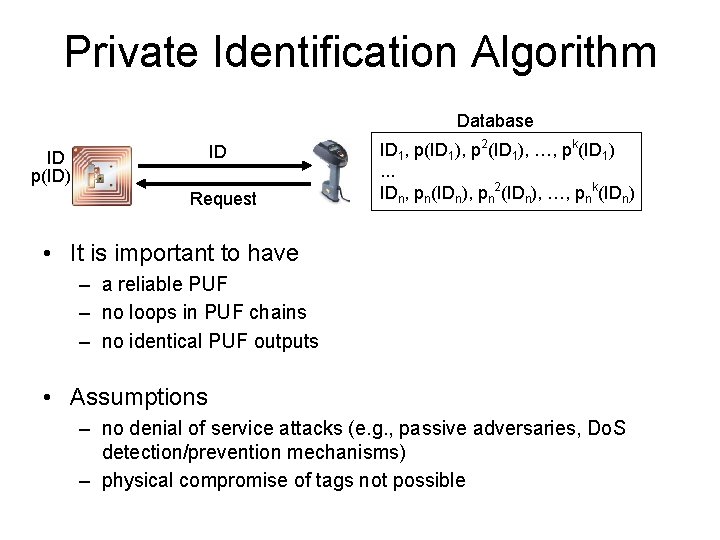
Private Identification Algorithm Database ID ID p(ID) Request ID 1, p(ID 1), p 2(ID 1), …, pk(ID 1). . . IDn, pn(IDn), pn 2(IDn), …, pnk(IDn) • It is important to have – a reliable PUF – no loops in PUF chains – no identical PUF outputs • Assumptions – no denial of service attacks (e. g. , passive adversaries, Do. S detection/prevention mechanisms) – physical compromise of tags not possible
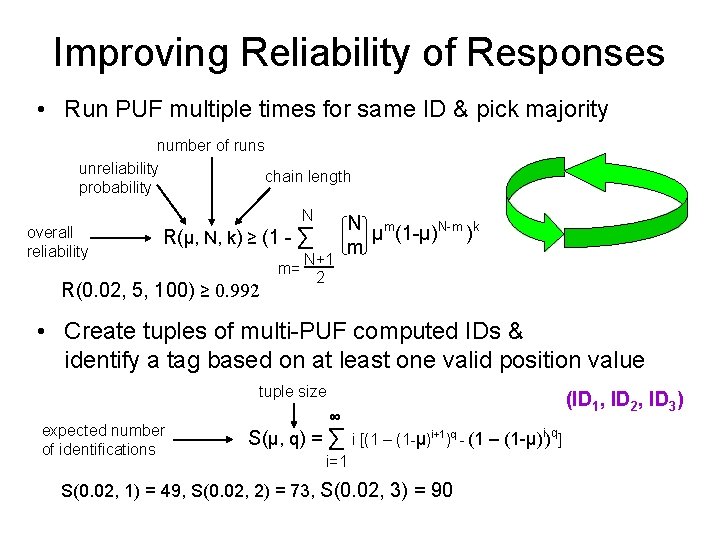
Improving Reliability of Responses • Run PUF multiple times for same ID & pick majority number of runs unreliability chain length probability overall reliability N R(μ, N, k) ≥ (1 - ∑ m= R(0. 02, 5, 100) ≥ 0. 992 N+1 2 N μm(1 -μ)N-m )k m • Create tuples of multi-PUF computed IDs & identify a tag based on at least one valid position value tuple size expected number of identifications (ID 1, ID 2, ID 3) ∞ S(μ, q) = ∑ i q i [(1 – (1 -μ)i+1)q - (1 – (1 -μ) ) ] i=1 S(0. 02, 1) = 49, S(0. 02, 2) = 73, S(0. 02, 3) = 90
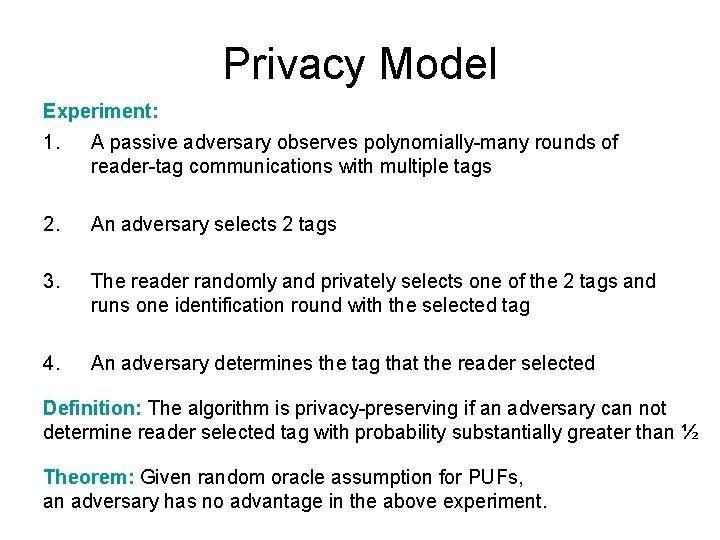
Privacy Model Experiment: 1. A passive adversary observes polynomially-many rounds of reader-tag communications with multiple tags 2. An adversary selects 2 tags 3. The reader randomly and privately selects one of the 2 tags and runs one identification round with the selected tag 4. An adversary determines the tag that the reader selected Definition: The algorithm is privacy-preserving if an adversary can not determine reader selected tag with probability substantially greater than ½ Theorem: Given random oracle assumption for PUFs, an adversary has no advantage in the above experiment.
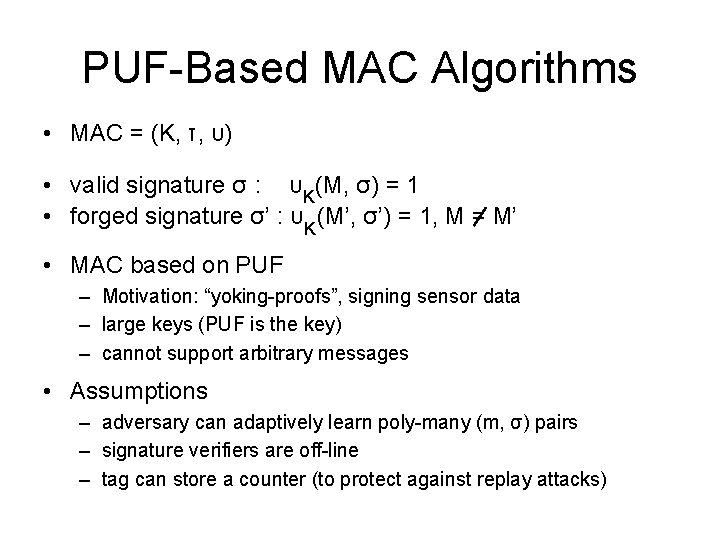
PUF-Based MAC Algorithms • MAC = (K, τ, υ) • valid signature σ : υ K(M, σ) = 1 • forged signature σ’ : υK (M’, σ’) = 1, M = M’ • MAC based on PUF – Motivation: “yoking-proofs”, signing sensor data – large keys (PUF is the key) – cannot support arbitrary messages • Assumptions – adversary can adaptively learn poly-many (m, σ) pairs – signature verifiers are off-line – tag can store a counter (to protect against replay attacks)
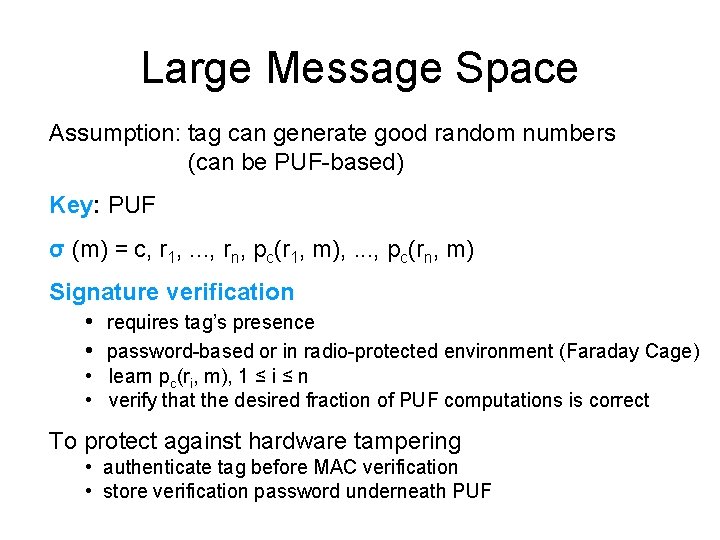
Large Message Space Assumption: tag can generate good random numbers (can be PUF-based) Key: PUF σ (m) = c, r 1, . . . , rn, pc(r 1, m), . . . , pc(rn, m) Signature verification • requires tag’s presence • password-based or in radio-protected environment (Faraday Cage) • learn pc(ri, m), 1 ≤ i ≤ n • verify that the desired fraction of PUF computations is correct To protect against hardware tampering • authenticate tag before MAC verification • store verification password underneath PUF
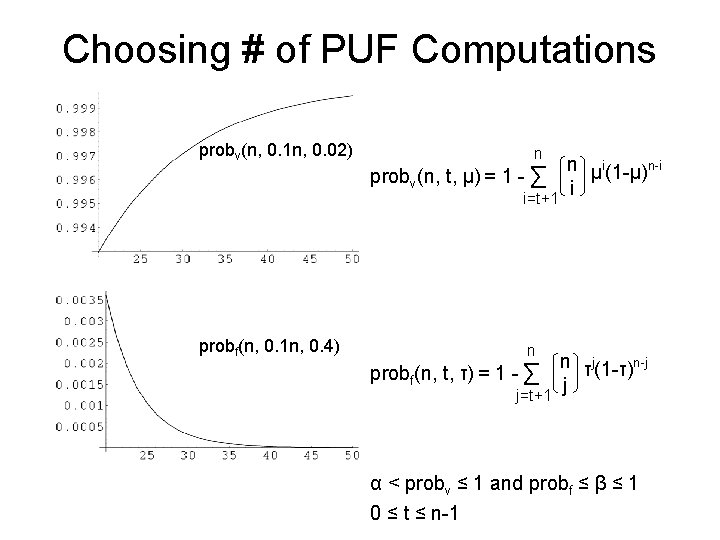
Choosing # of PUF Computations probv(n, 0. 1 n, 0. 02) n probv(n, t, μ) = 1 - ∑ i=t+1 probf(n, 0. 1 n, 0. 4) n probf(n, t, τ) = 1 - ∑ j=t+1 n μi(1 -μ)n-i i n τj(1 -τ)n-j j α < probv ≤ 1 and probf ≤ β ≤ 1 0 ≤ t ≤ n-1
Theorem Given random oracle assumption for a PUF, the probability that an adversary could forge a signature for a message is bounded from above by the tag impersonation probability.
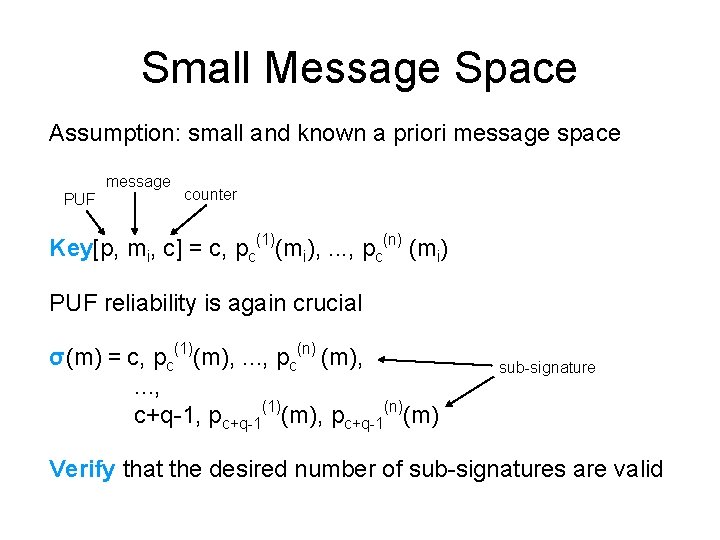
Small Message Space Assumption: small and known a priori message space message PUF counter Key[p, mi, c] = c, pc(1)(mi), . . . , pc(n) (mi) PUF reliability is again crucial σ(m) = c, pc(1)(m), . . . , pc(n) (m), . . . , c+q-1, pc+q-1(1)(m), pc+q-1(n)(m) sub-signature Verify that the desired number of sub-signatures are valid
Theorem Given random oracle assumption for a PUF, the probability that an adversary could forge a signature for a message is bounded by the tag impersonation probability times the number of sub-signatures.
Attacks on MAC Protocols • Impersonation attacks – manufacture an identical tag – obtain (steal) existing PUFs • Modeling attacks – build a PUF model to predict PUF’s outputs • Side-channel attacks – algorithm timing – power consumption • Hardware-tampering attacks – physically probe wires to learn the PUF – physically read-off/alter keys/passwords original clone
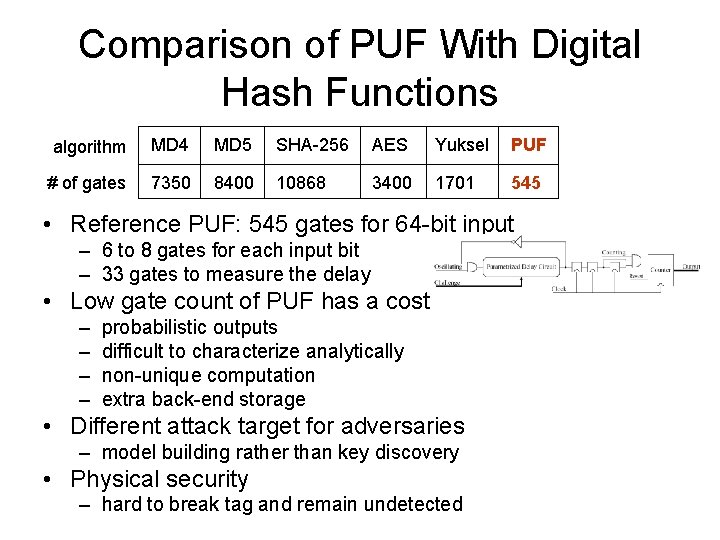
Comparison of PUF With Digital Hash Functions algorithm MD 4 MD 5 SHA-256 AES Yuksel PUF # of gates 7350 8400 10868 3400 1701 545 • Reference PUF: 545 gates for 64 -bit input – 6 to 8 gates for each input bit – 33 gates to measure the delay • Low gate count of PUF has a cost – – probabilistic outputs difficult to characterize analytically non-unique computation extra back-end storage • Different attack target for adversaries – model building rather than key discovery • Physical security – hard to break tag and remain undetected
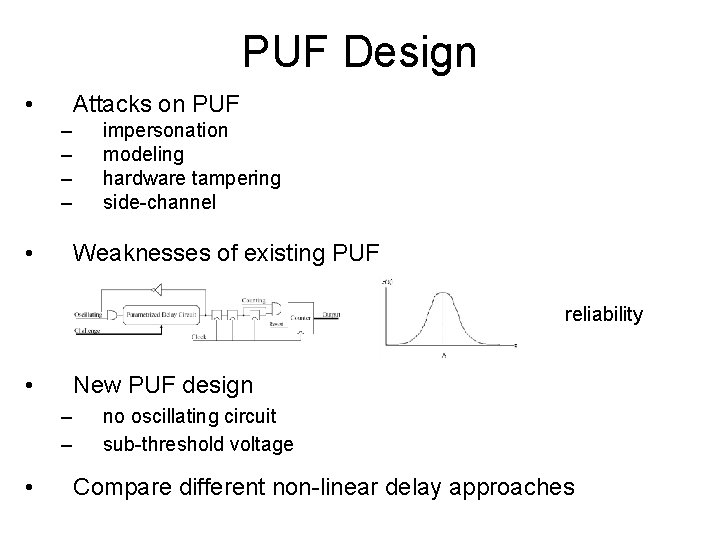
PUF Design • Attacks on PUF – – • impersonation modeling hardware tampering side-channel Weaknesses of existing PUF reliability • New PUF design – – • no oscillating circuit sub-threshold voltage Compare different non-linear delay approaches
Conclusions and Future Work • • PUF: hardware primitive for RFID security Identification and MAC algorithms based on PUFs protect tags from physical attacks PUFs is the key • Develop theoretical framework for PUF • Design new sub-threshold voltage based PUF • Manufacture and test PUFs – varying environmental conditions – motion, acceleration, vibration, temperature, noise • Design new PUF-based security protocols – ownership transfer – recovery from privacy compromise – PUFs on RFID readers } in progress
Thank You Questions ? Leonid Bolotnyy lbol@cs. virginia. edu Dept. of Computer Science University of Virginia
PUF-Based Ownership Transfer • To maintain privacy we need – ownership privacy – forward privacy • Physical security is especially important • Solutions – – public key cryptography (expensive) knowledge of owners sequence trusted authority short period of privacy
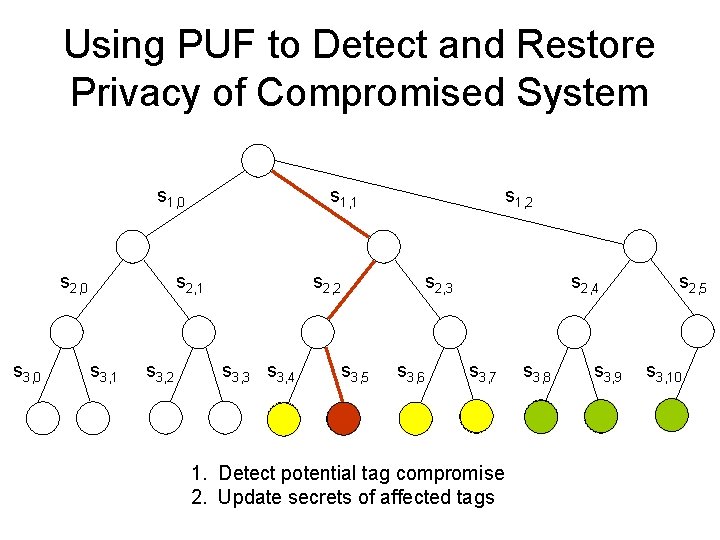
Using PUF to Detect and Restore Privacy of Compromised System s 1, 0 s 2, 0 s 3, 0 s 1, 1 s 2, 1 s 3, 2 s 2, 2 s 3, 3 s 3, 4 s 3, 5 s 1, 2 s 2, 4 s 2, 3 s 3, 6 s 3, 7 1. Detect potential tag compromise 2. Update secrets of affected tags s 3, 8 s 3, 9 s 2, 5 s 3, 10
![Related Work on PUF • Optical PUF [Ravikanth 2001] • Silicon PUF [Gassend et Related Work on PUF • Optical PUF [Ravikanth 2001] • Silicon PUF [Gassend et](http://slidetodoc.com/presentation_image/1483c051a2ddf894f204934bfbffe08d/image-21.jpg)
Related Work on PUF • Optical PUF [Ravikanth 2001] • Silicon PUF [Gassend et al 2002] – Design, implementation, simulation, manufacturing – Authentication algorithm – Controlled PUF • PUF in RFID – Identification/authentication [Ranasinghe et al 2004] – Off-line reader authentication using public key cryptography [Tuyls et al 2006]
- Slides: 21