Perimeter Security Firewall IDSIPS UTM application firewall web


Perimeter Security • Firewall, IDS/IPS, UTM, application firewall, web filter, email security, remote access www. danapardaz. net ﺷﺮکﺖ ﺩﺍﻧﺎ پﺮﺩﺍﺯ ﻧﻤﺎیﻨﺪﻩ ﺭﺳﻤی ﻣﺤﺼﻮﻻﺕ 2/30
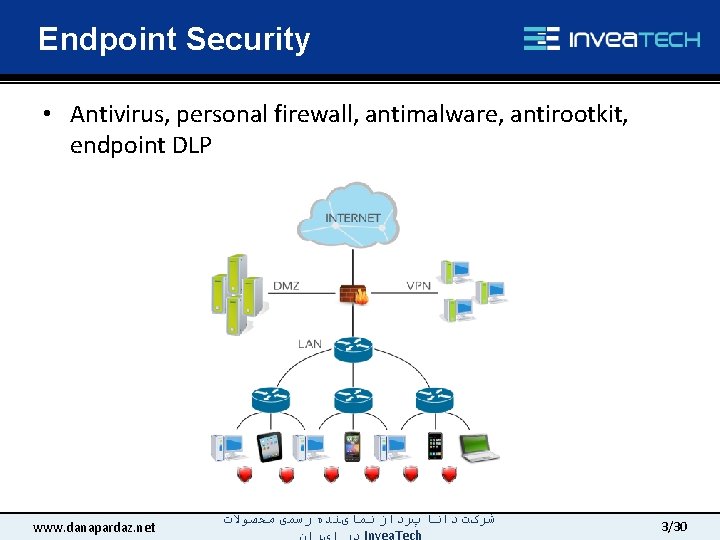
Endpoint Security • Antivirus, personal firewall, antimalware, antirootkit, endpoint DLP www. danapardaz. net ﺷﺮکﺖ ﺩﺍﻧﺎ پﺮﺩﺍﺯ ﻧﻤﺎیﻨﺪﻩ ﺭﺳﻤی ﻣﺤﺼﻮﻻﺕ 3/30
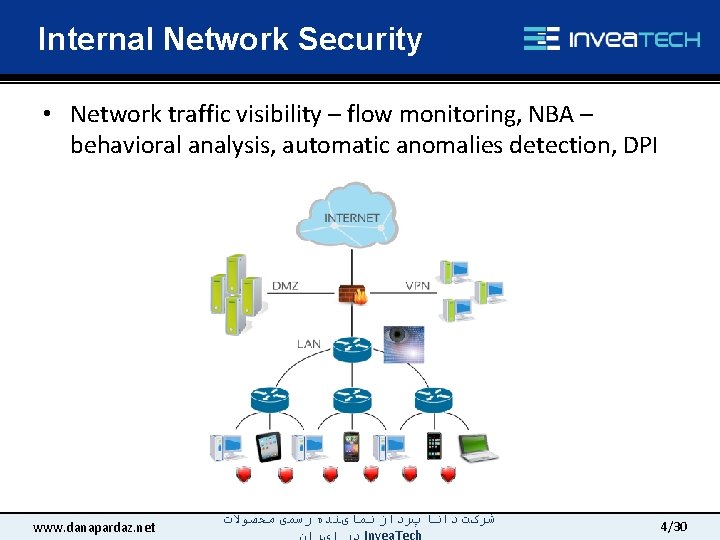
Internal Network Security • Network traffic visibility – flow monitoring, NBA – behavioral analysis, automatic anomalies detection, DPI www. danapardaz. net ﺷﺮکﺖ ﺩﺍﻧﺎ پﺮﺩﺍﺯ ﻧﻤﺎیﻨﺪﻩ ﺭﺳﻤی ﻣﺤﺼﻮﻻﺕ 4/30
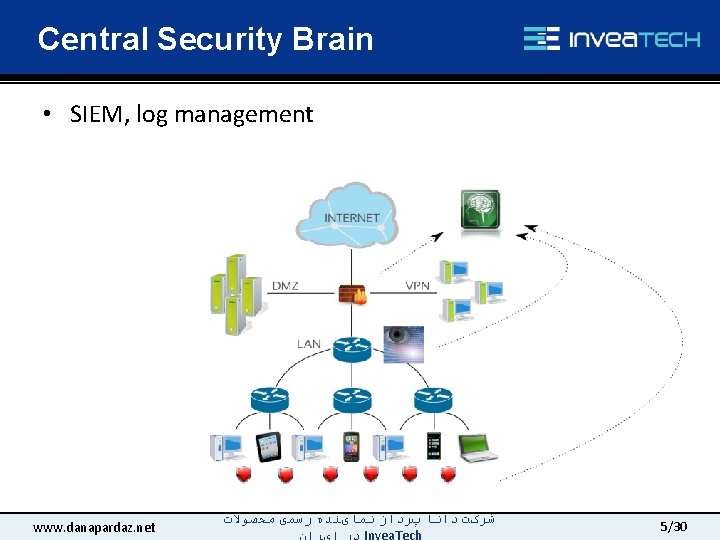
Central Security Brain • SIEM, log management www. danapardaz. net ﺷﺮکﺖ ﺩﺍﻧﺎ پﺮﺩﺍﺯ ﻧﻤﺎیﻨﺪﻩ ﺭﺳﻤی ﻣﺤﺼﻮﻻﺕ 5/30
Summary • All the tools mentioned are very important from a security point of view • Most are aimed at protection from known threats and attackers • That’s why continuous monitoring and detailed information about activities in the network is important q An analogy of physical security of e. g. a server room and cameras, movement detectors www. danapardaz. net ﺷﺮکﺖ ﺩﺍﻧﺎ پﺮﺩﺍﺯ ﻧﻤﺎیﻨﺪﻩ ﺭﺳﻤی ﻣﺤﺼﻮﻻﺕ 6/30
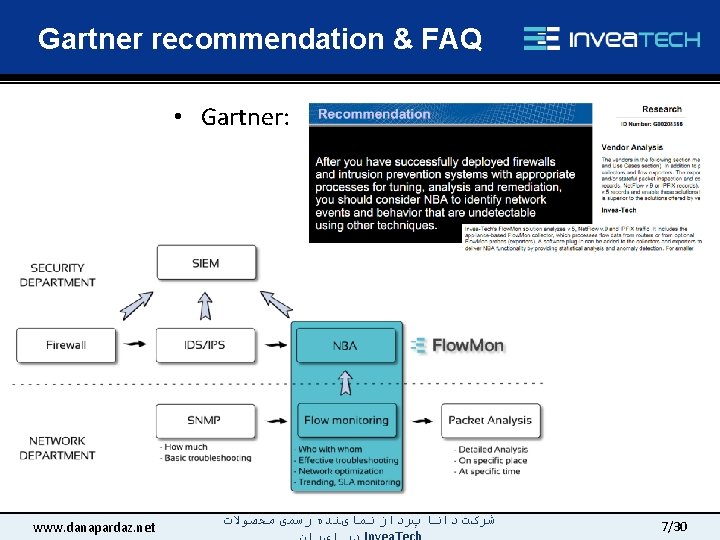
Gartner recommendation & FAQ • Gartner: www. danapardaz. net ﺷﺮکﺖ ﺩﺍﻧﺎ پﺮﺩﺍﺯ ﻧﻤﺎیﻨﺪﻩ ﺭﺳﻤی ﻣﺤﺼﻮﻻﺕ 7/30
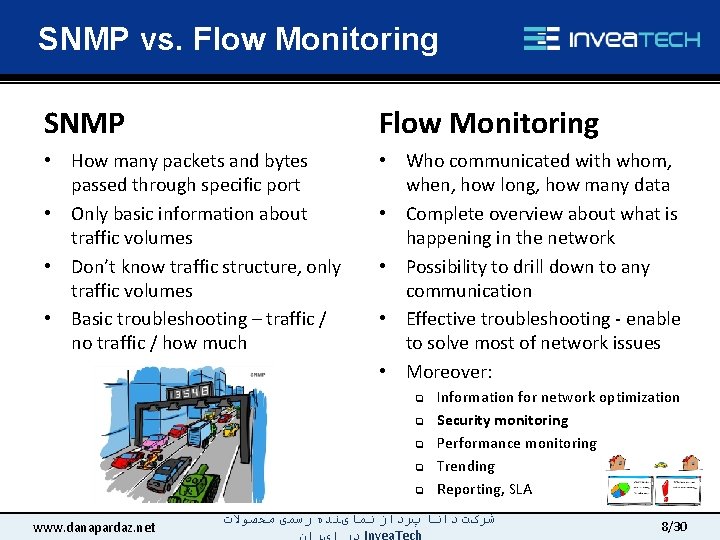
SNMP vs. Flow Monitoring SNMP Flow Monitoring • How many packets and bytes passed through specific port • Only basic information about traffic volumes • Don’t know traffic structure, only traffic volumes • Basic troubleshooting – traffic / no traffic / how much • Who communicated with whom, when, how long, how many data • Complete overview about what is happening in the network • Possibility to drill down to any communication • Effective troubleshooting - enable to solve most of network issues • Moreover: q q q www. danapardaz. net Information for network optimization Security monitoring Performance monitoring Trending Reporting, SLA ﺷﺮکﺖ ﺩﺍﻧﺎ پﺮﺩﺍﺯ ﻧﻤﺎیﻨﺪﻩ ﺭﺳﻤی ﻣﺤﺼﻮﻻﺕ 8/30
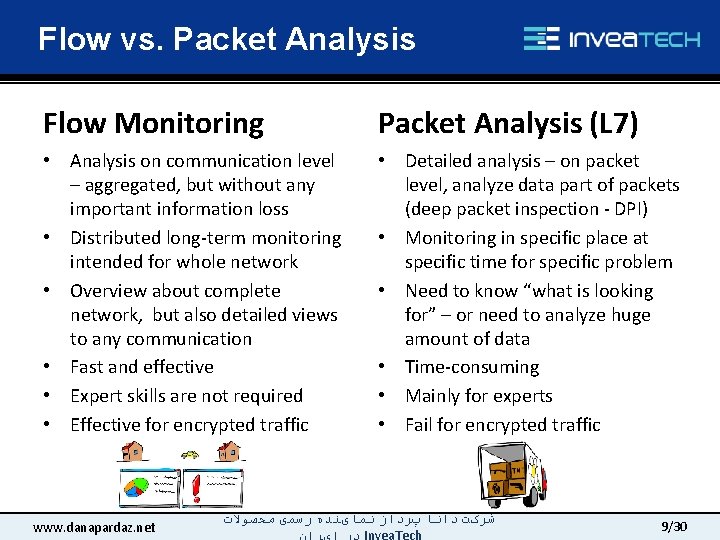
Flow vs. Packet Analysis Flow Monitoring Packet Analysis (L 7) • Analysis on communication level – aggregated, but without any important information loss • Distributed long-term monitoring intended for whole network • Overview about complete network, but also detailed views to any communication • Fast and effective • Expert skills are not required • Effective for encrypted traffic • Detailed analysis – on packet level, analyze data part of packets (deep packet inspection - DPI) • Monitoring in specific place at specific time for specific problem • Need to know “what is looking for” – or need to analyze huge amount of data • Time-consuming • Mainly for experts • Fail for encrypted traffic www. danapardaz. net ﺷﺮکﺖ ﺩﺍﻧﺎ پﺮﺩﺍﺯ ﻧﻤﺎیﻨﺪﻩ ﺭﺳﻤی ﻣﺤﺼﻮﻻﺕ 9/30
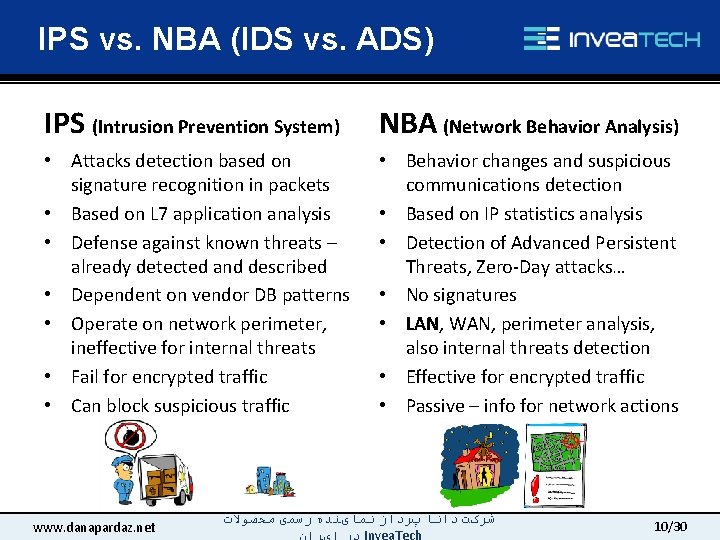
IPS vs. NBA (IDS vs. ADS) IPS (Intrusion Prevention System) NBA (Network Behavior Analysis) • Attacks detection based on signature recognition in packets • Based on L 7 application analysis • Defense against known threats – already detected and described • Dependent on vendor DB patterns • Operate on network perimeter, ineffective for internal threats • Fail for encrypted traffic • Can block suspicious traffic • Behavior changes and suspicious communications detection • Based on IP statistics analysis • Detection of Advanced Persistent Threats, Zero-Day attacks… • No signatures • LAN, WAN, perimeter analysis, also internal threats detection • Effective for encrypted traffic • Passive – info for network actions www. danapardaz. net ﺷﺮکﺖ ﺩﺍﻧﺎ پﺮﺩﺍﺯ ﻧﻤﺎیﻨﺪﻩ ﺭﺳﻤی ﻣﺤﺼﻮﻻﺕ 10/30
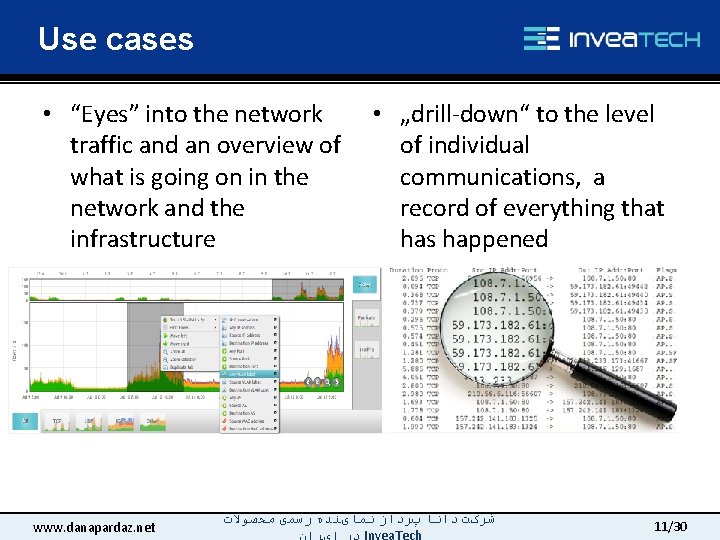
Use cases • “Eyes” into the network traffic and an overview of what is going on in the network and the infrastructure www. danapardaz. net • „drill-down“ to the level of individual communications, a record of everything that has happened ﺷﺮکﺖ ﺩﺍﻧﺎ پﺮﺩﺍﺯ ﻧﻤﺎیﻨﺪﻩ ﺭﺳﻤی ﻣﺤﺼﻮﻻﺕ 11/30
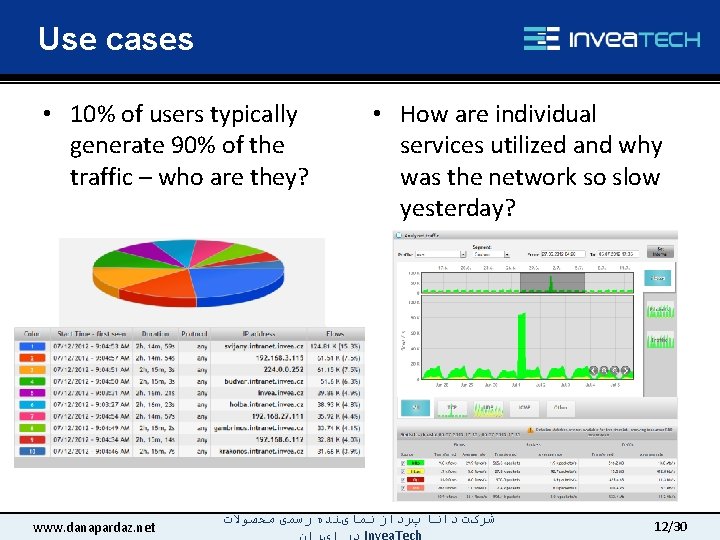
Use cases • 10% of users typically generate 90% of the traffic – who are they? www. danapardaz. net • How are individual services utilized and why was the network so slow yesterday? ﺷﺮکﺖ ﺩﺍﻧﺎ پﺮﺩﺍﺯ ﻧﻤﺎیﻨﺪﻩ ﺭﺳﻤی ﻣﺤﺼﻮﻻﺕ 12/30
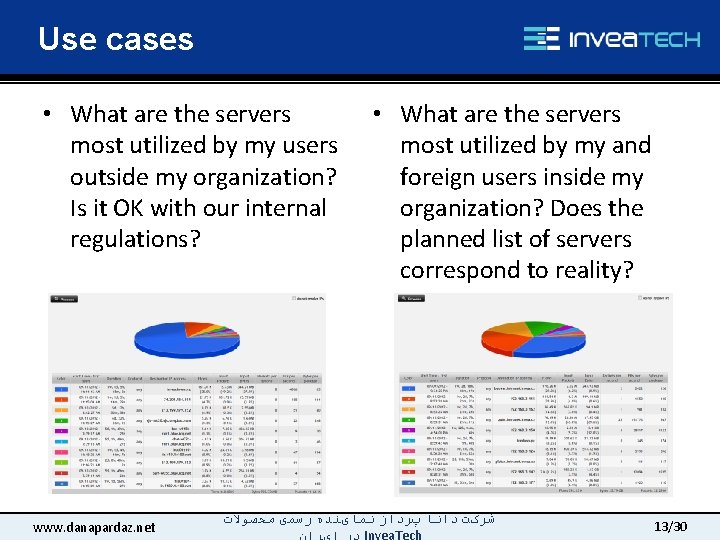
Use cases • What are the servers most utilized by my users outside my organization? Is it OK with our internal regulations? www. danapardaz. net • What are the servers most utilized by my and foreign users inside my organization? Does the planned list of servers correspond to reality? ﺷﺮکﺖ ﺩﺍﻧﺎ پﺮﺩﺍﺯ ﻧﻤﺎیﻨﺪﻩ ﺭﺳﻤی ﻣﺤﺼﻮﻻﺕ 13/30
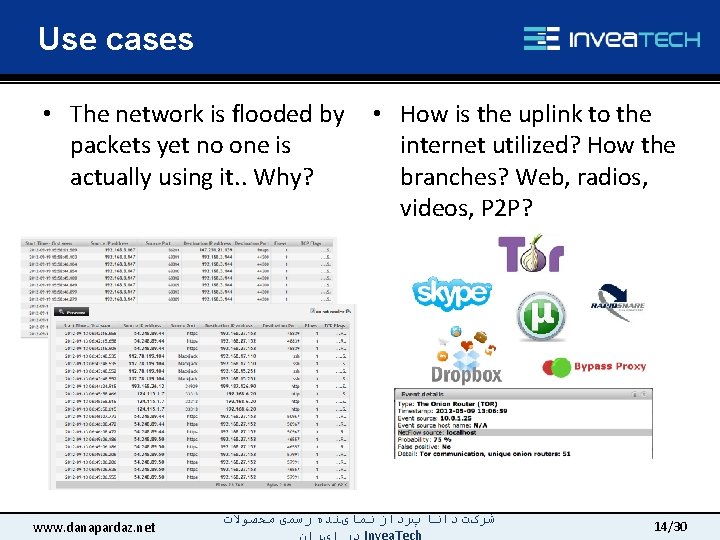
Use cases • The network is flooded by packets yet no one is actually using it. . Why? www. danapardaz. net • How is the uplink to the internet utilized? How the branches? Web, radios, videos, P 2 P? ﺷﺮکﺖ ﺩﺍﻧﺎ پﺮﺩﺍﺯ ﻧﻤﺎیﻨﺪﻩ ﺭﺳﻤی ﻣﺤﺼﻮﻻﺕ 14/30
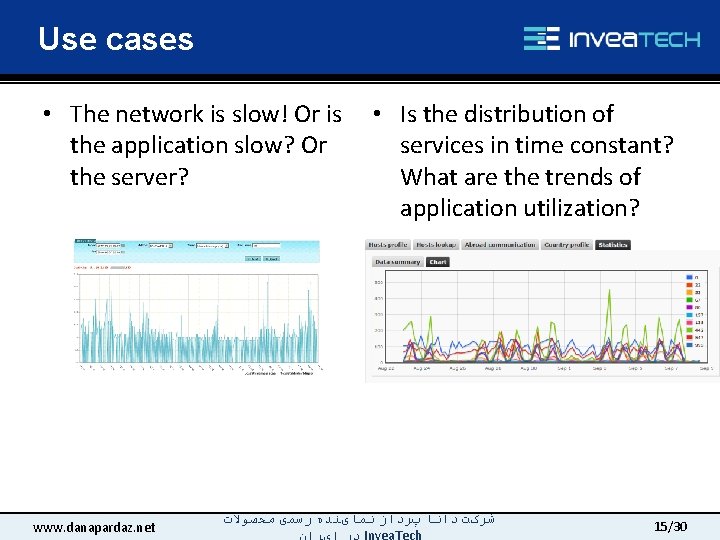
Use cases • The network is slow! Or is the application slow? Or the server? www. danapardaz. net • Is the distribution of services in time constant? What are the trends of application utilization? ﺷﺮکﺖ ﺩﺍﻧﺎ پﺮﺩﺍﺯ ﻧﻤﺎیﻨﺪﻩ ﺭﺳﻤی ﻣﺤﺼﻮﻻﺕ 15/30
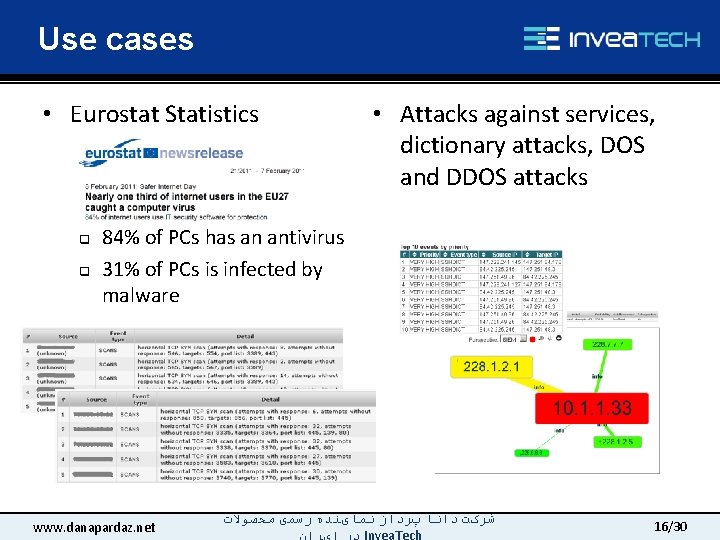
Use cases • Eurostat Statistics q q • Attacks against services, dictionary attacks, DOS and DDOS attacks 84% of PCs has an antivirus 31% of PCs is infected by malware www. danapardaz. net ﺷﺮکﺖ ﺩﺍﻧﺎ پﺮﺩﺍﺯ ﻧﻤﺎیﻨﺪﻩ ﺭﺳﻤی ﻣﺤﺼﻮﻻﺕ 16/30
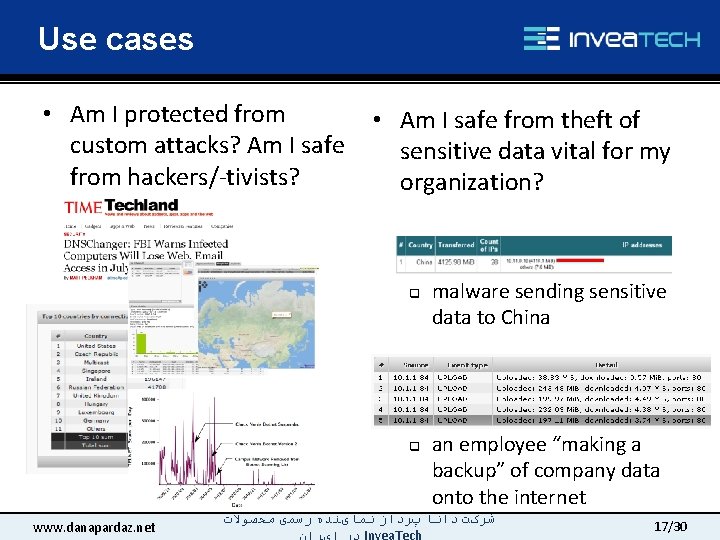
Use cases • Am I protected from custom attacks? Am I safe from hackers/-tivists? • Am I safe from theft of sensitive data vital for my organization? q q www. danapardaz. net malware sending sensitive data to China an employee “making a backup” of company data onto the internet ﺷﺮکﺖ ﺩﺍﻧﺎ پﺮﺩﺍﺯ ﻧﻤﺎیﻨﺪﻩ ﺭﺳﻤی ﻣﺤﺼﻮﻻﺕ 17/30
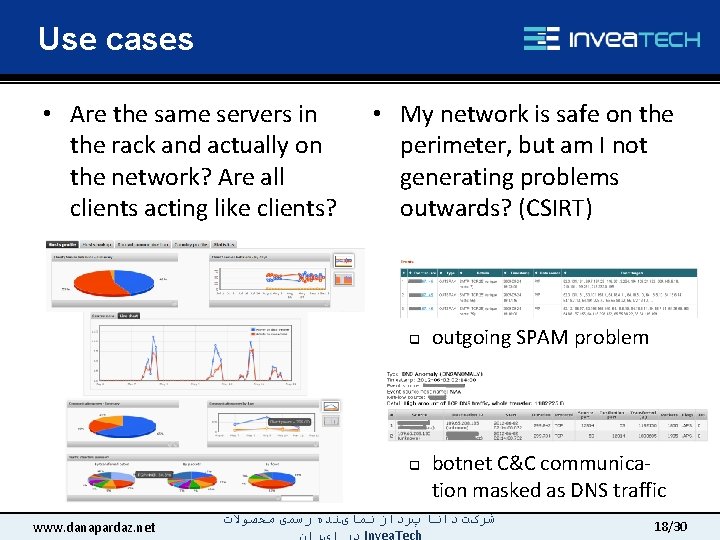
Use cases • Are the same servers in the rack and actually on the network? Are all clients acting like clients? • My network is safe on the perimeter, but am I not generating problems outwards? (CSIRT) q q www. danapardaz. net outgoing SPAM problem botnet C&C communication masked as DNS traffic ﺷﺮکﺖ ﺩﺍﻧﺎ پﺮﺩﺍﺯ ﻧﻤﺎیﻨﺪﻩ ﺭﺳﻤی ﻣﺤﺼﻮﻻﺕ 18/30
Flow monitoring and NBA benefits 1. Flow Monitoring gives the administrator “eyes” – network stops being a blackbox that either works or not 2. Efficient troubleshooting – Decrease of time necessary to solve problems in the network and IT infrastructure by orders of magnitude 3. Complete reporting about actions on the network – TOP services, servers, users 4. Optimization of infrastructure and services 5. Cost savings on Internet connectivity, linking of branches 6. Increase of not only external but mainly internal network security 7. Detection of network scanning, dictionary attacks, computers with malware 8. Revealing of specific and unknown threats - security problems that antivirus, FW, IPS won’t and can’t possibly reveal (there are no signatures) 9. Detection of undesirable user activities such as P 2 P, Skype, IM, storage 10. Effective also for encrypted traffic - trend and future! www. danapardaz. net ﺷﺮکﺖ ﺩﺍﻧﺎ پﺮﺩﺍﺯ ﻧﻤﺎیﻨﺪﻩ ﺭﺳﻤی ﻣﺤﺼﻮﻻﺕ 19/30
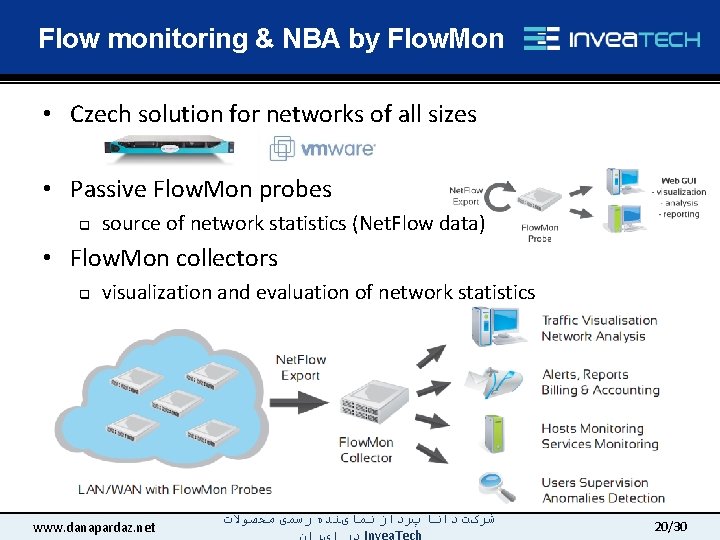
Flow monitoring & NBA by Flow. Mon • Czech solution for networks of all sizes • Passive Flow. Mon probes q source of network statistics (Net. Flow data) • Flow. Mon collectors q visualization and evaluation of network statistics www. danapardaz. net ﺷﺮکﺖ ﺩﺍﻧﺎ پﺮﺩﺍﺯ ﻧﻤﺎیﻨﺪﻩ ﺭﺳﻤی ﻣﺤﺼﻮﻻﺕ 20/30
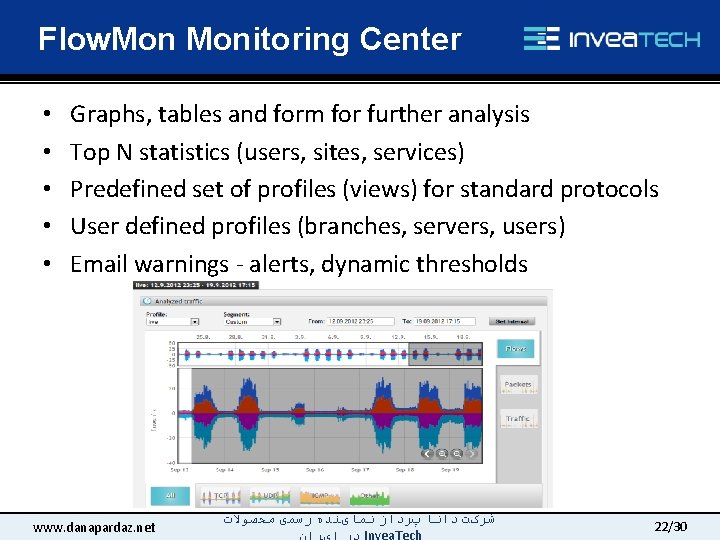
Flow. Monitoring Center • • • Graphs, tables and form for further analysis Top N statistics (users, sites, services) Predefined set of profiles (views) for standard protocols User defined profiles (branches, servers, users) Email warnings - alerts, dynamic thresholds www. danapardaz. net ﺷﺮکﺖ ﺩﺍﻧﺎ پﺮﺩﺍﺯ ﻧﻤﺎیﻨﺪﻩ ﺭﺳﻤی ﻣﺤﺼﻮﻻﺕ 22/30
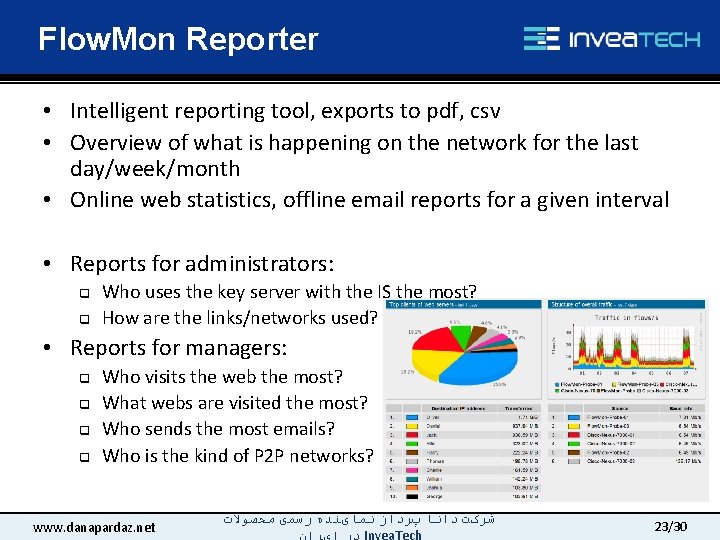
Flow. Mon Reporter • Intelligent reporting tool, exports to pdf, csv • Overview of what is happening on the network for the last day/week/month • Online web statistics, offline email reports for a given interval • Reports for administrators: q q Who uses the key server with the IS the most? How are the links/networks used? • Reports for managers: q q Who visits the web the most? What webs are visited the most? Who sends the most emails? Who is the kind of P 2 P networks? www. danapardaz. net ﺷﺮکﺖ ﺩﺍﻧﺎ پﺮﺩﺍﺯ ﻧﻤﺎیﻨﺪﻩ ﺭﺳﻤی ﻣﺤﺼﻮﻻﺕ 23/30
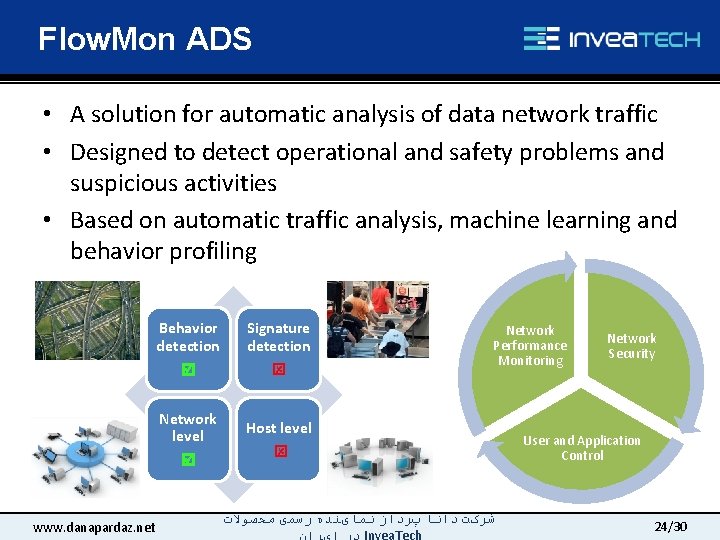
Flow. Mon ADS • A solution for automatic analysis of data network traffic • Designed to detect operational and safety problems and suspicious activities • Based on automatic traffic analysis, machine learning and behavior profiling Behavior detection Signature detection Network level Host level www. danapardaz. net Network Performance Monitoring ﺷﺮکﺖ ﺩﺍﻧﺎ پﺮﺩﺍﺯ ﻧﻤﺎیﻨﺪﻩ ﺭﺳﻤی ﻣﺤﺼﻮﻻﺕ Network Security User and Application Control 24/30
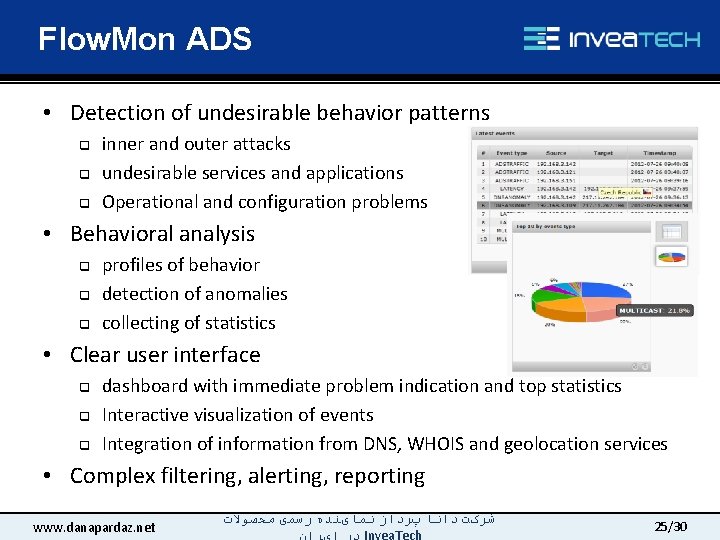
Flow. Mon ADS • Detection of undesirable behavior patterns q q q inner and outer attacks undesirable services and applications Operational and configuration problems • Behavioral analysis q q q profiles of behavior detection of anomalies collecting of statistics • Clear user interface q q q dashboard with immediate problem indication and top statistics Interactive visualization of events Integration of information from DNS, WHOIS and geolocation services • Complex filtering, alerting, reporting www. danapardaz. net ﺷﺮکﺖ ﺩﺍﻧﺎ پﺮﺩﺍﺯ ﻧﻤﺎیﻨﺪﻩ ﺭﺳﻤی ﻣﺤﺼﻮﻻﺕ 25/30
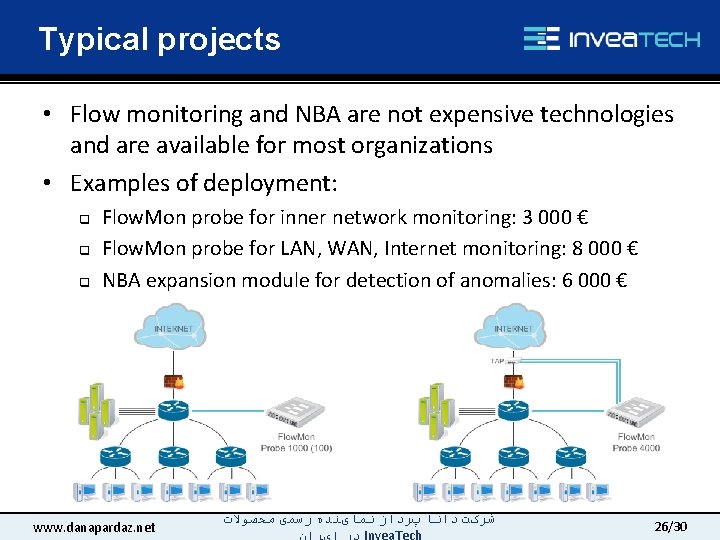
Typical projects • Flow monitoring and NBA are not expensive technologies and are available for most organizations • Examples of deployment: q q q Flow. Mon probe for inner network monitoring: 3 000 € Flow. Mon probe for LAN, WAN, Internet monitoring: 8 000 € NBA expansion module for detection of anomalies: 6 000 € www. danapardaz. net ﺷﺮکﺖ ﺩﺍﻧﺎ پﺮﺩﺍﺯ ﻧﻤﺎیﻨﺪﻩ ﺭﺳﻤی ﻣﺤﺼﻮﻻﺕ 26/30
INVEA-TECH • University spin-off company q q 10 years of development, participation in EU funded projects project Liberouter and programmable hardware, 10 mil Euro invested, creation of world's unique technologies • Company profile q q q Strong academic background: CESNET, MU, VUT Founded 2007 Expansion onto foreign markets since 2010: UK, US, Canada, Germany, Japan and others • Key products: q q q Flow. Mon: network traffic monitoring ADS: detection of anomalies, operational and security issues Flow. Mon + ADS = a complete solution for monitoring and security www. danapardaz. net ﺷﺮکﺖ ﺩﺍﻧﺎ پﺮﺩﺍﺯ ﻧﻤﺎیﻨﺪﻩ ﺭﺳﻤی ﻣﺤﺼﻮﻻﺕ 27/30

Reference • • GEÁNT 2, Federica – monitoring of 7 European backbones CZ Ministry of Defense (via VDI META) Korea Telecom AVG, Aegon CESNET T-Mobile and more. . . www. danapardaz. net ﺷﺮکﺖ ﺩﺍﻧﺎ پﺮﺩﺍﺯ ﻧﻤﺎیﻨﺪﻩ ﺭﺳﻤی ﻣﺤﺼﻮﻻﺕ 28/30
Conclusion & Summary • Flow Monitoring and NBA q q q allow you to see into the network help administer your network more effectively and cheaper elevate the security of your network to a higher level www. danapardaz. net ﺷﺮکﺖ ﺩﺍﻧﺎ پﺮﺩﺍﺯ ﻧﻤﺎیﻨﺪﻩ ﺭﺳﻤی ﻣﺤﺼﻮﻻﺕ 29/30
- Slides: 30