Performance Analysis of Reputationbased Mechanisms for Multihop Wireless
Performance Analysis of Reputation-based Mechanisms for Multi-hop Wireless Networks Fabio Milan Dipartimento di Elettronica Politecnico di Torino Turin, Italy Email: fabio. milan@polito. it March 22, 2006 Juan José Jaramillo and R. Srikant Coordinated Science Laboratory Dept. of Electrical and Computer Engineering University of Illinois at Urbana-Champaign Email: {jjjarami, rsrikant}@uiuc. edu CISS 2006, Princeton, NJ, USA
Outline • • Problem Formulation Cooperation without Collisions Cooperation with Collisions Performance Analysis March 22, 2006 CISS 2006, Princeton, NJ, USA 2
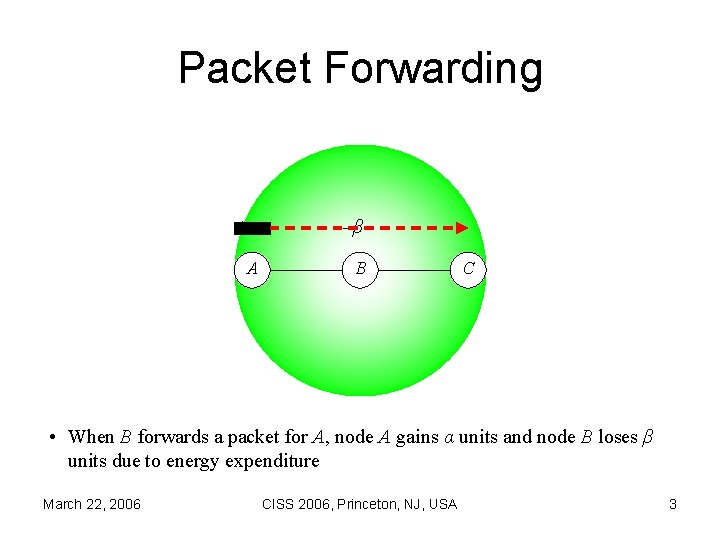
Packet Forwarding +α –β A B C • When B forwards a packet for A, node A gains α units and node B loses β units due to energy expenditure March 22, 2006 CISS 2006, Princeton, NJ, USA 3
Utility • • α is the packet value β is the transmission cost pi is the dropping probability of node i p-i is the dropping probability of the neighbor of node i ui = βpi – αp-i • βpi is the gain of dropping packets from the neighbor • αp-i is the loss for packets being dropped by the neighbor March 22, 2006 CISS 2006, Princeton, NJ, USA 4
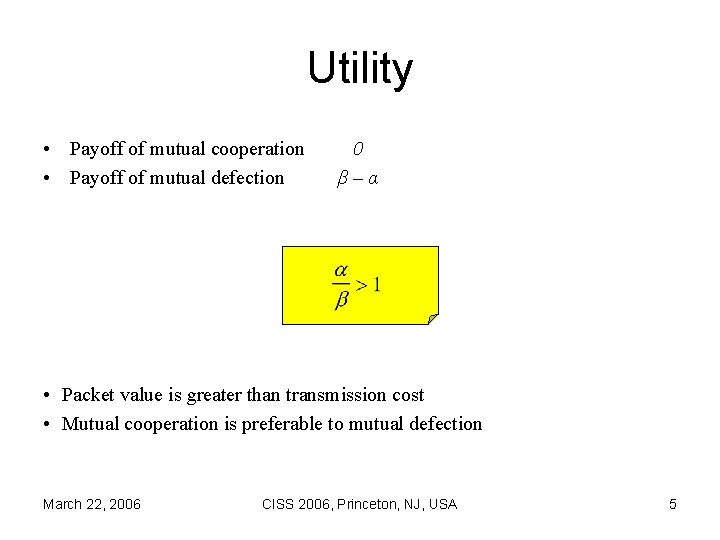
Utility • Payoff of mutual cooperation • Payoff of mutual defection 0 β–α • Packet value is greater than transmission cost • Mutual cooperation is preferable to mutual defection March 22, 2006 CISS 2006, Princeton, NJ, USA 5
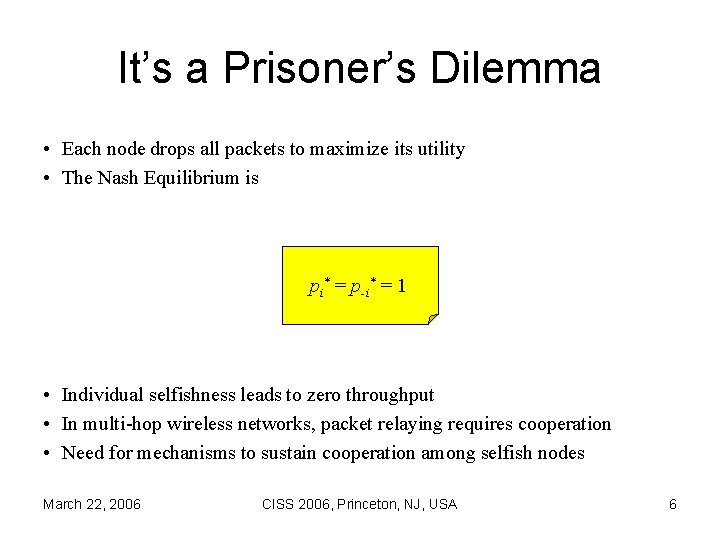
It’s a Prisoner’s Dilemma • Each node drops all packets to maximize its utility • The Nash Equilibrium is pi* = p-i* = 1 • Individual selfishness leads to zero throughput • In multi-hop wireless networks, packet relaying requires cooperation • Need for mechanisms to sustain cooperation among selfish nodes March 22, 2006 CISS 2006, Princeton, NJ, USA 6
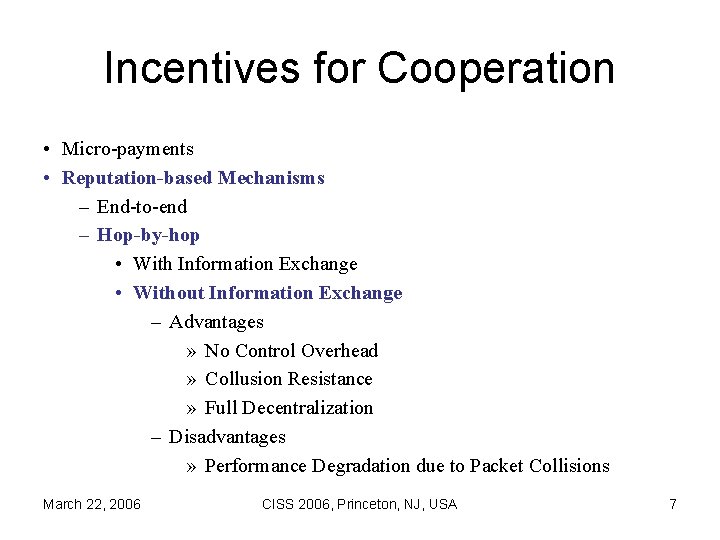
Incentives for Cooperation • Micro-payments • Reputation-based Mechanisms – End-to-end – Hop-by-hop • With Information Exchange • Without Information Exchange – Advantages » No Control Overhead » Collusion Resistance » Full Decentralization – Disadvantages » Performance Degradation due to Packet Collisions March 22, 2006 CISS 2006, Princeton, NJ, USA 7
Outline • • Problem Formulation Cooperation without Collisions Cooperation with Collisions Performance Analysis March 22, 2006 CISS 2006, Princeton, NJ, USA 8
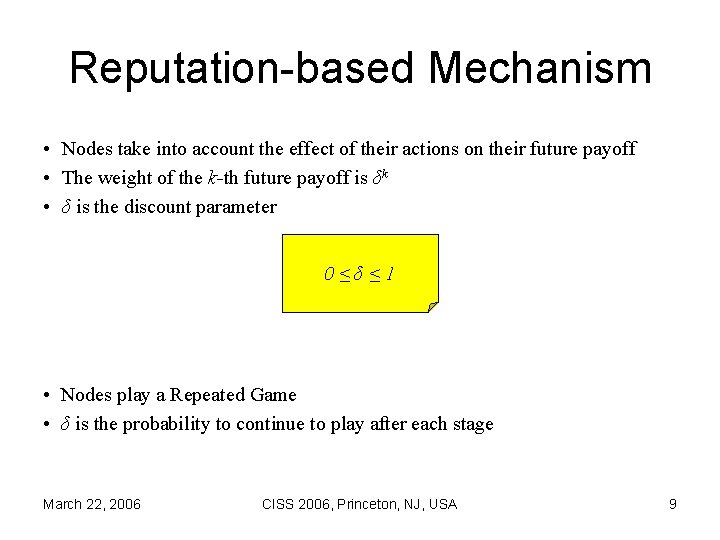
Reputation-based Mechanism • Nodes take into account the effect of their actions on their future payoff • The weight of the k-th future payoff is δk • δ is the discount parameter 0≤δ≤ 1 • Nodes play a Repeated Game • δ is the probability to continue to play after each stage March 22, 2006 CISS 2006, Princeton, NJ, USA 9
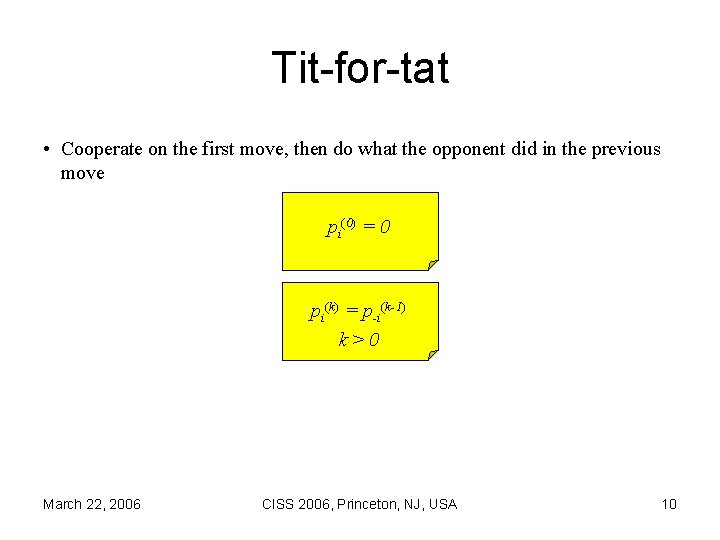
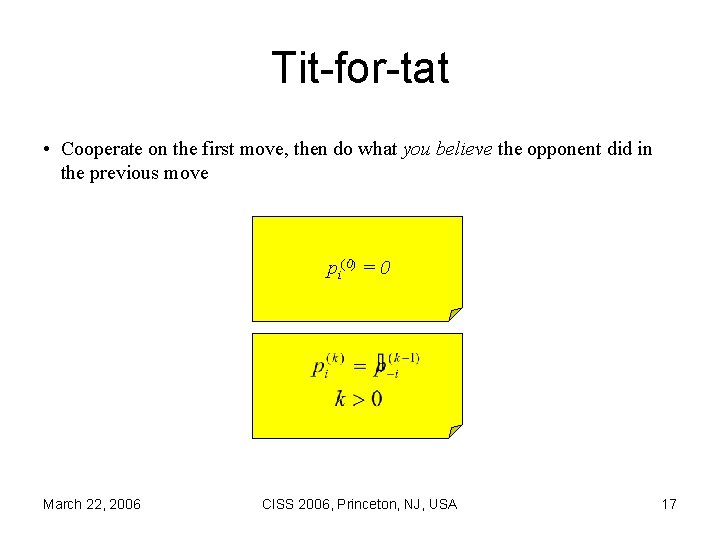
Tit-for-tat • Cooperate on the first move, then do what the opponent did in the previous move pi(0) = 0 pi(k) = p-i(k-1) k>0 March 22, 2006 CISS 2006, Princeton, NJ, USA 10
One-step Deviation • If both nodes cooperate, their payoff is 0. • Assume that node i deviates, by setting a dropping probability p>0 – Node i initially benefits from this deviation – As the neighbor reacts, node i suffers packet losses – Node i reacts to the punishment by punishing its neighbor –… • The discounted payoff of i in case of deviation is a function of α, β, δ and p • If it is not greater than 0, then being the first to defect is not rational March 22, 2006 CISS 2006, Princeton, NJ, USA 11
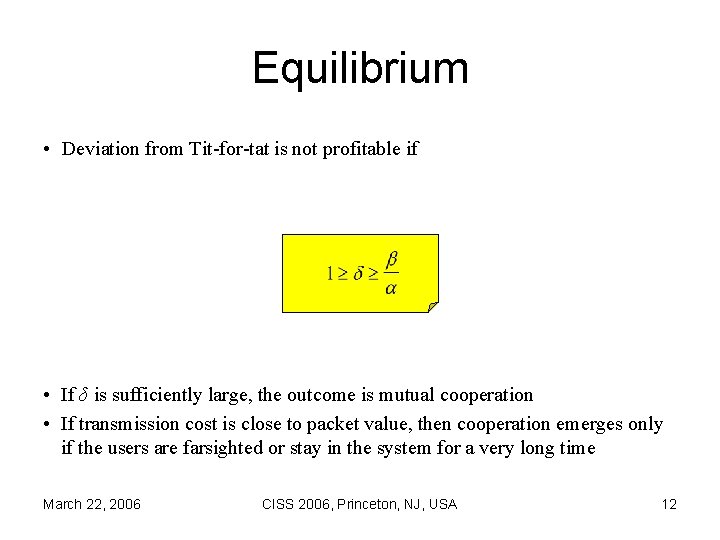
Equilibrium • Deviation from Tit-for-tat is not profitable if • If δ is sufficiently large, the outcome is mutual cooperation • If transmission cost is close to packet value, then cooperation emerges only if the users are farsighted or stay in the system for a very long time March 22, 2006 CISS 2006, Princeton, NJ, USA 12
Outline • • Problem Formulation Cooperation without Collisions Cooperation with Collisions Performance Analysis March 22, 2006 CISS 2006, Princeton, NJ, USA 13
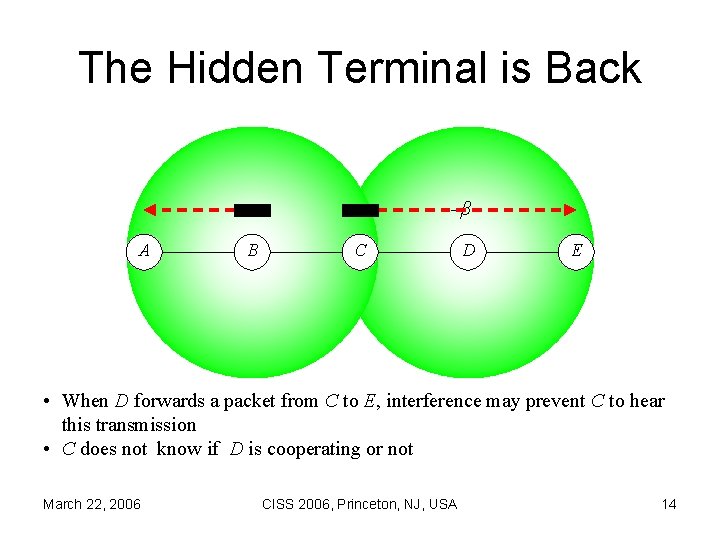
The Hidden Terminal is Back A B –α –β C D E • When D forwards a packet from C to E, interference may prevent C to hear this transmission • C does not know if D is cooperating or not March 22, 2006 CISS 2006, Princeton, NJ, USA 14
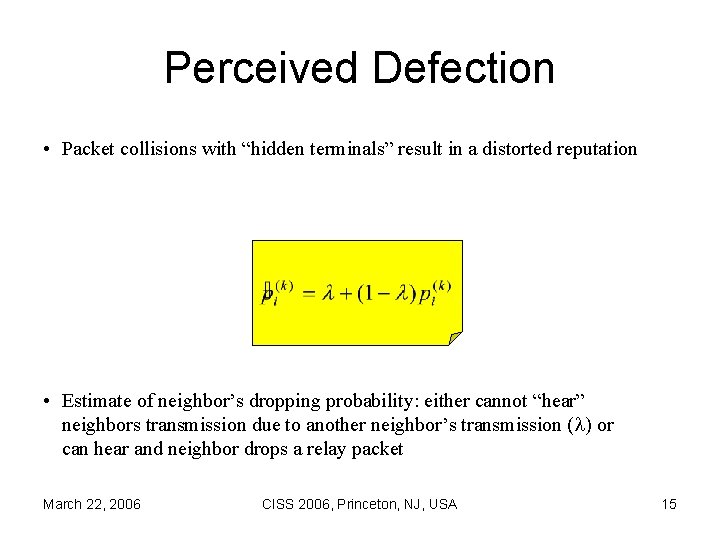
Perceived Defection • Packet collisions with “hidden terminals” result in a distorted reputation • Estimate of neighbor’s dropping probability: either cannot “hear” neighbors transmission due to another neighbor’s transmission ( ) or can hear and neighbor drops a relay packet March 22, 2006 CISS 2006, Princeton, NJ, USA 15
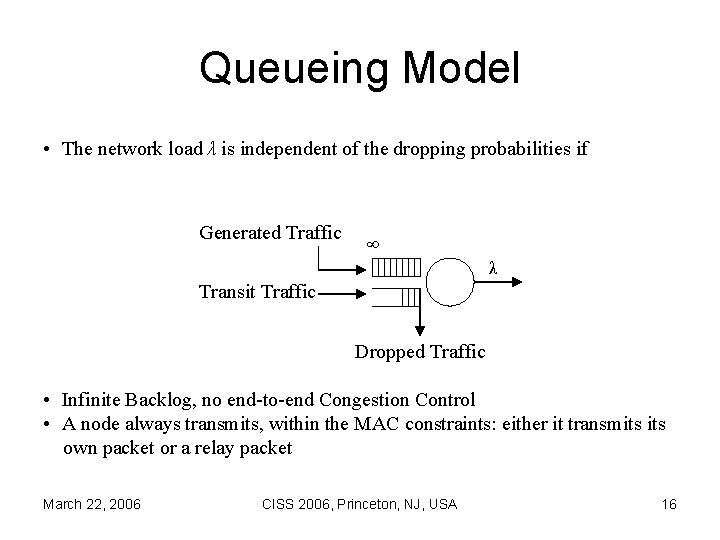
Queueing Model • The network load λ is independent of the dropping probabilities if Generated Traffic ∞ λ Transit Traffic Dropped Traffic • Infinite Backlog, no end-to-end Congestion Control • A node always transmits, within the MAC constraints: either it transmits own packet or a relay packet March 22, 2006 CISS 2006, Princeton, NJ, USA 16
Tit-for-tat • Cooperate on the first move, then do what you believe the opponent did in the previous move pi(0) = 0 March 22, 2006 CISS 2006, Princeton, NJ, USA 17
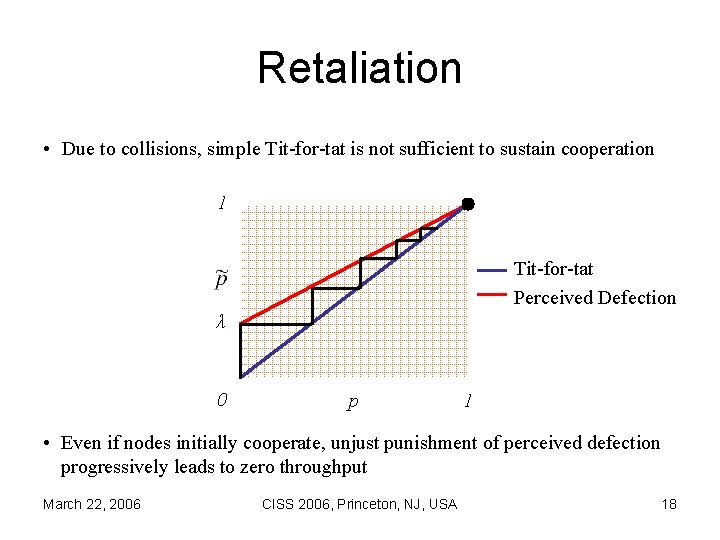
Retaliation • Due to collisions, simple Tit-for-tat is not sufficient to sustain cooperation 1 Tit-for-tat Perceived Defection λ 0 p 1 • Even if nodes initially cooperate, unjust punishment of perceived defection progressively leads to zero throughput March 22, 2006 CISS 2006, Princeton, NJ, USA 18
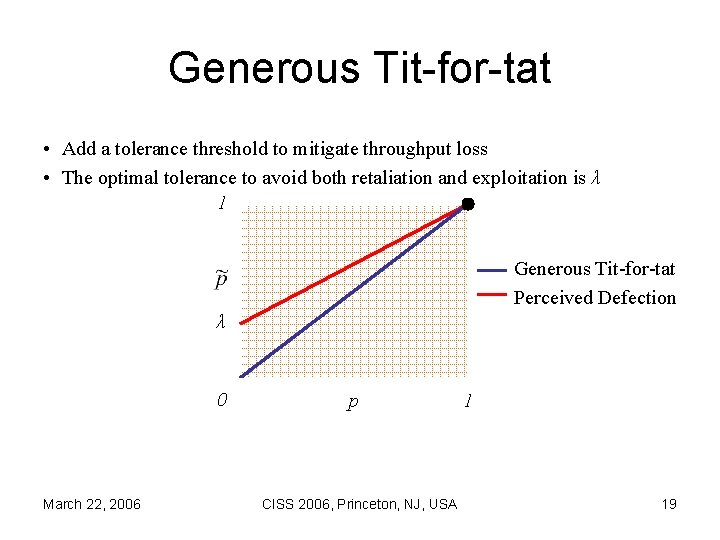
Generous Tit-for-tat • Add a tolerance threshold to mitigate throughput loss • The optimal tolerance to avoid both retaliation and exploitation is λ 1 Generous Tit-for-tat Perceived Defection λ 0 March 22, 2006 p CISS 2006, Princeton, NJ, USA 1 19
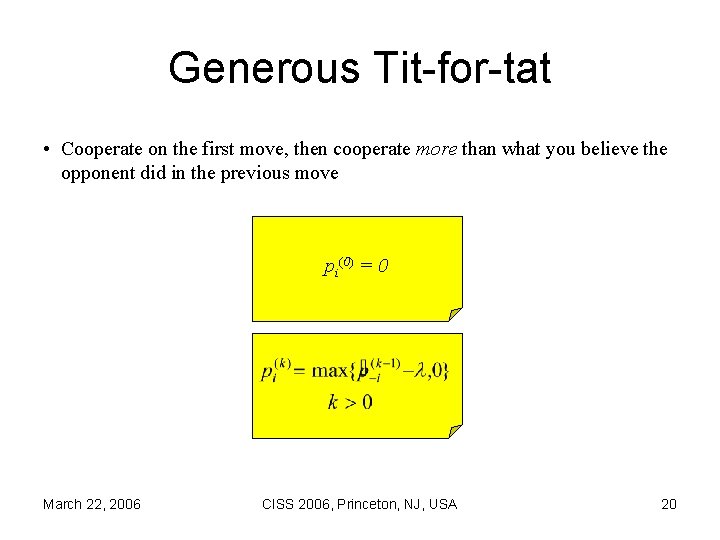
Generous Tit-for-tat • Cooperate on the first move, then cooperate more than what you believe the opponent did in the previous move pi(0) = 0 March 22, 2006 CISS 2006, Princeton, NJ, USA 20
Equilibrium • Deviation from Generous Tit-for-tat is not profitable if • If δ is sufficiently large, the outcome is mutual cooperation • Need an even larger δ now due to imperfect knowledge of neighbor’s actions March 22, 2006 CISS 2006, Princeton, NJ, USA 21
Outline • • Problem Formulation Cooperation without Collisions Cooperation with Collisions Performance Analysis March 22, 2006 CISS 2006, Princeton, NJ, USA 22
Game Parameters • λ is a measure of the network load, if every node transmits at the same rate • δ is a measure of the session length – If a session involves a great number of packets, it is reasonable to assume δ → 1 • α is a measure of the information contained in a packet, with respect to the overall information flow transferred from source to destination – For a multimedia stream source, tolerant to packet losses, the packet value is small. For a file transfer source, the packet value is high. • β is a measure of the energy spent to transmit a packet, with respect to the total energy available to the node – For a terminal connected to the AC power, the transmission cost is low. For a terminal running out of battery, the transmission cost is high. March 22, 2006 CISS 2006, Princeton, NJ, USA 23
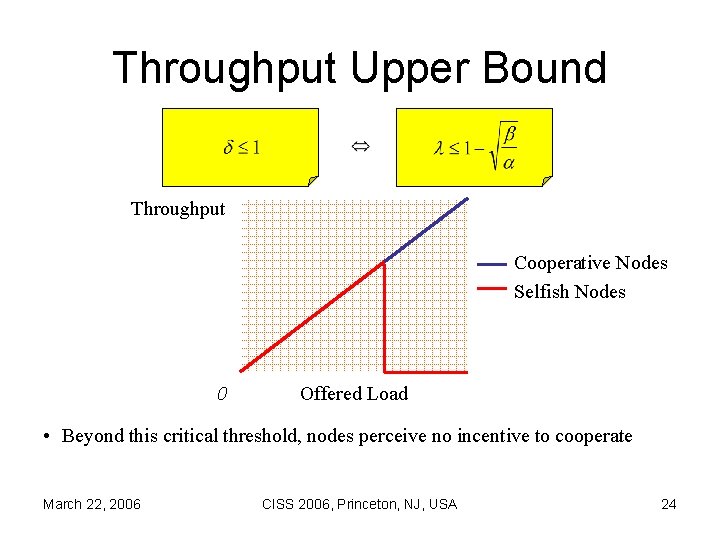
Throughput Upper Bound Throughput Cooperative Nodes Selfish Nodes 0 Offered Load • Beyond this critical threshold, nodes perceive no incentive to cooperate March 22, 2006 CISS 2006, Princeton, NJ, USA 24
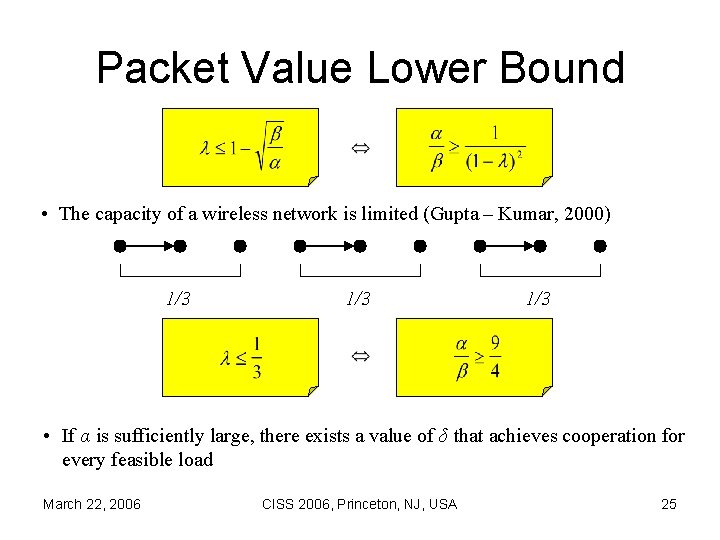
Packet Value Lower Bound • The capacity of a wireless network is limited (Gupta – Kumar, 2000) 1/3 1/3 • If α is sufficiently large, there exists a value of δ that achieves cooperation for every feasible load March 22, 2006 CISS 2006, Princeton, NJ, USA 25
Conclusion • Developed a game-theoretic framework to evaluate the performance of hopby-hop reputation-based mechanisms for multi-hop wireless network, in presence of packet collisions with “hidden terminals” • Explored the conditions for the emergence of cooperation in a network of selfish users, in terms of network load, session length, application type and energy constraints • Ongoing work: How does the network topology affects the conditions for the emergence of cooperation? • Ongoing work: Simulation experiments to study how the externalities introduced by an end-to-end congestion control affect the stability of the mechanism • As for now, our model suggests that if nodes use Skype™ while running out of battery, then they are unlikely to cooperate… March 22, 2006 CISS 2006, Princeton, NJ, USA 26
Thank You! March 22, 2006 CISS 2006, Princeton, NJ, USA 27
- Slides: 27