Penetration Test Debrief Ted Vera Mark Trynor November
Penetration Test Debrief Ted Vera & Mark Trynor November 30, 2010 Confidential and Proprietary Gamers First Information
Agenda • Pen Test Review • Recommendations Confidential and Proprietary Gamers First Information
Overview • During the test we enumerated 302 hosts running 1174 services on the target netblocks as discovered by nmap. • Nessus identified 346 vulnerabilities broken out as follows: 3 High, 6 Medium, and the remainder Low severity. • Of these, 0 were successfully compromised and 1 password was obtained (anonymous ftp server). Confidential and Proprietary Gamers First Information
Pen Test Review: Day 1 • Kick-off Meeting • Reviewed customer ROE • Installed pen test tools on attack VMs • Performed automated port and vulnerability scans against target systems Confidential and Proprietary Gamers First Information
Pen Test Review: Day 2 • Started comprehensive Nessus scan against the target IP addresses. Nessus is a vulnerabilityscanning program that targets remote access vulnerabilities, misconfigurations, default passwords, and utilizes mangled packets for possible Denial of Service (Do. S) attacks. • Identified one high-risk vulnerability and relayed information to Phil: Microsoft IIS Web. Dav ntdll. dll Remote Overflow (MS 03 -007) Confidential and Proprietary Gamers First Information
Pen Test Review: Day 3 • Performed automated attacks against enumerated hosts/services using Metasploit with over 900 exploit modules. • Completed brute-force attacks against open authentication services. • Identified one anonymous ftp user account. • Completed automated cross-site-scripting attacks against all http servers. Confidential and Proprietary Gamers First Information
Pen Test Review: Day 3 • Brute-force attacks against web login pages are currently underway. • Rescanning ports based on Chris's findings. Scanning is still underway. • Performed manual custom XSS attacks against four HTTP servers. • Performed automated cross-site scripting attacks using XSSer (Table 6. XSSer Output). Cross Site Scripting (XSS) allows code injection by bypassing web browser client-side security measures. Confidential and Proprietary Gamers First Information
Pen Test Review: Day 4 • Manually verified numerous Nessus false positives. • Ran Nikto web application scanner. Nikto is a web application scanner that checks for over 9000 potentially dangerous files/CGIs, version specific problems, and server configuration issues. Confidential and Proprietary Gamers First Information
Pen Test Review: Day 5 • Day 5 of the test focused on manually validating false positives reported by automated tools, running automated attack tools, and performing custom exploit development and attacks. Confidential and Proprietary Gamers First Information
Pen Test Review: Day 6 -10 • Day 6 -10 consisted of running intensive nmap port scan of target netblocks. Identified numerous additional ports/services and updated excel spreadsheet with results. Compiled final reports and presentation. Confidential and Proprietary Gamers First Information
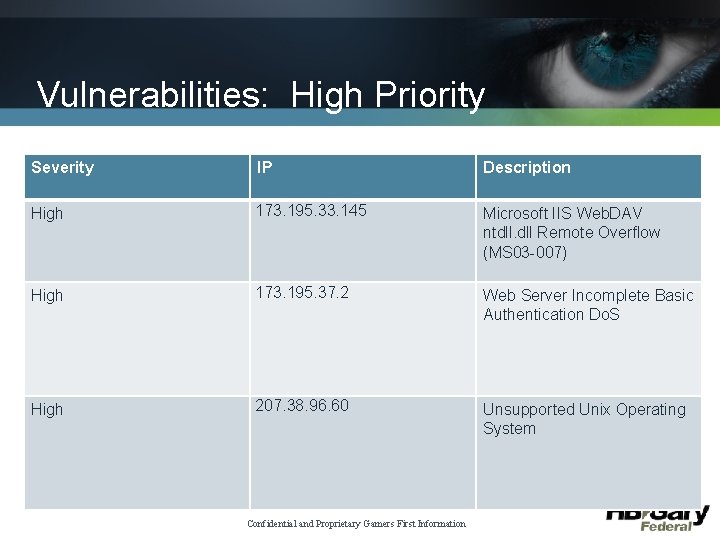
Vulnerabilities: High Priority Severity IP Description High 173. 195. 33. 145 Microsoft IIS Web. DAV ntdll. dll Remote Overflow (MS 03 -007) High 173. 195. 37. 2 Web Server Incomplete Basic Authentication Do. S High 207. 38. 96. 60 Unsupported Unix Operating System Confidential and Proprietary Gamers First Information
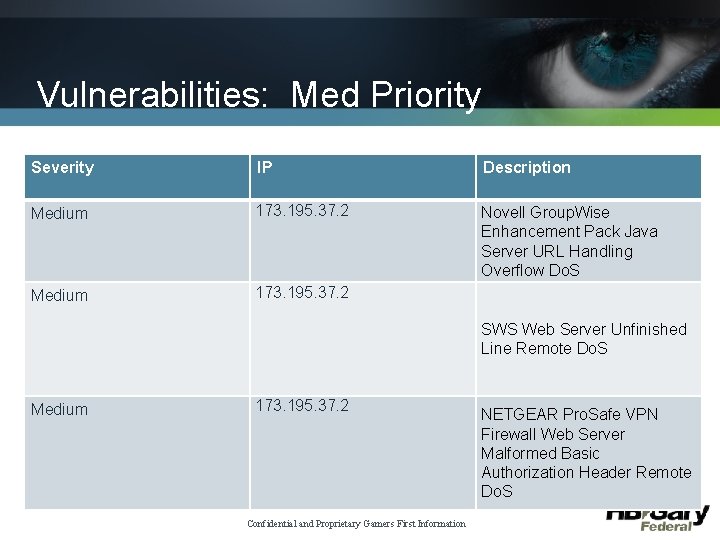
Vulnerabilities: Med Priority Severity IP Description Medium 173. 195. 37. 2 Novell Group. Wise Enhancement Pack Java Server URL Handling Overflow Do. S Medium 173. 195. 37. 2 SWS Web Server Unfinished Line Remote Do. S Medium 173. 195. 37. 2 Confidential and Proprietary Gamers First Information NETGEAR Pro. Safe VPN Firewall Web Server Malformed Basic Authorization Header Remote Do. S
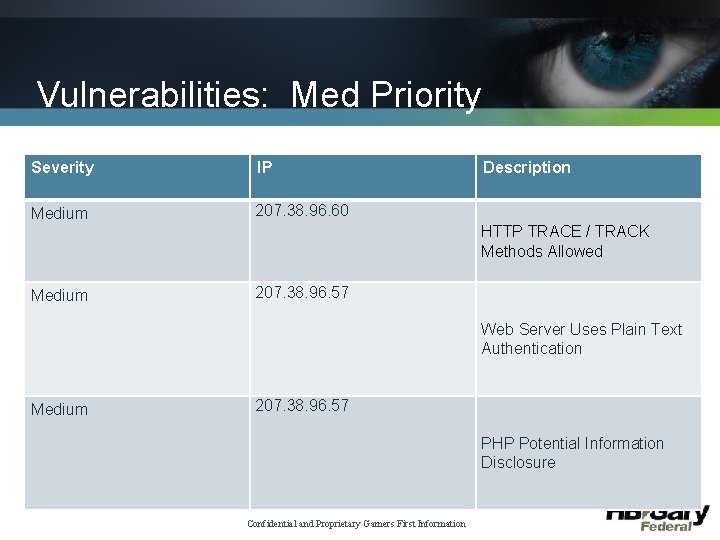
Vulnerabilities: Med Priority Severity IP Medium 207. 38. 96. 60 Description HTTP TRACE / TRACK Methods Allowed Medium 207. 38. 96. 57 Web Server Uses Plain Text Authentication Medium 207. 38. 96. 57 PHP Potential Information Disclosure Confidential and Proprietary Gamers First Information
Recommendations: Manually Verify Medium & High Severity Vulnerabilities Disable Unnecessary Services Enforce strong user passwords • Ensure passwords at least 8 characters in length, use a combination of uppercase and lowercase letters (Aa–Zz), numbers (0– 9), and symbols ( @ # $ % ^ & * ( ) _ + | ~ - = { } [ ] : ; < > ? , . /). • To prevent injection attacks, do not allow passwords to use symbols (back slash) or ' ” (quotes). Patch Management • Install operating system and application patches Confidential and Proprietary Gamers First Information in a timely manner.
- Slides: 14