PASSWORD SECURITY By Cheragh Shah Qusai Rehab Did
PASSWORD SECURITY By: Cheragh Shah Qusai Rehab
Did you know? Most common symbols used are —~@#$%&? Definition of a Password 1 According to Merriam-Webster, a password is “a secret series of numbers or letters that allows you to use a computer system. ” Referencing this, a password can mean anything; numbers, letters, figures, signs A password is needed for multiple reasons; it can be used for security in your house, or while you are playing around with social media. A password can also be used to stop hackers or “predators” from appearing and stealing your identity Maintaining a good password is a must; it is needed for a number of reasons, but the most crucial is for security of identity
2 How to Create a Good Password According to the Microsoft official website, there are multiple ways in creating a good password. These tips include: No personal information, like your name, your address or your family members. Interesting fact: 66% of people online utilize only 1 or 2 passwords for all of their accounts. At least eight letters long (Microsoft) Is something you can easily remember Write it down on a note pad DO NOT share your passwords with anyone at anytime. https: //www. youtube. com/watch? v=0 RCs. HJf. HL_4
Other Tips Organizations Should Implement 3 Organizations should have a policy where they keep a keen eye on all the users. Such examples include making sure everyone in the company signs a memo where they make sure to keep these password tips. Make sure to keep all of the passwords in the file of the lead businessman, so if a worker forgets, they can access it through these files. Any form of hacking will be severely punished. Punishments include termination of their jobs, suspensions and even identifying the police.
4 The Password Pirate’s “Top 3” techniques 1. Shoulder surfing By peering over a shoulder using readily available Web cameras, ‘password pirates’ can easily track the sequence of keystrokes used by the victim to log in 2. Guesswork and dictionary searches People usually choose passwords that are fairly obvious, such as their date of birth, mother’s maiden name, partner’s name or their pet’s name 3. Keyboard tapping This technique works by infecting a PC with ‘remote control’ agent software such as Net. Bus, Back Orifice or PC Anywhere. These allow the hacker to take control of the user’s machine remotely, across the LAN or WAN enabling them to capture every keystroke that the user makes on his or her Pc.
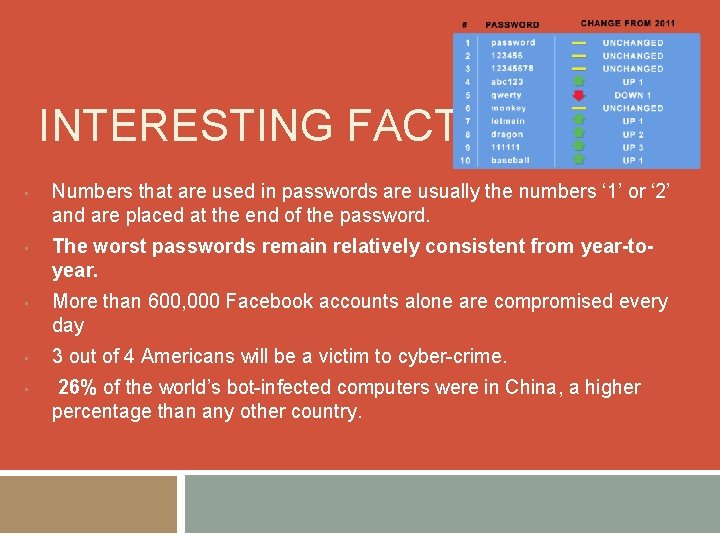
INTERESTING FACTS • • • Numbers that are used in passwords are usually the numbers ‘ 1’ or ‘ 2’ and are placed at the end of the password. The worst passwords remain relatively consistent from year-toyear. More than 600, 000 Facebook accounts alone are compromised every day 3 out of 4 Americans will be a victim to cyber-crime. 26% of the world’s bot-infected computers were in China, a higher percentage than any other country.
- Slides: 6