PART VII Security Mc GrawHill The Mc GrawHill

- Slides: 31

PART VII Security Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
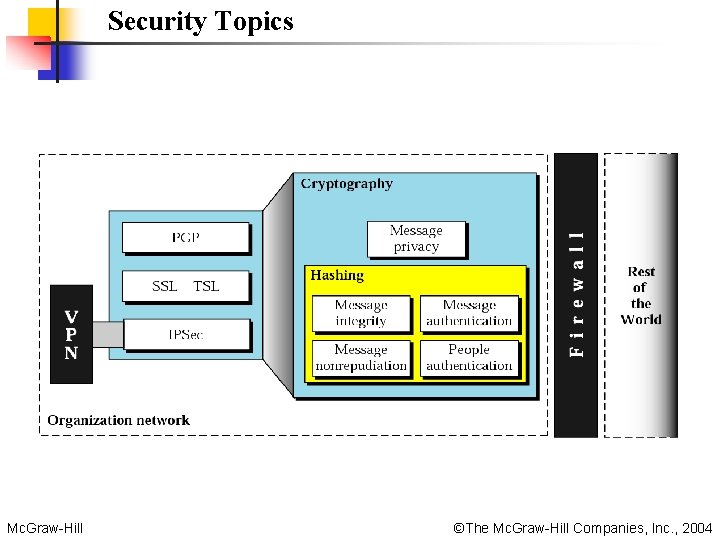
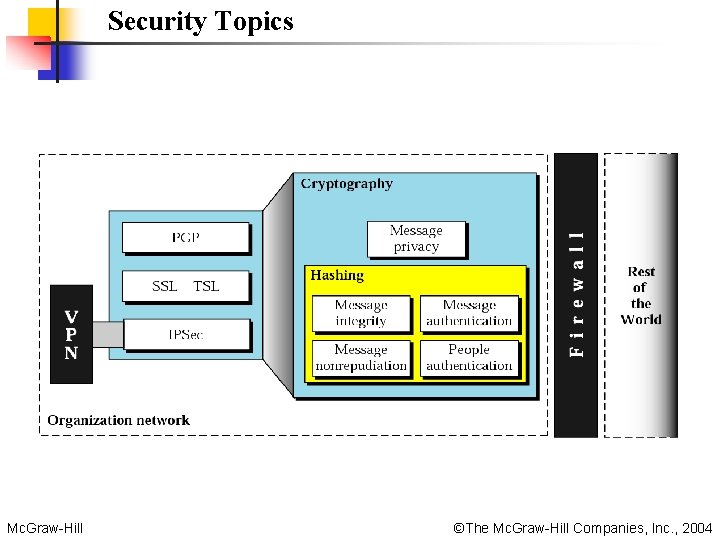
Security Topics Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
Chapters Chapter 29 Cryptography Chapter 30 Message Authentication, User Authentication, and Key Management Chapter 31 Security Protocols in The Internet Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
Chapter 29 Cryptography Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
29. 1 Introduction to Cryptography Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
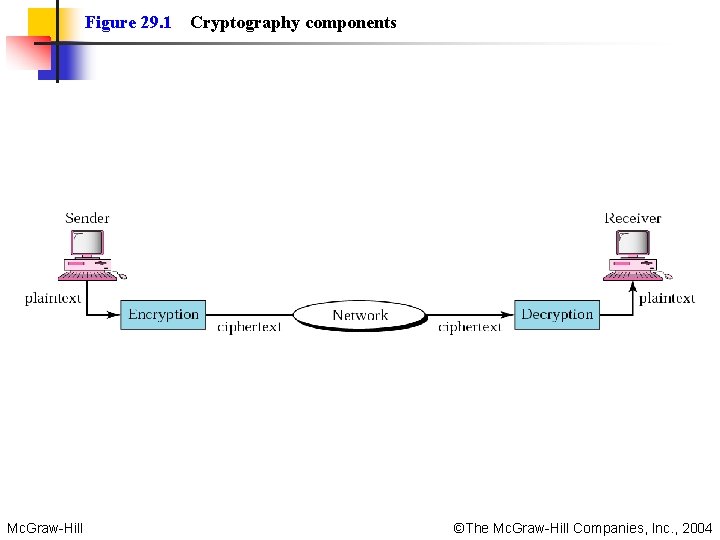
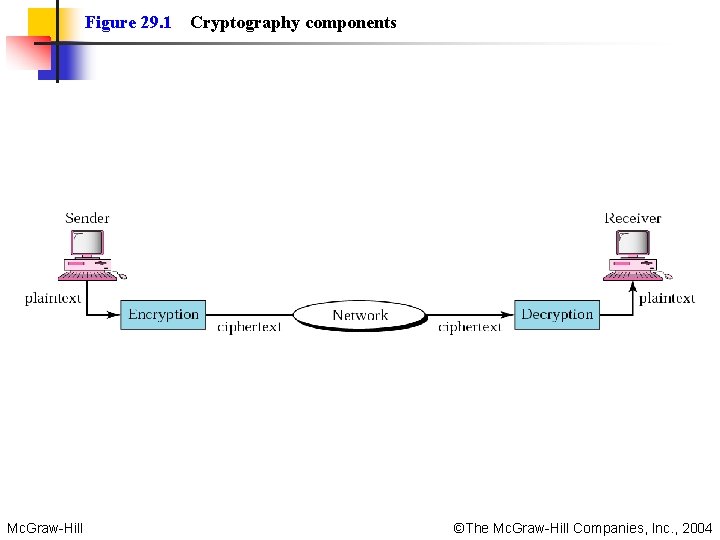
Figure 29. 1 Mc. Graw-Hill Cryptography components ©The Mc. Graw-Hill Companies, Inc. , 2004
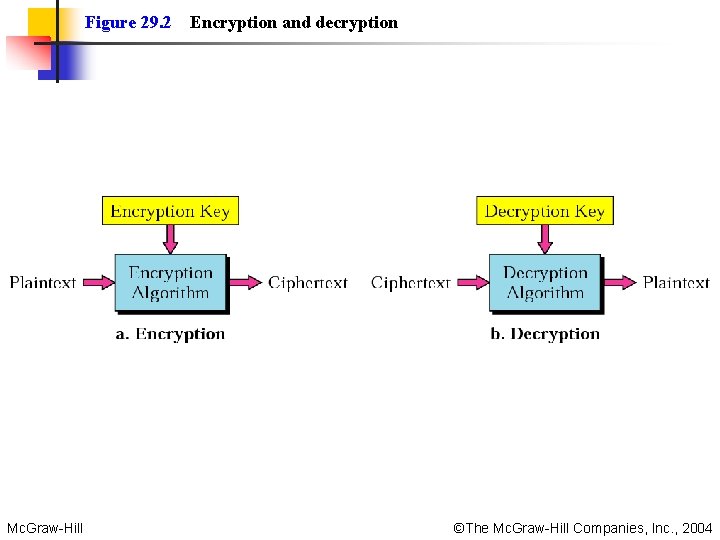
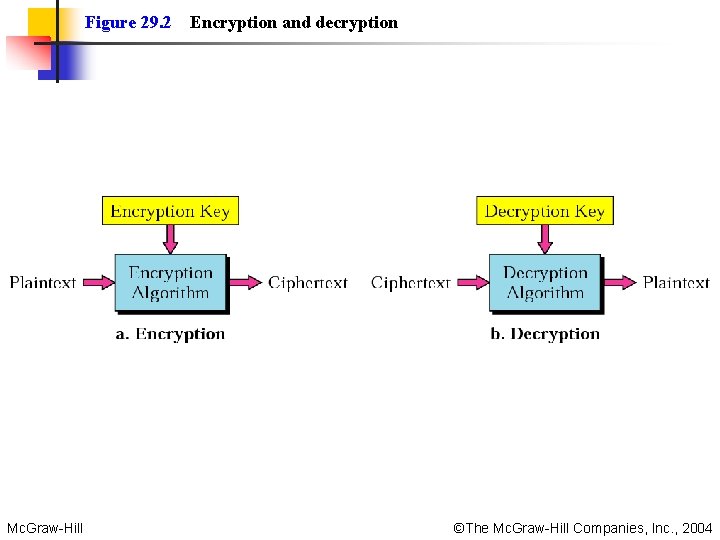
Figure 29. 2 Mc. Graw-Hill Encryption and decryption ©The Mc. Graw-Hill Companies, Inc. , 2004
Note: In cryptography, the encryption/decryption algorithms are public; the keys are secret. Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
29. 2 Symmetric-Key Cryptography Traditional Cipher Block Cipher Operation Modes Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
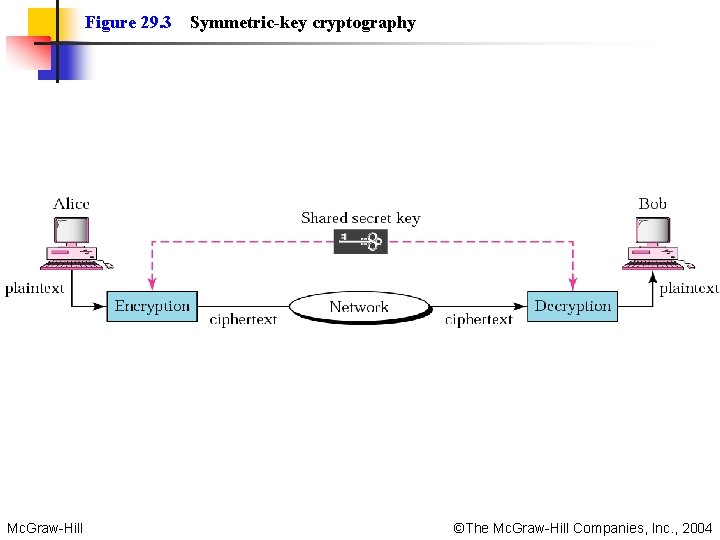
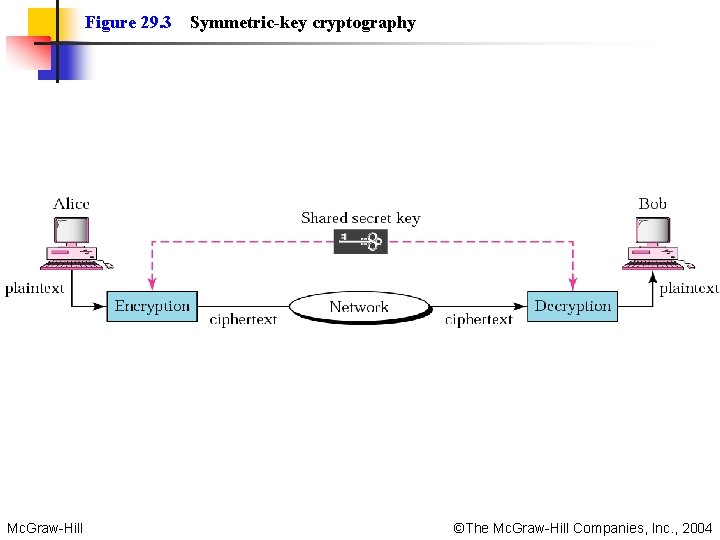
Figure 29. 3 Mc. Graw-Hill Symmetric-key cryptography ©The Mc. Graw-Hill Companies, Inc. , 2004
Note: In symmetric-key cryptography, the same key is used by the sender (for encryption) and the receiver (for decryption). The key is shared. Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
Note: In symmetric-key cryptography, the same key is used in both directions. Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
Note: Symmetric-key cryptography is often used for long messages. Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
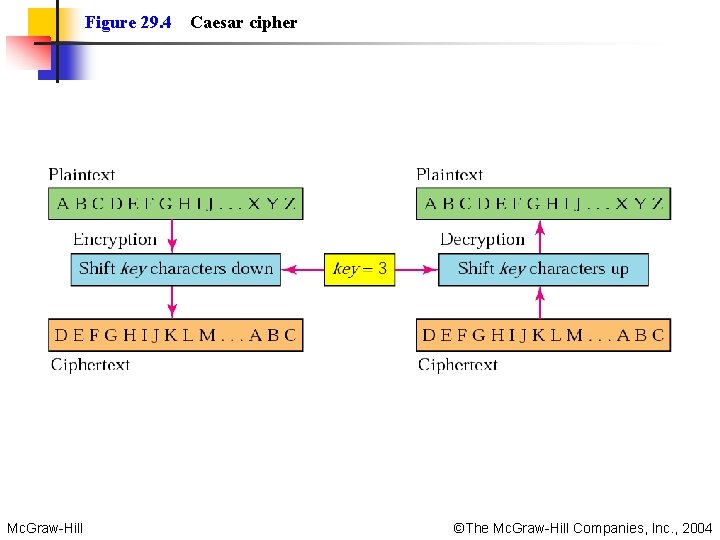
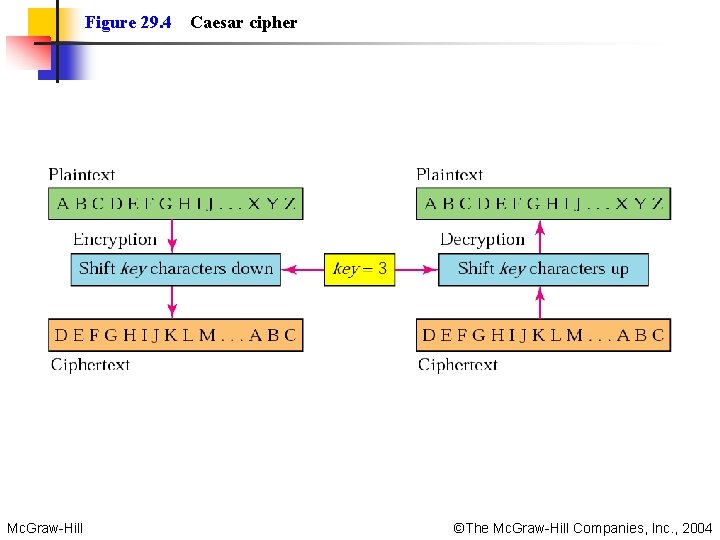
Figure 29. 4 Mc. Graw-Hill Caesar cipher ©The Mc. Graw-Hill Companies, Inc. , 2004
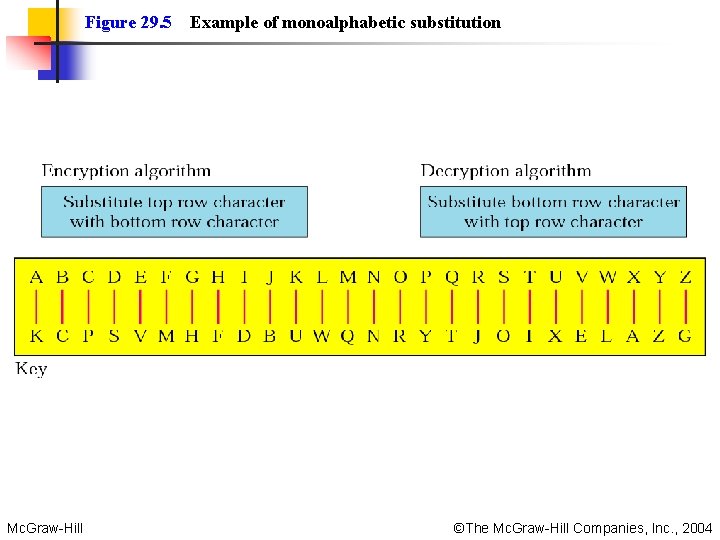
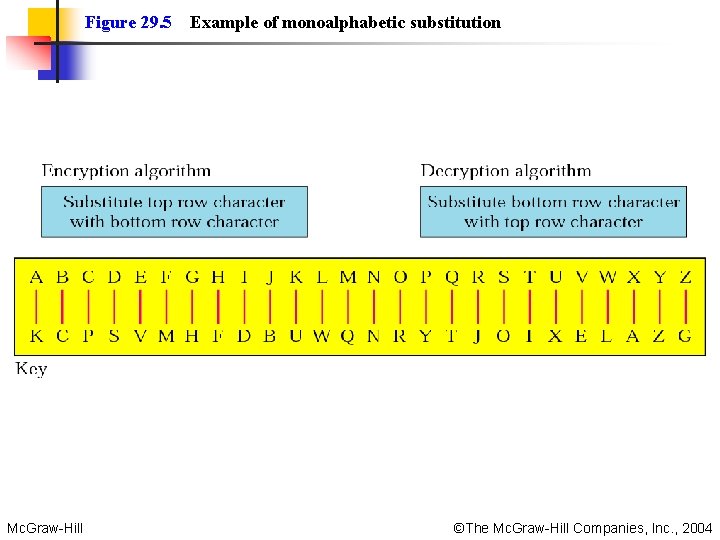
Figure 29. 5 Mc. Graw-Hill Example of monoalphabetic substitution ©The Mc. Graw-Hill Companies, Inc. , 2004
Note: In monoalphabetic substitution, the relationship between a character in the plaintext to the character in the ciphertext is always one-to-one. Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
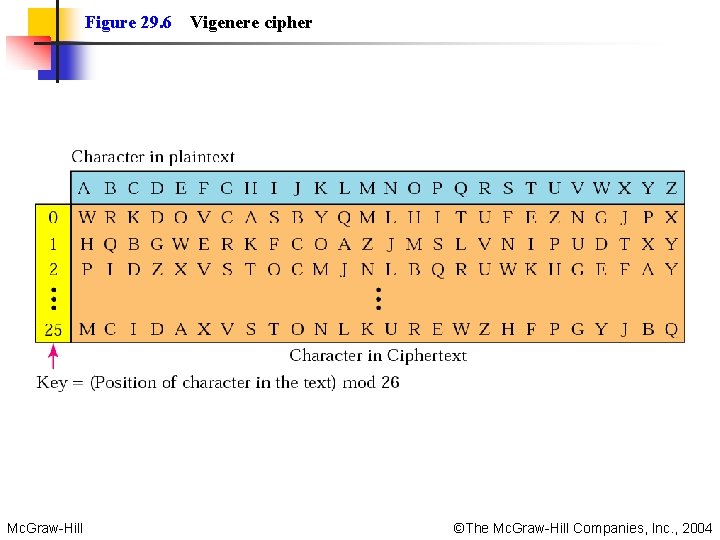
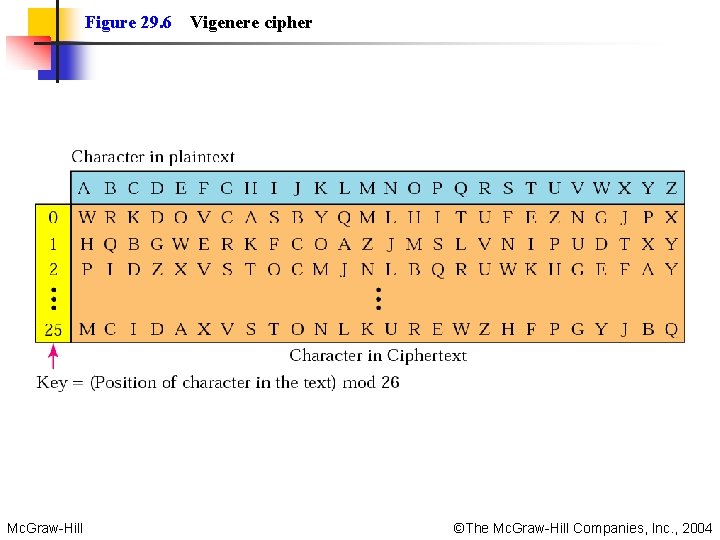
Figure 29. 6 Mc. Graw-Hill Vigenere cipher ©The Mc. Graw-Hill Companies, Inc. , 2004
Note: In polyalphabetic substitution, the relationship between a character in the plaintext and a character in the ciphertext is one-to-many. Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
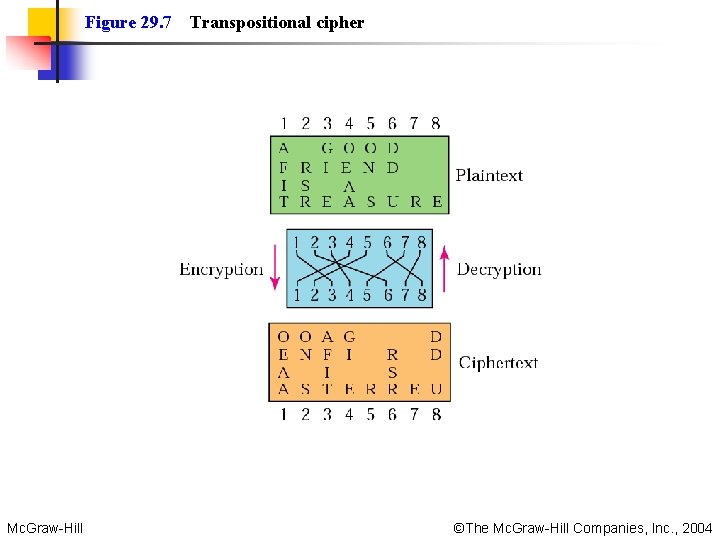
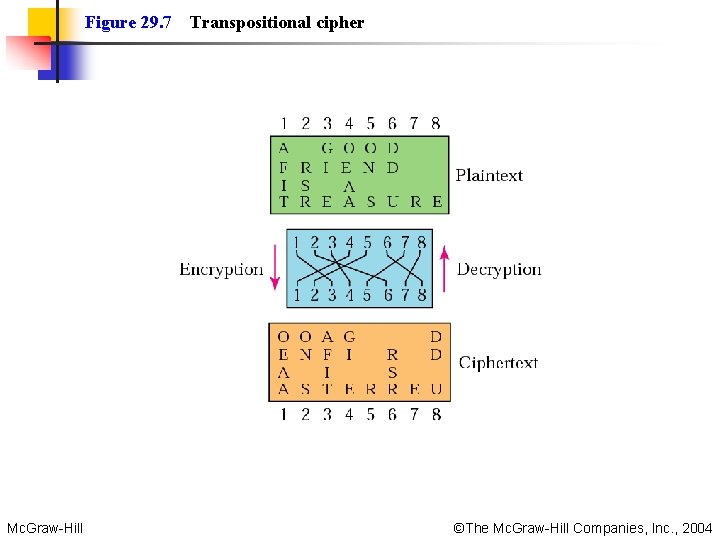
Figure 29. 7 Mc. Graw-Hill Transpositional cipher ©The Mc. Graw-Hill Companies, Inc. , 2004
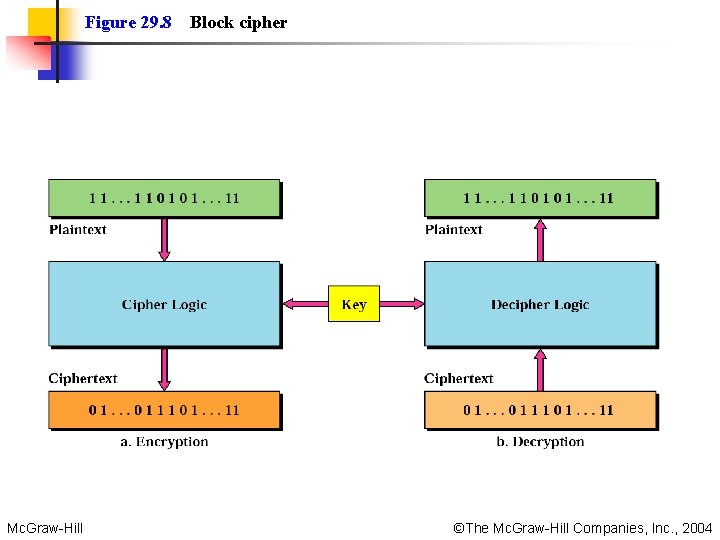
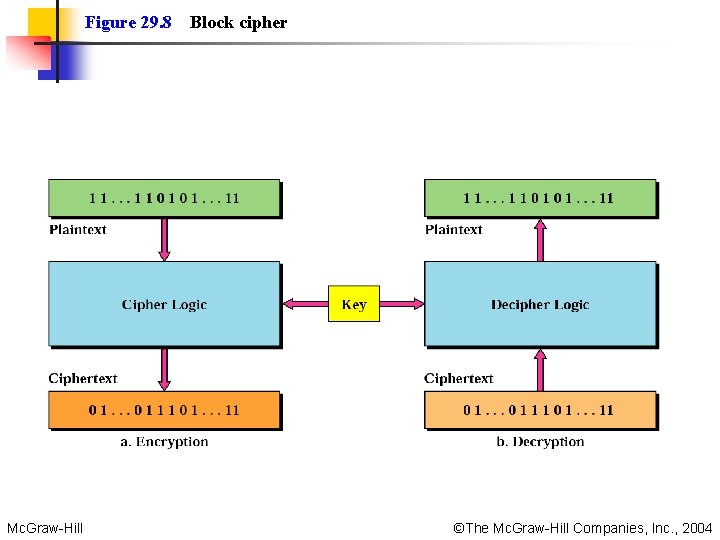
Figure 29. 8 Mc. Graw-Hill Block cipher ©The Mc. Graw-Hill Companies, Inc. , 2004
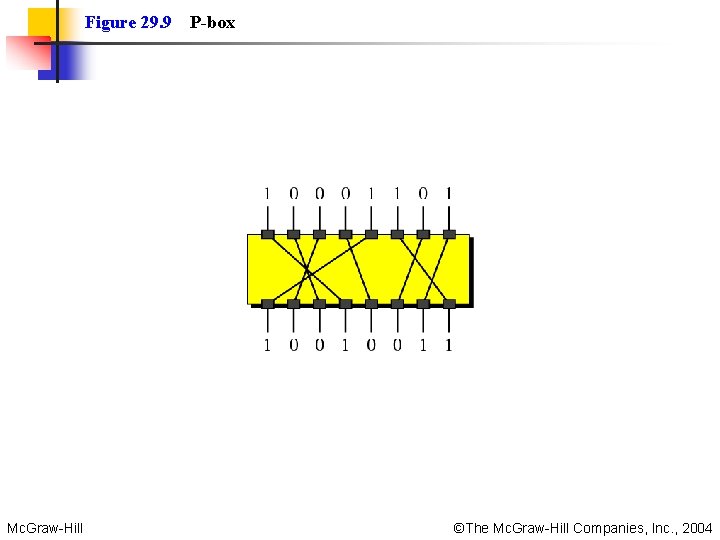
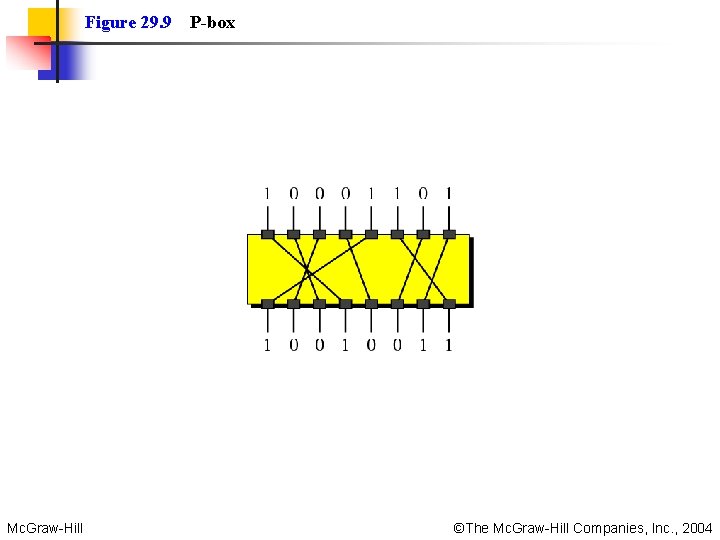
Figure 29. 9 Mc. Graw-Hill P-box ©The Mc. Graw-Hill Companies, Inc. , 2004
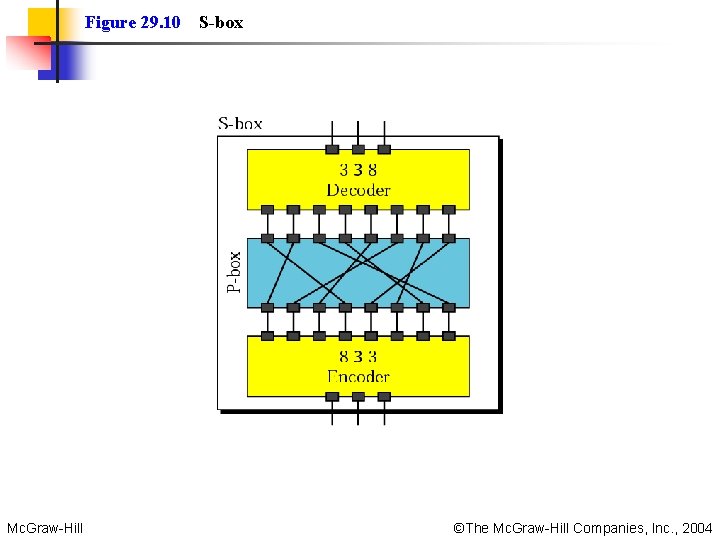
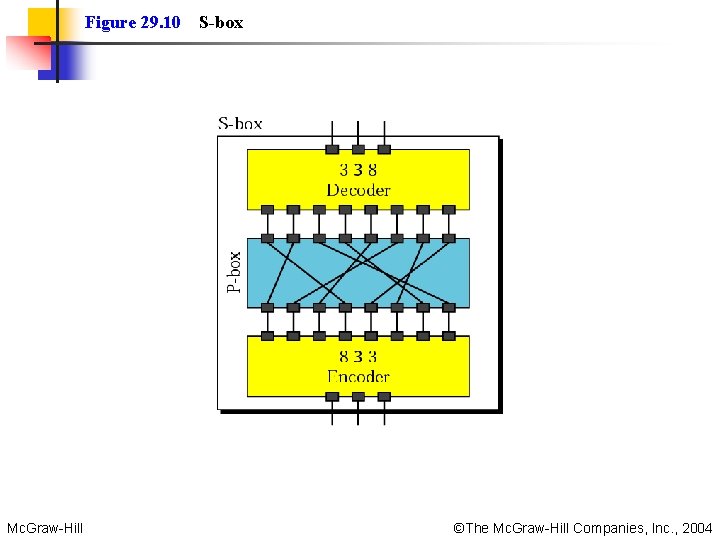
Figure 29. 10 Mc. Graw-Hill S-box ©The Mc. Graw-Hill Companies, Inc. , 2004
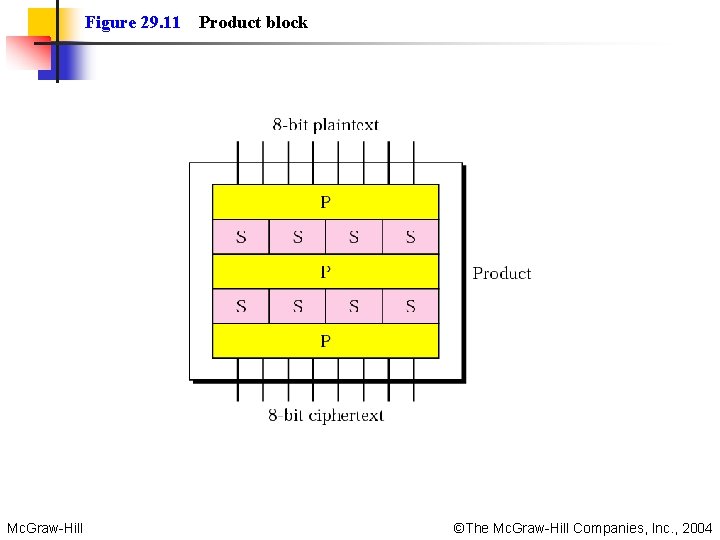
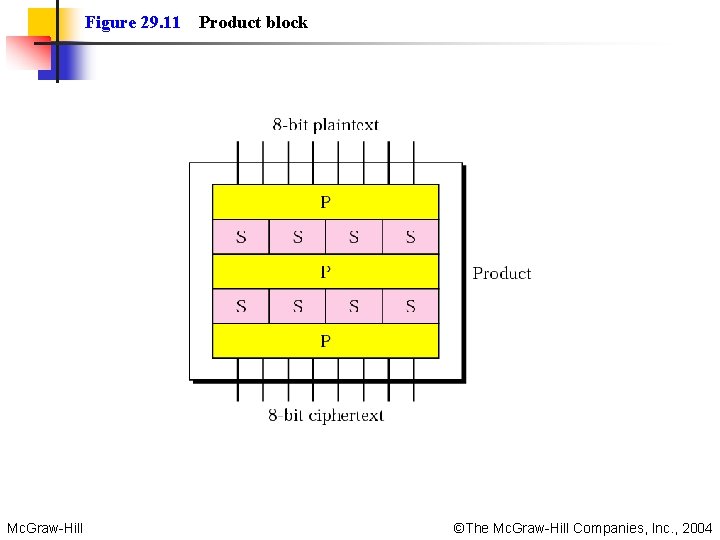
Figure 29. 11 Mc. Graw-Hill Product block ©The Mc. Graw-Hill Companies, Inc. , 2004
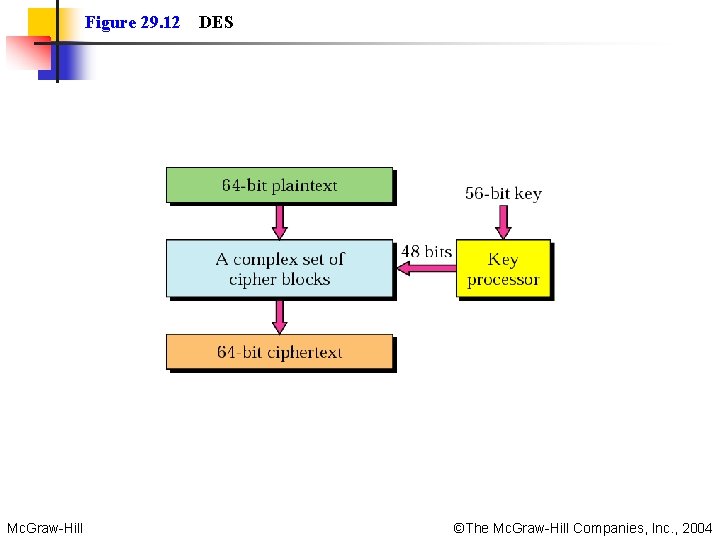
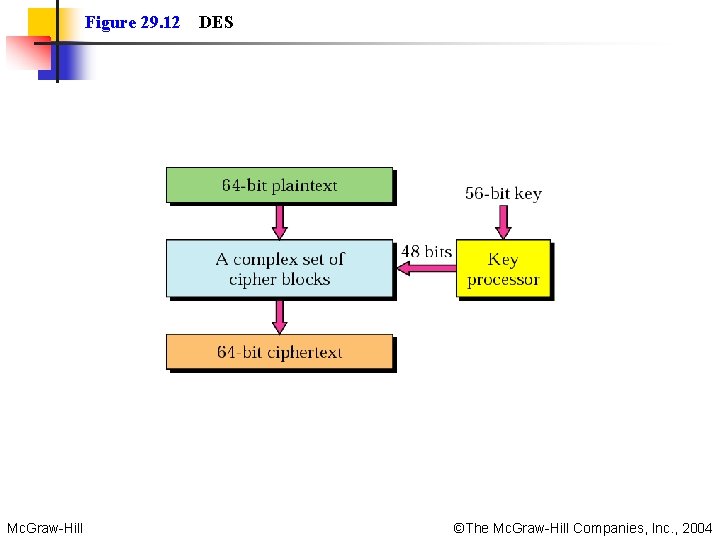
Figure 29. 12 Mc. Graw-Hill DES ©The Mc. Graw-Hill Companies, Inc. , 2004
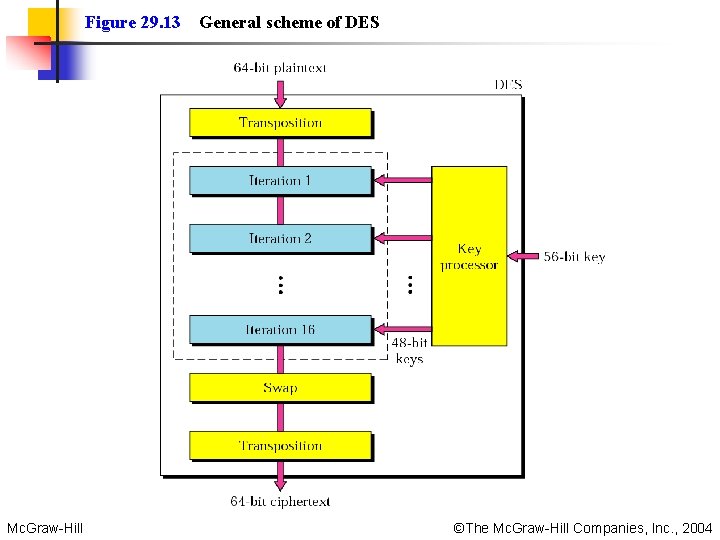
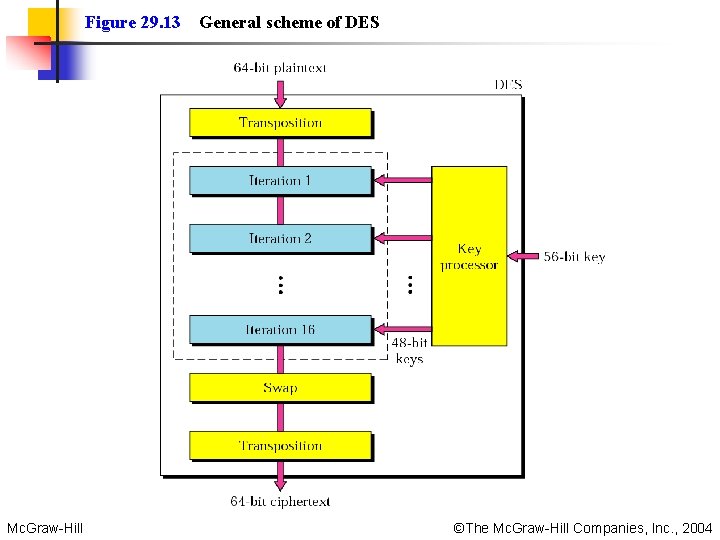
Figure 29. 13 Mc. Graw-Hill General scheme of DES ©The Mc. Graw-Hill Companies, Inc. , 2004
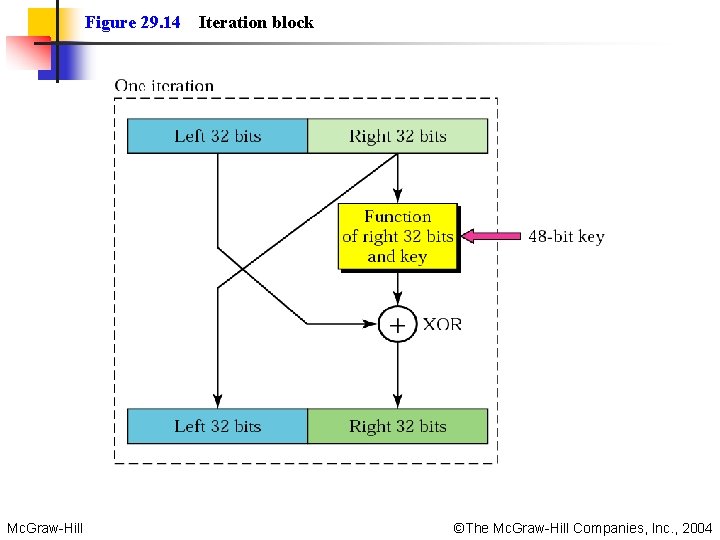
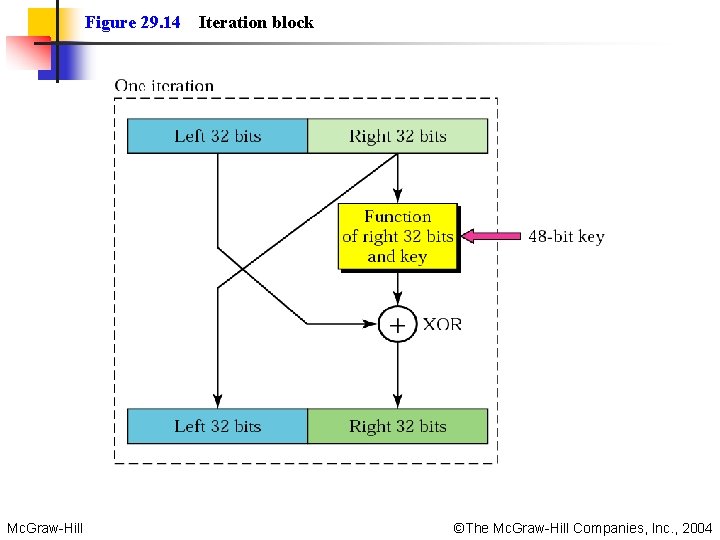
Figure 29. 14 Mc. Graw-Hill Iteration block ©The Mc. Graw-Hill Companies, Inc. , 2004
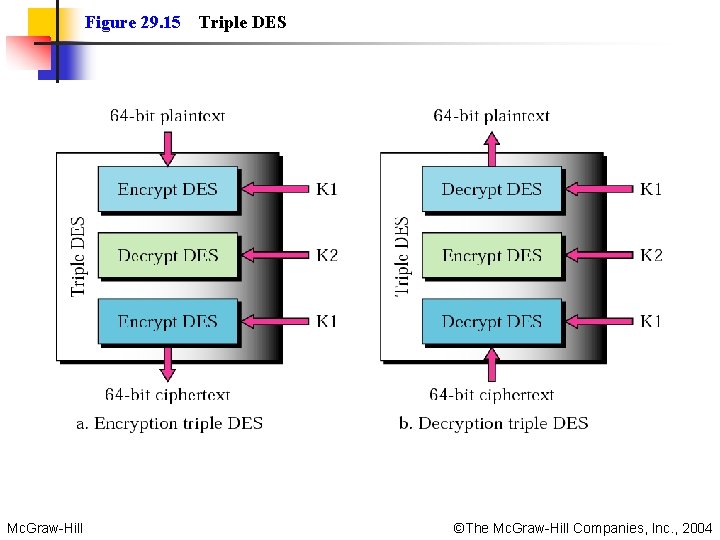
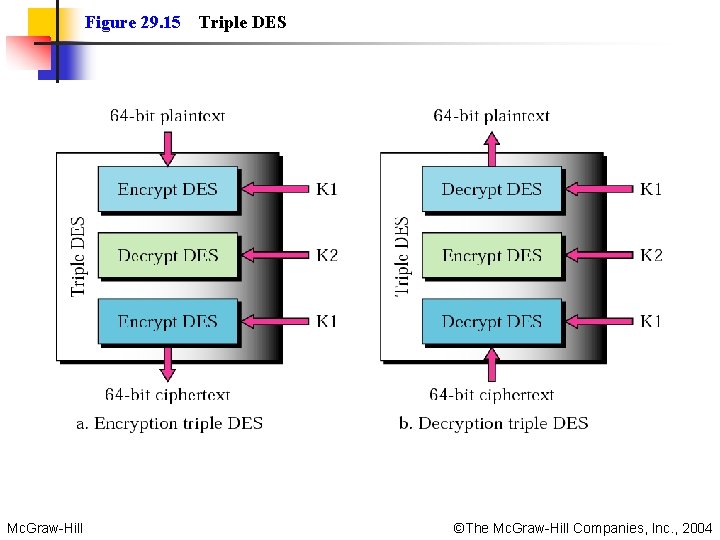
Figure 29. 15 Mc. Graw-Hill Triple DES ©The Mc. Graw-Hill Companies, Inc. , 2004
29. 3 Public-Key Cryptography RSA Choosing Public and Private Keys Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
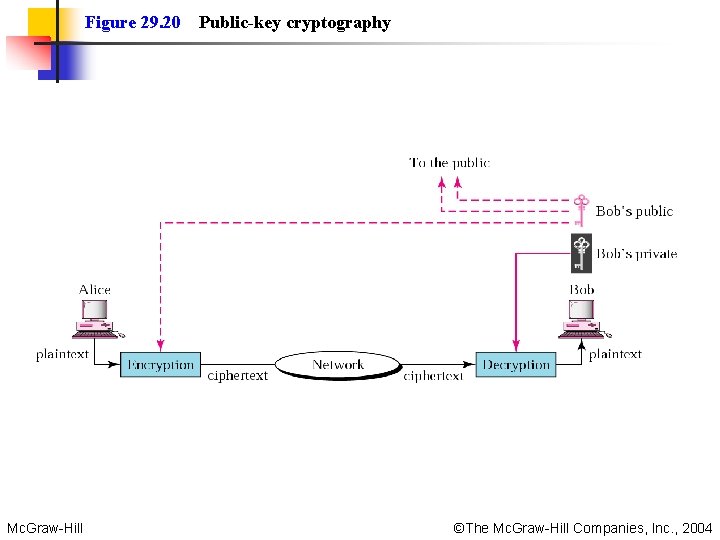
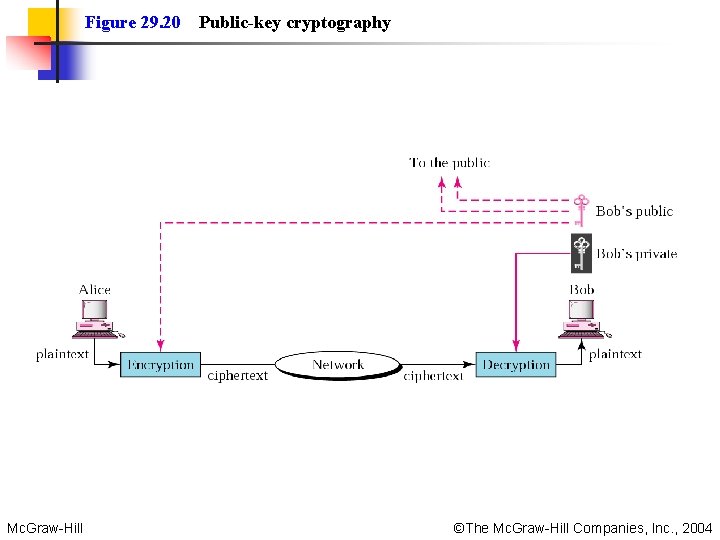
Figure 29. 20 Mc. Graw-Hill Public-key cryptography ©The Mc. Graw-Hill Companies, Inc. , 2004
Note: Public-key algorithms are more efficient for short messages. Mc. Graw-Hill ©The Mc. Graw-Hill Companies, Inc. , 2004
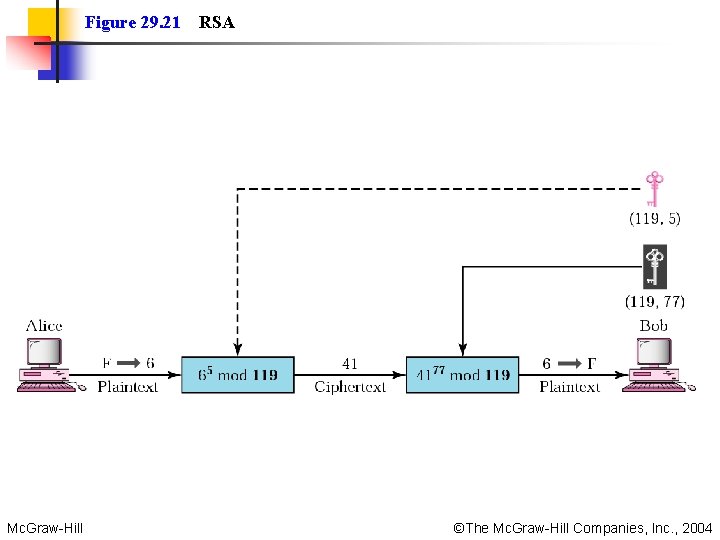
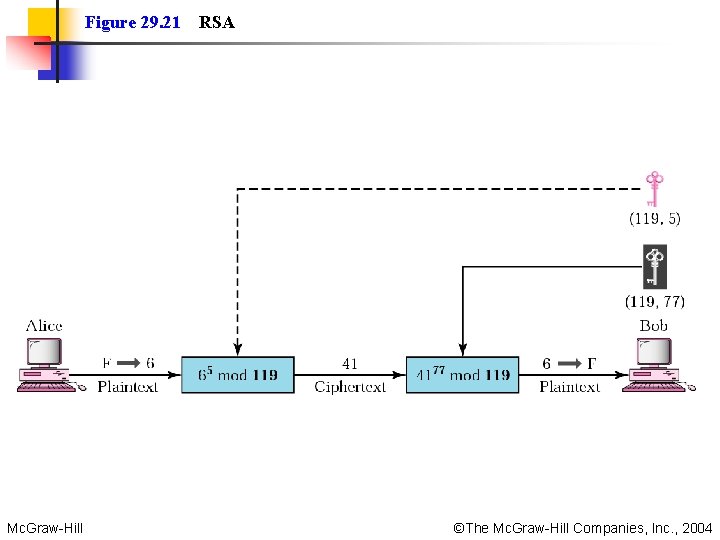
Figure 29. 21 Mc. Graw-Hill RSA ©The Mc. Graw-Hill Companies, Inc. , 2004