Part 5 Security Network Security Access Control Encryption

























- Slides: 31

Part 5: Security Network Security (Access Control, Encryption, Firewalls) CS 140 Westmont College

Secure Networks l l Secure network is not an absolute term Need to define security policy for organization Network security policy cannot be separated from security policy for attached computers Costs and benefits of security policies must be assessed FALL 2005 CSI 4118 – UNIVERSITY OF OTTAWA – R. L. PROBERT 2

Network Security Policy Devising a network security policy can be complex because a rational policy requires an organization to assess the value of information. The policy must apply to information stored in computers as well as to information traversing a network. FALL 2005 CSI 4118 – UNIVERSITY OF OTTAWA – R. L. PROBERT 3

Aspects of Security l l Data integrity Data availability Data confidentiality Privacy FALL 2005 CSI 4118 – UNIVERSITY OF OTTAWA – R. L. PROBERT 4

Responsibility and Control l l Accountability: how an audit trail is kept Authorization: who is responsible for each item and how is responsibility delegated to others FALL 2005 CSI 4118 – UNIVERSITY OF OTTAWA – R. L. PROBERT 5

Integrity Mechanisms l Techniques to ensure integrity l l l Parity bits Checksums CRCs These cannot guarantee data integrity (e. g. , against intentional change) Use of message authentication code (MAC) that cannot be broken or forged FALL 2005 CSI 4118 – UNIVERSITY OF OTTAWA – R. L. PROBERT 6

Access Control and Passwords l l Passwords used to control access Over a network, passwords susceptible to snooping FALL 2005 CSI 4118 – UNIVERSITY OF OTTAWA – R. L. PROBERT 7

Encryption and Confidentiality l l To ensure confidentiality of a transmitted message, use encryption Secret key or public key schemes message m FALL 2005 encryption decryption Secret key S CSI 4118 – UNIVERSITY OF OTTAWA – R. L. PROBERT message m 8
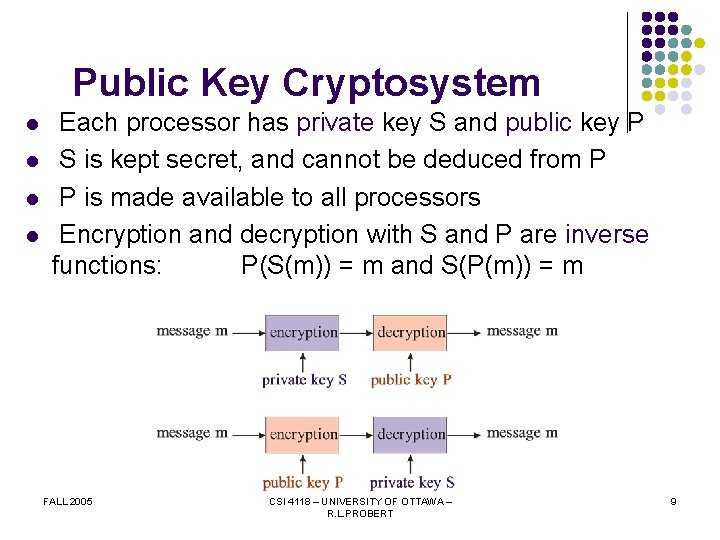
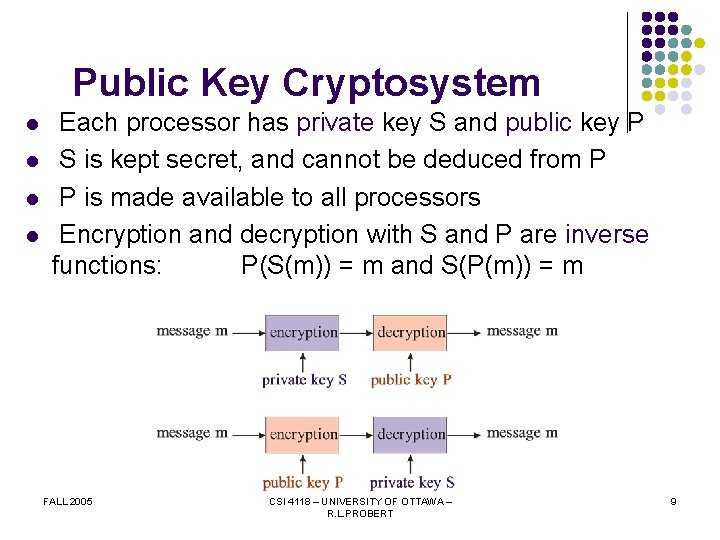
Public Key Cryptosystem l l Each processor has private key S and public key P S is kept secret, and cannot be deduced from P P is made available to all processors Encryption and decryption with S and P are inverse functions: P(S(m)) = m and S(P(m)) = m FALL 2005 CSI 4118 – UNIVERSITY OF OTTAWA – R. L. PROBERT 9

Message Digest l l l Digest function maps arbitrary length message m to fixed length digest d(m) One-way function: given d(m), can't find m Collision-free: infeasible to generate m and m' such that d(m) = d(m') FALL 2005 CSI 4118 – UNIVERSITY OF OTTAWA – R. L. PROBERT 10
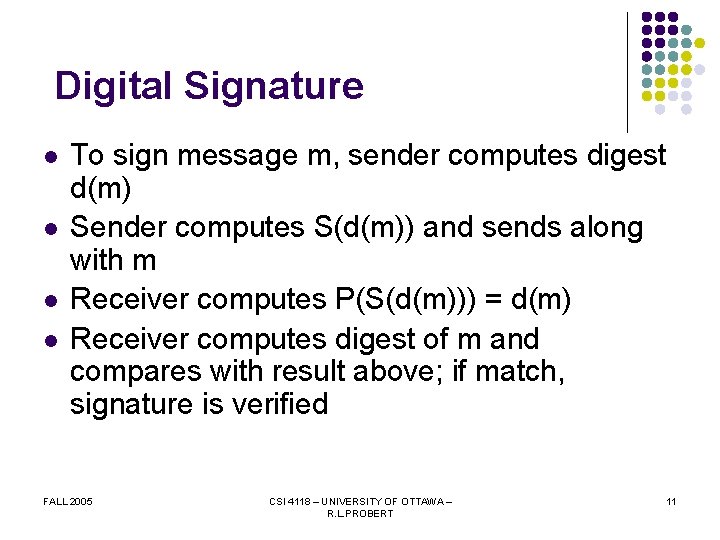
Digital Signature l l To sign message m, sender computes digest d(m) Sender computes S(d(m)) and sends along with m Receiver computes P(S(d(m))) = d(m) Receiver computes digest of m and compares with result above; if match, signature is verified FALL 2005 CSI 4118 – UNIVERSITY OF OTTAWA – R. L. PROBERT 11

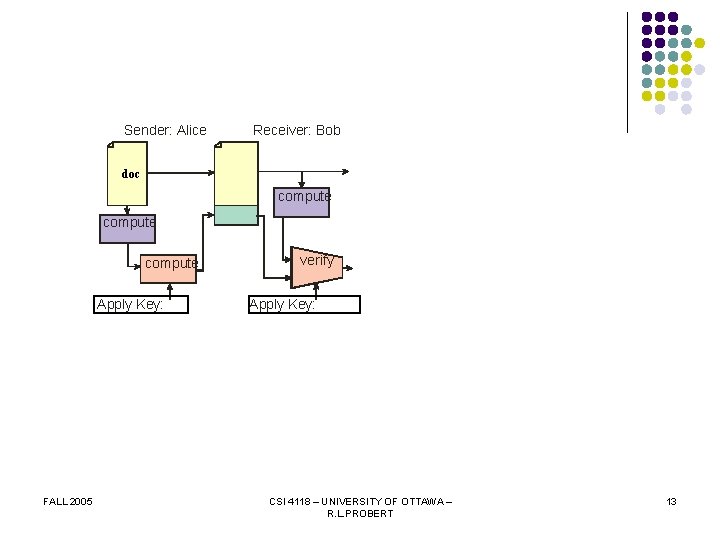
Digital Signature FALL 2005 CSI 4118 – UNIVERSITY OF OTTAWA – R. L. PROBERT 12
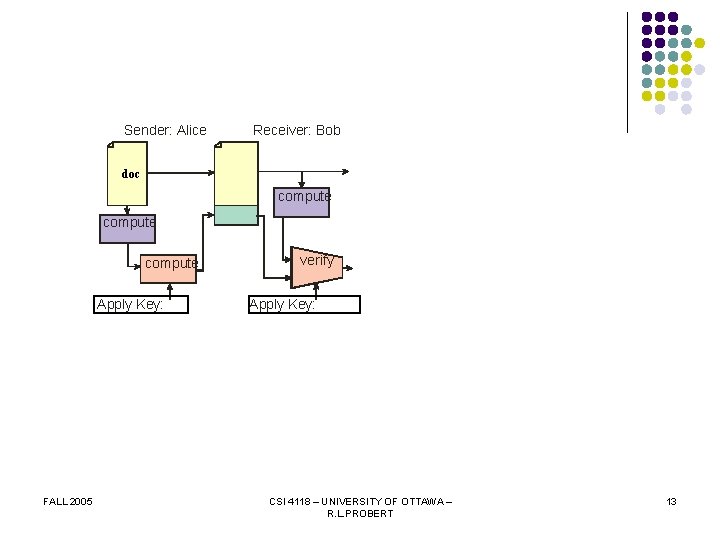
Sender: Alice Receiver: Bob doc compute Apply Key: FALL 2005 verify Apply Key: CSI 4118 – UNIVERSITY OF OTTAWA – R. L. PROBERT 13
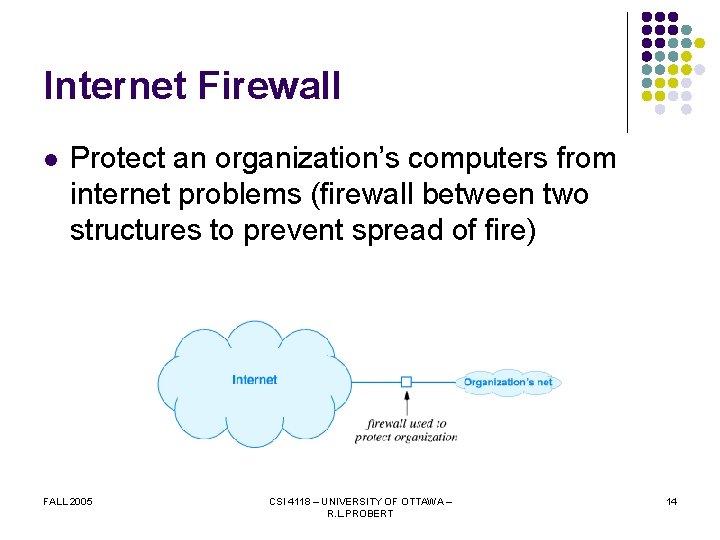
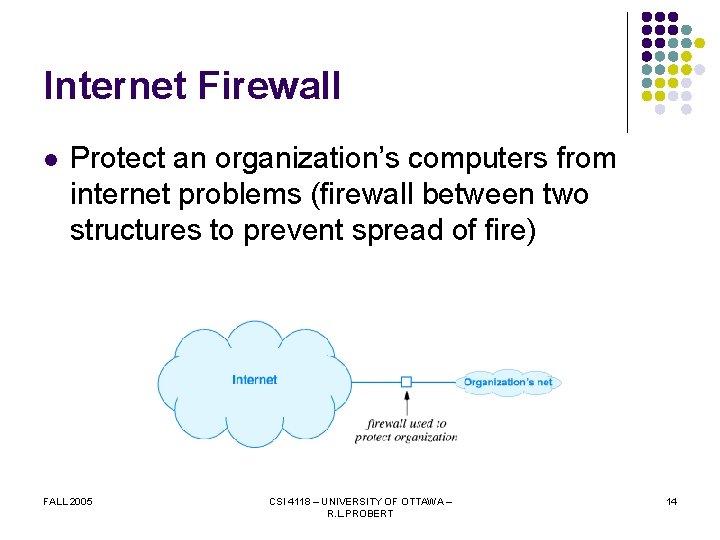
Internet Firewall l Protect an organization’s computers from internet problems (firewall between two structures to prevent spread of fire) FALL 2005 CSI 4118 – UNIVERSITY OF OTTAWA – R. L. PROBERT 14
Internet Firewall l l All traffic entering the organization passes through the firewall All traffic leaving the organization passes through the firewall The firewall implements the security policy and rejects any traffic that doesn’t adhere The firewall must be immune to security attacks FALL 2005 CSI 4118 – UNIVERSITY OF OTTAWA – R. L. PROBERT 15

Packet Filtering l l Packet filter is embedded in router Specify which packets can pass through and which should be blocked FALL 2005 CSI 4118 – UNIVERSITY OF OTTAWA – R. L. PROBERT 16

Using Packet Filters to Create a Firewall l Three components in a firewall l FALL 2005 Packet filter for incoming packets Packet filter for outgoing packets Secure computer system to run applicationlayer gateways or proxies CSI 4118 – UNIVERSITY OF OTTAWA – R. L. PROBERT 17

Virtual Private Networks l Two approaches to building corporate intranet for an organization with multiple sites: l l l Private network connections (confidential) Public internet connections (low cost) Virtual Private Network l l FALL 2005 Achieve both confidentiality and low cost Implemented in software CSI 4118 – UNIVERSITY OF OTTAWA – R. L. PROBERT 18

Virtual Private Network l VPN software in router at each site gives appearance of a private network FALL 2005 CSI 4118 – UNIVERSITY OF OTTAWA – R. L. PROBERT 19

Virtual Private Network l l l Obtain internet connection for each site Choose router at each site to run VPN software Configure VPN software in each router to know about the VPN routers at other sites VPN software acts as a packet filter; next hop for outgoing datagram is another VPN router Each outgoing datagram is encrypted FALL 2005 CSI 4118 – UNIVERSITY OF OTTAWA – R. L. PROBERT 20

Tunneling l l Desire to encrypt entire datagram so source and destination addresses are not visible on Internet How can internet routers do proper forwarding? Solution: VPN software encrypts entire datagram and places inside another for transmission Called IP-in-IP tunneling (encapsulation) FALL 2005 CSI 4118 – UNIVERSITY OF OTTAWA – R. L. PROBERT 21

Tunneling l l Datagram from computer x at site 1 to computer y at site 2 Router R 1 on site 1 encrypts, encapsulates in new datagram for transmission to router R 2 on site 2 FALL 2005 CSI 4118 – UNIVERSITY OF OTTAWA – R. L. PROBERT 22

Other Security Methods FALL 2005 CSI 4118 – UNIVERSITY OF OTTAWA

PGP – Pretty Good Privacy l l l PGP is a security technology which allows us to send email that is authenticated and/or encrypted. Authentication confirms the identity of the sender or a message. Encryption scrambles the contents of a message so that only the intended recipients can read it. Each user of PGP has a public and a private key. They are generated in matched pairs: a public key only ever works with its twin private key. A user's public key is not a secret and can be distributed widely. A user's private key however must be kept secret, and is protected by a pass phrase (like a password but longer). FALL 2005 CSI 4118 – UNIVERSITY OF OTTAWA – R. L. PROBERT 24

PGP – Pretty Good Privacy l l A public key is used in two ways: Alice can authenticate a signed message from Bob using his public key. If the message matches Bob's public key then Alice can be sure that the message came from Bob. Alice can send a secure message to Bob by encrypting the message using Bob's public key. The only person who can decrypt the message is Bob. A private key also has two uses: Bob can send an authenticated message to Alice by signing it with his private key. Since Bob is the only person who has his private key (and the pass phrase that protects it), Alice knows that if the message matches Bob's public key, then it must have been sent by Bob can read a secure message sent by Alice by decrypting it with his private key. FALL 2005 CSI 4118 – UNIVERSITY OF OTTAWA – R. L. PROBERT 25
SSL (Secure Sockets Layer) l l The SSL (Secure Sockets Layer) Handshake Protocol was developed to provide security and privacy over the Internet. The SSL protocol runs in a "layer" above TCP/IP and below higher-level protocols such as HTTP or IMAP. The SSL protocol is able to negotiate encryption keys as well as authenticate the server before data is exchanged by the higher-level application. The SSL protocol maintains the security and integrity of the transmission channel by using encryption, authentication and message authentication codes. FALL 2005 CSI 4118 – UNIVERSITY OF OTTAWA – R. L. PROBERT 26

HTTPS l l l HTTPS stands for Hypertext Transfer Protocol over Secure Socket Layer, or HTTP over SSL. HTTPS encrypts and decrypts the page requests and page information between the client browser and the web server using a secure Socket Layer (SSL). SSL transactions are negotiated by means of a keybased encryption algorithm between the client and the server. FALL 2005 CSI 4118 – UNIVERSITY OF OTTAWA – R. L. PROBERT 27

IPsec l l Short for IP Security, IPsec is a set of protocols developed by the IETF to support secure exchange of packets at the IP layer. IPsec supports two encryption modes: Transport and Tunnel. Transport mode encrypts only the data portion (payload) of each packet, but leaves the header untouched. The more secure Tunnel mode encrypts both the header and the payload. On the receiving side, an IPSec-compliant device decrypts each packet. FALL 2005 CSI 4118 – UNIVERSITY OF OTTAWA – R. L. PROBERT 28

SET – Secure Electronic Transactions l l Short for Secure Electronic Transaction, a standard that will enable secure credit card transactions on the Internet. SET has been endorsed by virtually all the major players in the electronic commerce arena, including Microsoft, Netscape, Visa, and Mastercard. By employing digital signatures, SET will enable merchants to verify that buyers are who they claim to be. It will protect buyers by providing a mechanism for their credit card number to be transferred directly to the credit card issuer for verification and billing without the merchant being able to see the number. FALL 2005 CSI 4118 – UNIVERSITY OF OTTAWA – R. L. PROBERT 29

Summary l Security is desirable but must be defined by an organization l l FALL 2005 Assess value of information and define a security policy Aspects to consider include privacy and data integrity, availability, and confidentiality CSI 4118 – UNIVERSITY OF OTTAWA – R. L. PROBERT 30

Summary (continued) l Mechanisms to provide aspects of security l l l Encryption: secret and public key cryptosystems Firewalls: packet filtering Virtual private networks l FALL 2005 Use Internet to transfer data among organization’s sites but ensure that data cannot be read by others CSI 4118 – UNIVERSITY OF OTTAWA – R. L. PROBERT 31