Paper Reviews Written reviews for each paper to
![Link-State Approach [Dijkstra 1959 and Mc. Quillan+ 1980] – Traditional link-state protocols may not Link-State Approach [Dijkstra 1959 and Mc. Quillan+ 1980] – Traditional link-state protocols may not](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-4.jpg)
![Distance-Vector Approach [Ford+ 1962 and Leiner+ 1987] – Based on shortest-path routing algorithms i. Distance-Vector Approach [Ford+ 1962 and Leiner+ 1987] – Based on shortest-path routing algorithms i.](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-5.jpg)
![Destination-Sequenced Distance-Vector Routing (DSDV) [Perkins+ 1994] – Based on classical distributed Bellman-Ford routing mechanism Destination-Sequenced Distance-Vector Routing (DSDV) [Perkins+ 1994] – Based on classical distributed Bellman-Ford routing mechanism](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-8.jpg)
![Dynamic Source Routing (DSR) [Johnson+ 1996] When node S wants to send a packet Dynamic Source Routing (DSR) [Johnson+ 1996] When node S wants to send a packet](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-11.jpg)
![Route Discovery in DSR Y Broadcast transmission [S] S Z E F B C Route Discovery in DSR Y Broadcast transmission [S] S Z E F B C](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-13.jpg)
![Route Discovery in DSR Y S E Z [S, E] F B C A Route Discovery in DSR Y S E Z [S, E] F B C A](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-14.jpg)
![Route Discovery in DSR Y Z S E F B [S, E, F] C Route Discovery in DSR Y Z S E F B [S, E, F] C](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-15.jpg)
![Route Discovery in DSR Y Z S E [S, E, F, J] F B Route Discovery in DSR Y Z S E [S, E, F, J] F B](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-16.jpg)
![Route Discovery in DSR Y Z S E [S, E, F, J, M] F Route Discovery in DSR Y Z S E [S, E, F, J, M] F](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-17.jpg)
![Route Reply in DSR Y S E Z RREP [S, E, F, J, D] Route Reply in DSR Y S E Z RREP [S, E, F, J, D]](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-19.jpg)
![Data Delivery in DSR Y DATA [S, E, F, J, D] S Z E Data Delivery in DSR Y DATA [S, E, F, J, D] S Z E](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-22.jpg)
![Use of Route Caching [S, E, F, J, D] [E, F, J, D] S Use of Route Caching [S, E, F, J, D] [E, F, J, D] S](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-26.jpg)
![Use of Route Caching: Can Speed up Route Discovery [S, E, F, J, D] Use of Route Caching: Can Speed up Route Discovery [S, E, F, J, D]](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-27.jpg)
![Route Error (RERR) Y RERR [J-D] S Z E F B C M J Route Error (RERR) Y RERR [J-D] S Z E F B C M J](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-29.jpg)
![Cluster Gateway Switch Routing (CGSR) [Chiang+ 1997] – Nodes are grouped into clusters with Cluster Gateway Switch Routing (CGSR) [Chiang+ 1997] – Nodes are grouped into clusters with](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-34.jpg)
![Ad-hoc On-Demand Distance Vector Routing (AODV) [Perkins+ 1999] – Improvement on DSDV due to Ad-hoc On-Demand Distance Vector Routing (AODV) [Perkins+ 1999] – Improvement on DSDV due to](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-37.jpg)
![Location-Aided Routing (LAR) [Ko+ 1998] – Utilizes location information (via GPS) to limit the Location-Aided Routing (LAR) [Ko+ 1998] – Utilizes location information (via GPS) to limit the](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-41.jpg)
![Power-Aware Routing [Singh+ 1998] – In existing MAC protocols, nodes are powered on most Power-Aware Routing [Singh+ 1998] – In existing MAC protocols, nodes are powered on most](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-46.jpg)
![Zone Routing Protocol (ZRP) [Hass+ 1998] – Hybrid protocol incorporates the merits of proactive Zone Routing Protocol (ZRP) [Hass+ 1998] – Hybrid protocol incorporates the merits of proactive](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-47.jpg)
![References [Bertsekas+ 1987] D. Bertsekas and R. Gallager, Data Networks, Prentice-Hall, Englewood Cliffs, N. References [Bertsekas+ 1987] D. Bertsekas and R. Gallager, Data Networks, Prentice-Hall, Englewood Cliffs, N.](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-48.jpg)
![References [Leiner+ 1962] B. M. Leiner, D. L. Nielson, and F. A. Tobagi, Issues References [Leiner+ 1962] B. M. Leiner, D. L. Nielson, and F. A. Tobagi, Issues](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-49.jpg)
- Slides: 49
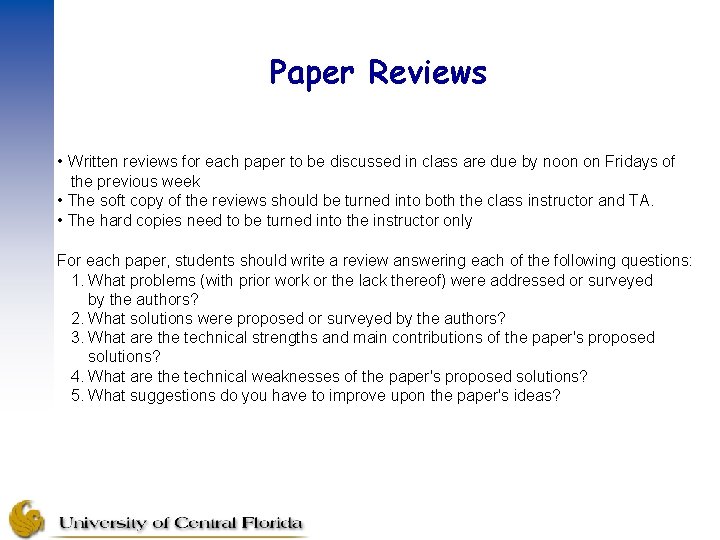
Paper Reviews • Written reviews for each paper to be discussed in class are due by noon on Fridays of the previous week • The soft copy of the reviews should be turned into both the class instructor and TA. • The hard copies need to be turned into the instructor only For each paper, students should write a review answering each of the following questions: 1. What problems (with prior work or the lack thereof) were addressed or surveyed by the authors? 2. What solutions were proposed or surveyed by the authors? 3. What are the technical strengths and main contributions of the paper's proposed solutions? 4. What are the technical weaknesses of the paper's proposed solutions? 5. What suggestions do you have to improve upon the paper's ideas?
Routing in Mobile Ad hoc Networks
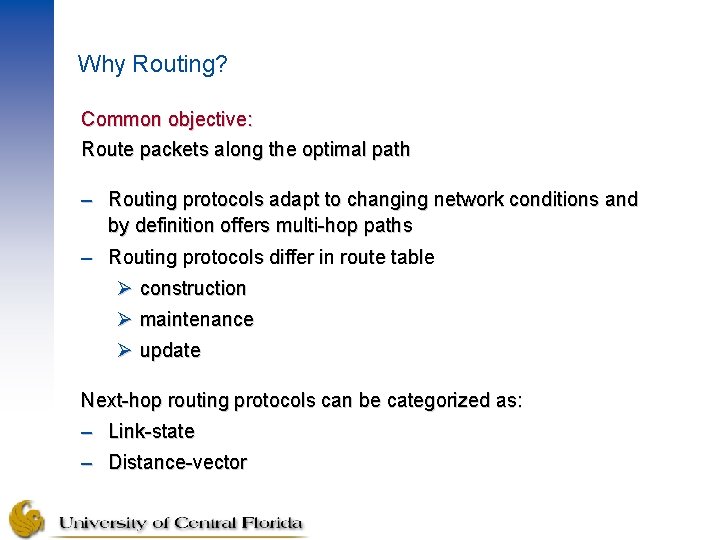
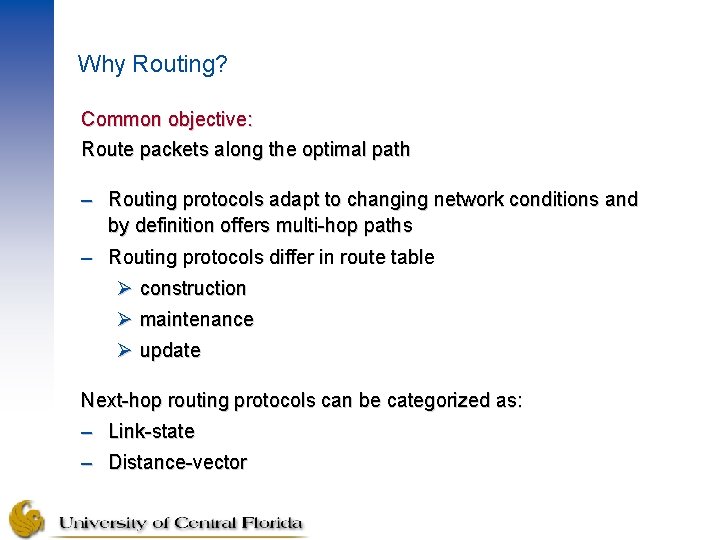
Why Routing? Common objective: Route packets along the optimal path – Routing protocols adapt to changing network conditions and by definition offers multi-hop paths – Routing protocols differ in route table Ø construction Ø maintenance Ø update Next-hop routing protocols can be categorized as: – Link-state – Distance-vector
![LinkState Approach Dijkstra 1959 and Mc Quillan 1980 Traditional linkstate protocols may not Link-State Approach [Dijkstra 1959 and Mc. Quillan+ 1980] – Traditional link-state protocols may not](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-4.jpg)
Link-State Approach [Dijkstra 1959 and Mc. Quillan+ 1980] – Traditional link-state protocols may not be suitable – Closer to centralized version of shortest-path algorithm – Each node maintains a view of network topology with a cost for each link – Link costs are broadcast periodically to keep the views consistent – Each node updates its view and applies a shortest-path algorithm to find its next hop for each destination – Routing loops may occur due to propagation delays, partitioned networks, and so on – Alternative link-state routing approaches may not require all nodes to have the identical link-state information and route selection algorithms and may find routes on demand
![DistanceVector Approach Ford 1962 and Leiner 1987 Based on shortestpath routing algorithms i Distance-Vector Approach [Ford+ 1962 and Leiner+ 1987] – Based on shortest-path routing algorithms i.](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-5.jpg)
Distance-Vector Approach [Ford+ 1962 and Leiner+ 1987] – Based on shortest-path routing algorithms i. e. , Distributed Bellman-Ford – DBF algorithms are also known as Distance-Vector (DV) – For each destination, the node stores a single route table entry along with next-hop neighbor – Route table entry for destination contains metric which is distance from node to the destination and also the next-hop (vector) towards destination
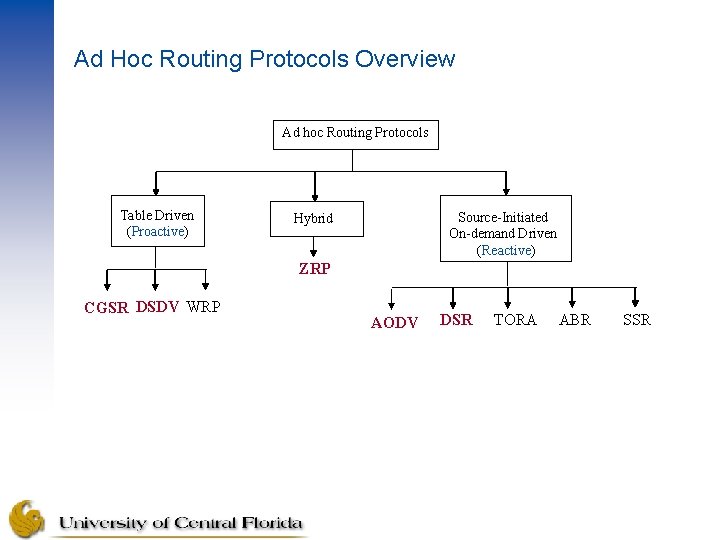
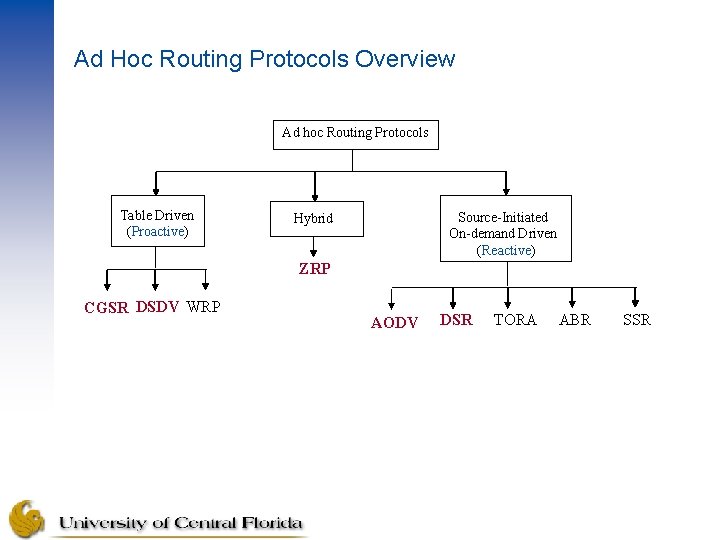
Ad Hoc Routing Protocols Overview Ad hoc Routing Protocols Table Driven (Proactive) Source-Initiated On-demand Driven (Reactive) Hybrid ZRP CGSR DSDV WRP AODV DSR TORA ABR SSR
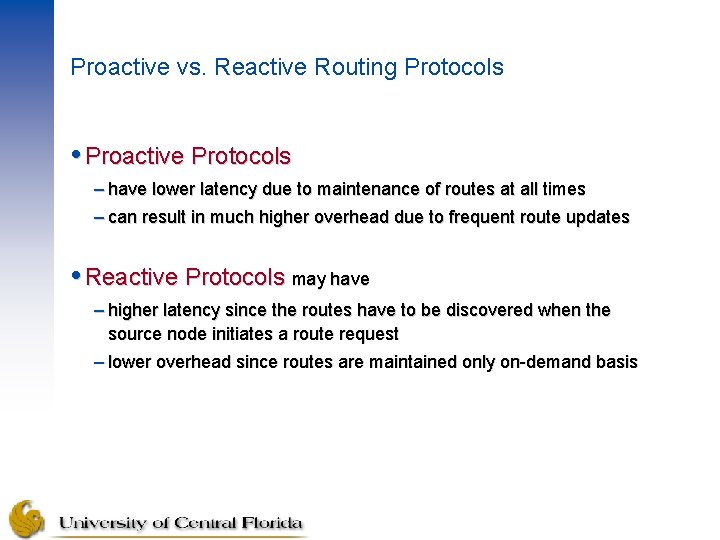
Proactive vs. Reactive Routing Protocols Proactive Protocols – have lower latency due to maintenance of routes at all times – can result in much higher overhead due to frequent route updates Reactive Protocols may have – higher latency since the routes have to be discovered when the source node initiates a route request – lower overhead since routes are maintained only on-demand basis
![DestinationSequenced DistanceVector Routing DSDV Perkins 1994 Based on classical distributed BellmanFord routing mechanism Destination-Sequenced Distance-Vector Routing (DSDV) [Perkins+ 1994] – Based on classical distributed Bellman-Ford routing mechanism](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-8.jpg)
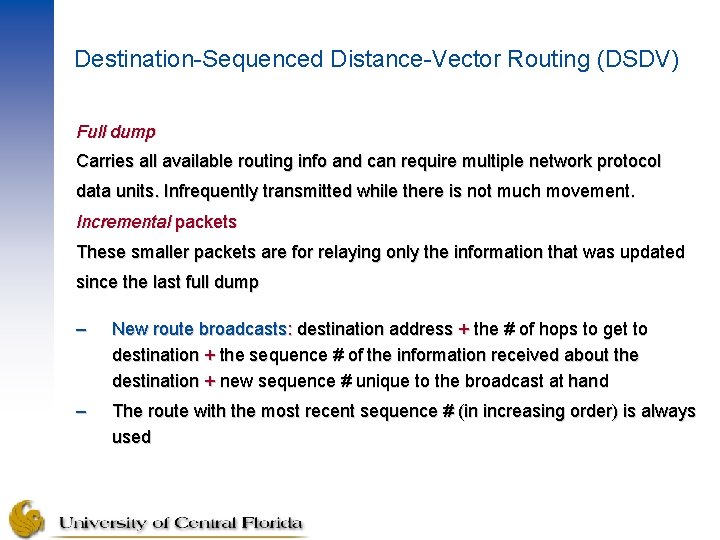
Destination-Sequenced Distance-Vector Routing (DSDV) [Perkins+ 1994] – Based on classical distributed Bellman-Ford routing mechanism – Routing loops in a mobile network have been eliminated – Each node has a routing table (all possible destinations within network, and number of routing hops to each destination) – A sequence numbering system to distinguish stale routes from new ones and assigned by the destination node – Routing table updates are sent periodically (table consistency) – High volumes of control traffic meaning an inefficient utilization of network resources – To alleviate this problem, the protocol uses two types of route update packets
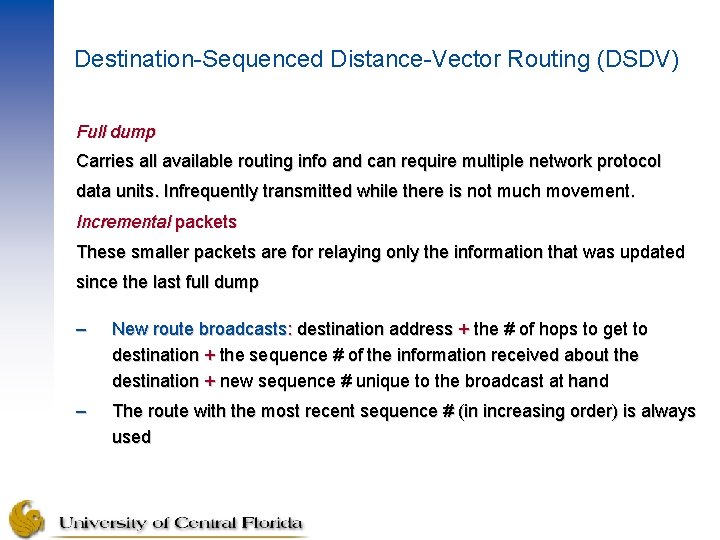
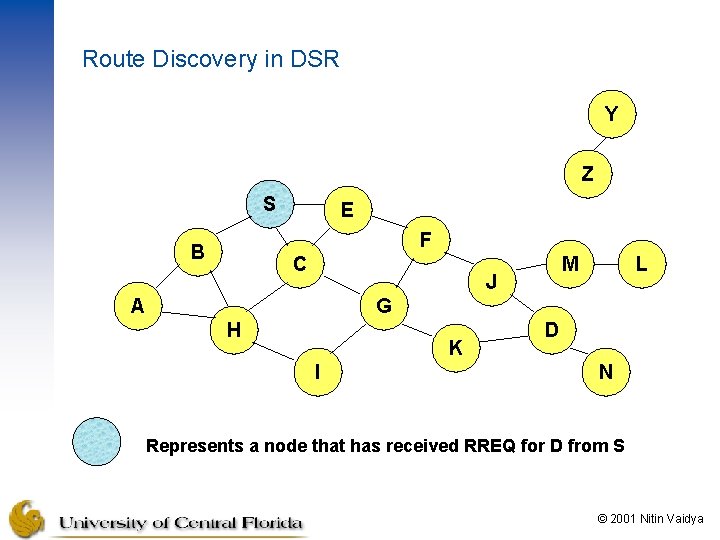
Destination-Sequenced Distance-Vector Routing (DSDV) Full dump Carries all available routing info and can require multiple network protocol data units. Infrequently transmitted while there is not much movement. Incremental packets These smaller packets are for relaying only the information that was updated since the last full dump – New route broadcasts: destination address + the # of hops to get to destination + the sequence # of the information received about the destination + new sequence # unique to the broadcast at hand – The route with the most recent sequence # (in increasing order) is always used
Destination-Sequenced Distance-Vector Routing (DSDV) – If there is an occurrence of two updates with the same sequence # , the route with the smaller hop count is used in order to obtain optimized (shorter) path – Mobiles keep track of other metrics such as settling time of routes, or the weighted average time – The broadcast of a routing update is delayed by the settling time in order to reduce network traffic, as well as optimizing routes
![Dynamic Source Routing DSR Johnson 1996 When node S wants to send a packet Dynamic Source Routing (DSR) [Johnson+ 1996] When node S wants to send a packet](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-11.jpg)
Dynamic Source Routing (DSR) [Johnson+ 1996] When node S wants to send a packet to node D, but does not know a route to D, node S initiates a route discovery Source node S floods Route Request (RREQ) Each node appends own identifier when forwarding RREQ © 2001 Nitin Vaidya
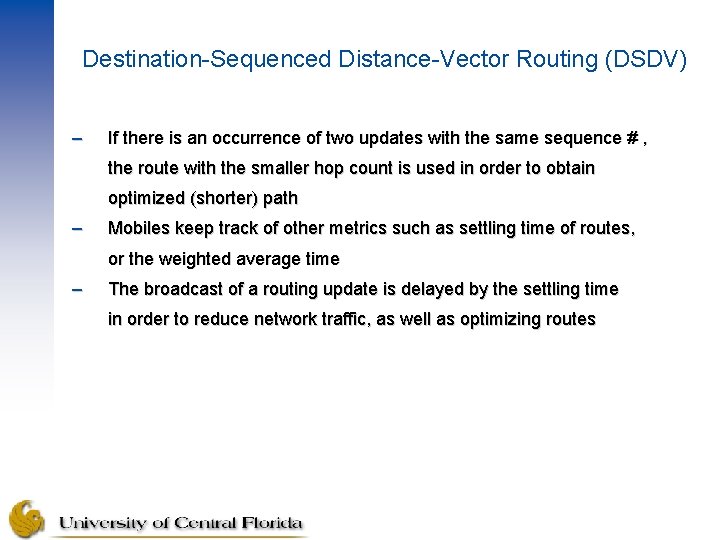
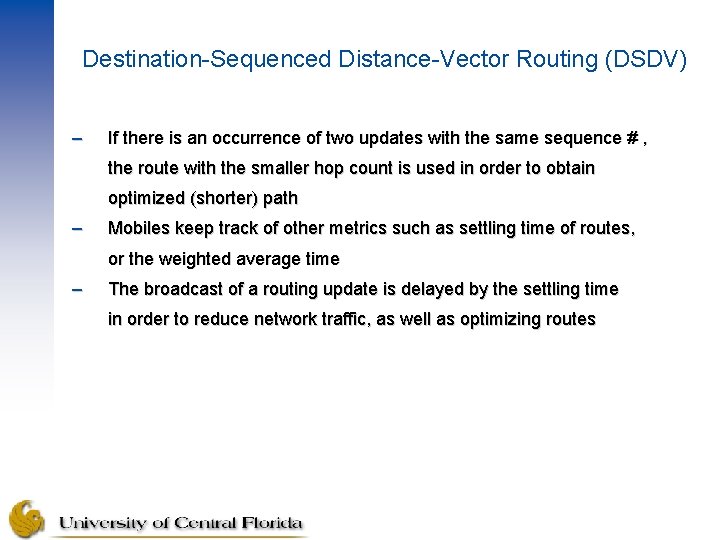
Route Discovery in DSR Y Z S E F B C M J A L G H K I D N Represents a node that has received RREQ for D from S © 2001 Nitin Vaidya
![Route Discovery in DSR Y Broadcast transmission S S Z E F B C Route Discovery in DSR Y Broadcast transmission [S] S Z E F B C](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-13.jpg)
Route Discovery in DSR Y Broadcast transmission [S] S Z E F B C M J A L G H K D I N Represents transmission of RREQ [X, Y] Represents list of identifiers appended to RREQ © 2001 Nitin Vaidya
![Route Discovery in DSR Y S E Z S E F B C A Route Discovery in DSR Y S E Z [S, E] F B C A](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-14.jpg)
Route Discovery in DSR Y S E Z [S, E] F B C A M J [S, C] H L G K I D N • Node H receives packet RREQ from two neighbors: potential for collision © 2001 Nitin Vaidya
![Route Discovery in DSR Y Z S E F B S E F C Route Discovery in DSR Y Z S E F B [S, E, F] C](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-15.jpg)
Route Discovery in DSR Y Z S E F B [S, E, F] C M J A L G H I [S, C, G] K D N • Node C receives RREQ from G and H, but does not forward it again, because node C has already forwarded RREQ once © 2001 Nitin Vaidya
![Route Discovery in DSR Y Z S E S E F J F B Route Discovery in DSR Y Z S E [S, E, F, J] F B](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-16.jpg)
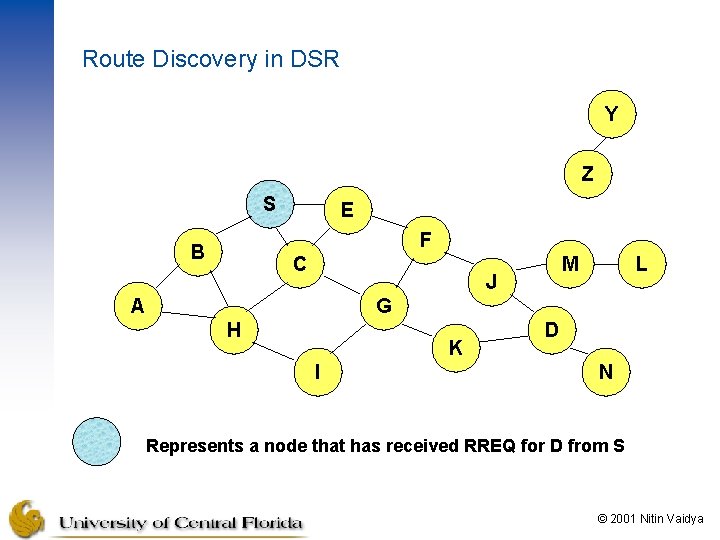
Route Discovery in DSR Y Z S E [S, E, F, J] F B C M J A L G H K I D [S, C, G, K] N • Nodes J and K both broadcast RREQ to node D • Since nodes J and K are hidden from each other, their transmissions may collide © 2001 Nitin Vaidya
![Route Discovery in DSR Y Z S E S E F J M F Route Discovery in DSR Y Z S E [S, E, F, J, M] F](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-17.jpg)
Route Discovery in DSR Y Z S E [S, E, F, J, M] F B C M J A L G H K I D N • Node D does not forward RREQ, because node D is the intended target of the route discovery © 2001 Nitin Vaidya
Route Discovery in DSR Destination D on receiving the first RREQ, sends a Route Reply (RREP) RREP is sent on a route obtained by reversing the route appended to received RREQ RREP includes the route from S to D on which RREQ was received by node D © 2001 Nitin Vaidya
![Route Reply in DSR Y S E Z RREP S E F J D Route Reply in DSR Y S E Z RREP [S, E, F, J, D]](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-19.jpg)
Route Reply in DSR Y S E Z RREP [S, E, F, J, D] F B C M J A L G H K I D N Represents RREP control message © 2001 Nitin Vaidya
Route Reply in DSR Route Reply can be sent by reversing the route in Route Request (RREQ) only if links are guaranteed to be bi-directional – To ensure this, RREQ should be forwarded only if it received on a link that is known to be bi-directional If unidirectional (asymmetric) links are allowed, then RREP may need a route discovery for S from node D – Unless node D already knows a route to node S – If a route discovery is initiated by D for a route to S, then the Route Reply is piggybacked on the Route Request from D. If IEEE 802. 11 MAC is used to send data, then links have to be bidirectional (since Ack is used) © 2001 Nitin Vaidya
Dynamic Source Routing (DSR) Node S on receiving RREP, caches the route included in the RREP When node S sends a data packet to D, the entire route is included in the packet header – hence the name source routing Intermediate nodes use the source route included in a packet to determine to whom a packet should be forwarded © 2001 Nitin Vaidya
![Data Delivery in DSR Y DATA S E F J D S Z E Data Delivery in DSR Y DATA [S, E, F, J, D] S Z E](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-22.jpg)
Data Delivery in DSR Y DATA [S, E, F, J, D] S Z E F B C M J A L G H K I D N Packet header size grows with route length © 2001 Nitin Vaidya
When to Perform a Route Discovery When node S wants to send data to node D, but does not know a valid route node D © 2001 Nitin Vaidya
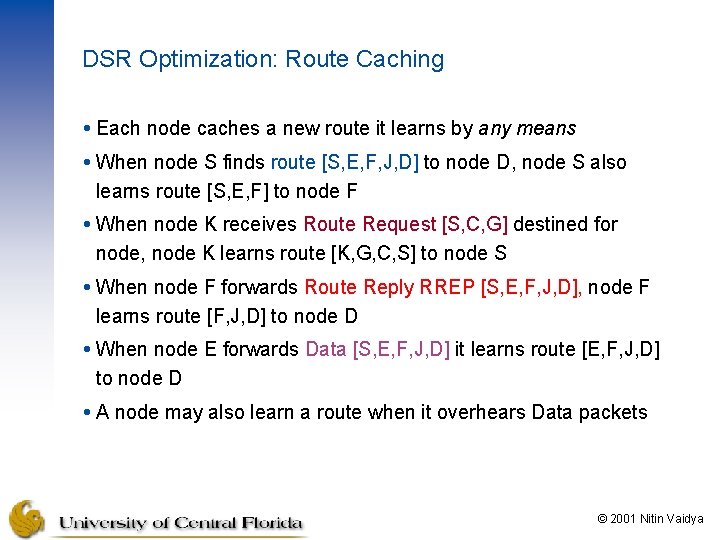
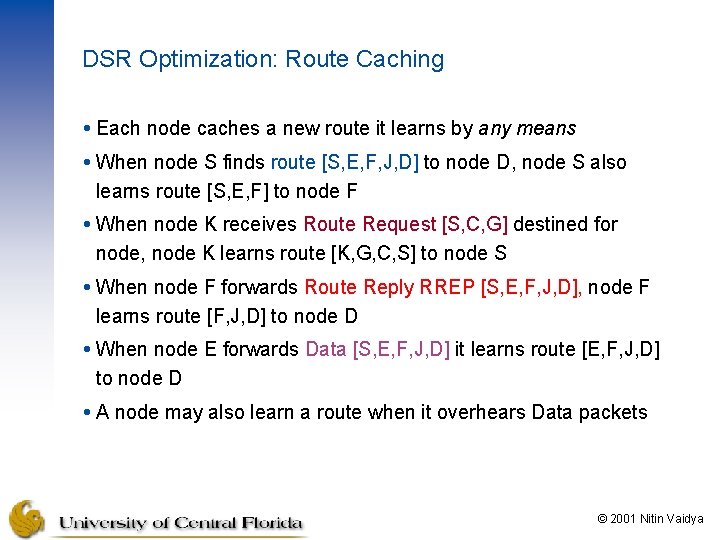
DSR Optimization: Route Caching Each node caches a new route it learns by any means When node S finds route [S, E, F, J, D] to node D, node S also learns route [S, E, F] to node F When node K receives Route Request [S, C, G] destined for node, node K learns route [K, G, C, S] to node S When node F forwards Route Reply RREP [S, E, F, J, D], node F learns route [F, J, D] to node D When node E forwards Data [S, E, F, J, D] it learns route [E, F, J, D] to node D A node may also learn a route when it overhears Data packets © 2001 Nitin Vaidya
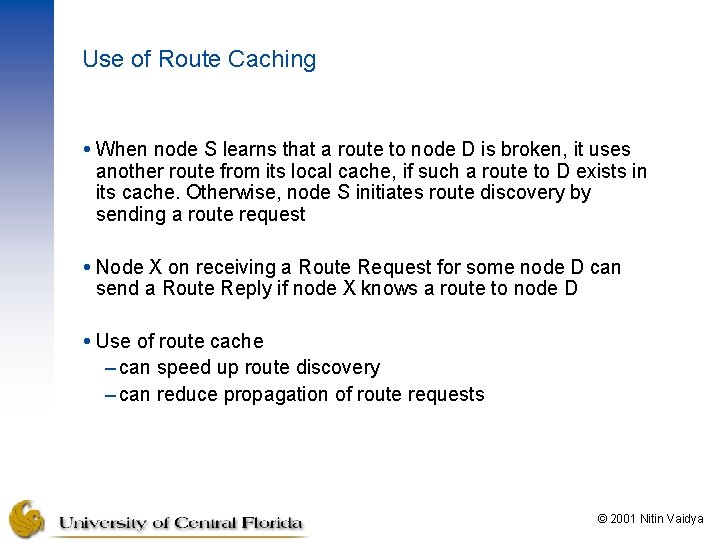
Use of Route Caching When node S learns that a route to node D is broken, it uses another route from its local cache, if such a route to D exists in its cache. Otherwise, node S initiates route discovery by sending a route request Node X on receiving a Route Request for some node D can send a Route Reply if node X knows a route to node D Use of route cache – can speed up route discovery – can reduce propagation of route requests © 2001 Nitin Vaidya
![Use of Route Caching S E F J D E F J D S Use of Route Caching [S, E, F, J, D] [E, F, J, D] S](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-26.jpg)
Use of Route Caching [S, E, F, J, D] [E, F, J, D] S [F, J, D], [F, E, S] E F B [J, F, E, S] C J [C, S] A M L G H [G, C, S] D K I N Z [P, Q, R] Represents cached route at a node (DSR maintains the cached routes in a tree format) © 2001 Nitin Vaidya
![Use of Route Caching Can Speed up Route Discovery S E F J D Use of Route Caching: Can Speed up Route Discovery [S, E, F, J, D]](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-27.jpg)
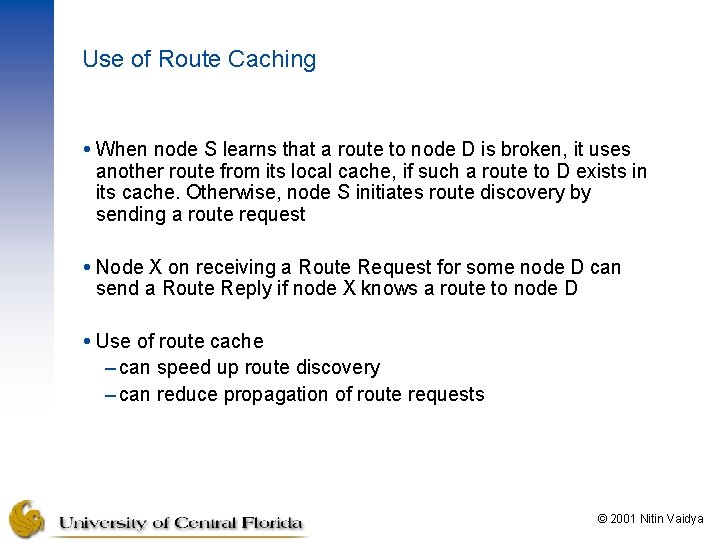
Use of Route Caching: Can Speed up Route Discovery [S, E, F, J, D] [E, F, J, D] S [F, J, D], [F, E, S] E F B C [G, C, S] [C, S] A [J, F, E, S] M J L G H I [K, G, C, S] K D RREP N RREQ When node Z sends a route request for node C, node K sends back a route reply [Z, K, G, C] to node Z using a locally cached route Z © 2001 Nitin Vaidya
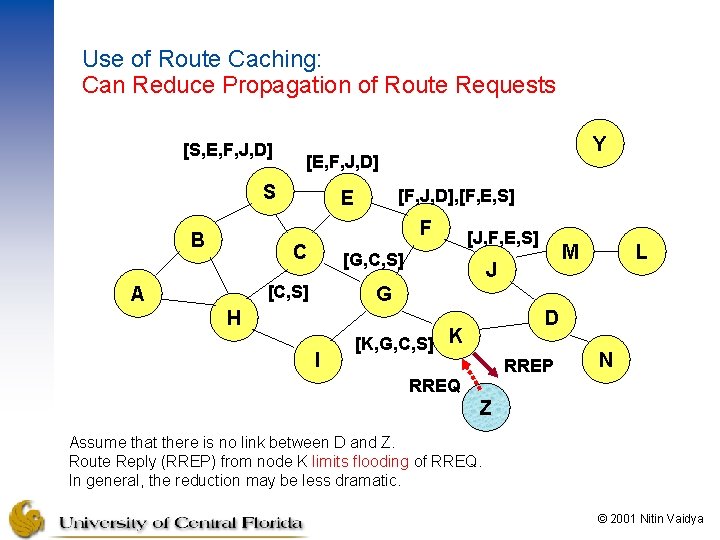
Use of Route Caching: Can Reduce Propagation of Route Requests [S, E, F, J, D] Y [E, F, J, D] S [F, J, D], [F, E, S] E F B C [G, C, S] [C, S] A [J, F, E, S] M J L G H I D [K, G, C, S] K RREP N RREQ Z Assume that there is no link between D and Z. Route Reply (RREP) from node K limits flooding of RREQ. In general, the reduction may be less dramatic. © 2001 Nitin Vaidya
![Route Error RERR Y RERR JD S Z E F B C M J Route Error (RERR) Y RERR [J-D] S Z E F B C M J](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-29.jpg)
Route Error (RERR) Y RERR [J-D] S Z E F B C M J A L G H K D I N J sends a route error to S along route J-F-E-S when its attempt to forward the data packet S (with route SEFJD) on J-D fails Nodes hearing RERR update their route cache to remove link J-D © 2001 Nitin Vaidya
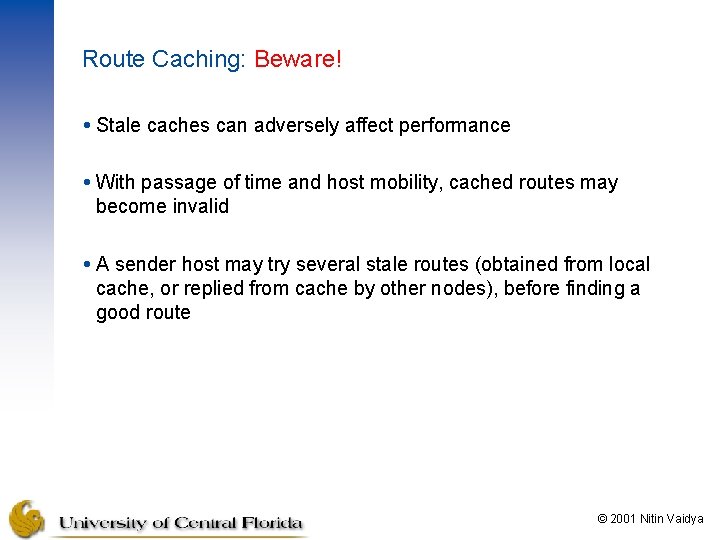
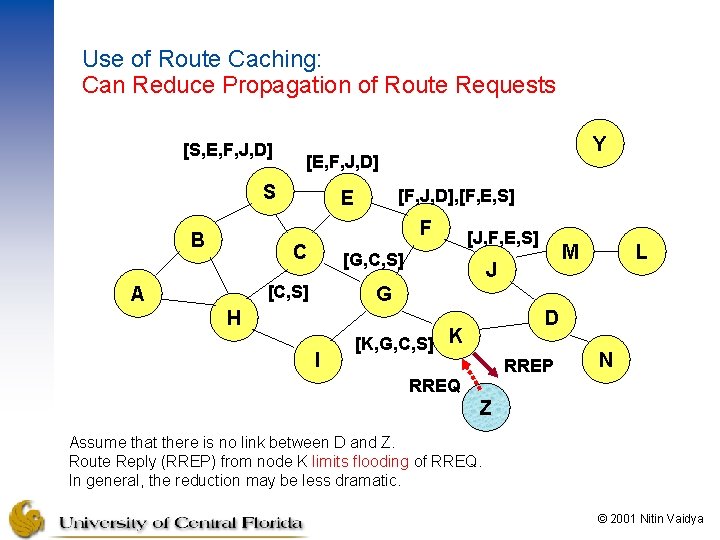
Route Caching: Beware! Stale caches can adversely affect performance With passage of time and host mobility, cached routes may become invalid A sender host may try several stale routes (obtained from local cache, or replied from cache by other nodes), before finding a good route © 2001 Nitin Vaidya
Dynamic Source Routing: Advantages Routes maintained only between nodes who need to communicate – reduces overhead of route maintenance Route caching can further reduce route discovery overhead A single route discovery may yield many routes to the destination, due to intermediate nodes replying from local caches © 2001 Nitin Vaidya
Dynamic Source Routing: Disadvantages Packet header size grows with route length due to source routing Flood of route requests may potentially reach all nodes in the network Care must be taken to avoid collisions between route requests propagated by neighboring nodes – insertion of random delays before forwarding RREQ Increased contention if too many route replies come back due to nodes replying using their local cache – Route Reply Storm problem – Reply storm may be eased by preventing a node from sending RREP if it hears another RREP with a shorter route © 2001 Nitin Vaidya
Dynamic Source Routing: Disadvantages An intermediate node may send Route Reply using a stale cached route, thus polluting other caches This problem can be eased if some mechanism to purge (potentially) invalid cached routes is incorporated. For some proposals for cache invalidation, see [Hu+ 2000] – Static timeouts – Adaptive timeouts based on link stability © 2001 Nitin Vaidya
![Cluster Gateway Switch Routing CGSR Chiang 1997 Nodes are grouped into clusters with Cluster Gateway Switch Routing (CGSR) [Chiang+ 1997] – Nodes are grouped into clusters with](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-34.jpg)
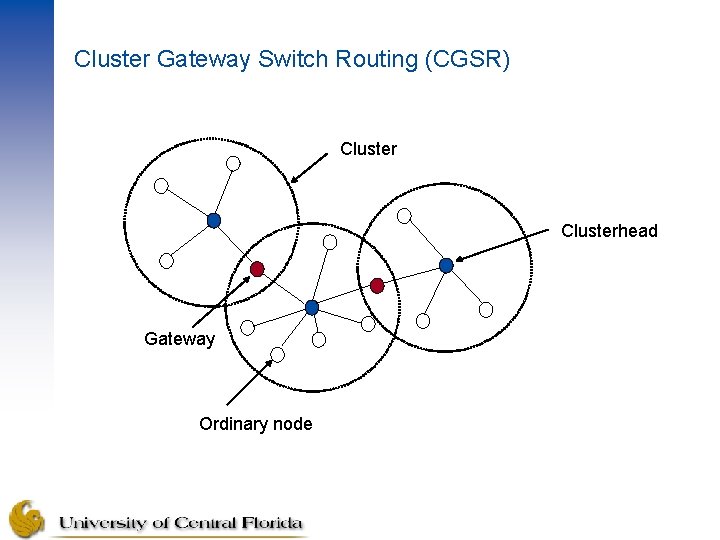
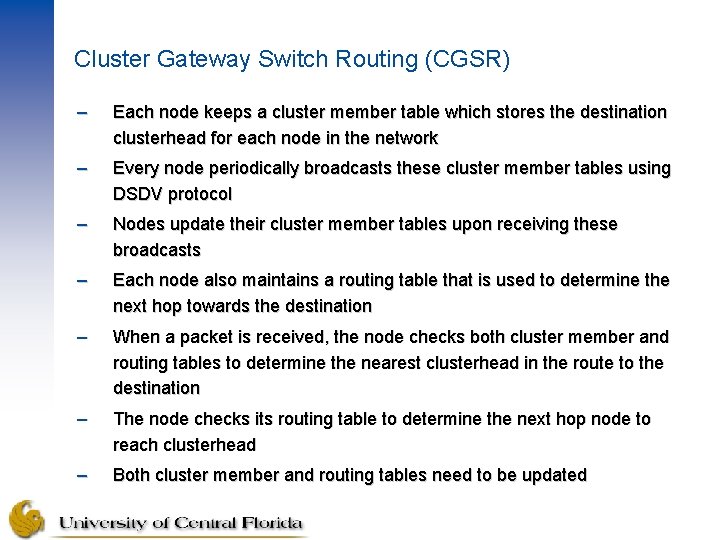
Cluster Gateway Switch Routing (CGSR) [Chiang+ 1997] – Nodes are grouped into clusters with one clusterhead in charge of nodes in a cluster – Distributed clusterhead selection algorithm is used to elect clusterheads – This algorithm needs to be invoked when a clusterhead moves away – Least Cluster Change (LCC) algorithm is introduced to avoid re-invoking election algorithm when the cluster membership update occurs – LCC algorithm allows the invocation of election algorithm when two clusterhead come into contact or when a node no longer be able to attach to any clusterheads – Uses DSDV as an underlying routing scheme – The route traffic follows: Source Clusterhead Gateway Clusterhead ……. . Destination
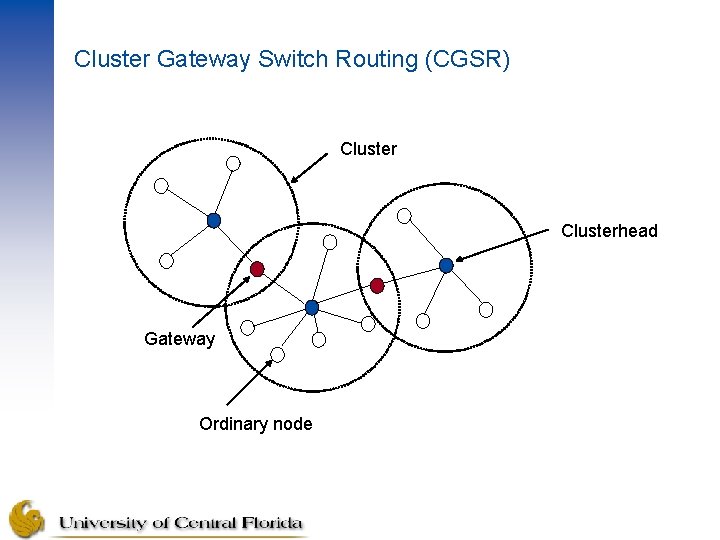
Cluster Gateway Switch Routing (CGSR) Clusterhead Gateway Ordinary node
Cluster Gateway Switch Routing (CGSR) – Each node keeps a cluster member table which stores the destination clusterhead for each node in the network – Every node periodically broadcasts these cluster member tables using DSDV protocol – Nodes update their cluster member tables upon receiving these broadcasts – Each node also maintains a routing table that is used to determine the next hop towards the destination – When a packet is received, the node checks both cluster member and routing tables to determine the nearest clusterhead in the route to the destination – The node checks its routing table to determine the next hop node to reach clusterhead – Both cluster member and routing tables need to be updated
![Adhoc OnDemand Distance Vector Routing AODV Perkins 1999 Improvement on DSDV due to Ad-hoc On-Demand Distance Vector Routing (AODV) [Perkins+ 1999] – Improvement on DSDV due to](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-37.jpg)
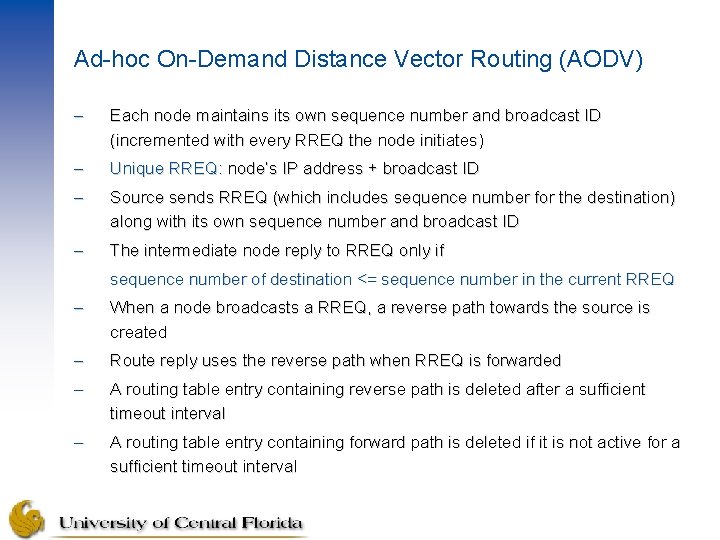
Ad-hoc On-Demand Distance Vector Routing (AODV) [Perkins+ 1999] – Improvement on DSDV due to minimizing number of broadcasts by creating routes on-demand basis – Improves DSR by maintaining routing tables only at the nodes between source and destination unlike routes being included in the data packets in DSR – Source initiates a path discovery process to locate the destination node by broadcasting a route request (RREQ) packet to its neighbors. The neighbors in turn forward the request to their neighbors and so on until either an intermediate node with valid (fresh enough) route or destination is located – Destination sequence numbers are used to ensure that routes are loop free and has the most recent route information
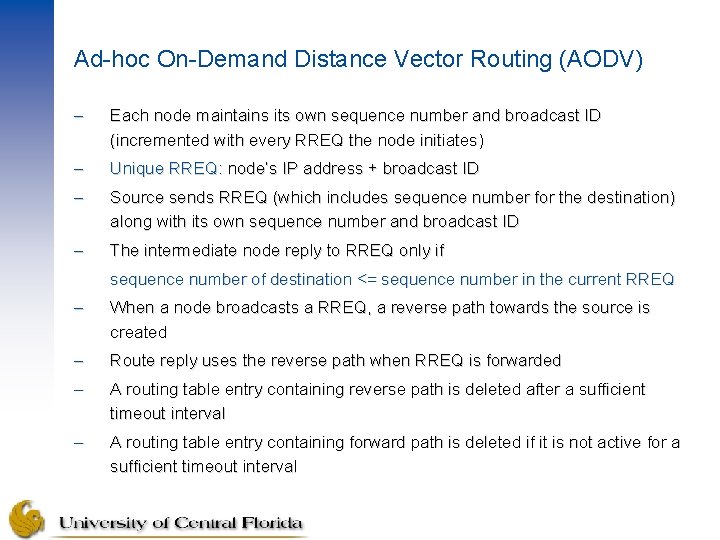
Ad-hoc On-Demand Distance Vector Routing (AODV) – Each node maintains its own sequence number and broadcast ID (incremented with every RREQ the node initiates) – Unique RREQ: node’s IP address + broadcast ID – Source sends RREQ (which includes sequence number for the destination) along with its own sequence number and broadcast ID – The intermediate node reply to RREQ only if sequence number of destination <= sequence number in the current RREQ – When a node broadcasts a RREQ, a reverse path towards the source is created – Route reply uses the reverse path when RREQ is forwarded – A routing table entry containing reverse path is deleted after a sufficient timeout interval – A routing table entry containing forward path is deleted if it is not active for a sufficient timeout interval
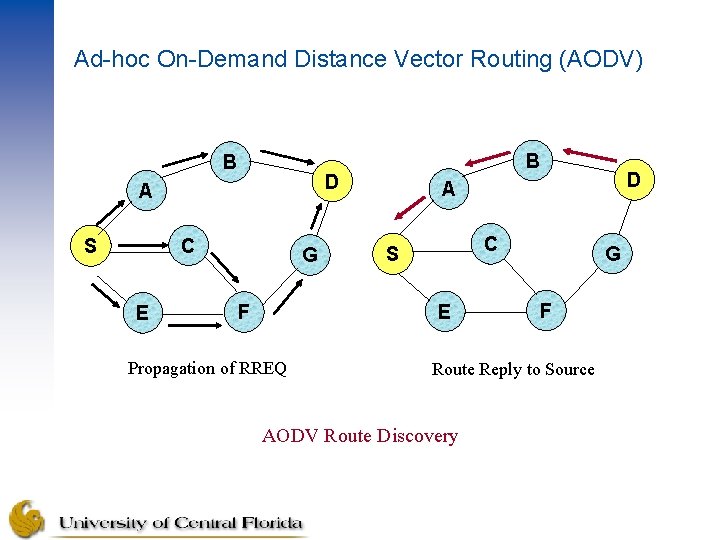
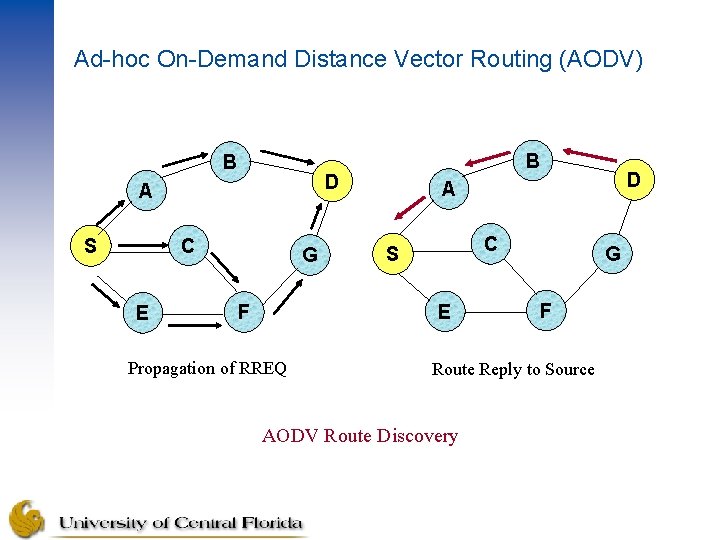
Ad-hoc On-Demand Distance Vector Routing (AODV) B D A C S E B G C S E F Propagation of RREQ D A G F Route Reply to Source AODV Route Discovery
Ad-hoc On-Demand Distance Vector Routing (AODV) – A node is considered active if it participates in forwarding the packets – Link failures are known to all active nodes using Route Error (RERR) messages (destination sequence numbers are also updated) – When a node cannot forward a packet towards a destination, it generates a RERR message; increments sequence number for destination; includes this incremented destination sequence number in the RERR message – When a source receives the RERR, it initiates a new route discovery process for the destination using sequence number equal or greater than the destination sequence number in RERR message – Periodic Hello messages are used to ensure the links exist – A link failure occurs when no hello message are exchanged for a timeout interval – Failure to receive MAC-level acknowledgement can also be interpreted as a link failure
![LocationAided Routing LAR Ko 1998 Utilizes location information via GPS to limit the Location-Aided Routing (LAR) [Ko+ 1998] – Utilizes location information (via GPS) to limit the](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-41.jpg)
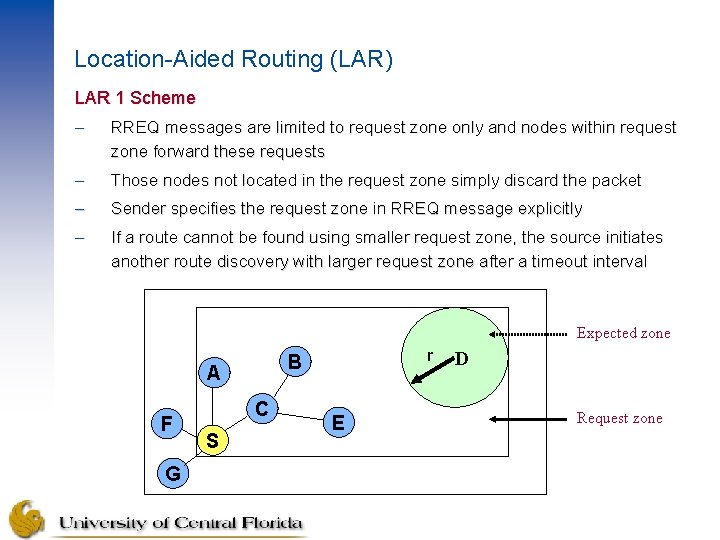
Location-Aided Routing (LAR) [Ko+ 1998] – Utilizes location information (via GPS) to limit the boundary of route request flood – Two new concepts: Ø Expected zone: determined based on the location and velocity if the destination and it is expected to contain the location of destination Ø Request zone: smallest rectangle which includes the location of source and the expected zone – It has assumed that source has advanced knowledge of the destination location and velocity – Two schemes proposed: Ø LAR 1 Ø LAR 2
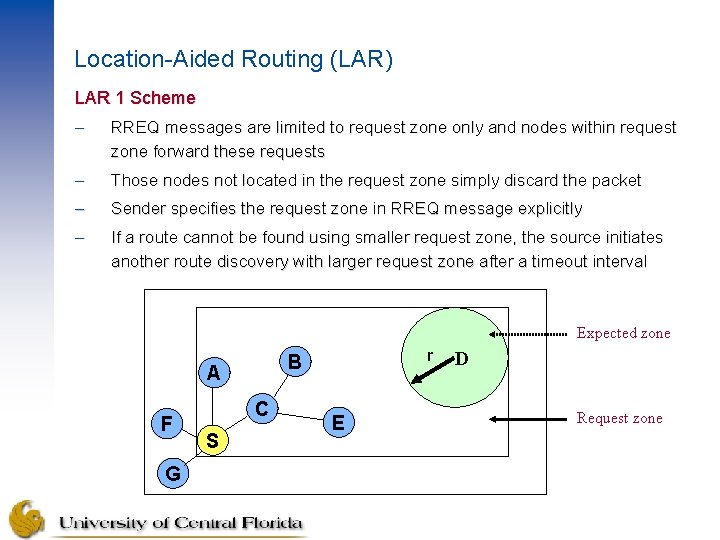
Location-Aided Routing (LAR) LAR 1 Scheme – RREQ messages are limited to request zone only and nodes within request zone forward these requests – Those nodes not located in the request zone simply discard the packet – Sender specifies the request zone in RREQ message explicitly – If a route cannot be found using smaller request zone, the source initiates another route discovery with larger request zone after a timeout interval Expected zone A F G C S r B E D Request zone
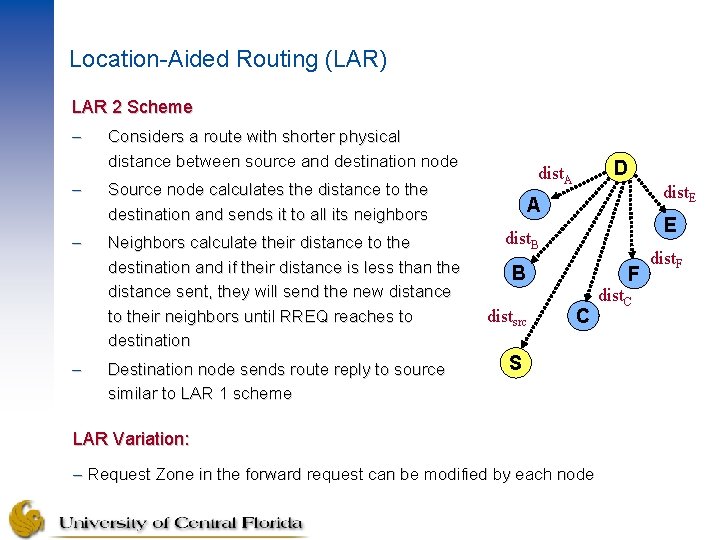
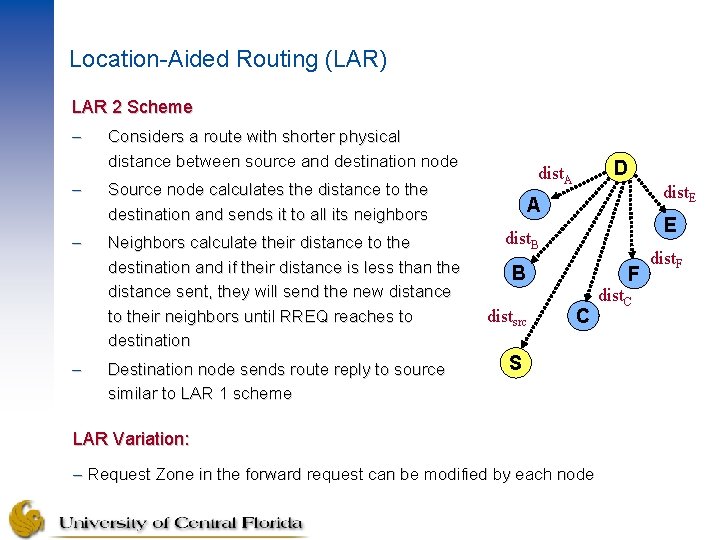
Location-Aided Routing (LAR) LAR 2 Scheme – – Considers a route with shorter physical distance between source and destination node Source node calculates the distance to the destination and sends it to all its neighbors Neighbors calculate their distance to the destination and if their distance is less than the distance sent, they will send the new distance to their neighbors until RREQ reaches to destination Destination node sends route reply to source similar to LAR 1 scheme D dist. A dist. E A E dist. B B distsrc F C S LAR Variation: – Request Zone in the forward request can be modified by each node dist. C dist. F
Location-Aided Routing (LAR) Advantages: – Reduces the route request flood to a limited area and reduces route discovery overhead as a result Disadvantages: – A node needs to know its physical location – GPS availability is not worldwide – All mobile nodes may not necessarily equipped with GPS receivers (heterogeneity of devices) – Error in positional information – Routing is solely based on location information – Prior and advance information about destination node may not be readily available at the source node – An existing route from intermediate node to destination node is not used
Location-Aided Routing (LAR) Suggestions/Improvements: – Possible improvement with more accurate request zones by using GPS; security concerns must be addressed – A request zone can be calculated at each intermediate node than from the source node – In LAR 1 scheme, each intermediate node calculate its own request zone and broadcast to all its neighbors. This may further reduce the overhead and route discovery can be initiated from intermediate node to the destination – In LAR 1 scheme, determine the rectangle by considering relative positions of source and destination – Scalability – Performance comparison of LAR with widely used routing protocols – LAR and CGSR – LAR and AODV
![PowerAware Routing Singh 1998 In existing MAC protocols nodes are powered on most Power-Aware Routing [Singh+ 1998] – In existing MAC protocols, nodes are powered on most](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-46.jpg)
Power-Aware Routing [Singh+ 1998] – In existing MAC protocols, nodes are powered on most of the time even when they are idle – There is a need for increasing node and network life-time by using power -aware metric for routing – Five power-aware metrics for determining routes based on battery power consumption at the nodes are introduced: Ø Minimize energy consumed/packet Ø Maximize time to network partition Ø Minimize variance in node power levels Ø Minimize cost/packet Ø Minimize maximum node cost
![Zone Routing Protocol ZRP Hass 1998 Hybrid protocol incorporates the merits of proactive Zone Routing Protocol (ZRP) [Hass+ 1998] – Hybrid protocol incorporates the merits of proactive](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-47.jpg)
Zone Routing Protocol (ZRP) [Hass+ 1998] – Hybrid protocol incorporates the merits of proactive (table-driven) and reactive (on-demand) routing protocols – Each node has a routing zone by specifying a zone radius in terms of hops – Size of a zone can affect the communication performance – Within the routing zone, a table driven routing protocol is used; therefore, each node has a route to all the other nodes within the zone – If destination falls out of the routing zone of source node, an on-demand routing protocol is used – Three sub-protocols: Ø Intrazone Routing Protocol (IARP) proactive Ø Interzone Routing Protocol (IERP) reactive Ø Bordercast Resolution Protocol (BRP)
![References Bertsekas 1987 D Bertsekas and R Gallager Data Networks PrenticeHall Englewood Cliffs N References [Bertsekas+ 1987] D. Bertsekas and R. Gallager, Data Networks, Prentice-Hall, Englewood Cliffs, N.](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-48.jpg)
References [Bertsekas+ 1987] D. Bertsekas and R. Gallager, Data Networks, Prentice-Hall, Englewood Cliffs, N. J. , 1987, 297 -333. [Chiang+ 1997] C. -C. Chiang, H. K. Wu, W. Liu, and M. Gerla, Routing in Clustered Multihop, Mobile Wireless Networks with Fading Channel, Proceedings of IEEE SIGCON’ 97, pp. 197 -211. [Dijkstra 1959] E. W. Dijkstra, A Note on Two Problems in Connection with Graphs, Numerische Math, 1: 269 -271. [Ford+ 1962] L. R. Ford, Jr. and D. R. Fulkerson, Flows in Networks, Princeton University Press, Princeton, N. J. , 1962. [Haas+ 1998] Z. J. Haas and M. R. Pearlman, The Performance of Query Control Schemes for the Zone Routing Protocol, ACM MOBICOM 1998. [Hu+ 2000] Y-C Hu and D. B. Johnson, Caching strategies in on-demand routing protocols for wireless ad hoc networks, MOBICOM 2000, pp. 231 -242. [Johnson+ 1996] D. B. Johnson and D. A. Maltz, Dynamic Source Routing in Ad-Hoc Wireless Networks, Mobile Computing, ed. T. Imielinski and H. Korth, Kluwer Academic Publishers, pp. 153 -181, 1996. [Ko+ 1998] Y. Ko and N. H. Vaidya, Location-Aided Routing (LAR) in Mobil Ad Hoc Networks, MOBICOM'98, October 1998, Dallas. (Recipient of the MOBICOM'98 Best Student Paper Award)
![References Leiner 1962 B M Leiner D L Nielson and F A Tobagi Issues References [Leiner+ 1962] B. M. Leiner, D. L. Nielson, and F. A. Tobagi, Issues](https://slidetodoc.com/presentation_image/35a1344be49136c7bc8094dbed16b84e/image-49.jpg)
References [Leiner+ 1962] B. M. Leiner, D. L. Nielson, and F. A. Tobagi, Issues in Packet Radio Network Design, Proceedings of the IEEE (Special Issue Packet Radio Networks), 75(1), January 1987, pp. 6 -20. [Mc. Quillan+ 1980] J. M. Mc. Quillan, I. Richer, and E. C. Rosen, New Routing Algorithm for the ARPANET, IEEE Transactions on Communications COM-28(5), May 1980, pp. 711 -719. [Perkins+ 1994] C. E. Perkins and P. Bhagwat, Highly Dynamic Destination-Sequenced Distance. Vector Routing (DSDV) for Mobile Computers, Commuter Communications Review, October 1994, pp. 234 -244. [Perkins+ 1999] C. E. Perkins and E. M. Royer, Ad-hoc On-Demand Distance Vector Routing, Proceedings of 2 nd IEEE Workshop on Mobile Computing Systems and Applications, 1999. [Singh+ 1998] S. Singh, M. Woo and C. S. Raghavendra, Power-Aware Routing in Mobile Ad Hoc Networks, Proceedings of ACM/IEEE MOBICOM’ 98, pp. 181 -190.