Panoply LowTCB Linux Applications With SGX Enclaves Shweta
Panoply: Low-TCB Linux Applications With SGX Enclaves Shweta Shinde Dat Le Tien Shruti Tople Prateek Saxena National University of Singapore
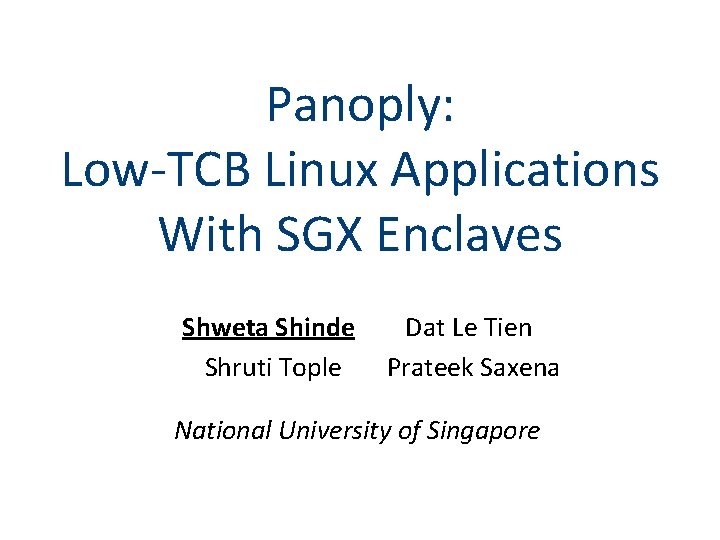
TCB: Hosting a Web Server Current systems have a large TCB 183 KLOC Webserver 10 MLOC 150 KLOC Operating System Hypervisor 2
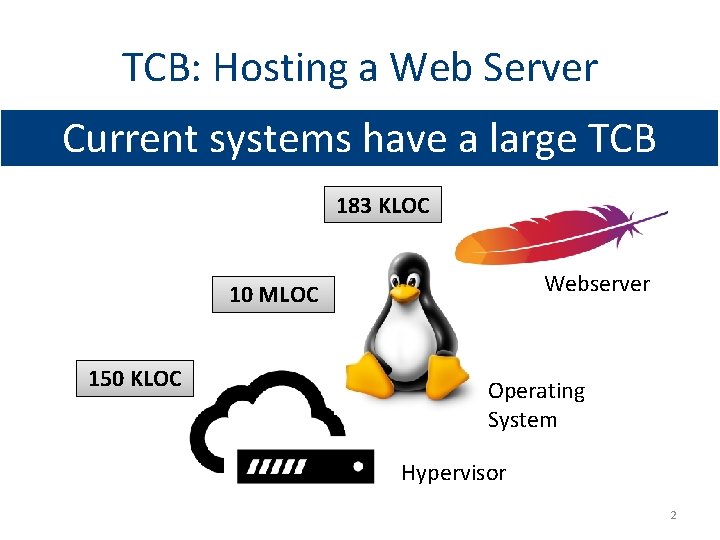
SGX: Hardware-root of Trust Ring 3 Web Server Enclave Other Applications RAM Operating System / VMM Ring 0 - 2 EPC Trusted Untrusted 3
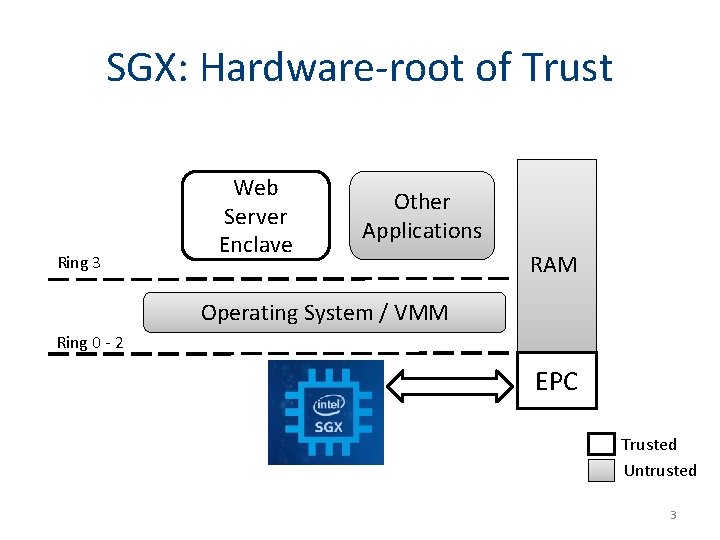
SGX: Hardware-root of Trust Webserver 10 MLOC 150 KLOC Enclave 183 KLOC Operating System Hypervisor Confidentiality and Integrity Hardware 4
. . but limits the expressiveness of the SGX eliminates all the applications (e. g. , no syscalls) non-application software from TCB. . 5
![TCB & Expressiveness Trade-off TCB Library. OS Haven [OSDI’ 14] ~1 MLOC Containers ~100 TCB & Expressiveness Trade-off TCB Library. OS Haven [OSDI’ 14] ~1 MLOC Containers ~100](http://slidetodoc.com/presentation_image_h/238e0e467d575802421837e46dfc6550/image-6.jpg)
TCB & Expressiveness Trade-off TCB Library. OS Haven [OSDI’ 14] ~1 MLOC Containers ~100 KLOC Scone [OSDI’ 16] Ryoan [OSDI’ 16] ~KLOC S c ys all ll s all s t a c c m d d g s s Sy rea t M Th Th en Ev Graphene-SGX [Euro. Sys’ 14] ? ll s t a m c d g s Sy rea t M ec Th en / ex Ev rk o Expressiveness 6
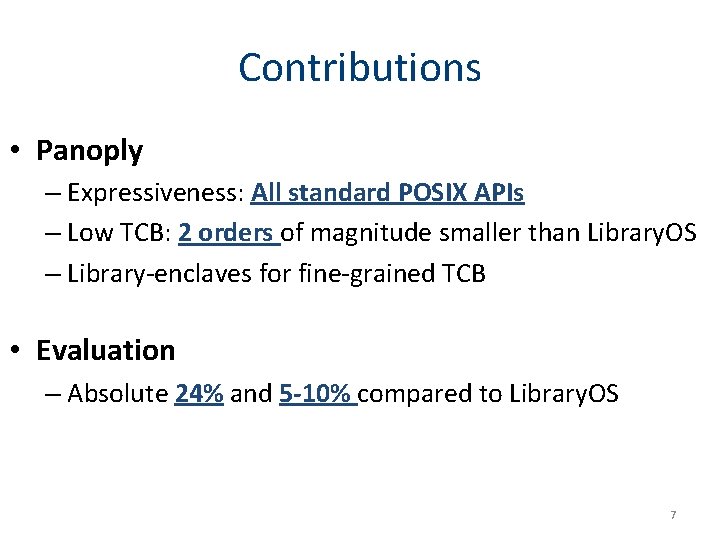
Contributions • Panoply – Expressiveness: All standard POSIX APIs – Low TCB: 2 orders of magnitude smaller than Library. OS – Library-enclaves for fine-grained TCB • Evaluation – Absolute 24% and 5 -10% compared to Library. OS 7
Problem 8
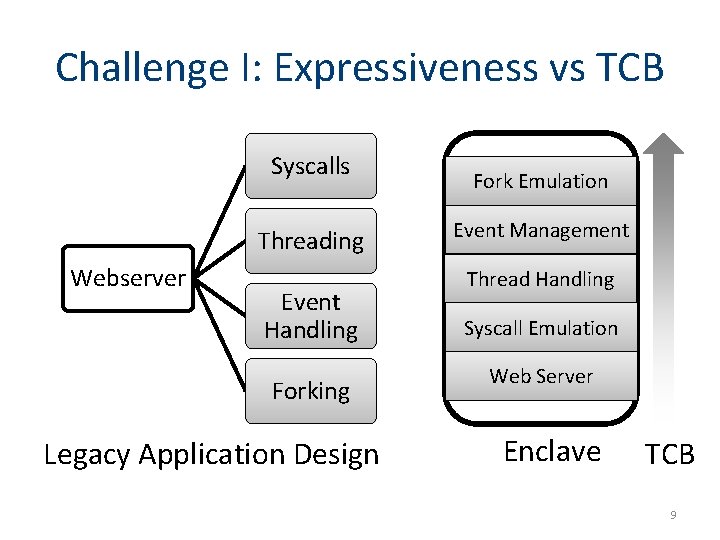
Challenge I: Expressiveness vs TCB Syscalls Threading Webserver Event Handling Forking Legacy Application Design Fork Emulation Event Management Thread Handling Syscall Emulation Web Server Enclave TCB 9

Challenge I: Expressiveness vs. TCB Expressiveness TCB 10
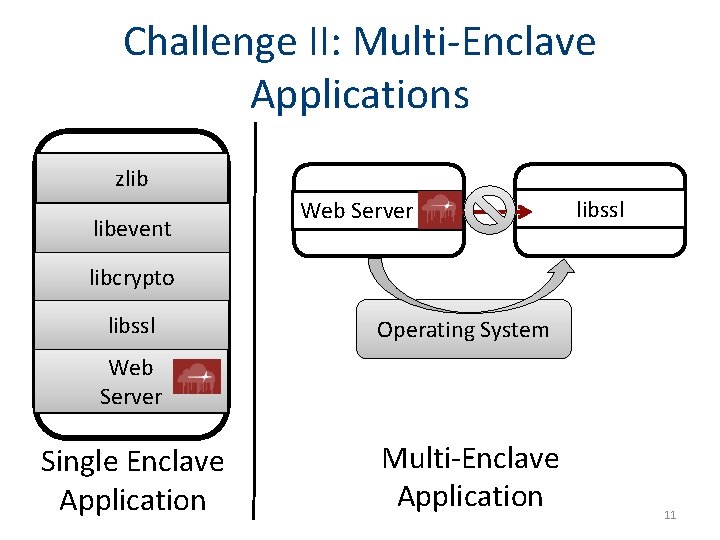
Challenge II: Multi-Enclave Applications zlib libevent Web Server libssl libcrypto libssl Operating System Web Server Single Enclave Application Multi-Enclave Application 11
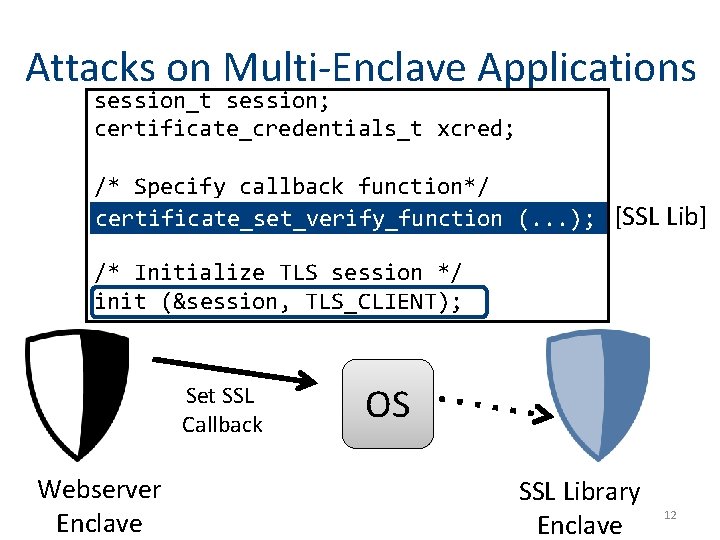
Attacks on Multi-Enclave Applications session_t session; certificate_credentials_t xcred; /* Specify callback function*/ certificate_set_verify_function (. . . ); [SSL Lib] /* Initialize TLS session */ init (&session, TLS_CLIENT); Set SSL Callback Webserver Enclave OS SSL Library Enclave 12
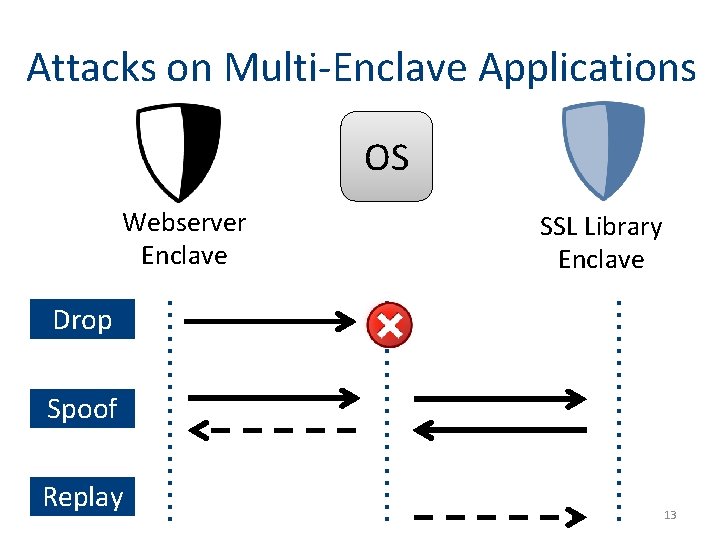
Attacks on Multi-Enclave Applications OS Webserver Enclave SSL Library Enclave Drop Spoof Replay 13

Our Solution: Panoply 14

Panoply Runtime Microns keep libc outside the enclave Micron Enclave-bound Logic Panoply Shim Lib libc. so Trusted SGX Lib Non-enclave Logic Untrusted SGX Lib Enclave Non- Enclave Linux User-level Process 15
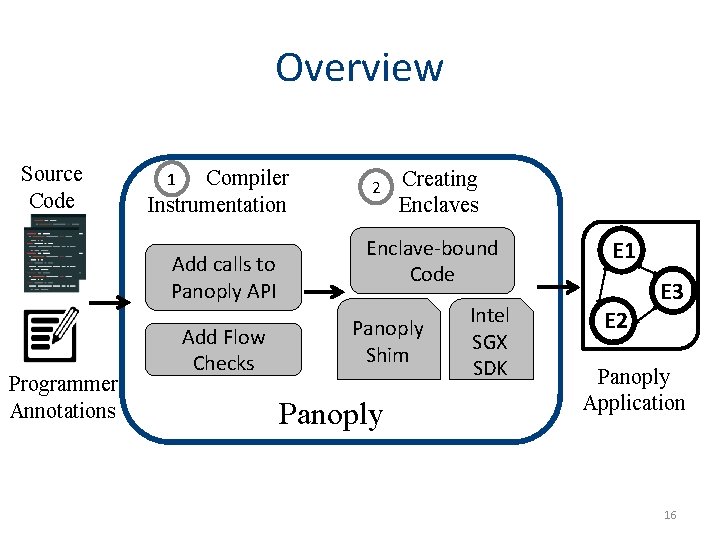
Overview Source Code Compiler Instrumentation 1 Add calls to Panoply API Programmer Annotations Add Flow Checks 2 Creating Enclaves E 1 Enclave-bound Code E 2 Panoply Shim Panoply Intel SGX SDK E 1 Ap. E 2 E 3 Panoply Application 16
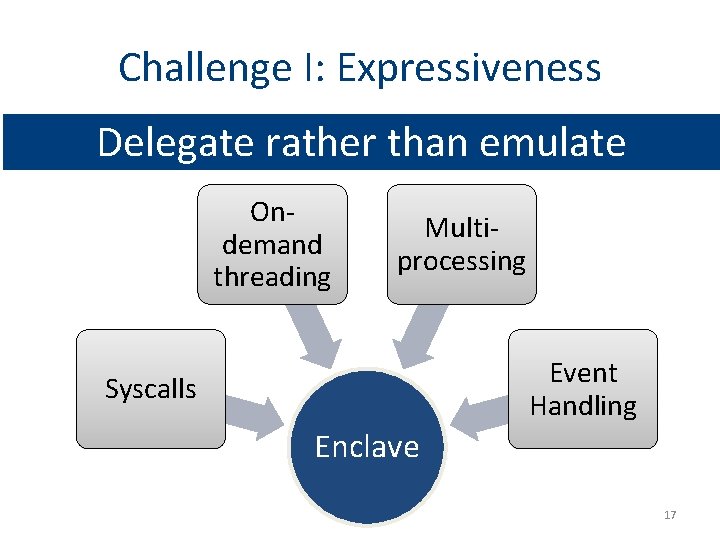
Challenge I: Expressiveness Delegate rather than emulate Ondemand threading Multiprocessing Event Handling Syscalls Enclave 17
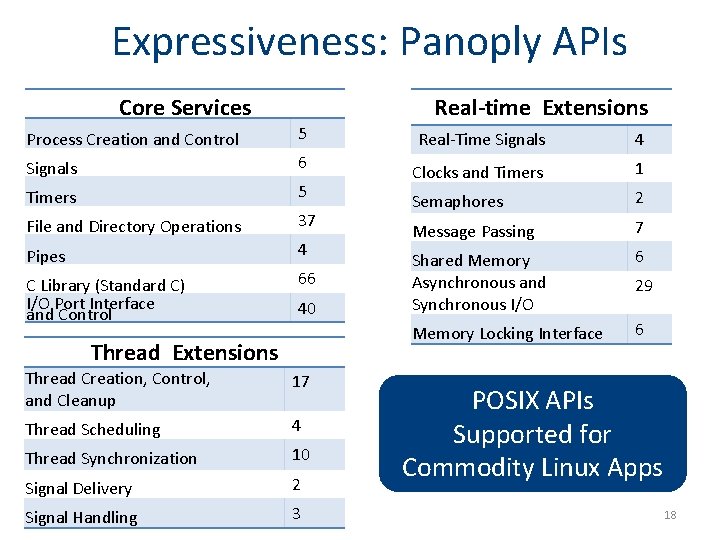
Expressiveness: Panoply APIs Real-time Extensions Core Services Process Creation and Control 5 Signals 6 Timers 5 File and Directory Operations 37 Pipes 4 C Library (Standard C) I/O Port Interface and Control 66 40 Thread Extensions Thread Creation, Control, and Cleanup 17 Thread Scheduling 4 Thread Synchronization 10 Signal Delivery 2 Signal Handling 3 Real-Time Signals 4 Clocks and Timers 1 Semaphores 2 Message Passing 7 Shared Memory Asynchronous and Synchronous I/O 6 Memory Locking Interface 6 29 POSIX APIs Supported for Commodity Linux Apps 18
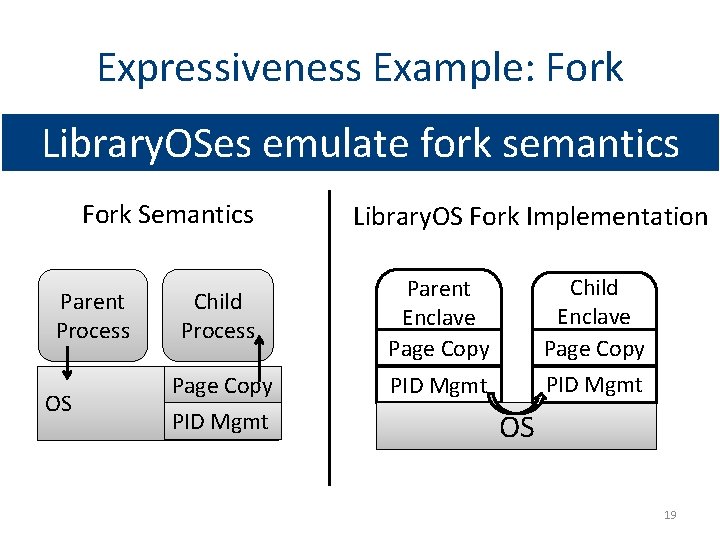
Expressiveness Example: Fork Library. OSes emulate fork semantics Fork Semantics Parent Process OS Library. OS Fork Implementation Child Process Parent Enclave Page Copy Child Enclave Page Copy PID Mgmt OS 19
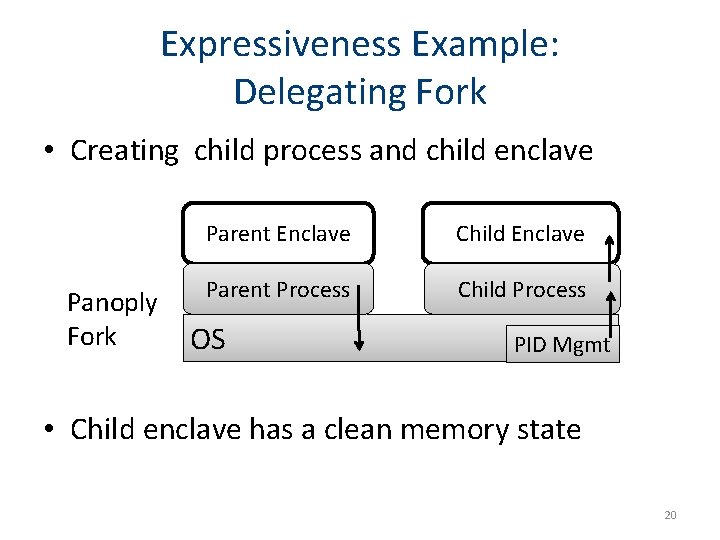
Expressiveness Example: Delegating Fork • Creating child process and child enclave Parent Enclave Child Enclave Parent Process Child Process Panoply Fork OS PID Mgmt • Child enclave has a clean memory state 20
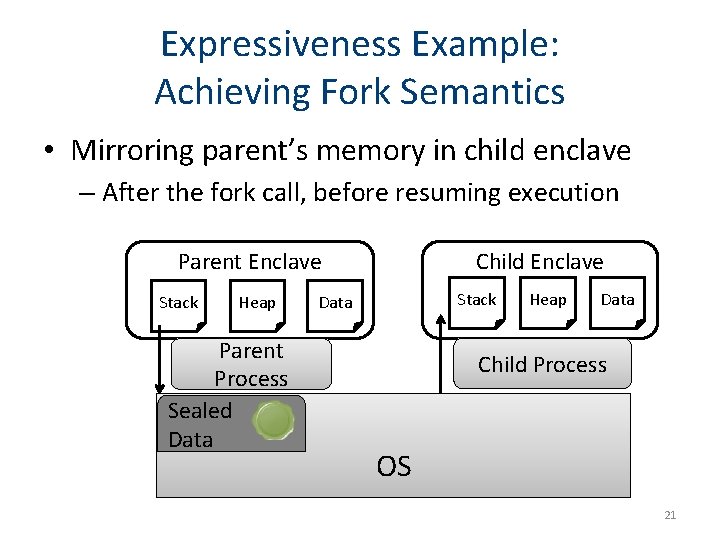
Expressiveness Example: Achieving Fork Semantics • Mirroring parent’s memory in child enclave – After the fork call, before resuming execution Parent Enclave Stack Heap Parent Process Sealed Data Child Enclave Stack Data Heap Data Child Process OS 21
Expressiveness Example: Achieving Fork Semantics • Mirroring parent’s memory in child enclave – Full replica: default mode in Panoply • Alternative strategies to full replica – Copy on demand: Requires page-fault support from SGX v 2 – Copy on need: Replicate selected addresses which are pre-determined by static analysis 22
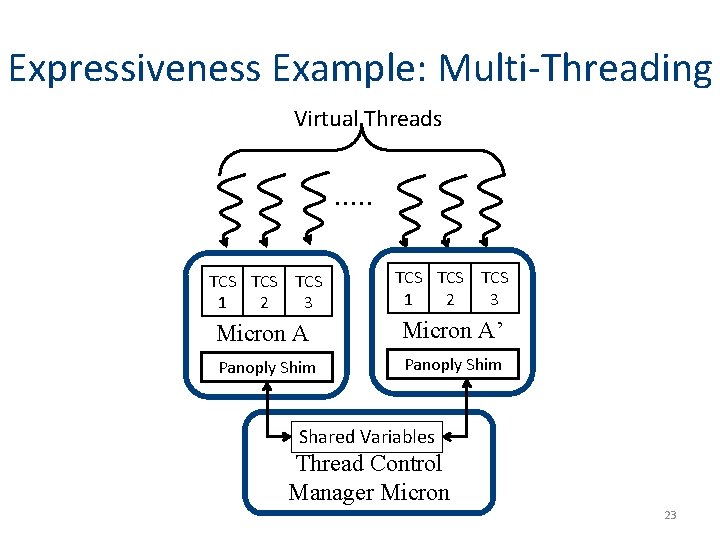
Expressiveness Example: Multi-Threading Virtual Threads TCS TCS TCS 1 2 3 Micron A’ Panoply Shim Shared Variables Thread Control Manager Micron 23
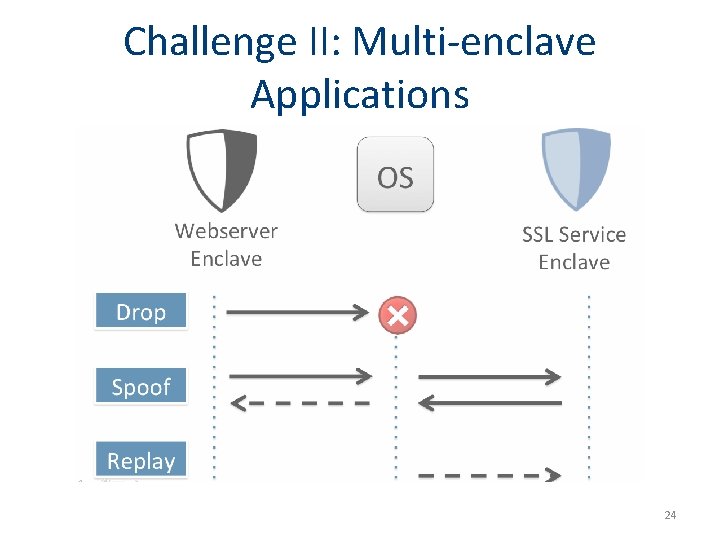
Challenge II: Multi-enclave Applications 24

Securing Multi-Enclave Apps Enclave Pair-wise Identity Nonce Enclave 1 Attack Spoofing Replay Silent Drops OS Call Ack Enclave 2 Security Property Sender / Receiver Authentication Message Freshness Reliable Delivery 25
Evaluation 26
Benchmarks • Real-world use-cases for SGX – 4 apps: Tor, H 2 O web server, Free. TDS, Open. SSL • Operating system stress testing – 26 LMBench benchmarks tests – 17 metrics for memory, network, signal, syscall APIs 27
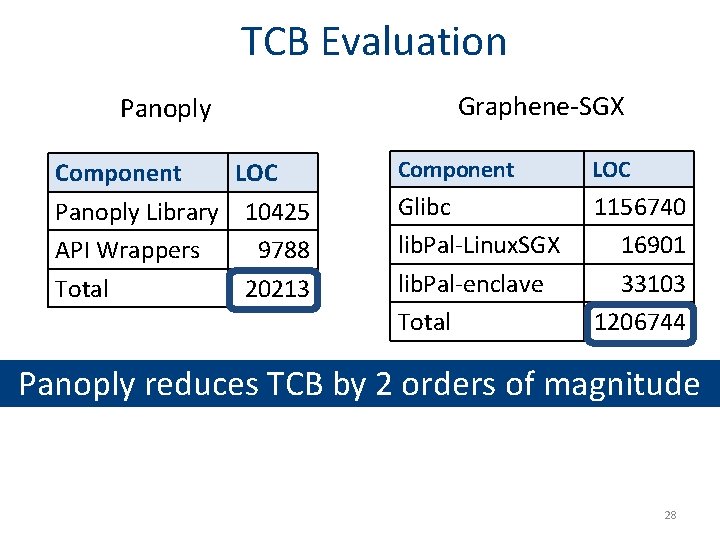
TCB Evaluation Panoply Component LOC Panoply Library 10425 API Wrappers 9788 Total 20213 Graphene-SGX Component LOC Glibc lib. Pal-Linux. SGX lib. Pal-enclave Total 1156740 16901 33103 1206744 Panoply reduces TCB by 2 orders of magnitude 28
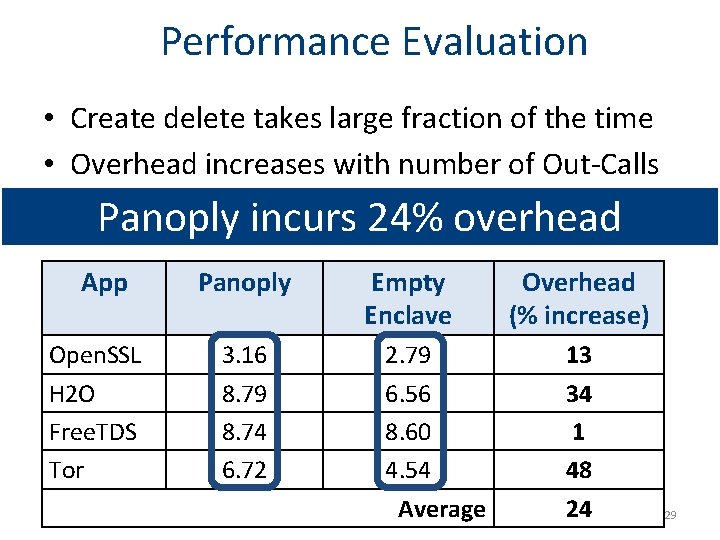
Performance Evaluation • Create delete takes large fraction of the time • Overhead increases with number of Out-Calls Panoply incurs 24% overhead App Open. SSL H 2 O Free. TDS Tor Panoply 3. 16 8. 79 8. 74 6. 72 Empty Enclave 2. 79 6. 56 8. 60 4. 54 Average Overhead (% increase) 13 34 1 48 24 29
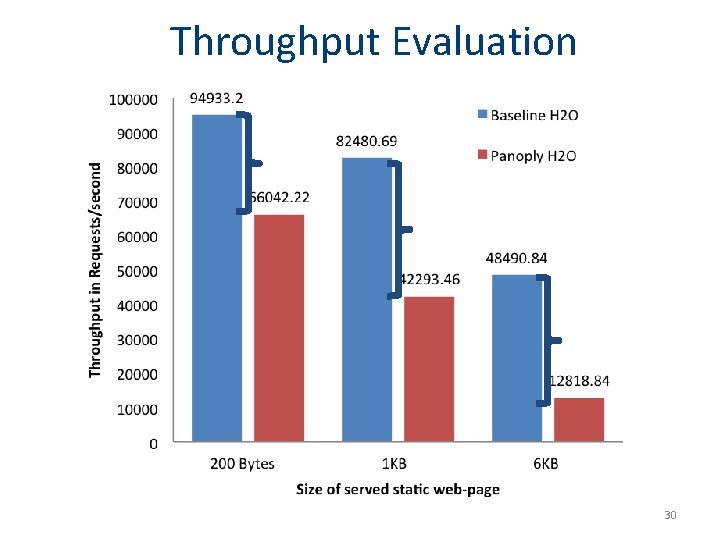
Throughput Evaluation 30
Throughput Evaluation Overhead for SGX-apps is proportional to the size of requests 31
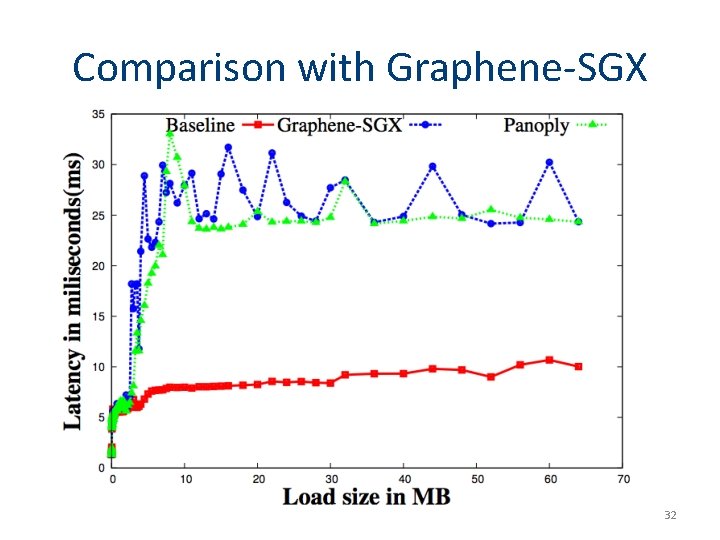
Comparison with Graphene-SGX 32
Comparison with Graphene-SGX Panoply performance varies by 5 -10% as compared to Graphene-SGX 33
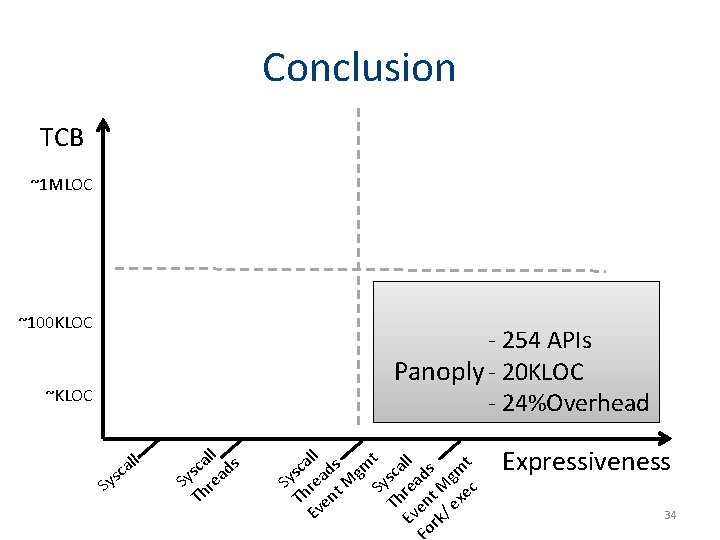
Conclusion TCB ~1 MLOC ~100 KLOC - 254 APIs Panoply - 20 KLOC - 24%Overhead ~KLOC S c ys all ll s a sc ad y S re Th ll s t a a c m d m s c g Sy rea t M Sys read Mg c h nt exe Th en T e Ev Ev rk/ o Expressiveness 34
Contact • Shweta Shinde shweta 24@comp. nus. edu. sg • Panoply Benchmarks & Casestudies: http: //shwetasshinde 24. github. io/Panoply/ Thank You ! 35
![References • [OSDI’ 14] A. Baumann, M. Peinado, and G. Hunt, Shielding Applications from References • [OSDI’ 14] A. Baumann, M. Peinado, and G. Hunt, Shielding Applications from](http://slidetodoc.com/presentation_image_h/238e0e467d575802421837e46dfc6550/image-36.jpg)
References • [OSDI’ 14] A. Baumann, M. Peinado, and G. Hunt, Shielding Applications from an Untrusted Cloud with Haven • [OSDI’ 16] S. Arnautov, B. Trach, F. Gregor, T. Knauth, A. Martin, C. Priebe, J. Lind, D. Muthukumaran, D. O’Keeffe, M. L. Stillwell, D. Goltzsche, D. Eyers, R. Kapitza, P. Pietzuch, and C. Fetzer, SCONE: Secure Linux Containers with Intel SGX • [OSDI’ 16] T. Hunt, Z. Zhu, Y. Xu, S. Peter, and E. Witchel, Ryoan: A Distributed Sandbox for Untrusted Computation on Secret Data • [Euro. Sys’ 14] Graphene-SGX Library OS - a library OS for Linux multi-process applications, with Intel SGX support 36
- Slides: 36